Professional-Cloud-Security-Engineer Practice Exam - Google Cloud Certified - Professional Cloud Security Engineer
Reliable Study Materials & Testing Engine for Professional-Cloud-Security-Engineer Exam Success!
Exam Code: Professional-Cloud-Security-Engineer
Exam Name: Google Cloud Certified - Professional Cloud Security Engineer
Certification Provider: Google
Certification Exam Name: Google Cloud Certified

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
Professional-Cloud-Security-Engineer: Google Cloud Certified - Professional Cloud Security Engineer Study Material and Test Engine
Last Update Check: Mar 23, 2026
Latest 134 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena Google Google Cloud Certified - Professional Cloud Security Engineer (Professional-Cloud-Security-Engineer) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
Google Professional-Cloud-Security-Engineer Exam FAQs
Introduction of Google Professional-Cloud-Security-Engineer Exam!
Google Professional-Cloud-Security-Engineer is a Google Cloud Platform certification exam. It tests a candidate's knowledge of Google Cloud Platform security features and best practices related to designing, implementing, and managing secure infrastructure on Google Cloud Platform.
What is the Duration of Google Professional-Cloud-Security-Engineer Exam?
The Google Professional Cloud Security Engineer exam is a two-hour exam consisting of 60 multiple-choice and multiple-select questions.
What are the Number of Questions Asked in Google Professional-Cloud-Security-Engineer Exam?
The Google Professional-Cloud-Security-Engineer Certification Exam consists of 90 multiple-choice and performance-based questions.
What is the Passing Score for Google Professional-Cloud-Security-Engineer Exam?
Google does not publish official passing scores for its certification exams. The Google Certified Professional-Cloud-Security-Engineer exam is designed to measure a candidate’s ability to design, develop, manage, and secure cloud solutions using Google Cloud Platform. Candidates must demonstrate an understanding of Google Cloud Platform security best practices, including secure access control, data protection, and logging and monitoring.
What is the Competency Level required for Google Professional-Cloud-Security-Engineer Exam?
The Competency Level required for the Google Professional-Cloud-Security-Engineer exam is Expert.
What is the Question Format of Google Professional-Cloud-Security-Engineer Exam?
The Google Professional-Cloud-Security-Engineer Exam consists of multiple choice, multiple select, and drag and drop questions.
How Can You Take Google Professional-Cloud-Security-Engineer Exam?
Google Professional-Cloud-Security-Engineer exam can be taken online or in a testing center. To take the exam online, you will need to register for the exam on the Google Cloud Platform website. Once you have registered, you will receive an email with instructions on how to access the exam. To take the exam in a testing center, you will need to find a testing center near you that offers the exam. You will then need to register for the exam at the testing center and follow their instructions.
What Language Google Professional-Cloud-Security-Engineer Exam is Offered?
Google Professional-Cloud-Security-Engineer Exam is offered in English.
What is the Cost of Google Professional-Cloud-Security-Engineer Exam?
The cost of the Google Professional-Cloud-Security-Engineer exam is $200 USD.
What is the Target Audience of Google Professional-Cloud-Security-Engineer Exam?
The target audience for the Google Professional-Cloud-Security-Engineer exam are individuals who are interested in demonstrating their expertise in designing, developing, and managing secure solutions on Google Cloud Platform. This includes security engineers, system administrators, and IT professionals who are responsible for designing, deploying, and managing secure solutions on Google Cloud Platform.
What is the Average Salary of Google Professional-Cloud-Security-Engineer Certified in the Market?
The average salary for a Professional Cloud Security Engineer with Google certification is $135,000 per year.
Who are the Testing Providers of Google Professional-Cloud-Security-Engineer Exam?
Google does not provide testing for the Professional-Cloud-Security-Engineer exam. The exam is administered by an independent testing provider, Kryterion.
What is the Recommended Experience for Google Professional-Cloud-Security-Engineer Exam?
The recommended experience for the Google Professional-Cloud-Security-Engineer exam includes having at least two years of experience in designing, developing, and managing secure cloud solutions, as well as experience in one or more of the following areas:
• Cloud security architecture
• Identity and access management
• Network security
• Data protection
• Security operations
• Compliance
• Incident response
• Risk management
• Cloud security best practices
What are the Prerequisites of Google Professional-Cloud-Security-Engineer Exam?
The Google Professional-Cloud-Security-Engineer exam does not have any prerequisites. However, it is recommended that candidates have at least two years of experience in designing, developing, and managing security solutions on Google Cloud Platform. Additionally, candidates should have a working knowledge of security best practices, cloud architecture, and Google Cloud Platform services.
What is the Expected Retirement Date of Google Professional-Cloud-Security-Engineer Exam?
The official website for the Google Professional Cloud Security Engineer exam is https://cloud.google.com/certification/cloud-security-engineer. You can find information about the retirement date of the exam on this page.
What is the Difficulty Level of Google Professional-Cloud-Security-Engineer Exam?
The difficulty level of the Google Professional-Cloud-Security-Engineer exam is considered to be intermediate.
What is the Roadmap / Track of Google Professional-Cloud-Security-Engineer Exam?
1. Become familiar with the Google Cloud Platform and its security features.
2. Read the Google Cloud Platform Security Whitepaper.
3. Take the Google Cloud Platform Security Fundamentals course.
4. Take the Google Cloud Platform Security Engineer Professional exam.
5. Take the Google Cloud Platform Security Engineer Professional certification exam.
What are the Topics Google Professional-Cloud-Security-Engineer Exam Covers?
The Google Professional-Cloud-Security-Engineer exam covers the following topics:
1. Security Concepts: This topic covers the basic concepts of security, including risk management, access control, authentication and authorization, encryption, and security best practices.
2. Security Architecture: This topic covers the architecture of Google Cloud Platform, including the security components and how they interact with each other.
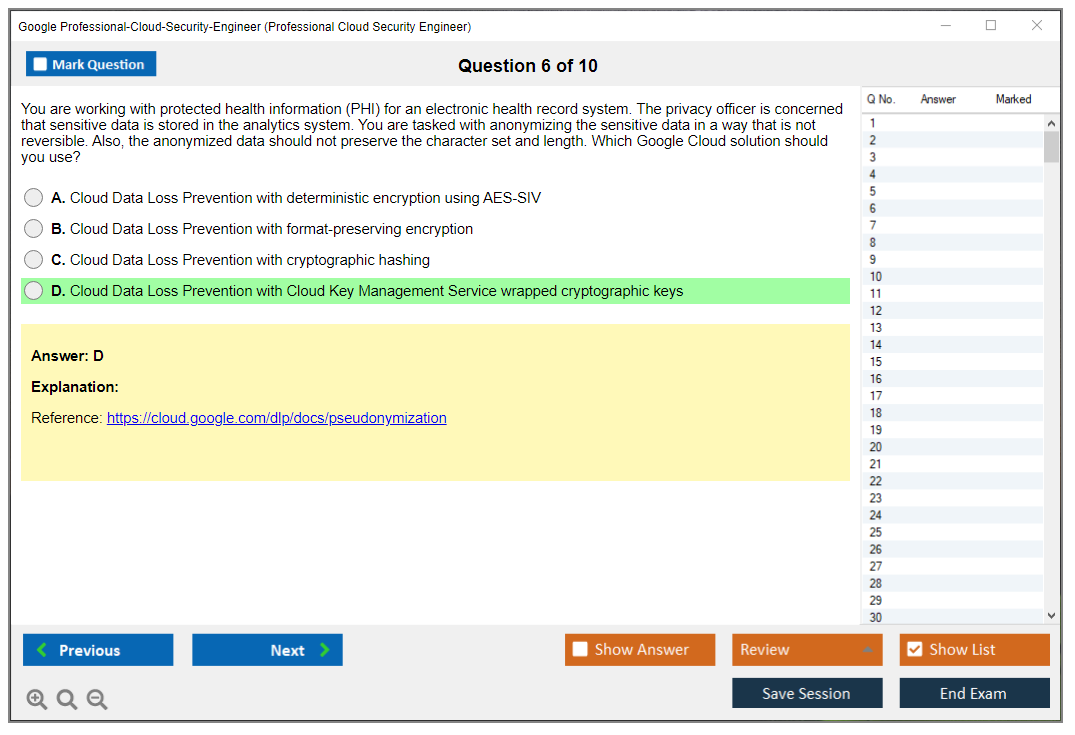
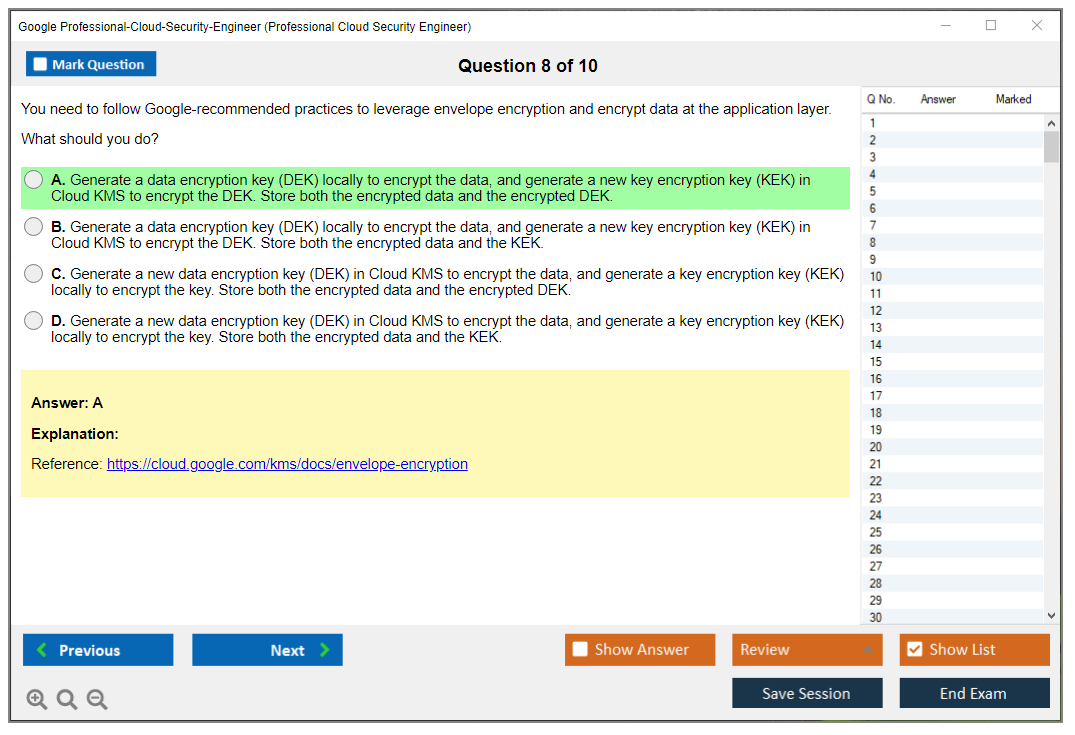
3. Data Protection: This topic covers data protection techniques, including data encryption, data masking, and data loss prevention.
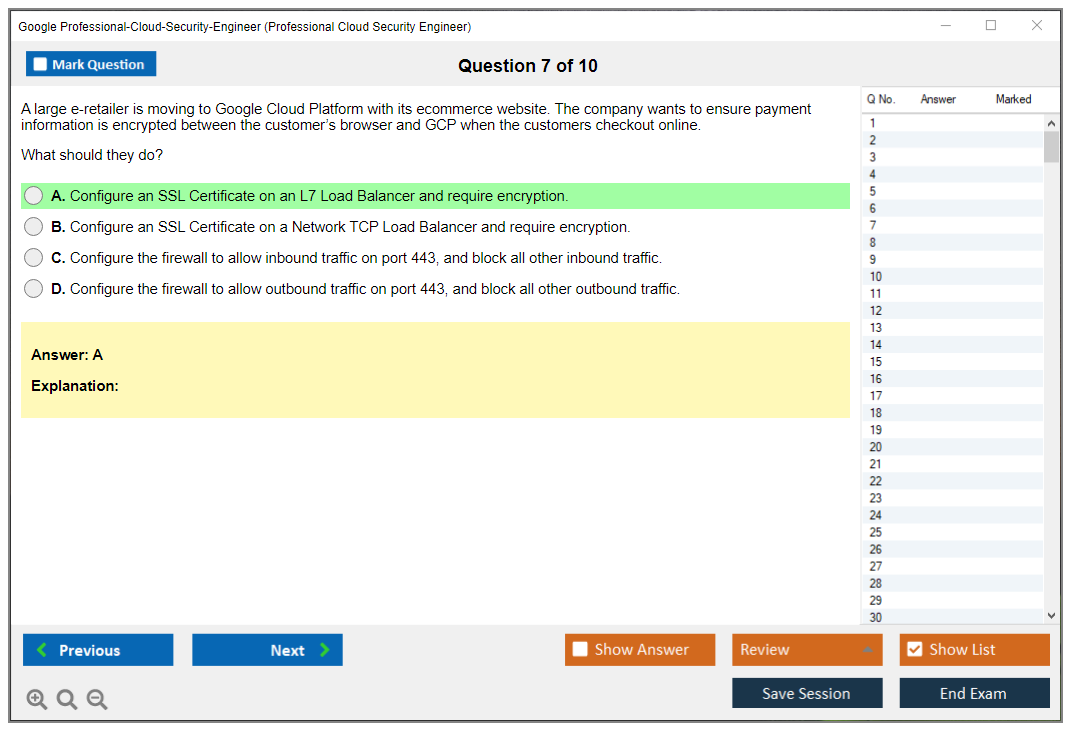
4. Network Security: This topic covers network security techniques, including network segmentation, firewalls, and virtual private networks.
5. Identity and Access Management: This topic covers identity and access management, including user authentication and authorization, identity federation, and access control lists.
6. Application Security: This topic covers application security, including secure coding practices, application security testing, and secure application deployment.
7. Incident Response
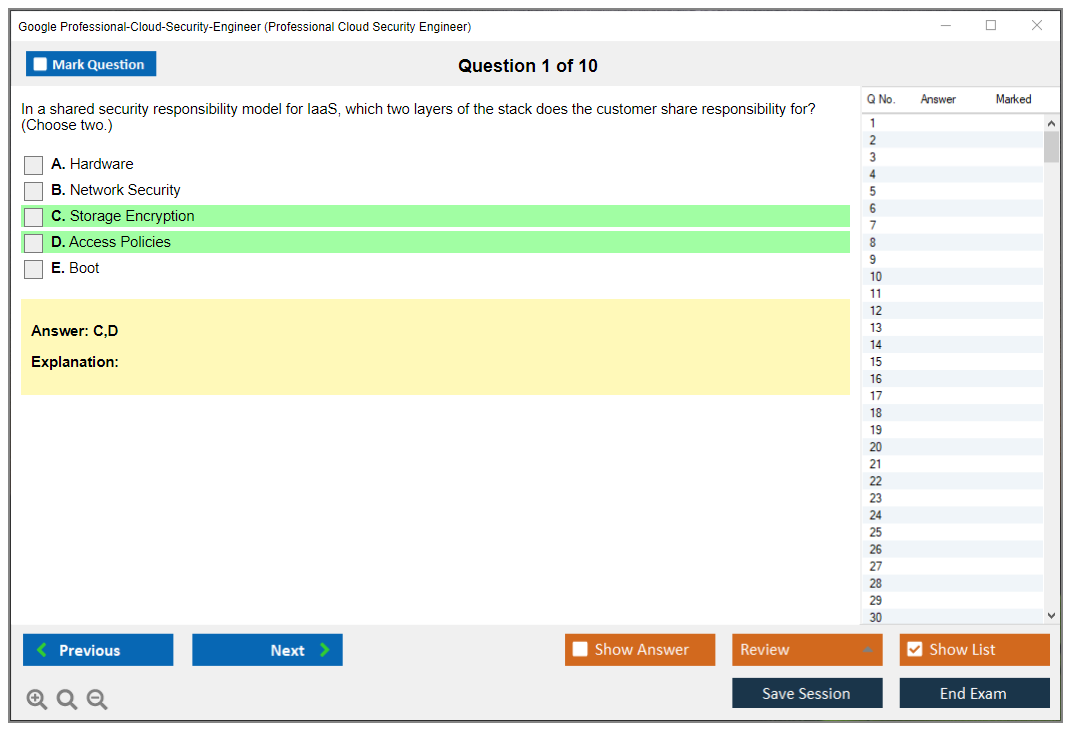
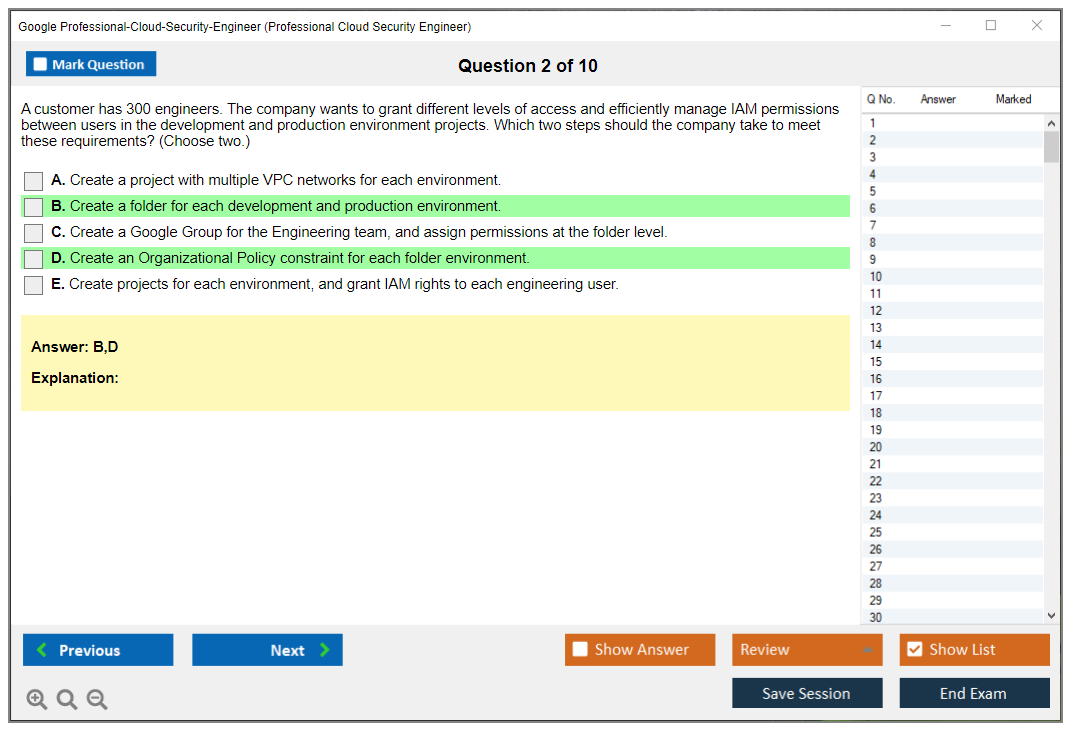
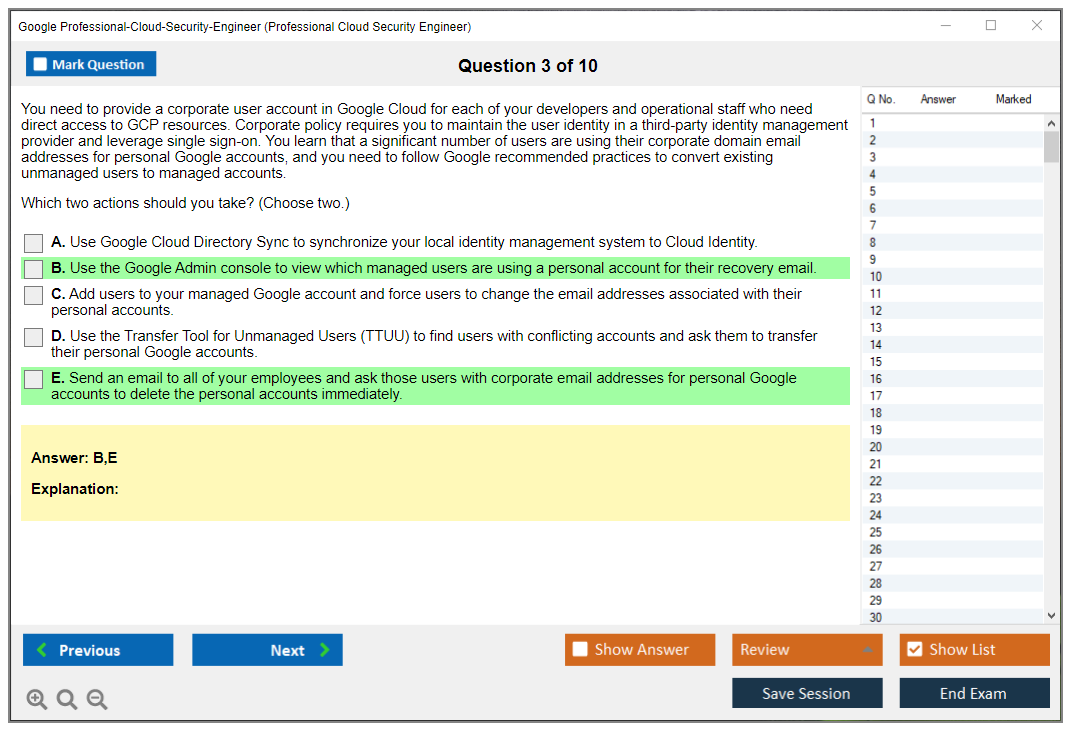
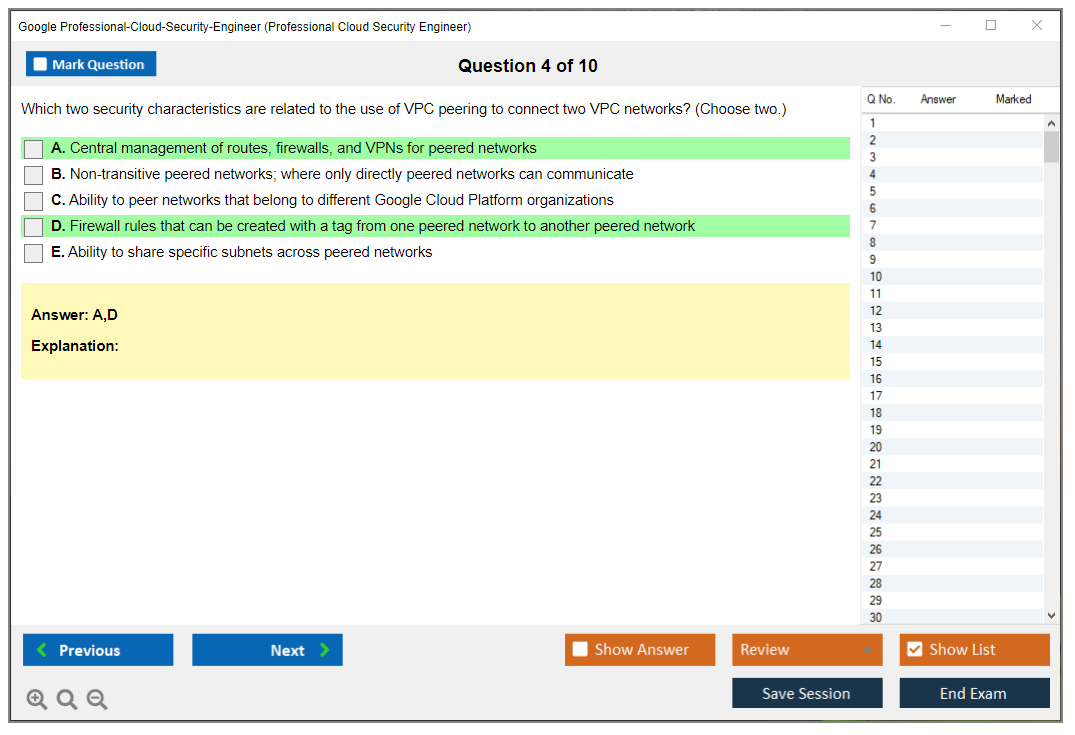
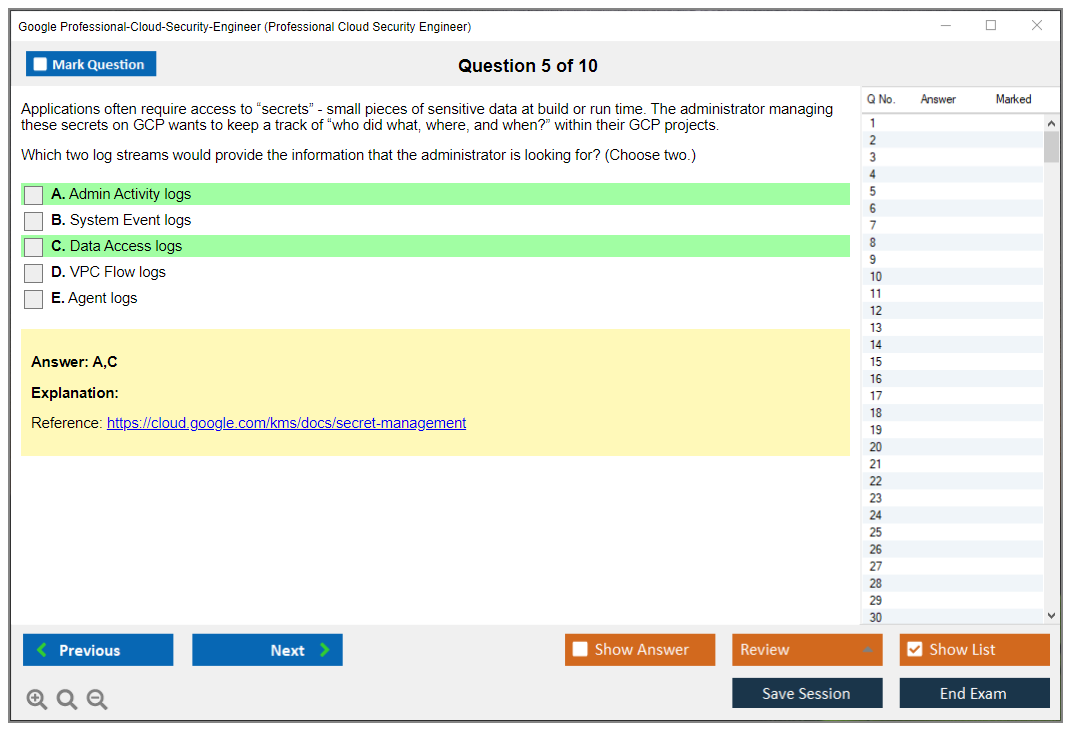
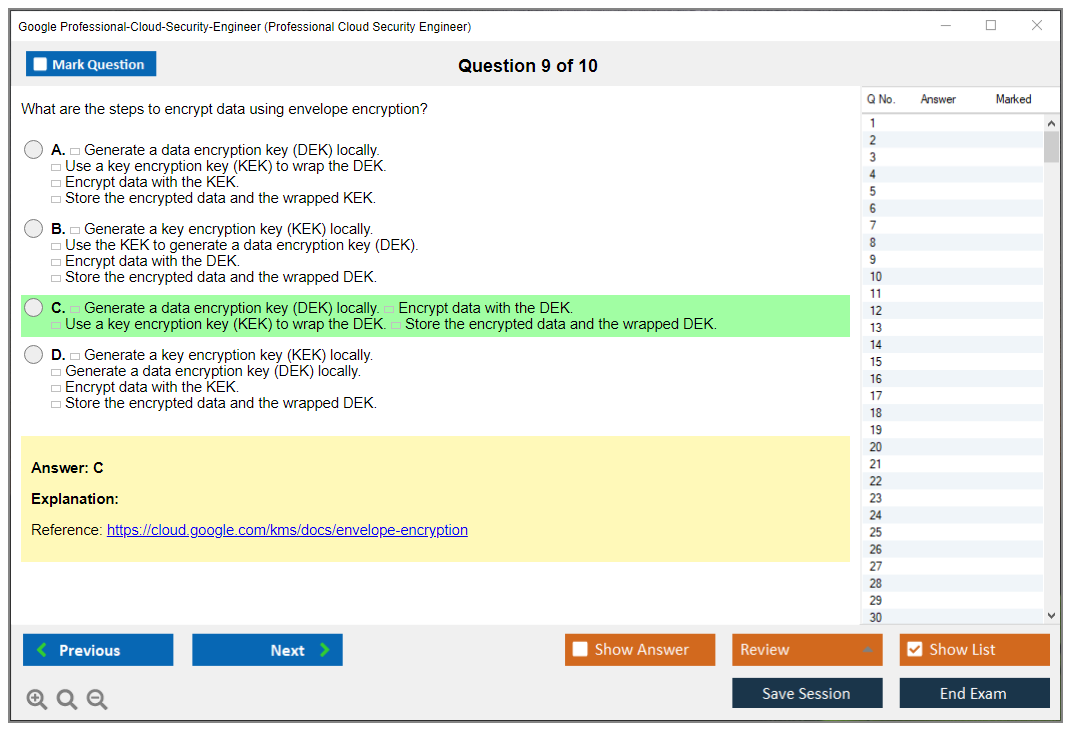
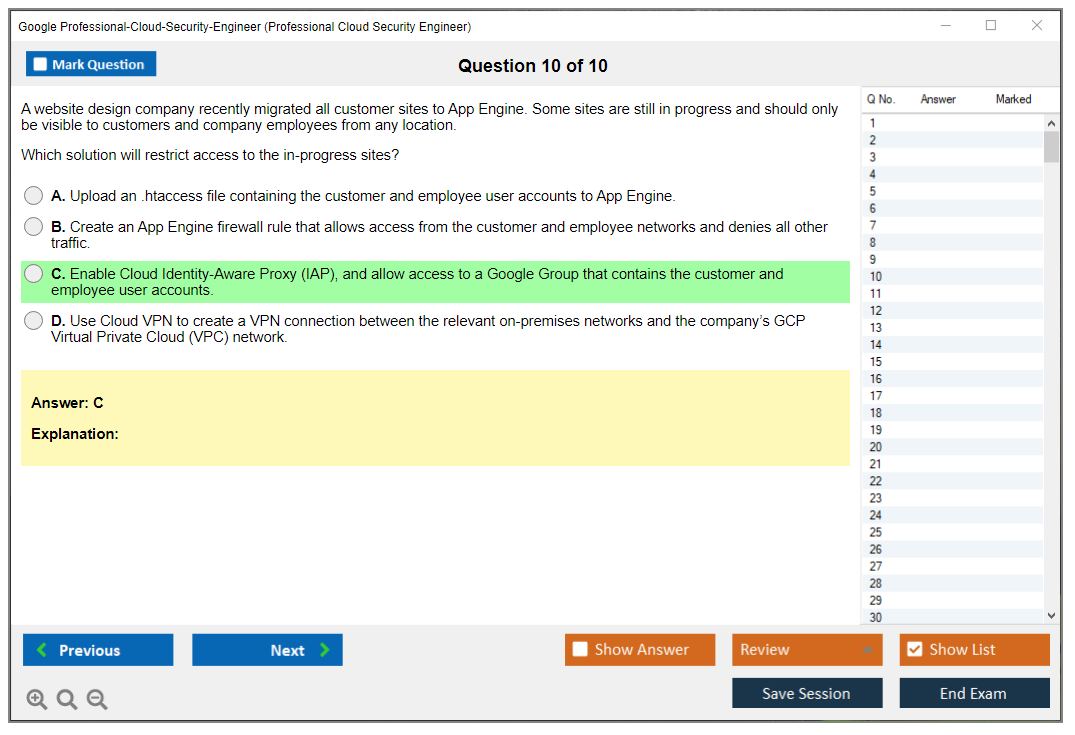
What are the Sample Questions of Google Professional-Cloud-Security-Engineer Exam?
1. What are the best practices for securely managing Google Cloud Platform resources?
2. How can you use Google Cloud Identity and Access Management (IAM) to secure your resources?
3. What methods can be used to secure data stored in Google Cloud Storage?
4. What are the security implications of running applications on Google Compute Engine?
5. How can you use Google Cloud Security Scanner to identify and fix security vulnerabilities?
6. How can you use Google Cloud Key Management Service to encrypt and manage cryptographic keys?
7. What are the advantages and disadvantages of using Google Cloud Security Operations Center?
8. How can you use Google Cloud Security Command Center to monitor and audit your cloud environment?
9. How can you use Google Cloud Security Health Analytics to detect and respond to security threats?
10. What are the best practices for implementing and managing secure access control in Google Cloud?
Google Professional-Cloud-Security-Engineer (Google Cloud Certified - Professional Cloud Security Engineer) Google Professional Cloud Security Engineer Certification Overview What is the Professional Cloud Security Engineer certification? The Google Professional Cloud Security Engineer certification is an advanced-level credential that validates your expertise in designing, implementing, and managing secure cloud infrastructure and applications on Google Cloud Platform. This is not some resume filler. It's Google essentially vouching that you can actually protect cloud workloads instead of just droning on about security in endless meetings that could have been emails. Anyone can spin up a VM in GCP, right? But securing that VM, plus the network it sits on, the data it processes, and the identities accessing it? That requires specialized knowledge most folks just do not have. This certification proves you understand both traditional security principles and how they translate to... Read More
Google Professional-Cloud-Security-Engineer (Google Cloud Certified - Professional Cloud Security Engineer)
Google Professional Cloud Security Engineer Certification Overview
What is the Professional Cloud Security Engineer certification?
The Google Professional Cloud Security Engineer certification is an advanced-level credential that validates your expertise in designing, implementing, and managing secure cloud infrastructure and applications on Google Cloud Platform. This is not some resume filler. It's Google essentially vouching that you can actually protect cloud workloads instead of just droning on about security in endless meetings that could have been emails.
Anyone can spin up a VM in GCP, right? But securing that VM, plus the network it sits on, the data it processes, and the identities accessing it? That requires specialized knowledge most folks just do not have. This certification proves you understand both traditional security principles and how they translate to cloud-native environments, which is honestly where a lot of security pros struggle. You're expected to know IAM architecture inside out, design network security that actually works (not just looks good in PowerPoint), implement data protection strategies that will satisfy auditors, and manage security operations at scale.
The real value? It combines vendor-neutral security concepts with GCP-specific tooling knowledge. You will work with Security Command Center, Cloud Armor, VPC Service Controls, and dozens of other services that traditional security pros have never touched. That's what makes this cert so valuable to enterprises migrating to or operating multi-cloud environments. You speak both languages fluently.
Who should take this exam?
Security engineers with cloud experience. Cloud architects who have realized security cannot be an afterthought. DevSecOps professionals needing to prove they understand GCP's security model. Compliance officers transitioning from checkbox auditing to actually implementing controls. IT security managers who need to speak credibly about cloud security to their teams.
Google recommends three or more years of industry experience and at least one year working specifically with GCP security, which is spot-on. I have seen people with less experience pass the exam, but they absolutely struggled. It showed when they tried applying the knowledge afterward because passing a test is not the same as understanding the material in ways that matter when production's on fire.
The exam assumes you have actually configured IAM policies that did not lock everyone out (we have all been there), designed VPC networks that balanced security and functionality, and responded to actual security incidents in production environments. Not simulated ones or lab exercises, but real incidents where executives start asking uncomfortable questions and your decisions have consequences.
Coming from the Associate Cloud Engineer track? This is a natural next step, but expect a significant difficulty jump. Working toward Professional Cloud Architect? This cert complements it beautifully since architecture and security overlap constantly in real projects.
Career outcomes and market positioning
The certification sits at the professional level alongside other role-based Google Cloud certifications, but it requires deeper security specialization than foundational certs. It shows up in over 40% of cloud security job postings, often as a required or preferred qualification for senior security roles at Fortune 500 companies and cloud-native organizations.
Average salary increase post-certification? Somewhere between 15% and 25% according to most surveys, though your mileage may vary. More importantly, it differentiates you in competitive job markets. Every cloud engineer can deploy resources. Far fewer can design zero-trust architectures, implement defense-in-depth strategies properly, or automate security controls that actually catch threats before they become breaches. That's what companies desperately need.
What makes this different from other security certs
The Professional Cloud Security Engineer certification focuses on cloud-native security rather than traditional infrastructure protection. Hold CISSP or CCSP? You know security principles. Great. This cert tests whether you can implement those principles using GCP-specific services, which is a completely different ballgame. Can you configure Cloud KMS for proper key rotation? Design VPC Service Controls that prevent data exfiltration? Use Cloud Logging and Cloud Monitoring for security event correlation? Configure Security Command Center to actually alert on meaningful threats rather than noise?
This addresses a genuine skills gap in the market. Tons of professionals understand traditional security. Tons understand cloud deployment. Very few understand both well enough to secure cloud environments properly, and that gap keeps companies up at night. That's the bridge this certification helps you cross.
Professional development pathway and longevity
Many candidates pursue this after Associate Cloud Engineer or alongside Professional Cloud Architect. It's complementary to CISSP, CCSP, or AWS security certifications, not a replacement. Working in multi-cloud environments (and who is not these days)? Having both GCP and AWS security certs makes you significantly more valuable.
Two-year validity period. Some people complain about recertification requirements, but it makes sense. Cloud security evolves rapidly. New services launch. Attack vectors change. Compliance requirements shift. A two-year validity period keeps you current and demonstrates ongoing professional development commitment rather than one-and-done credential collecting, which employers see right through anyway.
Real-world application
What you will actually do with this knowledge: design zero-trust architectures that assume breach, implement defense-in-depth strategies across multiple security layers, automate security controls so humans are not the weak link, respond to cloud security incidents effectively, and ensure regulatory compliance across frameworks like HIPAA, PCI-DSS, and GDPR.
You will work with Google Cloud IAM for identity and access management, configure network security using VPC design and firewall rules, implement encryption using Cloud KMS, manage security operations through logging and monitoring, and ensure compliance through governance controls. These are not theoretical exercises or academic thought experiments. They're daily responsibilities for cloud security professionals actually doing the work.
The exam validates competencies that employers actually need, which is why it maintains strong industry recognition even as cloud security certifications proliferate. Not all certs are created equal (some are honestly just money grabs), but this one consistently shows up in job requirements for senior security roles.
Exam Details: Format, Cost, and Registration
Exam details: format, cost, and registration
Money first. Honestly that's what everyone asks when they're deciding if the Google Professional Cloud Security Engineer certification is happening this month or gets punted to "someday." As of 2026, the Professional Cloud Security Engineer exam cost is $200 USD for the registration fee, and that's pretty consistent across most markets. Some countries have regional pricing variations, so don't freak out if your checkout page looks a little different. Still. Plan for $200.
Taxes can absolutely sneak up on you, which.. I mean, nobody thinks about until checkout, but VAT or sales tax may get tacked on depending on where you're registering from, and it's calculated at checkout before you confirm payment so you'll see the final total before clicking that last button. Budget a little extra if you're in a VAT-heavy region. Annoying? Yes. Normal? Also yes.
Payment's straightforward. You can pay with major credit cards like Visa, MasterCard, and American Express, and PayPal's also accepted. If your employer's sponsoring you, organizational purchase orders are an option too, which is honestly nice for enterprise teams that don't want you expensing it on a personal card and then chasing reimbursement for two months while finance "investigates."
Rescheduling's where people get absolutely burned. Free rescheduling's available up to 72 hours before your scheduled exam time, which is generous if you treat it like an actual deadline. Miss that window and late reschedules are basically a full fee forfeiture, meaning you're paying again because you forgot to move it before the cutoff. Put a calendar reminder two days before the 72-hour mark. Just do it.
Cancellation terms're a bit more forgiving if you act early. Cancel 14 days or more before your exam date and you get a full refund. Cancel in the 7 to 14 day window and you're looking at a partial refund of 50%. Inside a week? Assume you're eating the cost. Look, life happens, but the policy's the policy.
Now the actual exam format. You get a 2-hour testing window, 120 minutes total, and there aren't any scheduled breaks included in that time. So if you need a bathroom break, that clock just keeps ticking. Drink water earlier. Eat before. Basic stuff, but people ignore it and then wonder why they rushed the last 10 questions while their bladder's staging a rebellion.
Question count's typically 50 to 60, and it's multiple choice and multiple select. The vibe's very "scenario first, answer second." Expect prompts that read like mini incident reports, architecture reviews, or compliance requirements, and then you've gotta pick the best control or configuration. Some scenarios reference diagrams or security configurations, which is why your study can't just be flashcards and hoping. If you're reviewing Professional Cloud Security Engineer exam objectives, keep asking yourself, "What would I actually set in GCP?" This matters for Google Cloud IAM security best practices, org policies, and service account usage.
Delivery options come down to remote proctoring or test center. Remote proctored exams run through the Kryterion platform, and you can take it from home or the office. In-person testing's available at authorized Kryterion test centers globally.
Remote proctoring's convenient. But you need your setup clean. Stable internet's required, minimum 1 Mbps upload and download, plus a webcam and microphone. You'll also need a government-issued photo ID, and you must be in a quiet private testing space. No roommates wandering through. No second monitor. No "my dog's chill." The proctor's paid to be suspicious, and you don't wanna argue with someone on webcam while your timer runs.
Test centers're underrated. Controlled environment. Dedicated testing computers. Quick technical support if something weird happens. Reduced connectivity risks, which, not gonna lie, is the whole game if your home internet occasionally decides to reinvent itself. The thing is, if you're the type who gets stressed by setup checklists, the test center's probably the better bet.
My cousin actually failed his first attempt not because he didn't know the material but because his wifi dropped halfway through and he spent 15 minutes trying to reconnect while panicking. The proctor couldn't do anything. By the time he got back in, he'd lost his focus and bombed the last section. He passed on the second try at a test center.
Registration isn't hard, but you do need to follow the steps. Create a Webassessor account, select the Professional Cloud Security Engineer exam, choose delivery method and date, complete payment, and then you'll get a confirmation email. That email matters. Save it. Screenshot it. Whatever. You'll want the appointment details handy on exam day.
Scheduling availability's usually decent. Test center appointments're commonly available within 1 to 2 weeks, depending on your city and season. Remote proctored slots often show up within 24 to 48 hours, which is great when you've been grinding Professional Cloud Security Engineer study materials and you hit that moment of "I'm ready, let's go."
Language options're another practical detail people miss. The exam's offered in English, Japanese, Spanish, and Portuguese, and you select the language during registration. Pick what you can read fastest under pressure, not what you "should" use.
ID rules're strict. You need a government-issued photo ID with a signature, and the name on your ID must exactly match your registration name. Exactly. If your account says "Mike" and your ID says "Michael," fix it before exam day. A secondary ID may be requested, so having a backup in your wallet's smart.
Prohibited items're basically everything you'd want when you're nervous. Mobile phones, smartwatches, notes, books, random electronics, food, beverages. Medical necessities can be exceptions, but get prior approval. Don't try to negotiate this live with a proctor. It's a losing game.
Accessibility accommodations exist. And they're worth requesting if you need them. Things like extra time, screen readers, and separate testing rooms're typically available, but you have to submit a formal accommodation request 10 or more days before the exam. Paperwork. Waiting. Plan ahead.
Results're fast at first, then slower. You get a preliminary pass/fail notification right when you finish. The official score report comes via email within 7 to 10 business days. Also, if you pass, the Credly digital badge's usually issued automatically 2 to 3 days later, and you can share it on LinkedIn, add it to your email signature, or drop it into your professional profiles. It's a small thing. Recruiters notice it anyway.
One last opinion. If your prep's included a Google Cloud Security Engineer practice test or two, plus real hands-on work with Security Command Center configuration, Google Cloud KMS and encryption, and cloud logging monitoring and incident response on GCP, the exam day logistics become the easy part. But if you ignore logistics? You can fail a good day before it even starts.
Passing Score and Scoring Explained
Is there an official passing score?
Google doesn't publish passing scores. Period.
Most major certification providers keep these thresholds confidential, and honestly it makes sense from their perspective, though I get why candidates find it frustrating when they're trying to gauge whether they're ready. The thing is they adjust the passing threshold per exam version to maintain consistent standards, which means the exact number you need can vary slightly depending on which questions you get.
What we do know from candidate reports and industry chatter is that the exam uses a scaled scoring system ranging from 200 to 1000 points. The passing threshold typically falls somewhere between 700 and 750 based on what people share after taking the test. I mean, these're educated guesses from the community rather than official numbers, but they're pretty consistent across multiple sources.
The scaled scoring approach serves a real purpose beyond just being mysterious. It ensures fairness across different exam versions since not every version has identical difficulty levels. Some question sets might be slightly harder than others, and psychometric scaling accounts for these variations so candidates aren't penalized just because they happened to get a tougher version of the test. Whether this actually makes things fairer or just adds another layer of confusion is debatable, but at least there's some logic behind it.
How the exam is scored (what candidates should know)
Not all questions carry equal weight.
That's important to understand. Performance gets measured against standards rather than a simple percentage of correct answers, which means you can't just count up the questions you think you nailed and calculate your score. The more involved scenario questions about implementing VPC Service Controls or configuring Security Command Center carry greater weight than straightforward recall questions about basic IAM concepts. This weighting makes sense because the certification aims to validate professional-level skills, not just memorization ability, though honestly some memorization's still required.
Your score report won't show you a number anyway. Instead, you'll see performance levels across the five major exam domains, things like "high," "medium," or "low" for each section. Google does this to shift focus toward understanding your actual gaps rather than obsessing over point totals. If you pass, great, you demonstrated minimum acceptable ability for professional cloud security engineering roles. If you don't, you get specific domain feedback to guide your next study session, which's actually more valuable than a number would be.
One policy that catches people off guard: no partial credit on multiple select questions. You need all correct answers selected to get any points for that question. Partially correct responses receive zero points, which's harsh but consistent with how Google evaluates readiness. Either you know how to properly configure something or you don't, there's no middle ground in production environments.
Look, the scoring timeline differs for beta exam versions too. If you take a beta (which isn't common for this mature certification but happens when major content updates roll out), expect to wait 4-6 weeks for results. Google uses beta attempts to establish baseline performance benchmarks before the exam goes live to regular candidates, so your score calculation happens after they've analyzed the full beta cohort's performance.
What you won't get is numerical score comparison with other candidates. Employers receive only pass/fail status when they verify your certification through Credly or your candidate profile. This maintains focus on certification achievement rather than turning it into a competition about who scored highest, which honestly would be pointless anyway given the scaled scoring approach.
What to do if you don't pass (retake strategy)
Immediate retakes aren't permitted.
You've gotta wait 14 days before your second attempt, and if that fails too, later attempts require a 60-day waiting period between tries. This cooling-off period actually helps because cramming the same material immediately rarely fixes fundamental knowledge gaps, even though it feels like the natural response when you're frustrated about failing.
Use the domain performance feedback wisely. If your score report shows "low" performance in data protection but "high" in network security, you know exactly where to focus. Complete additional hands-on labs around Cloud KMS, customer-managed encryption keys, key rotation policies, and data classification approaches. The Professional Cloud Network Engineer certification covers some overlapping networking concepts if you need deeper foundation work there.
Review your approach to scenario questions particularly. Many people fail not because they lack knowledge but because they struggle with the multi-step decision-making process these questions require. Practice identifying security requirements, weighing trade-offs between different GCP security services, and selecting solutions that balance security with operational efficiency and compliance requirements.
Budget for multiple attempts if needed. Each retake costs the full $200 exam fee with no discount, so three attempts would run you $600 total. Not gonna lie, that adds up quickly, which makes thorough preparation before your first attempt the most cost-effective move, though I've got mixed feelings about whether the cooling-off periods're long enough or too restrictive.
There's no formal score appeal process available either. Google's scoring decisions're final, which can be frustrating if you felt you performed better than your result indicates, but the psychometric scaling process is designed to be objective and consistent across all candidates.
Industry estimates suggest 60-70% of properly prepared candidates with the recommended experience pass on their first attempt. "Properly prepared" means 3+ years of hands-on security work on GCP and dedicated study time covering all five exam domains. If you're coming from AWS or Azure security roles, consider starting with the Associate Cloud Engineer certification to build GCP-specific foundations before tackling the professional security exam.
Difficulty: How Hard Is the Professional Cloud Security Engineer Exam
Google Professional Cloud Security Engineer Certification Overview
What is the Professional Cloud Security Engineer certification?
The Google Professional Cloud Security Engineer certification is Google's pro-level badge for folks who can actually design and run security on GCP, not just talk about it. Advanced stuff, honestly.
It maps to how Google expects you to secure identities, networks, data, and operations across projects and orgs, while staying audit-friendly. Look, it's closer to "security architect who can still configure things" than "SOC analyst who read a doc once."
Who should take this exam? (roles and experience fit)
Cloud security engineers. Platform engineers who own IAM and VPCs. Security architects working in GCP day to day.
If you're mostly AWS or Azure, you can still pass, but not gonna lie, the mental model shift hurts. Especially around org hierarchy, policy evaluation, and how Google thinks about perimeter and service-to-service access. Expect friction. Little gotchas everywhere.
Benefits and career outcomes
Hiring managers like it 'cause it signals you can do GCP security without constant hand-holding. It also gives structure to the Professional Cloud Security Engineer exam objectives, which're basically a checklist of what you'll be asked to do at work anyway. More interviews. Better scope. Sometimes more money, depending on your market.
Exam Details: Format, Cost, and Registration
Exam cost (fees, taxes, rescheduling basics)
The Professional Cloud Security Engineer exam cost is typically $200 USD plus taxes, depending on where you test. Rescheduling rules vary by provider, and late changes can cost you, so read the fine print before you click stuff at 1 a.m.
Exam format (length, question types, delivery options)
Two hours. Mostly multiple choice and multiple select. Delivered at a test center or online proctoring, depending on availability.
Time's sneaky here. You get roughly 2 to 2.5 minutes per question, and some questions're tiny, while others're long, constraint-heavy scenarios that force you to reread because one word changes the whole answer. I mean, you'll see what I mean when you hit question 30 and realize you've got 90 left.
Exam policies (ID requirements, retakes, accommodations)
Bring matching ID. Follow the proctor rules. Retakes're allowed, but there're waiting periods, and you don't wanna burn attempts while "kinda ready." Accommodations exist if you need them, but plan early.
Passing Score and Scoring Explained
Is there an official passing score?
Google doesn't publish a fixed Professional Cloud Security Engineer passing score. So if you're hunting for "need 72% to pass," you won't find it.
How the exam is scored (what candidates should know)
You're scored on a scaled system. Some questions may weigh differently. And no, you don't get a neat domain-by-domain breakdown that tells you exactly where you face-planted. Annoying, but that's reality.
What to do if you don't pass (retake strategy)
Treat the score report like a compass, not a diagnosis. Go back to the Professional Cloud Security Engineer study materials, tighten the weak domains, and do targeted scenario practice. The thing is, also take a hard look at whether you lacked hands-on reps, because reading isn't the same as configuring.
Difficulty: How Hard Is the Professional Cloud Security Engineer Exam?
Difficulty factors (breadth vs depth, scenario questions)
Overall difficulty rating: advanced. Harder than Associate Cloud Engineer. Comparable to Professional Cloud Architect. That's the vibe.
The exam hits a lot of GCP security services, but it also expects depth in security architecture and implementation details. Which's where people get surprised, because you're not only naming the tool, you're choosing it under constraints like "must meet PCI-DSS, minimal operational overhead, hybrid connectivity, and the app team refuses to change code" all at the same time. Multi-layered scenarios. Lots of trade-offs. Some questions blend domains too, like IAM choices that quietly break your network segmentation plan or your audit story.
Distractors're also high quality. Wrong answers're often technically plausible, and a few're "fine" in the real world, just not the most Google-recommended approach for that particular scenario. Add occasional ambiguity where multiple answers feel defensible, and you're forced to pick "most appropriate" based on Google's best practices. Not your personal preference or what worked at your last job.
Side note: I've seen people spend 20 minutes on a single question arguing with themselves about policy inheritance edge cases, then rush the last 15 questions. Don't be that person. Flag it, move on, circle back if time permits.
Skills that make the exam easier (IAM, networking, logging, encryption)
IAM's the big one.
Nested policies. Org hierarchy. Service accounts. Workload Identity. Conditional IAM. If you can reason through Google Cloud IAM security best practices without guessing, the exam gets way calmer, honestly.
Network security's next. VPC Service Controls, Private Google Access, Cloud Armor, hybrid connectivity security, and the "where does this traffic actually flow" questions that make you draw diagrams in your head. Data protection matters too, especially Google Cloud KMS and encryption choices like CMEK vs customer-supplied keys, plus rotation strategy and operational risk. Then operations: Security Command Center configuration, Cloud Logging, Cloud Monitoring, and what "good" incident response looks like when the evidence lives across projects and sinks and maybe a SIEM you don't control.
Common reasons candidates fail (and how to avoid them)
Most failures I see come from thin hands-on time, over-reliance on docs, and shaky fundamentals in security principles like least privilege, segmentation, key lifecycle, and auditability.
Fix it by building small labs, breaking them, then repairing them while keeping compliance in mind. Practice beats highlighting PDFs. Every time, no exceptions.
If you want focused reps, I mean, a Google Cloud Security Engineer practice test helps, but only if you review why each wrong choice's wrong. The Professional-Cloud-Security-Engineer Practice Exam Questions Pack is one option people use to pressure-test their decision-making. Not just memorize answers like it's high school vocab.
Exam Objectives (Domains) You Must Master
Configure access within a cloud solution environment (IAM, org policies)
Org policies. IAM roles. Service account impersonation. Workload Identity Federation. Policy inheritance.
Configure network security (VPC design, firewall rules, segmentation)
Firewall rules aren't enough. You need segmentation patterns, service perimeters, and secure hybrid connectivity thinking.
Ensure data protection (encryption, KMS, secrets, key rotation)
CMEK vs Google-managed keys, who controls rotation, where keys live, and what happens during incident response when keys're compromised. Secrets Manager shows up too.
Manage operations in a cloud solution environment (logging, monitoring, IR)
Cloud logging monitoring and incident response on GCP's a whole domain. Sinks, retention, SCC findings, alerting, and response workflows.
Ensure compliance (auditability, governance, regulatory alignment)
Expect references to GDPR, HIPAA, PCI-DSS, SOC 2, and how GCP features support GCP security architecture and compliance. Not legal advice. Practical controls.
Prerequisites and Recommended Experience
Official prerequisites (what Google requires vs recommends)
No formal Professional Cloud Security Engineer prerequisites beyond agreeing to the rules and paying. Google recommends real experience though, and they're not kidding.
Recommended hands-on experience (GCP services and security tooling)
Two years of GCP security experience makes the difficulty feel moderate. Less than that, or mostly AWS/Azure, and it gets way harder because the defaults and patterns differ in ways that'll trip you up.
What to learn first if you're new to Google Cloud security
Learn IAM and org structure first. Then VPC basics. Then KMS and logging. After that, SCC and service perimeters.
Best Study Materials (Official and Third-Party)
Official Google Cloud learning paths and documentation
Start with the official learning path and the Professional Cloud Security Engineer exam guide plus the published Professional Cloud Security Engineer exam objectives. That's your map.
Hands-on labs and sandboxes (what to practice)
Build an org-like setup with folders, projects, and policies. Set up logging sinks. Try SCC. Configure KMS with CMEK on a resource and rotate keys.
Books, video courses, and notes (how to choose quality resources)
Pick resources that explain "when to choose what." If it's just feature tours, skip it.
Practice Tests and Exam Readiness
Where to find reliable practice tests
Be picky. Lots of junk out there. The Professional-Cloud-Security-Engineer Practice Exam Questions Pack is a paid option at $36.99, and it's most useful when you treat it like scenario training. Not trivia night.
How to use practice exams effectively (review method, error log)
Keep an error log. Write why you missed it. Note the service you misunderstood. Rebuild it in a lab if possible.
Practice scenarios aligned to objectives (IAM, SCC, KMS, logging)
Do scenarios that mix domains. IAM plus VPC SC. KMS plus logging and forensics. SCC findings plus response steps. That's the exam.
Study Plan (1 to 6 Weeks) Based on Your Experience
Fast-track plan for experienced cloud security engineers
1 to 2 weeks. Tight review of objectives, then hammer scenarios and weak spots with practice questions like the Professional-Cloud-Security-Engineer Practice Exam Questions Pack.
Standard plan for GCP practitioners transitioning to security
4 to 6 weeks. Expect 40 to 80 hours. Mix reading with labs every week.
Beginner plan (foundations first, then exam objectives)
Start with IAM and VPC foundations, then loop back to the objectives. Otherwise you'll memorize terms and still fail.
Renewal and Recertification
How long the certification is valid
The Google Professional Cloud Security Engineer certification is typically valid for two years.
Renewal requirements and process (recertification exam timing)
Professional Cloud Security Engineer renewal usually means retaking the current exam before expiration. No shortcuts.
Keeping skills current (what to track as GCP evolves)
Track IAM changes, SCC updates, and new org policy controls. GCP moves fast. Your notes should too.
FAQs
Cost, passing score, and difficulty (quick answers)
Cost: see above, typically $200 USD plus taxes. Passing score: not published. Difficulty: advanced, comparable to Pro Architect, and tougher than AWS Security Specialty for many people because of GCP's model.
Objectives and prerequisites (quick answers)
Objectives're public and matter. Prereqs aren't formal, but real experience is.
Best study materials and practice tests (quick answers)
Use official docs plus labs, then validate with a Google Cloud Security Engineer practice test that explains the why. Not just the letter.
Renewal timeline and retake rules (quick answers)
Renew about every two years by retesting. Retakes're allowed with waiting periods.
Exam Objectives: Domains You Must Master
What the exam actually covers
Here's the deal. The Professional Cloud Security Engineer exam splits into five domains, and weight distribution matters way more than people realize. You can't just coast through one section and pray.
Domain 1 absolutely dominates at 27% of the exam. That's your entire IAM universe packed in there with principals, resources, permissions, roles, and yeah, that whole hierarchy dance GCP makes you do. If you can't walk someone through the actual difference between a predefined role versus when you'd legitimately need to build a custom role (and I mean, least privilege isn't just corporate speak here), you're setting yourself up for pain. Service accounts matter massively here, but it's the creation part. You've got to really understand workload identity for GKE, key rotation strategies that won't obliterate production at 3am when you're asleep, plus service account impersonation patterns that enterprises actually use. Organization policies need special focus because that's how you enforce controls across your resource hierarchy. The inheritance mechanics get legitimately weird once you start overriding things at different levels.
Identity federation? Know it cold. Cloud Identity setup, SAML and OIDC integrations, workforce identity federation. These show up in scenario questions where they'll describe some enterprise setup and you've gotta architect the correct solution on the spot. Access context management with device security status and IP ranges gives you conditional access tools. Privileged access management with just-in-time access and approval workflows appears more frequently than candidates anticipate.
Network security domain breakdown
Domain 2 sits at 20%. Network security territory. VPC design questions test whether you actually understand isolation patterns, shared VPC architectures (which trip up tons of people who haven't worked in multi-project organizations, honestly), and when VPC peering creates security implications you didn't account for.
Firewall rules? They get complicated fast. Hierarchical firewall policies versus VPC firewall rules, priority ordering that makes actual sense, egress controls that don't destroy everything. I've seen practice scenarios where you're figuring out why traffic isn't flowing, and it's always some implicit deny or priority conflict hiding somewhere.
Private Google Access is critical for shrinking your attack surface. VMs without external IPs that still reach Google APIs, Private Service Connect for managed services. VPC Service Controls deserve serious study time because service perimeters and data exfiltration prevention are exactly what shows up in those "prevent unauthorized data movement" questions.
Cloud Armor for DDoS protection and WAF rules, load balancer security with SSL termination and IAP integration, hybrid connectivity through Cloud VPN and Interconnect. All fair game. The Professional-Cloud-Network-Engineer cert overlaps here if you're considering the broader networking picture, but this exam wants the security angle specifically.
Data protection fundamentals
Domain 3 also hits 20%. Encryption at rest isn't just "flip the switch." You need to understand default encryption, when you'd actually use customer-managed encryption keys in Cloud KMS, and those rare scenarios where customer-supplied encryption keys really make sense.
Cloud KMS architecture gets detailed. Key rings, keys, key versions, rotation policies. Regional versus multi-regional considerations. You're designing the key management strategy for entire organizations sometimes, which is.. a lot. Encryption in transit with TLS/SSL configuration and certificate management rounds this out.
Secret Manager's the modern approach to handling API keys and passwords, not hardcoding them like some 2015 Terraform config someone found on StackOverflow. The DLP API for data loss prevention covers inspection, custom infoTypes, de-identification techniques. Data classification frameworks and tagging strategies appear when you need to apply security controls based on sensitivity levels.
Database security controls for Cloud SQL, object storage security in Cloud Storage with bucket policies and signed URLs, Key Access Justifications for CMEK auditing. Oh, and data sovereignty questions will test whether you know how to ensure data stays in required geographic regions for compliance purposes. If you're prepping with the Professional-Cloud-Security-Engineer Practice Exam Questions Pack, these encryption scenarios are what you should drill repeatedly.
I once spent two hours debugging why a Cloud SQL instance wouldn't connect, only to realize I'd configured CMEK in the wrong region. That kind of mistake? The exam loves catching people on it.
Operations and monitoring
Domain 4 hits 20%. Operations territory. Cloud Logging configuration with log sinks, routing to Cloud Storage or BigQuery, exclusion filters, retention policies. This builds your forensics foundation. Short sentences here. Then longer ones that explain how Cloud Monitoring creates security-focused dashboards and alerting policies on security events.
Security Command Center is massive here. Standard versus Premium tiers, understanding security findings, threat detection capabilities, Event Threat Detection integration. Not gonna lie, SCC questions feel like half this domain. Vulnerability scanning with Web Security Scanner and Container Analysis, OS patch management monitoring.
Incident response procedures get tested through scenarios. Developing IR playbooks, using Cloud Logging for forensics, preserving evidence without contaminating it, containment strategies that don't worsen things. Automated remediation with Cloud Functions responding to Security Command Center notifications is what separates people who've actually built this from folks just reading docs.
Security Health Analytics for detecting misconfigurations, forensics and investigation techniques with disk snapshots and log analysis, integration with SIEM platforms for security operations teams.
Compliance domain essentials
Domain 5 rounds out at 13%. Regulatory frameworks like GDPR, HIPAA, PCI-DSS, SOC 2, ISO 27001. You need to know how GCP services support compliance requirements. Compliance Reports Manager, shared responsibility model documentation, security control evidence.
Resource labeling strategies for compliance tracking, policy as code with Config Connector or Terraform constraints, audit trail requirements for tamper-proof log storage. Data residency compliance with resource location configuration. Access Transparency logs to monitor Google support access, Access Approval for controlling that access.
If you've done the Professional-Cloud-Architect cert, some compliance concepts overlap, but this exam wants the security and audit angle specifically. Continuous compliance monitoring and automated compliance checking used to involve Forseti Security before it got deprecated. Now it's mostly Security Command Center doing that heavy lifting.
The exam objectives are dense. But logical once you map them to real security architecture decisions.
Prerequisites and Recommended Experience
Official prerequisites (what Google requires vs recommends)
Google's pretty straightforward here: there aren't any mandatory Professional Cloud Security Engineer prerequisites to register for the exam. No gatekeeping whatsoever. No "must already hold X cert" checkbox situation. You pay the Professional Cloud Security Engineer exam cost, schedule it, show up.
That said. Recommendations do exist. Google suggests coming in with relevant experience, and they hint that prior Google Cloud certifications can help, though nothing's actually required. The thing is, this matters because people read "professional" and automatically assume there's some formal ladder you've gotta climb first, when really the exam itself is what filters people out.
Look, the gap between "allowed to take it" and "ready to pass it" is massive. The Google Professional Cloud Security Engineer certification expects you to think like someone who's responsible for production security decisions, not someone who just wrapped up a beginner cloud course and can click around the console a bit.
One more thing people get confused about: there's no official checklist from Google saying "you must have done KMS key rotation for six months." Instead, the exam tests whether you can pick the right approach in messy scenarios, which is why your background matters way more than any formal prerequisite.
Recommended hands-on experience (GCP services and security tooling)
If you want a realistic bar, plan on 3+ years in information security, IT operations, or cloud architecture roles where security's part of the actual job, not some side quest you do on Fridays. I'm talking about time spent making calls under pressure. Deciding whether to block a suspicious service account. How to segment a network without breaking apps. Or responding when logs show weird access patterns but the product team insists "it's probably fine."
One year of hands-on GCP security work is the other big recommendation, and honestly, it's a real one. Reading Professional Cloud Security Engineer study materials helps, sure, but you need the muscle memory of building and defending systems on Google Cloud, not just theory. You should be comfortable with org structure, projects, folders, policies, and you should know how Google Cloud IAM security best practices actually play out when teams want speed, auditors want proof, and you're trying to maintain least privilege.
IAM is the exam's constant background noise. Authentication versus authorization should be automatic in your head. Same for RBAC ideas, but translated into Google Cloud's model: primitive roles versus predefined roles versus custom roles, service accounts, workload identity, how IAM policies inherit down the resource hierarchy. If you've never had to untangle "why does this service account have Editor on the project," you're gonna feel serious pain on scenario questions.
Networking shows up everywhere too. TCP/IP, DNS, VPN concepts, subnetting, routing, firewall rules, load balancing, segmentation strategies, all assumed knowledge. Not as trivia, though. As design constraints. You need to read a scenario and understand why a private Google access setting, a route, or a firewall target tag changes the blast radius, and why "just open 0.0.0.0/0 for testing" is how breaches become postmortems.
Security ops matters too.
Logging. Monitoring. Incident response. Vulnerability management. SOC workflows. A lot of candidates underestimate this because they think the cert's only about architecture, but the exam loves operational reality, like how you'd set up alerting, what you'd investigate first, how you'd make your environment audit-friendly. You should be comfortable with cloud logging monitoring and incident response on GCP, including what goes into Cloud Logging, how to query it, how to make it useful during an actual incident.
On the GCP tooling side, you'll want real exposure to Security Command Center configuration, at least enough to understand findings, sources, how it fits into triage workflows. Add Google Cloud KMS and encryption knowledge: CMEK compared to Google-managed keys, envelope encryption concepts, key rotation expectations, when Secret Manager's the right answer instead of "store it in an environment variable and pray."
Compliance is the last "soft prerequisite" that isn't soft at all when you're on the hook. You don't need to be a lawyer or anything. You do need familiarity with GDPR, HIPAA, PCI-DSS basics, how audits work in practice, because GCP security architecture and compliance is a real theme, and the exam expects you to care about evidence, controls, governance, not just cool tech.
By the way, I once watched a talented developer with zero compliance background completely bomb a mock scenario about data residency requirements because he kept trying to solve it with clever automation when the answer was just "pick the right region and document it properly." Sometimes the boring answer is the correct one, which drives a lot of people nuts.
What to learn first if you're new to Google Cloud security
Start with foundations, because without them you'll memorize an exam guide and still miss the questions. Cloud computing concepts. Shared responsibility. Multi-tenancy. Threat models. The CIA triad and defense-in-depth should be reflexes, not vocabulary words. Master them. Then apply them everywhere.
Next, get your IAM house in order. Build a small org-like setup in a lab project, create service accounts, assign roles, break access, fix it, watch inheritance unfold. It's boring, I mean, really boring. Do it anyway. A lot of the Professional Cloud Security Engineer exam objectives revolve around "who can do what, where, and why," and that's IAM plus org policy plus resource hierarchy, with a side of "don't accidentally let a developer impersonate prod."
After that, do networking and logging together, because they connect in ways you won't see coming. Stand up a VPC, subnets, routes, firewall rules, maybe a Cloud VPN conceptually, then generate traffic and watch what you can and can't see in logs. Add segmentation. Test assumptions. Not gonna lie, this is where people who only ever worked behind a corporate network team get exposed, because cloud networking makes you own design decisions you used to outsource to someone three teams over.
Finally, do data protection and ops. Encrypt something with KMS. Rotate a key. Use Secret Manager. Turn on SCC in a project and interpret findings. Create basic alerting tied to audit logs. If you can do those things and explain your reasoning out loud, you're in the zone where a Professional Cloud Security Engineer exam guide actually makes sense, and a Google Cloud Security Engineer practice test becomes a diagnostic tool instead of a confidence destroyer.
Quick reality check: people ask about the Professional Cloud Security Engineer passing score, but Google doesn't publish a fixed number, so chasing some magic percentage is wasted energy. People also ask about Professional Cloud Security Engineer renewal, and yes, it expires on a schedule, so plan for recertification later. For now, focus on being the person the exam's written for: someone who can make secure choices under constraints, with hands-on familiarity, not just good notes or flashcard mastery.
Conclusion
Ready to lock down your cert?
Look, you've read through everything. The exam domains, the prerequisites, the study materials. You know what Google Cloud IAM security best practices look like, you understand GCP security architecture and compliance frameworks, and you've probably already played around with Google Cloud KMS and encryption settings. But here's the thing: knowing the material and passing the Professional Cloud Security Engineer exam are two different animals.
Won't sugarcoat it.
This certification isn't easy. The scenario-based questions will test whether you actually understand Security Command Center configuration or if you just memorized some bullet points. There's a massive difference between regurgitating facts and actually troubleshooting a misconfigured service perimeter in real-time under pressure. You'll need to demonstrate real knowledge of cloud logging monitoring and incident response on GCP, not just surface-level familiarity. The exam objectives span five massive domains, and each one demands hands-on experience plus theoretical understanding.
That said? It's doable if you prepare smart.
Your study plan needs three components. First, hands-on labs where you actually configure network security policies, manage encryption keys, and set up monitoring workflows. Second, quality study materials that align with current exam objectives (not outdated stuff from 2020). Third, and honestly this is where most people stumble, you need realistic practice questions that mirror the exam's complexity and format.
The exam cost runs around $200. Not pocket change. And with no official passing score published, you can't afford to walk in unprepared hoping for the best. You get your results immediately, but you don't want to be scheduling a retake and dropping another $200 because you skipped the practice test phase. The Professional Cloud Security Engineer certification renewal comes every two years, so you're making a commitment here.
I bombed a different cert once because I thought watching videos would be enough. Spent three weeks just passively consuming content, barely touched the console. Failed by what felt like a mile. Sometimes you need to actually break things and fix them to understand how they work.
Here's what I recommend for your final prep stage: grab the Professional Cloud Security Engineer Practice Exam Questions Pack. These aren't basic recall questions. They're scenario-driven problems that test your ability to apply security controls across real-world GCP environments. You'll see questions on IAM policy troubleshooting, VPC Service Controls implementation, and compliance audit preparation that actually reflect what Google throws at you.
Work through them multiple times. Review your wrong answers obsessively. Your mistakes reveal exactly where your understanding breaks down, which is way more valuable than the stuff you already know cold. Use them to spot gaps in your knowledge about specific services or security patterns.
You've got this. The demand for cloud security skills keeps climbing, and this certification proves you can actually secure production GCP environments, not just talk about it. Go schedule that exam.
Show less info
Hot Exams
Related Exams
G Suite Certification
Looker Business AnalystExam
Google Certified Professional - Cloud Developer
Google Professional Machine Learning Engineer
Google Analytics Individual Qualification (IQ)
Google Cloud Certified - Professional Cloud Network Engineer
Google Cloud Certified - Associate Cloud Engineer
Google AdWords Fundamentals
Google Certified Professional - Cloud Architect (GCP)
Looker LookML Developer Exam
Google Developers Certification - Associate Android Developer (Kotlin and Java Exam)
Google LookML Developer
Google Cloud Certified - Professional Cloud Security Engineer
Google Professional Data Engineer Exam
Google Cloud CertifiedGenerative AI Leader Exam
Google Cloud - Apigee Certified API Engineer
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.