Google Professional-Cloud-Network-Engineer (Google Cloud Certified - Professional Cloud Network Engineer)
Google Professional Cloud Network Engineer Certification Overview
Okay, look. Full transparency?
When I first heard about the Google Professional Cloud Network Engineer certification, I thought "great, another cloud cert to add to the pile." But here's the thing: after seeing what this actually validates and the doors it opens, I changed my tune pretty fast. This isn't your typical checkbox certification.
The Google Professional Cloud Network Engineer certification is Google's way of saying "this person actually knows how to design, implement, and manage network architectures on GCP that won't fall over when traffic spikes or security threats show up." We're talking advanced stuff here. Not just clicking through console wizards, but actually understanding how to build secure, scalable networks that real companies depend on. I mean, if you're running production workloads on Google Cloud, you need someone who knows the difference between a good VPC design and one that'll cause headaches six months down the road.
Who this certification is actually for
This exam targets network engineers, cloud architects, DevOps professionals, and infrastructure specialists who already have their feet wet. Google recommends at least three years of industry experience and one year of hands-on Google Cloud networking work.
That's not gatekeeping. It's reality.
The scenarios they throw at you assume you've been in the trenches, you know? You've configured VPCs at 2 AM during some nightmare outage, troubleshot BGP routing issues that made absolutely no sense until suddenly they did, and you understand why someone would choose Cloud Interconnect over Cloud VPN (and when that choice matters financially, which honestly is what executives care about most).
If you're coming straight from the Associate Cloud Engineer cert, honestly? Take a breath first. Get some real-world GCP networking experience under your belt. The Professional level expects you to make architectural decisions, not just follow setup guides. I've seen plenty of folks rush into this and regret it big time.
Speaking of rushing, I once watched a colleague bomb this exam three times because he kept thinking he could memorize his way through it. Guy had every flashcard deck you could imagine. Zero production experience. Eventually he spent six months actually building networks before trying again, and guess what? Passed on the first attempt after that.
The career impact is real
Here's where it gets interesting. For your wallet and resume.
Organizations hiring for senior network engineer, cloud network architect, or infrastructure lead positions actively look for this certification. We're talking salaries in the $120,000 to $180,000 range annually, sometimes higher depending on location and company size.
Fortune 500 companies and cloud-native startups alike recognize this cert as proof you can handle enterprise-grade networking challenges. it's about knowing Google Cloud products. It's about demonstrating you can design networks that support business requirements like high availability, disaster recovery, compliance mandates, cost optimization, and global scalability. That's the stuff that keeps executives happy and systems running smoothly.
What you're actually proving you know
The certification validates a pretty full skill set across VPC design, hybrid connectivity solutions, network security implementation, load balancing configuration, network monitoring, and troubleshooting complex issues that would make junior engineers cry (been there). You need to know Virtual Private Cloud architecture inside and out. Understand when to use Cloud VPN versus Cloud Interconnect for hybrid connectivity. Configure Cloud Load Balancing for different use cases. Implement Cloud DNS and Cloud CDN properly. Secure networks with Cloud Armor and firewall rules. Use Network Intelligence Center to diagnose problems.
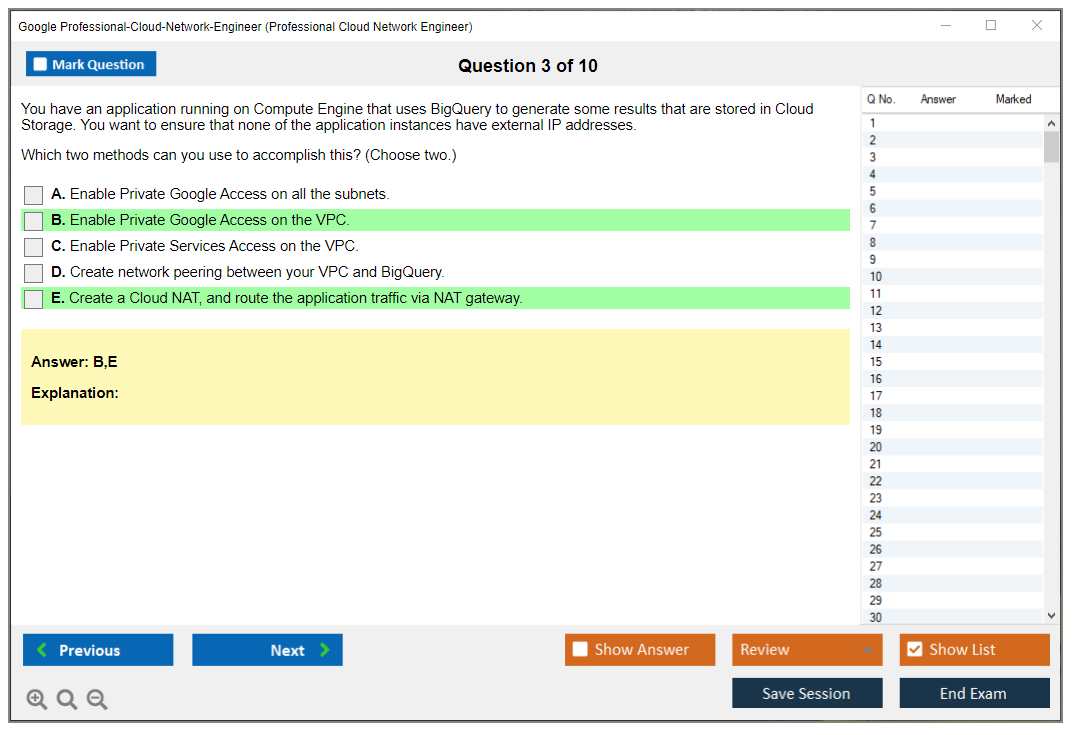
Technology-wise, you're covering VPCs (obviously), shared VPC configurations, Private Google Access, VPC peering, Cloud VPN, Dedicated Interconnect, Partner Interconnect, all the load balancing flavors. HTTP(S), TCP/UDP, internal, external. Cloud DNS, Cloud CDN, Cloud Armor, Cloud NAT, firewall rules, IAM for network resources, and third-party network virtual appliances.
It's a lot.
The exam expects you to know when to use each tool and, more importantly, why you'd choose one approach over another in specific business contexts.
How it differs from Associate-level stuff
People ask me this constantly.
The Associate Cloud Engineer certification covers foundational concepts. You're proving you can use Google Cloud services competently. The Professional Cloud Network Engineer exam cranks up the difficulty quite a bit. You need deeper architectural knowledge. The ability to analyze real-world scenarios with multiple valid approaches and pick the best one (which is way harder than it sounds). Multi-project networking strategies for enterprise organizations. Advanced troubleshooting capabilities that go way beyond "check the firewall rules."
The questions put weight on practical scenarios and architectural decisions. You'll see case studies about companies migrating to Google Cloud, needing hybrid connectivity between on-premises data centers and GCP, dealing with compliance requirements that affect network design, optimizing costs while maintaining performance, troubleshooting production issues under pressure. They're not asking you to memorize documentation. They want to see if you can think like a network architect who's been burned before and learned from it.
What you need to know before you start studying
Google assumes you understand the OSI model, TCP/IP protocols, routing and switching fundamentals, DNS, DHCP, BGP, network security principles, and basic Linux networking.
If those terms make you nervous, you're not ready yet. Seriously.
You'll also need familiarity with concepts like subnetting, CIDR notation, NAT, VPN protocols, load balancing algorithms, and network troubleshooting methods that go beyond just googling error messages.
The exam includes five major domains. Network design and planning. Implementing VPC networks. Configuring hybrid connectivity. Managing network services and traffic. Implementing network security plus monitoring. Each domain has multiple sub-topics that dig pretty deep. Network design asks you to plan architectures that meet business and technical requirements at the same time. Implementation tests your ability to configure VPCs, subnets, routes, and connectivity options without breaking existing infrastructure. The hybrid connectivity section digs into Cloud VPN, Cloud Interconnect, and integrating with on-premises infrastructure (which is where things get messy in the real world). Network services covers load balancing, Cloud DNS, Cloud CDN, and traffic management. Security and monitoring test your knowledge of firewalls, Cloud Armor, IAM, Private Google Access, VPC Service Controls, Cloud Logging, and Cloud Monitoring.
The certification path and what's next
Most people pursue this after getting their Associate Cloud Engineer certification, or they're experienced network professionals transitioning from traditional infrastructure to cloud. Some come from other cloud platforms and want to specialize in Google Cloud networking specifically. The certification positions you well for more specialized roles or broader architecture positions like the Professional Cloud Architect cert.
Google expects hands-on experience, not just reading documentation. You should have configured VPCs in production environments, implemented hybrid connectivity for actual business needs, troubleshot network issues that affected real users, and optimized network performance under cost constraints.
If you haven't done those things? Find ways to practice. Use Qwiklabs, build test environments, volunteer for networking projects at work. Whatever gets you actual experience.
The exam also touches on multi-cloud considerations. While it focuses on Google Cloud, scenarios include hybrid architectures connecting on-premises infrastructure and sometimes other cloud providers. Real enterprises don't exist in single-cloud bubbles, and Google knows that reality well.
This certification proves expertise that organizations actually need, not just theoretical knowledge. That's why it commands respect and higher compensation in the market.
Exam Details: Format, Cost, and Registration
Exam details: format, cost, and registration
Look, if you're gunning for the Google Professional Cloud Network Engineer certification, here's what happens: people skip this section entirely until they're like two days out, then suddenly they're freaking out about proctoring requirements and question formats and whether their webcam even works. Don't be that person. The logistics actually matter. Stress eats up cognitive bandwidth you need for thinking like a network engineer who's gotta make high-stakes architectural calls under pressure.
Budget it properly. Block real time. Choose your method.
Professional Cloud Network Engineer exam cost
The Professional Cloud Network Engineer exam cost sits at $200 USD globally, though honestly your actual total might shift depending on where you live, local tax situations, currency conversion rates. You know the drill. If your employer's covering it, fantastic, but I'd still eyeball that receipt because reimbursement departments have this uncanny ability to question literally anything that appears on expense reports.
Vouchers exist too. The thing is, hardly anyone uses them. You can grab exam vouchers through Google Cloud training partners, corporate training setups, occasional promotional events that'll drop discounts or sometimes even free attempts. Wait, here's something most people miss: if you're at a company with an actual certification program, ask about bulk purchasing because organizations can buy voucher bundles at reduced rates for employee groups. That option usually hides behind HR or Learning & Development bureaucracy, so you might need to bug the right contact twice before anyone responds.
Payment's straightforward. Mostly, anyway. Major cards accepted.
Visa, MasterCard, American Express all work through Kryterion's platform, and you'll pay when you schedule, not on test day itself.
Exam format (question types, length, delivery method)
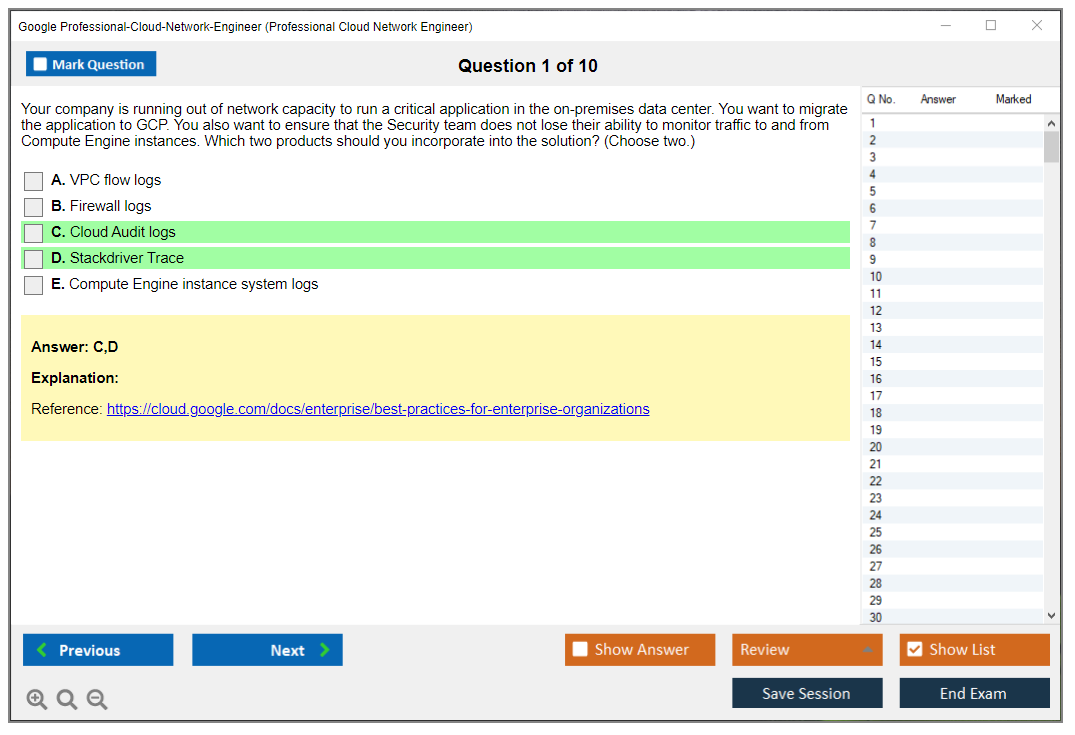
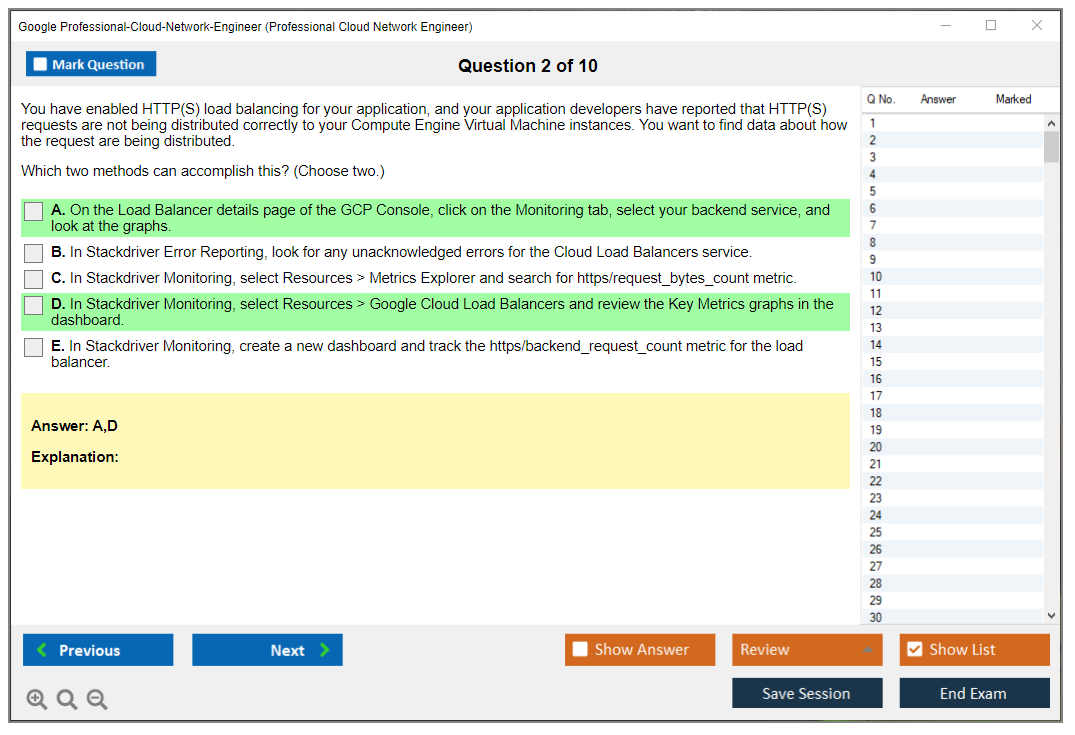
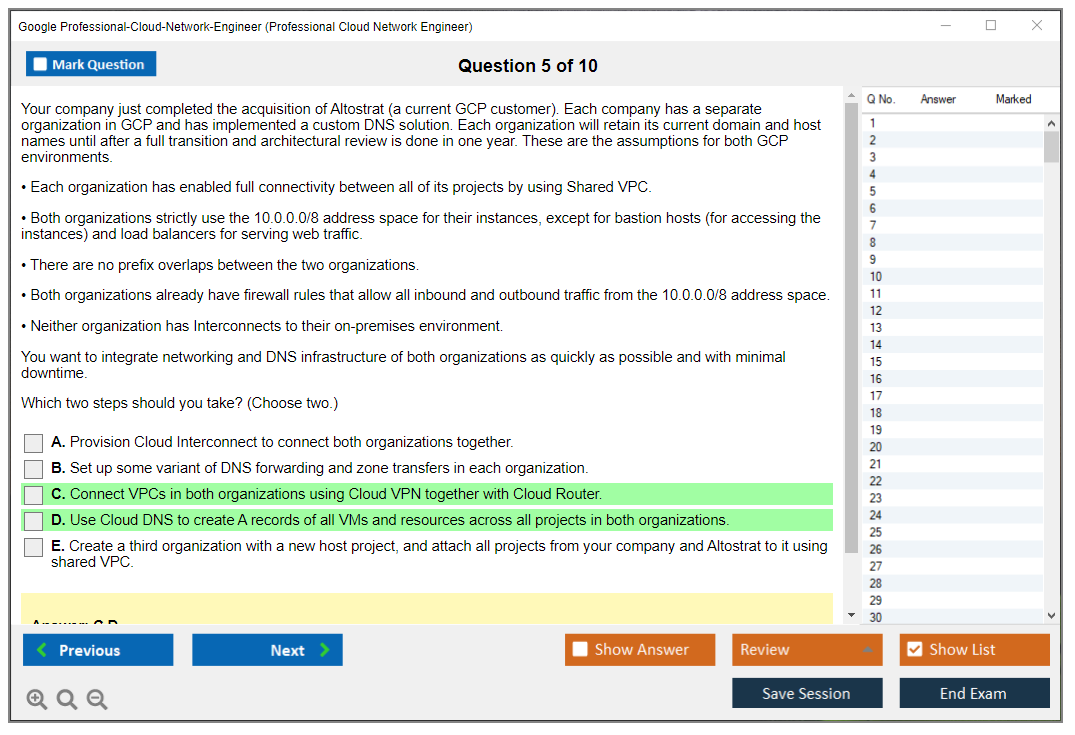
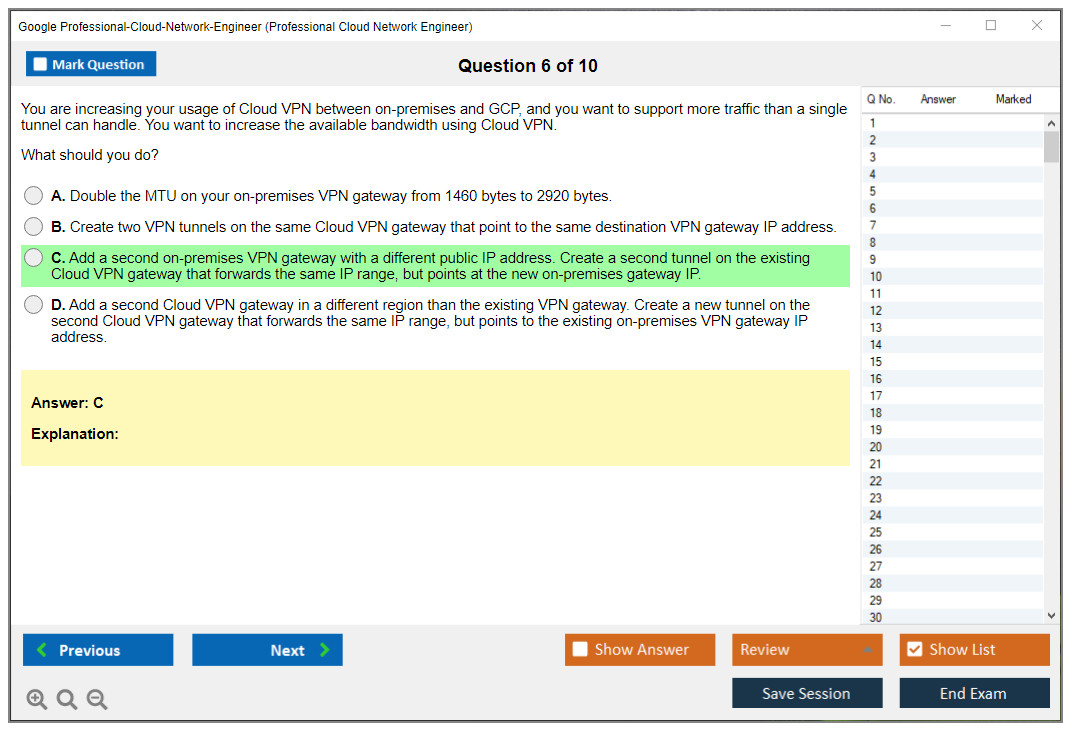
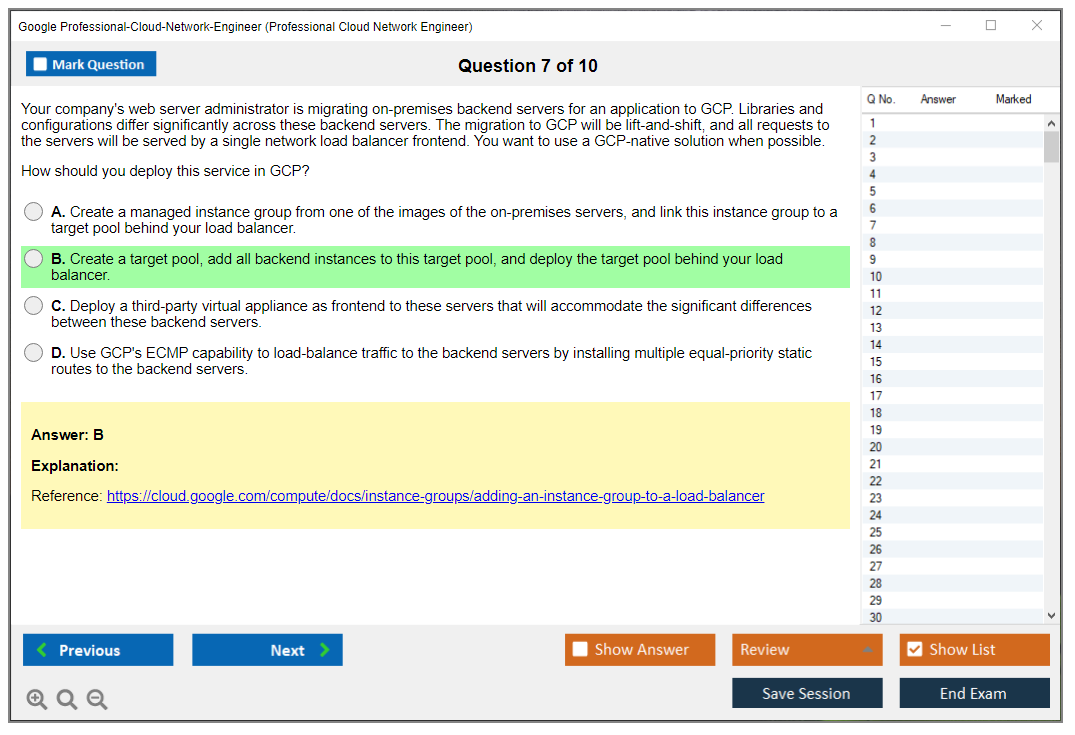
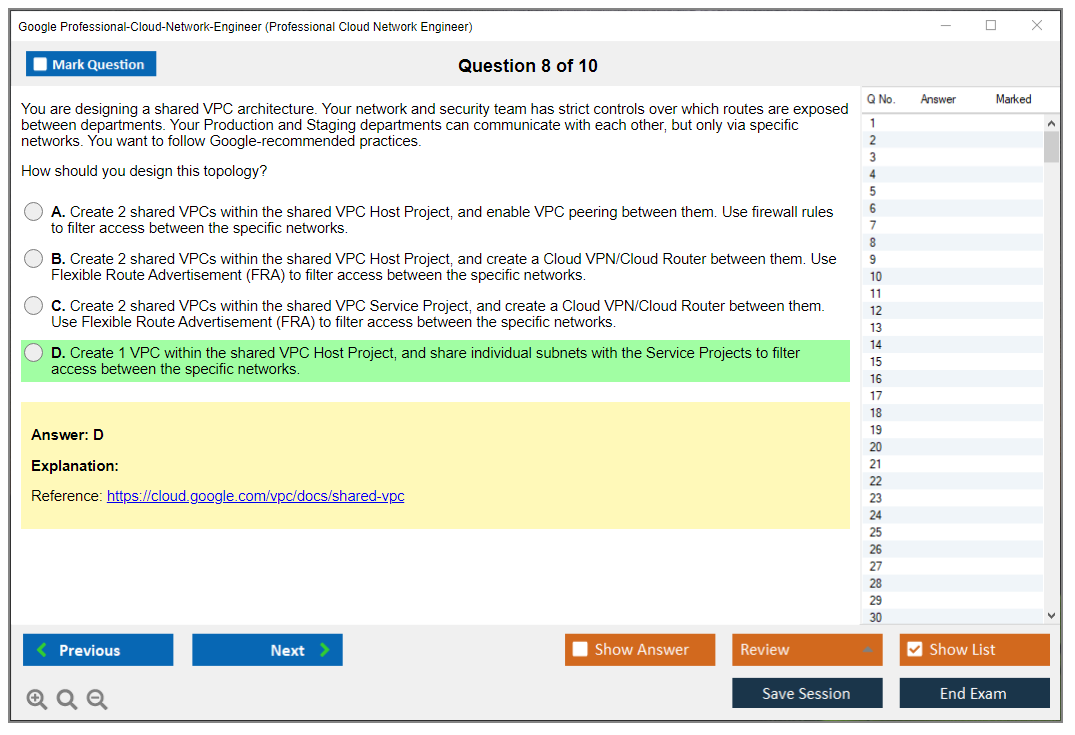
This exam throws 50 to 60 questions at you, all multiple-choice and multiple-select format. The vibe isn't trivia night at your local pub. It's scenario-driven problem-solving where you're reading through a business situation, identifying constraints buried in the text, then selecting the optimal architecture or operational response. Your brain needs to operate across Google Cloud VPC design and implementation, hybrid connectivity options (Cloud VPN, Cloud Interconnect), network security layers (firewalls, Cloud Armor, IAM policies), monitoring plus troubleshooting workflows (Cloud Logging/Monitoring), and load balancing with traffic management across Google Cloud infrastructure.
You get 2 hours (120 minutes). There aren't scheduled breaks built in, though you can pause briefly if needed. In reality that means you can lean back for maybe ten seconds, take a breath, refocus, but you can't expect a pause that actually stops the timer or lets you step away without potential consequences. Not gonna lie, that "no breaks" aspect hits different during remote proctoring because you're intensely conscious of any movement that takes you off-camera view.
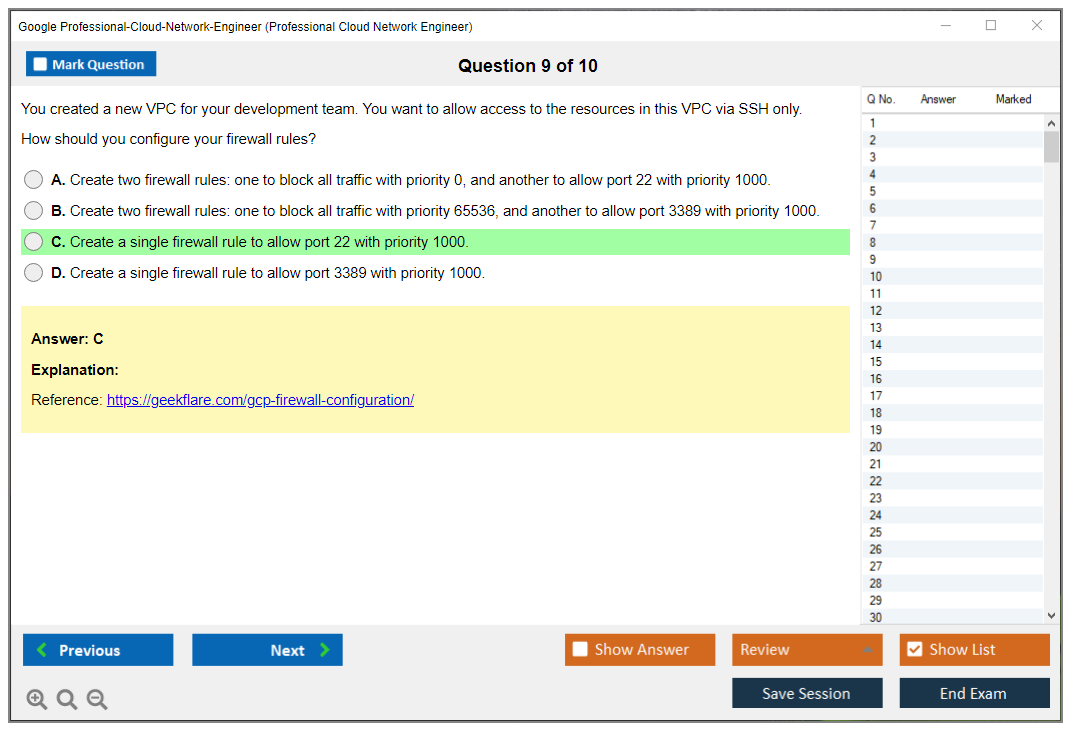
Multiple-select questions? That's where candidates crash hard. You'll encounter "choose 2" or "choose 3" from 5 or 6 possible options, and here's the kicker: partial credit doesn't exist. If you select two correct answers but miss the third required one, you get zero points for that question. Changes your entire approach to uncertainty. When you're unsure, you've gotta re-read the scenario and figure out what Google's actually optimizing for. These questions typically include one or two options that sound perfectly reasonable from general networking principles but don't align with GCP service limitations, the operational requirements specified, or the security posture they've described.
Expect heavy "real world" framing. Constraints everywhere. Tradeoffs matter.
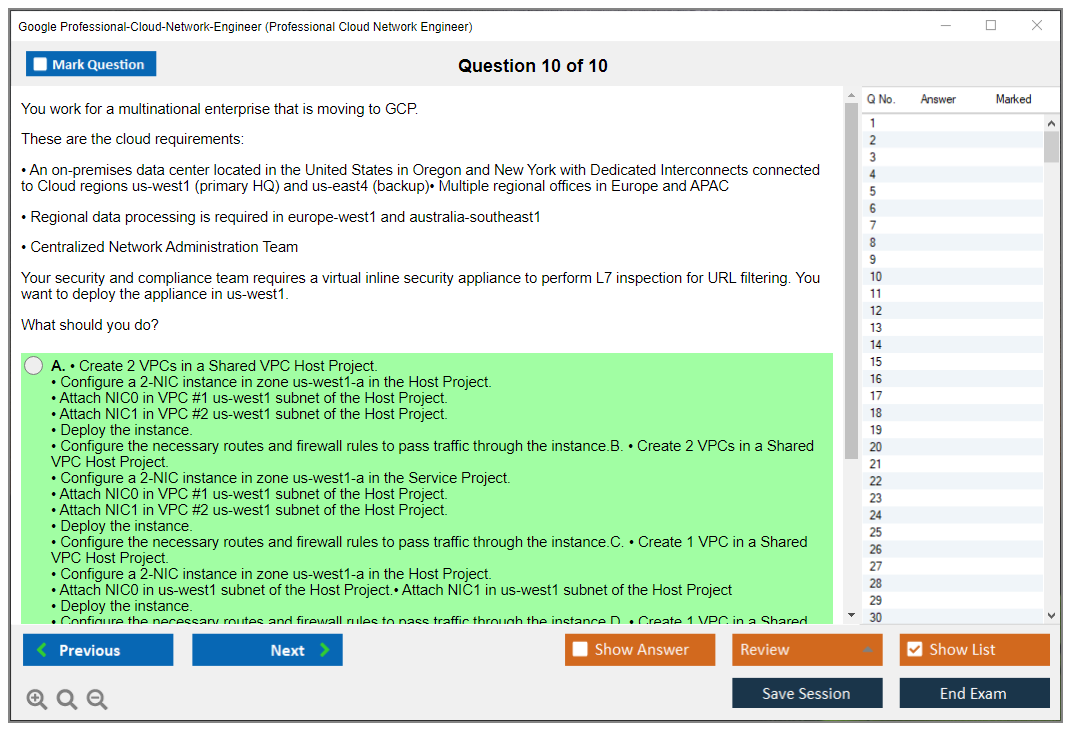
The scenarios push architectural decision-making constantly. Like, when should you pick Cloud Interconnect versus Cloud VPN, which load balancing type matches global versus regional requirements, how Shared VPC and IAM boundaries impact multi-team configurations, what firewall rules and hierarchical policies do to potential blast radius, and which monitoring signals you'd legitimately use when troubleshooting bizarre latency patterns or mysteriously dropped packets.
Language options are decent enough: English, Japanese, Spanish, and Portuguese. Content stays consistent across languages, so you're not getting an easier or harder version by selecting one, but you should choose whichever language you can read fastest under pressure because the scenarios get wordy and that clock keeps moving regardless.
Delivery runs through Kryterion, either remote online proctoring via Kryterion Webassessor or in-person testing at authorized Kryterion test centers. Both options work. Both have upsides and downsides. I mean, the actual content's identical, but the experience can feel totally different based on how controlled your environment is.
Oh, speaking of controlled environments, I once watched a coworker do a remote proctored exam from his "home office" which was basically a corner of his kitchen. His cat jumped on the desk mid-exam, knocked over a water bottle, and the proctor flagged it as suspicious activity. He had to spend like five minutes explaining through the chat that no, the cat wasn't somehow feeding him answers. They let him continue, but man, talk about unnecessary stress. Get your space sorted.
Scheduling the exam and test center vs. online proctoring
Registration's pretty straightforward: create an account at webassessor.com/googlecloud, select the Professional Cloud Network Engineer exam, pick your delivery method, schedule an appointment. Done. What actually trips people up is the timing and rescheduling rules, plus the whole "will my laptop completely betray me mid-exam" anxiety factor.
Online proctoring runs 24/7, which is really amazing if you're managing a job, kids, irregular shift work, whatever. Test centers operate on local business hours and capacity constraints, and popular locations fill up fast, especially around quarter-end when companies push certification targets hard.
Book early enough. Two weeks minimum. Four's safer honestly.
My recommendation? Schedule 2 to 4 weeks ahead if you care about a specific date and time, particularly if you want a test center slot. If you're taking it online at 2:00 a.m. on a random Tuesday, you've got more wiggle room, but even then, don't assume your preferred slot will be available the day before you want it.
Rescheduling policy's actually pretty fair: you can reschedule for free up to 72 hours before your appointment time. Cancel within 72 hours, you typically forfeit the exam fee. Honestly, this is where the "I'll just book something and sort it out later" approach becomes expensive real fast, so don't schedule until you're at least reasonably close to ready.
Now the big choice: test center versus remote.
Test center advantages are simple and weirdly underrated. Controlled environment, period. No dealing with home internet hiccups. No roommates barging in. No neighbor firing up a lawnmower right when you're deep in a complex scenario about hybrid connectivity and routing protocols. Also, if your personal workspace is chaotic, a test center offers a clean reset. They provide the workstation, they've usually got lockers for your belongings, which matters because prohibited items rules are strict as hell.
Remote proctoring can be excellent too, but you need to treat it like a production change window. Serious preparation required. You must have a reliable internet connection with minimum 1 Mbps upload/download, plus a webcam, microphone, a government-issued ID, and a quiet private room with a clean desk workspace. No phone on the desk. No smartwatch. No notes anywhere. No books. No extra monitors. And absolutely no other person walking through the room, even briefly, because proctors can terminate your session if it appears you're receiving assistance.
There's a required system check too, and you should take it seriously: complete the technical system test 24 to 48 hours before your scheduled exam to verify browser compatibility, camera access, microphone functionality, and connection stability. Look, doing it ten minutes beforehand is how you end up furiously texting your manager that Kryterion "won't launch" while the clock burns through your appointment window.
Check-in eats time that people don't account for. For a test center, arrive 15 minutes early minimum. For online proctoring, plan a 15 to 30 minute check-in where you complete ID verification and a workspace scan. Yeah, they can ask you to move your camera around showing the desk, the floor, the walls, anything nearby that might be notes or a second screen.
ID requirements are strict and boring but critical: you need a government-issued photo ID with a name matching your registration exactly, like a passport, driver's license, or national ID card. If your Webassessor profile says "Mike" and your ID shows "Michael" with a different last name format, fix it before exam day arrives. Don't gamble on that.
One more thing. NDA. You accept it. No question sharing.
Before the exam launches, you'll accept a non-disclosure agreement prohibiting sharing specific exam content. That means no posting "here are the exact multiple-select options I encountered" on forums, even if you think you're being helpful to other candidates.
If you need accessibility accommodations, they're available, but you've gotta plan ahead properly. Extra time, screen readers, other adjustments exist, and you request them through Kryterion support, typically 10+ business days before your exam date. Waiting until exam week is how you end up rescheduling and losing all momentum.
Quick note on common "People also ask" stuff that surfaces while you're planning: yes, candidates ask about the passing score, difficulty level, the best study materials, renewal requirements. Those are all legitimate concerns, but none of them matter if you can't get cleanly booked and show up with proper setup. Lock down the logistics first, then return to your Professional Cloud Network Engineer exam guide, practice test plan, and exam objectives, because you want exam day to feel operationally boring, with all your mental energy focused on the scenarios and the architecture choices.
Passing Score, Results, and Retake Policy
Understanding the passing score for Google's Professional Cloud Network Engineer exam
Okay, so here's the deal. Google doesn't publish the exact Professional Cloud Network Engineer passing score. They're weirdly secretive about it.
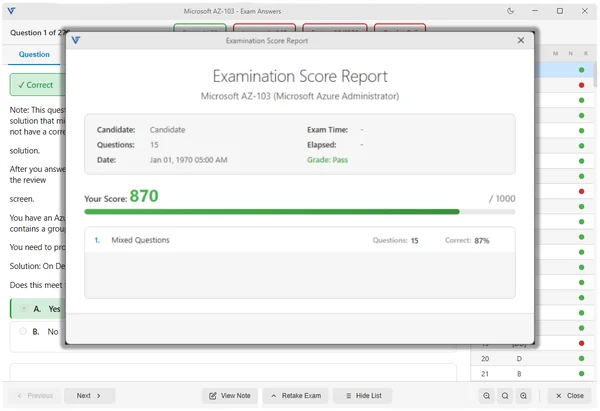
Industry estimates and feedback from test-takers suggest you'll need somewhere around 70-75% correct answers to pass, but honestly that's just educated guessing based on what people report after taking the exam. The actual threshold could shift slightly depending on the specific exam version you get, which is where scaled scoring comes into play.
Google uses a scaled scoring system. Ranges from 200 to 1000 points. This isn't just converting your raw score to a different scale for kicks. It accounts for difficulty variation across different exam versions, ensuring that if you get a slightly harder set of questions, the scoring adjusts so you're not penalized compared to someone who got an easier version. It's meant to ensure consistent standards regardless of which question pool you draw from. Sounds fair in theory. But it also means you can't just count questions and know exactly where you stand.
How the scoring actually works (and what you won't get)
Here's something that trips people up: there's no partial credit on multiple-select questions whatsoever. If a question asks you to choose all correct answers and there are three right options, you've gotta select all three. Pick two out of three? Zero points. This makes the multiple-select questions particularly brutal because you're essentially gambling. If you're not completely confident, you might second-guess yourself into missing points you could've earned. I once watched a colleague agonize for five minutes over whether to add a third selection, only to find out later he had the first two right but left off the correct third option. Costly hesitation.
The exam consists of multiple-choice and multiple-select questions. Each one's scored independently. You won't see a breakdown of "you got 42 out of 60 questions correct" because Google doesn't disclose the exact number of questions you answered correctly or your numerical percentage. Instead they provide performance indicators by domain.
After you finish the exam, you get immediate preliminary results if you're taking it through online proctoring. We're talking within seconds of hitting submit. If you're at a test center, results typically pop up within minutes. But the thing is, this is just a pass or fail indicator. The real detailed feedback? Comes later.
What your score report actually tells you
The official score report gets emailed within 7-10 business days, though most people I've talked to received theirs within 2-3 business days, which is nice. This report breaks down your performance by exam domain: things like designing and planning networks, implementing VPCs, configuring hybrid connectivity, managing network services, security, and monitoring.
For each domain you'll see performance indicators. "Needs improvement," "meets expectations," or "exceeds expectations." This is really helpful for understanding where you fell short if you failed, or where you were strongest if you passed. But again, no exact scores. You won't know if you "exceeded expectations" with 95% or 85% in a particular area, which is kinda frustrating.
If you pass, your digital badge gets issued through Credly within 2-3 weeks. You get a downloadable certificate PDF and can share it on LinkedIn, which is pretty standard for cloud certifications these days. If you're coming from other Google Cloud certs like the Associate Cloud Engineer or considering the Professional Cloud Architect next, you'll recognize the same credential delivery system.
What happens if you don't pass
Not gonna lie, failing stings.
But the score report for a failed attempt? Actually more valuable than you might think. That domain-level breakdown shows exactly which areas need work. Maybe you crushed the VPC design questions but struggled with hybrid connectivity and BGP configurations. Or perhaps security policies and Cloud Armor tripped you up. This feedback's your roadmap for the next attempt.
One thing to understand: failed exam scores aren't retained or combined with future attempts, meaning each attempt is scored independently from scratch. You can't think "well, I got the VPC section perfect last time, so I can focus less on that." Every attempt stands alone.
Retake policy and attempt limits
Here's where Google's policy gets specific. Between your first and second attempt there's no waiting period required. Fail once? You can schedule your retake immediately if you want, though I wouldn't recommend rushing back without proper prep.
Between the second and third attempts you need to wait 14 days. After the third failed attempt? There's a 60-day waiting period before you can try again. This escalating structure's designed to prevent people from just brute-forcing the exam repeatedly.
There's also an annual limit. Five exam attempts per 12-month period. This resets one year from your first attempt date, so if you take your first shot on January 15th, you might take up to four more attempts before January 15th of the next year.
Each retake costs the full exam fee of $200. No discounts. No "you already paid once" breaks. This adds up fast if you're not prepared, which is why using resources like the Professional Cloud Network Engineer practice test materials before attempting or retaking makes financial sense: $36.99 for practice questions versus $200 per failed attempt is an easy calculation.
Appeals and verification
There's no formal appeal process for exam results. If you believe technical issues affected your performance like proctoring software crashed, questions didn't display properly, or connectivity problems interrupted your exam, you need to contact Kryterion support within 24 hours. But you can't appeal just because you disagree with your score or think a question was unfair, which seems reasonable.
Employers can verify your certification status through Google Cloud's certification directory using your name and certification ID. This is the official verification method, so there's no ambiguity about whether someone actually holds the credential.
Strategy for retaking after a failed attempt
If you fail, here's what I'd do: first, let the disappointment pass for a day or two, then dig into that score report. Identify the one or two domains where you performed worst. These are your focus areas.
For most people, hybrid connectivity components like Cloud Interconnect, Partner Interconnect, and HA VPN configurations tend to be weak spots. Network security with Private Service Connect, VPC Service Controls, and firewall rules hierarchies also trips people up. Get hands-on experience with these specific areas. Reading documentation isn't enough. You've gotta actually configure these services in a project.
Take additional practice exams and track your weak areas. The Professional Cloud Network Engineer exam prep materials can help identify gaps you might've missed. Don't just retake practice tests you've already seen. Your brain memorizes answers rather than learning concepts.
Wait at least two weeks. Even if you don't have to. Use that time for focused study, not just reviewing everything again. If you studied broadly the first time, study deeply the second time on your weak domains.
Some candidates find value in pursuing related certifications to build adjacent knowledge: the Professional Cloud Security Engineer overlaps significantly on security topics, while the Professional Cloud Architect covers broader design principles that inform network architecture decisions.
The scaled scoring system means you can't game this by memorizing question pools or looking for patterns. You need actual understanding of VPC design, routing, BGP, load balancing architectures, and troubleshooting methodologies. Focus there, and your retake becomes a formality rather than another gamble.
Exam Difficulty and Preparation Timeline
Exam difficulty and preparation timeline
The Google Professional Cloud Network Engineer certification is legitimately one of the tougher Google Cloud certs. No question. You've gotta think like an architect while simultaneously troubleshooting like you're on-call at 2 AM, and the questions don't ask "what's this feature called?" They're more like "okay, the business is literally melting down, which option won't bankrupt us while also not making everything worse."
Hard exam.
Super judgment-heavy.
If you want a straightforward difficulty rating, I mean, I'd drop it in the "high" bucket for Google Cloud stuff, especially when you stack it against Associate-level tests where things feel more forgiving and less like working through a minefield of architectural trade-offs. Industry pass rate estimates hover around 50 to 65% on the first attempt. That honestly tracks with what I've witnessed in study groups and teams I've worked with over the years. Lower than Associate Cloud Engineer for sure, pretty comparable to other Professional-level Google Cloud exams where they stop being nice. And yeah, it's in roughly the same difficulty class as AWS Advanced Networking and Azure Network Engineer certs. You know, the ones where questions are thick with scenarios and the "best answer" depends on weird constraints you almost missed in paragraph three.
Why this exam feels hard in practice
Scenario questions. That's the game.
You'll get this massive setup: multi-project org, Shared VPC spanning like four teams, some services deployed in two regions, a hybrid connection tunneling back to an on-prem data center that's probably running hardware from 2014. Then a requirement drops like "private connectivity, absolutely no public IPs, minimal ops overhead, and oh by the way keep costs sane because finance is watching." Multiple answers might technically work in the real world, but the exam wants the most optimal choice given cost, performance, security, and business requirements. You don't get partial credit for "close enough" or "this would probably work."
Short version?
It's not trivia. It's design pressure with consequences.
The other thing people massively underestimate is depth vs. breadth, and honestly I've seen this kill people who thought they could skim. This isn't some light tour of VPCs and load balancers where surface-level knowledge gets you through. It goes deep into edge cases, limitations, and integration patterns across services, like how Private Google Access behaves in different network configurations. What actually happens with firewall rule precedence when you start mixing hierarchical firewall policies with VPC firewall rules. Where certain load balancing types do and absolutely do not fit despite what the marketing says.
You need to know what the product can do. But also what it cannot do.
Because Google loves throwing you a requirement that quietly forces you away from the "cool" option toward the boring one that actually works.
Architectural decision complexity shows up constantly, and it's exhausting. You'll be comparing approaches like Cloud VPN vs Cloud Interconnect, or different load balancing families (and there are way too many), or Shared VPC vs VPC peering vs Private Service Connect. The question will quietly include something like "must support overlapping RFC1918 ranges" or "security team requires centralized policy control," and that one detail buried in the middle flips the right answer completely. I once spent twenty minutes staring at a question during a practice run before I realized the word "global" in one sentence eliminated three of the four options. Felt like an idiot.
Troubleshooting is a big chunk
A significant portion of the exam is basically: here's the symptom, here's the janky environment someone built at 3 AM, what's the root cause and what do you do next without making it worse. You'll need comfort with Network monitoring and troubleshooting (Cloud Logging/Monitoring), plus practical instincts like checking effective firewall rules, routes, and load balancer health checks before you go nuclear and start redesigning the whole network because you panicked.
This is where people fail.
Fast.
Common pain points that show up again and again in post-exam debriefs:
- Hybrid connectivity (Cloud VPN, Cloud Interconnect) details, like BGP behavior nobody actually remembers until it breaks, route exchange quirks, and design choices for reliability when you've got SLA requirements
- Load balancing and traffic management on Google Cloud, where you need to match the correct LB type to protocol, scope, and backend needs or everything just doesn't work
- Firewall rule precedence, including tags/service accounts, those implied rules that bite you, and org policy interactions that override everything
- Shared VPC configurations, especially service project permissions and the eternal question of who can create what and where
- Private Google access options, figuring out which "private" feature actually applies to the specific path in the question because Google has like six things called "private something"
I'll explain two of those because they're where I see the most "I memorized this but don't actually get it" problems.
Hybrid connectivity is full of detail. The question is rarely "what is Cloud VPN." It's usually "the link flaps under load," "routes aren't being advertised the way you expect and nobody knows why," or "you need predictable latency for a specific app tier that's revenue-critical." If you've never had to reason through BGP route priority (and let's be honest, most people haven't), or how HA VPN behaves with dynamic routing when things get spicy, you end up guessing and hoping. Bad exam strategy.
Load balancing is its own swamp, and the thing is, people mix up global vs regional behavior, L4 vs L7, proxy vs passthrough, and what happens when you add Cloud Armor or need TLS termination in a particular place for compliance reasons. The exam writers absolutely know how to poke those weak spots because they've seen the same mistakes for years.
Experience level matters more than people admit
Candidates with 2+ years of hands-on Google Cloud networking usually walk in with way higher confidence and better pass rates than folks who only did reading and videos and maybe spun up a VPC once to see what it looked like. That makes sense, right? The exam is testing operational judgment, not just definitions you can parrot back, and you can't really fake that easily without having debugged a production network at least a few times.
Also, check your own background honestly. Like, really honestly.
If you're strong in on-prem routing and BGP but relatively new to Google Cloud VPC design and implementation, expect a learning curve around how Google models networks, projects, IAM boundaries, and shared responsibility. It's different enough to trip you up. Cloud networking is still networking, obviously, but the control plane changes how you think about problems.
How much study time is realistic
Typical total study time is 60 to 120 hours of focused work, depending on how much Google Cloud you already do day-to-day and how deep your networking fundamentals are from previous roles.
Here's what the timeline tends to look like for different people I've coached or watched prep:
Network engineers with 1+ year of Google Cloud experience usually need 6 to 8 weeks part-time, around 10 to 15 hours weekly, which is doable if you're disciplined and don't let Netflix win. Career transitioners coming from on-prem to cloud often need 10 to 12 weeks. They need way more hands-on labs because the "concepts" don't actually stick in your brain until you've built things and broken them and figured out why.
If you already hold Associate Cloud Engineer, cool, that helps with platform basics and general Google Cloud literacy, but you still need 8 to 10 weeks focusing on advanced networking topics that go beyond Associate scope by a mile. The Associate exam doesn't push hard on multi-project network governance, complex hybrid patterns, or deep troubleshooting that requires reading logs and correlating events. This one absolutely does.
An accelerated plan is possible. A real one, I mean.
If you're already working as a Google Cloud network engineer and touching this stuff daily, you can squeeze prep into 4 weeks if you do 2 to 3 hours daily plus weekend lab sessions where you actually build things. Not gonna lie, it's mentally expensive and you'll feel it by week three when your brain starts rejecting information.
A longer timeline can actually be better for retention and sanity. A 12 to 16 week plan gives you time to explore advanced topics properly, do more realistic builds that simulate production complexity, and retain the material for your actual job instead of dumping it from memory the day after exam day. Which happens more than people admit. That matters if you're using the cert to actually move into a network role or get promoted, not just collect badges for LinkedIn.
A practical week-by-week prep plan
Look, you can study randomly and hope things stick.
Or you can plan it.
A solid phase breakdown that matches how the exam actually feels when you're in the seat:
Week 1 to 2: foundation review, which sounds boring but matters. VPC fundamentals, subnetting (yes, really), routing basics, DNS fundamentals, IAM concepts that affect networking because everything touches IAM. Careful pass through the Professional Cloud Network Engineer exam objectives so you stop guessing what actually matters and what's just noise.
Week 3 to 5: core networking services deep dive where things get interesting. VPC design patterns, Shared VPC configurations, Private Service Connect (which is newer and they love testing), Cloud DNS, load balancing types and when to use each without screwing up. The stuff you only learn by reading docs carefully instead of skimming blog posts.
Week 6 to 8: security and hybrid connectivity, which is where most people realize they've been hand-waving details. Firewalls and how they actually evaluate rules, Cloud Armor for DDoS and WAF scenarios, IAM boundaries that everyone forgets about, private access choices that have confusing names. Plus Cloud VPN and Interconnect design decisions that require understanding cost vs. performance trade-offs.
Week 9 to 10: practice exams and weak-area remediation, which is non-negotiable. You need a Professional Cloud Network Engineer practice test routine that includes reviewing why each wrong answer is wrong and what signal you missed. Not just chasing a score so you can feel good.
Daily study approach that doesn't wreck your life or relationships: 1 to 2 hours on weekdays focused on one topic at a time. 3 to 4 hours on weekends doing hands-on labs and practice scenarios that simulate real decision-making. Take a rest day, seriously. Burnout kills retention faster than anything, and exam fatigue makes you sloppy with those long scenario questions that require focus.
If you want structured practice questions that don't suck, I'd pair your study with something like the Professional-Cloud-Network-Engineer Practice Exam Questions Pack while you're in that week 9 to 10 phase. You need reps reading scenarios and selecting the best option under time pressure when your brain is tired. I've also seen people use the same pack earlier as a diagnostic to figure out what they don't know, then come back later for validation. Works well if you're disciplined and don't just memorize answers like a parrot.
Common failure reasons and how to dodge them
Most failures come from a few patterns I've seen over and over:
Not enough hands-on experience. Memorization without understanding. Neglecting troubleshooting skills entirely. Poor time management during the exam where you spend 10 minutes on one question. Underestimating scenario complexity and treating it like a quick multiple-choice quiz.
Fixes are boring but work.
Build small labs that mirror the scenarios you're studying. Break them on purpose. Like, intentionally misconfigure firewall rules or mess up routing and force yourself to troubleshoot. Force yourself to explain out loud why you chose Internal TCP/UDP LB vs HTTP(S) LB, or why you picked Interconnect over HA VPN. What you'd lose with each option because there's always a trade-off.
Also, people get weirdly hung up on administrative details like the Professional Cloud Network Engineer exam cost (just look it up, it's on Google's site) or the Professional Cloud Network Engineer passing score as if there's some magic number they can "aim for" like a video game achievement.
Google doesn't publish a simple passing score number. Focus on actual competence and understanding. The score follows naturally.
Retakes and second-attempt timing
If you don't pass, don't spiral into existential dread. I've seen too many people do that and it doesn't help. Use the score report domains to target weak areas specifically, and give yourself 3 to 4 weeks of focused repair time before a second attempt. That's enough runway to rebuild labs, redo practice sets with fresh eyes, and patch the specific gaps that cost you points the first time.
And if you want a clean way to measure readiness before you rebook and spend more money, doing timed runs of scenario questions from the Professional-Cloud-Network-Engineer Practice Exam Questions Pack can help validate your progress. As long as you treat every miss like a mini incident report: what signal did you miss, what constraint actually mattered, what service limit did you forget existed because you never hit it in your lab environment.
Quick answers people always ask
"How hard is the Google Cloud Network Engineer certification?"
Hard.
And it's hard in the way real networking is hard: ambiguity, trade-offs, and troubleshooting under pressure with incomplete information.
"What are the best study materials for the Professional Cloud Network Engineer exam?" Official docs plus hands-on labs that you actually build. Plus a decent Professional Cloud Network Engineer exam guide that doesn't just regurgitate feature lists. Plus practice questions that force scenario thinking instead of flashcards you can memorize in an afternoon.
"How do I renew the Google Professional Cloud Network Engineer certification?" Google's Professional Cloud Network Engineer renewal requirements are basically recertification on Google's schedule, so plan to re-test when your cert is expiring. Keep up with product changes throughout the validity period so you're not re-learning everything from scratch like it's the first time. Wait, actually that's a good point. Staying current makes renewal way easier than treating it like a surprise exam two years later.
Exam Objectives and Core Domains
What the exam actually tests
The Professional Cloud Network Engineer certification breaks down into five domains, with design and VPC implementation taking up more than half the exam at 26% each. Google wants you capable of both planning networks from scratch and actually building them without breaking production. The remaining portions split between network services (18%), hybrid connectivity (14%), and security (12%). That weighting tells you exactly where to spend your study time, honestly.
Domain 1 hits you with design decisions you'll face in real consulting or architecture roles. You're choosing between custom and auto mode VPCs, which seems basic until you realize auto mode creates subnets in every region automatically and you can't control those CIDR blocks. Fine for labs. Terrible for enterprises with existing IP schemes. Secondary IP ranges come up constantly because GKE needs them for pods and services. If you don't plan those ranges properly during cluster creation, you're in for a painful migration later when you run out of IPs.
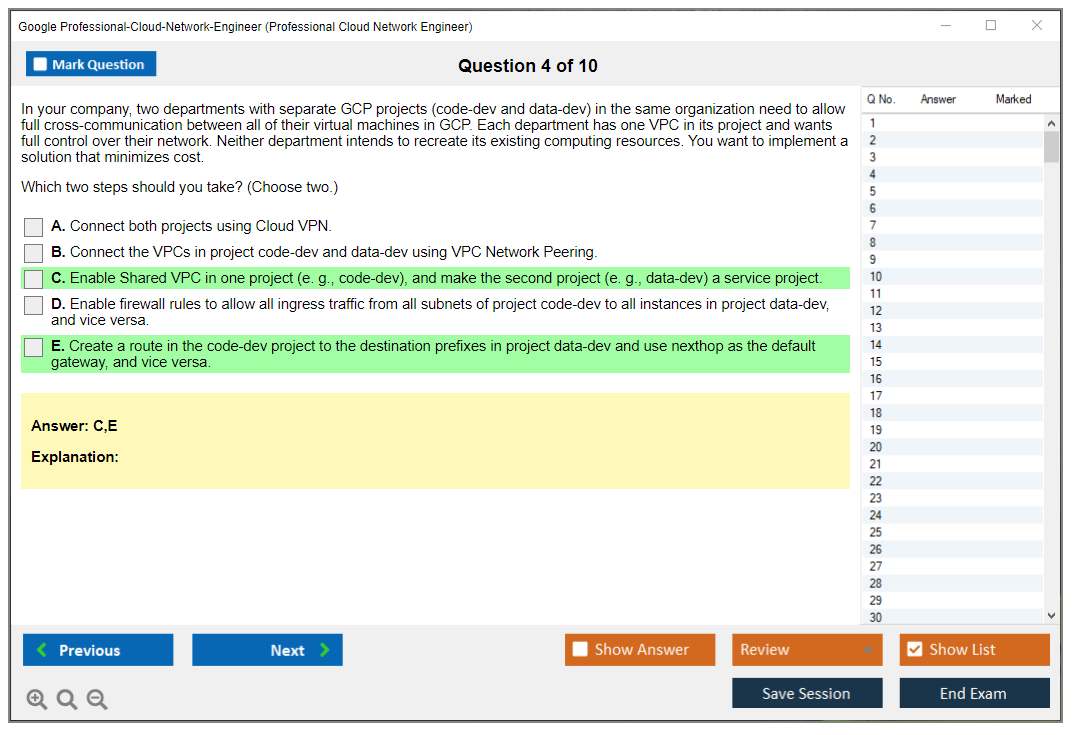
Shared VPC architecture shows up heavy in this domain. The host project owns the VPC, service projects attach to it, and you're managing IAM permissions across project boundaries which gets complicated fast. I've seen people mess up the network admin versus security admin roles and suddenly developers can't deploy anything. Organizational policy constraints add another layer. You might design a beautiful multi-project network only to find out a policy prevents VPC peering or, I mean, restricts certain IP ranges that you actually needed for production.
Hybrid connectivity design requires understanding when Cloud VPN makes sense versus shelling out for Interconnect. VPN works great up to about 3 Gbps per tunnel if you configure HA VPN with multiple tunnels, but latency varies because you're going over public internet. Dedicated Interconnect gives you 10 or 100 Gbps links with consistent low latency, but you're paying monthly port fees plus colocation or you're using Partner Interconnect through a provider. The exam will throw scenarios at you where cost matters, where SLA requirements matter, where bandwidth projections matter. You need to justify your choice based on actual business constraints not just technical preferences.
Funny thing is, I once watched someone spec out Dedicated Interconnect for a dev environment that pushed maybe 200 Mbps on average. The finance team nearly had a stroke when they saw the quote.
Building actual VPC infrastructure
Domain 2 drops you into the console or gcloud commands to implement what you designed. Creating a custom mode VPC seems straightforward until you're configuring Private Google Access, which lets instances without external IPs reach Google APIs. But wait, there's also Private Google Access for on-premises hosts, which uses different IP ranges (199.36.153.8/30 and 199.36.153.4/30) and requires specific routes. Then Private Service Connect enters the chat for accessing Google services or third-party services through internal endpoints. Three different "private access" features that solve different problems and you'll mix them up if you're not careful.
Subnet management includes expanding IP ranges, which you can do without recreating the subnet. Good luck finding that option buried in the console though. You can expand but never shrink, period. Secondary ranges for GKE require planning because each node pool can reference one pod range and one services range. Expanding those later means careful coordination with the cluster team who'll complain loudly if you mess up their deployments.
Routing gets interesting with custom static routes and dynamic routing modes. Regional dynamic routing (the default) means Cloud Router only shares routes within one region. Global dynamic routing shares routes across all regions, which sounds great until you realize cross-region data transfer costs and you've accidentally created traffic patterns you didn't intend. Route priorities matter when you have overlapping destinations. Lower number wins, and the default route to internet is priority 1000 which becomes relevant when you're troubleshooting why traffic isn't flowing where you expected.
VPC Network Peering has limits that catch people off guard. No transitive peering means if VPC-A peers with VPC-B and VPC-B peers with VPC-C, VPC-A can't reach VPC-C. You also can't peer more than 25 VPCs to a single VPC, which enterprises hit faster than you'd think. Exchange of custom routes works but you control what gets exchanged. Subnet routes are always exchanged whether you like it or not.
Cloud NAT configuration comes up because you need outbound internet access for private instances to download patches or reach external APIs. You're setting up which subnets use the NAT gateway, whether to allocate specific IP addresses or let it auto-allocate, and monitoring for port exhaustion when you have thousands of concurrent connections competing for limited resources.
Firewall rules seem simple. Allow or deny traffic based on source/destination and protocol. Then you're managing 200 rules across multiple projects and trying to figure out why traffic is blocked. Implied deny ingress means you're explicitly allowing everything that should flow. Priority 65535 means your rules with priority 1000 take precedence. The thing is, service account-based targeting is cleaner than network tags for security because tags can be changed by anyone with instance admin, but service accounts require IAM permissions which provides better access control.
Network services and traffic management
Domain 3 covers load balancing types and the decision matrix is complex, not gonna lie. External HTTP(S) Load Balancer is global, anycast IP, routes to closest healthy backend. Internal HTTP(S) Load Balancer stays within your VPC and can be regional or cross-region. Network Load Balancer is regional, pass-through, preserves source IP. TCP/SSL Proxy Load Balancers terminate connections and are global. You need to know which supports what protocol, which is global versus regional, which preserves client IP. The exam loves scenario questions about this.
Setting up an HTTP(S) load balancer involves backend services, backend buckets for Cloud Storage, URL maps for routing, target proxies, forwarding rules, and health checks. Miss one piece and traffic doesn't flow, trust me. Cloud CDN integration happens at the backend service level, and you're configuring cache modes (cache all, cache static, use origin headers), TTLs, and cache keys. Signed URLs and signed cookies control access to cached private content when you're serving media or downloadable files to authenticated users.
Cloud DNS managed zones hold your records, but split-horizon DNS requires two zones. One for internal resolution, one for external which seems redundant until you need different answers for internal versus external clients. DNS peering lets you query another VPC's private zones. DNSSEC adds cryptographic signatures to prevent spoofing but requires careful key management that can break resolution if you screw up rotation. Cloud DNS policies control inbound and outbound forwarding, which matters for hybrid environments where you need on-premises resolvers to query Google Cloud zones or vice versa depending on where services live.
Health checks configure the interval (how often to check), timeout (how long to wait for response), healthy threshold (how many successes before marking healthy), and unhealthy threshold (how many failures before removing from pool). Different application types need different settings. HTTP health checks work for web apps, TCP for databases, SSL for encrypted services that won't respond to plain HTTP probes.
Connecting on-premises to cloud
Domain 4 focuses on hybrid connectivity implementation which is honestly where most enterprises spend real effort. Classic VPN is route-based or policy-based, supports one tunnel per gateway, gives you 99.9% SLA if you configure two gateways. HA VPN uses two external IPs on the Google side, requires you to configure two tunnels to meet 99.99% SLA, and you're establishing BGP sessions to exchange routes dynamically instead of maintaining static route tables that drift over time.
VPN tunnel configuration includes IKE version, pre-shared keys, and routing options that need to match on both ends or the tunnel won't establish. Static routing works for simple setups but dynamic routing with Cloud Router and BGP scales better. You're advertising subnet routes from Google Cloud to on-premises and importing on-premises routes. You can customize those advertisements to control traffic flow and prevent unwanted routing that could create asymmetric paths.
Cloud Interconnect provisioning takes weeks because you're coordinating physical connections between facilities. Dedicated Interconnect means you're in a colocation facility with Google, ordering cross-connects, configuring 10 or 100 Gbps links through fiber patches. Partner Interconnect uses a service provider's existing connection to Google, giving you flexibility from 50 Mbps to 10 Gbps without needing your own colocation space. VLAN attachments carry your traffic over the physical connection. You're establishing BGP sessions to exchange routes just like VPN but with way better bandwidth and latency characteristics.
Redundancy configurations for 99.9% SLA require two VLAN attachments in the same metro area. For 99.99% you need four attachments across two metros, which gets expensive but eliminates single points of failure including entire facility outages. The exam tests whether you know the topology requirements for each SLA level and can architect appropriately for business requirements.
Hybrid DNS using inbound and outbound server policies lets on-premises resolvers query Cloud DNS private zones or lets Google Cloud instances query on-premises DNS servers. You're specifying target name servers, configuring forwarding zones, and testing resolution in both directions to verify split-horizon resolution works correctly.
Securing everything
Domain 5 covers network security starting with firewall best practices that organizations often ignore until they get breached. Hierarchical firewall policies apply at the organization or folder level, enforced before VPC-level rules, giving you centralized control. You're implementing least-privilege by allowing only required ports to specific targets. Using service accounts instead of tags where possible. Enabling firewall rule logging for security audits even though it generates tons of data.
Cloud Armor sits in front of HTTP(S) load balancers providing WAF functionality, rate limiting, and geographic restrictions for public-facing applications. You're creating security policies with rules that allow, deny, or throttle traffic based on IP addresses, geo-location, request headers, or custom expressions using the Common Expression Language. Preconfigured WAF rules protect against OWASP Top 10 vulnerabilities like SQL injection and XSS. Rate limiting prevents DDoS by throttling excessive requests from a single source before they overwhelm your backends.
Look, the exam doesn't just test memorization of features. You're getting scenarios where you choose technologies, troubleshoot broken connectivity, optimize costs, or meet compliance requirements with competing constraints. Understanding how the pieces fit together matters more than knowing every gcloud command flag, honestly. If you've worked with Google Cloud as an Associate Cloud Engineer, you've seen some basics, but the Professional level expects you to design complete network architectures, not just deploy a VPC and call it done. The overlap with Professional Cloud Architect exists but Network Engineer goes much deeper on connectivity, routing protocols, and load balancing internals that architects might gloss over.
Conclusion
Getting exam-ready means honest practice
Look, the Google Professional Cloud Network Engineer certification isn't something you wing. I've seen people with solid networking backgrounds stumble because they underestimated how Google does things differently. The thing is, the exam tests real scenarios like VPC design under weird constraints, troubleshooting hybrid connectivity when Cloud VPN suddenly isn't cutting it, choosing between different load balancer types when requirements conflict. You need reps.
Quality practice questions matter.
That's where it gets interesting. I mean, reading documentation's great but it doesn't prepare you for that moment when you're staring at a question about shared VPC service projects and IAM bindings and three answers look almost identical, and you're second-guessing everything you studied the night before. The Professional Cloud Network Engineer practice test experience needs to mirror the real thing. Same pressure, same question styles, same mix of straightforward and "wait what" scenarios.
The exam objectives cover everything from basic VPC implementation to complex hybrid architectures with Cloud Interconnect and custom routes. You'll hit questions on Cloud Armor rules, Private Google Access configurations, network monitoring with Cloud Logging. Some questions test pure knowledge, others make you think through a multi-step solution. The hardest part isn't memorizing commands but understanding why you'd architect something one way versus another. (Though I once spent an entire weekend just memorizing subnet ranges before realizing that wasn't even the point. Live and learn.)
Don't skip the renewal requirements conversation
Your certification lasts three years. Then you recertify.
Simple but easy to forget when you're job hunting or deep in projects. I've watched colleagues miss their renewal window and have to scramble. Staying current with Google Cloud network features matters because they ship updates constantly. New load balancer capabilities, VPC improvements, security features. The Professional Cloud Network Engineer renewal requirements basically mean taking the exam again, so keeping your skills sharp throughout those three years isn't optional.
The Professional Cloud Network Engineer exam cost runs around $200, which isn't cheap but reasonable for a professional cert. One attempt. No partial credit. The passing score isn't published but you'll know immediately if you passed. Most people need 8-12 weeks of solid prep if they're working full-time, maybe 4-6 if you're living and breathing Google Cloud networking daily.
Final resource that actually helps
Not gonna lie, I've tried a bunch of study materials. Some are outdated, some are just brain dumps that teach you nothing. What you want is something that explains why answers are right, breaks down the Google Cloud Network Engineer study materials into digestible chunks, and covers those tricky scenarios around VPC peering limitations or when to use global versus regional resources.
Real talk here.
The Professional-Cloud-Network-Engineer Practice Exam Questions Pack does exactly that. It's structured around the actual exam objectives. VPC design, hybrid connectivity with Cloud VPN and Interconnect, network security with firewalls and IAM, load balancing configurations, monitoring and troubleshooting. Each question comes with detailed explanations, not just correct answers but why the wrong ones don't work in specific contexts.
If you're serious about passing, combine hands-on labs with solid practice questions. Build a few VPCs, configure some Cloud Routers, break things and fix them. Then test yourself repeatedly with realistic questions. That combination, that's what separates people who pass from people who retake.