212-89 Practice Exam - EC Council Certified Incident Handler (ECIH v3)
Reliable Study Materials & Testing Engine for 212-89 Exam Success!
Exam Code: 212-89
Exam Name: EC Council Certified Incident Handler (ECIH v3)
Certification Provider: ECCouncil
Corresponding Certifications: ECIH , ECCouncil Other Certification

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
212-89: EC Council Certified Incident Handler (ECIH v3) Study Material and Test Engine
Last Update Check: Mar 21, 2026
Latest 167 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena ECCouncil EC Council Certified Incident Handler (ECIH v3) (212-89) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
ECCouncil 212-89 Exam FAQs
Introduction of ECCouncil 212-89 Exam!
ECCouncil 212-89 is the exam for the Certified Ethical Hacker (CEH) certification. It is a comprehensive exam that tests a candidate's knowledge and skills in ethical hacking and information security. The exam covers topics such as network security, cryptography, malware, and web application security.
What is the Duration of ECCouncil 212-89 Exam?
The duration of the ECCouncil 212-89 exam is 2 hours.
What are the Number of Questions Asked in ECCouncil 212-89 Exam?
There are a total of 125 questions on the ECCouncil 212-89 exam.
What is the Passing Score for ECCouncil 212-89 Exam?
The passing score required in the ECCouncil 212-89 exam is 70%.
What is the Competency Level required for ECCouncil 212-89 Exam?
The ECCouncil 212-89 exam is designed to test the knowledge and skills of a cybersecurity professional who has achieved the Certified Ethical Hacker (CEH) certification. The exam is divided into five domains, each of which covers a different area of cybersecurity. To pass the exam, a candidate must demonstrate a mastery of the material in each domain. The minimum competency level required to pass the exam is a CEH certification.
What is the Question Format of ECCouncil 212-89 Exam?
The ECCouncil 212-89 exam consists of multiple-choice, drag and drop, and fill in the blank questions.
How Can You Take ECCouncil 212-89 Exam?
The 212-89 exam can be taken online or in a testing center. To take the exam online, you must register with the ECCouncil website, then select the exam and purchase it. To take the exam in a testing center, you must register for the exam with the testing center and select a date and time for the exam. The testing center will provide further instructions on how to take the exam.
What Language ECCouncil 212-89 Exam is Offered?
The ECCouncil 212-89 exam is offered in English.
What is the Cost of ECCouncil 212-89 Exam?
The cost of the ECCouncil 212-89 exam is $250 USD.
What is the Target Audience of ECCouncil 212-89 Exam?
The target audience of the ECCouncil 212-89 exam is cyber security professionals who want to demonstrate their knowledge and skills in implementing, monitoring, and maintaining information security programs, policies, and procedures. This exam is also suitable for those who are preparing for the Certified Ethical Hacker (CEH) certification.
What is the Average Salary of ECCouncil 212-89 Certified in the Market?
The exact salary you can expect after earning the ECCouncil 212-89 exam certification depends on your experience, the type of job, and the location of the job. According to the Global Knowledge 2020 IT Skills and Salary Survey, the average salary for a professional in the cybersecurity field is $91,637.
Who are the Testing Providers of ECCouncil 212-89 Exam?
ECCouncil offers official exam testing for the 212-89 exam through Pearson VUE, a global testing company. You can visit their website, www.pearsonvue.com, to register for the exam and to find a testing center near you.
What is the Recommended Experience for ECCouncil 212-89 Exam?
To ensure success in the EC-Council 212-89 Exam, it is recommended that candidates have at least two years of experience in Information Security and/or related fields. It is also recommended that candidates have experience in the following areas: Risk Analysis, Security Policies, Auditing and Compliance, Cryptography, Network Security, Access Control, Business Continuity and Disaster Recovery, and Security Architecture. Additionally, it is beneficial for candidates to have experience in implementing security solutions on a variety of platforms, including Windows, Linux, and UNIX.
What are the Prerequisites of ECCouncil 212-89 Exam?
The prerequisites for the ECCouncil 212-89 exam are that you have to have a minimum of two (2) years of relevant work experience in either information security or IT auditing. Candidates must also have a valid and active ECCouncil membership.
What is the Expected Retirement Date of ECCouncil 212-89 Exam?
The official website for the ECCouncil 212-89 exam is https://www.eccouncil.org/programs/certified-ethical-hacker-ceh/. There is no information about the expected retirement date of the exam on this website.
What is the Difficulty Level of ECCouncil 212-89 Exam?
The difficulty level of the ECCouncil 212-89 exam is considered to be moderate.
What is the Roadmap / Track of ECCouncil 212-89 Exam?
The EC-Council 212-89 exam is part of the Certified Ethical Hacker (CEH) certification track. It is a rigorous exam that tests the knowledge and skills of a security professional in the areas of system hacking, network hacking, and countermeasures. The exam is designed to measure a candidate's ability to identify, analyze, and respond to security threats. Successful completion of the exam is required for CEH certification.
What are the Topics ECCouncil 212-89 Exam Covers?
The EC-Council 212-89 exam covers a range of topics related to the principles and practices of ethical hacking. These topics include:
1. Footprinting and Reconnaissance: This topic covers the process of gathering information about a target system or network, such as IP addresses, domain names, email addresses, and other relevant information.
2. Scanning Networks: This topic covers the process of using network scanning tools to identify vulnerabilities in a target system or network.
3. Enumeration: This topic covers the process of using various techniques to gather additional information about a target system or network.
4. System Hacking: This topic covers the process of gaining unauthorized access to a target system or network.
5. Malware Threats: This topic covers the types of malicious software that can be used to compromise a target system or network.
6. Sniffing: This topic covers the process of intercepting network traffic and analyzing
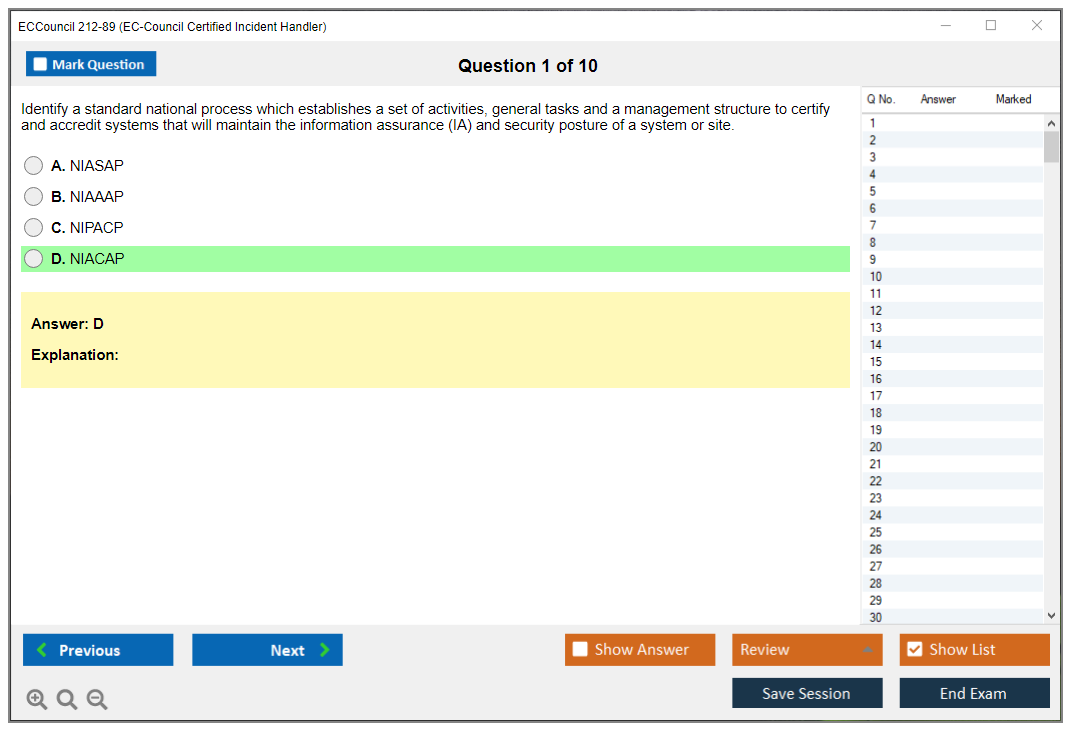
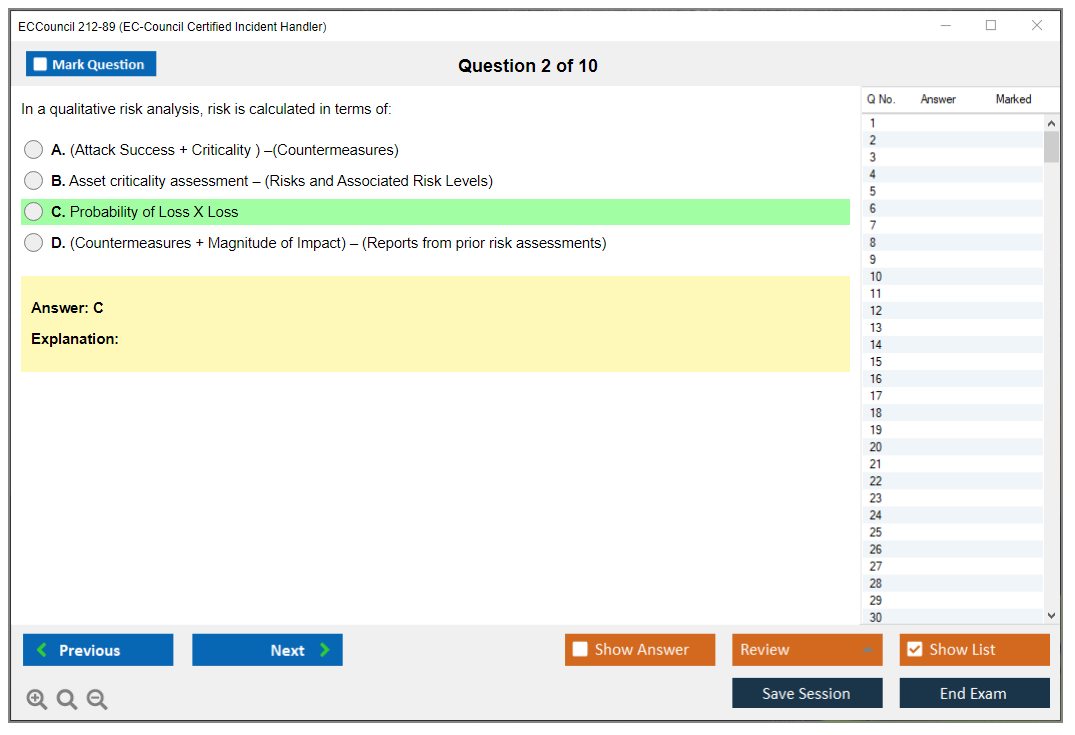
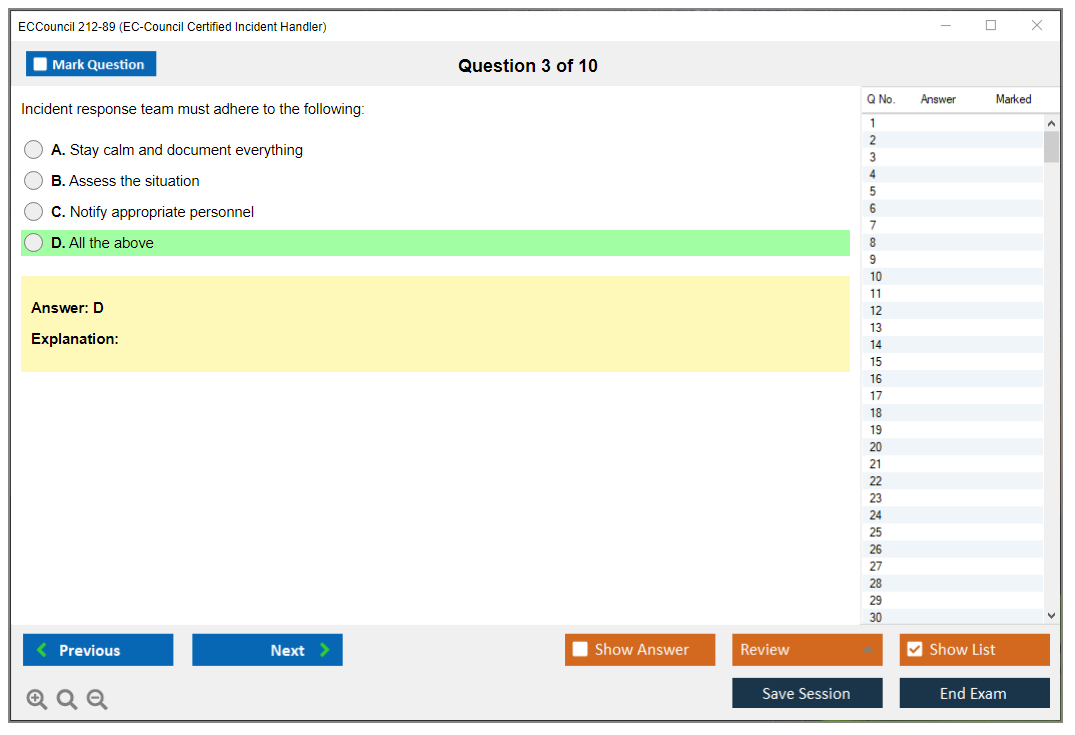
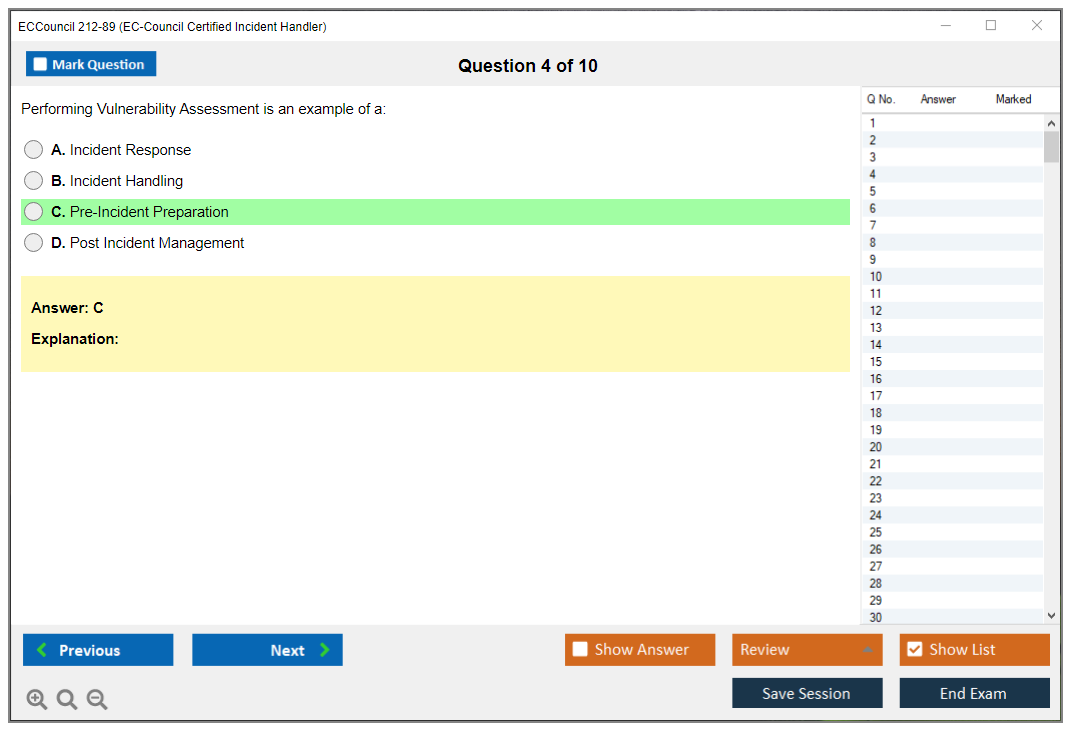
What are the Sample Questions of ECCouncil 212-89 Exam?
1. What are the three main components of the ECCouncil 212-89 exam?
2. What is the purpose of the ECCouncil 212-89 exam?
3. What are the topics covered in the ECCouncil 212-89 exam?
4. How is the ECCouncil 212-89 exam scored?
5. What is the time limit for the ECCouncil 212-89 exam?
6. What are the eligibility requirements for taking the ECCouncil 212-89 exam?
7. What is the format of the ECCouncil 212-89 exam?
8. What is the passing score for the ECCouncil 212-89 exam?
9. What are the best study resources for the ECCouncil 212-89 exam?
10. What are the benefits of passing the ECCouncil 212-89 exam?
ECCouncil 212-89 (EC Council Certified Incident Handler (ECIH v3)) EC-Council 212-89 (ECIH v3) Exam Overview Look, here's the deal. The 212-89 exam? It's officially the EC-Council Certified Incident Handler version 3, and honestly, it validates your skills in handling security incidents from start to finish. This certification isn't just another piece of paper. It shows you've got what it takes to manage cybersecurity incidents in real-world scenarios where everything's falling apart at once. What's covered? Tons, honestly. You're looking at incident handling processes, forensic fundamentals, and the entire incident response lifecycle that organizations desperately need when things go sideways. We're talking about preparation, detection, containment (which is harder than it sounds), eradication, recovery, and those post-incident activities nobody really wants to do but absolutely should. I spent three weeks once just documenting lessons learned from a ransomware incident, and yeah, it... Read More
ECCouncil 212-89 (EC Council Certified Incident Handler (ECIH v3))
EC-Council 212-89 (ECIH v3) Exam Overview
Look, here's the deal.
The 212-89 exam? It's officially the EC-Council Certified Incident Handler version 3, and honestly, it validates your skills in handling security incidents from start to finish. This certification isn't just another piece of paper. It shows you've got what it takes to manage cybersecurity incidents in real-world scenarios where everything's falling apart at once.
What's covered? Tons, honestly.
You're looking at incident handling processes, forensic fundamentals, and the entire incident response lifecycle that organizations desperately need when things go sideways. We're talking about preparation, detection, containment (which is harder than it sounds), eradication, recovery, and those post-incident activities nobody really wants to do but absolutely should. I spent three weeks once just documenting lessons learned from a ransomware incident, and yeah, it was tedious, but we caught two major gaps in our monitoring that way.
The exam tests whether you can identify security incidents quickly. Can you respond appropriately under pressure when stakeholders are breathing down your neck? Can you implement recovery procedures that actually work instead of just sounding good in meetings?
Mixed feelings here. It's thorough, sure, but it's also pretty intense. Covers malware analysis, log management, network security fundamentals, and vulnerability assessment techniques you'll legitimately use in the field.
Worth pursuing? Depends on your career goals, but incident handlers are in serious demand right now across industries that can't afford downtime or data breaches.
EC-Council 212-89 (ECIH v3) exam overview
What is the ECIH v3 certification?
The EC-Council Certified Incident Handler (ECIH) v3 is basically EC-Council's answer to the growing need for people who can actually handle security incidents when things go sideways. Version 3's a major update, tweaked specifically for the 2024-2026 threat space where ransomware gangs are getting bolder and cloud attacks are everywhere.
This certification validates your skills in managing cybersecurity incidents from the moment you detect something suspicious all the way through post-incident activities like writing reports nobody wants to read but everyone needs. The complete incident handling lifecycle gets covered: preparation, detection, containment, eradication, recovery, and those post-incident activities where you figure out what went wrong and how to prevent repeat disasters.
What makes ECIH v3 different from purely forensic certifications is the focus on real-time response and business continuity. Forensics is cool when you're analyzing a disk image at 2am, but incident handling is about stopping the bleeding right now while keeping the business running. The certification aligns heavily with NIST SP 800-61 and industry best practices, which matters because you're not just learning EC-Council's proprietary methodology. You're learning frameworks that actually matter in the real world.
This cert targets hands-on practitioners, not people who just want theoretical knowledge to pass a test. It fits with job roles including SOC analyst, incident responder, security analyst, and threat hunter positions. If you've already got the Certified Ethical Hacker (CEHv12), ECIH v3 complements it nicely by focusing specifically on defensive operations instead of the offensive side.
Modern threats addressed? Ransomware (obviously), APTs that hide in your network for months, insider threats from that disgruntled admin, and cloud-based attacks that exploit misconfigurations in AWS or Azure. It incorporates SIEM and log analysis for incident response workflows. This is key since you'll be drowning in logs from day one in any SOC role. Without proper analysis skills you're basically useless. The certification also hammers on decision-making under pressure and communication with stakeholders during incidents, because telling your CEO that all the data's encrypted requires a different skillset than running Wireshark.
Actually, one of the most underrated aspects of incident handling is managing your own stress response when alerts start firing at 4am on a Saturday. Nobody talks about that part in the exam blueprint, but it's half the job. You can know every technical detail of ransomware behavior patterns and still freeze when your entire production environment is encrypting in real time.
ECIH v3 gets recognized globally by SOC teams, incident response teams, and organizations building cybersecurity capabilities from scratch or trying to mature their existing programs.
Who should take the 212-89 exam?
SOC analysts seeking to formalize incident response knowledge and advance their careers are prime candidates. You're already dealing with alerts and escalations, so getting certified proves you know what you're doing beyond just following runbooks someone else wrote.
IT security professionals transitioning into dedicated incident response roles should absolutely consider this. System administrators responsible for security incident handling in smaller organizations where you wear seventeen hats will find this particularly valuable. Network security engineers expanding into detection and response capabilities can use ECIH v3 to bridge that gap between preventing attacks and responding when prevention fails (because it always does eventually).
Cybersecurity students pursuing careers in defensive security operations can get a head start with this certification, though you'll get more value from it if you have some real-world experience first. Not to be harsh, but that's just reality. Compliance officers needing to understand incident response requirements and procedures will benefit from understanding what actually happens during an incident, not just what the framework document says should happen.
Penetration testers wanting to understand the defensive perspective and detection mechanisms should consider this. Knowing how blue teams detect your techniques makes you better at red teaming. IT auditors evaluating organizational incident response capabilities need to understand what good looks like, and ECIH v3 provides that framework while also giving you practical insights that purely theoretical knowledge can't deliver. Consultants advising clients on building or improving incident response programs can use this certification to demonstrate expertise. Career changers with IT background moving into cybersecurity incident handling will find it provides structured learning for a complex domain.
Military personnel in cyber defense? Yes. Government personnel? Absolutely. Managed security service provider (MSSP) analysts handling multiple client incidents simultaneously need this. Anyone seeking vendor-neutral recognition (despite EC-Council branding) of IR competency should all consider the 212-89 exam. It's also useful if you're preparing for advanced certifications like GCIH, GCFA, or CISSP concentrations because ECIH v3 builds a solid foundation that those advanced certs expand upon.
Career value and industry recognition
ECIH v3 certification demonstrates practical incident handling capabilities to employers in a way that saying "I've handled incidents" on your resume just doesn't. I've seen it increasingly required or preferred in SOC analyst and incident responder job postings, especially from organizations that take incident response seriously rather than treating it as an afterthought (which happens more than you'd think).
The salary impact's real. Certified incident handlers command a 12-18% premium over non-certified peers with similar experience, though your mileage will vary based on location and organization size. Obviously New York City pays differently than Omaha. More importantly, it opens doors to specialized roles in threat hunting, malware analysis, and forensics that you might not get considered for otherwise.
The certification's valuable for organizations pursuing cyber insurance with incident response requirements. Insurers increasingly want to see that you have trained, certified personnel who can actually respond to incidents effectively, not just someone who Googles solutions during emergencies. It gets recognized in compliance frameworks requiring trained incident response personnel, which matters if you're in healthcare, finance, or other regulated industries where auditors actually check credentials.
ECIH v3 provides common language and methodology for multi-team incident coordination. When everyone's using the same framework and terminology, incidents get resolved faster with less confusion about who's responsible for what. It boosts credibility when communicating with executives during security incidents. Having certifications behind your name makes executives more likely to listen when you're recommending expensive containment actions at 3am, which is unfortunately how corporate politics works.
Career progression support? Definitely. The certification supports movement from tier 1 SOC analyst to senior incident response positions. It's not the only thing you need, but it signals that you've invested in developing IR-specific skills beyond general security knowledge.
Certification positioning in the cybersecurity space
ECIH v3 sits between foundational certifications like Security+ or CySA+ and advanced forensics credentials, carving out its own niche. It's more hands-on and scenario-based than CompTIA Security+ but less technically deep than GIAC GCIH, which dives deeper into forensic artifacts and advanced analysis techniques. Both approaches have value, just depends on your goals.
Organizational incident response matters more here than individual forensic artifacts. You're learning to coordinate response across multiple teams, make containment decisions that balance security with business needs, and manage the entire incident lifecycle. You're not just analyzing a single piece of evidence in isolation like you're solving a CSI episode.
It complements offensive certifications like CEH or OSCP by covering detection and response. If you understand both how to attack systems and how to defend them, you're exponentially more valuable than someone who only knows one side. ECIH v3's a practical alternative to academic incident response courses for working professionals who need certification credit and don't have time for a semester-long university course.
Vendor-neutral despite EC-Council branding? Pretty much. It covers Windows, Linux, and cloud platforms rather than focusing on specific tools, which is smart future-proofing. You'll learn principles that apply regardless of whether your organization uses Splunk or Elastic for SIEM, or CrowdStrike versus Carbon Black for EDR. Tools change, principles don't. The focus on real-world decision-making over pure technical tool mastery means you're learning to think like an incident handler, not just memorize commands.
It's suitable for both enterprise SOC environments with dedicated IR teams and smaller organizations building IR capabilities where one person might be the entire incident response program.
ECIH v3 Exam Details
EC-Council 212-89 (ECIH v3) exam overview
What is the ECIH v3 certification?
EC-Council Certified Incident Handler (ECIH) v3 is EC-Council's incident response cert that tries measuring whether you can think like an analyst when things are on fire. Not a red team trophy. More blue-team muscle memory, honestly. The ECIH v3 exam 212-89 is asking, "Given this situation, what do you do next, and what do you absolutely not do?"
A lot of people study incident response as a list, which makes sense at first, but this exam pushes you toward reasoning instead of pure memorization. That matters when you're dealing with real incidents where you have to weigh why you isolate a host now versus later, why you collect volatile data first before it evaporates, why you escalate to legal or HR at specific trigger points, and how all those decisions ripple outward when you're under time pressure and everyone's watching. Also, the exam writers seem to love throwing in scenarios where multiple answers look correct but only one accounts for evidence preservation. That's the vibe.
Who should take the 212-89 exam?
SOC analysts. Junior incident responders. Help desk folks trying to break into security, plus anyone who keeps getting pulled into "can you look at this weird alert" and wants actual credibility behind their decisions.
Managers can take it too, but the questions read like you're on the keyboard making calls under time pressure, not writing a policy doc in a calm meeting next Thursday. Some of it's governance. Most? Decisions.
ECIH v3 exam details (212-89)
Exam format, question types, and duration
The EC-Council 212-89 exam is straightforward multiple-choice. 50 questions total. You get 2 hours (120 minutes). No hands-on lab component inside the exam itself, which surprises people who are used to performance-based testing, though it kind of makes sense because EC-Council's trying to standardize delivery across online proctoring and test centers.
Some questions? Direct knowledge checks. Define this. Identify that. Quick wins. Others are scenario-based questions that force you to read a mini incident story, then pick the best next step or the best containment approach. Those are the ones that eat time because they're written to feel like real-world messiness, complete with incomplete information and competing priorities.
Expect log excerpts. Short alert samples. Timelines. Little snippets that smell like SIEM output, firewall denies, EDR detections, or "user reported a pop-up, then X happened, then Y happened." You won't be doing packet carving, but you'll need SIEM and log analysis for incident response basics, plus enough intuition to avoid doing something that trashes evidence or makes containment impossible.
The exam pulls from all domains of the ECIH v3 exam objectives, but it's weighted toward practical incident handling decisions rather than pure memorization. You can memorize terms all day and still miss questions where the real test is sequencing, prioritization, and scoping under constraints. Limited staff, limited time, conflicting stakeholders, and suddenly the scenario says "CEO laptop," so now the risk math changes entirely.
Communication and escalation show up too. Who do you notify. When do you involve legal. What do you say to users. What do you document. That's the part a lot of technical folks roll their eyes at until they're in an actual incident and suddenly it matters more than anything.
Short sentences now. Read carefully. Manage time.
Exam cost (voucher/training considerations)
Pricing's the part nobody wants to talk about, because it varies and it's rarely "cheap." Voucher-only pricing's usually about $450 to $550 USD, depending on region and promotions. The official training bundle (courseware plus exam) commonly lands in the $2,500 to $3,500 USD range.
Self-study people can buy a voucher through EC-Council or authorized partners. That's often the route if your employer's paying for exam only and you're bringing your own ECIH 212-89 study guide plan. Corporate teams can negotiate training packages for multiple employees, and that can change the math a lot, especially if leadership wants consistent incident handling playbooks across the group.
Retake vouchers exist, often cheaper when bundled up front. Not gonna lie, if you're not 100% sure on the content, that bundle can be less stressful than paying full price again later. Also watch for discounts around security awareness events or conferences. They do happen. Government and military pricing can apply through specific EC-Council programs, and student discounts may apply if you can verify enrollment.
Total cost of ownership's the real number. Voucher plus study materials plus a decent ECIH v3 practice test source plus maybe a retake. Add it up before you commit, because the surprise expenses are what kill motivation.
Passing score (what to expect and why it can vary)
As of 2024 through 2026, the passing expectation's commonly stated as 70%, which is 35 out of 50 correct, for the ECIH v3 / 212-89 exam. EC-Council uses scaled scoring, so your reported score may not map perfectly to a raw percentage in the way people expect. That's why two candidates can feel like they got similar numbers right but see slightly different-looking results.
No partial credit. Each multiple-choice question's right or wrong. You get a pass/fail notification immediately after finishing, and score reports typically show performance by domain, which's actually useful if you're planning a retake because it tells you where you bled points.
Passing is passing. There's no "with honors" ECIH certificate. A 70% and a 100% look the same on paper, which's how most certs work, but people still stress about perfection. Don't. Focus on being consistently correct on decision-making questions, because that's where the exam tries to separate "read the slides" from "can handle an incident."
Where to schedule the exam (proctoring/testing options)
You can take the exam through the ECC exam portal with online proctoring, or schedule in-person via Pearson VUE testing centers in many countries. Online proctoring needs a webcam, microphone, stable internet, and a quiet private room. They'll usually make you do a system check first, and you should take that seriously because nothing's worse than burning your exam day troubleshooting browser permissions.
Testing centers are boring, controlled, and honestly sometimes better if your home setup's unpredictable. No roommates walking in. No flaky Wi-Fi. Just you, the clock, and the questions.
Schedule 2 to 3 weeks ahead if you want a specific time slot, especially if you're aiming for weekends. Online proctoring can be close to 24/7 depending on region, but you still usually pick a scheduled start time. Rescheduling policies commonly require 24 to 48 hours notice to avoid fees.
Bring the right ID. Government-issued photo ID, and your registration name has to match. Prohibited items are the usual: notes, phones, smart watches, reference materials. Scratch paper rules vary. Some online sessions give you a digital whiteboard instead, which's.. fine. Accessibility accommodations exist, but request them early with documentation.
ECIH v3 exam objectives (what you must know)
Incident response fundamentals and lifecycle
You need the incident handling lifecycle cold: preparation, detection, containment, eradication, recovery, post-incident. Not as buzzwords. As actions. What happens in each phase. What artifacts matter. What mistakes cause re-infection or destroy evidence.
Preparation: policies, playbooks, and readiness
Policies, playbooks, asset inventory, logging standards, and who's got authority to pull the plug. This's where compliance questions show up too, because incident response lives inside legal and regulatory constraints whether you like it or not.
Detection and triage: alerts, logs, and SIEM basics
This's the SOC part. SOC incident triage and escalation logic. Validate alerts. Reduce false positives. Decide severity. Scope affected users and systems. You'll see questions that are basically "is this an incident yet" and "who do you notify first."
Containment strategies (short-term vs long-term)
Containment's where the exam tests judgment. Sometimes you isolate. Sometimes you monitor quietly to understand the spread. Sometimes you block at the firewall. Sometimes you disable accounts. The "best" answer depends on business impact and evidence preservation, and the exam likes to make those tradeoffs explicit.
Eradication and recovery: remediation and validation
Patch, remove persistence, rotate credentials, clean or reimage, validate with scans and monitoring. Then confirm normal operations. Recovery isn't "system's back up." Recovery's "system's back up and not still compromised."
Post-incident activity: reporting, lessons learned, and improvement
After-action reports, root cause, metrics, and updating playbooks. Documentation. Who gets the report. What gets shared. What gets retained.
Evidence handling and forensics fundamentals
You don't need to be a full-time examiner, but digital forensics basics for incident response matter. Chain of custody. Volatile data first. Hashing. Proper storage. What not to do on a suspected compromised host if you might need the evidence later.
Malware and attack techniques relevant to incident handling
You're expected to recognize patterns and respond. Malware analysis fundamentals at the "triage analyst" level, like identifying indicators, understanding persistence concepts, and knowing when to detonate in a safe environment versus when to escalate.
Prerequisites and recommended experience
Official prerequisites (if any)
EC-Council often lists recommended knowledge rather than strict prerequisites. You can sit for the exam without proving experience in many cases, but check the current policy when you buy the voucher.
Recommended background (networking, Windows/Linux, security fundamentals)
TCP/IP basics. Windows event logs. Linux auth logs. Common ports and services. Basic Active Directory concepts. If those are weak, you'll spend too long decoding questions instead of answering them.
Who should consider training before attempting the exam?
If you've never worked tickets in a SOC, never written an incident timeline, and never had to decide "contain now or observe," the ECIH v3 training course can help, but it's expensive. A cheaper path's pairing a solid study guide with hands-on home labs.
ECIH v3 difficulty and pass rate expectations
How difficult is ECIH v3 for beginners vs experienced analysts?
Beginners struggle with prioritization. Experienced analysts struggle less, because they've lived the tradeoffs. The exam isn't trying to trick you with obscure acronyms. It's trying to see if you'll do something reckless like wiping a machine before collecting evidence.
Common challenge areas (triage, scoping, containment decisions)
Triage severity. Scoping beyond the first alert. Containment choices that balance business uptime and risk. Also communications. People ignore that until they fail questions about escalation paths and stakeholder updates.
How it compares to similar certifications (role-based IR focus)
Compared to Security+, ECIH's more incident-response specific and more scenario-heavy. Compared to CEH, it's less about "how to attack" and more about "how to respond when attacked." Difficulty depends on your day job, honestly.
Best study materials for ECIH v3 (212-89)
Official EC-Council courseware and labs
Official materials map closely to objectives. If work's paying, fine. If you're paying, you need to decide if that price tag beats self-study plus practice questions.
Recommended incident response books and references
NIST-style incident response guidance's still useful. So are practical IR handbooks that focus on containment and evidence handling. Keep references focused. Too many sources wastes time.
Hands-on practice: home lab ideas (logs, endpoints, basic forensics)
Spin up a small SIEM-ish setup. Collect Windows logs. Generate a few failed logons. Practice building a timeline. Do basic disk image hashing. Review a fake phishing incident and write the steps you'd take. Simple. Repetitive. That's what makes it stick.
Study plan (2 to 6 weeks / 6 to 10 weeks options)
If you already work in a SOC, 2 to 6 weeks with focused review and practice tests is realistic. If you're new, 6 to 10 weeks gives you time to build intuition, not just memorize terms.
ECIH v3 practice tests and exam prep strategy
What to look for in quality practice tests
You want scenario-heavy questions, not trivia dumps. Explanations matter more than the score. If the practice test can't explain why the other options are wrong, it's not helping you learn judgment.
Practice test schedule (diagnostic, targeted drills, full mocks)
Take one diagnostic early. Then drill weak domains. Then do at least one full timed mock to practice pacing, because 50 questions in 120 minutes sounds easy until you hit long scenarios and start rereading logs.
Exam-day strategy (time management, eliminating distractors)
Don't camp on one question. Mark it and move. Read the last line first sometimes, because it tells you what the question actually wants. Eliminate answers that violate evidence handling or escalation rules. The "best" answer's usually the one that keeps options open and preserves proof.
ECIH v3 renewal and certification maintenance
Validity period and renewal requirements
EC-Council certs typically run on a renewal cycle with continuing education expectations. Verify the current ECIH policy when you pass, because programs change.
Continuing education (ECE/CE credits) and fees
You'll usually need ECE credits and an annual fee. Training, conferences, webinars, and relevant work activities can count, but you need documentation.
Audit-proof documentation tips for renewals
Save certificates. Keep attendance emails. Track dates and hours. Write short notes about what you learned. Do it as you go, because trying to reconstruct a year of learning the night before renewal's pain.
ECIH v3 FAQ
Cost, passing score, and retake questions
How much does the ECIH v3 (212-89) exam cost? Typically $450 to $550 for voucher-only, with bundles far higher. What's the passing score for the EC-Council 212-89 exam? Expect 70% (35/50) as a practical target, with scaled scoring on the report.
Study materials and practice tests recommendations
What are the best study materials and practice tests for ECIH v3? Start with the official objectives, a focused ECIH 212-89 study guide approach, and at least one reputable ECIH v3 practice test source with explanations.
Objectives and prerequisites recap
Is ECIH v3 harder than CEH or Security+? Harder than Security+ for IR decision-making, different from CEH because it's response-focused. The thing is, official prerequisites are usually recommendations, but real-world familiarity helps a lot.
Renewal steps summary
How do I renew the ECIH certification and how long's it valid? Expect a renewal cycle with ECE credits plus fees, and keep documentation ready for audits as part of ECIH certification renewal.
ECIH v3 Exam Objectives (What You Must Know)
Incident response fundamentals and lifecycle
Okay, so here's the thing: before you even crack open that ECIH v3 exam 212-89, you've gotta understand what incident response actually is. Honestly, tons of people mix up security events with genuine incidents, and it's not the same thing at all. An event? That's just something happening on your network. Maybe someone fat-fingered their password three times, whatever, no big deal. But an incident is when something's actually threatening your confidentiality, integrity, or availability, and the exam'll definitely test whether you can spot that difference because, I mean, that's where real-world IR begins.
NIST SP 800-61 is your go-to resource. The framework splits incident response into six phases you'll need backwards and forwards: preparation, then identification and detection, containment, eradication, recovery, and post-incident activity last. These aren't just boxes you check off theoretically. They're really how mature organizations handle breaches and attacks when everything hits the fan. The ECIH v3 exam objectives hammer this lifecycle relentlessly since it's the foundation for literally everything else.
You'll also need to grasp how incident handling fits into security operations more broadly. It doesn't exist in a vacuum. IR teams collaborate with SOC analysts, threat intel folks, IT operations, legal departments, sometimes even PR. The exam covers incident categorization systems too: how you classify severity based on impact, which systems got affected, what data types are involved. Ransomware hit your payroll system? Critical. Some random malware on a test machine? Probably low priority, honestly.
Chain of custody's another area they test hard. If you're collecting evidence that might end up in court or support terminating someone's employment, you'd better document who touched what and exactly when. The exam wants you knowing evidence handling basics even if you're not planning on becoming a full-time forensics person. It's about preserving your options while dealing with the immediate crisis, you know?
Compliance drivers matter. A lot. GDPR, HIPAA, PCI-DSS.. these regulations don't just suggest having an incident response plan, they flat-out require it, and they set timelines for breach notification that can make or break your organization's legal standing. The 212-89 exam includes questions about these regulatory requirements since real incident handlers need knowing when the clock's ticking on notifications.
Preparation: policies, playbooks, and readiness
Preparation's where most organizations completely fail. And where the exam spends serious time. You need documented policies defining what incidents are, who responds, what authorities they've got. But policies alone? Useless. You need playbooks walking through specific scenarios step by step. The exam covers creating effective playbooks for common incidents like phishing campaigns, ransomware, data exfiltration, insider threats.
Building your IR team is huge. Training them too. The exam tests different roles. Incident manager coordinates everything, analysts dig into technical details, communications handles stakeholder updates, legal advises on regulatory and litigation risks. Everyone needs knowing their lane before stuff hits the fan. I've seen organizations where nobody knows who's supposed to make the call on whether to shut down production systems during an active breach, and honestly? That's a recipe for absolute disaster.
Tool selection comes up. You'll see questions about SIEM platforms, EDR solutions, forensic toolkits, ticketing systems for tracking incidents. The exam expects understanding what each tool category does and why you need it. Asset inventory's another prep requirement. How can you protect critical systems if you don't even know where they are? Establishing baselines for normal behavior's equally important since you can't spot anomalies without knowing what normal looks like.
Tabletop exercises and simulations are tested concepts. These aren't just feel-good exercises. They're how you validate that your playbooks actually work and your team knows what to do under pressure. The ECIH v3 certification wants you understanding how to design and run these exercises properly.
Detection and triage: alerts, logs, and SIEM basics
Detection's where it gets real.
The exam covers log sources extensively. Firewall logs, IDS/IPS alerts, endpoint logs, authentication logs, application logs. You need knowing what each source can tell you and what it can't. SIEM platforms correlate these disparate sources to surface potential incidents, and the 212-89 exam tests your understanding of how SIEM and log analysis for incident response workflows actually function in practice.
Alert triage separates functional IR from chaos. Not every alert's an incident. Many are false positives, which is frustrating but reality. The exam covers the triage process: initial assessment, severity assignment, false positive filtering, escalation criteria. When does an alert get kicked up from tier 1 SOC to the actual IR team? You gotta know.
Indicators of compromise are everywhere in exam content. Can you spot IOCs in logs? Extract them from network traffic? EDR alerts? The exam scenario questions often present log snippets or alert details and ask you determining what's actually happening, which (honestly, the thing is) requires understanding context, not just memorizing patterns. Timeline construction from multiple sources is another tested skill: you need piecing together what happened when and in what order.
SOC incident triage and escalation procedures tie into this heavily. The exam expects understanding the workflow from initial detection through escalation to full incident response. User and entity behavior analytics (UEBA) gets mentioned too, especially for detecting insider threats or compromised credentials that don't trigger traditional signature-based tools.
Quick tangent: I once worked an incident where the SIEM missed everything for three days straight because someone had misconfigured the correlation rules after a "routine update." The attacker was in there moving laterally the whole time, and we only caught them because a developer noticed weird processes on his workstation. That's why baselines and multiple detection layers matter so much. Anyway.
Containment strategies (short-term vs long-term)
Containment's where you stop the bleeding. The exam distinguishes between short-term and long-term approaches. Short-term containment? Immediate damage control. Disconnect that ransomware-infected server right now before it encrypts the whole file share. Long-term containment's about sustainable controls you can maintain while planning eradication and recovery. Maybe you segment the compromised network zone and implement enhanced monitoring instead of just yanking cables.
The exam covers specific containment techniques: network isolation, account disablement, credential resets, blocking malicious IPs and domains at your perimeter and endpoints. But here's where it gets interesting. You also need understanding the decision factors. What's the business impact of your containment actions? Are you preserving evidence for later forensics? Will your containment actions tip off the attacker that you're onto them? These aren't simple yes-no questions.
Containment for specific incident types gets tested. Ransomware containment looks different from data exfiltration containment, which looks different from insider threat containment. The ECIH v3 practice test materials focus heavily on scenario-based questions where you need picking the appropriate containment strategy given specific circumstances.
Balancing containment with business continuity's a recurring theme. You can't just shut down everything and call it contained. The business still needs operating. Legal and regulatory considerations matter too. Some jurisdictions have rules about when you can and can't disconnect systems during an investigation.
Eradication and recovery: remediation and validation
Once you've contained the incident, you need actually removing the threat and getting back to normal operations. The exam tests your knowledge of eradication techniques: removing malware and backdoors, eliminating attacker persistence mechanisms, patching the vulnerabilities they exploited to get in. You might need rebuilding compromised systems from clean backups or known-good images. Credential rotation across affected accounts is standard procedure.
What the exam really focuses on? Validation. How do you know eradication was actually successful? You can't just assume the malware's gone because you ran an antivirus scan. That's naive. You need to scan, monitor, threat hunt for signs that persistence mechanisms remain. The exam covers this validation process extensively, and it's honestly where a lot of real-world IR teams struggle.
Recovery prioritization based on business criticality comes up in scenario questions. You can't bring everything back online simultaneously. Which systems get restored first? How do you test them before returning to production? The exam wants you understanding gradual service restoration with enhanced monitoring to catch any signs of recurrence.
Documentation throughout eradication and recovery's tested too. You need records of what you did, when, and why. This supports your post-incident review and helps if you face regulatory scrutiny or litigation later. If you're preparing with resources like the 212-89 Practice Exam Questions Pack, you'll see lots of questions about what should be documented at each phase.
Post-incident activity: reporting, lessons learned, and improvement
Post-incident activity's where learning happens. And the exam dedicates serious coverage to this phase. You need producing thorough incident reports for different audiences. Technical details for the IR team, business impact for management, compliance specifics for legal and regulatory bodies. The exam tests understanding what each stakeholder needs knowing.
Lessons learned sessions are mandatory in mature IR programs. The exam covers how to conduct effective post-mortem meetings, how to identify root causes without blame (which is harder than it sounds), how to extract actionable improvements from the incident. What process gaps did the incident reveal? What tools failed or were missing? What training would've helped?
Metrics collection's another exam topic. Time to detect, time to contain, time to recover, total business impact. These measurements help you improve over time and demonstrate IR maturity. Regulatory notification timelines get tested too. GDPR gives you 72 hours in some cases. Can you meet that? The exam wants you knowing these requirements cold.
Evidence preservation for potential legal proceedings is covered. Just because you've recovered doesn't mean you can delete everything. You might need that evidence months or years later. Threat intelligence sharing's encouraged too: anonymized IOCs and TTPs can help the broader community defend against the same attacks.
Evidence handling and forensics fundamentals
You don't need being a full forensics expert for the ECIH v3 exam, but you need digital forensics basics for incident response. Chain of custody documentation's critical. Every person who touches evidence must be documented with times and reasons. Evidence integrity must be preserved through proper handling and cryptographic hashing.
The exam covers collection priorities. Volatile data like memory needs capturing before you pull the power plug. Once it's gone, it's gone. Non-volatile data on disk can wait. Network packet captures might be your only evidence of lateral movement or data exfiltration, so you need knowing when to do forensic imaging versus logical copies, and how to collect evidence from Windows, Linux, and increasingly cloud environments.
Legal considerations come up frequently. What makes evidence admissible in court? What privacy concerns apply? When should you involve law enforcement and what should you provide them? The exam doesn't expect you being a lawyer, but you need understanding the basics. I mean, you can't just hand over everything without thinking about implications.
Remote evidence collection in distributed environments is a modern challenge the exam addresses. Not every system's sitting in your datacenter where you can physically access it. Cloud forensics introduces its own complications around data location, provider cooperation, and chain of custody maintenance.
Malware and attack techniques relevant to incident handling
The final major objective area covers malware analysis fundamentals and attack techniques. You need understanding common malware types: ransomware, trojans, rootkits, worms, spyware. What're the indicators of infection? How does each type behave? The exam includes questions about static versus dynamic malware analysis approaches, though you won't need doing deep reverse engineering. Thank goodness.
Attack vectors are tested extensively. Phishing, drive-by downloads, supply chain compromises, removable media. How do attackers get in initially? The MITRE ATT&CK framework shows up in exam objectives as a way to understand attacker tactics, techniques, and procedures. You should be familiar with how to map observed activity to ATT&CK techniques, which is super useful in real-world work too.
Lateral movement detection's critical. Once attackers compromise one system, how do they spread? What does lateral movement look like in logs and network traffic? Data exfiltration methods and detection techniques get covered. Persistence mechanisms, privilege escalation, command and control communications.. all tested topics that come up constantly in actual incidents.
Ransomware deserves special attention since it's so prevalent. The exam covers ransomware-specific response considerations, including the controversial question of whether to pay (spoiler: usually don't, but it's complicated). APT characteristics and how to respond to sophisticated, persistent attackers appear in more advanced questions. Insider threat indicators and investigation techniques round out this section.
If you're serious about passing the EC-Council 212-89 exam, you need hands-on practice beyond just reading. Honestly, concepts stick way better when you've actually done them. Setting up a home lab with log sources, endpoints, and basic forensic tools helps massively. The 212-89 Practice Exam Questions Pack gives you scenario-based questions similar to what you'll face on exam day, which is key for this practical certification.
The ECIH v3 exam objectives are thorough but focused on practical incident handling skills. Unlike broader certifications like Certified Ethical Hacker Exam (CEHv12) which covers offensive techniques, or Certified SOC Analyst (CSA) which focuses on monitoring and detection, the ECIH v3 certification zeroes in specifically on the incident response lifecycle. It complements forensics-focused credentials like Computer Hacking Forensic Investigator (CHFI-v10) by emphasizing the broader IR process rather than deep technical analysis.
The exam isn't easy. Let's be real. It requires understanding both theory and practical application across all IR phases. But if you're working toward a SOC or IR role, the knowledge directly transfers to real-world work. Master these objectives and you're not just passing an exam. You're building skills that organizations desperately need right now.
Prerequisites and Recommended Experience
Prerequisites and recommended experience
Look, people stress way too hard about prerequisites for the ECIH v3 exam 212-89. Honestly, I get the panic. Lots of certs force you through obstacle courses, demand training receipts, make you submit applications, or want resumes that look like you've survived actual cyber warfare. This one? Way simpler.
Zero gatekeeping. No mandatory class. No cert stack requirement. You. The exam. That's it.
The thing is, this simplicity cuts both ways. It's amazing for self-motivated learners who can sprint through material, but it's also kinda dangerous because incident handling isn't some "memorize definitions and wing it" subject, and the EC-Council 212-89 exam expects you to think like someone who's actually dealt with live alerts, compromised endpoints, and evidence that makes no sense at three in the morning.
Official prerequisites (if any)
So officially? EC-Council doesn't mandate formal prerequisites for the EC-Council Certified Incident Handler (ECIH) v3 exam. There's no work experience checkbox, no degree gate, no prerequisite cert ladder like you'd see with vendor-specific advanced tracks. You can purchase a voucher and book your test slot without proving anything beyond payment ability.
Training isn't required either. You don't need to complete the ECIH v3 training course before buying an exam voucher. Self-study folks can grab vouchers directly without enrolling in anything official. That's huge if your employer won't fund courseware, or if you're someone who learns better building labs and reading actual sources than sitting through structured classes.
Worth mentioning: there's zero "US versus international" difference. International candidates face identical prerequisites as US-based test-takers, because the prerequisite list is basically nonexistent. Education? Same story. No high school requirement. No associate degree checkbox. No bachelor's demand. Open registration, period.
Retakes follow simple rules too. Retake attempts require no additional prerequisites beyond the retake fee and whatever scheduling policies exist currently. No extra forms, no "remedial training" mandate, no waiting period where you submit study proof. Pay. Reschedule. Try again.
Now, EC-Council does recommend certain experience levels, and those recommendations exist for solid reasons. You can attempt the exam immediately after registration and payment, but passing is an entirely different conversation than simply being allowed to sit down.
Recommended background (networking, Windows/Linux, security fundamentals)
If you want the "I'm probably ready" baseline, I'd say 1 to 2 years in IT security, SOC operations, or system administration. Not because fancy job titles matter, but because incident response work is this massive pile of micro-skills that only click after you've touched actual systems and dealt with real constraints like "production cannot go down" and "nobody's documented what normal traffic even looks like anymore."
A big chunk of the ECIH v3 exam objectives assumes networking knowledge beyond rote memorization. You should understand TCP/IP basics, common ports and protocols, network architecture. Not just "HTTP runs on port 80" trivia, but actual ability to reason through traffic patterns when you're doing SOC incident triage and escalation and you've gotta decide whether something's scanning noise, misconfiguration, or active compromise happening right now.
Windows knowledge? Big deal. Working knowledge of Windows operating systems matters here, particularly Active Directory basics, event logs, registry stuff. I mean, people wildly underestimate how much IR work is staring at Windows logs and questioning your life choices. You should know where authentication events live, how to interpret common log fields, and what "normal admin activity" looks like in your mental model so abnormal stuff jumps out immediately.
Linux and Unix familiarity forms the other half. You don't need kernel developer skills, but you should feel comfortable in command line environments, understand file systems and permissions, recognize common services, know typical log locations. If you've never tailed a log, grepped for an IP address, or checked running processes on a potentially compromised server, the exam content will feel weirdly abstract even when you can recite textbook definitions.
Security basics are non-negotiable. You should already feel comfortable with concepts like CIA triad, defense in depth, least privilege. These aren't "intro to security" filler material. They appear in decision-making questions where the correct answer balances containment against business continuity, or chooses an access control fix that doesn't create a worse outage than the actual incident itself. Incident handling is applied security philosophy under brutal time pressure. Messy. Real. Ugly.
Tool exposure helps a ton. You don't need wizard-level expertise, but you should've seen firewalls, IDS/IPS, antivirus or EDR, SIEM platforms in actual environments. Tons of incident response involves translating what tools are screaming about into "what actually happened," and that translation depends on having at least some basic mental model of how those tools collect signals and how they fail spectacularly. False positives exist. Blind spots exist. Misconfigured log sources exist everywhere. All that feeds directly into SIEM and log analysis for incident response.
Log analysis is its own distinct skill and appears constantly. If you've done even basic pattern recognition in logs, you're miles ahead. Think repeated failed logins, weird user agents, PowerShell execution artifacts, suspicious parent-child process relationships, lateral movement hints, bizarre DNS lookups. You're not expected to be a full-time threat hunter, but you should read logs without feeling like you're deciphering alien poetry written backwards.
You should also grasp basic malware types and infection vectors. I'm not saying you need reverse engineering skills, but you should know how phishing, macro malware, droppers, credential theft, persistence tricks typically work, and how those choices alter response steps. This is where malware analysis fundamentals and digital forensics basics for incident response start mattering, because the exam isn't just "define ransomware," it's "what do you do next, what evidence gets preserved, what gets isolated first."
Ticketing and documentation experience? Wildly underrated and relevant. Incident response is paperwork plus adrenaline in equal measure. Experience with ticketing systems and incident documentation helps because you're expected to think in timelines, ownership, escalation paths, clear reporting. If you've never written an incident summary for non-technical stakeholders, you might struggle with questions about reporting, post-incident actions, lessons learned processes.
Organizational context helps too. Understanding how IT infrastructure supports business operations makes answering "best" response questions easier, because the best answer often depends on impact assessment. A containment action that's technically perfect but kills revenue systems? Might not be the right move at that moment. The exam tends to reward practical judgment, not just textbook purity or theoretical perfection.
Framework familiarity is useful, though not mandatory. Exposure to NIST guidance, ISO 27001 concepts, CIS Controls helps ground the incident handling lifecycle in real-world process expectations. You don't need memorized clause numbers. You do need understanding "good process" looks like: preparation, detection, containment, eradication, recovery, post-incident improvement cycles.
Compliance awareness follows similar logic. GDPR, HIPAA, PCI-DSS basics appear as "you should understand why evidence handling and reporting timelines matter," not as some legal exam. If you've ever asked "do we legally have to notify someone," you're already thinking in the right direction for these questions.
Cloud basics are becoming table stakes honestly. You don't need deep AWS forensics expertise, but you should understand cloud service models, shared responsibility concepts, the kinds of logs and identity controls you'd examine in AWS, Azure, GCP environments. Incidents don't politely stay on-premises anymore. They spread into identity systems, SaaS platforms, API logs frighteningly fast.
I had a colleague once who thought cloud IR was "basically the same thing" until he tried tracking lateral movement through federated identity systems and temporary credentials that expired before he could even pivot to the second account. That humbled him fast.
Hands-on command-line troubleshooting is the glue skill. Windows and Linux both. Basic commands. Quick checks. Fast validation. Because incident handling never happens with perfect information, and the exam pokes at the idea that you should validate, scope, confirm before declaring victory too early.
Who should consider training before attempting the exam?
Some people should do training first. Not because EC-Council forces it, but because it reduces risk and wasted time, and the how to pass ECIH v3 conversation changes dramatically depending on what you've actually done in real job environments.
If you're brand new to security? Training's the safer bet, honestly. If your background is mostly help desk and you've never worked a live alert, never touched a SIEM, never had to preserve evidence while everyone in Slack is panicking, course structure can help connect dots that self-study might leave floating as isolated random facts. Same applies if you've learned security through pure theory but haven't built the muscle memory of triage decisions under pressure.
Also, if you're switching domains, training helps. Maybe you're a network engineer who knows packets cold but not endpoint artifacts. Or you're a sysadmin who knows Windows internals deeply but hasn't done formal incident response workflows ever. The exam expects you to blend those worlds without thinking twice, and a solid ECIH 212-89 study guide plus labs can get you there, but official material can reduce "what am I supposed to focus on" anxiety.
Another group that should consider training: anyone who struggles creating hands-on practice environments. If you don't have a home lab plan, zero access to logs, no safe way to simulate incidents, you'll end up reading about response steps without ever feeling the friction that makes them stick in memory. That's where structured labs help. You get repetition. Workflow practice. The habit of documenting what you did.
And look, some folks just test better with guided paths. If you know you need deadlines, checklists, defined scope, training can keep you from spiraling into infinite prep mode. The exam is broad enough that it's ridiculously easy to over-study the wrong things. A focused plan plus a decent ECIH v3 practice test strategy can keep you honest and on track.
On the flip side, if you already work in a SOC, do incident triage weekly, can talk through containment tradeoffs without Googling anything, you can probably self-study fine. Grab the objectives, map them to what you do daily, patch the gaps, then hammer practice questions until you stop missing the same recurring themes. Training becomes optional polish at that point, not life support.
One last thing: don't rush it. Pass it clean on first attempt.
Even though formal prerequisites don't exist, treat this exam like role validation. If you can explain what you'd do, what you'd collect, what you'd isolate, how you'd communicate it under pressure, you're in solid shape. If you can't? Training or more hands-on time will save you money and frustration, and it'll make the cert actually mean something real when you put it on your resume next to "incident handler."
Conclusion
Wrapping up your ECIH v3 path
Real talk? The EC-Council 212-89 exam isn't some cakewalk, but it's also not engineered to wreck you completely. I mean, if you've logged actual hours working incidents, or at minimum built that muscle memory through labs and practice sessions, you're already miles ahead of most candidates who just memorize slide decks and call it prep. The ECIH v3 exam objectives cover everything from the incident handling lifecycle to malware analysis fundamentals, and that's precisely what gives this cert its street cred. It's practical stuff. You're not just regurgitating trivia about protocols. You're making judgment calls about containment strategies and evidence handling that actually mirror real SOC work.
Honestly? The biggest screwup I see people make is approaching this like some multiple-choice game instead of a competency check. Sure, you need to know your SIEM and log analysis for incident response inside out, but you also need to grasp why you'd escalate one alert and dismiss another during SOC incident triage and escalation. That judgment call stuff? That's where the exam ambushes you, no question. Not memorizing the incident response lifecycle stages. Understanding what goes sideways when you skip a step or misidentify the scope. Not gonna sugarcoat it, that's where a solid ECIH 212-89 study guide becomes your lifeline, especially one that breaks down the reasoning behind answers instead of just spitting out facts.
I remember back when I was cramming for my first IR cert, I spent three days straight on malware analysis and basically ignored the post-incident sections. Figured I'd wing it. Bad move. Missed two questions on lessons-learned documentation that would've been layups if I'd just read the material.
Still on the fence about readiness? Here's my honest take: run through at least three full-length practice exams before you schedule. Track weak spots religiously. Is it digital forensics basics for incident response? Containment decisions? Whatever's tripping you up, drill it until it clicks hard. The how to pass ECIH v3 formula isn't exactly rocket science. It's repetition combined with real-world context. And yeah, definitely budget serious time for those post-incident activity questions because they absolutely love testing whether you understand lessons-learned processes and reporting chains.
For anyone hunting quality prep material, the 212-89 Practice Exam Questions Pack at /eccouncil-dumps/212-89/ is honestly one of the better resources I've stumbled across. The questions mirror the actual exam's decision-based style, and (wait, this is key) the explanations don't just hand you the right answer. They walk you through why the wrong ones crash and burn in real scenarios. Pair that with hands-on lab work. Build a basic malware analysis sandbox, practice log correlation, whatever gets your hands dirty. That setup will get you ready to not just pass but actually use this cert.
The EC-Council Certified Incident Handler (ECIH) v3 credential carries serious weight in SOC and IR roles, but only if you earn it the legit way. Put in the work now, and three months from now you'll be the one fielding incidents instead of just reading about them. You've got this. Just don't skip the practice tests.
Show less info
Comments
Hot Exams
Related Exams
ECCouncil Computer Hacking Forensic Investigator
Computer Hacking Forensic Investigator (CHFI-v10)
Disaster Recovery Professional Practice Test
EC-Council Certified Security Specialist (ECSS) v10
Certified Ethical Hacker CEH v11
Computer Hacking Forensic Investigator (v9)
Certified SOC Analyst (CSA)
EC Council Certified Incident Handler (ECIH v3)
Certified Ethical Hacker Exam
EC-Council Certified Security Analyst (ECSA)
Certified Ethical Hacker Exam (CEHv12)
Computer Hacking Forensic Investigator
Ethical Hacking and Countermeasures V8
EC-Council Certified CISO (CCISO)
Certified Threat Intelligence Analyst (CTIA)
Certified EC-Council Instructor (CEI)
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.