EC-Council 412-79 (ECSA) Certification Overview
Look, here's the deal.
The EC-Council Certified Security Analyst (ECSA) credential is a pretty solid step up from basic ethical hacking certifications if you're trying to prove you've got actual penetration testing chops. The 412-79 exam? That's what stands between you and this designation, and the thing is, it's about knowing tools. You've gotta demonstrate you understand the methodology behind security assessments, the documentation requirements, and how to communicate findings in ways that actually make sense to stakeholders who don't live and breathe InfoSec.
Why it matters.
Lots of folks grab their CEH and think they're done. ECSA digs deeper into the analytical side. Think thorough reporting, legal considerations, and how you'd structure a real-world penetration test from scoping through remediation verification. It's more hands-on, honestly. More about what you'd actually do in the field versus what looks good on a course syllabus.
The exam itself? Tough but fair. You're expected to know vulnerability assessment frameworks and advanced scanning techniques. But here's what catches people off guard: you need to actually write a penetration testing report that executives and technical teams can both use. That documentation piece trips people up more than the technical stuff sometimes. Wasn't expecting that when I first looked into it, but it makes sense given what clients actually need. I've seen guys who can exploit a buffer overflow in their sleep but can't explain the business impact in plain English. That won't fly here.
Mixed feelings here: The certification definitely opens doors, especially in consulting or roles requiring formal pen testing. But whether it's worth the investment depends on where you're at career-wise and what credentials you've already stacked up.
What this certification actually means for your career
Here's the deal. I've watched way too many security professionals grab their Certified Ethical Hacker Exam (CEHv12) and then just stall out, wondering where to go next. The EC-Council 412-79 ECSA certification? It's that next logical step, and honestly it's where things get real.
CEH gives you solid foundation knowledge across maybe 20 different security domains, which is great for breadth. The EC-Council Certified Security Analyst credential, though, zeroes in on something way more focused: actually conducting professional penetration tests that organizations would pay real money for. Documented properly. Following methodologies that hold up when someone checks your work.
This isn't just wall decoration. The ECSA v10 exam tests whether you can follow methodical approaches to security testing, document findings like an actual consultant would, and communicate technical risks to executives who don't live in terminal windows all day. Anyone can run Metasploit, right? But explaining to a CISO why that SQL injection you discovered actually matters and what they should do about it? That's the difference we're talking about here.
The certification focuses heavily on penetration testing methodology and application security analysis. Frameworks and processes mirroring what actual security consulting firms use when they're hired to test enterprise networks. Not gonna lie, this makes you way more employable than just having tool knowledge. I knew a guy who spent six months learning every Kali tool by heart but couldn't write a finding that didn't sound like it came straight from a vulnerability scanner output. That's useless to clients.
Who actually benefits from taking ECSA
Security analysts. Ones who've been working SOC shifts for a couple years and want to move into offensive security roles, that's the sweet spot. Penetration testers already doing the work but lacking formal credentials to back up their skills also benefit massively. Vulnerability assessors needing to level up their documentation game for compliance requirements? Absolutely.
Got 2-3 years hands-on security experience? Tired of just monitoring alerts or running Nessus scans? ECSA might be your ticket to more interesting work, honestly. Network security engineers use this to transition into dedicated pentest roles. SOC analysts use it to move from detection to testing. Incident responders add it because understanding attack methodologies makes you better at investigating breaches. The thing is, you start seeing patterns differently once you know how attackers think through the entire kill chain.
Compliance auditors benefit too. Risk assessment specialists as well, even though they're not breaking into systems daily. Understanding how professional penetration testing works helps them evaluate third-party security assessments and internal testing programs more effectively. Organizations in finance, healthcare, and government often require this level of certification for anyone touching their security assessment programs.
The certification also matters if you're aiming for security consulting positions where you need to walk into a client site, conduct structured assessments, and deliver reports that don't just say "you're vulnerable" but actually provide actionable remediation steps with business context that executives can act on.
How ECSA differs from CEH and CPENT
People get confused here. EC-Council has three main penetration testing certifications that sound similar but serve completely different purposes, and I've seen this trip people up constantly.
The Certified Ethical Hacker Exam (CEH v11) is your foundation. Breadth over depth, covering twenty modules from footprinting to cloud security to IoT hacking. CEH teaches you what tools exist and basic concepts across the entire security space without going super deep into any one area.
ECSA 412-79 builds on that foundation by teaching methodology. It's not about knowing 50 different tools exist. It's about knowing which ones to use when, in what order, how to document what you find, and why those choices matter in professional contexts. The ECSA training course emphasizes structured approaches to web application testing, network penetration testing, and vulnerability assessment frameworks following industry standards that clients and regulators recognize.
Then there's CPENT. Top of the pyramid. That's the advanced practical certification where you're actually compromising systems in simulated enterprise environments within strict time limits, demonstrating hands-on skills by pivoting through networks, escalating privileges, maintaining persistence. All the stuff red teamers do.
Think of it this way: CEH proves you know the tools. ECSA proves you can execute professional security assessments following recognized frameworks. CPENT proves you can actually hack complex environments under pressure. Different purposes entirely.
The ECSA practical exam component sits between CEH's multiple-choice format and CPENT's intensive lab challenges. You're tested on application security analysis in controlled environments, but it's not as demanding as CPENT's multi-machine compromises that require you to chain exploits together. Career progression typically follows CEH, then ECSA, then CPENT if you're specializing in penetration testing. Plenty of people stop at ECSA because they're focused on security analysis rather than full-on red teaming.
Organizations hiring for mid-level penetration testing positions often list ECSA or equivalent as preferred qualifications in job postings. Senior consultant roles lean toward CPENT or OSCP. But ECSA hits that middle ground where you're demonstrating both methodology knowledge and practical application without needing the deep technical expertise CPENT demands or the extensive real-world experience some employers expect.
ECSA 412-79 Exam Details
What you're actually sitting through
The ECSA exam 412-79 consists of 150 multiple-choice questions that you need to complete in 4 hours. That's a marathon, honestly. Four hours. I mean, it's a really exhausting stretch to maintain focus, especially when you're dealing with scenario-based problems that require analyzing security assessment situations where context matters, threat vectors overlap, and you're constantly second-guessing whether the "best" answer is the one they're actually looking for or just the textbook response.
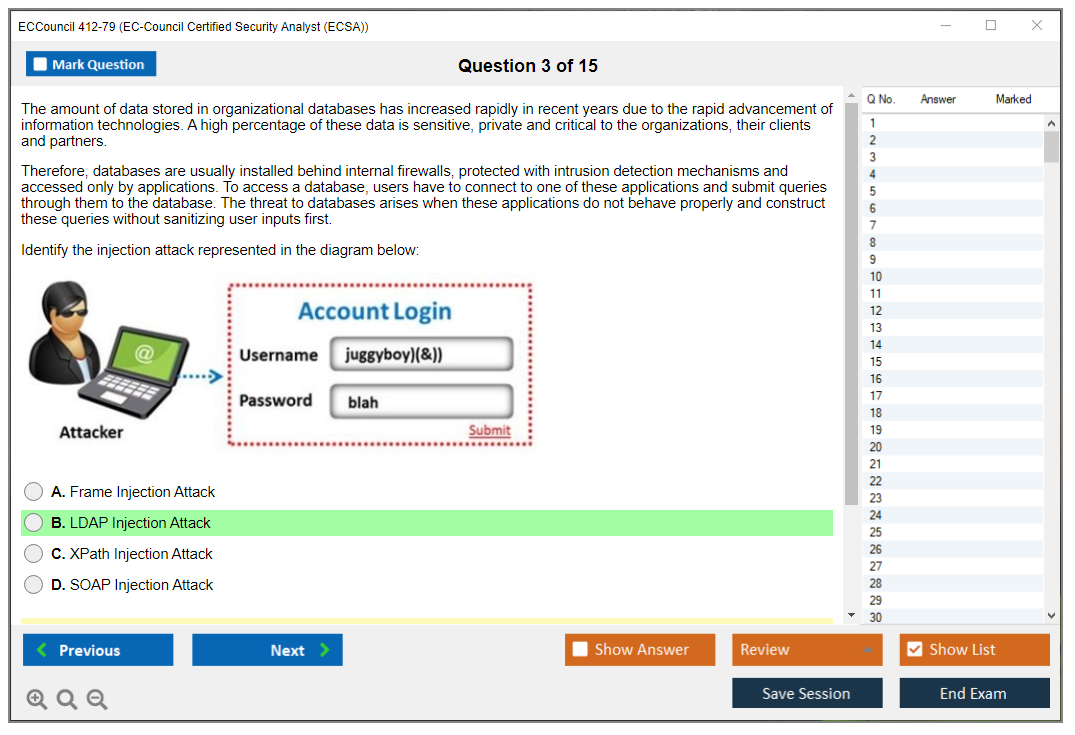
The exam tests both book knowledge and practical application understanding. You're not just memorizing definitions. The thing is, questions present security testing scenarios and ask you to identify appropriate methodologies, select correct tools for specific situations, or determine proper documentation approaches. Some questions provide vulnerability scan results or penetration test findings and ask you to recommend remediation steps or assess risk levels.
Format-wise? Computer-based testing. Pearson VUE centers or through online proctoring. Multiple-choice means you're selecting answers rather than demonstrating hands-on skills, but the ECSA practical exam component adds that application element. The practical portion tests web application testing and security analysis skills in lab environments where you're actually performing assessments rather than just answering questions about them.
I spent way too much time on practice questions that looked nothing like the real exam, which is its own form of torture. Sometimes the prep materials just miss the mark completely.
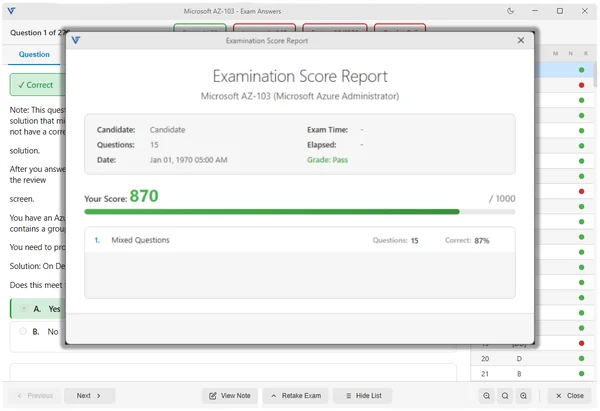
The passing score everyone wants to know
The ECSA passing score's 70%, which means you need at least 105 correct answers out of 150 questions. That's actually pretty standard for professional IT certifications, though it doesn't make the exam easy. The percentage is fixed, not scaled, so you know exactly what you're aiming for going in.
Honestly, aiming for just 70%? Risky move. You want buffer room for questions where you're really unsure or scenarios that throw you off. I mean, there's always a few curveballs that make you question everything you thought you knew about security testing methodology and whether you've been doing this all wrong. Most people I know who passed comfortably were scoring 80-85% on practice tests consistently before attempting the real thing.
The practical exam has separate scoring criteria based on objectives completed and vulnerabilities identified. You're graded on your ability to conduct security assessments, document findings properly, and show understanding of penetration testing methodology through actual application.
Official domains the exam covers
EC-Council breaks down the ECSA v10 exam objectives into modules covering security analysis fundamentals, penetration testing methodology, vulnerability assessment processes, web application security testing, network penetration testing techniques, database security analysis, and professional reporting standards.
Security analysis fundamentals? That's understanding the difference between vulnerability assessments and penetration tests. Knowing compliance requirements driving security testing. Recognizing when different testing approaches apply. This is foundational stuff that separates professional assessors from script kiddies.
The penetration testing methodology section is huge. You're learning structured approaches like PTES (Penetration Testing Execution Standard), OWASP testing guides, and NIST frameworks. Understanding pre-engagement activities, scoping, rules of engagement, and legal considerations that honestly determine whether you're conducting a legitimate security assessment or potentially committing a federal crime, which sounds dramatic but it's the reality of this profession. This part trips up people who just want to jump straight to exploitation.
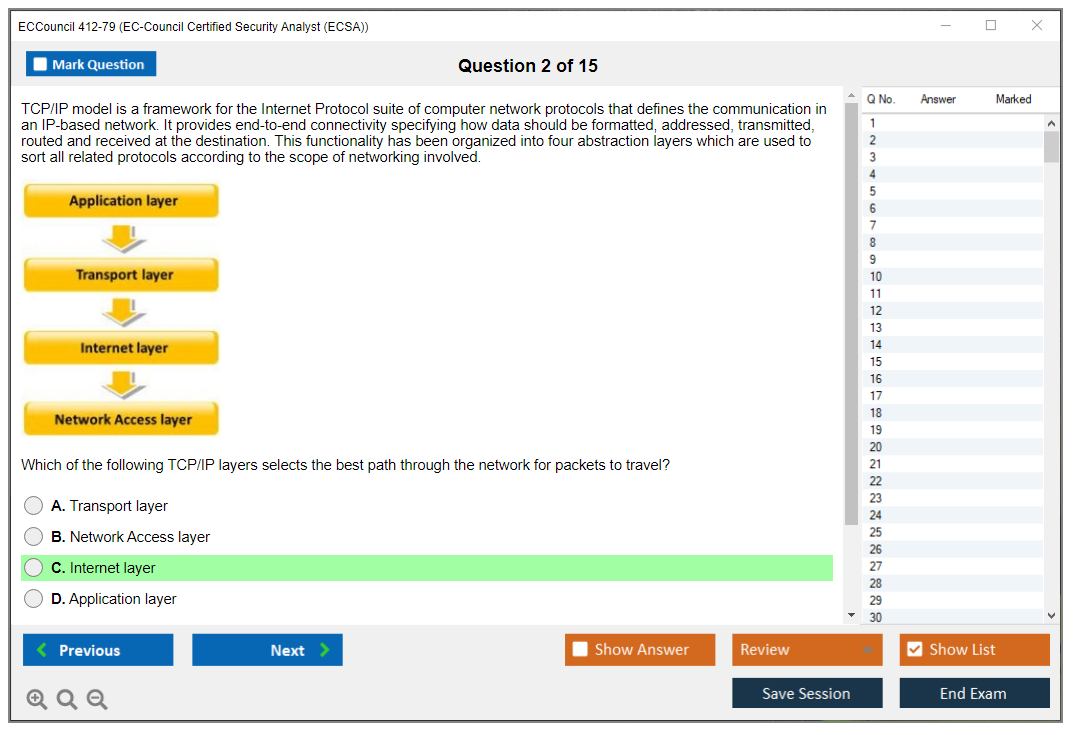
Web application testing covers OWASP Top 10 vulnerabilities in depth. Authentication and session management flaws. Injection attacks, cross-site scripting, security misconfigurations, and broken access controls. Network penetration testing includes reconnaissance, scanning, enumeration, exploitation, post-exploitation, and privilege escalation across Windows and Linux systems.
Database security analysis focuses on SQL injection techniques. Database enumeration. Privilege escalation within database systems and data extraction methods. Professional reporting standards cover documentation requirements, executive summary creation, technical findings presentation, risk rating approaches, and remediation recommendation development.
The practical exam component explained
Real talk? The ECSA practical exam tests your ability to perform actual security assessments in controlled lab environments. You're given access to target systems and asked to identify vulnerabilities, exploit them where appropriate, and document your findings following professional standards.
This isn't like CPENT where you're compromising entire networks. The ECSA practical focuses specifically on application security analysis and web application testing skills. You might be presented with a web application containing multiple vulnerabilities and asked to identify them, demonstrate exploitation, and document the security impact.
Time management matters here because you need to balance thorough testing with practical constraints. You're graded on methodology adherence, not just finding vulnerabilities, which can feel counterintuitive when you're racing the clock but want to prove you've got the skills. Following a structured approach, documenting each step, and providing clear evidence of findings all contribute to your score.
ECSA Exam Cost and Fees
What you're actually paying
The ECSA exam cost? Around $999. That's buying directly through EC-Council for the exam voucher. Just the exam fee, nothing bundled in. Some training providers package exam vouchers with their courses, which might save you something depending on how they've structured their pricing.
Here's the thing though: the exam fee is actually the smaller chunk of your total investment when you really think about it. The official EC-Council training course costs way more. Typically you're looking at somewhere between $2,500 to $3,500 depending on whether it's online, in-person, where you're located, that sort of thing. That package includes courseware, lab access, and instructor-led training that covers all the exam objectives you'll need.
Third-party training options exist and usually cost less. Independent training providers and online learning platforms offer ECSA preparation courses from about $500 to $1,500, but quality varies all over the place. Some are excellent. Experienced instructors, good lab environments, the whole deal. Others? Basically someone reading PowerPoint slides at you while you slowly lose the will to live.
I've noticed people underestimate the value of hands-on practice. You can memorize methodologies all day, but until you've actually fumbled through a real penetration test and wondered why your exploit isn't working, you're missing something key. Budget for lab time if your course skimps on it.
Retake policies if things go wrong
Retake fees match the original exam cost. Another $999 if you don't pass your first attempt. No discount for retakes, which honestly motivates you to prepare thoroughly before you schedule, because nobody wants to drop another thousand bucks unnecessarily.
EC-Council requires a waiting period between attempts, usually 14 days minimum. This prevents people from just repeatedly taking the exam hoping to memorize questions through repetition or luck. Use that time to identify weak areas and actually improve your knowledge rather than gambling on getting different question sets.
Rescheduling policies? They depend on notice. Cancel or reschedule at least 24 hours before your appointment and you typically avoid penalties. Miss your scheduled exam or cancel with less notice and you're forfeiting fees, plain and simple. Pearson VUE has specific policies about this stuff, so read the fine print when scheduling.
ECSA Difficulty and Pass Rate Expectations
How challenging this exam actually is
ECSA's tough. Tougher than CEH.
But it's not as brutal as CPENT. That's the thing. If you've got solid hands-on security experience and you've actually performed penetration tests or security assessments in real environments, the concepts won't feel foreign. Coming straight from CEH with minimal practical experience though? You're gonna struggle.
The difficulty comes from needing to understand methodology deeply, not just recognize tool names. Questions present complex scenarios requiring you to select appropriate testing approaches, identify proper documentation methods, or assess findings within business context. You can't just memorize answers because scenarios vary. I've noticed this catches people off guard who did well on CEH by cramming definitions.
The four-hour duration adds mental fatigue. Maintaining focus through 150 scenario-based questions requires stamina. I've seen people who know the material well but lost concentration in the final hour and made careless mistakes. Your brain starts playing tricks on you around hour three.
Skills that actually matter for passing
Hands-on experience with penetration testing tools matters. Understanding when and why?
That matters more. You need practical knowledge of web application vulnerabilities beyond just definitions. Actually exploiting SQL injection, understanding why XSS matters in different contexts, recognizing authentication bypass opportunities.
Network penetration testing skills help a lot. Understanding reconnaissance methodologies, enumeration techniques, privilege escalation approaches across different operating systems. The exam tests whether you can select appropriate techniques for specific scenarios rather than just listing what tools exist.
Documentation skills are underrated.
A big portion of questions involve professional reporting standards, risk assessment methodologies, and remediation recommendation development. Understanding how to communicate technical findings to different audiences, prioritize vulnerabilities based on business impact, and provide actionable remediation steps. Most pentesters hate this part but it's where clients actually see value.
Why people fail this exam
Insufficient hands-on experience. That's the biggest reason.
People study theory without actually practicing penetration testing techniques in lab environments. You can't pass this exam just by reading books or watching videos. You need practical application of the methodologies being tested. Period.
Poor time management during the exam trips people up. Spending too long on difficult questions early and then rushing through the final 30-40 questions. Pacing yourself across four hours while maintaining accuracy is rough.
Weak areas in specific domains that people neglect during preparation also kill candidates. Someone might be strong in network penetration testing but weak in web application security, or the other way around. The exam covers all domains, so you can't just focus on your comfort zones.
ECSA Prerequisites and Eligibility
What EC-Council officially requires
Look, here's the deal. EC-Council recommends having the Certified Ethical Hacker Exam certification before pursuing ECSA, but it's not a hard requirement. You can take ECSA without CEH if you meet alternative eligibility paths. That said, honestly, if you don't have the foundational knowledge CEH provides, ECSA will be way harder. We're talking night-and-day difference in how you'll grasp the material.
Official prerequisites include either holding CEH certification or completing the official EC-Council ECSA training course. Got neither? You can still qualify by submitting an application demonstrating at least 2 years of information security work experience in a related field.
The training requirement path means you attend the official ECSA training course, which automatically makes you eligible to sit for the exam regardless of prior certifications or experience. Most expensive route? Absolutely. But it gets you through all exam objectives with instructor-led training.
Background that actually helps
Two to three years? That's the sweet spot for hands-on security experience. Makes a huge difference, honestly. Working as a security analyst, network security engineer, or SOC analyst gives you practical context for the methodologies being tested. You've seen vulnerabilities in real environments, understood business impact, dealt with remediation processes. The whole nine yards.
Prior penetration testing experience helps. Even informal internal testing helps tremendously. Understanding the workflow of scoping an assessment, conducting testing, documenting findings, and presenting results lines up directly with exam content. Wait, actually, it's more than that. This experience makes exam scenarios feel familiar rather than abstract.
Real talk here: familiarity with security frameworks and compliance requirements provides context for why certain methodologies matter. Experience with PCI DSS, HIPAA, SOX, or other regulatory frameworks? That helps you understand the professional standards and documentation requirements emphasized in ECSA. Sometimes the "why" matters as much as the "how," especially when you're explaining findings to someone who barely knows what a firewall does.
Alternative paths if you're not quite ready
If you lack the recommended experience or CEH certification, the thing is, consider starting with Certified Cybersecurity Technician (CCT) or working toward CEH first. Building foundational knowledge before jumping to methodology-focused certifications makes more sense than struggling through advanced material. Trust me on this.
Practical experience matters. Gaining it through entry-level security positions, internships, or volunteer work provides the hands-on context that makes ECSA content meaningful. Even setting up home labs and practicing penetration testing techniques against intentionally vulnerable systems builds relevant skills.
Some people pursue related certifications like CompTIA PenTest+ or Certified Network Defender (CND) to build complementary knowledge before attempting ECSA. These provide different perspectives on security testing and defensive analysis that strengthen your overall understanding. And honestly, there's no shame in taking the longer route if it means you'll actually retain the knowledge.
Best Study Materials for ECSA 412-79
Official courseware and its actual value
The official EC-Council ECSA training course includes full courseware covering all exam objectives, access to iLabs cyber range environments for hands-on practice, and instructor-led training sessions. The courseware's thorough. You're getting detailed explanations of penetration testing methodologies, step-by-step walkthroughs of security testing techniques, and scenario-based examples that walk you through actual situations.
The iLabs environment? Valuable stuff. You practice web application testing, network penetration testing, and vulnerability assessment techniques in controlled environments that mirror exam scenarios. This hands-on component is worth the investment if you lack access to similar lab setups. Where else are you gonna get that kind of targeted practice?
Here's the thing though. Instructor quality changes depending on who's teaching the course. Some EC-Council Certified Instructors bring real-world penetration testing experience and provide insights beyond the courseware, sharing war stories and techniques they've used in the field. Others just read slides. Research the instructor's background before committing to expensive training.
Books and resources that actually help
The official EC-Council ECSA Study Guide covers exam objectives but reads pretty dry. It's structured for exam preparation rather than engaging learning. Gets the job done, but you'll need coffee. Use it as reference material alongside more hands-on resources.
"The Web Application Hacker's Handbook" by Dafydd Stuttard and Marcus Pinto remains required reading for the web application security portions of ECSA. Deep technical coverage of vulnerability classes, exploitation techniques, and testing methodologies that'll stick with you beyond exam day. This book goes past what you need for the exam but builds genuine expertise, which is kinda the point, right?
OWASP Testing Guide? Free. Full. It provides coverage of web application security testing methodologies that align closely with ECSA objectives. Maintained by security practitioners and reflects current best practices. The Penetration Testing Execution Standard (PTES) documentation offers detailed methodology frameworks covering all phases. It's also completely free, which matters when you're already dropping cash on the exam itself.
I spent way too much time one weekend trying to decide between three different study guides from Amazon before realizing the OWASP stuff was sitting right there, free, and probably better than two of the paid options anyway.
Setting up hands-on practice environments
You need lab environments. Period. VulnHub and HackTheBox provide vulnerable systems for practicing exploitation techniques. TryHackMe offers guided learning paths for penetration testing skills. PortSwigger Web Security Academy has excellent free labs for web application security testing. Honestly some of the best free content out there.
Setting up your own lab environment with virtualization software like VMware or VirtualBox gives you controlled testing spaces. Install intentionally vulnerable applications like DVWA (Damn Vulnerable Web Application), WebGoat, and Mutillidae for practicing web security testing. Deploy vulnerable operating systems like Metasploitable for network penetration testing practice.
Kali Linux becomes your primary testing platform, and you'll wanna get comfortable with it. Get familiar with tools included in Kali that align with ECSA objectives: Burp Suite for web application testing, Nmap for reconnaissance and scanning, Metaspl
What is ECSA and who should take it?
The EC-Council 412-79 ECSA certification is EC-Council's "show me you can assess security like a pro" credential, sitting in that space between theory-heavy certs and fully hands-on red team exams. It's aimed at people who already get the basics of ethical hacking and security analysis and now need to prove they understand a repeatable penetration testing methodology, how to scope work, how to analyze results, and how to communicate findings without sounding like a tool.
If you're a SOC analyst trying to pivot into offensive work, a junior pentester who wants a vendor badge, or a consultant who keeps getting asked "can you run a vulnerability assessment and reporting cycle end-to-end," ECSA makes sense. Look, if you've never run a scan, never read tool output, and "SQL injection" is still a vague concept, honestly you'll suffer.
ECSA vs CEH vs CPENT (key differences)
CEH is broader. More entry-level. It's a lot of terminology and "what does this tool do" style knowledge. ECSA (especially the ECSA v10 exam track) expects more maturity: scoping, professional standards, judgment calls in real scenarios, and deeper questions around web application testing and network testing.
CPENT? More hardcore hands-on.
It's closer to "do the work in a lab under pressure." ECSA can include a practical element (more on that below), but the 412-79 exam itself is mainly a structured knowledge test with scenario-based decision-making where you're forced to think through realistic engagement situations rather than regurgitate memorized facts.
Not gonna lie, if your goal is pure red team credibility, CPENT or OSCP is the usual conversation. If your goal is consulting-style penetration testing methodology plus a recognizable EC-Council ladder after CEH, ECSA's the cleaner next step. Though I've seen people skip CEH entirely and go straight here if they've got enough practical background. Nobody's checking your homework.
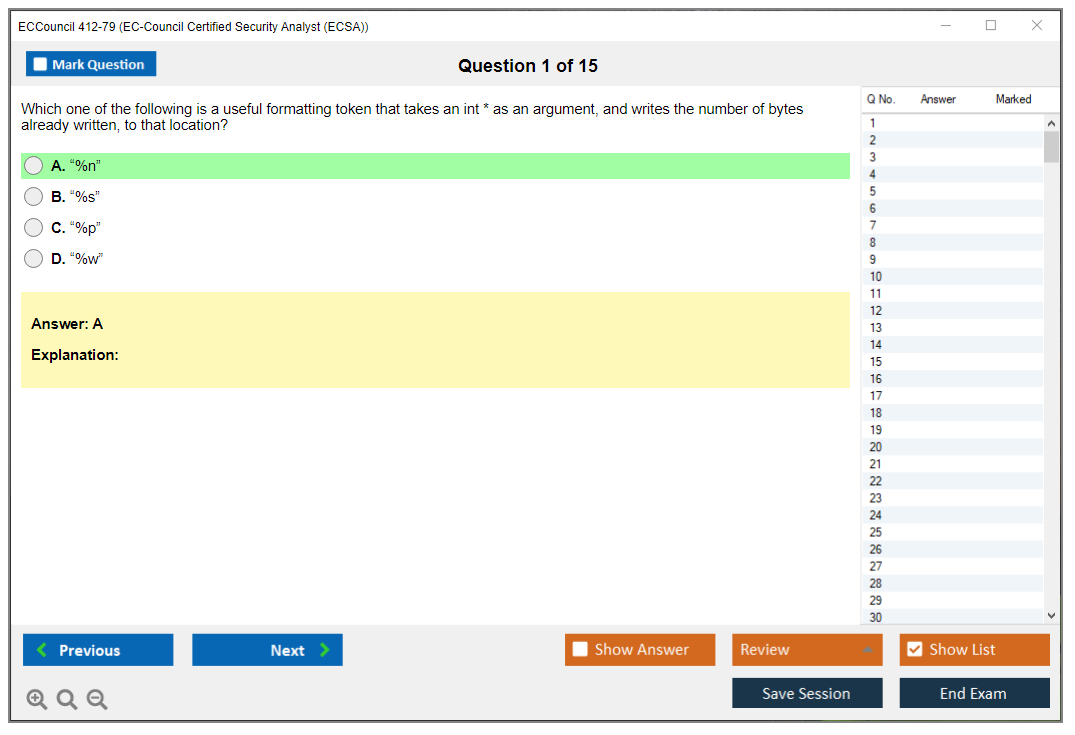
Exam format, number of questions, and duration
The ECSA exam 412-79 tests both book knowledge and practical judgment around penetration testing methodology and security analysis. The core written exam is 150 multiple-choice questions. You get 4 hours (240 minutes). That's generous, but it also lulls people into wasting time early, then panic-clicking later.
Do the math: 240 minutes divided by 150 questions gives you about 1.6 minutes per question, and that's before you account for review time, rereading scenarios, and the couple of items that are basically mini case studies demanding careful analysis of client requirements and testing constraints. Some questions are traditional single-answer multiple choice. Others are multiple-response selections, where more than one option's correct. Then you get scenario-based questions that ask you to read a situation and choose the right methodology, tool approach, or analysis step.
The exam delivery's through EC-Council's ECC Exam portal, either at an authorized testing center or via online proctoring for remote testing. The interface lets you mark questions for review and move around freely, so you can skip the time-sinks and come back.
Passing score for ECSA 412-79
The ECSA passing score is 70%, which is 105 correct answers out of 150. Fixed score. Not adaptive, not scaled. I mean, that's nice because you always know what "safe" looks like when you're using ECSA practice tests. EC-Council sets that threshold based on subject matter expert analysis, with the intention that certified folks meet a minimum bar for professional penetration testing.
You get immediate pass/fail results when you finish, right there in the testing interface. If you don't pass, you also get a domain-level breakdown so you can see what went wrong, which's way more useful than "sorry, try again."
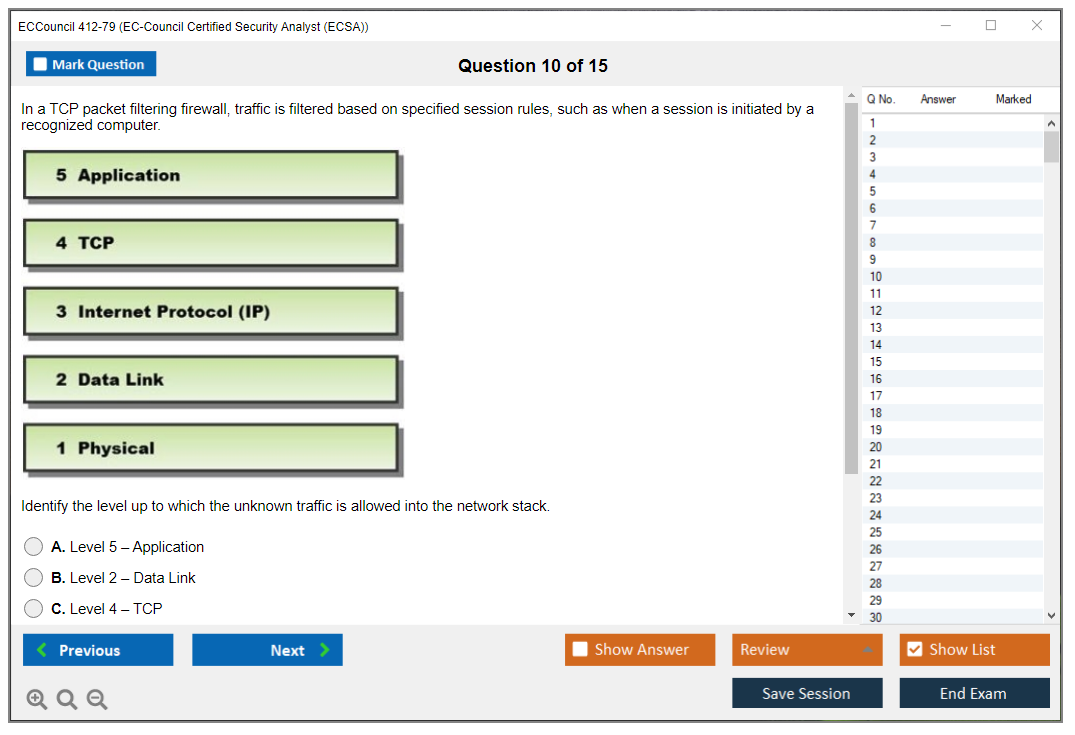
Exam objectives (official domains/topics)
EC-Council organizes ECSA content into domains that map to a real consulting engagement. Some domains tend to show up more, especially network penetration testing and web application testing, but you can't ignore the "boring" parts like scoping and report writing because those're the parts that get you sued if you mess them up.
Here're the domains you should expect:
- Domain 1: Introduction to penetration testing and methodologies
- Domain 2: Penetration testing scoping and engagement
- Domain 3: Open source intelligence (OSINT) gathering
- Domain 4: Social engineering penetration testing
- Domain 5: Network penetration testing
- Domain 6: Perimeter defense penetration testing
- Domain 7: Web application penetration testing
- Domain 8: Database penetration testing
- Domain 9: Wireless network penetration testing
- Domain 10: Cloud penetration testing
- Domain 11: Report writing and post-testing actions
Two that deserve extra attention.
Domain 2's where a lot of smart technical people faceplant because they treat it like paperwork. Scope definition, rules of engagement, legal boundaries, what's allowed in a test window, what evidence you can collect, what you must avoid, and how to document exceptions. The thing is, if you've only ever hacked boxes on your own time, this domain feels annoying. In real client work? It's everything.
Domain 11 is the "can you act like a professional" check. You'll see questions about documentation requirements, how to communicate risk to stakeholders, what belongs in an executive summary vs a technical appendix, and how you should frame recommendations. Fragments. Screenshots. Reproduction steps. Risk ratings. This's where vulnerability assessment and reporting becomes more than exporting a scanner PDF.
The rest? OSINT, social engineering concepts, wireless basics, cloud testing constraints, perimeter controls like IDS/IPS and firewall evaluation, and database testing with common injection and misconfiguration themes.
ECSA practical exam: what to expect (if applicable)
Depending on the track you're taking and what EC-Council's offering at the time, there's an ECSA practical exam component that tests hands-on application security analysis and web app testing in a controlled lab. You typically access a virtual environment with vulnerable systems and apps, then you're expected to identify issues, exploit where appropriate, and document evidence like you would in a real engagement.
This practical assessment's time-limited and it rewards a methodical approach. Recon, identify attack surface, validate vulnerabilities, capture proof, write it up clearly. The lab scenarios often feel like realistic client apps: auth issues, input validation failures, insecure configuration, outdated components, that kind of thing. Success requires both technical execution and reporting discipline, which's the point.
Exam voucher price and what's included
ECSA exam cost changes based on region, promos, and whether you're buying training bundles, so I'm not going to throw one magic number at you and pretend it's universal. Generally, the voucher covers one exam attempt through the ECC Exam portal, and you'll see options for remote proctoring or test center scheduling.
Read the fine print. Some bundles include an eligibility application path, courseware, labs, or a retake, and some don't. If your employer's paying, push for the bundle that includes official labs because, honestly, that's where people stop guessing and start understanding.
Training costs (official vs third-party)
The ECSA training course from EC-Council's usually the most expensive route, but it maps directly to their objectives and often includes lab access. Third-party training can be cheaper and sometimes better taught, but you need to verify it lines up with ECSA v10 exam objectives and not an older outline.
A solid compromise? Using official materials for domain coverage, then using outside labs for real skill building. Because memorizing tool names is one thing. Interpreting tool output under pressure's another.
Retake fees and rescheduling policies
If you fail, there's typically a waiting period before you can retake, and you'll pay the applicable retake fees. Policies can change, so check EC-Council's current exam retake and rescheduling rules before you schedule, especially if you're doing online proctoring and your home setup's questionable.
How hard is the ECSA exam?
ECSA's harder than CEH. Not because it's packed with trick questions, but because the scenarios force you to think like an assessor and not like a trivia contestant, and EC-Council updates exam content to reflect current threats, emerging vulnerabilities, and shifting methodology standards.
Some questions are straightforward. Many're "what should you do next" or "what's the right testing approach here," and you can't brute-force that if you've never done assessments for real.
Skills you need to pass (hands-on vs theory)
Both. No question. You need understanding of penetration testing phases, plus enough hands-on familiarity to recognize what tools do, when to use them, and how to interpret results. Expect technical depth in web apps, networks, and vulnerability assessment techniques. Also expect professional judgment questions around scoping, legal constraints, and reporting.
This's where people get surprised. Knowing an exploit exists isn't the same as knowing whether you should run it, how you'd validate it safely, and what you'd tell a stakeholder afterward.
Common reasons candidates fail
Rushing. Misreading multi-response prompts. Weak scoping knowledge. And the big one: treating reporting as an afterthought. Another quiet killer's relying on outdated notes, because ECSA v10 exam content shifts as EC-Council updates objectives.
Required experience (recommended background)
There's no single background that guarantees success, but you should be comfortable with TCP/IP, basic Linux, common web app concepts, and reading logs and scanner output. If you've done vulnerability management, SOC triage, sysadmin work, or junior pentesting, you're in the right zone.
Training requirements and exam eligibility paths
Eligibility and official paths can vary by EC-Council policy at the time you register. Some candidates come through official training, others through approved experience. Check your current requirements in the ECC portal flow, because that's what you'll be held to.
What to do if you don't meet prerequisites
Get reps first. Build a small lab, run through common web vulnerabilities, practice writing findings, and do at least one full mock assessment from scoping to report. Then book the exam. Otherwise you're donating money.
Official EC-Council courseware and labs
Official courseware's aligned to the domains and tends to mirror the way questions are phrased. The labs, when included, are useful for practicing methodology and documentation, not just popping shells.
Recommended books and references
OWASP Testing Guide for web methodology. NIST-style reporting and assessment references for structure. And a practical web hacking book if your web testing's weak. Keep it current, because old payloads and old cloud assumptions age fast.
Hands-on lab setup (tools, VMs, targets)
Kali or a similar distro. A couple of intentionally vulnerable targets like DVWA/Juice Shop and Metasploitable. Add a simple AD lab if you want network realism. Packet capture practice helps too. Wireshark literacy matters.
Where to find reliable ECSA practice tests
Use official practice material if you can, then sanity-check with reputable third-party question banks that explain answers. Avoid "brain dumps." They rot your understanding and they're a career hazard.
Practice exam strategy (timing, review, weak areas)
First pass: answer what you know, mark the rest. Second pass: tackle scenario questions with fresh eyes. Spend extra time on multi-response because one missed checkbox can sink the item. Use your domain score report style results from practice runs to focus, especially on scoping and reporting.
Final-week checklist and day-of-exam tips
Sleep. Confirm your ID and testing environment. Do one timed run at 150 questions to build pacing. Review your weak domains, not your favorite ones. On exam day, read the question twice, especially when it asks for "best" vs "first" vs "most appropriate."
Certification validity period
EC-Council certs typically have a validity window tied to continuing education rules. Confirm the current cycle in your EC-Council account because policies can change.
Renewal requirements (ECE credits, fees, timelines)
Renewal generally involves earning ECE credits and paying renewal fees within the required timeline. Track this from day one, because people forget and then scramble at the end.
How to earn ECE credits quickly (training, events, writing)
Training courses count. Security conferences and webinars often count. Writing, presenting, or teaching can count too, and honestly that's one of the best ways to force yourself to learn the material deeply.
What is the EC-Council 412-79 (ECSA) certification?
It's EC-Council's mid-level penetration testing and security analysis credential, focused on methodology, assessment judgment, and professional reporting, with an exam that blends multiple-choice and scenario-based questions.
What is the passing score for the ECSA 412-79 exam?
The ECSA passing score is fixed at 70%, or 105/150.
How much does the ECSA exam cost?
Budget for the voucher plus optional training and possible retake costs. The exact ECSA exam cost depends on region and bundle, so check current pricing in EC-Council's store or through an authorized training partner.
How hard is the ECSA certification compared to CEH?
Harder. More scenario reasoning, more focus on methodology and reporting, and deeper coverage of web and network testing.
What are the prerequisites and renewal requirements for ECSA?
Prereqs and eligibility paths depend on EC-Council's current policy when you register. Renewal typically requires ECE credits and fees during the validity period, tracked through your EC-Council account.
Breaking down what you'll actually pay
Okay, so here's the thing. When I first looked into ECSA certification, I assumed it'd be one simple exam fee and I'd be done. Turns out I was completely off base. Understanding the complete financial investment helps you budget properly and plan your certification timeline, but you've gotta see the whole picture before jumping in.
The sticker shock? It hits different depending on your approach. Some folks drop $1,000 and they're good. Others are staring down $3,500+ before they even schedule the exam. ECSA exam cost includes multiple pieces beyond just the voucher: training expenses and prep materials that can seriously add up if you're not careful which route you choose.
What you're paying for with the exam voucher
ECSA exam cost for the 412-79 voucher purchased directly from EC-Council runs from $950 to $1,199 USD depending on region. Yeah. Just for one attempt. The voucher gives you a single shot at the ECSA 412-79 exam at authorized testing centers or through online proctored delivery, which at least provides flexibility in how you wanna take it.
One thing I actually appreciate? Voucher validity extends 12 months from purchase date. You're not stuck cramming because your voucher expires in three weeks. The exam fee includes immediate score reporting, digital certificate upon passing, and inclusion in EC-Council's certified professional directory. At least you get something tangible beyond just a pass/fail notification.
Here's the catch though. The voucher doesn't include study materials, practice tests, or access to official lab environments. Those require separate purchases. For almost $1,000, you'd think they'd throw in something extra, right?
Finding discounts and bundle deals
EC-Council pricing varies by region and purchasing channel. Different costs for direct purchase versus authorized training partner bundles. This is where things get interesting. Buyers who grab training packages through EC-Council or authorized centers often receive discounted vouchers bundled with courseware. Sometimes saving you a couple hundred bucks compared to buying everything separately.
EC-Council occasionally offers promotional pricing during specific periods, potentially reducing ECSA exam cost by 10-20% for certain buyers. I've seen Black Friday deals, end-of-quarter promotions, that sort of thing. Worth keeping an eye out, seriously.
Military personnel, government employees, and students may qualify for discounted pricing through EC-Council's special programs. If you fall into one of these categories, definitely check before paying full price. Could save you a few hundred dollars just by asking the right questions.
Training costs that make your wallet cry
Total investment in ECSA certification runs from $950 to $3,500+ depending on training choices and prep materials. The big variable? Training. Official EC-Council ECSA training course through authorized centers runs $2,800-$3,500 for instructor-led classes with full materials.
That's a lot.
Like, really a lot.
Official training includes access to EC-Council's courseware, hands-on lab environments, practice exercises, and often bundled vouchers. So you're getting instructor time, labs, courseware, and the exam attempt all rolled together. For some people with corporate training budgets, this is the obvious choice. No question. For self-funded folks though? It's brutal on the bank account.
Self-paced online ECSA training through EC-Council's iLearn platform ranges from $1,200-$1,800, providing flexible learning options without instructor interaction. Still pricey, but at least you can learn at 2am in your pajamas if that's your thing. Which honestly works better for some people's schedules. Third-party training providers offer ECSA exam prep courses ranging from $299-$899, focusing on exam objectives without official EC-Council endorsement.
Here's my take: people with strong CEH foundation and practical security experience may pass using self-study without expensive official training courses. I've seen people pass with just books, labs they built themselves, and practice exams they found online. But you need to be brutally honest about your skill level before going this route. If you're already doing penetration testing work and have solid vulnerability assessment and reporting experience, self-study might work fine. Fresh 312-50v12 (Certified Ethical Hacker Exam) holder with no real-world experience? Maybe that official training isn't such a bad investment after all.
Speaking of self-study, I once tried teaching myself advanced exploit development using only free resources and a laptop that kept overheating during VM sessions. Took me three months longer than it should have, but I was stubborn about not spending money. Sometimes that stubbornness pays off, sometimes it just costs you in wasted time. You gotta know which battles are worth fighting on your own.
Official training provides thorough coverage of penetration testing methodology but represents a big investment compared to self-study approaches. Corporate training programs may negotiate volume pricing for multiple employees pursuing ECSA certification at once, which is worth exploring if you're part of a security team all pursuing certs together.
When things don't go as planned
ECSA retake fees match the standard voucher price ($950-$1,199) as EC-Council doesn't offer discounted pricing for second or subsequent attempts. Ouch. The voucher covers one exam attempt only. Failed folks must purchase additional vouchers for retakes, which means a failed exam is basically like lighting $1,000 on fire and watching it burn.
People failing the first attempt must wait minimum 14 days before scheduling a retake to allow additional prep time. After second failed attempt, you face a 30-day waiting period before third attempt, with progressively longer waiting periods for subsequent failures. I mean, EC-Council isn't messing around here. They want you actually learning the material between attempts, not just memorizing question dumps.
Scheduling flexibility and cancellation penalties
Exam rescheduling must occur at least 24-48 hours before scheduled appointment to avoid forfeiture of voucher and fees. Life happens. I get it. But late cancellations within 24 hours of scheduled exam time result in voucher forfeiture requiring purchase of new exam attempt. Nobody wants to deal with that financially.
No-show for scheduled exam without prior cancellation results in complete voucher loss and full repayment for subsequent attempts. Don't be that person who oversleeps and loses a grand. Set multiple alarms if you have to. EC-Council allows one free reschedule per voucher if conducted within policy timeframes, providing flexibility for unexpected scheduling conflicts that inevitably pop up.
Emergency situations with proper documentation may qualify for special consideration regarding rescheduling policies and voucher validity extensions. Medical emergencies, family situations, they'll work with you if you've got documentation and communicate proactively rather than ghosting them.
Budget-friendly prep resources
Look. You don't need to drop $3,000 on training to pass this thing. Third-party platforms like Udemy, Cybrary, and specialized security training sites offer budget-friendly ECSA prep options with varying quality levels. Some are complete garbage, some are surprisingly good and actually helpful.
The 412-79 Practice Exam Questions Pack at $36.99 gives you practice questions that mirror actual exam format without breaking the bank. I'm not saying practice exams alone will get you there, but they're useful for identifying weak areas and getting comfortable with question styles and time management. Definitely more affordable than a $1,500 training course that might not even fit your learning style anyway.
If you're already working in application security analysis or doing web application testing professionally, you've got a huge advantage over someone coming in cold. You're practicing exam content every day at work without even realizing it. Maybe you just need to fill knowledge gaps rather than learning everything from scratch, which changes the math completely.
Making the smart financial choice
The right budget depends entirely on your situation. There's no one-size-fits-all answer here. Fresh to penetration testing with minimal security background? That $3,500 official training package might actually save you money compared to failing the exam twice at $1,200 per attempt, which adds up fast. Already doing this work professionally and just need the cert to back up your experience? Self-study plus practice exams might get you there for under $1,200 total investment.
Compare this to the 712-50 (EC-Council Certified CISO) or other advanced EC-Council certs, and ECSA sits in the middle cost-wise. Not as brutal as some, but definitely not cheap either. Let's be real about that. Budget at minimum $1,500-$2,000 if you're being realistic about needing some training materials and want a buffer for potential retakes just in case things don't go perfectly the first time around.
The 312-39 (Certified SOC Analyst) and 312-38 (Certified Network Defender) certs follow similar pricing structures, so if you're planning a certification pathway with multiple exams, expect these kinds of costs across the board.
Look, honestly? The ECSA's tough. Really tough. It's not one of those exams where you just memorize stuff and call it a day. The thing is, you're actually expected to think on your feet and demonstrate real-world penetration testing skills under pressure, which is a completely different beast compared to multiple-choice tests that just assess whether you've read the material.
Pass rates? They're not great.
EC-Council doesn't exactly publish official numbers, but from what folks in the industry say, we're looking at somewhere between 40-60% on the first attempt. That's pretty brutal if you think about it. Compare that to other certifications where pass rates hover around 70-80%, and you'll see why people get nervous.
Here's the thing though, and I'm gonna be real with you: the difficulty comes from the format itself. You've got a 12-hour practical exam where you need to compromise networks, document everything properly, and then write a professional penetration testing report. Twelve hours. That's an entire workday plus overtime, and you can't really take substantial breaks because, honestly, the clock just keeps ticking.
What makes people fail? Usually it's one of three things. Poor time management, where they spend way too long on one section and run out of time. Incomplete documentation, where they hack successfully but don't record their findings properly. Or subpar report writing, which trips up a lot of candidates since technical people sometimes struggle with communicating their findings in business language that executives would actually understand. I've seen guys who could pivot through a network blindfolded absolutely bomb the report section because they wrote it like a GitHub readme instead of something you'd present to a CISO.
But mixed feelings here: it's difficult for good reason. The certification actually means something. You've proven you can do the work, not just talk about it.
The EC-Council 412-79 ECSA certification is EC-Council's "next step after CEH" credential, aimed at people who can already talk ethical hacking and now need to think like an assessor. Not beginner stuff. Not pure red-team flex either. More like: can you run an assessment the way a consulting shop expects, then explain what you found without sounding like you're just reading tool output to a client who's already stressed about their security posture?
ECSA fits best if you're in vulnerability management, junior pentesting, security analyst roles, or you're the IT person who keeps getting handed "can you test this app real quick" requests. We've all been there. It's also a decent checkbox cert for certain job postings that want "EC-Council Certified Security Analyst" specifically, even if the hiring manager mostly cares whether you can do application security analysis and write a sane report.
Reality check here. Experience matters.
One thing nobody mentions enough: the report writing portion will expose you if you've never had to justify findings to someone who controls the budget. I've watched technical people freeze up when asked to translate "SQL injection in the login form" into business risk. That gap between finding the vulnerability and explaining why anyone should care about fixing it? That's what trips people up more than the technical content.
CEH is broad. ECSA goes deeper. CPENT? More hands-on intense.
CEH often feels like vocabulary plus tool awareness, which isn't bad, but it's surface-level compared to what comes after. ECSA expects you to know why you'd pick a method, how to interpret results when they're messy, and what to do next when the "obvious" answer fails and you're sitting there wondering if it's the tool or the config or just your coffee wearing off. CPENT pushes harder into practical execution and endurance in a lab-style environment where you can't just memorize answers.
The comparison you'll hear a lot is accurate: ECSA exam 412-79 difficulty lands intermediate-to-advanced. More challenging than CEH, less punishing than CPENT's practical demands, especially if you're not living in labs every week.
The 412-79 exam throws 150 questions at you in 4 hours. Seems reasonable when you first hear it, right? Then you do the math and realize you've got about 1.6 minutes per question. A lot of these are scenario-heavy monsters too. You can't just coast through. That whole "I'll flag it and come back" strategy falls apart when the clock starts getting aggressive. Mental stamina becomes a real problem because you're making security decisions for four straight hours while trying not to overthink the weird phrasing on harder questions.
Some questions are short.
Most aren't.
Oh, and bring snacks if they let you. Low blood sugar during hour three will absolutely wreck your focus in ways you don't expect until it happens.
Here's what nobody tells you upfront: people keep asking for one specific number for the ECSA passing score, but EC-Council uses this scaled approach that shifts depending on which exam form you get. You'll find different thresholds mentioned everywhere online, which gets annoying fast. Safest bet? Aim high enough that passing score details don't even matter, because if you're anywhere near the cutoff you're going to feel terrible during the actual test.
Chasing a "minimum" target score is honestly a mistake.
The exam mixes penetration testing methodology with practical tool analysis in ways that actually reflect real work. You'll see recon and scanning, vulnerability identification, exploitation concepts, web application testing, network attacks, and the business aspects like vulnerability assessment and reporting. Risk rating, remediation planning, scope definition, rules of engagement. A lot of candidates skip this stuff entirely and regret it later.
Frameworks appear throughout. PTES, OWASP, NIST-style thinking. Less "define this acronym" tedium, more "what phase are you in and what should happen next," which actually tests whether you understand the work.
EC-Council has practical components and add-on exams across different cert tracks, so candidates sometimes mention an ECSA practical exam experience even when their main 412-79 attempt stays multiple-choice. Creates confusion. If you're doing anything practical alongside your ECSA v10 exam prep, expect it to reward unglamorous fundamentals. Thorough enumeration, organized notes, validating findings properly, not getting tunnel vision on one exploit while the environment screams at you to pivot.
Labs punish guessing.
Brutally.
ECSA exam cost swings wildly depending on your region, whatever promos EC-Council's running that month, and whether you're bundling it with training packages or going solo. EC-Council pricing is never just "one clean number." Once you pile on taxes, proctoring fees, and those package add-ons, the total shifts around constantly. Budget for the voucher itself first, then assume you'll probably drop extra cash on practice platforms or lab environments if your current job doesn't hand you a safe sandbox to break stuff in.
The thing is, check what your voucher actually includes. Some bundles toss in official courseware access. Others? Nothing.
The ECSA training course straight from EC-Council can hit your wallet pretty hard, but it does line up tight with the stuff they test you on. Third-party training's usually cheaper, and sometimes the instructors are better at explaining concepts in ways that actually stick. You've gotta do the legwork yourself mapping their curriculum back to EC-Council's exam objectives though. Being really skilled at hacking and being "exam-ready for EC-Council's weird question style" are related skills, sure, but they're not identical twins.
I once watched a colleague blow through five different Udemy courses trying to find one that matched the official outline. He passed, but he could have saved himself three months of confusion by just picking one path and sticking with it.
One sentence warning. Don't buy dumps.
Retakes? That's where budgets go to die. Look hard at the voucher terms before you schedule that first attempt, because rescheduling windows and retake pricing rules shift around more than you'd think. Candidates lose money by assuming it works like CompTIA or Cisco. It doesn't. If you're not consistently crushing timed practice exams, delay the real attempt. A panicked first try almost always creates a second bill you didn't plan for.
Understanding ECSA exam difficulty helps you set realistic prep timelines and build study habits that actually match the test. This thing is not pure memorization. It also is not some chill "watched videos for a weekend" checkbox either.
The exam pushes beyond recall, which catches people off guard. You get scenario-based questions wanting you to apply ethical hacking and security analysis thinking to realistic engagements, pick the most appropriate methodology or tool for that specific context, and justify it implicitly by choosing answers that match the constraints, scope, and phase of testing you're actually in.
Here's the part nobody likes hearing: pass rates for ECSA 412-79 are not officially published by EC-Council, so anyone claiming precise numbers is basically guessing. Industry chatter and training-provider anecdotes often put first-attempt pass rates around 60 to 75% for adequately prepared candidates. That tracks with what I've seen in real life, where people with labs and some work experience usually pass, while people trying to brute-force it with slides and dumps often don't.
Time pressure adds teeth. Four hours feels long, sure, but 150 questions means you can't spend five minutes admiring a single web app scenario. The late-exam fatigue? Brutally real when you've been parsing tool output and second-guessing "best" answers for hours.
This exam rewards balanced ability.
Theory alone? Shaky. Pure tool button-clicking is also shaky, if we're being honest.
You need enough penetration testing methodology knowledge to know what comes next and what's actually appropriate in context, plus enough hands-on familiarity to recognize commands, syntax, and output patterns when they show up in a question without hesitating.
A few skills that matter:
- Web application testing, especially with Burp Suite, OWASP ZAP, and manual testing habits. I'm talking parameter tampering, auth/session weirdness, input validation issues, and knowing what an actual exploitable finding looks like versus scanner noise. This is where many candidates wobble. Web questions often combine multiple clues, and you've got to pick the best next step, not just name the vulnerability.
- Tool output interpretation, like reading Nmap results and understanding what they imply about services and next actions. Same idea with vulnerability scanner reports and exploitation feedback. If you've only seen screenshots in a PDF, you'll hesitate, and hesitation absolutely eats time.
- Metasploit basics, service enumeration, common priv-esc concepts in labs, and knowing how defensive controls change your approach.
Reporting shows up too. Risk rating, impact analysis, remediation language, and how you communicate findings to different audiences. Fragments work here. Exec summary. Technical appendix. Scope notes. The usual dance.
Funny thing is, I've seen people nail the technical sections and then fumble basic reporting questions because they never wrote an actual pentest report for a client. They know how to pop shells but can't explain business impact in two sentences.
The biggest failure pattern? Not enough hands-on. Simple.
Candidates miss questions because they memorized definitions but can't reason through a scenario asking "what tool or method fits here" or "what does this output mean," and the exam's packed with those, especially around application security analysis and app-layer exploitation logic.
Common mess-ups I keep seeing:
- Insufficient practice with security tools, so command syntax and output questions become coin flips
- Weak web testing foundation, which hurts because web and app security questions tend to be detailed and scenario-driven
- Terrible time management, which means the last 25 questions become panic clicking
- Attempting ECSA without CEH-level baseline or equivalent real experience, so the methodology and engagement flow feels abstract
- Relying on dumps, which you might recognize a question, but if the wording shifts or the scenario changes even slightly, you're stuck
Recommended background? Pretty straightforward, honestly. CEH knowledge or something equivalent, decent networking chops, Linux fundamentals. The thing is, you really need hands-on time running actual scans and poking at applications in lab environments before this makes sense. If you've tackled vulnerability assessments in your day job, the exam workflow just clicks because you've already lived through that grind of identifying issues, prioritizing them based on business impact and exploitability, documenting everything, and explaining technical findings to stakeholders who might not share your technical vocabulary.
Context matters.
I've seen people blow through the material with zero lab time and then freeze up when they hit the practical sections. Not pretty.
EC-Council opens eligibility two ways: complete their official training course, or go the application route where you'll document your real-world experience in penetration testing and security assessments. Honestly, check their current policy before you drop cash because requirements shift, forms get updated, and you don't wanna get blindsided.
Not there yet? Don't push it. I mean, seriously, build your foundation with CEH-level content first, then dedicate serious lab hours to web application testing, vulnerability scanning, basic exploitation techniques, and writing concise reports from your own findings, even if they're just practice scenarios. A small weekly routine? It'll beat frantic cramming every single time.
Official courseware fits with the exam tone. The labs? Actually do them. Take notes. They'll help with tool familiarity and output recognition, which is where most people lose points without even realizing it. I've seen folks skip the labs entirely because they think they already know the tools, then they blank on interpreting results under pressure.
Use PTES and OWASP Testing Guide style references for methodology and web testing. NIST guidance helps for process thinking. Also, keep a personal cheat sheet of commands and "what this output usually means." That's how you get faster without just guessing wildly and hoping something sticks, which wastes time you don't have during the actual exam when stress levels are high. Some people love massive reference binders. I don't. They slow you down when you're hunting for one specific syntax example.
Kali or Parrot. A couple target VMs like OWASP Juice Shop and DVWA work great. Metasploitable's solid for service testing. Add Burp Suite, ZAP, Nmap, and a notes system you can search fast.
One sentence. Take screenshots.
ECSA Practice Tests and Exam Prep Strategy
Look for reputable ECSA practice tests that actually explain answers. Don't just settle for ones that score you and move on. Here's the thing: if a practice bank feels like you're grinding through trivia questions with zero rationale behind why something's correct or incorrect, it won't train the specific skill ECSA's really asking for. You need to pick the best action in a scenario when you're under serious time pressure and second-guessing yourself.
Do timed sets. Period.
Review wrong answers by mapping them to methodology stages and tool behavior. This part's key. Then go reproduce the concept in a lab. Why? Because that transforms "I saw it once" into "I can recognize it under stress," and that's the whole game here, if we're being real.
Long rambling truth: if you can't explain why the right answer is actually right and why the tempting wrong answer is wrong (you know, the one that almost got you), you don't own the topic yet. The real exam will find that weak spot and poke it repeatedly for four exhausting hours. I've watched people who knew their stuff inside and out still bomb questions because they never practiced explaining their reasoning out loud. Sounds dumb but try it sometime.
Sleep matters. Eat something decent.
Do one or two timed blocks to stay sharp, but don't learn brand-new tools the night before. That's just asking for confusion and panic. During the exam itself, mark questions and move on when you're stuck, because burning five minutes early on one tricky question can snowball into you rushing through easier ones later and making careless mistakes you'd normally catch.
ECSA Renewal, Validity, and Continuing Education
Look, ECSA typically follows EC-Council's validity cycle rules. I mean, you'll want to verify the current term in your Aspen portal or official policy docs, honestly, because dates and requirements can change without much warning. One year they're saying three years, the next they've tweaked something, and you're left wondering what happened.
Renewal usually means ECE credits plus fees, tracked across the cycle. Keep receipts and proof. Don't wait until the last month and then scramble.
The thing is, it's ridiculously easy to procrastinate on this stuff until you've got like two weeks left, which I've definitely seen colleagues do, and then they're panicking about whether their webinar from eighteen months ago actually counts or if they've got enough documentation. Sometimes I think the whole ECE system exists just to teach time management the hard way.
Training courses count.
Security conferences and webinars often count too. Writing technical blogs or presenting internal training can count if documented correctly. Just make sure you're actually recording what you did, when you did it, and how it ties back to the certification body's requirements because the approval process isn't always straightforward. Keep a spreadsheet. Update it as you go, not six months later when you can't remember which CTF you participated in or whether that lunch-and-learn session was forty-five minutes or two hours.
Frequently Asked Questions (FAQ)
ECSA exam cost: what's the total budget?
Budget for the voucher. Add training. Honestly, throw in a retake buffer if you're not nailing timed practice consistently. The total? It'll swing wildly depending on whether your employer foots the bill and whether you spring for the official ECSA training course. I've watched colleagues argue for hours about whether the official training is worth it, and honestly, that debate wastes more time than just booking the thing.
ECSA passing score: is it fixed or scaled?
Treat it as variable. Different exam forms, different cutoffs. I mean, don't chase some magic number. Aim to be comfortably crushing any rumored threshold by actually mastering scenarios and tool interpretation instead.
Best study materials and practice tests for ECSA
Official courseware gives you alignment. OWASP/PTES/NIST for methodology. Practice tests with explanations are critical. But here's the thing: pair everything with labs, because this exam absolutely punishes "book-only" prep. I've seen that wreck people who thought they could memorize their way through.
ECSA prerequisites: do you need CEH first?
Not always formally. Practically? Yeah, you'll want CEH-level baseline or equivalent hands-on time under your belt. Going straight to ECSA without that foundation raises difficulty. Like, a lot.
ECSA renewal: how often and how to maintain it?
Track ECEs continuously. Pay attention to deadlines. Keep documentation tight. The thing is, if you treat renewal like a yearly habit instead of some last-minute fire drill, it's totally fine.
Conclusion
Wrapping up your ECSA path
Look, the EC-Council 412-79 ECSA certification isn't something you just walk into and wing it. You're dealing with application security analysis, vulnerability assessment and reporting, and actual penetration testing methodology that goes way beyond memorizing port numbers and attack vectors. Honestly, it's a whole different beast when you're not just running tools but actually understanding what the output means and how to communicate it to someone who signs checks.
The ECSA exam 412-79 sits in this weird middle ground. Harder than CEH, for sure. Why? You need to actually demonstrate skills, not just recognize concepts. But it's not as brutal as some of the more advanced certs out there, so there's that. The ECSA passing score (70% typically) sounds reasonable until you're staring at questions that require you to analyze actual scan results and decide on remediation priorities under time pressure.
Here's what I think matters most: the ECSA training course and hands-on practice. I mean, you can read every book, watch every video, but if you haven't spent time doing web application testing and ethical hacking and security analysis in a real or simulated environment, you're gonna struggle. Period. The ECSA v10 exam tests application, not memorization. That's where most people trip up.
The ECSA exam cost stings. Not gonna lie. Between the voucher, training materials, and potentially a retake if things don't go your way the first time, you're looking at a solid investment. Actually, that's exactly why practice becomes non-negotiable. You need to know where your gaps are before you sit for the actual exam. I learned this the hard way with a different cert once, spent three months prepping but missed entire sections that turned out to be heavily weighted. Never again.
If you're serious about passing on your first attempt, I'd recommend checking out the 412-79 Practice Exam Questions Pack at /eccouncil-dumps/412-79/. Real talk, quality ECSA practice tests make the difference between walking in confident versus second-guessing every answer. You want exposure to the question style, the scenario complexity, and the time pressure before it actually counts.
The thing is, the ECSA practical exam component means you can't fake your way through this one. But that's also what makes the EC-Council Certified Security Analyst credential actually valuable to employers. They know you've proven something beyond test-taking skills. Get your hands dirty, use solid prep materials, and you'll get there.