312-49 Practice Exam - Computer Hacking Forensic Investigator
Reliable Study Materials & Testing Engine for 312-49 Exam Success!
Exam Code: 312-49
Exam Name: Computer Hacking Forensic Investigator
Certification Provider: ECCouncil

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
312-49: Computer Hacking Forensic Investigator Study Material and Test Engine
Last Update Check: Mar 19, 2026
Latest 531 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena ECCouncil Computer Hacking Forensic Investigator (312-49) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
ECCouncil 312-49 Exam FAQs
Introduction of ECCouncil 312-49 Exam!
ECCouncil 312-49 is the exam for the Certified Ethical Hacker (CEH) certification. It is a comprehensive exam that tests a candidate's knowledge and skills in ethical hacking and information security. The exam covers topics such as network security, cryptography, malware, and web application security.
What is the Duration of ECCouncil 312-49 Exam?
The duration of the ECCouncil 312-49 exam is 4 hours.
What are the Number of Questions Asked in ECCouncil 312-49 Exam?
There are a total of 125 questions on the ECCouncil 312-49 exam.
What is the Passing Score for ECCouncil 312-49 Exam?
The passing score required in the ECCouncil 312-49 exam is 70%.
What is the Competency Level required for ECCouncil 312-49 Exam?
The ECCouncil 312-49 exam is designed to test the knowledge and skills of a Certified Ethical Hacker (CEH). To be eligible to take the exam, candidates must have at least two years of experience in the information security field and must have completed the official CEH training course. The exam is divided into six domains, each of which covers a different area of ethical hacking. The competency level required to pass the exam is Expert.
What is the Question Format of ECCouncil 312-49 Exam?
The ECCouncil 312-49 exam consists of multiple-choice questions, drag and drop questions, fill-in-the-blank questions, simulation questions, and short answer questions.
How Can You Take ECCouncil 312-49 Exam?
ECCouncil 312-49 exam is offered online via an online proctored exam and in a testing center. The online proctored exam can be taken from anywhere with an internet connection and webcam, while the testing center option requires you to physically attend a designated testing center.
What Language ECCouncil 312-49 Exam is Offered?
ECCouncil 312-49 Exam is offered in English.
What is the Cost of ECCouncil 312-49 Exam?
The cost of the ECCouncil 312-49 exam is $250 USD.
What is the Target Audience of ECCouncil 312-49 Exam?
The target audience for the ECCouncil 312-49 exam is information security professionals who need to demonstrate their knowledge and skills in computer forensics. This certification is designed for experienced professionals who have a background in information security, computer forensics, and incident response.
What is the Average Salary of ECCouncil 312-49 Certified in the Market?
According to PayScale, the average salary for someone holding an ECCouncil 312-49 certification is $62,831 per year.
Who are the Testing Providers of ECCouncil 312-49 Exam?
The ECCouncil provides official training and certification exams for the 312-49 exam. The official training materials and exam can be found on the ECCouncil website. Additionally, there are several third-party training providers and websites that offer practice tests and other resources to help prepare for the exam.
What is the Recommended Experience for ECCouncil 312-49 Exam?
The recommended experience for the ECCouncil 312-49 exam is at least two years of practical experience in IT security auditing, including topics such as system and network security, network access control, vulnerability assessment, and incident response. Knowledge of computer forensics, cryptography, and international standards for information security management are also recommended.
What are the Prerequisites of ECCouncil 312-49 Exam?
To become a EC-Council Certified Incident Handler (ECIH), applicants must first pass the EC-Council Certified Incident Handler (ECIH) Exam (312-49) and fulfill the following prerequisites:
* Complete the EC-Council Certified Incident Handler (ECIH) Training course with a passing grade
* Have a minimum of 2 years of working experience in the information security domain
* Agree to the EC-Council Code of Ethics
What is the Expected Retirement Date of ECCouncil 312-49 Exam?
The expected retirement date of the ECCouncil 312-49 exam is not available online. You can contact ECCouncil directly for more information. Their contact information can be found on their website: https://www.eccouncil.org/contact-us/.
What is the Difficulty Level of ECCouncil 312-49 Exam?
The difficulty level of the ECCouncil 312-49 exam is considered to be moderate to difficult. It requires a good understanding of the concepts and technologies related to computer forensics and digital investigations.
What is the Roadmap / Track of ECCouncil 312-49 Exam?
The ECCouncil 312-49 Exam is part of the EC-Council Certified Security Analyst (ECSA) certification track. It is a five-hour exam that tests an individual's knowledge and skills in ethical hacking and penetration testing. The exam covers topics such as network scanning, vulnerability analysis, system hacking, and countermeasures. Successful completion of the exam earns the individual the ECSA certification.
What are the Topics ECCouncil 312-49 Exam Covers?
ECCouncil 312-49 exam covers the following topics:
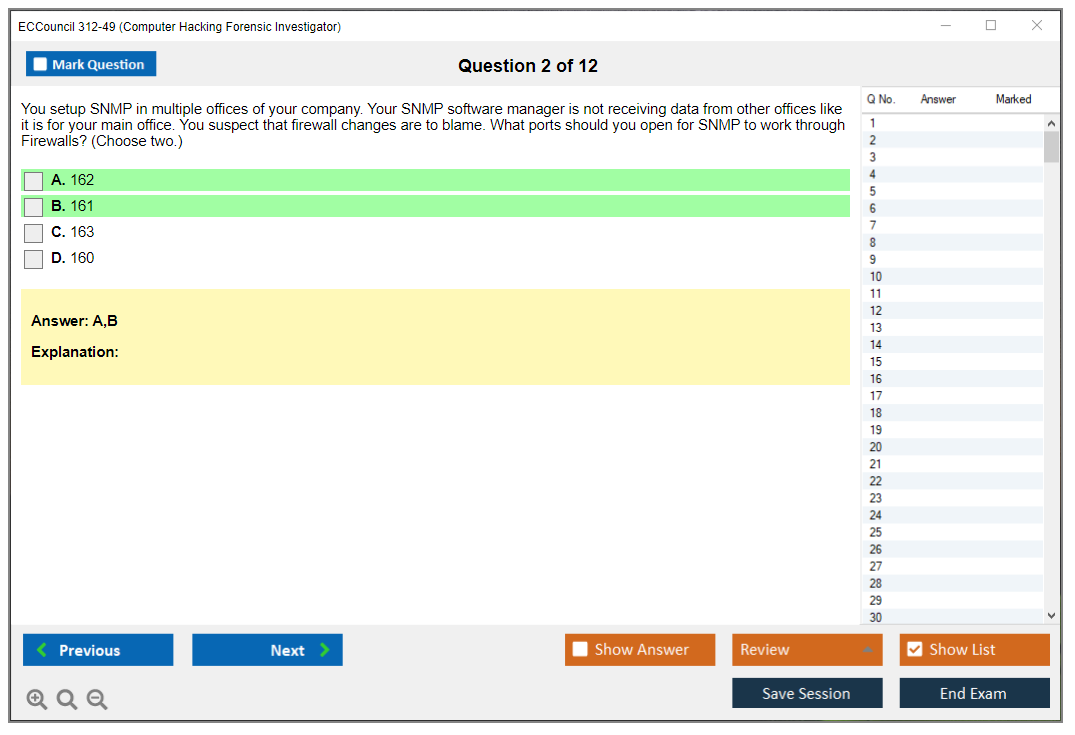
1. Network Security: This topic covers the fundamentals of network security, including firewalls, intrusion detection systems, and network access control. It also covers topics such as secure network architecture, secure communications, and network security assessment.
2. Cryptography: This topic covers the basics of cryptography, including encryption algorithms, key management, digital signatures, and authentication protocols. It also covers topics such as secure storage and transmission of data, and secure communication protocols.
3. System Security: This topic covers the fundamentals of system security, including operating system security, application security, and security policy. It also covers topics such as system hardening, patch management, and system security auditing.
4. Disaster Recovery and Business Continuity: This topic covers the fundamentals of disaster recovery and business continuity, including planning, implementation, and testing. It also covers topics such as data backup and recovery, and disaster recovery
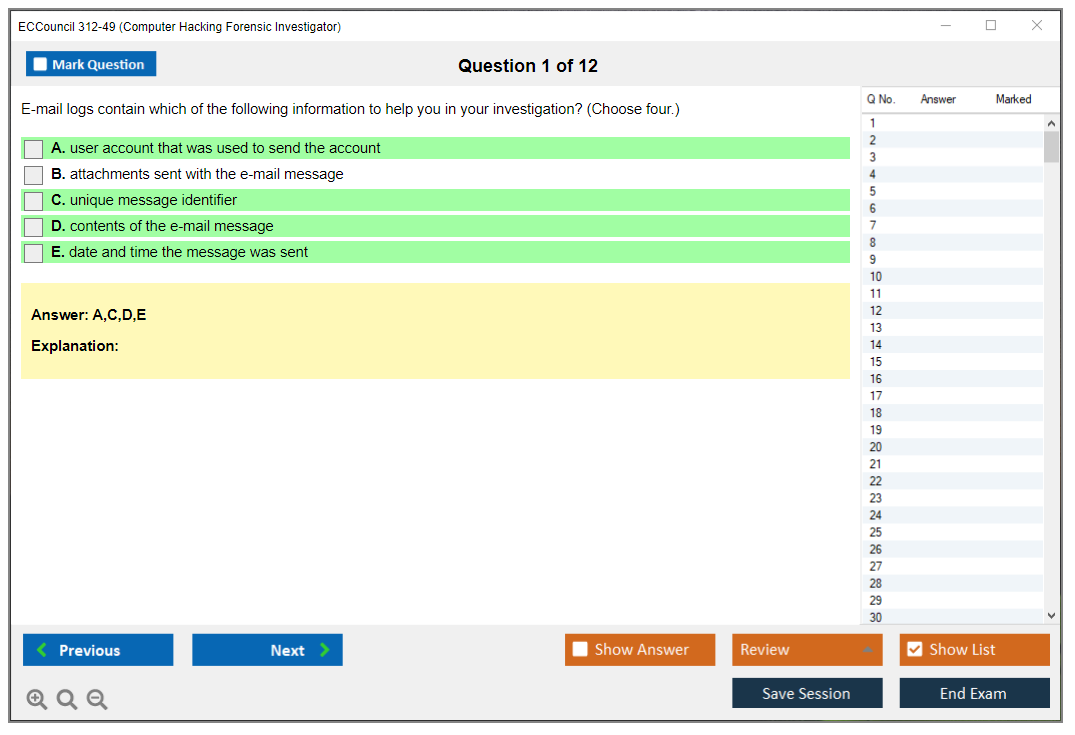
What are the Sample Questions of ECCouncil 312-49 Exam?
1. What is the purpose of the Security Event Manager (SEM) tool?
2. What are the different types of attacks that can be detected using the Intrusion Detection System (IDS)?
3. What is the purpose of using a honeypot in a network?
4. What is the difference between a false positive and a false negative in an IDS?
5. What are the steps involved in the incident response process?
6. What is the purpose of an intrusion prevention system (IPS)?
7. What is the purpose of the Network Intrusion Detection System (NIDS)?
8. What are the benefits of using a honeynet?
9. What is the difference between a vulnerability scan and a penetration test?
10. What is the purpose of a Security Information and Event Management (SIEM) system?
EC-Council CHFI 312-49 (Computer Hacking Forensic Investigator) Overview What CHFI validates (digital evidence + incident response skills) The ECCouncil 312-49 CHFI certification proves you've got what it takes to investigate cyberattacks from start to finish. Seriously practical stuff. You're showing you know how to detect when someone's breached a network, collect evidence without screwing up the integrity, analyze what the attacker actually did, and present findings that'll hold up in court. One documentation mistake and everything falls apart legally. The computer forensics investigator certification covers imaging suspect hard drives, tracing network packets, reconstructing deleted files attackers tried desperately to hide. CHFI goes deep on the complete investigation lifecycle. Initial incident detection, evidence preservation using proper forensic tools and techniques, analysis across Windows, Linux, mobile devices, cloud environments, network traffic, and final reporting that... Read More
EC-Council CHFI 312-49 (Computer Hacking Forensic Investigator) Overview
What CHFI validates (digital evidence + incident response skills)
The ECCouncil 312-49 CHFI certification proves you've got what it takes to investigate cyberattacks from start to finish. Seriously practical stuff. You're showing you know how to detect when someone's breached a network, collect evidence without screwing up the integrity, analyze what the attacker actually did, and present findings that'll hold up in court. One documentation mistake and everything falls apart legally.
The computer forensics investigator certification covers imaging suspect hard drives, tracing network packets, reconstructing deleted files attackers tried desperately to hide. CHFI goes deep on the complete investigation lifecycle. Initial incident detection, evidence preservation using proper forensic tools and techniques, analysis across Windows, Linux, mobile devices, cloud environments, network traffic, and final reporting that meets legal standards. The chain of custody in digital forensics component? Huge. One screwup in documentation can make months of investigative work inadmissible.
This cert's practical. You're proving competency in examining file systems, digging through Windows registry artifacts, conducting memory forensics to catch malware living only in RAM, analyzing network packet captures, investigating email headers and metadata, database forensics, collecting evidence from cloud service providers. The CHFI 312-49 exam tests whether you can actually do this stuff, not just recognize vocabulary.
Who should take CHFI (roles and career outcomes)
Makes sense for incident responders showing up after breaches. SOC analysts wanting to move beyond alert triage into actual investigation work. Security consultants needing to deliver forensic services. Law enforcement investigating cybercrime. System administrators suddenly handling security incidents. IT auditors too, verifying whether controls actually prevented data exfiltration. The thing is, most IT folks eventually touch incident response whether they planned to or not.
Career outcomes? Digital forensics analyst positions, incident response specialists at consulting firms or enterprise security teams, cybercrime investigators (corporate or government), forensic consultants charging premium rates, security analysts with specialized investigation skills, expert witnesses testifying in legal proceedings. Organizations value CHFI-certified professionals because they conduct thorough investigations while maintaining evidence integrity throughout the process, support legal teams with technically sound findings, implement forensic readiness programs making future incidents easier to investigate.
The credential pairs well with other security certs. Got CEH or Security+? CHFI adds the post-incident investigation piece. You know how to break in AND how to investigate after someone else breaks in. Works well with EC-Council's Certified Incident Handler too, creating a complete incident response skill set.
Exam format, question types, and time limit
The exam throws 150 multiple-choice questions at you. Four hours total. Sounds generous until you're reading through scenario descriptions, analyzing evidence snippets, or choosing the correct forensic procedure from similar-sounding options. It's proctored, either at a testing center or through remote proctoring if you prefer taking it at home.
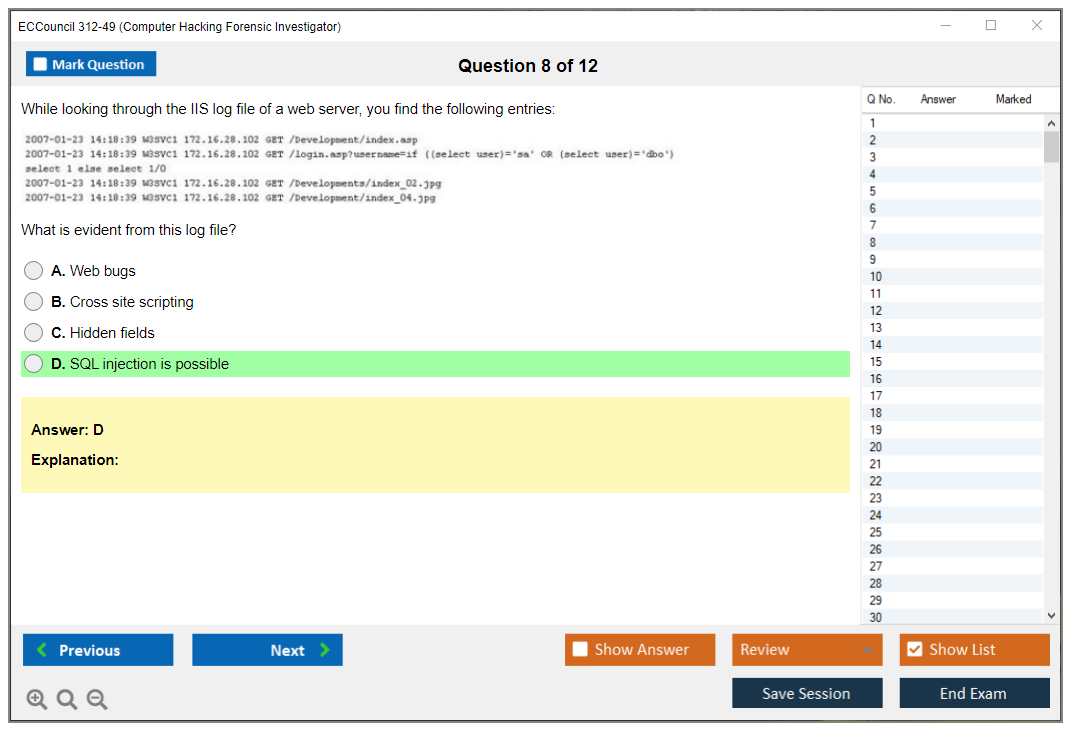
Questions test practical knowledge. You'll see scenarios like "An investigator images a suspect drive and the MD5 hash doesn't match after transfer. What went wrong?" or "Which Windows artifact shows USB devices that were previously connected?" or "In this network capture, identify the data exfiltration method." Some questions present investigation workflows, asking you to identify the step that violates proper procedure or breaks chain of custody.
Passing score (what to expect and how it's determined)
The CHFI passing score sits around 70%, but EC-Council uses scaled scoring so the exact raw number varies slightly between exam versions. You need roughly 105-110 questions correct out of 150. They don't tell you the precise cutoff beforehand. Annoying but standard for vendor certs.
Scaled scoring means exam difficulty's normalized. Get a slightly harder version? The passing threshold adjusts slightly downward. Easier version? It adjusts up. You see your score immediately after finishing (pass or fail plus numerical score), and honestly, most people either pass comfortably or fail by a noticeable margin rather than landing right on the borderline.
Difficulty (what makes CHFI challenging + who finds it easier)
Moderately difficult. Harder than Security+ but probably easier than GCFA if you're comparing forensics certs. The challenge? Breadth. You need to know Windows forensics AND Linux AND mobile AND network AND cloud AND legal procedures. People struggling usually lack hands-on experience with forensic tools or don't understand the "why" behind procedures.
Who finds it easier? People with incident response experience. Anyone who's actually imaged evidence drives before. Folks who've worked with tools like Autopsy, FTK, or Volatility. System administrators understanding file systems and registry structure. Anyone investigating actual security incidents. If you've only done offensive security testing, the investigative mindset shift takes adjustment.
What trips people up? Anti-forensics techniques. Attackers use encryption, steganography, file wiping, timestamp manipulation, log deletion to hide evidence. You need to recognize these techniques and know workarounds. Also, legal and ethical considerations. Search and seizure laws, privacy regulations, international evidence handling standards, expert testimony requirements. Technical skills alone won't cut it.
Exam voucher cost (typical price ranges and factors)
The ECCouncil CHFI exam cost runs around $950-$1,100 USD for just the exam voucher, depending on regional pricing and whether you're buying directly from EC-Council or through a partner. Yeah, it's expensive. That's EC-Council's pricing model across their certifications.
Sometimes you'll find discounts during promotional periods or if you're military, government, student. Training bundles including courseware, labs, and the exam voucher typically cost $2,500-$4,000, which sounds steep until you realize the official training alone normally costs $2,000+. Paying out of pocket and already have forensics background? Buying just the voucher and self-studying makes sense.
Training bundle vs voucher-only (pros and cons)
Official training bundles give you structured courseware, hands-on labs with pre-built evidence scenarios, access to EC-Council's iLearn platform, practice questions. The labs? Actually valuable because they provide realistic evidence artifacts you can analyze without building your own lab environment. For beginners or people switching from other IT fields, the training's really helpful.
Voucher-only works if you've got forensics experience and access to practice environments. You save thousands of dollars but need discipline covering all CHFI exam objectives thoroughly. I went voucher-only because I'd already done incident response work, but I spent serious time in home labs analyzing sample disk images and memory dumps.
Retake fees and policies (what to confirm before buying)
Retakes cost the same as the initial exam. Another $950-$1,100. Ouch. EC-Council makes you wait a certain period before retaking (think it's 14 days minimum, but confirm current policy). Some training packages include one free retake, which's worth considering if you're not confident about passing first attempt.
Always check the voucher expiration date. EC-Council exam vouchers typically expire 12 months after purchase. Buy a voucher and don't schedule within that window? You lose the money. Plan your study timeline before purchasing.
Digital evidence fundamentals (law, ethics, chain of custody)
This domain covers legal frameworks for digital investigations. Search and seizure laws, privacy regulations like GDPR and CCPA, rules of evidence, how to work with law enforcement and legal counsel. You learn proper chain of custody documentation: who handled evidence, when, where, why, and what they did with it. Every transfer must be documented because defense attorneys'll challenge evidence integrity.
Hashing's critical here. You create MD5, SHA-1, or SHA-256 hashes of evidence before and after every operation to prove it wasn't modified. Imaging procedures, write blockers preventing accidental modification of original media, proper storage and handling, maintaining professional objectivity even when investigating coworkers or friends.
Forensic readiness and investigation process
Organizations preparing for incidents before they happen investigate faster and more effectively afterward. Forensic readiness means having logging configured properly, retention policies defined, incident response procedures documented, forensic tools and licenses ready, trained personnel identified, legal considerations addressed proactively.
The investigation process follows defined phases: preparation and authorization, identification of evidence sources, evidence collection and acquisition, examination and analysis, reporting findings, potentially presenting in legal proceedings. Each phase's got specific procedures and documentation requirements.
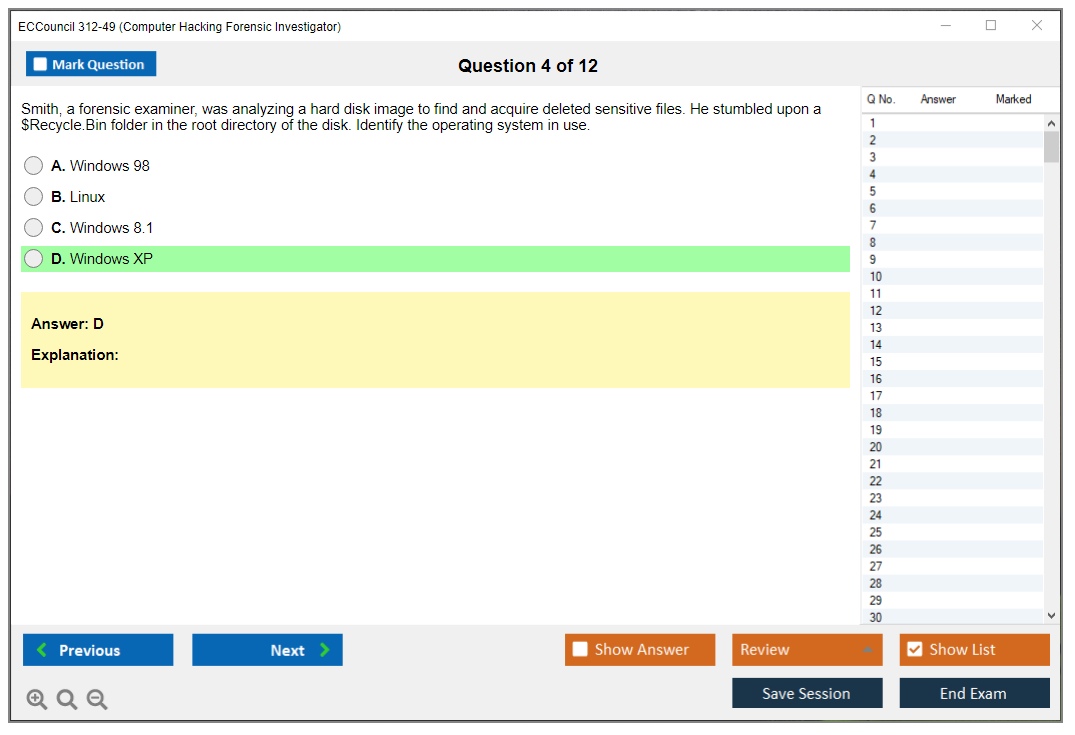
Windows, Linux, and file system forensics
Windows forensics digs into NTFS artifacts like $MFT (Master File Table), $LogFile, $UsnJrnl, Volume Shadow Copies, registry hives (SAM, SYSTEM, SOFTWARE, NTUSER.DAT), event logs, prefetch files showing program execution, Windows Search database, browser artifacts, more. You learn where Windows stores evidence of user activity and how to extract it even after deletion attempts.
Linux forensics covers ext3/ext4 file systems, journal analysis, bash history, log files in /var/log, cron jobs, authentication logs, process memory, Linux-specific artifacts. File system forensics includes understanding inodes, slack space, unallocated clusters where deleted file fragments hide, file carving to recover files without file system metadata. Sometimes you find entire emails or documents just sitting in unallocated space waiting to be reassembled.
Memory, malware, and artifact analysis basics
Memory forensics captures RAM contents finding malware existing only in memory, encryption keys, passwords, network connections, running processes, other volatile data lost when a system powers down. Tools like Volatility let you analyze memory dumps to reconstruct what was happening at capture time.
Malware investigation techniques include static analysis (examining code without executing it), dynamic analysis (running malware in isolated sandboxes), identifying indicators of compromise, reverse engineering basics, recognizing packing and obfuscation techniques. Artifact analysis means examining remnants left by user or system activity. Temp files, recently accessed documents, USB connection logs, browser history, email metadata, you name it.
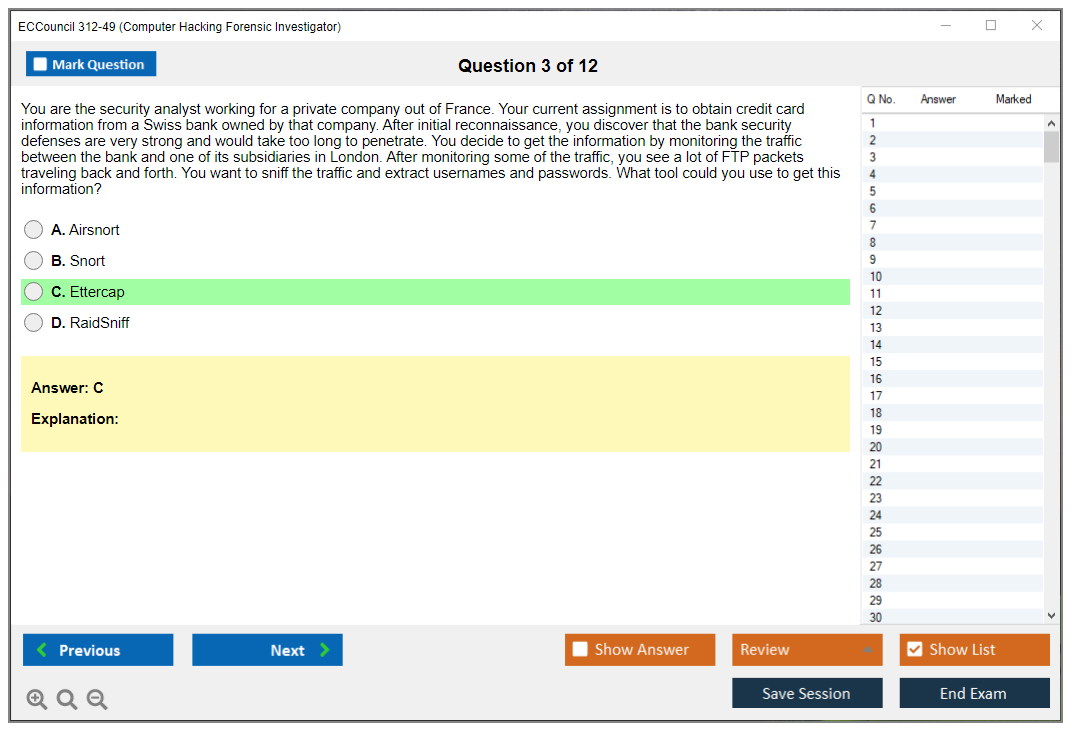
Network forensics and log analysis
Network forensics involves capturing and analyzing network traffic using tools like Wireshark or tcpdump, identifying suspicious patterns, reconstructing network sessions, detecting data exfiltration, analyzing protocol anomalies. You learn to spot command-and-control traffic, lateral movement, port scanning, other attack indicators in packet captures.
Log analysis covers aggregating logs from multiple sources (firewalls, IDS/IPS, servers, applications), correlating events across systems to build attack timelines, identifying log tampering or gaps indicating anti-forensics, using SIEM platforms effectively. Properly configured logging's often the difference between identifying an attacker and having no idea what happened.
Email, web, database, and cloud forensics concepts
Email forensics examines headers to trace message origin, analyze metadata, recover deleted messages, investigate phishing campaigns, handle email as evidence. Web forensics covers browser artifacts (history, cookies, cache, downloads), investigating web server compromises, analyzing web application logs, examining website defacement incidents.
Database forensics involves examining database logs, recovering deleted records, identifying unauthorized access or data modification, handling database evidence properly. Cloud forensics gets complicated because evidence lives on third-party infrastructure. You need to understand cloud service provider data retention policies, legal processes for obtaining cloud evidence (subpoenas, warrants, direct cooperation), challenges with multi-tenant environments and jurisdictional issues.
Reporting and presenting findings (documentation best practices)
Investigation reports must be clear, accurate, technically detailed yet understandable to non-technical readers, legally defensible. You document methodology, tools used, evidence examined, findings, conclusions, limitations. Reports support legal proceedings, management decisions, insurance claims, regulatory compliance demonstrations.
Expert witness testimony requires explaining technical findings to judges and juries without technical backgrounds, withstanding cross-examination, maintaining credibility under pressure, presenting opinions based on sound methodology. The certification covers basics of courtroom testimony and professional ethics expected of forensic investigators handling sensitive information.
Prerequisites (official requirements vs practical recommendations)
Official CHFI prerequisites are minimal. EC-Council suggests two years of information security experience but doesn't strictly enforce it. You can take the exam without proving prior experience, though you'll struggle without practical background.
Practical recommendations? Understand networking fundamentals (TCP/IP, protocols, packet structure). Know operating system internals for Windows and Linux (file systems, process management, registry or configuration files, logging). Have basic security knowledge covering common attacks, malware types, defensive concepts. Completely new to IT security? Honestly, start with Security+ or Network Defender first.
Suggested background (networking, OS internals, security fundamentals)
Networking knowledge helps you understand network forensics sections and trace attacker movement across systems. OS internals knowledge's critical because forensic artifacts are deeply embedded in how operating systems work. Security fundamentals provide context for why you're looking for specific indicators and what attacker techniques look like.
Hands-on experience beats theoretical knowledge. Never imaged a hard drive? Never mounted a forensic image read-only or analyzed artifacts with actual tools? You'll find exam scenarios confusing. Build a home lab with virtual machines, download sample evidence files from forensic challenge websites, practice with tools like Autopsy (free) before spending money on commercial suites.
Who should take a fundamentals course first (and which topics)
Transitioning from non-security IT roles? Take a digital forensics fundamentals course covering basic concepts, tools overview, investigation procedures. People without Windows administration background should study Windows internals specifically. Registry structure, event log types, NTFS features, user profile artifacts.
Anyone unfamiliar with Linux should learn basic command-line forensics, log file locations, Linux file system structure. Legal concepts foreign to you (chain of custody, evidence admissibility, privacy laws)? Study those separately because they're tested but often glossed over in technical training.
Official EC-Council materials (courseware, labs, iLearn)
EC-Council's official courseware's full but expensive. The iLearn platform provides structured modules, video instruction, knowledge checks. Labs give you hands-on practice with evidence scenarios: analyzing compromised systems, investigating data breaches, recovering deleted files, examining malware infections.
The labs? Honestly the best part of official training. They provide realistic evidence without you having to source or create it. Buy training? Actually do the labs multiple times until procedures become automatic. Don't just watch videos and read slides.
Books and references (digital forensics + incident response)
For self-study, look at books covering digital forensics methodologies and specific platforms. "File System Forensic Analysis" by Brian Carrier's excellent for understanding how file systems work at a deep level. Books on Windows forensics, memory forensics with Volatility, network forensics with Wireshark fill knowledge gaps.
Supplement with free resources like SANS reading room whitepapers, vendor documentation for forensic tools, case studies from real investigations (sanitized for publication). Online forensic challenges from sites like CyberDefenders or Digital Corpora provide practice evidence to analyze.
Hands-on labs (VM setup, artifacts, evidence collection practice)
Build a home lab with virtual machines running Windows and Linux. Create your own artifacts by browsing websites, installing programs, creating and deleting files, connecting USB devices, running scripts. Then practice collecting and analyzing those artifacts using forensic tools.
Download sample disk images and memory dumps from forensic challenge repositories. Work through them systematically, documenting findings as if preparing a real investigation report. Practice with both commercial tools (many offer trial versions) and open-source alternatives like Autopsy, Sleuth Kit, Volatility that you'll actually use in budget-conscious environments.
Notes and study plan (4-8 week templates by experience level)
With forensics experience? Plan 4-6 weeks of focused study covering exam objectives, practice labs, weak areas. Without experience, budget 8-12 weeks including time to learn foundational concepts and build hands-on skills.
Map exam objectives to study materials and track coverage. Spend more time on hands-on practice than reading. Schedule regular lab sessions analyzing evidence, not just reading about analysis techniques. Review legal and procedural topics even though they're less interesting because they're heavily tested.
Practice tests (how to choose reliable question banks)
Quality CHFI practice tests simulate actual exam question styles and difficulty. Look for practice exams explaining why answers are correct and incorrect, not just providing answer keys. Avoid brain dumps simply memorizing actual exam questions. They violate EC-Council policies and don't actually teach you forensics.
Good practice tests cover all exam objectives proportionally, use scenario-based questions similar to the real exam, include detailed explanations referencing specific forensic concepts or procedures. Free practice questions exist but usually lack explanation quality of paid options.
How to use practice exams effectively (review + weak-area loops)
Take an initial practice exam establishing baseline knowledge and identifying weak domains. Study those weak areas specifically, then retest to verify improvement. Don't just memorize practice question answers. Understand the underlying concepts so you can apply knowledge to different scenarios.
Review every question. Even ones you answered correctly. Sometimes you get the right answer for wrong reasons. Read explanations to reinforce correct reasoning and catch conceptual gaps. Track which objective areas you struggle with and focus additional study there.
Common mistakes (memorizing answers vs learning workflows)
Biggest mistake? Memorizing specific tool outputs or procedures without understanding why they work. Exam questions often twist scenarios slightly from what you've seen before. Only memorized the exact steps for one specific situation? You'll struggle when the question changes details.
Another mistake's neglecting legal and procedural topics because they seem boring compared to technical analysis. The exam tests this stuff extensively. Also, people underestimate anti-forensics knowledge. You need to recognize when attackers have actively tried to hide their tracks and know how to work around those attempts.
CHFI 312-49 Exam Details
What this certification actually proves
The ECCouncil 312-49 CHFI certification is basically the "can you investigate this mess without destroying evidence" credential. Really practical vibe.
It's computer forensics investigator certification with a workplace edge: you're expected to know what to collect, how to collect it, validate it properly, and then explain everything later when someone senior (or legal, or an actual court) asks uncomfortable questions that make you wish you'd documented better.
CHFI isn't about flexing exploit chains or showing off. Nope. It's defensive, procedure-heavy, artifact-focused work where you're documenting absolutely everything like your future self is gonna be cross-examined by a lawyer who really hates you and your methodology.
Who should take it
SOC analysts. Particularly those who keep getting dragged into "can you pull logs and tell us what happened" tickets. Incident responders who already know containment and eradication but want the evidence side to stop feeling hand-wavy or improvised. System admins who keep ending up as the default "forensics person" because they know where the servers live and everyone else is frankly terrified.
New-to-IT people can pass, sure. I mean, it's possible. Just harder. No shortcut exists.
Exam format and question types, straight up
The CHFI 312-49 exam is 150 multiple-choice questions. Four-hour window. That time limit? Matters way more than people admit, honestly, because 150 questions sounds totally manageable until you realize scenario questions make you reread details, second-guess tool choices, and burn minutes.
Quick math here. About 1.6 minutes per question on average. Some questions you'll answer in 20 seconds, others will eat five minutes if you let them.
Question formats vary:
- Single-answer multiple choice. Normal stuff, honestly.
- Multiple-answer selection. These are sneaky because one missed option tanks the whole item completely.
- Scenario analysis. You get a mini incident and have to pick the right forensic procedures, tools, or legal considerations, and the thing is this is where CHFI tries to separate "read a study guide" from "has actually done incident response and evidence handling in real environments."
The exam hits both theory and practical application. You're not just reciting what a hash is, you're deciding when to hash, what to hash, how to prove integrity convincingly, and what to do if the chain of custody in digital forensics gets sloppy or interrupted.
Where you take it (and what proctoring feels like)
Delivery is through EC-Council's Exam Central or Pearson VUE testing centers, which means you can do in-person proctored testing or online remote proctoring, depending on what you buy and what's available regionally.
Identity verification? Strict. Secure room rules apply. No reference materials whatsoever. Continuous monitoring throughout. If you're remote, expect the usual locked-down vibe: clean desk, camera angles verified, maybe a room scan, and zero tolerance for "I was just reading the question out loud while looking away." It's not personal, it's exam integrity.
Preliminary pass/fail shows immediately when you finish. Official certification documentation typically lands within 5 to 7 business days after passing, which honestly feels longer than it should.
Passing score and how EC-Council grades it
The CHFI passing score is 70%. With 150 questions, that's at least 105 correct to clear the bar, though EC-Council can adjust scoring using scaled scoring based on difficulty across versions, which..look, I get why they do it, but it makes prep slightly unpredictable.
That scaling piece matters. You can't game it by hoping for an "easy form." The goal is consistent standards, so a harder set of questions doesn't punish you compared to someone who got a lighter mix.
If you fail, you usually get a domain-level score report showing where you were weak. Actually useful! It lets you stop guessing and start studying the right parts of the CHFI exam objectives instead of wasting time on areas you've already nailed. You won't get the exact questions back. Not gonna lie, that part annoys everyone, but it's normal across most professional certs.
Difficulty and who finds it easier
This exam sits in that intermediate-to-advanced zone. Not "graduate cryptography," but also isn't "what port is HTTPS" foundational stuff.
The challenge? Workflow thinking: preservation, acquisition, analysis, and reporting, while keeping legal admissibility in mind constantly because one mistake can destroy months of investigative work in a courtroom.
People with incident response, security operations, or sysadmin backgrounds tend to find CHFI more accessible, because you already understand logs, file systems, permissions, and what attackers typically touch or modify during intrusions. Candidates new to cybersecurity struggle because CHFI assumes you can interpret artifacts like registry structures, common log formats, network protocols, memory artifacts, and file system internals without needing a full tutorial every question.
Compared to CEH, CHFI is more about defensive investigation and evidence handling than offensive techniques or exploitation. Compared to CompTIA Security+, CHFI goes deeper into evidence analysis and methodologies specifically. Compared to vendor-specific certs like EnCE or ACE, CHFI stays vendor-neutral, covering broader scenarios and multiple forensic tool platforms. Which I mean is good for career flexibility but also means you need breadth, not depth.
I once watched someone fail this thing twice because they kept treating it like a memorization test instead of a decision-making exam, and honestly that tracks with what most people get wrong about forensics work in general.
Exam cost and what you're paying for
People always ask about ECCouncil CHFI exam cost because EC-Council pricing can swing depending on region, promos, and whether you buy training bundles or just the voucher alone. Typical voucher pricing often lands somewhere in the several-hundred-to-over-a-thousand USD range, and yes, that's vague because it changes constantly and bundles muddy the waters intentionally.
What you're paying for depends on the path:
- Voucher-only: cheaper upfront, best if you already have skills and a solid CHFI study guide plan you trust.
- Training bundle: more expensive initially, but you get official courseware and often labs, which helps if you need structured learning or you're trying to convince an employer to reimburse something that looks "complete" and professional.
Retakes matter. Confirm retake policy before you buy anything. Some bundles include discounted retakes, some don't, and the rules can change without warning. Read the voucher terms like you're reading an incident report timeline, because missing a deadline feels exactly as dumb both places.
What the exam actually tests (objectives without the fluff)
CHFI covers all official objectives, with heavier emphasis on practical investigation skills, evidence handling procedures, and forensic analysis techniques. Not just definitions you memorized the night before.
Expect legal frameworks and ethical considerations across jurisdictions and org contexts, because "can we do this" matters as much as "can we extract this" in real investigations.
Core areas you'll see:
- Digital evidence fundamentals. Legal and ethics, professional standards, chain of custody, documentation standards, evidence labeling, storage procedures, hash verification protocols.
- Forensic readiness, which includes logging strategies, monitoring infrastructure, retention policies, incident response planning, and how to prep an org so investigations don't start with "we have no logs because nobody thought it mattered."
- Acquisition covers disk imaging techniques, memory dumping procedures, network capture methods, mobile extraction concepts, and cloud data collection realities that complicate traditional forensics.
- OS and file system forensics: Windows artifacts (registry, event logs, common persistence spots attackers love), Linux basics, file system internals you actually need.
- Memory and malware basics. What volatile artifacts matter most, how attackers hide presence, and what you can still recover post-reboot.
- Network forensics and logs: protocols, packet capture context, proxy/DNS/firewall logs, timeline building from multiple sources.
- Reporting and testimony involves writing court-admissible reports, explaining findings to non-technical stakeholders without condescension, and not overclaiming what the evidence actually proves.
Anti-forensics shows up too. File hiding techniques, encryption obstacles, steganography, evidence tampering methods. You're expected to recognize the tricks and know what "good enough" detection looks like in a real investigation, not a lab fantasy.
Prerequisites and recommended experience
CHFI prerequisites are one of those "official vs practical" conversations that never quite align. Officially, requirements can depend on whether you go through official training or apply via eligibility routes, so verify current EC-Council rules before assuming anything.
Practically, I'd want networking basics, Windows internals basics, comfort with logs in various formats, familiarity with disk concepts and virtualization environments. If you've never imaged a disk, never validated hashes manually, and don't know what the registry is or why it matters, you're stacking difficulty for absolutely no reason.
Some people should take fundamentals first, honestly. If TCP/IP feels foggy or you've never touched a SIEM interface, do Security+ level material or an intro IR course before you try to brute-force CHFI and waste money.
Study materials that won't waste your time
Start with official EC-Council materials if you like structure and official alignment. Courseware plus labs can help, especially for people without daily exposure to forensic tools and techniques in production environments.
Then add references that teach concepts, not exam trivia that expires next version. A good CHFI study guide is the one that forces you to explain processes: acquisition order, integrity checks, documentation standards, and decision points when the scenario changes unexpectedly.
Hands-on matters enormously. Build a small VM lab. Nothing fancy. Windows plus Linux. Practice collecting artifacts, exporting event logs correctly, grabbing memory with a trusted tool, imaging a disk, verifying hashes, and writing a tiny report that states what you did, what you found, and what you didn't prove because honesty matters.
Simple plan: four weeks if you're experienced, eight if you're newer. Fragments in your calendar work. Daily reps build competence.
Practice tests and how to not fool yourself
CHFI practice tests help, but only if you use them to find weak domains, not to memorize patterns you'll never see again. Bad question banks train you to recognize bad writing, not to do forensics properly.
Here's how I'd do it. Take a timed set early. Not to score high, just to find pain points and knowledge gaps. Review every miss and every lucky guess honestly, then map it back to the CHFI exam objectives so you know what topic you actually failed, not just surface symptoms. Repeat with shorter timed drills, because time management is a real constraint and you need to build the "read, decide, move on" muscle memory.
Common mistakes? Obsessing over tool commands, ignoring process entirely. CHFI cares that you know the right workflow, evidence integrity principles, and documentation standards, because in real incidents your mistake can compromise evidence, wreck legal admissibility, or just waste a week of everyone's time chasing ghosts.
Renewal and keeping it active
CHFI renewal requirements run on EC-Council's continuing education model (ECE credits). The cycle length, credit totals, and fees can change periodically, so confirm on EC-Council's current policy page, but the practical advice is stable: track what you do as you go along.
Earn credits through training, webinars, conferences, some work activities, and related learning that actually improves your skills. Save proof immediately. Receipts, completion certs, agendas, notes. If you ever get audited, future you will either thank you profusely or curse you bitterly.
CHFI 312-49 FAQ
How much does the EC-Council CHFI (312-49) exam cost?
ECCouncil CHFI exam cost varies a lot by voucher vs bundle, region, and discounts available at purchase time. Check EC-Council's store and authorized training partners, and confirm what's included (retake terms, labs, official courseware).
What is the passing score for the CHFI 312-49 exam?
The CHFI passing score is 70%, so you're aiming for at least 105 correct out of 150, with scaled scoring possibly adjusting based on form difficulty to maintain consistency.
Is the CHFI certification hard compared to CEH or Security+?
Harder than Security+ for most people because it's deeper on artifacts and investigation process. Different from CEH entirely, because CHFI is defensive and evidence-focused, with more legal and documentation pressure throughout.
What are the best study materials and practice tests for CHFI 312-49?
Official courseware plus hands-on labs, then a solid CHFI study guide that sticks to objectives without fluff, plus reputable CHFI practice tests that explain why answers are right or wrong. Avoid random dumps. They're career poison.
How do CHFI renewal and CPE/EC-Council ECE credits work?
You earn ECE credits across the renewal cycle, pay the required fees, and keep documentation proving completion. Track everything as you do it. Don't rebuild proof at the deadline when panic sets in.
CHFI 312-49 Exam Cost and What You're Paying For
What you're actually buying when you drop cash on the voucher
Look, the ECCouncil CHFI exam cost isn't exactly pocket change. You're staring down $950 to $1,199 USD just for the exam voucher alone, depending on where you live and how you buy it. I've seen people absolutely sticker-shocked when they first check pricing, especially if they're coming from CompTIA certs that run a few hundred bucks.
Here's the thing though. That voucher price isn't random. You get one attempt at the 312-49 exam, preliminary scoring right after you finish (assuming you test at a center or via online proctoring), your official ECCouncil 312-49 CHFI certification upon passing, a digital badge you can slap on LinkedIn, and your initial certification period without hidden fees. No surprise charges for score reports or certificate issuance, which honestly is refreshing.
EC-Council adjusts pricing based on market conditions, regional economics, and when they enhance the program, so what's current today might shift in six months. Always verify through official channels before you budget. I mean, nothing worse than planning for $950 and discovering it's actually $1,150 in your region.
Training bundles versus going solo with just the voucher
You can buy the voucher standalone. Or grab it bundled with training through EC-Council Authorized Training Centers. Training bundles typically run $2,500 to $4,500 depending on delivery format: self-paced, instructor-led virtual, or in-person. That price includes courseware, lab access, exam voucher, and usually some level of instructor support.
The math gets interesting here, honestly. If you're experienced in digital forensics exam preparation and already work with forensic tools daily, buying just the voucher makes sense. You save thousands and study independently using books, labs you build yourself, and maybe a 312-49 Practice Exam Questions Pack for $36.99 to test readiness.
But if you're newer to incident response and evidence handling, those bundled packages provide structure. You get guided labs, instructor Q&A, and courseware that maps directly to CHFI exam objectives. Some bundles even include retake vouchers or guarantees, which protects your investment if you don't pass first try. Not gonna lie, that peace of mind matters when you're dropping four grand.
I went the self-study route because I'd been doing forensics work for a couple years. Saved money but spent probably 60-70 hours building practice environments and tracking down quality study materials. Trade-offs everywhere.
What EC-Council is actually funding with your exam fee
The exam cost funds way more than you'd think. They're basically ensuring questions actually test what they claim to test through psychometric validation. They do ongoing content updates reflecting new forensic tools and techniques, malware trends, cloud evidence collection methods, and legal considerations around chain of custody in digital forensics.
You're also paying for secure delivery infrastructure. Whether you test at a Pearson VUE center or via online proctoring, there's serious backend tech ensuring exam integrity. Technical support during scheduling, score reporting systems, certification verification databases.. all that infrastructure costs real money to maintain.
The exam fee includes access to EC-Council's scheduling system with flexibility to choose testing centers or online proctoring. You get official score reports. Digital badges through Credly or Acclaim. Inclusion in their certification verification system that employers can check.
Compared to vendor-specific forensic certs that lock you into one toolset, CHFI's vendor-neutral approach covers Windows forensics, Linux analysis, memory dumps, network packet analysis, and mobile device examination across multiple platforms. That broader applicability potentially offers better long-term career value, especially if you switch employers or roles. Actually, I knew a guy who got CHFI certified and ended up doing forensics for three different companies in five years, each one using completely different tool suites, and the cert stayed relevant through all of it.
Hidden costs nobody mentions until you're already committed
The exam voucher is just the starting point, the thing is. Budget for additional study materials beyond official courseware. Quality practice tests run $100-300 depending on the provider. The $36.99 practice pack I mentioned is actually on the affordable end. Reference books covering computer forensics investigator certification concepts cost $50-150. If you need lab environments beyond what you can build with VirtualBox and free forensic tools, commercial lab subscriptions add another $50-200 monthly.
Retake fees typically match or slightly reduce the original exam cost. EC-Council's specific retake pricing varies, so confirm before your first attempt. Some candidates budget $2,000 total assuming they might need one retake. Better to plan for it than get caught short.
Time investment is the invisible cost though. Most people need 4-8 weeks of focused study depending on background. If you're working full-time in incident response, maybe you're on the shorter end. Coming from helpdesk or general IT admin roles? Plan for the longer timeline and more hours weekly.
Who gets discounts and how much they save
Government employees, military personnel, and students can access discounted pricing through EC-Council's academic and government programs. Discounts typically run 20-40%, which on a $1,000 exam drops you to $600-800. That's actually significant.
Corporate buyers purchasing multiple vouchers sometimes negotiate volume pricing, though you'd need to go through authorized training centers or EC-Council directly. Individual candidates don't usually get this option unless their employer handles procurement.
Organizations often reimburse certification costs for security, incident response, or forensic roles. I've seen companies cover the full exam fee plus reasonable study material costs, recognizing CHFI validates specialized skills supporting organizational security capabilities. If your employer offers professional development budgets, definitely check eligibility before paying out of pocket.
How CHFI pricing compares to alternatives in forensics
CHFI sits mid-to-premium range. It's definitely pricier than CompTIA Security+ or even Certified Ethical Hacker (CEH), but comparable to SANS GIAC Certified Forensic Analyst (GCFA) which runs around $2,000 for exam-only or $8,000+ with training. EnCE (EnCase Certified Examiner) pricing varies but typically sits similar to CHFI.
The value proposition depends on your career trajectory, honestly. If you're moving into SOC analysis or incident response roles, pairing CHFI with something like EC Council Certified Incident Handler creates a strong forensics-focused credential stack. For broader security careers, CEH might deliver better ROI since it covers more domains.
Look. Vendor-neutral versus vendor-specific is the real differentiator. CHFI doesn't lock you into Magnet AXIOM or FTK or EnCase exclusively. You learn concepts applicable across platforms, which matters in environments where budget dictates tool selection more than analyst preference.
Renewal costs and the three-year calculation
The certification's three-year validity means you're not done spending after passing. Renewal requires earning EC-Council ECE credits through continuing education: training, conferences, webinars, work experience documentation. Renewal fees run $80-200 depending on when and how you renew, plus whatever you spend on ECE-eligible training.
So the real cost calculation? $1,000 exam + $300 study materials + $150 renewal every three years = roughly $1,450 over three years, or about $483 annually. That's actually reasonable for specialized certifications, especially if your employer covers renewal.
Some people stack EC-Council certs and use group renewal discounts. If you hold CCISO and CHFI and CSA, you might save on administrative fees renewing multiple certs at once. Small optimization but worth knowing.
Where to buy and payment mechanics
Purchase exam vouchers directly from EC-Council's website or through authorized training centers. Payment typically accepts credit cards, and corporate buyers can use purchase orders. Some training centers offer financing for bundled packages, spreading $3,500 costs over several months.
Avoid third-party voucher resellers. Or "discounted" exam codes from unauthorized sources. I've heard horror stories of invalid vouchers, no support when scheduling fails, or vouchers that don't actually grant certification upon passing. Stick with official channels even if pricing seems higher. You're paying for legitimacy and support.
No hidden fees for scheduling, score reporting, or digital certificate issuance. Physical certificate shipping might cost extra if you want the fancy paper version for your wall, but digital credentials included in the exam fee work fine for LinkedIn, resumes, and employer verification.
Is the investment actually worth it for your career goals
Honestly? Depends where you're headed. If you're pursuing digital forensics investigator, incident response analyst, or security operations roles requiring evidence handling, CHFI absolutely delivers value. The certification demonstrates vendor-neutral competency in evidence acquisition, analysis, and reporting, skills directly applicable to real-world investigations.
Salary impact varies by market and experience level, but certified forensics professionals typically earn $75,000-$130,000+ annually depending on geography and specialization. If CHFI helps you land a role paying $15,000 more annually, it pays for itself in months.
For general IT professionals without forensics aspirations, the ROI gets murkier. You might get better value from broader security certifications or specializing in cloud, networking, or application security instead.
The 312-49 practice materials help you validate readiness before committing to the full exam fee. Scoring well on practice tests indicates you're ready. Struggling suggests more study time needed before dropping a grand on the real thing.
CHFI Exam Objectives
What CHFI validates (digital forensics + incident response skills)
The ECCouncil 312-49 CHFI certification is EC-Council's "prove you can handle a forensic case without destroying evidence" credential. It sits between pure incident response and pure lab-style forensics. You're expected to know how to collect data cleanly, analyze common artifacts, and write it up so it can survive a lawyer's scrutiny.
This matters at work. A lot. People get slopby. And sloppy breaks cases.
CHFI isn't only about tools. It's workflows, legal constraints, and being able to explain your work like an adult, which is why the CHFI exam objectives read like a full investigation lifecycle instead of a single tech niche. Real cases don't fit in neat tool-shaped boxes, and that's the entire point.
SOC analysts who keep getting pulled into "can you preserve this laptop" requests, that's who. Junior incident responders who can hunt alerts but freeze up when someone says "chain of custody in digital forensics." Internal audit and compliance folks who need to understand evidence handling without becoming reverse engineers.
DFIR interns too. Career switchers sometimes. Consultants, obviously.
If you want a computer forensics investigator certification that maps to real org problems like insider cases, ransomware triage, and policy-driven evidence handling, CHFI can fit. Even if you later jump to something like GCFA and never look back.
The CHFI 312-49 exam is a multiple-choice style exam. EC-Council sticks to their standard format, and it leans heavy on scenario thinking: what do you do first, what do you document, what's admissible, what's the right acquisition method, what artifact proves execution. Time limit and question count can vary by delivery and region, so confirm the current numbers on the voucher page before you schedule. Assumptions get people burned.
Some questions feel like policy. Some feel like tools. A few feel annoying.
If you've done hands-on labs and you've read at least one decent CHFI study guide, the pacing's manageable.
The CHFI passing score isn't a single fixed number published forever. EC-Council uses exam forms and scoring models that can shift. So the practical advice is: treat it like you need to be strong across domains, not a "cram one section and pray" exam.
Aim for consistency. Don't gamble on one topic. Patch the weak zones.
The hardest part's the breadth. The CHFI exam objectives span legal foundations, disk internals, Windows artifacts, network traffic, web logs, cloud acquisition problems, and mobile basics. That's a lot if you've only lived in one environment and suddenly you're expected to know all these different ecosystems.
It's easier if you've already done incident response tickets where you preserved evidence, pulled triage images, reviewed logs, and wrote reports for someone else to act on. The exam keeps coming back to process discipline and proof, not vibes.
People always ask about ECCouncil CHFI exam cost. Prices move. Sales happen. Training bundles change the math completely. In the real world you'll see voucher-only pricing often land somewhere in the mid hundreds to over a thousand USD depending on region, promo windows, and whether you're buying through official channels or an approved partner.
Not cheap. Sometimes employer pays. Sometimes you wait for deals.
My buddy waited three months for a Black Friday discount and saved almost thirty percent. He also spent those three months stressed about the wait, so maybe there's a cost-benefit question there nobody talks about.
Training bundle vs voucher-only (pros/cons)
Bundle makes sense if you need structure and labs, or if your background's more "security generalist" than "forensics hands-on." Voucher-only's fine if you already have a lab, know your artifacts, and just need to map study time to the objectives without someone holding your hand.
One warning. Read the fine print. Know what expires.
Confirm retake rules before you click buy: waiting periods, whether there's a discounted retake option, how long the voucher stays valid, and what happens if you reschedule late. People lose money here because they assume all vendors behave like Pearson VUE with the same policies. They don't.
The CHFI exam objectives cover twelve primary domains, and the first chunk's basically "don't get your evidence thrown out." Computer forensics in today's world is where EC-Council drops the legal and ethical framework: what computer forensics is, what roles exist in an investigation, what your responsibilities are when you touch evidence, and how legal compliance shapes everything you do afterward. Judges don't care about your cool tool if you can't prove you followed proper procedure.
This domain covers search and seizure laws, privacy regulations, evidence admissibility standards, and the ethics piece that people love to ignore until court's involved. Chain of custody's central: you document who had the evidence, when, where it was stored, how it was transferred, and what condition it was in. If you can't prove integrity and control, your technical findings can be treated like fan fiction.
Jurisdiction also shows up here. Different countries treat digital evidence differently, and even within one country you can run into state vs federal differences, workplace privacy rules, and consent requirements. Candidates need to understand how international cooperation and data location issues can change what you're allowed to collect and how you're allowed to collect it.
The computer forensics investigation process domain's the "do it in order and document it" section. It covers pre-investigation prep, evidence identification, collection, preservation, analysis, documentation, reporting, and closure. And yes, you need the boring parts.
Planning matters. Scope matters. Communication matters.
You'll see investigation planning, resource allocation, team coordination, stakeholder updates, and project management concepts for bigger cases. This is where experienced folks get free points because they've already lived the pain of an unplanned investigation where five people image the same system and nobody knows which copy's the authoritative one.
Forensic readiness's a big deal too: logging, monitoring, retention policies, incident response capability, and having playbooks so you're not inventing process at 2 a.m. after a breach. Organizations that prepare up front collect better evidence later, and they spend less time arguing about where the logs are and more time figuring out what happened.
Understanding hard disks and file systems is the part that separates "I ran a tool" from "I know what the tool's doing." You need storage fundamentals, partition structures, file system architecture, and how data's physically stored vs logically presented. Expect FAT/NTFS/exFAT, ext2/3/4, HFS+, APFS, plus metadata, journaling, timestamps, and artifacts you can use for timeline reconstruction.
Disk geometry shows up. Sector addressing, partition tables, boot processes. Also deletion behavior, allocation behavior, recovery behavior. When you get why file carving works and why it sometimes fails, you stop making confident claims based on half a recovered header.
Then you hit OS-specific work. Windows forensics focuses on registry analysis, event logs, prefetch, link files, jump lists, recent docs, browser artifacts, USB tracking, user profiles, application execution evidence, and security logging. The exam loves "what artifact supports this claim," so train yourself to tie activity to a source, not just a guess.
Linux and Mac forensics extends that to Unix-based systems: log locations like '/var/log', shell history, cron jobs, config files, permissions and ownership, plus Mac logs and plist files. Different defaults, different artifacts, different failure modes. People forget Mac forensics exists until the CEO's laptop's involved.
The objectives also push you into anti-forensics and malware, because attackers hide their work and memory often holds the good stuff. Defeating anti-forensics techniques includes encryption detection, steganography, hidden files, timestamp manipulation, log deletion, secure deletion tools, and artifact destruction.
Here's the part worth actually thinking about: you're not only trying to recover data, you're also trying to document that anti-forensics happened. That can show intent or sophistication and it changes how you interpret "missing" logs or weird timestamp clusters. When you see gaps, you don't shrug. You explain them.
Malware forensics is usually tested at the "recognize the approach" level: static vs dynamic analysis, sandboxing, basic reverse engineering concepts, malware types, persistence mechanisms, and indicators of compromise. You won't become a full-time RE from CHFI, but you should be able to preserve samples safely, extract meaningful artifacts, and describe impact.
Network forensics is about capturing and analyzing traffic, reconstructing attacks from packet captures and logs, and understanding protocols like TCP/IP, HTTP, DNS, and SMTP. It also ties directly into incident response and evidence handling because network evidence can be volatile and you need to capture it without breaking the environment or contaminating the story.
Tools come up. Wireshark, tcpdump, NetworkMiner. You correlate logs, you build timelines, you identify C2 patterns or exfil behavior. The hardest questions here are the ones that mix protocol basics with "what would you do next" triage decisions.
Investigating email crimes covers headers, tracing origin, spoofing and phishing indicators, protocol basics (SMTP/POP3/IMAP), and client artifacts like Outlook or Thunderbird, plus webmail considerations. You're looking for proof: header anomalies, authentication results, server hops, mailbox artifacts, and deleted email recovery options.
Investigating web attacks is web server logs and web app attack patterns: SQL injection evidence, XSS attempts, brute forcing, suspicious user agents, weird status codes, and correlating web logs with host compromise. Log formats matter here, and candidates should be comfortable reading Apache, IIS, and Nginx logs without panicking.
Database forensics hits structures, transaction logs, backups, deleted record recovery concepts, and unauthorized access evidence across common platforms like SQL Server, MySQL, and Oracle. You're proving what was queried, changed, or dumped, and when.
Cloud forensics is the modern headache. Evidence acquisition might be API-based, tied to provider cooperation, and complicated by multi-tenancy and data location. Legal considerations show up again, because jurisdiction and contract terms can dictate what you can collect and how fast you can get it.
CHFI keeps circling back to reporting because your analysis is useless if nobody can act on it or defend it. Documentation standards, repeatable steps, screenshots and hashes where appropriate, and clear timelines matter, plus being able to present findings as an expert witness without overclaiming.
Write what you did. Write what you saw. Write what it means.
If you want to score well, map your notes to the objectives and practice explaining conclusions with supporting artifacts. The exam likes "best answer" logic that rewards careful, defensible work.
CHFI prerequisites depend on whether you go through official training or attempt the exam via eligibility options, and EC-Council changes process details over time, so verify current requirements on the official site before you plan. Practically, you want basic networking, OS internals familiarity, and comfort with command line and logs.
CHFI practice tests help most when they're realistic and current. Avoid sketchy dumps. Use practice questions that explain why an answer's right, because "memorize A, B, C" falls apart fast when the exam twists the scenario.
Renewal cycle overview (EC-Council ECE/CE requirements)
CHFI renewal requirements are tied to EC-Council's ECE credit system, fees, and reporting cycles, and you need to track what you submit and keep proof in case of audit. Training, webinars, conferences, and even some work activities can count, but you have to document it like you document evidence.
How much does the EC-Council CHFI (312-49) exam cost? Check current voucher pricing because it varies, and factor training bundles and retakes.
What's the passing score for the CHFI 312-49 exam? It varies by form, so plan to be solid across all domains.
Is CHFI hard compared to CEH or Security+? Broader and more process heavy, less "spot the exploit," more "prove it happened and preserve it."
What're the best study materials and practice tests for CHFI 312-49? Official courseware plus a solid digital forensics exam preparation lab plan, and practice tests with explanations.
How long does it take to prepare? Four to eight weeks is common if you study consistently, faster if you already do forensic tools and techniques work on the job.
Conclusion
Wrapping this up
Look, the ECCouncil 312-49 CHFI certification isn't something you knock out in a weekend. Real talk here. It's a serious exam that tests whether you can actually handle digital forensics work, not just recite definitions. The CHFI 312-49 exam objectives cover everything from chain of custody in digital forensics to memory dumps to cloud artifact analysis, which can feel overwhelming (especially if you're coming in without solid incident response and evidence handling background).
Here's what I've seen work, though. People who treat this like a real forensic investigation tend to hit that CHFI passing score without drama. Methodical, detail-focused, checking their work. The ones who struggle? Usually rushing through a CHFI study guide without actually spinning up VMs, practicing with forensic tools and techniques, or understanding why you'd image a drive before you touch it. I mean the exam's gonna ask you scenario-based questions where you need to know what tool does what and in what order, so there's that.
CHFI practice tests are where most candidates finally connect the dots. You'll spot patterns in how ECCouncil phrases questions around computer forensics investigator certification topics, and you'll catch gaps in your knowledge before exam day costs you $550 or whatever the current ECCouncil CHFI exam cost is. Not gonna lie, that retake fee stings if you show up unprepared.
Mixed feelings here. If you've worked through the CHFI prerequisites, put in your lab time, and you're confident with the digital forensics exam preparation material, you're probably ready. But if you're still second-guessing sections (maybe network forensics or mobile artifact collection) don't schedule yet. Just don't. Spend another week drilling weak spots, because rushing never helps anyone.
Side note, I once watched someone fail by three points because they skipped the mobile forensics section entirely during study. Figured it wouldn't be heavily tested. Wrong call. Cost them another month and another chunk of money they didn't have budgeted.
Before you book that exam voucher, grab the 312-49 Practice Exam Questions Pack and run through it like it's the real thing. Timed. No notes. See where you stand. If you're consistently above 80%, schedule the exam. If not, you know exactly what needs work. The CHFI renewal requirements mean you'll be maintaining this cert for years, so take the time to pass it right the first time.
Show less info
Comments
Hot Exams
Related Exams
EC Council Certified Incident Handler (ECIH v3)
Certified Ethical Hacker Exam (CEHv12)
Linux Security
Computer Hacking Forensic Investigator (CHFI-v10)
EC-Council Certified Security Analyst (ECSA)
EC-Council Information Security Manager (E|ISM)
Certified Network Defender (CND)
EC-Council Certified Security Analyst (ECSA) V10
Computer Hacking Forensic Investigator (v9)
EC-Council Certified Security Specialist (ECSS) v10
EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing
Ethical Hacking and Countermeasures V8
EC-Council Certified Security Analyst (ECSA)
Certified Ethical Hacker Exam (CEH v11)
ECCouncil Computer Hacking Forensic Investigator
Certified Ethical Hacker Exam
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.