GSEC Practice Exam - GIAC Security Essentials
Reliable Study Materials & Testing Engine for GSEC Exam Success!
Exam Code: GSEC
Exam Name: GIAC Security Essentials
Certification Provider: GIAC
Corresponding Certifications: Security Administration , GSEC

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
GSEC: GIAC Security Essentials Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 279 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena GIAC GIAC Security Essentials (GSEC) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
GIAC GSEC Exam FAQs
Introduction of GIAC GSEC Exam!
The GIAC Security Essentials (GSEC) exam is a certification exam that covers topics related to information security, including operating system security, network security, cryptography, authentication, security policy, and incident response. The exam is designed to test a candidate’s knowledge of these topics and their ability to apply them to real-world scenarios.
What is the Duration of GIAC GSEC Exam?
The GIAC GSEC exam is a 4-hour exam consisting of approximately 125 multiple-choice questions.
What are the Number of Questions Asked in GIAC GSEC Exam?
There are a total of 125 questions on the GIAC GSEC Exam.
What is the Passing Score for GIAC GSEC Exam?
The passing score for the GIAC GSEC exam is 74%.
What is the Competency Level required for GIAC GSEC Exam?
The GIAC GSEC (Security Essentials) exam is designed to test a candidate's knowledge and understanding of information security concepts and principles. The exam is intended to assess a candidate's ability to identify, analyze, and respond to security threats and risks. The competency level required to pass the exam is professional.
What is the Question Format of GIAC GSEC Exam?
The GIAC GSEC exam consists of multiple-choice and performance-based questions.
How Can You Take GIAC GSEC Exam?
The GIAC GSEC exam can be taken online or at a Pearson VUE testing center. To take the exam online, you must register for the exam through the GIAC website and select the online proctored option. To take the exam at a Pearson VUE testing center, you must register for the exam through the GIAC website and select the onsite proctored option. You will be required to provide a valid form of identification at the testing center.
What Language GIAC GSEC Exam is Offered?
The GIAC GSEC Exam is offered in English.
What is the Cost of GIAC GSEC Exam?
The cost of the GIAC GSEC exam is $1,199.
What is the Target Audience of GIAC GSEC Exam?
The GIAC GSEC (GIAC Security Essentials Certification) exam is aimed at IT professionals who want to demonstrate their knowledge of system security principles, technologies and tools. This certification is ideal for those who are looking to validate their skills in system security and gain recognition in the field. The target audience for the GIAC GSEC exam includes security administrators, security engineers, system administrators, network administrators, auditors, and anyone responsible for the security of an organization's networks and systems.
What is the Average Salary of GIAC GSEC Certified in the Market?
The average salary for a GIAC GSEC certified professional is around $80,000 per year. Salaries can vary greatly depending on experience, location, and other factors.
Who are the Testing Providers of GIAC GSEC Exam?
GIAC offers authorized testing centers around the world. You can find a list of authorized testing centers on their website.
What is the Recommended Experience for GIAC GSEC Exam?
The recommended experience for the GIAC GSEC exam is two to five years of information security experience. This experience should include installation, administration, and management of security technologies, as well as the development and implementation of security policies, procedures, and standards. Candidates should also have experience in risk management and incident response.
What are the Prerequisites of GIAC GSEC Exam?
The GIAC GSEC (GIAC Security Essentials Certification) exam requires candidates to have a minimum of two years of experience in information security. Candidates must also demonstrate experience and knowledge of the fundamental principles of information security, such as authentication, access control, encryption, and system and network security.
What is the Expected Retirement Date of GIAC GSEC Exam?
The official GIAC website (giac.org) does not list the expected retirement date for the GSEC exam. However, the GIAC GSEC page (https://www.giac.org/certification/security-essentials-gsec) does provide the current version of the exam and the exam objectives.
What is the Difficulty Level of GIAC GSEC Exam?
The GIAC GSEC exam is considered to be of moderate to difficult difficulty level. It is designed to test the knowledge and skills of IT professionals who are seeking to demonstrate their mastery of the security field.
What is the Roadmap / Track of GIAC GSEC Exam?
The GIAC GSEC certification roadmap consists of the following steps:
1. Register for the GIAC GSEC exam.
2. Complete the GIAC GSEC training course.
3. Read the GIAC GSEC exam objectives.
4. Take a practice exam to assess your knowledge.
5. Take the GIAC GSEC exam.
6. Receive your GIAC GSEC certification.
What are the Topics GIAC GSEC Exam Covers?
The GIAC Security Essentials (GSEC) certification exam covers a wide range of topics related to information security. The topics include:
1. Security Fundamentals: This covers the basic concepts of information security, such as risk management, security policies, and security architecture.
2. Identity and Access Management: This covers topics such as authentication, authorization, and identity management.
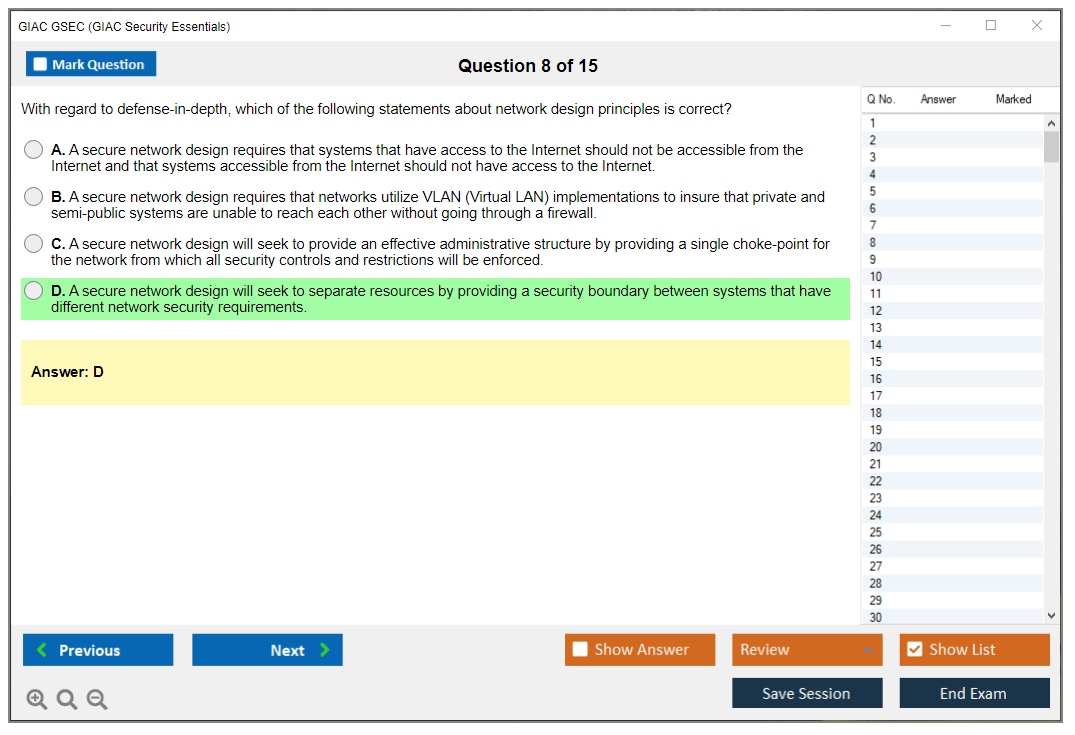
3. Network Security: This covers topics such as network protocols, network design, and network security technologies.
4. System Security: This covers topics such as operating system security, application security, and system hardening.
5. Data Security: This covers topics such as encryption, data classification, and data loss prevention.
6. Security Operations: This covers topics such as incident response, security monitoring, and security operations.
7. Compliance and Auditing: This covers topics such as compliance requirements, auditing, and security testing.
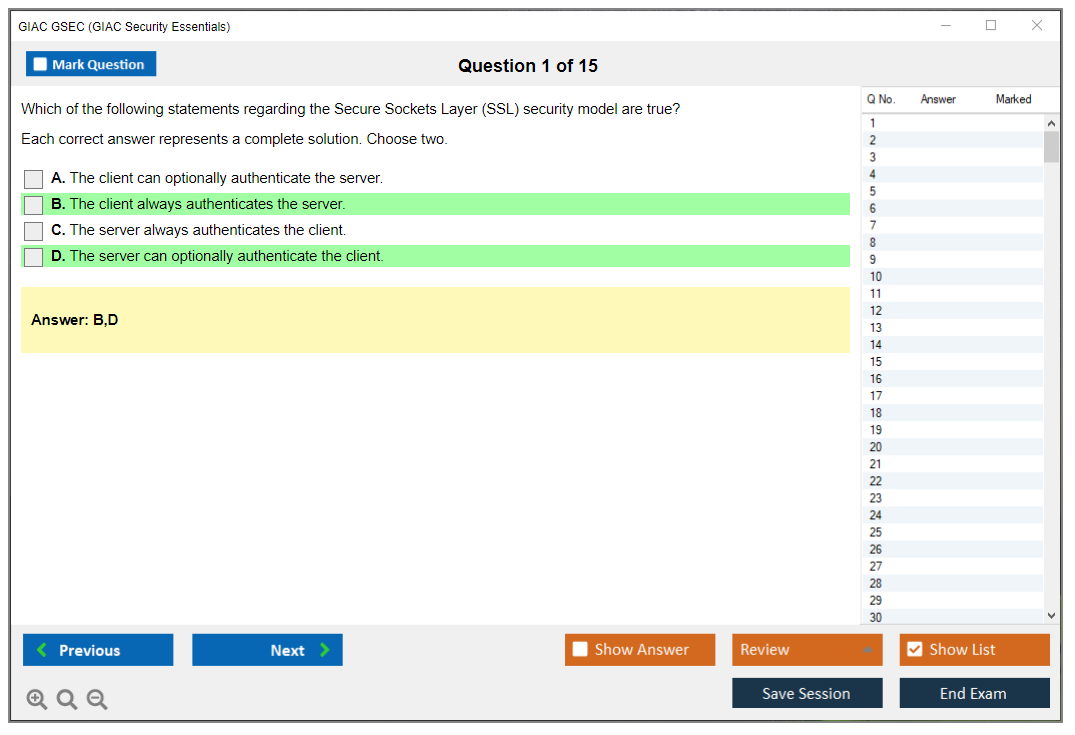
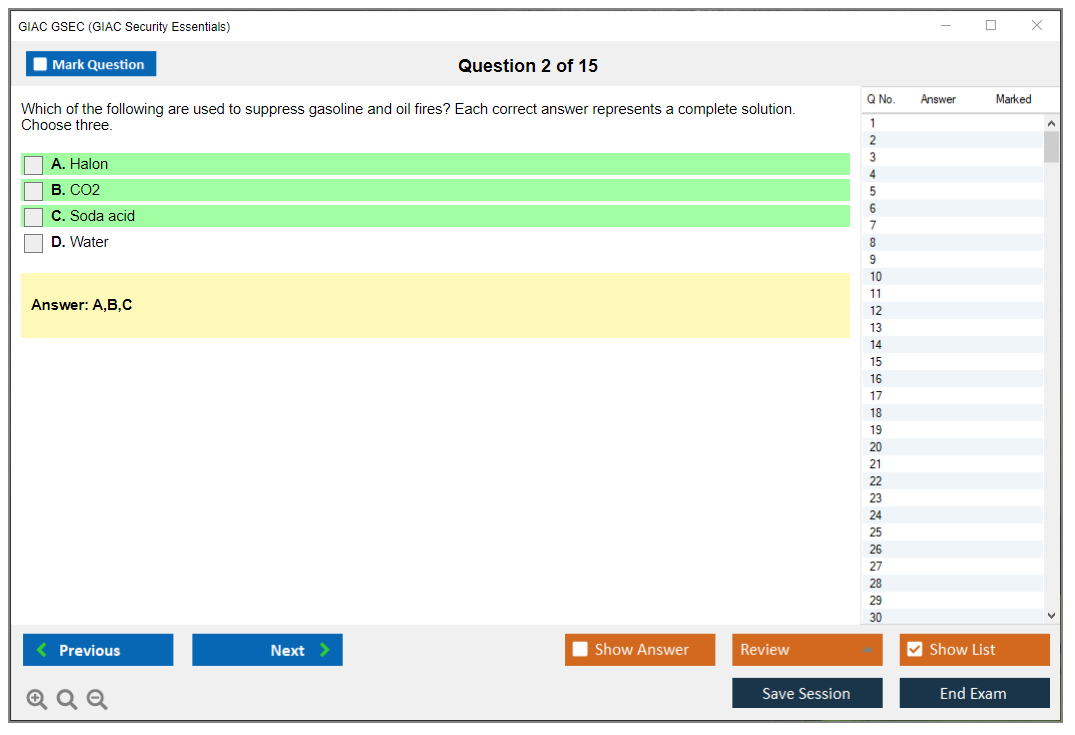
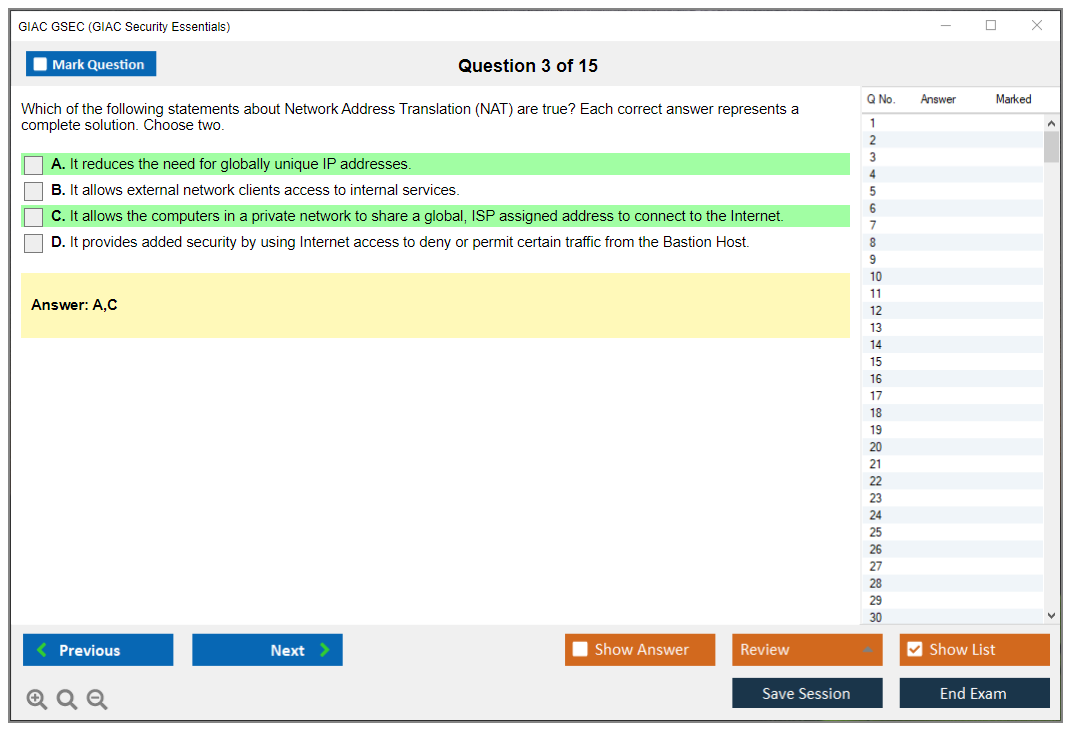
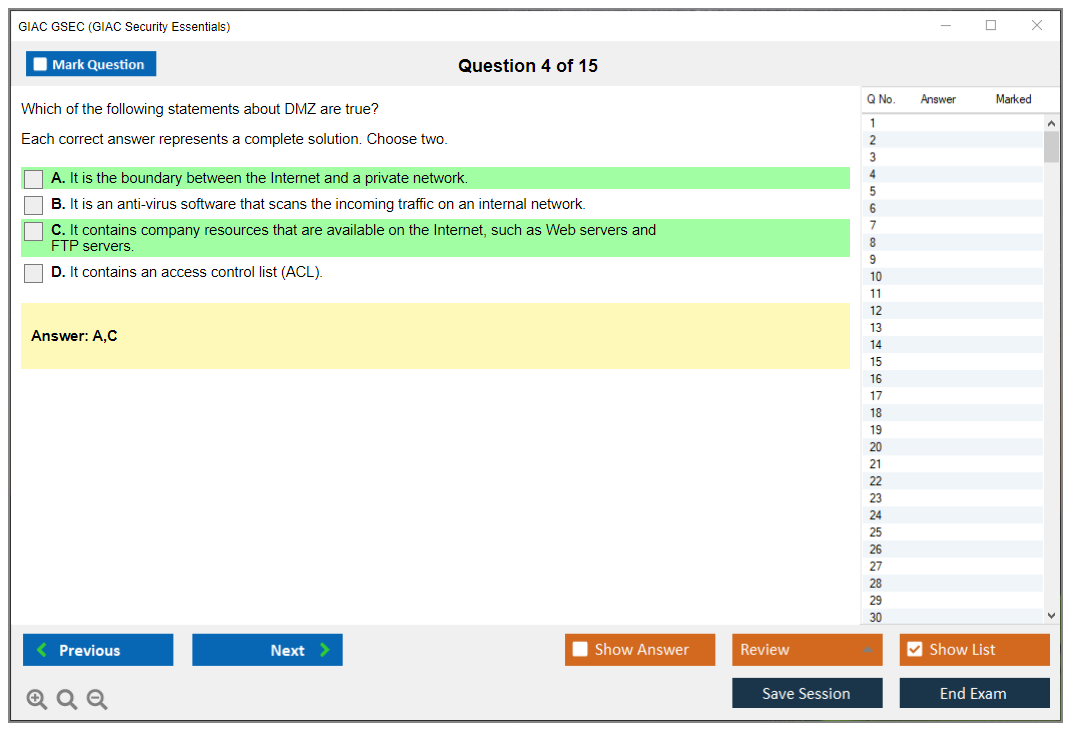
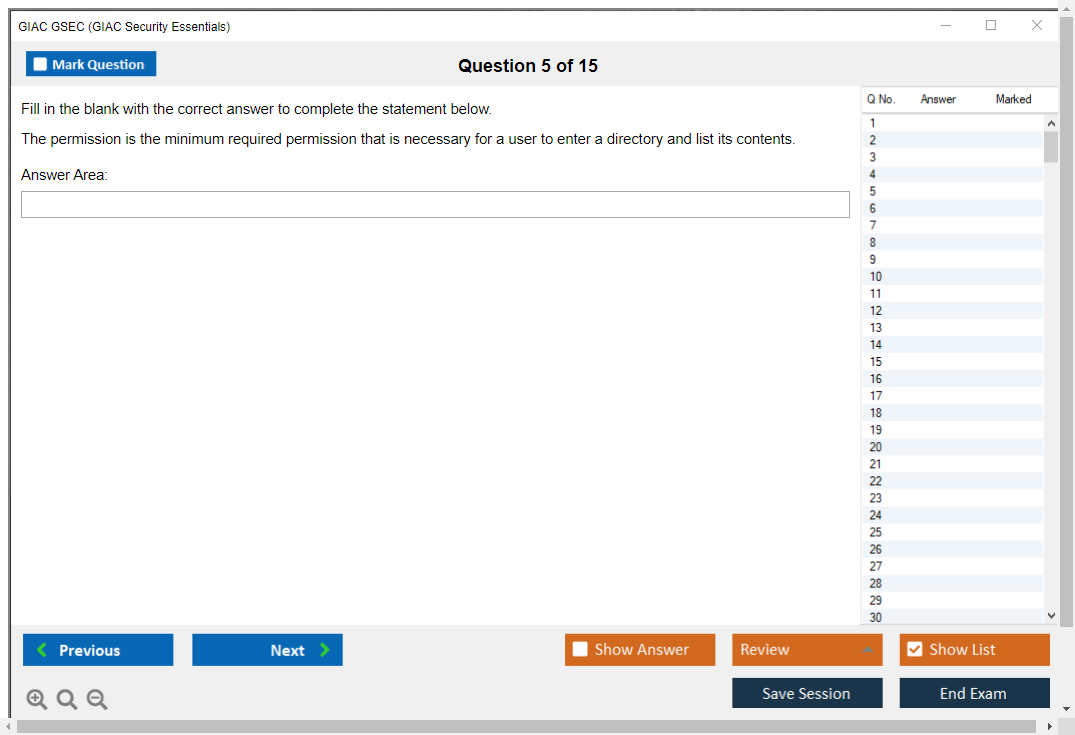
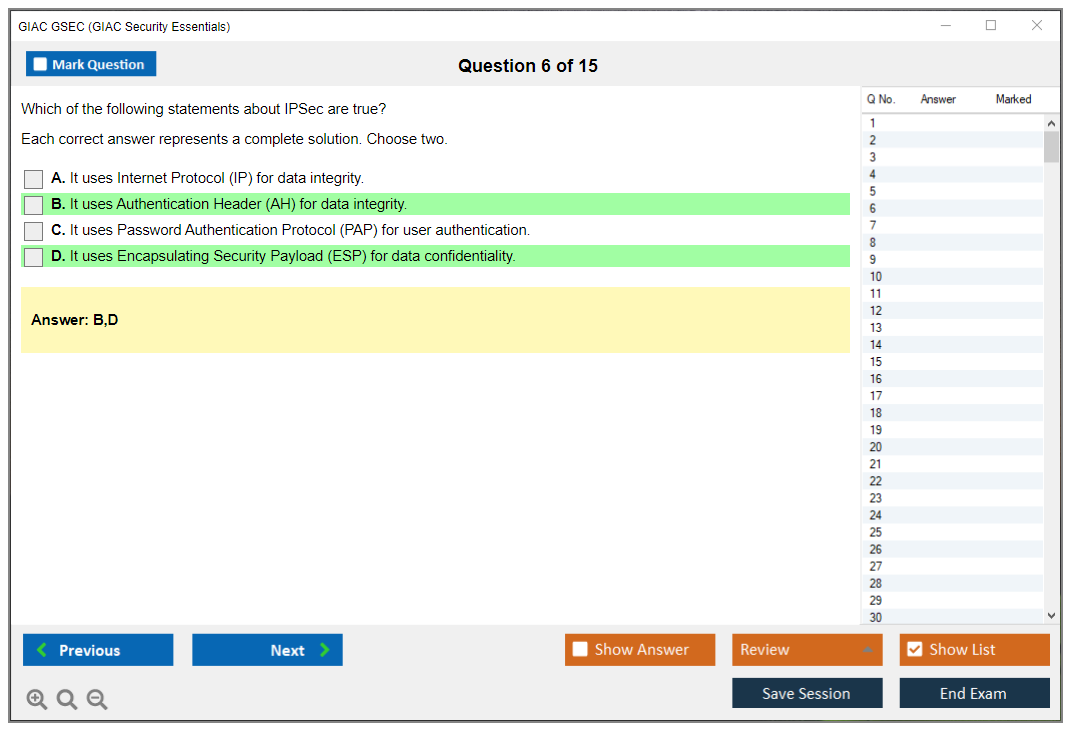
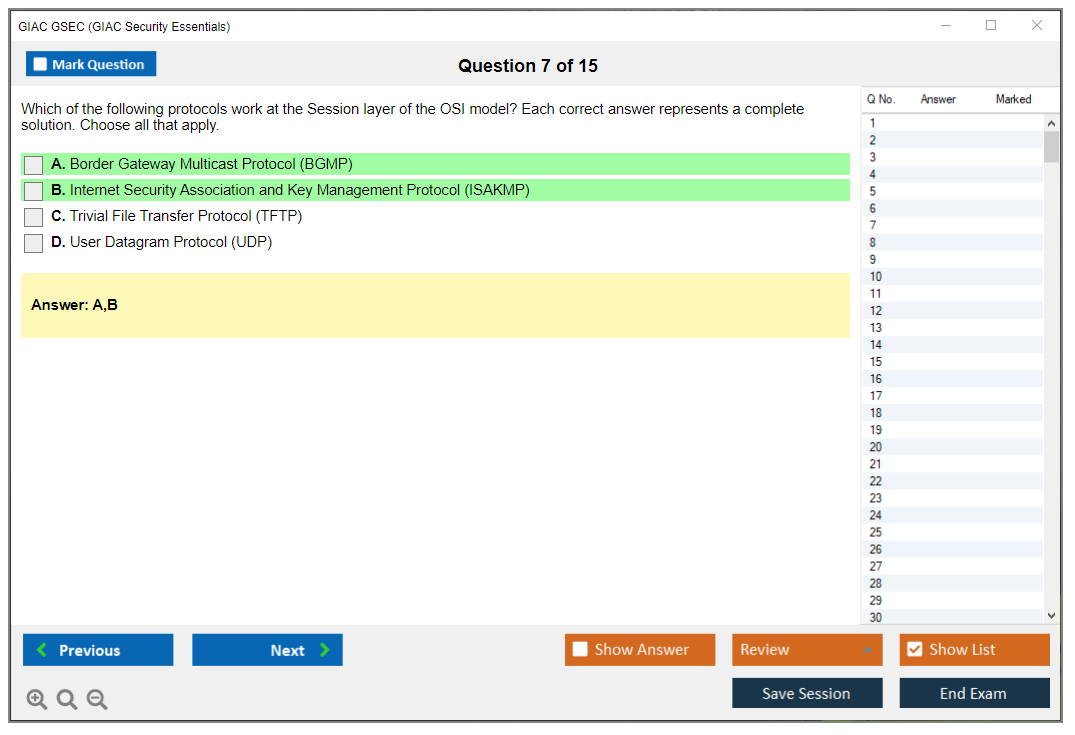
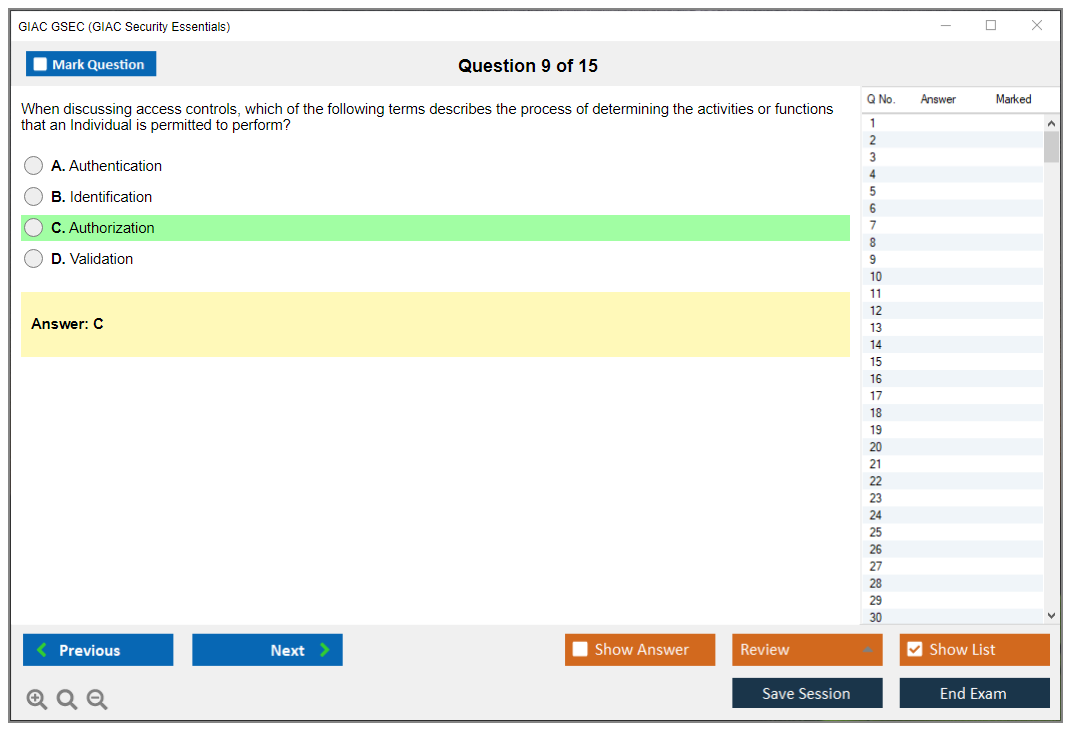
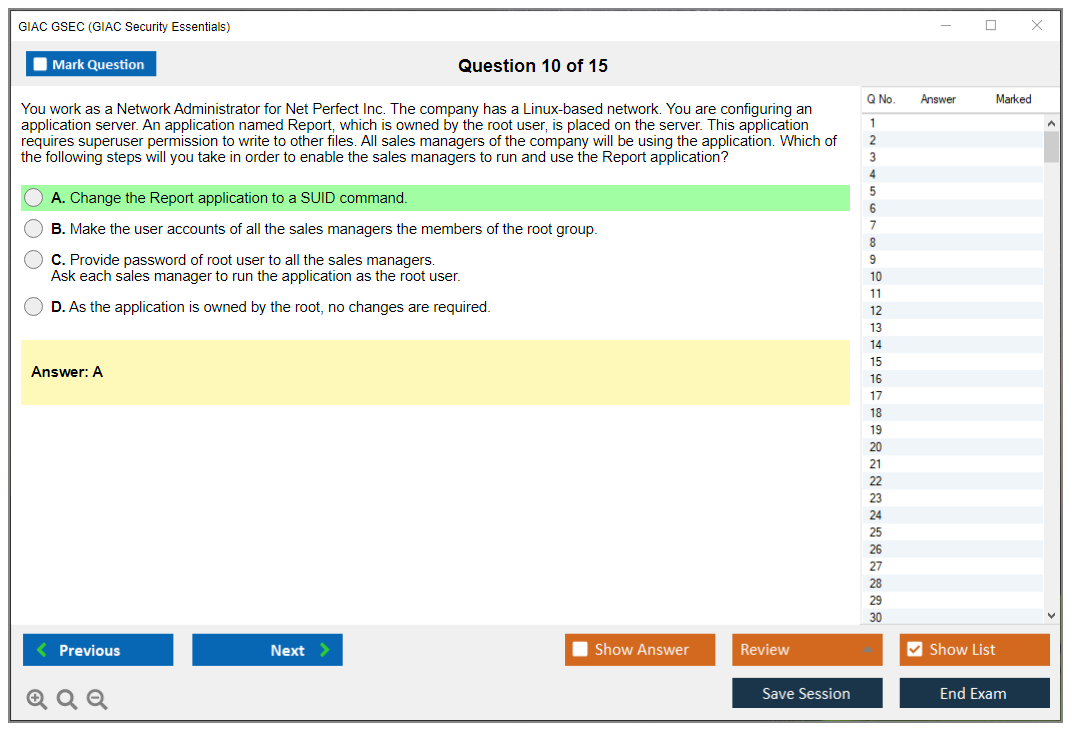
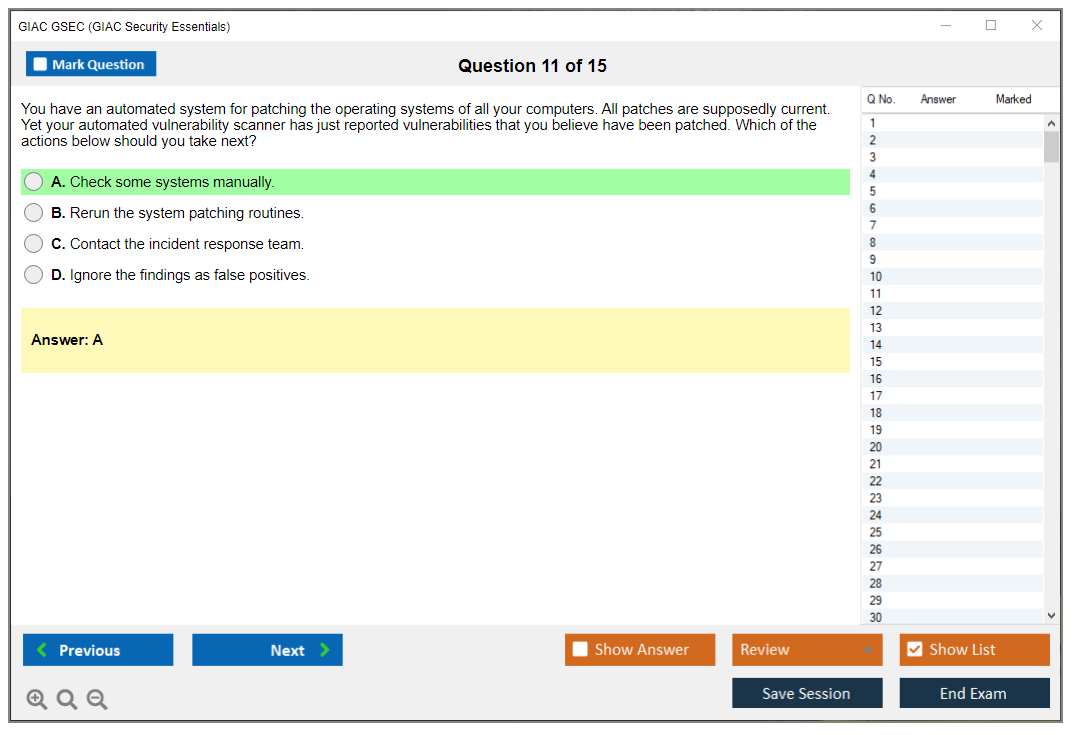
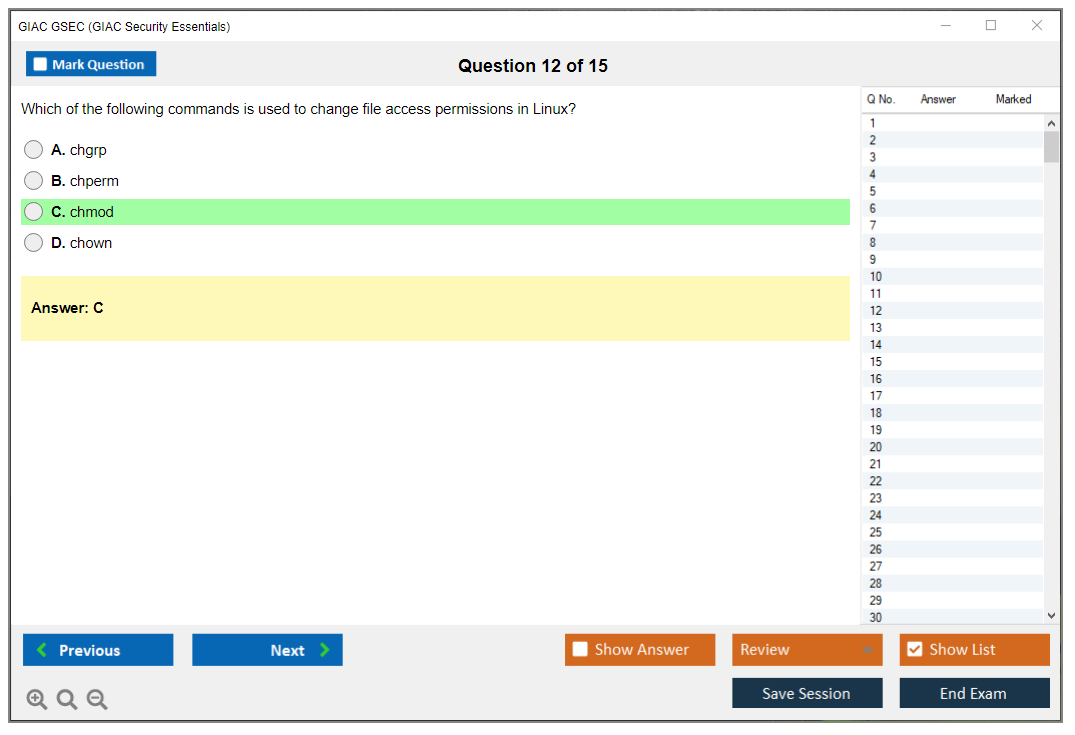
What are the Sample Questions of GIAC GSEC Exam?
1. What is the purpose of a security policy?
2. What is the difference between a firewall and an IDS?
3. What are the components of a secure network architecture?
4. What is the role of cryptography in network security?
5. How can you prevent malicious code from entering a network?
6. How can you detect and respond to security incidents?
7. What are the different types of authentication methods?
8. What measures can be taken to protect a wireless network?
9. What is the purpose of a vulnerability assessment?
10. What are the best practices for developing secure software?
GIAC GSEC (GIAC Security Essentials) What is the GIAC GSEC (GIAC Security Essentials) certification? Okay, so here's the deal. If you're digging around IT security lately, you've definitely run into the GIAC GSEC certification (that's the GIAC Security Essentials one). Job postings are absolutely loaded with this thing, particularly government gigs and defense contractor openings. There's actually a solid reason why. GSEC's basically this vendor-neutral credential proving you actually understand information security fundamentals and (here's what matters) can legitimately do defensive security work in real environments. We're not talking about parroting textbook garbage here. You're implementing controls, identifying threats, jumping into incident response, hardening systems. The actual work. The Global Information Assurance Certification (GIAC) handles administration, and they're tied to the SANS Institute ecosystem. You know, those people running intensive security training that'll... Read More
GIAC GSEC (GIAC Security Essentials)
What is the GIAC GSEC (GIAC Security Essentials) certification?
Okay, so here's the deal. If you're digging around IT security lately, you've definitely run into the GIAC GSEC certification (that's the GIAC Security Essentials one). Job postings are absolutely loaded with this thing, particularly government gigs and defense contractor openings. There's actually a solid reason why.
GSEC's basically this vendor-neutral credential proving you actually understand information security fundamentals and (here's what matters) can legitimately do defensive security work in real environments. We're not talking about parroting textbook garbage here. You're implementing controls, identifying threats, jumping into incident response, hardening systems. The actual work. The Global Information Assurance Certification (GIAC) handles administration, and they're tied to the SANS Institute ecosystem. You know, those people running intensive security training that'll cost you more than buying a decent used car. Honestly, it's ridiculous but whatever.
Who actually needs this thing
Security analysts? They're grabbing this constantly. System administrators who've had enough of just rebooting servers and really want dedicated security roles, yeah, them too. SOC team members need it since it covers that broad defensive security space they're wrestling with every single day.
Incident responders use it for structuring their knowledge around detection, analysis, response fundamentals. But honestly? It's absolutely massive with military and government IT folks because GSEC satisfies DoD 8570.01-M IAT Level II requirements, which isn't some weird obscure regulation. It's literally what you've gotta have for certain government security positions. Defense contractors love it too. Eyeing those jobs? GSEC's practically mandatory, no way around it.
Compliance and audit professionals grab it when they need understanding of technical security controls beyond just checkbox exercises. Career changers coming from other IT areas use it as their entry point into cybersecurity, though I'd argue you need some technical background first. This definitely isn't a "I just got my A+ last month" kind of cert. Not even close.
What kind of experience you actually need
The thing is, wait, the "essentials" name? Super misleading. This isn't beginner-level despite what that title's suggesting to people. You're expected to have working knowledge of networking, operating systems, basic security concepts before you even crack open study materials. Most folks taking GSEC have 1-3 years of IT experience or maybe 6-12 months of focused security work already under their belt.
It occupies this interesting middle ground. More advanced than CompTIA Security+ (which is really entry-level material), but less specialized than advanced GIAC certs like GCIH for incident handling or GCIA for intrusion analysis. Perfect stepping stone between foundational certifications and specialized credentials, really.
I remember my buddy Mike trying to jump straight into GSEC right after getting Security+ because he thought "essentials" meant easy. He crashed and burned on his first attempt. Spent like two grand on the exam and boot camp before realizing he needed actual hands-on time first. Took him another six months of working helpdesk tickets with security implications before things clicked. Sometimes you gotta learn the hard way.
What you're actually proving you know
The exam validates ability across multiple security domains rather than drilling deep expertise in just one narrow area. Defensive network architecture stuff like security zones, segmentation, DMZs, the whole network defense strategy playbook everyone talks about. Access control and authentication, implementing least privilege principles, managing authentication mechanisms, authorization models.
Cryptography fundamentals matter here. Big time. Symmetric and asymmetric encryption, hashing, PKI basics, SSL/TLS, practical crypto applications in real scenarios. Not just "what is encryption" fluff but "when do you use which type and why does it matter."
Security operations monitoring's massive in this exam. Log analysis, SIEM basics, security event correlation, anomaly detection techniques. If you're heading into a SOC role, this stuff is literally your bread and butter daily. Incident response and defense basics cover handling procedures, evidence preservation requirements, containment strategies, recovery processes. The practical "oh crap, we're compromised, now what do we actually do" scenarios nobody wants but everyone faces eventually.
Endpoint security and hardening for both Windows and Linux systems gets covered. Patch management strategies. Secure configuration baselines that actually work. Network protocols and security, TCP/IP from a security perspective specifically, common vulnerabilities lurking in protocols everyone uses.
Vulnerability management covering scanning methodologies, assessment techniques, prioritization frameworks, remediation strategies that make sense. Web application security fundamentals touch on common web vulnerabilities everyone exploits, OWASP Top 10 awareness (obviously), basic web defense mechanisms.
Wireless security covers 802.11 security protocols, wireless threats people actually use, secure wireless deployment practices. Cloud security basics are in there now too. Understanding cloud security considerations, shared responsibility model confusion, cloud-specific controls.
There's security policy and compliance awareness mixed in, understanding security frameworks organizations actually use, policy development processes, regulatory requirements. Even penetration testing awareness makes an appearance because, honestly, understanding attacker methodologies helps you defend systems way better than just knowing defense theory.
The practical application angle
What distinguishes GSEC from purely theoretical exams? The focus on real-world scenarios and practitioner knowledge, period. You're not just answering "what is a firewall" questions some intern could Google. You're analyzing logs, configurations, command outputs, security events that look messy and confusing.
The exam throws scenarios at you requiring actual decision-making. What would you do in this specific situation? Which control would you implement first? How would you respond to this particular indicator?
This hands-on cybersecurity exam approach means you absolutely can't just memorize definitions and pass comfortably. You need understanding of why things work the way they do and how to apply that knowledge when you're actually defending systems under pressure.
Career paths and certifications that make sense
Works well for people needing full security knowledge rather than deep expertise in a single domain, you know? It's recognized globally as a mid-level certification demonstrating hands-on security operations competency that employers actually value. Government agencies love it. Defense contractors require it constantly. Enterprise security teams respect it.
Looking at related paths? GPEN goes deeper into penetration testing methodologies, while GCFA specializes in forensics analysis work. For enterprise defenders specifically, GCED builds on similar foundations with more advanced content layered in. The GISF is actually more foundational if you're really brand new to security. Don't let the GSEC "essentials" label fool you into thinking it's easier, because it's not.
Not gonna lie, the certification demonstrates mastery across multiple security domains, which makes you way more versatile than someone with narrow specialization in just one thing. That breadth legitimately matters when you're working in smaller security teams or transitioning between different security roles. You become that person who can handle firewall configs, review logs properly, harden systems, respond to incidents without needing three different specialists in the room every time something happens.
GIAC GSEC exam details (format, cost, and logistics)
What is the GIAC GSEC (GIAC Security Essentials) certification?
GSEC is basically security fundamentals but for actual jobs. It's aimed at folks who need to prove they can handle practical security tasks across Windows, Linux, networking, some cloud stuff, crypto basics, and security operations without just hiding behind theory all day.
Who GSEC is for (roles and experience level)
Here's the thing. If you're already in IT and security work keeps landing on your desk, GIAC Security Essentials (GSEC) makes sense. Junior security analysts? Check. SOC people? Yep. Sysadmins hardening servers? Absolutely. Help desk staff trying to level up? Sure. Even managers wanting to understand their team's work without all the hand-wavy buzzwords. Honestly it works for them too.
What skills GSEC validates (security essentials overview)
You're showing you understand incident response plus defense basics, can actually read logs, spot common attacks, and make configuration choices that aren't completely insane. Plus you're proving to employers you can handle hands-on cybersecurity exam questions that feel way closer to real troubleshooting than some trivia night situation.
GIAC GSEC exam details (format, cost, and logistics)
Understanding the exam structure matters more than most people want to admit. Your prep plan and your budget are completely tied together. If you think you're "just taking a test," you'll probably under-budget it, schedule way too late, then scramble with indexing the week before. Creates a terrible vibe for what's really a 5-hour proctored marathon.
GIAC exams stick to a consistent format across certifications. GSEC's got its own specific parameters that don't change much, even when objectives get refreshed every so often. Proctoring's strict because GIAC wants the credential to maintain its value with employers. That's part of why it carries actual weight compared to lighter entry-level certs.
I've seen people show up with zero indexing prep thinking they'll just wing it with the books. They burn through maybe 40 questions before realizing they're spending 4 minutes hunting for a single answer about Kerberos delegation, and then panic sets in hard.
GSEC exam cost (what you pay for and typical inclusions)
The standalone GSEC exam cost without training typically runs about $949 to $979 USD, and yeah, prices shift sometimes. That purchase gets you one exam attempt where you're sitting for 180 questions with a 5-hour time limit.
You also typically snag a GSEC practice tests option when you register for the exam attempt. Usually one practice test included. Which is useful for calibration purposes. Not magic or anything. Just feedback. It'll tell you if you're moving too slow on log questions, if your crypto basics are shaky, or whether you keep mixing up ports and protocols when fatigue sets in.
Want the big official path? The SANS GSEC course (SEC401) bundle often runs $8,900+ and includes training, materials, plus the exam attempt. OnDemand training with exam often lands around $7,200 to $7,500 depending on whatever promos are running. Live online and in-person options exist too. They're priced like premium training because that's SANS for you.
Retakes sting less than your first shot but still hurt your wallet. Expect about $469 to $509 per retake attempt. Academic pricing can knock a lot off the total, often 30% to 50% for qualifying students. There are also government and military discount programs for eligible personnel, and employer-sponsored training's really common since plenty of organizations would rather pay for SEC401 than gamble on inconsistent internal training that might not stick.
Work Study's another angle. You help with conference assistance and your training cost drops a lot. Not free, exactly. But way more reachable for folks paying out-of-pocket.
No recurring exam fees though. You pay to take it once, and you only pay again if you retake. Renewal later's its own separate thing, but you're not paying "annual exam rent" or anything weird like that.
Cost comparison time. CompTIA Security+ runs around $404, CISSP's $749 exam-only (but requires experience you might not have yet), and GSEC sits between them on exam-only price while often feeling closer to premium territory because of the open-book design and quality of official materials. The value proposition's basically industry recognition, strong alignment with real-world security work, and DoD 8570/8140 acceptance in a lot of roles. Which is why employers don't laugh when they see it on your resume.
Budget planning tip? Factor in your GSEC study materials costs, printing expenses, binding, indexing time investment, a practice run, and the possibility you might pay for a retake. The retake line item's the one people pretend won't happen to them, and then it totally does.
Exam format (question types, time limit, delivery)
180 multiple-choice questions. That's the format. Covers all the GSEC exam objectives, and you've got 300 minutes total. Works out to about 1.67 minutes per question, which sounds fine until you hit a few "read this scenario, inspect this log snippet, pick the best next step" items back-to-back and suddenly you're behind.
Question style varies throughout. Standard multiple-choice with 3 to 5 options, often 4. Scenario-based questions that feel like an actual ticket from a SOC queue. Technical questions where you're interpreting commands, logs, configs, and sometimes exhibits like screenshots or network diagrams that require actual analysis.
Open-book's the big talking point here. You're typically allowed two books or bound materials, plus an index you create yourself, with specific GIAC rules around page size (usually 8.5"x11" for index pages) and what's allowed regarding tabs and annotations. But it's not open-internet, not open-laptop, not open-PDF access. No electronic devices allowed. No digital notes whatsoever. If your indexing plan's basically "I'll just Ctrl+F," you're in for a really bad day.
The test isn't adaptive. Everyone gets the same number of questions no matter what. You can mark questions for review and come back later. You usually get immediate preliminary pass/fail at the end, and the official score report typically shows up in the GIAC portal within 24 to 48 hours after you finish.
Registration, scheduling, and testing options (remote vs test center)
Registration's straightforward enough. Create a GIAC account, purchase the exam, then schedule it within your eligibility window. The big gotcha? Time limit. Your exam attempt's typically valid for 120 days from purchase, so you need to schedule and complete it inside that window. Advance planning matters here, especially if you want a specific day and time slot.
Delivery options are solid. Remote proctoring through ProctorU is most popular because it's flexible and you can test from home in your own space. Pearson VUE testing centers are the other main option if you prefer an in-person controlled environment without worrying about your home setup.
Remote testing requirements are strict though. Private room required. Stable internet connection (GIAC/ProctorU commonly references around 1.5 Mbps minimum, but more's better). Webcam and microphone that actually work. Clear desk with nothing extra on it. No people walking through mid-exam. Lighting that doesn't make you look like some shadow figure. You'll do a technical check about 15 to 30 minutes before the appointment time, and the proctor will want to inspect your workspace and your approved reference materials thoroughly.
Pearson VUE's got its own pros and cons. Controlled environment means fewer "why's my webcam driver updating right now" moments. But you might face limited locations, less flexible scheduling options, and travel time eating into your day. Bring two forms of ID for a test center appointment, and expect a government-issued photo ID requirement for remote proctoring too.
Scheduling flexibility's best with remote, often 24/7 availability, but you still want to book 1 to 2 weeks ahead for your preferred slot. Peak periods happen, like right after SANS events, and availability tightens up fast. Rescheduling's usually allowed up to 48 hours before your exam without penalty, and late cancellations inside that window can mean you forfeit fees entirely. Also, time zones matter way more than people think. Schedule when your brain actually works, not when a calendar slot just looks convenient, because five hours straight is really long.
GIAC GSEC FAQ
How much does the GIAC GSEC exam cost?
Standalone exam's typically $949 to $979. SEC401 bundles run much higher, usually $8,900+, with OnDemand bundles often $7,200 to $7,500 depending on timing.
What is the passing score for the GSEC exam?
GIAC publishes passing standards in the portal for your specific exam version. Check your GIAC dashboard for the current GSEC passing score since it can vary by form and update cycle.
How hard is the GIAC GSEC certification?
Broad coverage. Fast-paced. Open-book but definitely not easy by any stretch. If your index is weak, you'll burn time searching. If your fundamentals are weak? The books won't save you from that gap.
What are the best study materials for GSEC (SEC401 vs self-study)?
SEC401's the cleanest path, period. Materials are built specifically for the exam and the indexing approach is already laid out. Self-study can work if you're disciplined and you've already got strong fundamentals, but you need a serious plan covering references, labs, and timed practice sessions.
How do you renew the GSEC certification and how often?
You renew on the GIAC cycle using GIAC certification renewal (CMUs) or by retesting entirely. The exact dates and GSEC renewal requirements live in your GIAC portal, and you want to track them early so you're not scrambling at the deadline trying to figure it out.
GSEC passing score and scoring policy
What is the GSEC passing score?
The passing score? 73%.
That's roughly 131 correct answers out of 180 total questions on the exam. GIAC actually publishes this threshold openly, which is refreshing compared to vendors who guard their cut scores like they're hiding nuclear codes or something.
This 73% requirement stays locked in place across every administration of the test, and I mean it doesn't budge whether you're taking it on a random Tuesday morning in March or squeezing it in during a Saturday afternoon session in November when you'd rather be doing literally anything else.
How criterion-referenced scoring shapes your exam experience
GIAC uses what's called criterion-referenced scoring for the GSEC exam.
What's that mean? Your performance gets measured against established competency standards, not against how other candidates perform. You're not competing with the person in the next testing booth or anyone who took the exam last month. No normalization happens here. No curving, no adjustments, nothing. The 73% threshold represents what GIAC considers minimum competency for a Security Essentials practitioner, and that standard doesn't shift based on whether the current candidate pool finds certain questions tricky or whether a particular version happens to be slightly harder.
This matters because you can plan your preparation with a concrete target in mind. When you're working through GSEC practice tests or reviewing your notes, you know exactly what percentage you need to hit. There's no guessing about whether "maybe they'll curve it" or "hopefully this version is easier."
Breaking down what 131 correct answers really means
Look, when you think about needing 131 out of 180 questions correct, that gives you a 49-question cushion.
That's not nothing.
But here's where people mess up. They treat those 49 questions like a comfortable safety net and get sloppy. Time management becomes critical because careless errors eat into that margin fast. Every question carries equal weight. The straightforward ones about basic access control concepts count exactly the same as the trickier scenario-based questions about incident response procedures, which honestly can feel unfair when you're sitting there trying to remember specific protocol details under pressure.
No partial credit exists. Multiple-choice means you're either right or wrong. There's no "well, you showed your work and got close" scoring here.
Strategic thinking about your actual target score
You shouldn't aim for exactly 73%.
Honestly, that's cutting it way too close. Most people who pass comfortably report scoring 80% or higher on their practice attempts leading up to exam day. Why aim higher? Because exam conditions differ dramatically from your study environment. You might encounter questions worded in ways you didn't expect. Time pressure affects decision-making in weird ways. That one domain you thought you understood pretty well might show up with questions from an angle you hadn't considered. The point is you need breathing room when exam anxiety kicks in.
When I was prepping for my GSEC, I wouldn't schedule the exam until I consistently hit 85% on practice tests. That extra cushion meant I could walk into the testing center without that gnawing anxiety about whether I'd studied enough. Some questions on the actual exam felt easier than practice material, others felt harder, but the buffer mattered big time.
I remember one guy at a security meetup who swore he was ready after hitting 75% on a single practice run. Scheduled his exam the next week. Failed by three questions. Had to wait and pay again. Don't be that guy.
What happens on exam day with scoring
You'll get your preliminary pass/fail result displayed immediately when you complete the exam.
This isn't like some certifications where you wait days or weeks wondering if you passed. The system calculates your percentage and tells you right there whether you hit that 73% threshold. The preliminary result is highly reliable. I've never heard of someone getting a preliminary pass and then having the official score come back as a fail, or vice versa. GIAC's system is pretty solid about this.
Your official score report shows up in the GIAC portal within 24 to 48 hours typically, and this report breaks down more than just your overall percentage. It includes performance by domain so you can see exactly where you excelled and where you struggled across different security areas. You might see something like "Network Security: 78%, Cryptography: 85%, Defense and Incident Response: 68%." This breakdown becomes super useful if you need to retake the exam, or even just for understanding where your knowledge sits.
The no-curve reality and DoD alignment
Since GIAC doesn't curve scores, the 73% you need today is the same 73% someone needed three years ago and will need three years from now.
This consistency matters especially for DoD 8570 compliance. Government contracts and positions require specific certifications at specific competency levels, and the GSEC passing score fits with those requirements. Whether you take the exam standalone after self-study or as part of the SANS SEC401 training course, that passing standard stays identical. The delivery method doesn't change the bar.
Handling questions strategically during the exam
With 180 questions and that 49-question cushion, you need a strategy beyond just "answer everything and hope for the best."
I always recommend prioritizing questions where you feel confident first. Mark uncertain ones for review and come back to them. Never leave questions blank. There's no negative scoring, wrong answers don't subtract points, they just fail to add any. If you're running out of time, guess on everything remaining. An unanswered question counts as incorrect anyway, so you might as well take the chance on getting some right through educated guessing.
What you can't do with your score afterward
For security reasons, you cannot review specific exam questions after completing the test.
GIAC doesn't provide item-level feedback showing which questions you missed, which protects exam integrity but means you can't go back and see exactly where you went wrong on individual items. The domain-level breakdown in your score report is the most granular feedback you'll receive. If you fail, this breakdown becomes your roadmap for focused remediation study before your retake attempt.
Retake considerations and the value of that score
If you don't hit 73% on your first attempt, you can retake the exam after paying an additional fee and observing a required waiting period.
Each attempt costs the same, which gets expensive fast. Another reason to prepare thoroughly before your first try. Once you do pass, that score remains valid indefinitely for certification purposes. Your certification itself requires renewal every four years through continuing education credits or retesting, but the passing score achievement doesn't expire. The certificate gets issued digitally within one to two weeks usually, with physical certificates available as an option.
Looking at other GIAC certifications, the 73% threshold is pretty standard across their portfolio. If you're planning a GIAC certification path, maybe starting with GSEC and moving toward something like GCIH or GPEN, you'll see similar scoring policies. Understanding how criterion-referenced scoring works for GSEC prepares you for other GIAC exams down the road.
GSEC difficulty: how hard is the exam?
What is the GIAC GSEC (GIAC Security Essentials) certification?
The GIAC GSEC certification is basically the "prove you can actually do the work" version of an information security fundamentals cert. Defensive-leaning. Broad. Very ops-flavored, honestly.
GIAC Security Essentials (GSEC) is not a vibe check, I mean it is a skills check across tons of security domains, and the whole point is that you can function in real security operations, not just recite terms you half-remember from some flashcard deck you bought on impulse. Some questions? Basic. Others get uncomfortably specific, which is why people argue about GSEC difficulty nonstop, and that debate is not ending anytime soon.
Who GSEC is for (roles and experience level)
SOC analysts with 1-2 years in the trenches, system administrators who "also do security," network engineers shifting into blue team work, and military plus government IT folks who already live around policy, compliance frameworks, and operational controls.
What skills GSEC validates (security essentials overview)
You are expected to understand defensive security, networking, systems, cryptography, and incident response plus defense basics. Not in research depth, but in "can you interpret this output and pick the best action" depth. Practical stuff. Sometimes annoying.
GIAC GSEC exam details (format, cost, and logistics)
This is where expectations get real.
GSEC exam cost (what you pay for and typical inclusions)
GSEC exam cost changes depending on how you buy it (bundle, training package, promo windows), but GIAC exams are expensive, full stop, and there is no sugarcoating that financial reality. You are usually paying for the attempt, and often you will get practice tests if you bought through official channels. If you are budgeting, assume the exam is the big-ticket item, and everything else is "supporting spend."
Exam format (question types, time limit, delivery)
The exam is 180 questions in 5 hours. Open book. Mostly multiple choice, but the "multiple choice" often looks like a mini incident report with logs, configs, or tool output attached, so do not assume it is easy just because it is not essay format. Hands-on cybersecurity exam questions show up in the sense that you need to recognize command-line tools, log formats, and technical outputs, even though you are not typing commands into a live terminal.
Five hours sounds generous until you do the math: 1.67 minutes per question, and honestly, that is the trap because open-book makes people think they can look everything up, but you cannot do that 180 times without running out of runway.
Registration, scheduling, and testing options (remote vs test center)
You can generally schedule through GIAC and take it at a test center or via a proctored remote option depending on what is available in your region. Plan for logistics friction. ID checks, system checks, quiet room rules. Not hard, just easy to underestimate.
GSEC passing score and scoring policy
People obsess about this part. It feels like a simple target, right? It is not the whole story.
What is the GSEC passing score?
The GSEC passing score is set by GIAC and published on the exam page for the current version. It can change over time, so do not trust random forum numbers from 2019. Check the official listing right before you schedule.
How GSEC scoring works (what to expect on exam day)
You answer questions, you get a scaled result, and you either clear the bar or you do not. What matters on exam day is pace plus accuracy, because you will see questions where two answers look "kinda right," and the exam wants the BEST option based on the scenario and common security operations context.
GSEC difficulty: how hard is the exam?
GSEC difficulty is debated constantly among certification candidates and security professionals because it hits different backgrounds in different ways, and there is no universal experience here. If you have been doing SOC triage, half the test feels familiar, but if you are a pure beginner, it can feel like getting pelted with acronyms and log snippets for five straight hours.
Generally? I would rate it intermediate. Way harder than Security+ (mostly because of the applied angle and the breadth), but more accessible than advanced GIAC certs that go deep into a single specialty.
Difficulty factors (breadth of objectives, pace, applied knowledge)
Breadth is the headline issue. The exam spans defensive security, networking, systems, cryptography, and incident response, and that wide knowledge domain means you cannot rely on deep expertise in one area and hope to brute force the rest. You will bounce from Windows concepts to TCP/IP behavior to authentication flows to detection logic, sometimes back-to-back, and your brain gets context-switched to death.
Depth is uneven, and that is part of the stress: some items are fundamentals, others want protocol-level understanding (the kind you get from actually troubleshooting networks or reading packet captures), and then there are occasional "obscure detail" questions pulled from the SANS GSEC course (SEC401) material or a security standard that you skimmed at 2 a.m. Open-book helps with that, but only if your index is dialed in.
Format matters more than people admit, honestly. Scenario-based questions are common. You will analyze logs, configurations, security events, and tool output, then pick the best response or explanation. No purely theoretical questions where you can float on definitions. Everything is tied to practical security operations. Also, questions often include detailed exhibits that require careful reading, and if you rush, you miss one tiny clue and pick the wrong "almost correct" answer, which is incredibly frustrating when you review afterward.
Time pressure is real. Five hours is a lot, yet with 180 questions you do not get extended deliberation. Not gonna lie, the open-book decision-making makes it worse for anxious test takers, because you are constantly choosing between "trust my knowledge" and "burn two minutes searching notes."
Index quality directly correlates with exam success. A poor index turns the exam into panic-scrolling through PDFs, while a good one turns it into quick confirmation, which is what open-book is supposed to be.
By the way, I once watched a colleague spend 40 minutes on question 12 because he insisted on finding the "perfect" reference, then had to rush the last 30 questions. He passed but barely, and swore he would never open-book another cert exam without practicing his lookup speed first. Kind of a tangent, but it stuck with me because it shows how the format can wreck even smart people who overthink.
Who finds GSEC easiest vs hardest
Easiest for people in these camps:
SOC analysts with 1-2 years experience, because the log-reading and triage mindset maps well to the exam. System administrators with security responsibilities do well because they have touched hardening, permissions, patching, and incident cleanup in real life. Network engineers transitioning to security often crush it too, since protocol fundamentals are a cheat code on this test.
Hardest for these groups:
Pure beginners without infrastructure experience or networking knowledge. The thing is, you are building foundational knowledge while also trying to pass an intermediate cert, which is brutal. Developers who have not lived in ops struggle because systems content and defensive monitoring can feel alien. People who rely on memorization without practice get punished because scenario interpretation destroys shallow recall. Narrow specialists (like someone who only does penetration testing) can also struggle because GSEC is broad defensive work, not "find bug, pop shell." Non-native English speakers can get slowed down by scenario wording and technical terminology. Test anxiety sufferers often waste time second-guessing and over-searching their notes.
How long to study for GSEC (time estimates by background)
Study time varies wildly based on experience, training path, and how current your knowledge is.
If you attended SEC401 (that 5-6 day intensive), I mean, you still want 40-60 hours afterward for indexing, practice tests, and drilling weak spots. For experienced security professionals, 60-100 hours is common to refresh and fill gaps, especially if you have been deep in one area and rusty in others.
For IT professionals with some security exposure, think 100-150 hours. You know the basics, but you need reps with incident workflows, crypto fundamentals, and defensive tooling outputs. Self-study without training is where it gets heavy: 150-250 hours over 3-6 months is a typical range, because you are building structure that the course normally hands you. Career changers or beginners can easily hit 200-300+ hours because you are learning networking and operating systems while also learning security.
Minimum timeline, even with training, is 6-8 weeks. Self-study folks should plan 4-6 months if they have a job and a life, which most people do. A workable schedule is 1-2 hours on weekdays and 4-6 on weekends for 2-3 months, but that assumes you already have IT foundations. Full-time study for 3-4 weeks can work, but it is mentally exhausting and you still need time to build an index you trust.
Also, do not ignore the "hidden" blocks of time: 20-30 hours building a serious index, 10-15 hours taking GSEC practice tests and reviewing misses, and 20-40 hours doing hands-on labs so the command output and log formats feel normal. Wait, actually that labs time might be even more critical than the reading for some learning styles.
GSEC exam objectives (domains you must know)
GSEC exam objectives cover a lot. That is kinda the point.
Core security concepts and foundational knowledge
Threats, controls, risk-ish thinking, and baseline defensive practices. Nothing purely academic. Expect operational framing.
Network and protocol fundamentals for defenders
TCP/IP behavior, common ports, DNS and DHCP quirks, HTTP basics, and what "normal" looks like so you can spot abnormal. This area can get surprisingly detailed, honestly.
Security operations, monitoring, and incident handling basics
Alert triage, log interpretation, containment thinking, and what to do first when something is on fire. This is where practical experience pays off.
Access control, authentication, and cryptography essentials
AAA concepts, IAM basics, hashing vs encryption, certificate ideas, and common failure modes. Some of this is easy, some is "wait, which property matters here?"
Hardening and secure configuration (systems and endpoints)
Windows and Linux hardening themes, least privilege, patching, services, baseline configs. If you have never administered systems, this part hurts.
GSEC prerequisites and recommended experience
Are there formal prerequisites?
No formal GSEC prerequisites in the strict sense. Nobody forces you to hold another cert first.
Recommended baseline knowledge (networking, OS, security basics)
You want basic networking, comfort with Windows and Linux concepts, and familiarity with logs and command output. If you do not have that? Plan more hours. Period.
Who should take GSEC before/after (common certification paths)
Security+ before GSEC is common. After GSEC, people often go into more specialized GIAC tracks depending on whether they like IR, detection, cloud, or pentest work.
Best GSEC study materials (official and supplemental)
Official SANS training (SEC401) and what it covers
SANS GSEC course (SEC401) aligns tightly with the exam, and that alignment is a huge deal. If your employer pays, it is the cleanest path.
Books, labs, and hands-on practice ideas
Do labs that force you to read logs, inspect network behavior, and interpret endpoint signals. Spin up a small home lab. Break things on purpose, then fix them.
Study plan (indexing/notes strategy, weekly schedule template)
Build your index as you study, not at the end. Start with high-level topics, then add keywords you know you will search under pressure. A messy index is worse than no index, because it wastes time and spikes stress.
If you want a cheap way to pressure-test readiness, a pack like GSEC Practice Exam Questions Pack can be useful as a pacing tool, not as a shortcut. The $36.99 price point is low enough that some folks treat it like extra reps alongside their main GSEC study materials, and reps matter for this exam.
GSEC practice tests and exam prep strategy
Where to find GSEC practice tests (official vs third-party considerations)
Official GIAC practice tests are the gold standard for style and difficulty. Third-party questions vary wildly. Some are fine for drilling recall, but they often miss the scenario feel.
That said, if you are struggling with timing, extra question volume helps you learn when to stop searching your notes and commit. GSEC Practice Exam Questions Pack can help you rehearse that decision, as long as you keep your expectations realistic and still prioritize SEC401-aligned content.
How to use practice questions effectively (diagnose weak domains)
Review every miss. Write down why you missed it. Was it knowledge, reading, or time? Fix the cause, not the symptom. Fragments in your notes? Add them to your index.
Final-week checklist (timed practice, review, readiness)
Timed sets. Tight index cleanup. Focus on weak areas. Sleep. And do at least one full-length practice run so 180 questions does not feel like a surprise endurance event.
GSEC renewal requirements (maintaining your certification)
Renewal cycle and continuing education (CMUs)
GIAC certification renewal (CMUs) is the normal route. You renew on the published cycle by earning continuing education units.
Renewal options (earning CMUs vs retesting)
You can earn CMUs through training, conferences, relevant work activities, and approved education, or you can retest. Most people do CMUs because retesting is expensive and stressful.
Common renewal pitfalls and how to avoid them
Do not wait until the last minute to log CMUs. Keep documentation as you go. Also track GSEC renewal requirements early so you are not scrambling at the deadline.
Is GIAC GSEC worth it? (career impact and ROI)
Jobs that value GSEC
SOC roles, security analyst positions, incident response-adjacent jobs, and hybrid sysadmin-security roles. Government contracting loves GIAC in general.
Salary/career outcomes (what employers look for)
Employers like that it is hands-on and proctored, and that the GIAC brand signals rigor. They also like that it maps to defensive operations rather than theory.
When to choose GSEC vs other entry/intermediate security certs
Choose GSEC if you want a tougher, more applied cert than Security+ and you can justify the GSEC exam cost. If you are brand new and funding yourself, Security+ first is often more rational, then come back when you have some ops experience.
GIAC GSEC FAQ
Cost, passing score, difficulty (quick answers)
How much does the GIAC GSEC exam cost? High, and it depends on how you buy it. What is the passing score for the GSEC exam? It is published by GIAC for the current exam version. How hard is the GIAC GSEC certification? Intermediate, harder than Security+ and easier than advanced GIAC certs, with pace and breadth doing most of the damage.
Study materials and practice tests (quick answers)
What are the best study materials for GSEC (SEC401 vs self-study)? SEC401 is the most aligned. Self-study is doable but slower. GSEC practice tests: prioritize official ones, then add extras for pacing. If you need more reps, GSEC Practice Exam Questions Pack is a low-cost way to drill timing and weak domains.
Objectives, prerequisites, and renewal (quick answers)
GSEC exam objectives: broad defensive coverage across networks, systems, crypto, and incident handling. GSEC prerequisites: none formally, but you want real IT basics. How do you renew the GSEC certification and how often? Through GIAC certification renewal (CMUs) on the published cycle, or by retesting if you really want pain.
GSEC exam objectives (domains you must know)
Core security concepts and foundational knowledge
Right off the bat? Foundations matter.
The first domain everyone hits covers foundational security principles, and honestly it's broader than you'd think going in. Like, way broader when you're actually sitting there answering questions. Defense-in-depth philosophy runs through everything. You need to understand layered security controls, how redundancy works when one layer fails, and what compensating controls actually look like in production environments where nothing's perfect and budgets are tight. Not just theory either. The exam will throw real-world scenarios at you where you're identifying which layer failed and what should've caught the threat.
Security principles matter more than memorization here. I mean, truly matter. Least privilege means users get exactly what they need, nothing more. Separation of duties prevents one person from owning an entire critical process. Fail-safe defaults mean systems lock down when something breaks, not open up. Complete mediation checks every access request, every time. These aren't buzzwords. The exam tests whether you can apply them to messy real situations where business needs clash with security requirements and everyone's yelling about productivity losses.
CIA triad application shows up everywhere. You'll see questions about confidentiality breaches, integrity violations, and availability disruptions, but they won't just ask for definitions. They'll describe an incident and you figure out which part of the triad got compromised and how. That's what separates this from entry-level certs. You're analyzing, not recalling.
Risk management fundamentals take up significant space. Threat modeling requires understanding who your adversaries are and what they want. Script kiddies versus nation-states make different choices. Risk assessment means quantifying likelihood and impact, not just saying "this is bad." Risk mitigation strategies include accept, transfer, avoid, or mitigate. You need to know when each makes sense and when management is making terrible decisions that'll bite them later.
Security frameworks awareness is tested but not deeply, thankfully. You should recognize NIST Cybersecurity Framework's five functions. Know ISO 27001/27002 exists as an international standard. Understand CIS Controls provide prioritized security actions. The exam won't drill into implementation details but expects you to know which framework fits which scenario.
The thing is, compliance and regulatory space gets surprisingly detailed for a technical cert. HIPAA protects health information. PCI-DSS governs payment card data. GDPR basics cover EU privacy rights. SOX mandates financial controls, FISMA applies to federal systems. You don't need to cite section numbers, but you absolutely need to know which regulation applies when someone describes a breach scenario involving customer credit cards versus medical records versus government data.
Security policies and procedures show up in scenario questions where context matters. Acceptable use policies define what users can do with company resources. Incident response plans outline who does what when things go wrong. Disaster recovery focuses on restoring operations after major disruptions. The exam tests whether you understand the difference between these documents and when each gets invoked.
Asset classification and data handling matters more than people expect. Way more. Data sensitivity levels range from public to confidential to restricted, each requiring different controls. Proper labeling ensures users know what they're handling. Secure disposal means wiping drives, not just hitting delete. Questions often describe mishandled data and ask what went wrong in the classification or handling process.
Actually, quick tangent here. I've seen people obsess over memorizing every control number from frameworks and then bomb questions about basic data handling because they never worked in an environment where classification actually mattered. The exam assumes you've touched this stuff, not just read about it.
Network and protocol fundamentals for defenders
TCP/IP protocol suite deep dive is no joke. Honestly, it's intense. You need to understand IPv4 and IPv6 addressing, subnetting, how TCP three-way handshakes work, UDP's connectionless nature, ICMP's diagnostic role. All from a security perspective where attackers exploit normal protocols. What does a SYN flood look like in packet captures? How do attackers abuse ICMP for reconnaissance? The exam assumes you can read packet headers and spot anomalies.
Network architecture and segmentation gets tested through design scenarios that feel pretty real. DMZ design questions ask where to place web servers, database servers, application servers. VLANs provide logical segmentation, network zoning separates trust levels. Micro-segmentation takes it further with granular controls between workloads. You'll see network diagrams and need to identify security weaknesses or recommend improvements that actually make sense for the environment described.
Firewall technologies and configurations come up constantly. Like, constantly. Stateful inspection tracks connection state, not just individual packets. ACLs define what traffic passes through. Next-generation firewalls add application awareness, intrusion prevention, and SSL inspection. Questions describe firewall rules and ask what traffic they allow or block. Or present security requirements and ask you to write appropriate rules.
Intrusion detection and prevention systems require understanding signature-based detection, which matches known attack patterns, versus anomaly-based detection that identifies deviations from baseline. IDS monitors and alerts. IPS can block. Placement matters. You'll answer questions about where to deploy sensors for maximum visibility with minimum performance impact.
Network traffic analysis shows up in practical questions where you're basically playing detective. You need basic Wireshark skills: filtering traffic, following TCP streams, identifying protocols. More importantly, you need to recognize malicious traffic patterns like port scans, reconnaissance attempts, or data exfiltration. The exam might show packet captures and ask what attack is occurring.
DNS security covers multiple attack vectors that honestly feel overwhelming at first. DNSSEC provides authentication for DNS responses. DNS tunneling smuggles data through DNS queries. Cache poisoning redirects users to malicious sites. You should know how each attack works and what defenses exist, because scenario questions describe symptoms and you identify the attack or recommend countermeasures.
Common network attacks need detailed understanding. Not surface-level stuff. ARP spoofing redirects traffic by poisoning ARP caches. VLAN hopping lets attackers jump between network segments. MAC flooding overwhelms switch CAM tables. DHCP attacks exhaust address pools or redirect traffic through rogue servers. For each attack, know the mechanism, indicators, mitigations.
Security operations, monitoring, and incident handling basics
Look, this domain connects theory to practice in ways that matter for actual jobs. Security operations means running detection and response day-to-day. Log management and analysis requires knowing what to collect, how long to retain it, what patterns indicate compromise versus normal weirdness. SIEM systems aggregate logs from multiple sources. You need to understand correlation rules, alert tuning, false positive reduction.
Incident detection and response follows structured processes, structured for good reason. Detection identifies potential incidents through alerts, user reports, anomaly detection. Triage determines severity and scope. Containment stops the bleeding, eradication removes the threat. Recovery restores normal operations, lessons learned improves future response. The exam presents incident scenarios and asks what phase you're in or what action comes next.
Security monitoring tools include network monitors, host-based agents, endpoint detection and response platforms. Security orchestration tools tie everything together. You don't need vendor-specific knowledge but should understand capabilities and deployment considerations. Questions might describe monitoring gaps and ask what tool addresses them.
Vulnerability management is ongoing. Never stops. Scanning identifies weaknesses. Assessment prioritizes based on risk, not just CVSS scores. Remediation fixes issues, verification confirms fixes work. The exam tests understanding of scan types like authenticated vs unauthenticated, vulnerability scoring basics, patch management challenges. Compensating controls when patching isn't immediately possible because production systems can't go down.
Access control, authentication, and cryptography essentials
Access control models need solid understanding because they show up everywhere in different contexts. Discretionary access control lets resource owners set permissions. Mandatory access control enforces system-wide policies based on labels. Role-based access control assigns permissions to roles, not individuals. Attribute-based access control makes decisions based on multiple attributes, or sometimes combinations of attributes depending on context. Questions describe access scenarios and ask which model is in use or which would work best.
Authentication factors include something you know like passwords, something you have like tokens, something you are like biometrics. Multi-factor authentication combines at least two different factor types. Not just two passwords. The exam tests understanding of authentication strength, when MFA is required, how different methods resist specific attacks.
Cryptography essentials cover symmetric encryption where the same key encrypts and decrypts. Fast, but key distribution challenges. Asymmetric encryption uses public/private key pairs. Slower, but enables digital signatures. Hashing is a one-way function for integrity verification. You need to know when to use each, common algorithms like AES, RSA, SHA-256. What happens when cryptography is implemented incorrectly because developers didn't understand the fundamentals.
Public key infrastructure enables asymmetric cryptography at scale. At actual enterprise scale. Certificate authorities issue certificates, registration authorities verify identities. Certificates bind public keys to identities. Certificate revocation lists track invalidated certificates. Questions cover certificate validation, trust chains, PKI failure modes.
Hardening and secure configuration (systems and endpoints)
Windows security configuration includes user account control, local security policies, group policy objects. Windows Defender settings, BitLocker encryption. Linux security covers file permissions, SELinux or AppArmor, package management, service hardening. You need practical knowledge of both platforms because questions describe misconfigurations and ask what's wrong or how to fix it without breaking everything else.
Endpoint protection extends beyond antivirus. Way beyond. Application whitelisting allows only approved software. Host-based firewalls control network connections. Endpoint detection and response monitors for suspicious behavior. Full disk encryption protects data at rest. Questions test understanding of defense-in-depth on endpoints. What happens when one control fails and others should catch the threat?
Secure baseline configurations eliminate unnecessary services. Apply least privilege, enable logging, configure secure defaults that won't annoy users into finding workarounds. The exam might present a system configuration and ask what security issues exist. Or describe security requirements and ask what settings achieve them. Center for Internet Security benchmarks provide good reference points, though the exam doesn't require memorizing specific settings.
Patch management balances security and stability. Always a tradeoff. Critical patches need rapid deployment, testing prevents patches from breaking production. Change management ensures documentation and approval. Questions address patch prioritization, testing strategies, handling systems that can't be patched immediately due to application compatibility or uptime requirements.
Mobile device security covers MDM platforms, containerization, remote wipe capabilities. Encryption requirements that vary by sensitivity. BYOD policies balance user convenience against corporate security. Questions might describe mobile security incidents and ask what controls would've prevented them, or present BYOD scenarios and ask what policies apply.
Not gonna lie, the breadth here is what gets people. It's really overwhelming at first. Each domain goes deeper than you expect, and the exam doesn't let you get by with surface knowledge. You need to apply concepts to scenarios you haven't seen before, which means actually understanding the material, not just memorizing dumps. That's why people who try to shortcut with practice tests without learning fundamentals tend to struggle when exam questions twist the scenario slightly.
The exam objectives align with SANS SEC401 course content, but they extend beyond just regurgitating class material. They really do. You're expected to synthesize information, analyze security situations, recommend appropriate controls based on the scenario presented. That's what makes GSEC valuable. It validates you can actually apply security essentials, not just recognize textbook definitions.
Conclusion
Putting it all together
Okay, real talk here.
The GIAC GSEC certification? It's not a walk in the park, but it's also not some impossible nightmare designed to crush your soul. What it actually does is validate that you know your stuff. The real fundamentals of information security that go way beyond just memorizing definitions from some dusty manual. I mean the practical security essentials that come into play when you're monitoring networks, locking down systems, or handling live incidents as they unfold. If you've been grinding in IT for a few years and you're ready to pivot into security, or maybe you're already knee-deep in security work but need that official credential to back up what you know, GSEC's a smart choice.
The exam cost? Yeah, it hurts. We're looking at over $2,000 when you go the complete SANS SEC401 route, which explains why everyone's freaking out about nailing it on attempt number one. But here's what matters: that investment starts paying dividends the second you're getting callbacks for SOC analyst gigs or security admin openings that mention GSEC in the requirements. Employers get it. They recognize you've covered incident response and defensive fundamentals, that you've wrapped your head around access control and cryptography basics, and that you can translate hands-on cybersecurity exam questions into actual real-world applications.
Short sentences work.
The GSEC passing score's set at 73%, which sounds doable until you're sitting there staring at 106 questions and suddenly the sheer scope of the GSEC exam objectives smacks you in the face. You'll need solid study materials plus an actual strategy. The official SANS course delivers incredible value if your budget allows it, though plenty of folks pass through focused self-study, notes, and relentless practice sessions.
Speaking of practice (and this is critical): this step separates candidates who set themselves up to succeed from those who stumble in woefully unprepared. You've gotta drill repeatedly with questions that replicate the exam's format and challenge level. Not just passively skimming answers, but timing yourself, pinpointing your weaker domains, and developing that automatic recall for the massive range of topics GSEC throws at you. My cousin failed twice before he figured this out, kept thinking he could wing it because he'd been working helpdesk for three years. Turns out desktop support and actual security knowledge aren't the same thing, who knew?
If you're committed to passing (and not flushing that exam fee down the drain), check out the GSEC Practice Exam Questions Pack. It's built to help you spot knowledge gaps, get comfortable with how questions are structured, and walk in with solid confidence come test day. The GSEC renewal requirements mean you'll maintain this cert through CMUs, so getting it right initially matters way more than people think.
You've got this. Just don't skip the practice work.
Show less info
Comments
Hot Exams
Related Exams
GIAC Certified Enterprise Defender
GIAC Information Security Fundamentals
GIAC Security Leadership Certification (GSLC)
GIAC Penetration Tester
GIAC Certified Incident Handler
GIAC GIAC Secure Software Programmer - C#.NET
GCIA – GIAC Certified Intrusion Analyst Practice Test
GIAC Certified Firewall Analyst
GIACCertified Forensics Analyst
GIAC Secure Software Programmer – Java
GIAC GIAC Secure Software Programmer - C#.NET
GIAC Certified Project Manager Certification Practice Test
GIAC Certified Perimeter Protection Analyst
GIAC Critical Controls Certification (GCCC)
GIAC Security Essentials
GIAC Information Security Professional
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.