GPYC Practice Exam - GIAC Python Coder (GPYC)
Reliable Study Materials & Testing Engine for GPYC Exam Success!
Exam Code: GPYC
Exam Name: GIAC Python Coder (GPYC)
Certification Provider: GIAC
Certification Exam Name: Security Certification: GPYC

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
GPYC: GIAC Python Coder (GPYC) Study Material and Test Engine
Last Update Check: Mar 19, 2026
Latest 73 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena GIAC GIAC Python Coder (GPYC) (GPYC) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
GIAC GPYC Exam FAQs
Introduction of GIAC GPYC Exam!
GIAC GPYC (GIAC Python Coder) is an intermediate-level certification exam that tests a candidate's ability to write, debug, and optimize Python scripts to solve real-world security problems. It covers topics such as data types, functions, classes, and objects, as well as more advanced concepts such as writing secure code, debugging, and optimizing code for performance.
What is the Duration of GIAC GPYC Exam?
The GIAC GPYC exam is a two-hour, multiple-choice exam.
What are the Number of Questions Asked in GIAC GPYC Exam?
The GIAC GPYC exam contains a total of 125 multiple choice questions.
What is the Passing Score for GIAC GPYC Exam?
The passing score for the GIAC GPYC Exam is 70%.
What is the Competency Level required for GIAC GPYC Exam?
The competency level required for the GIAC GPYC exam is advanced.
What is the Question Format of GIAC GPYC Exam?
The GIAC GPYC exam consists of multiple-choice questions, drag-and-drop questions, and performance-based questions.
How Can You Take GIAC GPYC Exam?
The GIAC GPYC exam can be taken either online or at a testing center. To take the exam online, you must first register for the exam and pay the exam fee. Once registered, you will be provided with a link to access the exam. To take the exam at a testing center, you must first register for the exam, pay the exam fee, and then schedule an appointment at a testing center. On the day of the exam, you must bring two forms of valid identification and arrive at the testing center at least 15 minutes prior to your scheduled appointment.
What Language GIAC GPYC Exam is Offered?
The GIAC GPYC exam is offered in English.
What is the Cost of GIAC GPYC Exam?
The cost of the GIAC GPYC Exam is $1,199.
What is the Target Audience of GIAC GPYC Exam?
The GIAC GPYC Exam is intended for security practitioners who have knowledge of the basics of Python programming, and who want to gain a more in-depth understanding of the language and its applications in cybersecurity. It is also suitable for those who are interested in pursuing a career in cybersecurity and want to demonstrate their proficiency in Python.
What is the Average Salary of GIAC GPYC Certified in the Market?
The average salary for a GIAC GPYC certified professional is around $90,000 per year. However, salaries can vary depending on experience, location, and other factors.
Who are the Testing Providers of GIAC GPYC Exam?
GIAC provides testing for the GIAC GPYC exam. Candidates who wish to take the exam can register through the GIAC website.
What is the Recommended Experience for GIAC GPYC Exam?
The GIAC GPYC exam is designed to test a candidate's knowledge and skills in the field of Python programming. To ensure success on the exam, it is recommended that candidates have at least two years of professional experience working with Python, including experience with the Python language, libraries, and frameworks. Candidates should also have a basic understanding of data structures, algorithms, and software engineering principles. Additionally, it is recommended that candidates have experience working with databases, web development, and network programming.
What are the Prerequisites of GIAC GPYC Exam?
The Prerequisite for GIAC GPYC Exam is to have a minimum of two years of professional experience working in a field related to information security.
What is the Expected Retirement Date of GIAC GPYC Exam?
The official website to check the expected retirement date of GIAC GPYC exam is https://www.giac.org/certification/gpyc-giac-python-certified.
What is the Difficulty Level of GIAC GPYC Exam?
The difficulty level of the GIAC GPYC exam is considered to be intermediate.
What is the Roadmap / Track of GIAC GPYC Exam?
The GIAC GPYC certification roadmap consists of the following steps:
1. Complete the GIAC GPYC Exam Preparation Course.
2. Pass the GIAC GPYC Exam.
3. Complete the GIAC GPYC Certification Program.
4. Achieve the GIAC GPYC Certification.
5. Maintain your GIAC GPYC Certification.
What are the Topics GIAC GPYC Exam Covers?
The GIAC GPYC exam covers the following topics:
1. Foundations of Cybersecurity: This section covers the basic principles of cybersecurity, including risk management, security policies and procedures, and security architecture. It also covers the fundamentals of cryptography and authentication.
2. Security Architecture and Design: This section covers the fundamentals of designing secure systems and networks, including network topologies, security protocols, and authentication methods.
3. Security Operations and Incident Response: This section covers the basics of security operations, including incident response, security monitoring, and security auditing.
4. Threats and Vulnerabilities: This section covers the fundamentals of identifying, analyzing, and mitigating threats and vulnerabilities.
5. Access Control and Identity Management: This section covers the fundamentals of access control and identity management, including authentication and authorization.
6. Data Security: This section covers the fundamentals of data security, including data encryption, data integrity, and data loss prevention
What are the Sample Questions of GIAC GPYC Exam?
1. What are the key components of a comprehensive cybersecurity program?
2. What are the best practices for performing risk assessments and security audits?
3. How can organizations protect their networks from malicious actors?
4. What are the principles of secure coding and how can they be applied to software development?
5. What are the most common threats to information security and how can they be mitigated?
6. What are the implications of the EU’s GDPR for organizations’ data protection practices?
7. How can organizations ensure compliance with relevant cybersecurity regulations?
8. What strategies can be used to detect and respond to cybersecurity incidents?
9. What are the benefits of using a cybersecurity management framework?
10. What are the steps to creating an effective incident response plan?
GIAC GPYC (GIAC Python Coder (GPYC)) What is GIAC GPYC (GIAC Python Coder) Certification What GIAC Python Coder really means for security work The GIAC Python Coder (GPYC) certification is an industry-recognized credential that validates your ability to write secure, efficient Python code specifically for cybersecurity operations. This isn't generic stuff. It's issued by Global Information Assurance Certification (GIAC), which has been a major player in the security certification space for years, and it focuses exclusively on practical Python application in security contexts rather than general software development. The kind of code that actually matters when you're triaging incidents at 2 AM. What makes GPYC different? Laser focus on automation. It's about security tool development and data analysis tasks that security professionals actually do every day, not academic exercises that look good on paper but fall apart in production. The certification validates that you can automate... Read More
GIAC GPYC (GIAC Python Coder (GPYC))
What is GIAC GPYC (GIAC Python Coder) Certification
What GIAC Python Coder really means for security work
The GIAC Python Coder (GPYC) certification is an industry-recognized credential that validates your ability to write secure, efficient Python code specifically for cybersecurity operations. This isn't generic stuff. It's issued by Global Information Assurance Certification (GIAC), which has been a major player in the security certification space for years, and it focuses exclusively on practical Python application in security contexts rather than general software development. The kind of code that actually matters when you're triaging incidents at 2 AM.
What makes GPYC different? Laser focus on automation. It's about security tool development and data analysis tasks that security professionals actually do every day, not academic exercises that look good on paper but fall apart in production. The certification validates that you can automate security tasks, parse logs, analyze threat data, and build custom tools that solve real security problems. Anyone can learn Python syntax from a tutorial, but GPYC proves you can apply it to security operations in a way that matters. There's a difference between knowing 'for' loops and actually using them to process 50GB of firewall logs efficiently.
Who actually needs this certification
Security analysts are probably the biggest group pursuing GPYC. They're drowning in repetitive tasks and need automation to stay sane. Incident responders also find this incredibly useful because they're constantly parsing logs, analyzing malware samples, and processing forensic data where Python scripts can save hours of manual work. Sometimes the difference between containing a breach in two hours versus two days.
Penetration testers building custom exploitation tools love this cert. Same with security engineers who automate infrastructure security checks and compliance reporting. SOC analysts creating detection scripts and threat hunting workflows? Absolutely.
Application security professionals who analyze code and build secure applications? Yep, them too.
The thing is, IT professionals trying to transition into cybersecurity roles with a technical emphasis should seriously consider GPYC. It demonstrates both coding capability and security awareness, which is a powerful combination that hiring managers actually look for now. Not just theory. I had a colleague who spent five years in network admin work before making the switch, and GPYC was what finally got him interviews at shops that previously ignored his resume.
Why Python skills matter so much in security right now
Python's become the standard. If you're in security and can't code, you're at a significant disadvantage in 2024 and beyond. Organizations increasingly require security staff with coding capabilities because manual processes just don't scale anymore when you're dealing with thousands of alerts daily or analyzing terabytes of log data. The human brain wasn't designed for that volume, but Python scripts handle it beautifully.
Automation skills reduce manual workload and improve response times. The ability to write a Python script that handles what used to take three analysts two days is a big deal for budget-conscious security teams. Python proficiency lets you build custom tools for unique security challenges that commercial products don't address, and GPYC certification demonstrates your commitment to developing these technical skills in a verifiable way that managers can actually justify to their leadership.
The credential differentiates candidates. When two applicants have similar security knowledge but one has GPYC, that coding validation tips the scales every time. This fits with the industry shift toward DevSecOps and security automation, where security teams need to integrate with development workflows and infrastructure-as-code environments. Honestly, it's where the field's headed whether we like it or not.
The technical skills GPYC actually validates
GPYC tests your ability to write clean, maintainable, Pythonic code following best practices. It validates that you understand secure coding practices to prevent vulnerabilities in your own scripts, which matters more than people realize. I've seen "security" tools introduce worse vulnerabilities than they detect.
Working with Python's standard library for file operations, networking, and data processing is basic stuff you'll use constantly.
You need to demonstrate competency with third-party libraries commonly used in security tasks. We're talking requests for API interactions, scapy for packet manipulation, cryptography libraries for secure operations. Not just knowing they exist, but actually implementing them correctly under time pressure. Parsing and analyzing various data formats like JSON, XML, CSV, and log files is huge because that's what security data looks like in the real world, not the sanitized examples from textbooks.
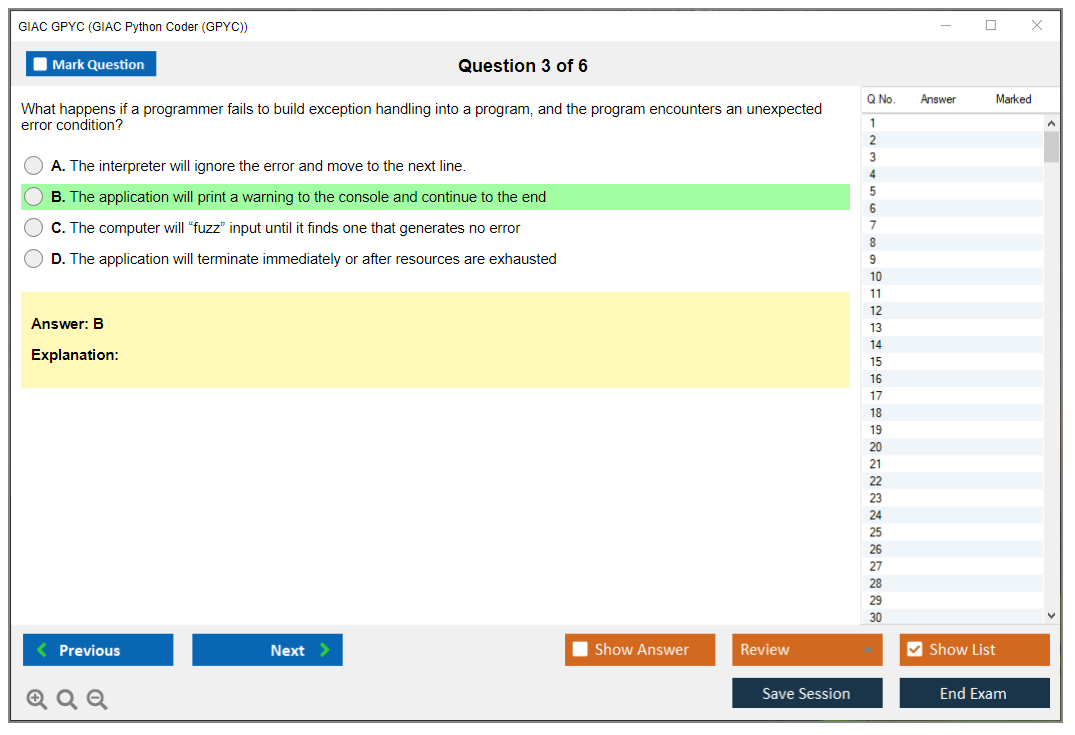
Automating security workflows? That's the point. The exam validates you can handle errors and exceptions appropriately in security contexts (because production always fails differently than dev), write unit tests to ensure code reliability, work with APIs for security tool integration, and process and visualize security data. These aren't abstract skills. They're what you'll actually use if you want to be effective in a modern security role instead of just manually copy-pasting indicators into spreadsheets all day.
How GPYC fits with other GIAC certifications
GPYC complements other GIAC security certifications like GSEC, GCIH, and GPEN. It is a foundational coding credential you might pursue before or alongside more advanced security certs. Kind of depends on your background and where you're starting from. The certification bridges the gap between security knowledge and technical implementation, which is exactly what GIAC intended when they created it.
This is part of GIAC's broader effort to address the automation skills gap in cybersecurity. Many security professionals know what needs to happen but lack the coding skills to implement solutions. They can diagram the perfect detection workflow but can't actually build it. GPYC fills that gap and pairs well with certifications like GCIA or GCFA where Python skills enhance your analytical capabilities beyond just theory.
Career advantages you actually get from GPYC
The certification increases your marketability for security positions requiring Python skills, which is becoming most of them. Real talk: coding skills command a premium in security salaries. We're talking potentially significant increases compared to non-coding peers at similar experience levels, sometimes 15-20% more depending on the market and role.
GPYC boosts your ability to contribute to security team objectives beyond just identifying problems. You can actually build solutions instead of filing tickets for developers who have their own priorities. It provides a foundation for learning additional programming languages once you've mastered Python in a security context.
You gain credibility when proposing automation solutions to management because you have a recognized credential backing your technical claims, not just "trust me, I can code" which never works with budget approval processes.
The GIAC and SANS community networking opportunities are valuable too, connecting you with other professionals who take technical skill development seriously instead of just collecting certifications for resume padding.
GPYC Exam Format and Structure
what GIAC GPYC (GIAC Python Coder) is
The GIAC GPYC certification is basically GIAC's way of saying "you can write Python that won't embarrass you in a security review." Not "I can script stuff," but "I can script stuff safely." Short version. Python plus security brain.
Who it's for: people doing Python for cybersecurity, automation in SOC/IR, detection engineering glue code, AppSec helpers, and anyone touching data parsing where one bad assumption turns into an incident. Honestly, if you've ever written a quick parser for logs and accidentally accepted garbage input, you already know why this exam exists, and why secure Python coding isn't optional once your scripts get adopted by a team.
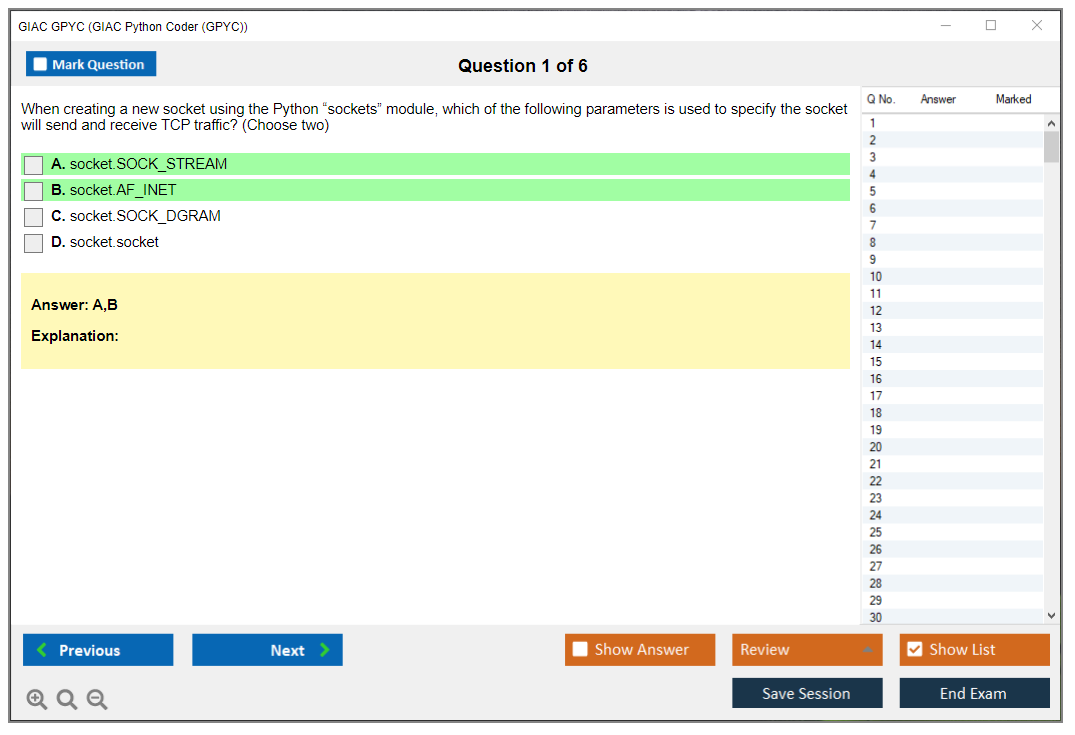
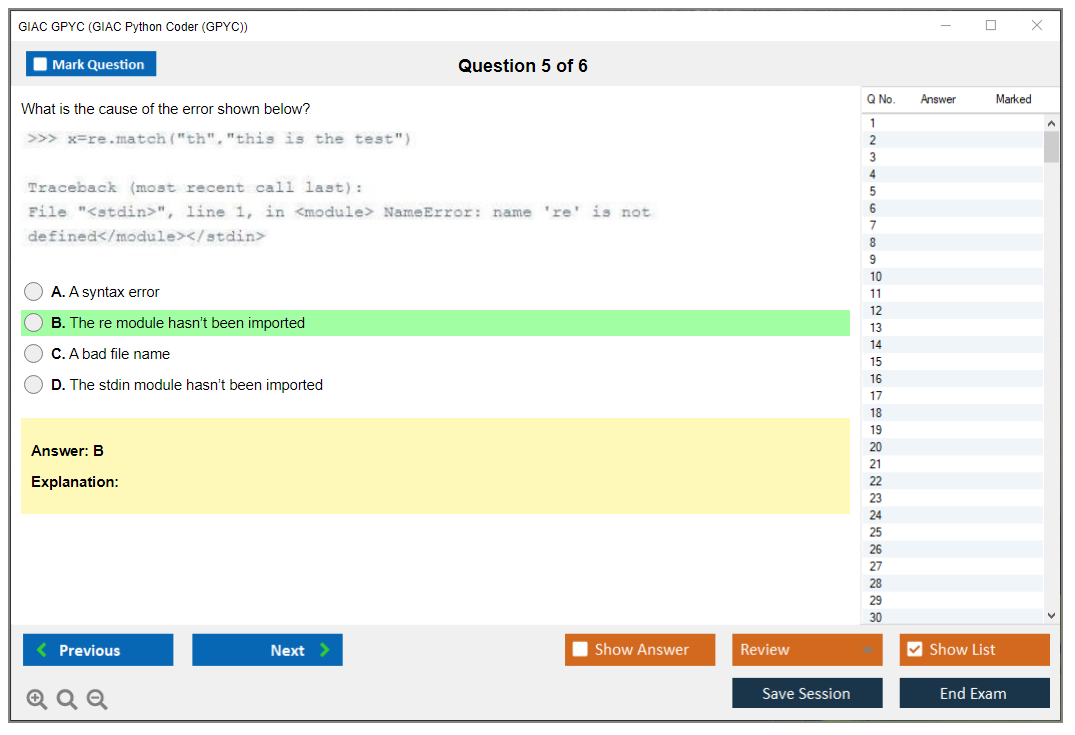
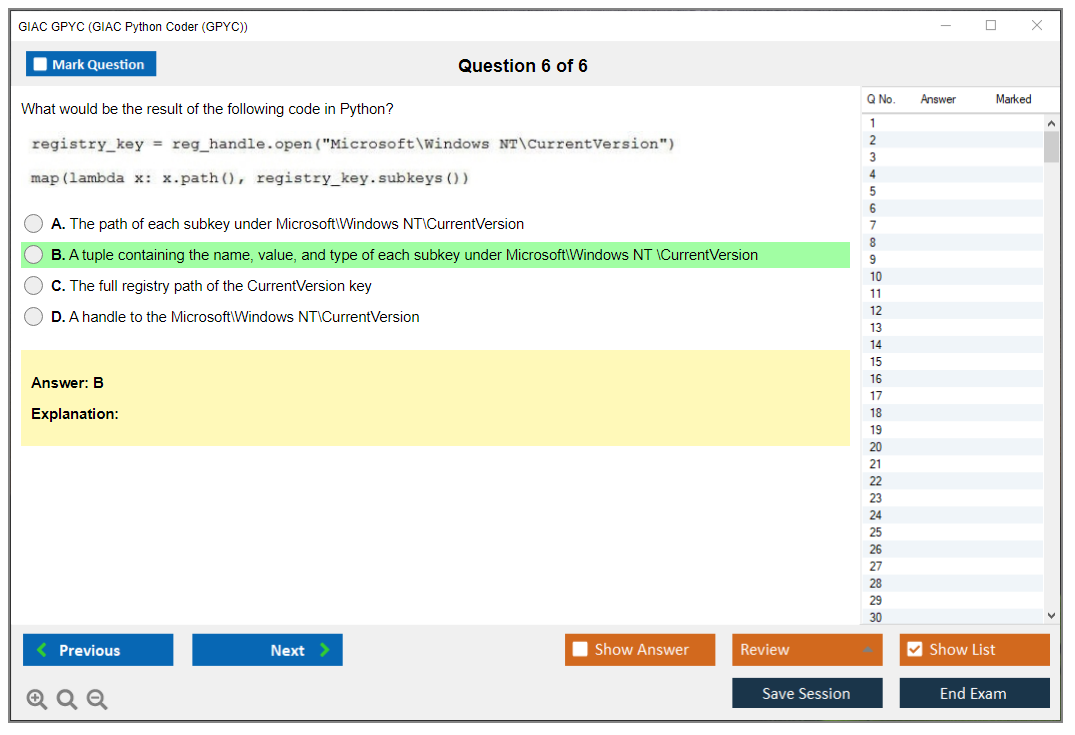
GPYC exam overview
The GPYC exam is computer-based and delivered through ProctorU remote proctoring. You can take it from home or the office, as long as your internet doesn't flake out mid-session.
Webcam, microphone, and a government-issued photo ID are required, and yes, they actually check. This is a proctored GIAC exam with strict monitoring that doesn't mess around with identity verification. Schedule it whenever you want inside your registration window, but don't be casual about the technical check. The "my camera drivers are weird" surprise is a bad way to start a timed exam. I mean, some locations may have alternative testing centers, which is nice if your home setup is chaos, or you just prefer the controlled vibe.
Format-wise, it's multiple-choice with a single best answer. Typically 75 to 82 questions depending on the version. You get 120 minutes. No breaks whatsoever. Plan accordingly. Questions come one at a time, linear. You can't skip and you can't go back. That one detail changes your strategy a lot, honestly, because you can't "bank" a hard one and return later, so you need to decide fast whether you're confident or you're making the best guess you can live with. Timer stays visible. Keep one eye on it.
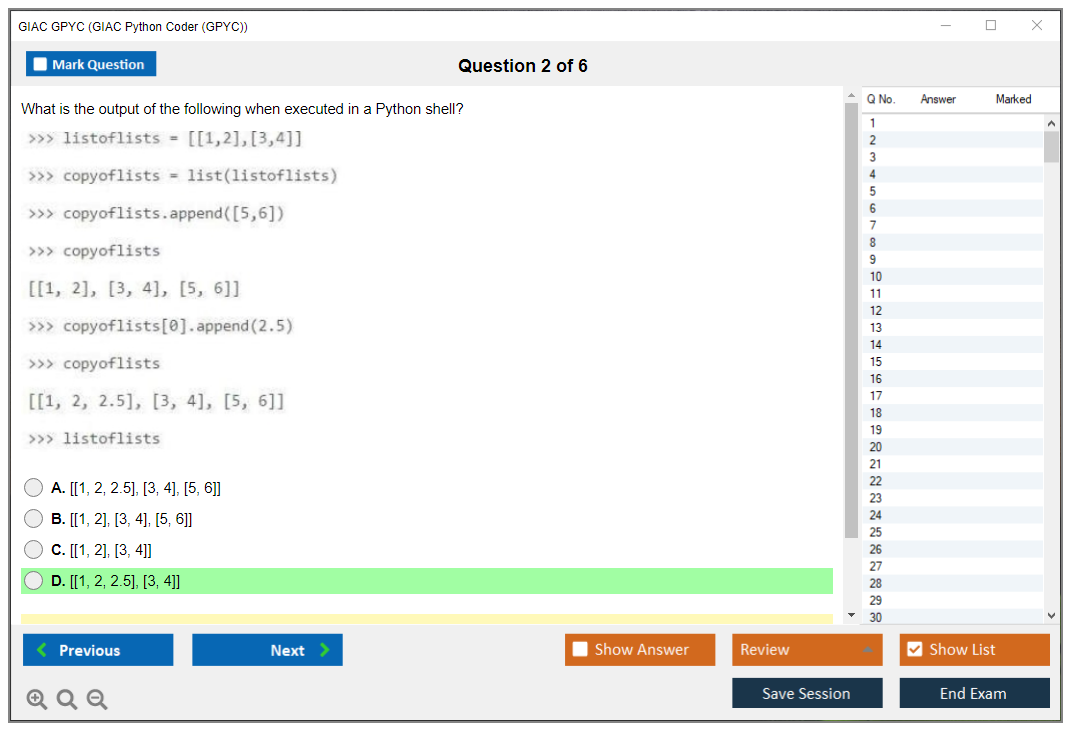
Question types and difficulty distribution
Expect questions that feel like real work. Like, "here's a function that processes user input, what's the risk and what's the fix," not just trivia.
You'll also see code snippet analysis where you have to understand what the code actually does. Output prediction questions require you to walk through the logic and figure out what gets printed or returned under specific conditions. This tests whether you've internalized Python's quirks or you're just guessing based on other languages. Debugging shows up too, usually in the form of identifying what's wrong, what exception you'll get, or which change fixes it without introducing a new problem.
Best-practice questions are common, especially around validation, parsing, handling untrusted data, error handling. How Python features can create security foot-guns. Conceptual questions exist, but they're usually tied to implications, not random history. Difficulty is mixed. Some are fundamentals. Some are the "wait, Python does that?" kind that punish sloppy mental models. I once saw someone trip over mutable default arguments on three separate questions because they never actually hit that bug in production. Seemed unlikely, but here we are.
Open-book policy and reference materials
GIAC exams are open-book. That's real. You can bring printed books, printed notes, and your own study materials. No electronic devices besides the exam computer, so no phone, no tablet, no e-reader.
Look, open-book doesn't mean easy. It means you're graded on speed and organization as much as memory, because 120 minutes goes fast when you're reading code and you can't revisit questions to double-check your work or reconsider answers you felt uncertain about during the first pass.
The single biggest advantage you can give yourself is an index. A good one. Many candidates build a detailed reference index during their prep, and it's not busywork, it's a time-management weapon. You should practice using your materials before exam day, because "I have it somewhere" isn't a strategy when the timer is bleeding out and you can't go back.
GPYC cost and registration validity
People always ask, "How much does the GIAC GPYC exam cost?"
The exact GPYC exam cost changes depending on whether you buy it bundled with training, discounts, and promos, so you need to check GIAC/SANS for the current number. What matters structurally is what you get: typically one attempt with the initial registration. Practice tests are often sold separately or included depending on the package.
Registration comes with a four-month window to schedule and complete the exam. You pick any date inside that validity period, but you must schedule at least 48 hours in advance. Rescheduling is allowed with enough notice. Fees may apply. If you miss the window, the attempt expires. Painful. Put the deadline on a calendar you actually look at.
Retake policy and results
One attempt is included. If you need another shot, you can buy additional attempts.
Retake eligibility is typically after a 30-day waiting period. Each attempt is scheduled separately, which gives you time to actually address the gaps in your knowledge rather than just immediately throwing yourself back at the same material hoping for different questions. Results are basically pass/fail, and you don't get a deep diagnostic breakdown. So if you fail, you're rebuilding your plan from your own notes and what you remember, not from a detailed score report.
"What is the passing score for GPYC?" GIAC sets a GPYC passing score, but they don't always plaster it everywhere in a way that stays consistent across time and exam versions, so treat any random number you see online with skepticism and verify with GIAC's current exam page. Same deal with "What are the GPYC exam objectives and topics?" The GPYC exam objectives are published by GIAC, and they're the only source I trust, because third-party lists tend to drift.
Difficulty, prerequisites, and prep reality check
"How hard is the GPYC certification exam?" It depends on whether you already write Python under pressure, and whether you've internalized security habits.
Time management matters more than people expect because of the linear question flow and no review. This is also where GPYC prerequisites come in: there aren't usually strict formal prerequisites, but recommended experience is real and you'll feel the difference if you skip the fundamentals. You want comfort with core syntax, standard library basics, reading other people's code, and common failure modes. Security knowledge helps, especially input handling, logging, safe defaults, and testing patterns.
For prep, people ask about GPYC practice tests and GPYC study materials. If you can get the official practice tests, do it, but don't just chase the score. Use them to tune your index and identify where you're slow. Official SANS courseware is the direct route if you're taking SANS Python security training, but supplemental stuff matters too: Python docs, linters, secure coding references.
Extra: build a few mini-scripts that parse messy input, handle errors cleanly, and log responsibly. That kind of practice pays back.
Finally, "How do I renew my GPYC certification?" That's the GPYC renewal requirements piece, and it ties into GIAC certification renewal (CPEs). GIAC certs generally renew on a cycle with continuing education credits and a fee. You track CPEs through training, conferences, relevant work, teaching, stuff like that. Boring admin. Still important.
GPYC Exam Objectives and Domain Breakdown
Overview of GPYC exam objectives structure
Real talk? GIAC's actually transparent here. They publish the full breakdown on their website, which makes planning study time way less painful than those vendor certs that keep you guessing about what's tested. The exam content gets organized into weighted domains that directly reflect how important each area is. Understanding those percentages matters because you don't want to spend three weeks mastering file operations only to realize it's 20% while Python fundamentals is 30%, you know?
The objectives get updated periodically. I mean, Python evolves fast. What mattered in 2019 isn't necessarily what you need in 2024, right? Each domain breaks down into specific topics and subtopics, like a full study checklist that's actually useful instead of marketing fluff. When I first looked at the objectives, I used them as a literal checklist, crossing off topics as confidence built.
Domain 1: Python fundamentals and syntax (approximately 25-30%)
This is foundational stuff. Expect heavy coverage of data types: strings, integers, floats, booleans, None. Variables, operators, expressions. The basic building blocks. Control flow structures like if/elif/else statements and both for and while loops come up repeatedly.
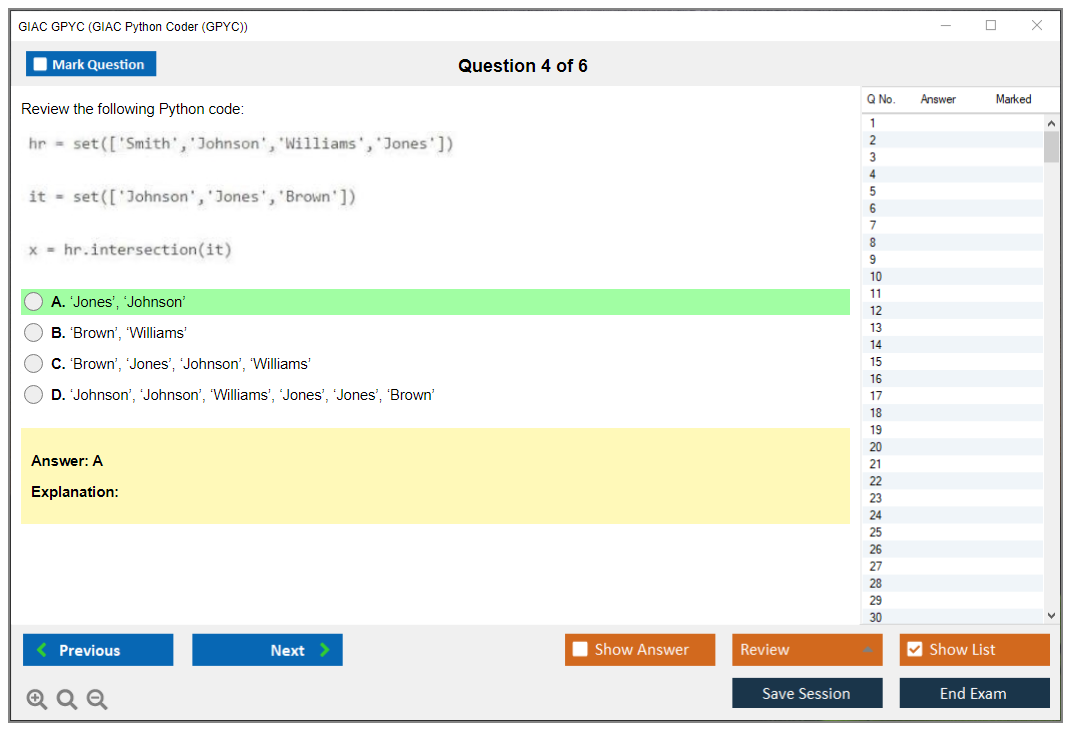
Functions? Huge. Definition, parameters, arguments, return values, scope. You've gotta understand all of it cold, because the exam tests this relentlessly in scenario-based questions that mirror real security scripting work. Data structures get tested thoroughly: lists, tuples, dictionaries, sets, plus questions on list comprehensions and generator expressions. String manipulation methods and formatting appear in practical situations where you're parsing logs or processing output.
The exam tests built-in functions like len, range, enumerate, zip, map, filter in context. You should understand mutable versus immutable objects. That's where people trip up. Exception handling with try/except/finally blocks and raising exceptions is critical for secure coding portions. Modules and imports matter too, plus Python's execution model (how the interpreter actually runs your code).
Domain 2: working with files and data (approximately 20-25%)
File operations? Everywhere in security work. Opening, reading, writing, closing files using different modes: read, write, append, binary. Context managers and the 'with' statement prevent resource leaks, which matters more in production security tools than people realize. You'll process CSV files using the csv module and work with JSON parsing and generation through the json module. That's huge for API work and configuration files.
XML processing shows up. Regular expressions for pattern matching and text extraction get tested heavily because, honestly, regex is how you actually parse logs and find indicators in security operations. There's no way around it. The os and pathlib modules handle file paths, and you need to know both approaches, even though pathlib is newer and cleaner. Reading and processing log files is a common scenario thread. Text encodings like UTF-8 and ASCII matter when dealing with international data or weird input. Binary file operations come into play for malware analysis situations.
I once spent an entire afternoon debugging a script that failed on log files from European servers. Turns out I'd assumed everything was ASCII, and some French accents broke my whole parsing routine. Cost me four hours I could have spent on actual analysis, all because I'd skipped the encoding basics during my initial learning. UTF-8 should be your default assumption unless you know otherwise.
Domain 3: Python standard library for security (approximately 15-20%)
Socket module basics. Foundational networking knowledge for client/server operations. HTTP operations using urllib and http modules let you interact with web services without external dependencies. The subprocess module is critical for executing system commands safely. Emphasis on safely, because this is where injection vulnerabilities hide and cause real damage.
Working with datetime and time modules helps with log analysis. Hashing and cryptographic operations with hashlib show up in integrity checking situations. The argparse module for command-line argument parsing is practical for building security tools that other analysts can actually use. The logging module lets you do proper application logging instead of just sprinkling print statements everywhere like a rookie. Collections module tools like Counter, defaultdict, and namedtuple make data processing cleaner. Meanwhile, itertools provides efficient iteration patterns that reduce memory overhead. Environment variables through the os module round out system interaction knowledge.
Domain 4: third-party libraries for cybersecurity (approximately 15-20%)
Requests library? Dominates. HTTP/HTTPS operations and API interactions in modern Python security work all run through requests. Beautiful Soup or lxml handle web scraping and HTML parsing when you're pulling threat intelligence or analyzing phishing sites. Scapy for packet crafting and network analysis is the gold standard for network security testing. No question.
The cryptography library handles encryption and decryption operations properly. Not rolling your own crypto, please. Pandas shows up for data analysis and manipulation, especially when working with large security datasets where manual processing isn't feasible. You need to understand when and how to install packages with pip. Also why virtual environments matter for project isolation, because that prevents dependency hell. Reading library documentation effectively is actually a tested skill because security practitioners need to learn new libraries constantly as the threat space shifts. Common security-focused libraries like yara-python, pefile, and dnspython appear in scenario questions.
Domain 5: secure coding practices (approximately 15-20%)
Input validation and sanitization techniques prevent most common vulnerabilities. Period. Command injection prevention is critical when using subprocess or system calls. SQL injection avoidance matters even though Python isn't SQL. You're often building queries that get executed elsewhere. Secure credential handling means not hardcoding passwords or leaving API keys in code where any intern with GitHub access finds them.
Path traversal prevention keeps file operations from accessing unauthorized directories. Proper error handling without information disclosure is a balance. Helpful debugging without revealing system internals to attackers who read stack traces. Secure random number generation uses the secrets module, not random (which is predictable and cryptographically weak). Understanding dangerous functions like eval, exec, and pickle helps you avoid security pitfalls that create vulnerabilities. The principle of least privilege in code design runs throughout secure Python development as a foundational concept.
Domain 6: testing and debugging (approximately 10-15%)
Writing unit tests with unittest or pytest frameworks ensures code reliability before production deployment. Debugging with pdb and strategic print statements solves problems faster than staring at code. Understanding Python tracebacks and error messages? Fundamental troubleshooting. Test-driven development concepts influence how you approach security tool development from the ground up. Code quality tools like pylint, flake8, and black maintain standards across teams. Testing edge cases and error conditions prevents security gaps in production that attackers exploit.
The GPYC exam objectives tie directly to real-world Python security work, unlike some certs that test trivia. If you're also pursuing broader security knowledge, check out GSEC or GPEN for complementary skills.
GPYC Exam Cost and Registration Process
What is GIAC GPYC (GIAC Python Coder)?
The GIAC GPYC certification (also called GIAC Python Coder (GPYC)) targets folks writing Python for security stuff. AppSec people. Pentesters. SOC automation folks. Even platform engineers who got voluntold to "just script it."
Python's everywhere in cybersecurity now, and honestly, GPYC is one of the few certs pushing you toward secure Python coding instead of cute syntax trivia. The thing is, hiring managers may not know every GIAC code, but they usually know GIAC means proctored, pricey, and not a random badge mill. That reputation can help when you're trying to move from "I write scripts" to "I build safe tooling."
Who GPYC is for
Security automation. Scripting for detection. Safer internal tools. Code review basics. People tired of breaking production with dumb string concatenation bugs.
Why GPYC matters for cybersecurity roles
It maps to real work. Parsing logs. Handling input. Avoiding dumb mistakes. Shipping code that won't bite you later.
GPYC exam overview
GIAC exams involve a proctored GIAC exam experience, meaning you're monitored remotely (typically ProctorU) and you're playing by strict rules. Closed environment, no wandering off, no second monitor unless explicitly allowed. It feels intense the first time.
Time pressure happens. Questions are practical. Some are "what does this code do," some are "what's the safest fix," and some are "spot the bug." If you're slow at reading Python, you'll feel it, because you're doing comprehension and security judgment at the same time. Annoying but fair, I guess.
Exam format (proctoring, question style, time limits)
One proctored attempt. Remote via ProctorU. Multiple-choice style with code snippets and scenarios.
GPYC exam objectives (what you're tested on)
The GPYC exam objectives generally orbit Python fundamentals plus security-minded coding: safer input handling, files, modules, common libraries, testing approaches, and patterns you'll see in tools. Always verify the live objectives on GIAC though, because they tweak them.
What skills GPYC validates
Secure Python coding. Automation patterns. Reading unfamiliar code fast. Debugging logic and security issues.
GPYC cost and registration
Let's talk money. People actually Google this at 2 a.m.
Standard exam-only registration is approximately $949 USD (2026 pricing), but how much the GIAC GPYC exam cost varies by region and promotions. You might see different numbers based on currency, taxes, or discounts. Wait, that price usually includes one exam attempt and a four-month scheduling window, and that window matters because miss it and you're emailing support and sweating.
You can also buy GPYC practice tests separately, usually around $99 to $149 each. Not gonna lie, GIAC practice tests are one of the better "pay to reduce anxiety" purchases if you're new to their style.
Retakes hurt. A retake exam is typically about $469 to $599 per additional attempt, again depending on current pricing. Prices subject to change, so verify current pricing on the GIAC website before you commit, especially if you're trying to get an employer PO cut.
GPYC exam cost (what's included, retake options if applicable)
Included with exam registration:
- one proctored exam attempt via ProctorU, which is the real gate
- four-month eligibility period to schedule
- access to exam objectives and candidate resources
- digital badge upon passing for LinkedIn and profiles
- certificate of achievement (digital and physical, though who actually frames these anymore?)
- listing in the GIAC certified professional registry
Additional costs (training, practice tests, renewal fees)
Extra costs add up fast. Supplemental GPYC study materials like Python books or secure coding references can run $50 to $200. You might spend $0 setting up a Python dev environment if you already have a laptop that isn't locked down by corporate policy.
Renewal is the other "surprise" line item. GPYC renewal requirements typically mean renewing every four years, with a fee around $469, plus earning CPEs. The cost of those CPEs varies wildly depending on whether you do paid training, conferences, or cheaper options like webinars and internal learning.
SANS training bundle options
If you want the full guided route, SANS has SEC573: Python for Penetration Testers, and it includes the GPYC exam. Pricing's usually in the $8,000 to $9,000 range with the exam, and yeah, that's a lot, but you're paying for instruction, a structured lab path, books, and four months of extended access. That's why some employers are fine funding it when "exam-only" doesn't come with a course.
Formats vary. OnDemand. Live online. In-person. Same content vibe, different schedule pain. SANS Python security training is basically exam prep plus hands-on reps, so if you're shaky on fundamentals, this route's less stressful than self-study plus hope.
Funding's the cheat code. Employer training benefits. Vouchers. Reimbursement programs. Sometimes payment plans through SANS for training bundles. Ask HR. Seriously.
Registration process step-by-step
Create an account on giac.org. Pick GPYC from the catalog. Choose exam-only or the training bundle option.
Pay via credit card for instant processing, or use a purchase order if you're corporate or government. You'll get a confirmation email. Then your four-month eligibility window activates. When you're ready you schedule through the ProctorU portal, picking a time when your house is quiet and your internet won't randomly die.
Payment and invoicing options
Credit cards are fastest. Purchase orders are common for employers. Training vouchers show up through SANS partners. Check with your manager before you front the money.
Refund and transfer policies
Exam registrations are generally non-refundable after purchase, so don't impulse buy. Transfers to another GIAC exam may be possible with approval and fees. SANS courses have their own cancellation rules. Read the terms, then buy.
GPYC passing score and scoring
People ask about the GPYC passing score, and GIAC does publish passing thresholds per exam, but they can update them. So the honest answer is: check the GPYC page for the current passing score number.
GIAC scoring's straightforward from a candidate perspective. You submit, you get a score report, and you know whether you passed. No weird "scaled mystery" explanations you have to decode.
GPYC difficulty - how hard is it?
Hard if you're slow at Python. Hard if you've never thought about security failures in code. Manageable if you've built scripts that parse messy input, handle errors, log safely, and you can read code quickly without panicking.
If you want a cheap warm-up, grab GPYC Practice Exam Questions Pack and use it to find your weak spots, then go back to the official GPYC exam objectives and patch the gaps. I mean, $36.99 is nothing compared to a retake.
GPYC prerequisites and recommended experience
Officially, GPYC prerequisites are usually "none required." Reality's different.
You should be comfortable with Python syntax, functions, exceptions, common standard library modules, basic tooling, and reading code you didn't write. Security knowledge that helps includes input validation, logging, basic crypto hygiene, testing habits, and knowing what "unsafe default" looks like.
Best GPYC study materials
Official stuff first. GIAC/SANS courseware if you have it. Candidate resources. The published objectives.
Supplemental: Python docs, secure coding references, linters like ruff/flake8, type hints with mypy if that's your style, and a few small scripts you write yourself. Also, if you want more reps before you burn your official attempt, GPYC Practice Exam Questions Pack is a decent way to pressure-test recall without overthinking it.
GPYC practice tests and exam prep strategy
Official GPYC practice tests feel closest to the exam vibe. Use one early to calibrate. Use one later to confirm you're ready.
Indexing notes can help if your prep style's book-heavy, but don't overdo it. Build quick references you can actually search mentally. For hands-on, write mini-projects: log parser, safe file handler, small API client with error handling, and a script that sanitizes input and produces structured output.
If you're cramming, GPYC Practice Exam Questions Pack can be your "what am I missing" checklist, not your whole plan.
GPYC renewal requirements
Renewal's typically every four years, with a maintenance fee around $469 and GIAC certification renewal (CPEs). Track deadlines. Don't guess.
You can earn credits through training, conferences, work projects, and teaching, plus other approved activities. Costs vary. Some are free. Some are expensive. Plan ahead so you're not paying last-minute for random webinars just to hit a number.
GPYC Passing Score and Scoring System
GPYC passing score requirements
You need 70% correct answers. That works out to roughly 53 to 58 questions right out of 75 total. Might sound generous compared to some vendor certs demanding 80% or higher, but GIAC exams are pretty consistent across their portfolio with this threshold. They've settled on 70% as the sweet spot that separates people who really know their stuff from those who got lucky cramming the night before.
What is the passing score for GPYC is standardized across all exam versions. You're not getting an easier or harder cut depending on which question pool you draw. GIAC uses a criterion-referenced model where you're measured against a fixed competency standard, not against other test-takers. No partial credit for multiple-choice questions either. Right or wrong. That's it. Each question weighted equally in scoring calculation, so that one obscure question about exception handling counts the same as a straightforward syntax question.
You have to demonstrate competency across all exam domains. That's the catch. Can't just ace Python basics and bomb secure coding principles and expect to pass. GIAC wants to see you're reasonably proficient across the board. Passing indicates job-ready Python coding skills for security contexts, which means employers who see your GPYC credential expect you can write secure scripts for automation, analysis, and tool development without creating new vulnerabilities.
How GIAC scoring works
Automated scoring immediately after exam completion. The moment you click that final submit button, the system's already calculating your result. Results available within minutes of finishing exam. You'll see pass/fail determination displayed on screen right there, which is both a relief and terrifying depending how you did. Those few seconds waiting for the result page to load feel like an eternity, honestly.
Detailed score report sent via email within 24 to 48 hours. That's where the real insight lives. Score report includes overall percentage and domain breakdown, showing you exactly where you crushed it and where you struggled. Domain-level performance shows strength and weakness areas using categories like "Above Target," "Near Target," and "Below Target." If you're planning a retake or just want to identify gaps in your knowledge, this breakdown's actually pretty valuable. Seeing "Below Target" on a domain you thought you knew well is humbling. I've been there.
Understanding your score report
Overall percentage score clearly indicated at top. Can't miss it.
Performance by domain gives you the granular view of where your Python security skills are solid and where they need work. Helps identify areas for improvement if retake needed, which most people don't need but some do. Even if you pass comfortably, that domain breakdown can guide your continued learning priorities once you're working with Python in actual security contexts.
No question-by-question breakdown provided. GIAC doesn't tell you which specific questions you missed because of exam security concerns. They reuse questions across exam versions, and detailed feedback would compromise the question pool. Your score report's proof you passed, though. Score valid for demonstrating competency to employers. You can share it with hiring managers if they want verification beyond the public registry.
Historical score data not compared. You're not competing against other candidates. Someone else's 85% doesn't make your 72% any less valid.
What happens if you don't pass
You still receive detailed feedback on domain performance even if you fail. Actually, especially if you fail. That domain breakdown becomes your study roadmap. There's a 30-day waiting period before retake eligibility, which gives you time to actually address weaknesses rather than just immediately burning another attempt.
Must purchase separate retake exam attempt. Yeah, GIAC doesn't bundle retakes into the initial exam cost like some vendors do. Frustrating when you're already out the cash from the first attempt and now you're staring down another payment just for the privilege of trying again. Use score report to focus additional study efforts on the domains where you fell short. If you scored "Below Target" on secure coding principles but "Above Target" on Python basics, you know where to concentrate your next month of prep.
Can retake exam multiple times if needed. There's no lifetime limit or anything punitive like that. Previous attempts don't negatively impact future results. Each exam's a fresh start. If you want practice without the financial hit of multiple attempts, the GPYC Practice Exam Questions Pack at $36.99 gives you realistic question exposure for a fraction of the retake cost.
Score validity and credential status
Passing score grants GPYC certification immediately. You're certified the moment that screen shows "Pass." Certification valid for four years from exam pass date, which is standard across most GIAC credentials. Score itself doesn't expire but certification requires renewal through CPEs, similar to how GSEC and GCIH work.
Employers verify certification through GIAC registry. They can look you up by name and see your active certifications and their expiration dates. Digital badge issued for LinkedIn and email signatures, which looks pretty sharp if you're building out your profile. I've seen people get recruiter messages within days of updating their LinkedIn with the badge, though obviously that's anecdotal. Physical certificate mailed to address on file, though most people care more about the digital verification these days.
Comparing GPYC difficulty to other GIAC exams
Generally considered intermediate difficulty. It's not as conceptually demanding as GCIA or as broad as GISP, but it requires actual hands-on Python experience. Focuses on practical application rather than memorization of security frameworks.
Technical nature requires hands-on Python experience. You can't just read about list comprehensions and exception handling and expect to nail those questions. You need to have written enough code that you recognize patterns and anti-patterns instinctively, the kind of pattern recognition that only comes from debugging your own mistakes at 2 AM when a script you thought was bulletproof keeps throwing unexpected exceptions.
The 70% passing score stays consistent with most GIAC certifications like GPEN and GCFA.
Pass rates not publicly disclosed by GIAC. Don't expect hard data on how many people pass on first attempt. Anecdotally, people with real Python experience and security awareness tend to pass without drama, while those coming from pure security backgrounds without coding practice struggle more.
GPYC Prerequisites and Recommended Experience
Official GPYC prerequisites (what GIAC actually requires)
Here's the deal. For the GIAC GPYC certification, there aren't any formal prerequisites. None. GIAC doesn't gatekeep this one. No "you must already have X certification" bureaucracy, no mandatory prior certs, and they're not forcing you into a SANS course before you can take a proctored GIAC exam.
Anyone can register if you're ready to prep and demonstrate competency. Self-study candidates sit right alongside SANS training students, which I honestly appreciate because it prevents the cert from becoming pure pay-to-play. Even though, let's be real, the whole ecosystem still costs a fortune.
But here's the thing. Practical experience? Strongly recommended for success, because GPYC isn't some vocab memorization drill where you cram definitions and coast through. You're gonna read code, reason about code, and identify mistakes that real developers make when they're rushing to ship something.
Prerequisites vs recommended experience (the part people ignore)
When people ask about GPYC prerequisites, I break it down two ways. Official prereqs? "Have money and ID for the proctor." Recommended prereqs? "Don't make this exam your literal first rodeo writing Python that does something useful."
I mean, I've seen people attempt brute-forcing this cert after a weekend binge of Python videos. They usually crash into the same wall. They can copy-paste code, but debugging under time pressure? Nope. And they lack instincts for safe input handling or structuring scripts so they don't devolve into tangled nightmares.
This is where "recommended experience" quietly impacts cost too. Go in underprepared, and suddenly you're buying extra GPYC practice tests, spending months on extended study, maybe even paying for a retake. Actually, funny thing about retakes, I once watched someone blow through three attempts because they kept treating it like a multiple choice theory exam instead of actual applied coding, but that's another story. Anyway, that's how the GPYC exam cost balloons in practice, even when the listed price stays fixed.
Recommended Python programming baseline (what "ready" feels like)
Want a clean baseline? Six to twelve months of hands-on Python coding is ideal. Not "I watched tutorials." You actually wrote scripts at work, at home, wherever. You broke them, debugged them, made them better. You should write Python scripts of 100+ lines independently without panicking, because once you're past toy examples, the challenge becomes organizing logic rather than remembering what lists do.
Python 3.x is essential. Python 2's basically extinct for modern security work, and any GPYC exam objectives aligned to actual environments assume Python 3 behavior. Get familiar with the standard library. Modules like argparse, json, csv, re, datetime, pathlib, logging, subprocess, plus urllib or http clients. Not every module ever created. Just the common ones you grab when building automation or parsing data.
The REPL? Your best friend. The Python interactive interpreter lets you test quickly, check types, validate regex patterns, or confirm function returns. People who never touch the REPL tend to be slower, more error-prone.
Reading other people's Python code matters tremendously. You'll encounter different styles, bizarre naming conventions, and code that technically functions but makes you question reality. Layer on basic debugging skills. Tracebacks, exceptions, knowing when to print statements, when to fire up a debugger, when to simplify until the problem reveals itself.
Tooling matters. Be comfortable in a terminal. Running scripts, passing arguments, redirecting output, inspecting files. Use a text editor or IDE: VS Code, PyCharm, Vim, whatever. Just pick one and master it enough that you're not wrestling your tools during prep.
Programming concepts you should know (no, not all CS theory)
Core programming concepts are straightforward. Variables, data types, type conversion. Conditionals. Loops. Exception handling. Functions, parameters, return values, scope. OOP basics like classes, objects, methods. Lists, dicts, sets, and knowing which to use when.
File I/O and text processing is huge for security-flavored Python, since so much work involves "grab this log, parse it, summarize it, alert on it." Code organization and modularity count too. You don't need to publish packages, but you should split code into functions, maybe modules, keeping everything readable.
Time and space complexity? Basic understanding only. Like, don't accidentally write an O(n²) loop over massive datasets when a dict lookup solves it. Don't load a 5GB file into RAM because you forgot about streaming line-by-line.
Security knowledge that helps (the GPYC edge)
GPYC is "Python coder," but it's clearly targeted at Python for cybersecurity work and secure Python coding, not just building random web apps. Basic cybersecurity concepts and terminology help since you'll recognize what code's trying to accomplish. OWASP Top 10 awareness proves useful, particularly around injection attacks, auth mistakes, unsafe deserialization patterns.
Input validation and secure coding principles appear everywhere. Logging too. If you've done log analysis or incident response, you already think in artifacts, timestamps, "what would I want this script to output so I can prove what happened." Networking basics help. TCP/IP, HTTP, DNS. You don't need packet-level wizardry, but understanding requests, responses, ports, common failure modes matters.
Crypto concepts, at minimum the basics. Hashing versus encryption. What salts accomplish. Why rolling your own crypto is catastrophic. Even if you never implement cryptography, you'll need to call the right library correctly and dodge unsafe defaults.
Security tooling familiarity is bonus points. SIEMs, IDS/IPS, firewalls. Mentioning them's easy, but the real advantage is understanding workflow. Alerts arrive, enrichment scripts execute, analysts need clean output, your Python glue code makes everything less miserable. That's why SANS Python security training pairs so well, even for folks self-studying with their own GPYC study materials.
Technical environment familiarity (what makes prep smoother)
Linux or Unix command line proficiency helps enormously. Windows PowerShell or cmd works too. Just don't be helpless outside GUIs. Understand file systems and directory structures, basic permissions, common networking commands like ping, netstat, nslookup.
You'll want comfort with pip and virtual environments. This one I'll actually expand on because it derails people constantly. If you can't create a venv, install dependencies, freeze requirements, reproduce your setup, you waste hours during prep and develop bad habits that surface later on the job. Git basics help but aren't required. Same with working with APIs and making HTTP requests, though that's standard in security automation.
Who should consider additional preparation (before paying for the exam)
Complete programming beginners should take an intro course first. Honestly. You'll progress faster overall building fundamentals, then circling back.
If you've only got scripting experience in another language, you might manage fine, but expect a ramp-up on Python idioms and the standard library. Professionals without recent hands-on coding practice should do a short rebuild phase too. Rust is genuine, and the exam clock shows zero sympathy.
People also ask about GPYC passing score, and sure, know the target before sitting, but the bigger point? The score's easier to hit when your fingers already know how to code. Same applies to GPYC renewal requirements later, or GIAC certification renewal (CPEs), because staying current becomes dramatically less stressful when you actually use Python in real work.
Conclusion
So is GIAC GPYC actually worth your time?
Honestly? Yes.
If you're already writing Python for security work (automation scripts, log parsers, API integrations, whatever) the GIAC GPYC certification is one of the few credentials that actually validates you can do it securely. And I mean like actually securely, not just "hey I followed a tutorial once" securely. Most Python certs are pretty generic, not gonna lie. They prove you can write a for-loop. GPYC proves you won't accidentally introduce SQL injection in your SIEM automation or leak credentials in your IR toolkit.
The thing is, the GPYC exam cost isn't cheap. The GPYC passing score threshold means you need to really know this stuff, not just memorize dumps. But that's kind of the point, right? When you pass, people know you've studied SANS Python security training or put in equivalent hands-on work. The exam objectives cover everything from secure coding patterns to practical tooling. Wait, actually it's theory, which matters way more than people realize.
Here's the deal.
GPYC prerequisites aren't strict ones, but you'll struggle if you're brand new to Python for cybersecurity. If you've been scripting for six months and understand input validation, exception handling, and why pickle is dangerous, you're probably ready to start studying. The difficulty curve is real though. Time management during the proctored GIAC exam kills people who haven't practiced enough. I've seen folks who could code circles around me just freeze up when the clock starts ticking.
GPYC study materials matter more than you'd think. Official courseware is solid but expensive. You'll want GPYC practice tests to calibrate your speed and identify weak spots in secure Python coding concepts. Hands-on labs beat flashcards every time for this cert, honestly. And yeah, don't forget about GPYC renewal requirements. You'll need CPEs through GIAC certification renewal, which honestly isn't hard if you're staying active in the field, attending conferences, or doing continued training.
Mixed feelings here.
If you're serious about validating your Python security skills and want to actually prepare instead of winging it, I'd suggest checking out a GPYC Practice Exam Questions Pack. Practice under realistic conditions makes a huge difference when you're sitting for the real proctored exam. You'll get familiar with question styles, timing pressure, and which exam objectives need more study time. It's not magic, but solid practice materials help you walk in confident instead of just hoping you studied the right things.
Show less info
Hot Exams
Related Exams
GCIA – GIAC Certified Intrusion Analyst Practice Test
GIAC Advanced Smartphone Forensics
GIAC GIAC Secure Software Programmer - C#.NET
GIAC Certified Perimeter Protection Analyst
GIAC Certified ISO-2700 Specialist Practice Test
GIAC Information Security Fundamentals
GIAC Certified Project Manager Certification Practice Test
GIAC GIAC Secure Software Programmer - C#.NET
GIAC Security Essentials
GIAC Python Coder (GPYC)
GIAC Secure Software Programmer – Java
GIAC Information Security Professional
GIACCertified Forensics Analyst
GIAC Certified Enterprise Defender
GIAC Systems and Network Auditor
GIAC Certified Firewall Analyst
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.