GCIH Practice Exam - GIAC Certified Incident Handler
Reliable Study Materials & Testing Engine for GCIH Exam Success!
Exam Code: GCIH
Exam Name: GIAC Certified Incident Handler
Certification Provider: GIAC
Corresponding Certifications: Security Administration , GCIH

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
GCIH: GIAC Certified Incident Handler Study Material and Test Engine
Last Update Check: Mar 23, 2026
Latest 705 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena GIAC GIAC Certified Incident Handler (GCIH) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
GIAC GCIH Exam FAQs
Introduction of GIAC GCIH Exam!
GIAC Certified Incident Handler (GCIH) is an exam administered by the Global Information Assurance Certification (GIAC) organization. The GCIH certification is designed to validate an individual's knowledge, skills and abilities to handle security incidents in a professional manner. The exam covers topics such as incident response processes and procedures, host-based analysis, network-based analysis, malware analysis, and more.
What is the Duration of GIAC GCIH Exam?
The GIAC Certified Incident Handler (GCIH) exam is a four-hour, computer-based exam consisting of 150 multiple-choice questions.
What are the Number of Questions Asked in GIAC GCIH Exam?
There are a total of 125 questions on the GIAC GCIH exam.
What is the Passing Score for GIAC GCIH Exam?
The passing score for the GIAC Certified Incident Handler (GCIH) exam is 70%.
What is the Competency Level required for GIAC GCIH Exam?
The GIAC GCIH exam requires a “Competent” level of knowledge and skills. This is the second highest level of certification, after “Expert.” In order to obtain a GIAC GCIH certification, candidates must have a deep understanding of the topics covered in the exam and be able to demonstrate their ability to apply their knowledge to real-world situations.
What is the Question Format of GIAC GCIH Exam?
GIAC GCIH exam have multiple choice, multiple response, drag and drop, fill in the blank and simulation type of questions.
How Can You Take GIAC GCIH Exam?
The GIAC GCIH exam can be taken online or at a testing center. To take the exam online, you must first register for the exam on the GIAC website. Once you have registered and paid for the exam, you will be sent an email with instructions on how to access the exam. To take the exam at a testing center, you must first find a testing center that offers the GIAC GCIH exam. Once you have found a testing center, you will need to register for the exam and pay the associated fee. You will then be given instructions on how to access the exam at the testing center.
What Language GIAC GCIH Exam is Offered?
The GIAC GCIH Exam is offered in English.
What is the Cost of GIAC GCIH Exam?
The cost of the GIAC GCIH exam is $699.00 USD.
What is the Target Audience of GIAC GCIH Exam?
The target audience for the GIAC GCIH exam is information security professionals who want to demonstrate their knowledge and experience in incident handling. Professionals who take this exam may include security analysts, system administrators, security engineers, and network administrators.
What is the Average Salary of GIAC GCIH Certified in the Market?
The average salary for someone with a GIAC GCIH certification is around $90,000 per year, depending on experience and location.
Who are the Testing Providers of GIAC GCIH Exam?
GIAC provides the official testing for the GIAC Certified Incident Handler (GCIH) exam. Candidates can register for the exam through the GIAC website.
What is the Recommended Experience for GIAC GCIH Exam?
The GIAC Certified Incident Handler (GCIH) exam is designed to test a candidate's knowledge and skills in incident handling and response. To prepare for the exam, GIAC recommends that candidates have at least three years of information security experience, with at least one year of incident handling and response experience. Additionally, GIAC recommends that candidates have experience in the following areas:
• Networking concepts, including TCP/IP, routing, and switching
• Operating systems, including Windows, Linux, and Mac OS X
• Security concepts, including firewalls, intrusion detection/prevention, and malware
• Security protocols, including SSL/TLS, SSH, and IPSec
• Security tools, including vulnerability scanners, packet sniffers, and log analysis
• Incident response processes, including incident identification, containment, eradication, and recovery
• Forensic analysis, including evidence collection, analysis, and reporting
What are the Prerequisites of GIAC GCIH Exam?
The prerequisite for the GIAC GCIH exam is a minimum of two years of experience in the Information Security domain, as well as a professional certification in a related field such as CompTIA Security+ or GIAC Security Essentials (GSEC).
What is the Expected Retirement Date of GIAC GCIH Exam?
The official GIAC website provides the most up to date information on exam retirements, including the GCIH exam. You can find the information here: https://www.giac.org/certification/retirement-schedule
What is the Difficulty Level of GIAC GCIH Exam?
The GIAC GCIH exam is considered to be of medium difficulty. It is recommended that candidates have at least three years of experience in the field before attempting the exam.
What is the Roadmap / Track of GIAC GCIH Exam?
The GIAC Certified Incident Handler (GCIH) certification roadmap consists of the following steps:
1. Become familiar with the GIAC Certified Incident Handler (GCIH) exam objectives.
2. Take a GIAC Certified Incident Handler (GCIH) training course.
3. Study the GIAC Certified Incident Handler (GCIH) exam objectives and related materials.
4. Take practice tests and review your results.
5. Register for the GIAC Certified Incident Handler (GCIH) exam.
6. Take the GIAC Certified Incident Handler (GCIH) exam.
7. Receive your GIAC Certified Incident Handler (GCIH) certification.
What are the Topics GIAC GCIH Exam Covers?
The GIAC Certified Incident Handler (GCIH) exam covers the following topics:
1. Security Incident Handling Process: This topic covers the process of responding to and managing security incidents, including the identification, containment, eradication, and recovery phases.
2. Network and Host-Based Analysis: This topic covers the analysis of network and host-based data to identify and respond to security incidents.
3. Malware Analysis: This topic covers the analysis of malware to identify its purpose and behavior, and how to respond to it.
4. Security Technologies: This topic covers the use of security technologies such as firewalls, intrusion detection systems, and vulnerability scanners to detect and respond to security incidents.
5. Digital Forensics: This topic covers the use of digital forensics techniques to investigate and respond to security incidents.
6. Security Policies and Procedures: This topic covers the development of security policies and procedures to ensure the secure operation
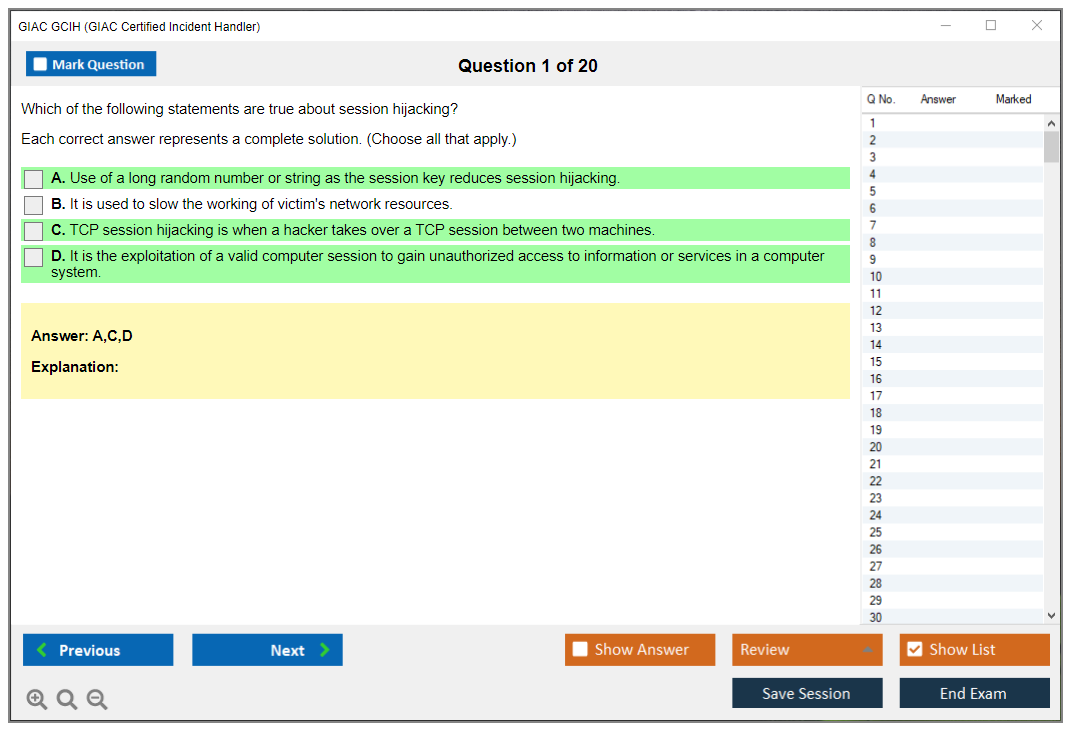
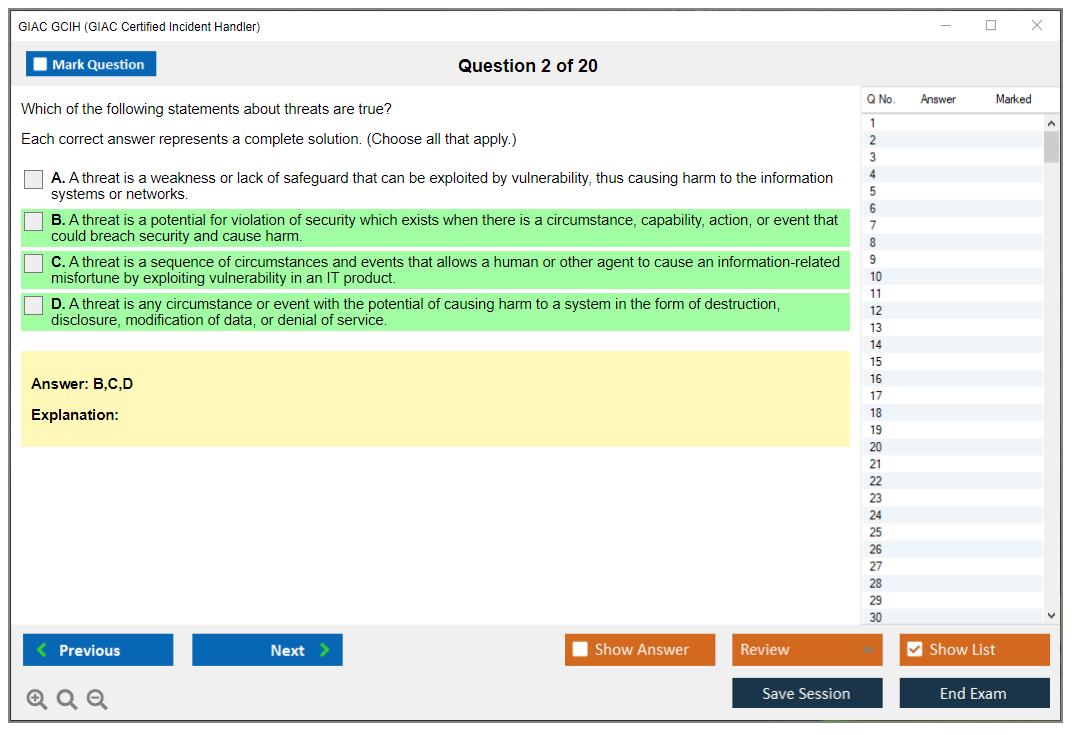
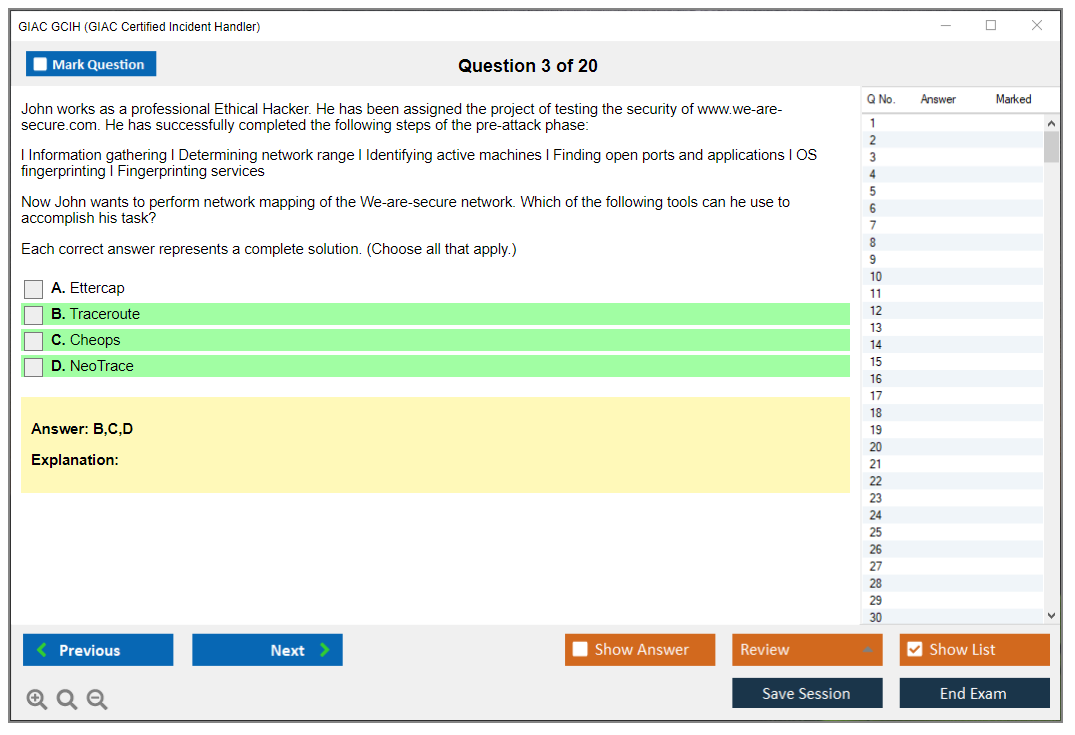
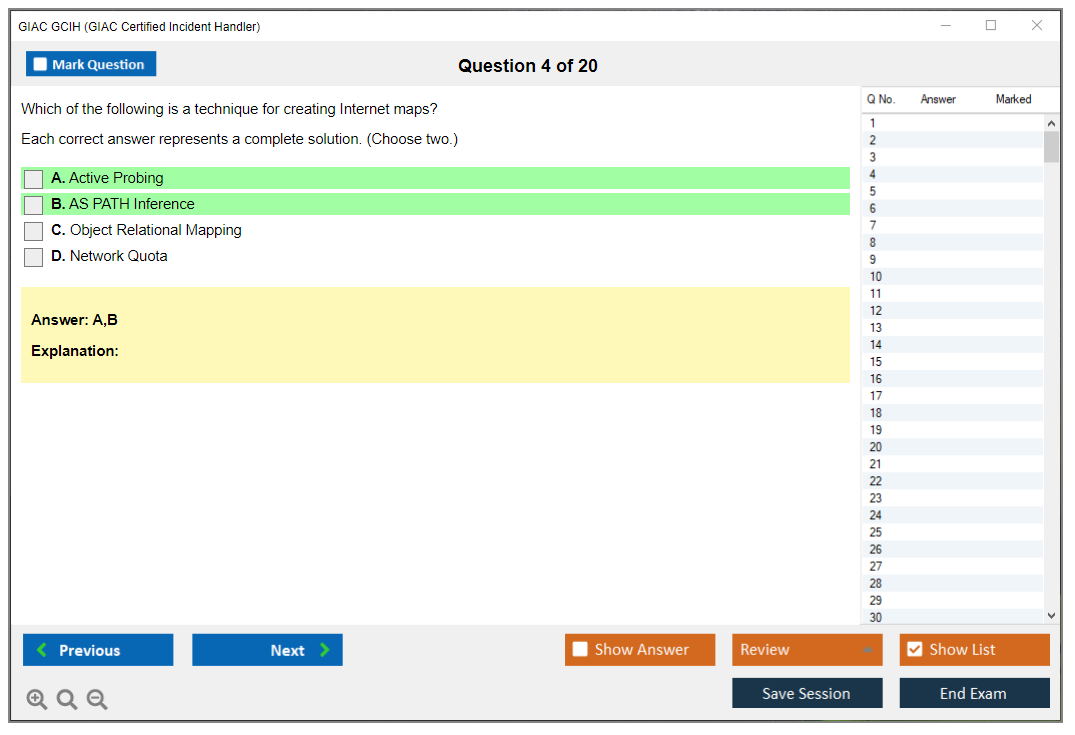
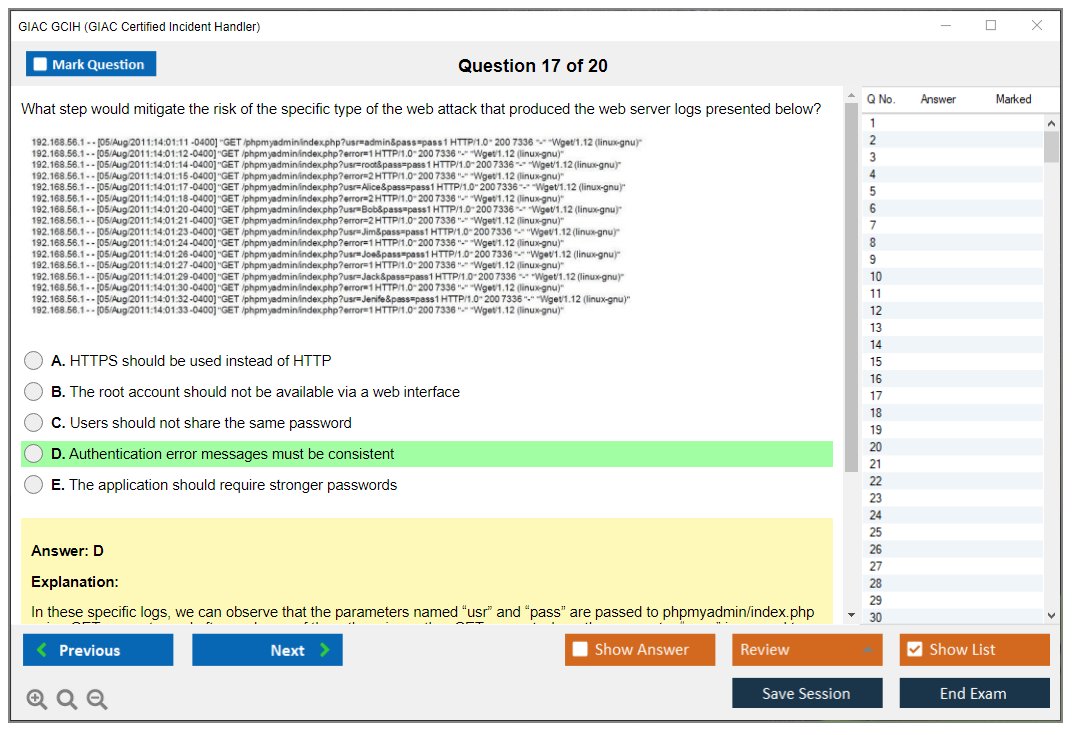
What are the Sample Questions of GIAC GCIH Exam?
1. What is the purpose of a honeypot in a network security system?
2. How can a network administrator detect malicious network traffic?
3. What methods can be used to secure a wireless network?
4. What is the difference between a vulnerability assessment and a penetration test?
5. What is the purpose of a firewall in a network security system?
6. What is the difference between a static and a dynamic analysis of malware?
7. How can an organization protect itself from insider threats?
8. What is the purpose of an intrusion detection system?
9. What techniques can be used to identify suspicious activity on a network?
10. How can an organization detect and respond to a denial of service attack?
GIAC GCIH (GIAC Certified Incident Handler) What is the GIAC GCIH (GIAC Certified Incident Handler) Certification? Look, if you're serious about incident response work, you need to know about the GIAC Certified Incident Handler certification. It's basically the gold standard for proving you can actually handle security incidents, not just talk about them at meetings. The GCIH validates that you've got the technical chops to detect attacks, respond when things go sideways, and clean up the mess afterward using real security skills that matter in the field. What GCIH actually proves you can do The GIAC Certified Incident Handler isn't one of those paper tiger certifications where you memorize some definitions and call it a day. This thing demonstrates you understand incident handling methodologies from start to finish. We're talking detection, containment, eradication, recovery. The whole lifecycle. You've gotta show you can analyze network traffic when something feels off, dig through... Read More
GIAC GCIH (GIAC Certified Incident Handler)
What is the GIAC GCIH (GIAC Certified Incident Handler) Certification?
Look, if you're serious about incident response work, you need to know about the GIAC Certified Incident Handler certification. It's basically the gold standard for proving you can actually handle security incidents, not just talk about them at meetings. The GCIH validates that you've got the technical chops to detect attacks, respond when things go sideways, and clean up the mess afterward using real security skills that matter in the field.
What GCIH actually proves you can do
The GIAC Certified Incident Handler isn't one of those paper tiger certifications where you memorize some definitions and call it a day. This thing demonstrates you understand incident handling methodologies from start to finish. We're talking detection, containment, eradication, recovery. The whole lifecycle. You've gotta show you can analyze network traffic when something feels off, dig through system logs to find indicators of compromise, handle malware incidents without making things worse, and document everything properly for legal teams and compliance auditors who'll inevitably ask questions three months later.
I mean, the skills here separate tier 1 SOC analysts who just escalate tickets from the people who actually solve problems. You'll prove you understand how attackers move laterally through networks, how ransomware operators establish persistence, and what to do when you discover someone's been in your environment for six months. Not gonna lie. These are the scenarios that keep security managers up at night, and GCIH shows you know how to handle them under pressure when everyone's panicking and executives are demanding answers before you've even finished your initial triage.
Who runs this certification and where it came from
The Global Information Assurance Certification organization administers GCIH. They're part of the SANS Institute family. Yeah, the people who basically wrote the book on practical security training. GCIH's been around as a foundation blue team incident response credential for years now. It's not some fly-by-night cert that appeared last year trying to cash in on the cybersecurity shortage.
GIAC built their reputation on practitioner-focused certifications that actually test whether you can do the work, not just whether you can regurgitate textbook answers. The GCIH specifically targets defensive security, which is where most organizations desperately need help right now because everyone's getting breached left and right.
Who should actually pursue GCIH
Honestly? This certification's designed for SOC analyst incident handling professionals who want to level up their game. If you're working in a security operations center dealing with alerts all day, responding to phishing campaigns, or trying to figure out if that weird network connection's malicious or just Bob from accounting doing something stupid again, GCIH's for you.
Incident responders are obvious candidates. Security engineers transitioning into defensive roles. Threat hunters who need to formalize their incident handling knowledge. I've also seen IT security professionals use this to pivot from general IT into dedicated security operations positions, which honestly makes sense because the cert forces you to learn the technical details you'll need. Blue team specialists who want proof they know their stuff fall into this category too.
Where GCIH fits in the bigger GIAC picture
The GIAC certification portfolio's huge, but GCIH sits at this sweet spot as a practitioner-level certification. It's more advanced than foundational certs like GISF but not as specialized as something like GCFA which focuses purely on forensic analysis. Think of it as the bridge between knowing security concepts and becoming an expert in specific domains.
It complements other GIAC credentials really well. If you've got GSEC covering your security essentials, GCIH's a natural next step into incident response. It pairs nicely with GCIA too since intrusion analysis and incident handling overlap constantly in real SOC environments. You can also branch into GPEN afterward if you want to understand the offensive side better, though that's a different animal entirely.
What you'll actually use these skills for
Here's where GCIH gets practical. You'll manage the complete incident lifecycle in production environments, from that first alert hitting your SIEM at 2 AM through the post-incident report your CISO presents to the board. You'll analyze network traffic patterns using tools like Wireshark when endpoint detection tools flag suspicious behavior, correlate logs from five different sources to build attack timelines, and respond to ransomware attacks without accidentally helping the attackers encrypt more systems.
The containment piece? Huge. Acting too fast can tip off sophisticated attackers, but waiting too long lets them exfiltrate your entire customer database. GCIH teaches you how to make those judgment calls. You'll also handle phishing campaigns that get past email filters, investigate potential insider threats without creating HR nightmares, and document everything for potential legal proceedings because sometimes these incidents end up in court whether you like it or not.
One thing nobody tells you is that you'll spend almost as much time explaining technical details to non-technical people as you will actually doing the technical work. Your CIO doesn't care about packet headers. They want to know if customer data got stolen and whether the CEO needs to start drafting a breach notification. GCIH doesn't explicitly teach executive communication, but you learn fast when you're writing those reports.
How GCIH fits with frameworks everyone actually uses
Look, certifications that don't map to real frameworks are basically worthless. GCIH aligns directly with the NIST incident response framework phases: preparation, detection and analysis, containment/eradication/recovery, and post-incident activity. That's the framework most organizations either use or pretend they use, so having a cert that follows it makes your life easier.
It also covers MITRE ATT&CK defensive techniques, which is increasingly becoming the common language for threat detection and response. When you're writing detection rules or explaining to management why you need budget for better endpoint visibility, being able to reference ATT&CK techniques by number makes you sound like you know what you're doing. Because you do.
The cert also reinforces SOC operational best practices that apply regardless of what tools your organization bought. Playbook development, escalation criteria, communication protocols during active incidents.
Career doors this thing opens
The incident response field's desperate for qualified people right now. Getting GCIH certified typically opens doors to incident response team positions at companies that take security seriously, tier 2 and tier 3 SOC analyst incident handling roles where you're actually making decisions instead of just following runbooks, and security operations leadership tracks if that's your thing.
I've seen people report salary increases of 15-25% after certification, though obviously that depends on your market and current compensation. More importantly, it qualifies you for specialized threat detection positions where you're hunting threats proactively instead of just reacting to alerts. Those roles usually pay better and they're more interesting than generic security positions.
For government work, GCIH's approved for DoD 8570/8140 IAT Level II and CSSP Incident Responder positions, which matters if you're interested in federal contracting or military cybersecurity roles.
Why vendor-neutral matters more than people think
Unlike vendor-specific certifications that basically train you to use one company's product, GCIH covers tools, techniques, and methodologies that work across diverse technology environments. Your skills transfer whether the next organization runs CrowdStrike or Carbon Black, Splunk or Elastic, Windows or Linux. You're learning incident handling principles, not just how to click buttons in a specific console.
This vendor-neutral approach means you're not locked into specific technology stacks, which gives you way more career flexibility. Companies change security tools every few years anyway, so learning fundamental skills that transcend specific products is the smarter long-term play.
The practical focus that actually matters
Real talk here. GCIH emphasizes hands-on technical skills over pure theory. You need to demonstrate actual incident handling capabilities, not just memorize incident response definitions from a textbook. The exam tests whether you can analyze real attack scenarios, interpret log data correctly, and make appropriate response decisions under time pressure.
This practical focus? It's why the cert actually means something to hiring managers. They know GCIH holders can contribute immediately instead of needing six months of on-the-job training to become useful.
Recognition that opens doors globally
The GIAC Certified Incident Handler certification's recognized by employers worldwide, not just in the US. Fortune 500 companies value it. Government agencies accept it. Managed security service providers actively recruit people with GCIH because they can bill them at higher rates to clients. That global recognition matters when you're job hunting or negotiating compensation, because you're not constantly explaining what your certification means.
The SANS SEC504 connection
While you don't technically need to take any specific training, GCIH exam objectives align closely with SANS SEC504 (Hacker Tools, Techniques, Exploits, and Incident Handling) course content. That's the full training most people use to prepare. SEC504's expensive though, so plenty of folks self-study using the objectives and various resources. The training's really good if you can afford it or convince your employer to pay, but it's not mandatory.
Why this isn't an offensive security cert
GCIH focuses on defensive blue team incident response, not penetration testing or ethical hacking like GPEN. You're learning to defend. Not attack. That said, understanding attacker methodologies is required for effective defense, so you'll study how attacks work but from the defender's perspective. The thing is, if you want to break things professionally, look elsewhere. If you want to stop the people breaking things, GCIH's your path.
What you need before starting
There aren't formal prerequisites, but honestly, you'll struggle without some foundation. Successful candidates typically have 2-3 years of IT security experience, strong networking fundamentals (TCP/IP, ports, protocols), familiarity with both Windows and Linux operating systems, and basic understanding of common attack vectors. If you've got Security+ or similar foundational knowledge, you're probably ready to start studying seriously.
GCIH Exam Format, Structure, and Objectives
what is the GIAC GCIH (GIAC Certified Incident Handler)?
The GIAC GCIH certification is an incident handling certification that basically tries to prove you can survive real blue team incident response work without freezing when the alerts start stacking. It's tied closely to SANS SEC504 GCIH, so the vibe is very "practical defender who understands attacker tradecraft," not academic security theory.
Who's it for? Look, if you're a SOC analyst grinding incident handling queues all day, an IR analyst doing investigations, a security engineer who gets pulled into containment calls, or a blue team lead writing the postmortem, this one fits. New folks can take it too, but honestly you'll have a better time if you've already touched Windows logs, basic Linux, and at least one packet capture that made you question your life choices.
What skills does it validate? Detection and triage. Network and host analysis. Containment and eradication. Some web and cloud incident basics. Malware handling fundamentals. And yeah, the "adulting" parts like evidence handling, comms, and post-incident reporting. Short version? You respond. You document. You improve. Then you do it again next Tuesday when someone clicks the phishing link anyway.
GCIH exam overview
GCIH's administered as a proctored exam, and you can take it either at an in-person testing center or through remote online proctoring. That flexibility matters if you're not near a test center, or you don't wanna burn a whole day commuting just to stare at questions under fluorescent lighting.
The test is 106 questions. Four hours total, which works out to about 2.25 minutes per question. Some are quick recall. Some are "here's a scenario, here are the artifacts, what do you do next," which eats time because you're reading carefully, interpreting context, trying not to overthink the distractor answers. No negative marking, so a wrong answer doesn't subtract points. Guess if you must. Leaving blanks is just donating points.
GCIH's open-book. Printed books, personal notes, indexes, course materials. This is where people get the wrong idea. Open-book doesn't mean easy. It means you're tested on whether you can find the right thing fast, and whether you understand it well enough to apply it in a messy situation when the question's written like a mini incident ticket with incomplete details. The thing is, indexing becomes part of your skill set, not a nice-to-have.
Remote proctoring has its own rules. You'll need a webcam, microphone, government-issued ID, and a secure testing environment that's quiet and interruption-free, plus compliance with GIAC's proctoring protocols. No wandering off. No "my roommate will be quiet" assumptions. Clear your desk. Do the system check early because that stuff's boring until it isn't, and then it becomes the reason you're rescheduling.
Difficulty progression is real. Early questions can feel like basic terminology and process checks, then you hit scenarios where you're analyzing logs, network traffic behaviors, or indicators that hint at a specific technique, and you're asked for the best response action, not just the technically correct statement. I mean, many questions put you right in the middle of an active incident, and they're written to see if you can think like both attacker and defender, because that's how incident response works in practice.
You get preliminary pass/fail immediately when you finish. Official score reports typically land within 24 to 48 hours.
GCIH exam objectives (domains)
The GCIH exam objectives are split into domains with approximate weightings. The percentages matter 'cause they hint where your study time pays off, but don't be that person who ignores "small" domains and then gets wrecked by a handful of questions that were basically free points.
Domain 1: incident handling and response fundamentals (15 to 18%). This is lifecycle stuff. NIST-style phases, categorization, prioritization, chain of custody, evidence preservation, comms protocols, and stakeholder coordination. It sounds fluffy. It isn't. A lot of real incidents go sideways because people don't track decisions, don't preserve evidence, or notify the wrong group at the wrong time.
Domain 2: detection and analysis (20 to 23%). This is the heart of SOC work: logs, SIEM correlation, network monitoring, endpoint detection, normal vs anomalous behavior, triage, scoping, and reducing false positives. Expect questions that feel like "you see X alert plus Y log line, what's your next move," because that's the job.
Domain 3: network-based attacks and defense (18 to 21%). TCP/IP fundamentals for security. ARP spoofing, DNS attacks, man-in-the-middle, command-and-control patterns, Wireshark-style traffic analysis concepts, and containment actions you can do at the network layer. Tool-agnostic approach applies here. The question might name Wireshark, but it's really testing whether you understand what the packet behavior means and what defensive step makes sense.
Domain 4: host-based attacks and defense (18 to 21%). Windows and Linux internals at the "incident handler" level, privilege escalation concepts, persistence mechanisms, registry and scheduled task abuse, services, credential theft, pass-the-hash, and artifact collection. This domain's where people burn time flipping through notes because the artifacts are numerous and the question wording can be picky. Plus Windows registry paths all start to look the same after question 60.
Domain 5: web application and cloud security incidents (10 to 13%). SQL injection, XSS, CSRF, web server logs, cloud basics, container fundamentals, and how to respond when the attack's at the app layer. Not gonna lie, this domain can feel broad, but the exam tends to focus on recognizable patterns and response steps, not deep dev work.
Domain 6: malware analysis and threat intelligence (12 to 15%). Malware categories like trojans, ransomware, worms. Static vs dynamic analysis concepts, behavioral clues, extracting indicators of compromise, and integrating threat intel into response decisions. You're not doing reverse engineering here, but you are expected to know what to look for and how to contain.
Domain 7: containment, eradication, and recovery (8 to 11%). Isolation strategies. Segmentation, remediation, secure rebuilds, backup restoration, validation, and preventing reinfection. This is where "best" answer matters, 'cause you can often do multiple things, but only one's the safest next step given the scenario.
Domain 8: post-incident activities (6 to 9%). Documentation, timelines, root cause analysis, lessons learned, metrics, reporting, compliance notifications, and continuous improvement. Process heavy. Still tested. Still points.
GCIH cost, passing score, and grading
People always ask about GCIH exam cost and GCIH passing score, and I mean.. those change. GIAC updates pricing, bundles, and policies often enough that quoting a number in a blog post can age badly. Same for passing score: GIAC publishes it, but it's not something I like to hardcode without checking the current page the week you're registering.
Grading's straightforward from a candidate perspective: multiple-choice questions, no negative marking, and you get that immediate provisional result at the end. If you fail, you'll be looking at a retake process and whatever current retake policy applies at purchase time, which is why you should read what your exam attempt includes before checkout, not after.
how difficult is the GCIH exam?
Is GCIH harder than Security+ or CySA+? Usually, yeah, because it expects more operational thinking and less memorization-only behavior, plus the scenarios are closer to what you see in blue team incident response. But it's also open-book, which changes the game. Open-book rewards organization and calm execution. It punishes chaos.
Time management's the silent killer. Two minutes per question goes fast when you're scanning an index, flipping pages, rereading a log snippet, and then realizing the question's asking for the "best next action" rather than "what does this term mean." Build your index. Practice using it under a timer. Do at least some GCIH practice tests if you can, 'cause they train your pacing and show where your notes are weak.
Common failure reasons? Weak indexing. Overreliance on searching through books mid-exam. Not enough hands-on familiarity with logs and traffic. And honestly, some folks just haven't built the defensive mindset yet, where you can think like an attacker long enough to predict what evidence they leave behind.
GCIH prerequisites and recommended experience
Official GCIH prerequisites aren't usually framed as strict "must have X cert," but recommended background matters. You want comfort with TCP/IP, basic Windows and Linux administration concepts, common log sources, authentication basics, and a little scripting literacy (PowerShell exposure helps). Prior certs like Security+ or CySA+ can help as a base, but GCIH expects you to apply, not just recall.
best GCIH study materials and indexing
Most people go through SEC504 courseware, 'cause it maps cleanly to the exam. Self-study's possible, but you'll need to recreate the structure yourself, and that's harder than it sounds when you're trying to cover network attacks, host artifacts, malware handling, and incident process all at once.
Indexing: do it step-by-step. First pass, capture key terms, tools, and "when you see X, check Y" type notes. Second pass, add page numbers and short labels that you can scan fast. Third pass, test the index using practice questions and fix whatever slows you down. Keep it printable and simple. Fancy formatting doesn't win points.
Other GCIH study materials you add are up to you. Some people like extra Windows artifacts references. Others want more Wireshark practice. Mentioning the rest casually: vendor log guides, threat intel primers, basic web vuln references, incident response playbook templates.
GCIH renewal (recertification) basics
GCIH renewal (recertification) is part of the deal with GIAC certs, and it typically involves a renewal cycle, fees, and earning GIAC recertification CPEs through approved activities. The exact numbers and deadlines can shift, so check the current GIAC recertification page when you're planning, not when you're already late and scrambling for credits.
quick GCIH FAQs
How much does the GCIH exam cost? Check GIAC's current pricing page for your region and what's included with the attempt.
What's the passing score for GCIH? GIAC publishes the current passing score for the exam, and you should verify it close to your test date.
What are the GCIH exam objectives and domains? The eight domains above are the core: fundamentals, detection, network, host, web and cloud, malware and threat intel, containment and recovery, post-incident.
How do I renew my GCIH certification? Track your GIAC recertification CPEs, submit them in the portal, and pay the renewal fee within the renewal window.
Is GCIH worth it? If you want credibility in SOC and incident response roles and you actually plan to do the work, yeah, it's a strong signal. If you're chasing letters with no plan to touch logs or handle incidents, you're gonna hate studying for it.
GCIH Exam Cost and Investment Considerations
The reality of GCIH pricing in 2026
Not gonna lie, the GIAC GCIH certification costs serious money. As of 2026, a standalone exam attempt runs you $949. That's just the test. No study materials, no practice questions, nothing else included. Feels pretty steep when you're paying basically a thousand bucks for the privilege of sitting the exam compared to something like GSEC or even CompTIA options that come in cheaper.
Here's the thing, though. Most people don't just buy the exam by itself, and that's where the whole pricing picture shifts completely. Bundling it with training changes everything about what you're actually spending money on.
The SANS SEC504 bundle and what you're really paying for
Real talk here. The full SANS SEC504 Hacker Tools, Techniques, Exploits, and Incident Handling course with the GCIH exam included typically costs between $8,200 and $9,500 depending on delivery format. Live online courses hover around the middle of that range. In-person training at conferences or dedicated events can push toward the upper end. Yeah, that's a serious chunk of change. More than some used cars I've owned.
OnDemand training provides another path. You'll get self-paced access to all the course videos, labs, and materials for four months, plus the exam attempt bundled in. Usually runs around $7,500 to $8,000. It's cheaper than live instruction but requires way more self-discipline since there's no instructor keeping you accountable or classmates to bounce ideas off when you're stuck on some concept.
SANS training is legitimately good, though. The SEC504 courseware is dense, practical, and directly aligned to what the GCIH exam tests. If you're completely new to incident handling, that training can compress years of on-the-job learning into a week or a few months of focused study depending on your background. I once tried self-studying for a similar certification and ended up wasting three months going down rabbit holes about packet analysis techniques I'd never actually use, so having that structured path matters more than you'd think.
Practice tests and the hidden costs that add up
Official GIAC practice tests? $299 each.
That might seem steep for what's basically a glorified quiz, but these practice exams are worth every penny if you're serious about passing. They simulate the actual exam difficulty and question style better than any third-party resource. For more affordable prep I'd also check out the GCIH Practice Exam Questions Pack at $36.99 which gives you solid question exposure without the full GIAC price tag.
Most candidates take at least one practice test. Some take two. Add that to your running total, and we're not even talking about the extra materials yet. Maybe you grab a couple books on incident response or network forensics. Perhaps you subscribe to an online platform for hands-on labs. Possibly you need some software licenses or cloud credits to build a practice environment. These costs are smaller individually but they accumulate fast. I mean, I've seen people spend $100 to $500 easily on this stuff before they even sit the exam. Catches folks off guard.
When things don't go as planned
Failed your first attempt?
The retake fee is $649. That's actually $300 less than the initial exam but still not pocket change by any measure. Depending on your original purchase package, retake policies might vary. Some SANS bundles include a free retake or discounted second attempt, but the standalone exam purchase usually doesn't offer squat.
Success rates for GCIH are decent if you've done the SANS training and put in proper study time. Self-study candidates without formal training face tougher odds, though, since you're basically gambling that $949 on your ability to learn complex incident handling concepts and SANS-specific approaches without structured guidance or instructor feedback.
Ways to reduce the financial hit
Employer sponsorship is huge, honestly. Many organizations will fully cover GCIH certification costs for SOC analysts, incident responders, or security engineers where incident handling is a core job function. If you're in one of those roles, absolutely explore this before paying out of pocket. I've worked places that had annual training budgets per employee specifically for certs like this.
Government and military pricing exists. It can knock 10-25% off depending on your affiliation, though it's not advertised everywhere. You just need to ask SANS or check during registration.
Early bird discounts for SANS courses sometimes offer $400-$600 savings if you book months in advance. Group discounts apply when organizations send multiple people to the same training session, with savings scaling based on headcount. If you've got coworkers who also need the cert, coordinate and save collectively.
The self-study route brings total costs down to maybe $1,200-$1,500 if you're disciplined. Exam fee plus practice test plus some reference books. But let's be real, you're accepting higher risk of failure and potentially needing that $649 retake, which could actually make the total higher than if you'd just done the training initially.
The investment math that actually matters
Here's what changed my perspective. GCIH-certified professionals report average salary bumps of $8,000 to $15,000 annually. The certification frequently pays for itself within 6-12 months just through compensation improvements alone. Job postings requiring GCIH specifically are common in government contracting, defense sectors, and organizations with mature security operations programs. Roles that often pay premium rates compared to general security positions.
Beyond immediate salary impact? The cert accelerates career progression.
Demonstrating commitment to professional development and validating your incident handling skills often speeds up promotion timelines in SOC and incident response career tracks. I've seen people jump from tier 2 analyst to senior IR consultant roles partly on the strength of GCIH plus experience. Obviously the experience matters too, though.
The skills you build during preparation have immediate daily value. Even if you never took the actual exam (wait, that sounds weird, but hear me out) working through SEC504 material or studying incident handling methodologies makes you better at your job starting immediately. You'll triage alerts faster, investigate suspicious activity more effectively, and understand attacker techniques at a deeper level than before.
The time cost nobody talks about enough
Study time represents significant opportunity cost beyond monetary expenses. Preparation typically demands 60-120 hours depending on your background. That's 60-120 hours you're not spending on side projects, family time, other learning, or just relaxing. If you've got a demanding job and personal responsibilities, carving out that study time becomes its own investment that's harder than the money part for some folks.
Building lab environments for hands-on practice might require additional hardware, software licenses, or cloud infrastructure costing another $100-$500 realistically. In-person SANS training could necessitate travel, hotels, and meals adding $1,000-$3,000 to your total depending on location and duration.
Long-term value considerations
GCIH stays valid four years before renewal.
That's actually pretty good compared to annually-renewed certifications that nickel-and-dime you constantly. The renewal fee is $429 plus you'll need continuing education credits, but that's spread across four years. You're getting extended value from a single investment rather than constant recertification treadmills.
Comparing to related certs, GCIA dives deeper into intrusion analysis but costs similarly. GPEN focuses on offensive testing from a different angle entirely. The GCFA forensics certification builds on incident handling skills if you want to specialize further down the line. Each serves different career trajectories but all carry similar pricing structures, so you're not getting ripped off specifically on GCIH versus other GIAC options.
Is GCIH expensive? Absolutely, no question. Is it worth it if incident response is your career path? Also yes, assuming you can swing the upfront cost or get employer support to foot the bill. The certification opens specific doors, validates practical skills, and typically delivers positive ROI within a year through salary and opportunity improvements. Just go in with realistic expectations about the total investment. it's the exam fee, it's everything around it too.
GCIH Passing Score and Grading System
What is the GIAC GCIH (GIAC Certified Incident Handler)?
GIAC GCIH certification is one of those credentials that hiring managers recognize fast because it maps to real blue team incident response work, not trivia. It's aimed at people who're expected to detect, contain, and clean up security incidents without panicking, plus write down what happened in a way that doesn't make leadership's eyes glaze over.
SOC analysts. IR folks. Blue team engineers.
This is also a great fit if you're the security person who keeps getting pulled into "hey can you take a look at this weird alert" and you want a structured way to level up. The GIAC Certified Incident Handler (GCIH) name's literal. You're proving you can handle incidents. That's why it's got staying power.
Who GCIH is for
If your day includes SIEM alerts, endpoint telemetry, packet captures, or explaining to IT why you need isolation on a host right now, you're the target audience. SOC analyst incident handling's a huge chunk of what the exam feels like, especially the "triage quickly, then go deeper" mindset. Security engineers doing on-call rotations also get value here, because the test pushes you toward repeatable process instead of vibes.
What skills GCIH validates
Detection and triage. Network and host analysis. Basic attacker tradecraft. Containment and recovery.
And look, the part people underestimate's the reporting and post-incident stuff. Lessons learned. Scoping. Evidence handling. That's the difference between "we cleaned the box" and "we actually reduced the chance it happens again."
GCIH exam overview
The GCIH exam's proctored and multiple-choice. It's also open-book, which sounds like easy mode until you realize open-book only helps if you can find answers fast. If you're flipping through PDFs like it's 2009, you're gonna burn time and miss questions you actually know.
106 questions total. Fixed time window.
A lot of candidates take it after SANS SEC504 GCIH training, and that pairing makes sense because SEC504's basically the curriculum for the incident handling certification. Self-study's possible, but you need your own structure, and you need labs or real work exposure so the concepts stick.
Exam format (proctored, question style, open-book policy)
Everything's scored right or wrong. No partial credit. That matters more than people admit. If two options look close and you "almost" know it, you still get nothing for being close, so accuracy beats vague familiarity every time.
Open-book also rewards indexing. Hard.
GCIH exam objectives (domains)
GIAC breaks the GCIH exam objectives into eight major domains, and your score report later'll show how you did in each one. The domains cover the incident handling lifecycle, detection and triage, network and host attacks, web attack basics, malware and tradecraft, containment and recovery, and then post-incident activities like reporting and improvement.
Some topics are straight memorization. Others're pattern recognition. Knowing what artifact matters, where to look next, and what a specific behavior usually indicates.
GCIH cost (exam fees and total cost considerations)
People always ask, "How much does the GCIH exam cost?" because yeah, GIAC pricing's not subtle. The standalone exam attempt's commonly listed at $949, and retakes're $649, which is a $300 discount from the initial attempt price. Not cheap. Not pretend cheap either.
Training's the bigger variable. SANS SEC504's the common path, and it's excellent, but it's a real budget conversation, especially if your employer isn't paying. If you're self-studying, you end up paying in time and trial-and-error instead of tuition. Or both, really, depending on how stubborn you are about learning everything the hard way.
What's included and what people forget
GIAC practice tests matter. A lot. The official ones help you calibrate timing and find weak domains before you burn an attempt. If you also want extra reps, you'll see products like a GCIH Practice Exam Questions Pack for $36.99 floating around, and while I'm not saying it replaces real study, it can be a useful way to pressure-test recall and your index speed.
GCIH passing score and grading
This is the part everyone googles at 2 a.m.
The GCIH passing score requirement's 71% or higher to earn the credential. With 106 questions, that means you need at least 75 correct answers. That's the line. No vibes. No "I felt good about it."
GCIH passing score (what you need to pass)
71%'s the threshold, and it's stayed pretty consistent across exam versions. GIAC can adjust based on psychometric analysis, but historically this one's been stable, so you can plan around it. Also, scores're absolute. There's no curve, no adjustment against other test-takers, no "everyone did poorly so you're fine." Your performance's measured against a fixed standard.
Here's where people get tripped up. GIAC uses scaled scoring. Your raw score's converted to a standardized scale so different versions of the exam stay fair, and that means two people can take different question sets and still be evaluated consistently. It's not a trick, it's just how professional exam programs keep things stable over time.
No partial credit either, since it's multiple-choice. You either have the right answer or you don't. That's why "I kind of know malware persistence" isn't enough. You need to know it cleanly.
Score reporting and what happens if you fail (retake process)
When you finish the exam, you typically get an immediate preliminary pass/fail on screen. The official score report usually shows up by email within 24 to 48 hours.
That report's more useful than people think. You get your overall percentage score, plus a breakdown by domain area, so you can see strengths and weaknesses mapped directly to the GCIH exam objectives. If you fail, that domain analysis's basically your study plan for round two. If you pass but barely, it still tells you what to shore up for real-world work, because a close-call pass often means you've got blind spots that'll show up on the job.
Retakes're straightforward. If you score under 71%, you can purchase another attempt, and there's no mandatory waiting period before scheduling the second attempt. There's also no limit on retake attempts, which is nice in theory, but each attempt costs money, so you don't wanna treat it like unlimited retries on a practice app.
Also, your materials don't expire just because you failed. Your index, your tabs, your notes, your workflow. All reusable. Usually you just tighten it up, add the pages you kept searching for, and fix the domains where you bled points.
Performance expectations and "good" scores
71% gets you certified. That's all GIAC requires.
Employers usually care that you passed, not whether you got an 82% or a 91%, but competitive roles sometimes ask, especially if the hiring manager's also GIAC-heavy and wants to gauge depth. Not gonna lie, candidates often set their own target higher anyway. 80%+ is a common personal benchmark because it signals you weren't scraping by.
GIAC doesn't publish official average scores, but anecdotal ranges're pretty steady: many successful candidates land around 75% to 85%, and 71% to 74%'s the "close call" zone. Above 90%'s rarer and usually reflects either strong prior IR experience, very sharp indexing, or both.
One more opinionated point. Don't plan to "carry" weak domains with strong ones. Aim for 75%+ in all domains. If you bomb a domain like host-based analysis or containment and recovery, your overall score can still crater, and worse, that weakness shows up in real incidents.
How difficult is the GCIH exam?
People also ask, "Is GCIH harder than Security+ / CySA+?" and the honest answer's it depends on your background. If you live in incident response already, GCIH feels like organized vocabulary plus some targeted technical detail. If you're coming from general security knowledge with limited hands-on work, it can feel harder than CySA+ because it expects you to recognize attacks and response steps, not just define them.
Time management's the silent killer. Open-book tempts you to look everything up. That's a trap. The winning approach's knowing most answers cold, then using your index for the 20% that's detail-heavy.
Practice tests help a lot here, including extra sets like the GCIH Practice Exam Questions Pack if you want more repetition for recall and speed. Still, the best prep's a good index plus real reps with logs, packets, and endpoint artifacts.
GCIH prerequisites and recommended experience
GIAC doesn't really gate you with formal prerequisites, but the practical expectations're there. You should be comfortable with TCP/IP basics, common ports, Windows and Linux fundamentals, and reading logs without getting lost. Basic scripting helps, even if it's just enough to parse text and spot patterns.
Security+ knowledge's a baseline. CySA+ style thinking helps. Basic pentest concepts also help because you understand what attackers try first.
GCIH renewal (recertification) requirements
People ask, "How do I renew my GCIH certification?" and the short version's GIAC recertification CPEs're the path. You renew on a cycle, you submit continuing education credits, and you pay the renewal fee. The details can change, so always confirm the current numbers on GIAC, but the approach's stable: keep learning, document it, submit it on time.
Quick FAQs
What is the passing score for GCIH?
71%, which typically means at least 75 correct answers out of 106.
What are the GCIH exam objectives and domains?
Eight domains, and your score report shows domain-by-domain percentages so you can see gaps clearly.
How much does the GCIH exam cost?
Standalone exam attempts're commonly $949, and retakes're $649.
Can practice questions help?
Yes, if you treat them as timing and recall training, not as a replacement for understanding. I mean, if you want extra reps beyond official practice tests, something like the GCIH Practice Exam Questions Pack's one option at $36.99, but your index and hands-on practice still decide the outcome.
GCIH Prerequisites and Recommended Background
Official prerequisites, or lack thereof
Here's the thing about GCIH prerequisites: GIAC doesn't actually mandate any. You could register for the exam tomorrow with zero security experience and they'll take your money. I mean, they won't stop you. That's very different from saying you should do that, but technically there's no gatekeeper preventing anyone from attempting the GIAC Certified Incident Handler exam regardless of educational background or prior certifications.
This open-door policy? It's both liberating and potentially expensive if you're not ready. GIAC wants professionals to challenge themselves, but jumping into GCIH without appropriate background is like trying to run a marathon when you've never jogged. Possible? Sure. Smart? Probably not.
What experience actually helps
GIAC suggests (and I'd emphasize suggests strongly) that candidates bring 2-3 years of hands-on information security experience before tackling GCIH. We're talking real-world exposure to security monitoring, log analysis, or incident response activities. Maybe you've been a SOC analyst triaging alerts at 2 AM. Perhaps you've helped senior responders contain malware outbreaks when everything's hitting the fan and management's breathing down your neck for answers. That kind of practical context makes the exam content click instead of feeling like you're memorizing alien hieroglyphics.
The certification validates incident handling skills. Having actually handled incidents? Gives you mental hooks to hang concepts on. When the exam asks about containment strategies, you'll remember that time you isolated infected endpoints instead of just reciting textbook procedures.
Foundational knowledge you need
Before you even think about GCIH, you should possess solid understanding of TCP/IP networking fundamentals. I'm talking about knowing how packets actually flow through networks. Understanding the three-way handshake without Googling it. Recognizing common internet protocols like HTTP, DNS, SMTP, FTP. This isn't trivia. Incident handlers analyze network traffic constantly to spot malicious communication patterns.
You also need basic Windows and Linux system administration skills. Not expert-level, but intermediate proficiency where you're not panicking when presented with PowerShell commands or bash scripts. Understanding how these operating systems log events, manage processes, handle services.. that's all critical because attacks happen on real systems with real configurations. Comfortable working through both environments matters more than you'd think.
Networking fundamentals that matter
Strong grasp of the OSI model and TCP/IP stack? Essential for understanding network-based attack detection, which forms a substantial chunk of GCIH content. You should know common ports without constantly referencing cheat sheets. Port 443? HTTPS. Port 53? DNS. Port 3389? RDP. When you're analyzing potential compromises, recognizing unusual port usage happens instinctively if you've internalized this stuff.
Packet analysis basics using tools like Wireshark should feel familiar, not foreign. You don't need to be a Wireshark wizard, but understanding how to follow TCP streams, filter traffic, spot anomalies in packet captures.. these skills translate directly to exam scenarios and real incident response work.
Operating system comfort level
Windows proficiency means working through command prompt and PowerShell without fear. Understanding registry basics, knowing where event logs live and how to interpret them, managing services and scheduled tasks. A surprising number of attacks abuse built-in Windows functionality, so defenders need to understand the space attackers exploit.
Linux skills should include comfortable bash usage, understanding file system hierarchy, process management fundamentals. Knowing where different log files typically reside (/var/log becomes your friend). Many security tools run on Linux. Servers too. You can't effectively respond to incidents if half the infrastructure intimidates you. Actually, funny story: I once watched a junior analyst spend twenty minutes trying to find logs on a Linux box because nobody had shown them /var/log existed. Don't be that person.
Log analysis is huge
If you've never spent time reading and interpreting various log formats, GCIH will hurt. Windows Event Logs with their event IDs and XML structures. Syslog messages with their varying formats depending on the source. Web server logs showing GET and POST requests. Firewall logs indicating allowed and denied connections. Proxy logs revealing user browsing patterns.
Familiarity with these log sources before studying? Makes the incident handling methodology make sense because you understand the evidence you're collecting and analyzing. I've seen candidates struggle because they'd never actually looked at real logs before attempting to learn how to investigate incidents using those logs. It's like trying to learn surgery from a textbook without ever seeing blood.
Security tool exposure helps
Basic hands-on experience with security tools accelerates your GCIH preparation significantly. Wireshark for packet analysis obviously. The Sysinternals Suite for Windows analysis (tools like Process Explorer, Autoruns, ProcMon). Understanding basic SIEM concepts even if you haven't administered one. Endpoint detection fundamentals and how agents collect telemetry.
You don't need years with each tool. Having touched them in lab environments or production contexts gives you practical reference points when studying detection and analysis techniques. The exam doesn't test specific vendor products, but understanding tool categories and capabilities is required.
Scripting awareness, not mastery
While GCIH doesn't require advanced programming skills, understanding basic PowerShell, Python, or bash scripting helps with automation concepts covered in incident response. Responders often automate repetitive tasks. Collecting artifacts from multiple systems, parsing log files, enriching indicators with threat intelligence. You won't write complex programs during the exam, but appreciating why automation matters and recognizing simple scripts assists comprehension.
Lab skills and virtualization
Ability to build and manage virtual environments for testing and analysis purposes using platforms like VMware, VirtualBox, or Hyper-V proves incredibly valuable. Much of effective GCIH preparation involves hands-on practice in safe environments where you can detonate malware samples, test detection techniques, analyze artifacts without risking production systems.
Candidates comfortable spinning up VMs, creating snapshots, networking virtual machines together can build realistic incident response labs that transform abstract concepts into tangible skills. This stuff matters.
Complementary certifications that build foundation
CompTIA Security+ provides excellent foundational security knowledge covering basic incident response concepts. Makes GCIH a natural next step for security professionals who've already earned it. Security+ establishes terminology, introduces security principles, touches on incident response lifecycle. All useful groundwork.
CompTIA CySA+ (Cybersecurity Analyst)? Even better preparation with coverage of security analytics and threat detection. There's overlap that eases GCIH preparation, though GCIH goes significantly deeper into response techniques and hands-on analysis.
If you're looking at the GIAC family, GSEC provides a broad security knowledge base that supports the more specialized GCIH incident handling focus. Some candidates pursue GSEC first to establish fundamentals before tackling GCIH's narrower but deeper scope.
CompTIA Network+ establishes the networking foundation needed for understanding network-based attacks and traffic analysis components. If your networking knowledge is shaky, consider Network+ or equivalent experience before GCIH.
Certified Ethical Hacker (CEH) from an offensive perspective helps defenders anticipate and detect attacks. CEH alone doesn't fully prepare for GCIH's defensive focus, though. Understanding attacker methodologies provides useful context but isn't sufficient preparation by itself.
Formal education versus experience
While not required, degrees in computer science, information technology, cybersecurity, or related fields provide theoretical foundation supporting practical GCIH concepts. But look, I've met brilliant self-taught professionals with strong hands-on experience and extensive home lab practice who succeeded without formal degrees. GCIH emphasizes practical skills over academic credentials, which levels the playing field for non-traditional backgrounds.
Some structured learning helps most candidates organize the vast amount of material GCIH covers. Whether that's formal education, online courses, or the SANS SEC504 training.
Who struggles and who thrives
Brand-new security professionals without prior SOC or IT experience will find GCIH extremely challenging. Not impossible with dedicated study and extensive lab practice, but you're fighting uphill without contextual experience. The exam assumes familiarity with concepts that take time to internalize through exposure.
Mid-career security professionals with 2-5 years experience in SOC analyst roles, incident handling, network administration, or IT support find GCIH appropriately challenging and immediately applicable to their work. This sweet spot means you've encountered enough real scenarios to appreciate the methodology while still having knowledge gaps GCIH fills.
Even experienced incident responders benefit from GCIH's structured methodology and full coverage, often filling knowledge gaps in specific technical areas they haven't encountered in their particular environment. Maybe you're strong on Windows but weak on Linux. Excellent at network analysis but unfamiliar with web application attack indicators. GCIH forces breadth across the incident handling domain.
The continuous learning requirement
Incident handling evolves rapidly. New attack techniques emerging constantly. GCIH preparation requires commitment to staying current through security blogs, threat intelligence sources, and professional development beyond just studying for the exam. This mindset matters because the exam tests understanding of concepts that adapt as the threat space changes, not just memorization of static facts.
Conclusion
Wrapping up: is GCIH the right move for you?
Real talk here. The GIAC Certified Incident Handler isn't some magical career shortcut that'll instantly rocket you into a six-figure SOC gig overnight. But honestly? It's legitimately one of maybe three or four certs that actually demonstrates you can do the work when everything's actively burning down around you and management's simultaneously breathing down your neck demanding answers yesterday.
The exam's expensive. Period.
I mean, between the GCIH exam cost and potentially dropping several thousand dollars on that SANS SEC504 training, you're staring down a serious financial investment that'll make your wallet cry. But here's the thing, and I've seen this play out maybe a dozen times now, most certifications out there just teach you theory, toss you a pretty certificate, then sorta hope you'll figure out the messy real-world stuff on the job through trial and error. GCIH? It forces you to actually know detection signatures cold, really understand attacker TTPs from multiple angles, work methodically through containment scenarios under pressure, and document your findings precisely like you're writing reports for actual stakeholders who'll make million-dollar decisions based on your words.
That hands-on angle? That's why hiring managers actually recognize the cert when they spot it on a resume.
The passing score sits around 71%, which sounds totally reasonable until you're maybe 90 minutes deep staring at some gnarly network pcap question wondering if that's legitimate lateral movement or just a chatty backup job that runs overnight. Time management absolutely kills people on this exam, even with the open-book format which theoretically should help. Your index needs to be rock solid, meticulously organized, because you really won't have time to frantically flip through 700+ pages of dense courseware hunting for that one specific Wireshark filter syntax you sort of remember seeing somewhere.
And yeah, GCIH renewal requirements mean you're committing to 36 CPEs every four years. Honestly? Actually not terrible compared to some other ridiculously demanding GIAC recertification cycles I've dealt with. Attend a conference, write a technical blog post, complete some training modules. You'll hit that number without too much suffering. I once knocked out like 20 CPEs just from attending a two-day vendor event that had decent technical sessions, plus they fed us surprisingly good barbecue, so there are worse ways to spend your professional development time.
If you're really serious about blue team incident response work and you've already got the prerequisite knowledge locked down (basic networking fundamentals, decent comfort level with both Windows and Linux environments, solid understanding of logs and telemetry data), this cert validates skills that legitimately matter in the field. Not just for entry-level SOC analyst incident handling roles either, but for moving up into IR team lead positions or security engineering spots where you're actually building detection logic and hunting architectures.
Before you schedule though?
Don't skip the prep work. The GCIH exam objectives cover an overwhelming ton of ground spanning multiple domains, and you absolutely need solid GCIH study materials plus serious dedicated hands-on time with real tools. Work through multiple GCIH practice tests to identify your weak domains early, because that 71% threshold honestly doesn't leave much room for guessing or hoping you'll remember something under pressure. If you want realistic exam-style questions that'll brutally expose gaps in your knowledge before test day, check out the GCIH Practice Exam Questions Pack at /giac-dumps/gcih/. Not gonna lie, practice questions that actually mirror the format and difficulty level saved me from completely bombing at least two domains I really thought I had down cold.
Bottom line: GCIH's worth it if incident handling certification legitimately fits with where you want your career trajectory to go and you're willing to put in the unglamorous grinding work.
Show less info
Hot Exams
Related Exams
GIAC Python Coder (GPYC)
GIAC Critical Controls Certification (GCCC)
GIACCertified Forensics Analyst
GIAC Security Essentials
GIAC Information Security Fundamentals
GIAC Security Leadership Certification (GSLC)
GIAC Systems and Network Auditor
GIAC Certified Enterprise Defender
GIAC Certified Project Manager Certification Practice Test
GCIA – GIAC Certified Intrusion Analyst Practice Test
GIAC Information Security Professional
GIAC Certified Incident Handler
GIAC Secure Software Programmer – Java
GIAC Certified Firewall Analyst
GIAC Penetration Tester
GIAC Advanced Smartphone Forensics
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.