GCFA Practice Exam - GIACCertified Forensics Analyst
Reliable Study Materials & Testing Engine for GCFA Exam Success!

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
GCFA: GIACCertified Forensics Analyst Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 318 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena GIAC GIACCertified Forensics Analyst (GCFA) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
GIAC GCFA Exam FAQs
Introduction of GIAC GCFA Exam!
The GIAC Certified Forensic Analyst (GCFA) certification is an advanced-level certification that verifies a professional’s knowledge, skills, and abilities to understand and apply advanced digital forensics techniques in a wide range of environments. It is designed to validate a professionals ability to analyze, examine, and investigate computer networks, computer systems, and digital evidence.
What is the Duration of GIAC GCFA Exam?
The GIAC Certified Forensics Analyst (GCFA) exam is a four-hour, multiple-choice exam consisting of 150 questions.
What are the Number of Questions Asked in GIAC GCFA Exam?
There are approximately 200 questions on the GIAC GCFA exam.
What is the Passing Score for GIAC GCFA Exam?
The passing score required to pass the GIAC GCFA exam is 74%.
What is the Competency Level required for GIAC GCFA Exam?
The GIAC GCFA exam requires a Mastery level of knowledge and experience to pass.
What is the Question Format of GIAC GCFA Exam?
The GIAC GCFA exam is a multiple-choice type of exam, with questions that are presented in both single- and multiple-response formats. The exam consists of 175 questions, which must be completed within a three-hour time limit.
How Can You Take GIAC GCFA Exam?
The GIAC GCFA exam can be taken online or at a testing center. To take the exam online, you must register online and follow the instructions to create a GIAC account, select the exam you wish to take, and pay the exam fee. Once your payment has been processed, you will receive an email with instructions on how to access your exam. To take the exam at a testing center, you must register online and select the exam you wish to take. You will then be given instructions on how to locate a testing center near you and schedule an appointment.
What Language GIAC GCFA Exam is Offered?
The GIAC GCFA exam is offered in English.
What is the Cost of GIAC GCFA Exam?
The GIAC GCFA exam is offered at a cost of $1,699 USD.
What is the Target Audience of GIAC GCFA Exam?
The GIAC GCFA Exam is designed for IT professionals who manage, monitor, and analyze computer networks. This includes system and network administrators, security analysts, and IT auditors.
What is the Average Salary of GIAC GCFA Certified in the Market?
The average salary for someone with a GIAC GCFA certification is around $95,000 per year.
Who are the Testing Providers of GIAC GCFA Exam?
GIAC offers the GCFA exam through its online testing platform, GIAC Secure Testing. Candidates can register for the exam through the GIAC website and will be required to pay an exam fee.
What is the Recommended Experience for GIAC GCFA Exam?
The recommended experience for the GIAC GCFA exam is at least three years of information security experience, including two years of experience in incident response, malware analysis, digital forensics, and/or log analysis. It is also recommended that candidates have an understanding of computer networks, operating systems, and system administration.
What are the Prerequisites of GIAC GCFA Exam?
The GIAC GCFA exam requires that you have at least five years of experience in information security and at least three years of experience in digital forensics. You must also have a bachelor's degree in a related field or equivalent experience.
What is the Expected Retirement Date of GIAC GCFA Exam?
The official website to check the expected retirement date of GIAC GCFA exam is https://www.giac.org/certification/gcfa/retirement-date.
What is the Difficulty Level of GIAC GCFA Exam?
The difficulty level of the GIAC GCFA exam is considered to be intermediate. It requires knowledge and experience in the field of computer forensics and incident response.
What is the Roadmap / Track of GIAC GCFA Exam?
The certification roadmap for GIAC GCFA Exam is as follows:
1. Become familiar with the GIAC GCFA Exam objectives.
2. Take the GIAC GCFA Exam Prep Course.
3. Take the GIAC GCFA Exam.
4. Pass the GIAC GCFA Exam.
5. Receive your GIAC GCFA Certification.
6. Maintain your GIAC GCFA Certification.
What are the Topics GIAC GCFA Exam Covers?
The GIAC GCFA exam covers the following topics:
1. System Forensics: This covers the use of digital forensics and investigation techniques to analyze, investigate, and report on computer systems and networks.
2. Network Forensics: This covers the use of digital forensics and investigation techniques to analyze, investigate, and report on network traffic and attacks.
3. Malware Analysis: This covers the use of malware analysis techniques to investigate malicious code, identify threats, and provide recommendations for remediation.
4. Data Analysis: This covers the use of data analysis techniques to identify patterns, trends, and anomalies in data.
5. Incident Response: This covers the use of incident response techniques to investigate, contain, and remediate security incidents.
6. Security Architecture: This covers the use of security architecture principles and techniques to design, implement, and maintain secure systems.
7. Legal and Ethical Issues: This covers the
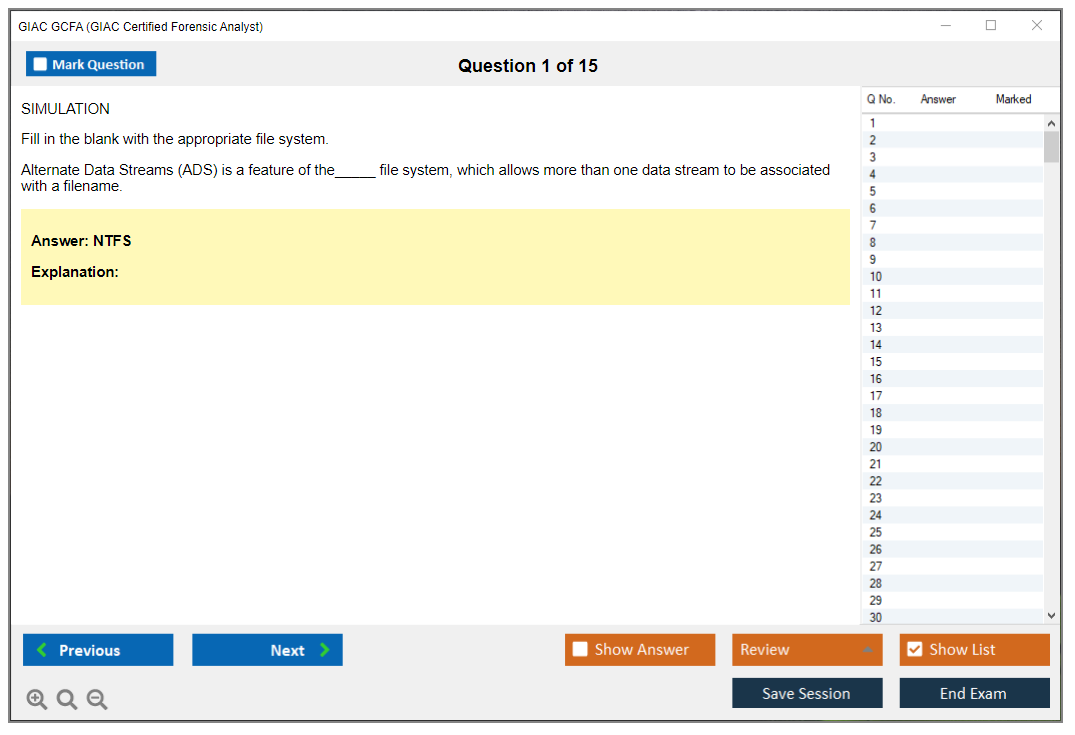
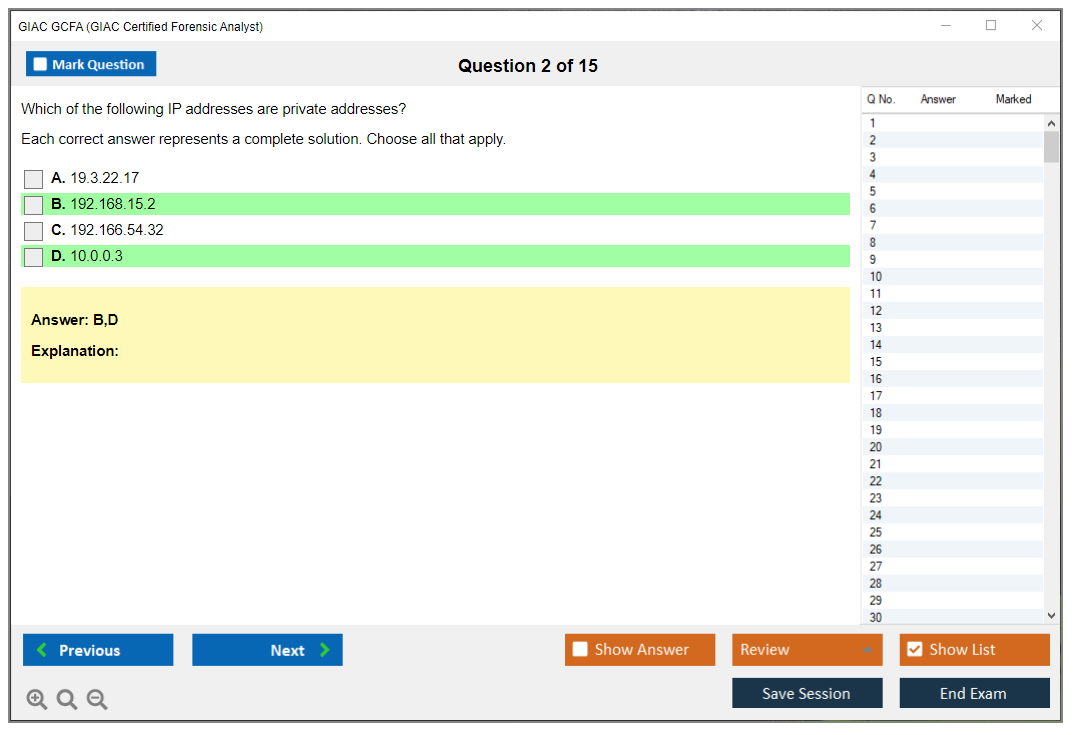
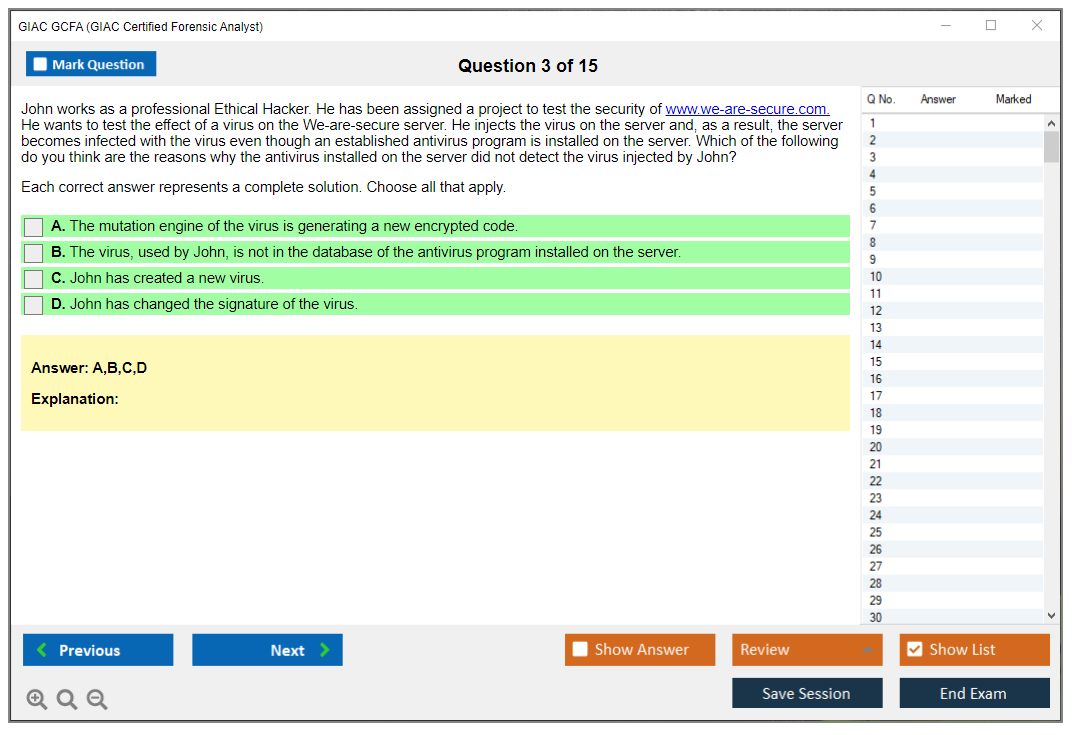
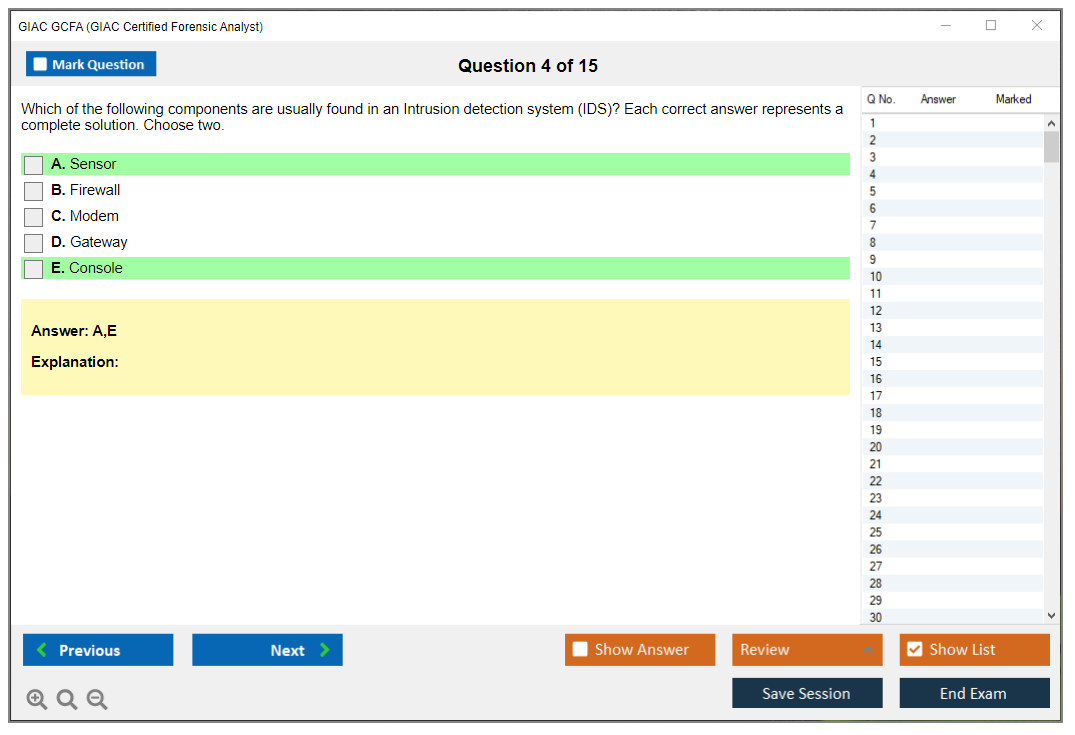
What are the Sample Questions of GIAC GCFA Exam?
1. How do you conduct a forensic analysis of a system using the EnCase forensic software suite?
2. What methods are used to authenticate digital evidence?
3. How do you use the Sleuth Kit to identify and recover deleted files?
4. What techniques can you use to identify malicious software on a system?
5. What are the steps involved in a live system forensics investigation?
6. How do you determine the source of an attack on a network?
7. How do you use the Volatility framework to analyze memory dumps?
8. What techniques can be used to detect and analyze network intrusions?
9. How do you use network traffic analysis to identify malicious activity?
10. What methods can be used to detect and analyze malware?
GIAC GCFA (GIACCertified Forensics Analyst) GIAC GCFA Certification Overview: What You Need to Know About the GIAC Certified Forensics Analyst The GCFA certification carries real weight in digital forensics and incident response circles. When someone mentions they're GCFA-certified, I know they can do way more than work through through a forensic tool's pretty interface. They've proven they can tear into Windows Registry hives at ungodly hours, piece together attacker timelines from fragmented artifacts, and defend their findings in court when lawyers start asking uncomfortable questions. What GCFA validates (forensics + incident response skills) The GCFA shows you've got the skills to investigate compromised systems methodically. We're talking analyzing Windows and Linux systems post-incident, examining memory dumps to uncover evidence of malware that never wrote anything to disk, and reconstructing attacker behavior by correlating filesystem metadata with event logs and browser... Read More
GIAC GCFA (GIACCertified Forensics Analyst)
GIAC GCFA Certification Overview: What You Need to Know About the GIAC Certified Forensics Analyst
The GCFA certification carries real weight in digital forensics and incident response circles. When someone mentions they're GCFA-certified, I know they can do way more than work through through a forensic tool's pretty interface. They've proven they can tear into Windows Registry hives at ungodly hours, piece together attacker timelines from fragmented artifacts, and defend their findings in court when lawyers start asking uncomfortable questions.
What GCFA validates (forensics + incident response skills)
The GCFA shows you've got the skills to investigate compromised systems methodically. We're talking analyzing Windows and Linux systems post-incident, examining memory dumps to uncover evidence of malware that never wrote anything to disk, and reconstructing attacker behavior by correlating filesystem metadata with event logs and browser history.
This isn't academic theory.
GCFA holders demonstrate competence in evidence acquisition using write-blockers, integrity verification through hash validation, maintaining proper chain of custody documentation, and producing reports that survive legal scrutiny. The certification addresses both dead-box forensics (analyzing powered-off systems) and live response techniques for grabbing volatile data before it vanishes into the digital void.
You'll validate skills in forensic artifact analysis across multiple sources. Windows Registry artifacts, event logs, $MFT records, prefetch files, ShimCache, AmCache, browser artifacts from Chrome and Firefox and Edge, email data from Outlook and Exchange, and memory forensics using tools like Volatility. It's thorough.
Who should pursue GCFA (roles and use cases)
This cert makes sense for incident responders needing to go beyond initial triage. SOC analysts transitioning into forensics roles. Law enforcement investigators handling computer crimes and consultants brought in after breaches. The thing is, it's vendor-neutral, which matters because you're not trapped in one tool ecosystem. The skills transfer whether you're using EnCase, FTK, X-Ways, Autopsy, or command-line tools.
Government agencies favor GCFA because it demonstrates understanding of legal and ethical considerations. Privacy expectations, warrant requirements, evidence admissibility standards. Corporate security teams value it because GCFA-certified analysts can identify data theft, insider threats, and advanced persistent threats through systematic examination rather than educated guessing.
I once worked with an analyst who could recite every SANS book from memory but froze when asked to explain their methodology in a deposition. Technical knowledge alone doesn't cut it.
Training pathway through SANS FOR508
The SANS FOR508 GCFA course represents the primary training route. Six days covering forensic methodologies, artifact locations across operating systems, analysis techniques, and timeline analysis and evidence handling. The course doesn't waste time. You're constructing timelines, analyzing real forensic images, and learning where artifacts actually reside in the filesystem and registry.
FOR508 teaches understanding of artifact generation mechanisms, not just button locations. Why does a particular registry key exist? What creates ShimCache entries? How does NTFS filesystem journaling actually work? When you understand the underlying mechanisms, you can validate tool outputs instead of blindly accepting them. That becomes key when you're explaining findings to executives or providing testimony.
The course addresses anti-forensics techniques too. Timestomping, log deletion, encryption, artifact wiping. You need to recognize when adversaries attempt covering their tracks and work around their counter-forensics efforts.
Exam format and what to expect
The GCFA exam tests practical knowledge through scenario-based questions you'll encounter in real investigations where multiple artifacts need correlation to establish what actually happened during an incident. You've got 115 questions and four hours to complete them. You can bring your course books and notes (it's open book).
Don't assume that makes it simple.
The GCFA exam difficulty stems from the depth of knowledge required and the time pressure of correlating multiple artifact sources to answer tricky scenarios. The GCFA passing score sits at 73%, which sounds manageable until you're 90 minutes deep and realizing you need to cross-reference three different index sections to answer one question. Many candidates find timeline questions particularly challenging because you're correlating NTFS timestamps with registry modification times and event log entries to determine event sequences.
Cost considerations and budget planning
Let's address money. The GCFA exam cost runs around $949 for the certification attempt itself. SANS FOR508 training varies depending on format (live online, in-person, or OnDemand) but expect $8,195 to $9,000+ for the full course with books and practice tests. That's serious investment, though many employers cover training costs for security team members.
Retake fees match initial exam cost if you don't pass first attempt.
I've seen people fail because they didn't build a proper index or didn't practice enough with the practice tests under timed conditions. Budget time for index creation. A well-organized index makes the difference between passing comfortably and running out of time on question 80.
Study approach and preparation timeline
Most people need 40-80 hours of study beyond the six-day course, which includes reviewing courseware, building and refining your exam index, working through practice datasets, and taking practice tests multiple times. The GCFA study materials from SANS include books, hands-on labs, and practice exams mirroring actual exam difficulty.
Your index should be artifact-focused. Where do you find evidence of program execution? What registry keys indicate USB device usage? Which event IDs matter for logon analysis? Organize by artifact type and investigation scenario, not just by book page numbers. This makes searching faster under pressure.
Practice tests reveal knowledge gaps. Review every wrong answer, find that topic in your books, re-index it better, then retest. This cycle represents how you actually prepare for the scenarios the exam throws at you.
Career value and certification renewal
The GCFA renewal requirements follow GIAC's standard four-year cycle. You'll need 36 CPE credits and pay renewal fees to maintain active status. Eligible activities include attending security conferences, taking additional training, publishing research, or teaching. It's not difficult if you're actually working in the field, but you need to document everything for potential audits.
Career-wise? GCFA opens doors. It's recognized alongside GCIH for incident response roles and complements GCIA for analysts needing both network and host forensics skills. The combination of incident response and forensics knowledge makes you valuable for breach investigations, threat hunting, and security operations leadership roles.
The certification proves you can execute the work, not just discuss it. That matters when you're the person management calls at midnight because someone just discovered ransomware on the file server.
Who Should Pursue GIAC GCFA Certification: Roles and Career Applications
GIAC GCFA certification overview (GIAC Certified Forensics Analyst)
The GIAC GCFA certification is a digital forensics certification that sits right at the intersection of incident response and host forensics. Real work, honestly.
It's for people who already deal with security incidents and want the "prove it with artifacts" skillset: forensic artifact analysis, timeline analysis and evidence handling, and the kind of investigative thinking that holds up when leadership, legal, or regulators start asking uncomfortable questions. Receipts matter here.
Look, if your job's mostly "see alert, close alert", GCFA's the push into "what happened on this endpoint, when, how, and what'd it touch". That's why it clicks for incident responders, forensic analysts, SOC analysts, and cybersecurity investigators who need advanced artifact analysis skills, not just tool familiarity.
Incident response team members get quick value because GCFA adds the forensic depth needed to investigate security incidents, determine root causes, assess impact, and give remediation recommendations that aren't based purely on gut feeling. Being able to say "persistence was via X, credential access likely happened here, lateral movement started at this minute" changes the whole conversation when executives are panicking and Legal's breathing down your neck about breach notification timelines.
Digital forensics examiners also fit. Law enforcement, government agencies, corporate investigation teams, internal investigations, criminal cases, e-discovery. Different context, same muscle: collect evidence correctly, interpret artifacts sanely, and explain it like you might have to defend it later.
What GCFA validates (forensics plus incident response skills)
GCFA's basically proof you can work a compromised host like an investigator, not a tourist.
You're expected to understand Windows internals, logs, common persistence and execution traces, and how attackers try to mess with your visibility. Plus you've gotta build timelines that don't fall apart when someone challenges a timestamp source. Context matters more than memorization here. You need to think through what artifacts actually mean in different attack scenarios, not just regurgitate definitions.
SOC analysts chasing career growth love it for a reason. SOC work can turn into a ticket factory. That's fine early on. But GCFA's one of the cleaner ways to move from alert monitoring into deep investigations where you're examining artifacts, validating IOCs, and building a narrative that can drive containment decisions.
Threat intel analysts benefit too, because artifact-focused work helps reverse-engineer attacker techniques from real evidence, not just a blog post, and then turn that into detection rules that match what endpoints actually leave behind. Malware analysts also pair well with it since reverse engineering tells you what the code can do, while host forensics tells you what it did do: deployment, persistence, lateral movement traces, and exfil evidence.
Pen testers and red teamers are an underrated audience here. Knowing defensive forensic capabilities improves your operational security, forces you to think about what artifacts you generate, and helps you emulate adversary anti-forensics techniques more realistically. Not for "how do I hide crimes" stuff, obviously. For understanding what blue teams can truly prove.
There's this weird moment in red team exercises where you realize the defenders can see way more than you thought they could. That's where things get interesting. You start thinking about timing, about which tools leave the ugliest traces, about whether RDP really needs to be your go-to pivot method when WMI exists. It's a whole different mindset shift.
Who should pursue GCFA (roles and use cases)
Cybersecurity consultants pick up GCFA because clients want incident response engagements and breach assessments delivered with confidence, and "we think" doesn't cut it when money and reputation are on the line.
MSSP analysts also benefit. You're supporting multiple clients with very different environments, and GCFA skills translate into compromise assessments and forensic investigation support without needing a full bespoke playbook every time.
InfoSec managers and directors sometimes get GCFA too, and that surprises people, but managing forensics without understanding forensics is painful. You can't scope an investigation well. Can't sanity-check vendor claims. Can't set expectations about evidence limits, retention gaps, and what "we can't tell" really means in practice when the CEO's demanding absolute certainty about whether customer data was accessed.
Compliance and audit professionals use these skills for investigating policy violations, insider threat cases, and validating control effectiveness through artifact examination. Legal folks like e-discovery specialists, litigation support analysts, and cyber attorneys get value from understanding methodologies and evidence handling, because it helps them ask better questions and avoid pushing teams into sloppy evidence mistakes.
System admins and IT pros trying to specialize in security also use GCFA as a pathway. You already know endpoints, AD, and "what normal looks like", so learning to extract and interpret artifacts is a natural next step. Career changers from IT, networking, or systems backgrounds can also point to GCFA as a specialization credential that signals commitment to security investigation work, especially when paired with something broader like GSEC (GIAC Security Essentials) or GISF.
Military and defense personnel? Absolutely. Academic educators teaching forensics courses. Enterprise security architects designing forensic readiness and logging architectures. All valid use cases.
And yes, organizations hiring forensic analysts and incident responders frequently list GCFA as preferred or required, especially in regulated industries like finance, healthcare, and critical infrastructure where incident investigation capability isn't optional.
GCFA exam details
People always ask about the mechanics.
The exam's proctored, timed, and open book. The question style rewards people who can find details fast and apply them under pressure, not people who memorized a glossary.
The GCFA passing score is set by GIAC and published on the exam page, and it can change, so check the current number before you schedule. Same with the GCFA exam objectives: treat them like your checklist for indexing and lab practice, because they hint at what artifacts and workflows you'll be expected to recognize quickly.
GCFA cost: exam fees and training pricing
GCFA exam cost isn't cheap. That's the truth.
Buying the GIAC attempt typically includes a practice test or two depending on how you purchase, and adding SANS FOR508 GCFA training is a bigger budget conversation for you or your employer, because you're paying for courseware and labs that are actually relevant to the test and the job.
Retakes hurt financially. Plan for them anyway. Not because you will fail, but because budgeting like an adult beats scrambling later when you're stressed about a deadline.
GCFA difficulty: how hard is the GCFA exam?
GCFA exam difficulty is "high, but fair".
It's challenging because the depth's real, artifact interpretation's easy to mess up when you're rushing, and time management becomes a skill on its own when you're flipping through notes, validating a detail, and trying not to second-guess yourself for 20 minutes on one question.
Common failure reasons are boring: weak index, not enough hands-on timeline building, and treating practice tests like a score chase instead of a diagnostic tool. You've gotta actually build timelines yourself, not just read about them, because exam questions will throw curveballs that test whether you understand artifact context or just memorized which registry key means what.
GCFA prerequisites and recommended background
Official GCFA prerequisites are basically "none", but practical prerequisites exist.
You want comfort with Windows artifacts, event logs, basic memory concepts, and how investigations flow from triage to containment to reporting. If you're coming from IR, GCIH is a common stepping stone. If you're more network focused, GCIA can help round you out.
Best GCFA study materials and practice tests
Your best GCFA study materials are the FOR508 courseware if you took it, plus your own index and your own lab notes.
Build an index you can actually use under stress. Tabs everywhere. Keywords. Page numbers. Artifact names. Tool output patterns. Make it ugly. Make it fast.
GCFA practice tests are where you learn pacing and find gaps. Review misses, update the index, redo the weak labs, then retest. That loop's the whole game.
GCFA renewal requirements
GCFA renewal requirements follow the GIAC renewal cycle with a maintenance fee and continuing education credits.
Keep documentation as you go. Save course certificates, conference attendance, internal training records, and write-ups. Audit-proofing later's annoying.
GCFA FAQ (People Also Ask)
How much does the GIAC GCFA exam cost? Check GIAC's current pricing, because it changes, and budget separately for FOR508 if you want the full lab experience.
What is the passing score for the GCFA exam? GIAC publishes the current GCFA passing score on the certification page for GCFA (GIACCertified Forensics Analyst).
Is the GCFA certification hard to pass? Yes, if you don't practice artifacts and timelines. Manageable if you do.
What's the best way to study for GCFA (FOR508)? Take FOR508 if possible, build a ruthless index, and use practice tests to drive lab rework.
How do I renew my GCFA certification and maintain CPEs? Track CPE activities continuously and pay the renewal fee on schedule, because scrambling at the end's how people lose certs they worked hard for.
GCFA Exam Format, Structure, and Logistics
Walking into the GCFA exam room (virtual or physical)
Look, the GCFA exam objectives aren't messing around. You're getting tested on forensic fundamentals, Windows forensics, Linux forensics, browser and email forensics, memory forensics, timeline analysis, and incident response integration. That's a lot of ground to cover. Each domain could be its own certification if GIAC wanted to split things up, honestly.
The examination itself throws 115 multiple-choice questions at you with a 3-hour time limit. Simple math? That's roughly 1.5 minutes per question, which sounds generous until you realize these aren't "What does NTFS stand for?" type questions. They're scenario-based and practical, often presenting forensic situations where you need to identify correct artifacts, interpret findings, or select appropriate analysis approaches based on what an investigator actually encountered.
I mean, you might see a question showing you a chunk of registry data and asking what user activity it indicates. Or presenting a timeline gap and asking you to identify which artifact could fill it. Not gonna lie, some questions'll have you flipping through your index faster than you thought possible. One candidate I know spent twenty minutes on a single question about MFT timestamps before realizing he was overthinking it. That kind of time sink can wreck your whole exam if you're not careful.
The open-book advantage (and why organization matters)
Here's what makes GCFA different from most certs: it's open-book. You can bring physical reference materials including course books, printed notes, and personally created indexes to assist during the examination. This isn't a memorization test, it's a "can you find and apply the right information quickly" test. Honestly reflects real forensic work better than pure recall ever could.
But before you think this makes things easy, consider that poorly organized materials become a liability when you're burning through 90 seconds per question. The people who pass with flying colors usually spent hours building detailed indexes that map topics to page numbers. Creating quick-reference sheets for Registry keys and event IDs. Tabbing their books like they're preparing for trial testimony.
Proctored delivery options? Both online proctoring through ProctorU and in-person testing at Pearson VUE testing centers worldwide. The online option gives you flexibility if you're nowhere near a testing center or just prefer your home setup, though it comes with its own headaches. You need a webcam, microphone, reliable internet connection, and private testing environment with strict proctoring rules including workspace inspections that feel invasive but are necessary to maintain exam integrity.
What the proctor actually checks
Candidates must present government-issued photo identification matching their GIAC account registration information before beginning. Make sure your name matches exactly. Middle initials matter, hyphenated last names matter, all of it. I've heard stories of people getting turned away over name mismatches that seemed trivial but violated the rules.
No electronic devices allowed. No mobile phones, smartwatches, or electronic reference materials are permitted regardless of delivery method. Your carefully organized OneNote? Can't use it. That searchable PDF of the courseware? Nope. Everything needs to be printed, which means significant prep time and potentially a small forest worth of paper if you're printing all six FOR508 books.
The exam uses computer-based testing format with on-screen questions and radio-button answer selection. You can mark questions for review and work through freely during testing time. This is actually helpful because you can skip the absolute brain-melters and come back when you've built momentum on easier questions.
The waiting game and score breakdown
GIAC exams don't provide immediate pass/fail notification upon completion. Honestly torture after three hours of intense concentration. Results typically arrive within 24-48 hours via email and your GIAC account portal. Some people get theirs in 12 hours, others wait the full 48, and there's no pattern I've ever figured out. The thing is, it feels random every single time based on what people report in study groups and forums.
The examination covers six major domains with weighted distribution that tells you where to focus study time. Forensic Fundamentals gets 15%, Windows Forensics dominates at 30%, Linux Forensics is 10%, Browser and Email Forensics takes 15%, Memory Forensics gets 15%, and Timeline Analysis rounds out the last 15%. That Windows weight should tell you something. If you're weak on NTFS forensics, registry analysis, or event log interpretation, you're in trouble.
Questions test both factual knowledge and applied skills. Artifact locations, file formats, and tool capabilities. But also interpreting artifacts, selecting analysis approaches, and identifying evidence of specific activities. You might need to know where Chrome stores cookies AND what a specific cookie value indicates about user behavior.
Scenario questions that mirror real investigations
Scenario-based questions may present artifact excerpts, log entries, registry values, or filesystem metadata requiring you to interpret meaning, identify timestamps, or determine attacker actions. These are the questions that separate people who memorized facts from people who've actually done forensics work or extensively practiced with the lab materials.
The exam includes questions about forensic tool capabilities and limitations too. It's not enough to know that Volatility can extract process lists. You need to understand when specific plugins are appropriate, what validation steps are necessary, and how to interpret the output in context of an investigation.
Time management becomes critical because even with the open-book format, you can't afford to spend five minutes hunting through unindexed materials for every question. You can use scratch paper, either provided at testing centers or blank paper verified by online proctors, for calculations, timeline construction, or note-taking. I've found this helpful for complex timeline questions where visualizing the sequence of events makes the answer obvious.
What the questions actually test
Questions may reference specific Windows Registry keys, event log IDs, filesystem metadata fields, or artifact locations requiring quick reference lookup capabilities. This is where a good index becomes your best friend. If you can flip directly to the page explaining UserAssist or jump straight to the event ID reference chart, you save precious minutes.
The examination tests understanding of forensic principles. Locard's Exchange Principle, evidence preservation requirements, and chain of custody documentation. But it's theory. They'll give you scenarios where you need to identify what went wrong in an investigation or what steps were missed.
Mixed feelings here. GCFA exam questions address anti-forensics awareness. Recognizing timestomping, detecting log deletion, identifying encrypted containers, and working with incomplete evidence. Because real attackers don't leave pristine forensic trails, and investigators need to recognize when artifacts have been manipulated.
Memory forensics questions require knowledge of Volatility framework plugins. Process analysis techniques. Network connection identification. Malware detection in memory dumps. Timeline analysis questions test your ability to correlate multiple artifact sources, identify timeline gaps, recognize suspicious temporal patterns, and construct defensible chronologies that would hold up under scrutiny.
Browser forensics covers Chrome, Firefox, Edge, and Safari artifact locations. Database structures. Interpretation of history, cache, and session data. Email forensics addresses PST/OST file analysis, Exchange artifacts, webmail examination, and email header interpretation. Linux forensics tests ext4 structures, log file locations, shell history analysis, and user activity artifacts.
If you're coming from GCIH background, you'll find GCFA digs deeper into the artifacts themselves rather than the response process. Compared to GCIA, GCFA focuses more on host-based evidence than network traffic, though there's overlap in timeline correlation skills.
GCFA Exam Cost: Pricing, Fees, and Budget Planning for 2026
GIAC GCFA certification overview (GIAC Certified Forensics Analyst)
GIAC GCFA certification? It's one of those digital forensics credentials that actually carries weight in incident response circles. This isn't some "watch videos, click next" deal. We're talking artifact work--evidence handling, timeline analysis, the stuff that forces you to slow down and really think through what happened on a compromised system.
What GCFA validates is forensic artifact analysis across Windows environments, plus the practical workflow of reconstructing incidents: what happened, when it occurred, and how confident you can be in your conclusions. Who should chase it? IR analysts constantly pulled into host triage situations, DFIR folks wanting a credential mapping to real investigations, SOC people trying to move into deeper endpoint work. Consultants too. Hiring managers notice it.
I almost went for CHFI first, actually, back when I was trying to figure out which forensics cert would land best. Wasted about three weeks on that rabbit hole before realizing GCFA mapped way better to the work I was already doing. Sometimes the brand-name path isn't the obvious one.
GCFA exam details
Classic GIAC format. Proctored, multiple choice, open book--but don't misread that as easy because "open book" mostly means your index better not stink or you're screwed. Time pressure's real. You'll be flipping between notes, SANS books, your own cheat sheets while trying not to second-guess every artifact call you make.
GIAC publishes the required threshold for your specific attempt when you register, so GCFA passing score varies by exam version. The thing is, treat practice test results as your reality check, not Reddit threads full of rumors. If your practice scores hover near the line, budget like you might need more prep time.
GCFA exam objectives focus on Windows forensics, common persistence methods, log interpretation, artifact analysis, memory traces, execution evidence, and building reliable timelines that'd hold up under scrutiny. You'll see questions that feel like "which artifact proves X" rather than "define X." That's why the SANS FOR508 GCFA angle matters so much.
GCFA cost: exam fees and training pricing
Money talk. Real numbers.
The standalone GCFA exam cost, when you buy an attempt separately from training, is $979 USD as of 2026. That's GIAC's standard certification exam pricing--one attempt, a defined eligibility window, and a score report if you fail. Not cheap, not outrageous, just very "GIAC."
Now the other path? Training. SANS FOR508 course registration includes one GCFA exam attempt in the price. OnDemand pricing typically runs around $8,499 USD, while live training is often $8,500 to $9,000 USD depending on format and event. Live online, in-person conferences, community events all run FOR508 with that included exam attempt, and community SANS events can be the sneaky-good value because tuition's sometimes reduced.
One detail people miss: the included exam attempt has a clock. You must activate it within four months of course completion, then you must use it within four months of activation. Eight months max from finishing the course. That sounds generous until work gets busy, your kid gets sick, or you're stuck on a case and your study plan just evaporates.
Retakes hurt. Retake fees cost the full $979 USD per additional attempt--no discount, no mercy. So budget planning should include potential retake costs, because GCFA exam difficulty is legit and time pressure makes even prepared people make dumb mistakes. Candidates who fail do get a detailed score report showing weak domains, which helps, but you're still paying full price to come back.
Practice tests are part of the cost story too. Official GCFA practice tests cost $119 USD each and include 115 questions in exam-identical format. They're not optional if you're self-funding and you care about not paying $979 twice. Also, if you want extra drilling outside GIAC's ecosystem, you'll see products like the GCFA Practice Exam Questions Pack for $36.99 mentioned around the web. Use stuff like the GCFA Practice Exam Questions Pack carefully, focus on learning the why behind answers, and don't let it replace real labs.
GCFA difficulty: how hard is the GCFA exam?
People find GCFA hard for boring reasons. Depth. Lots of artifacts. Lots of "close" answers where three options seem plausible. And the exam rewards fast lookup, which means your index and tabbing strategy matter as much as your raw knowledge--you can know the topic and still lose minutes hunting for the exact page that explains the exception case you're being tested on.
Prepared looks like this: you can explain Windows execution artifacts without hand-waving, you can build and validate timelines, and you can read the question and immediately know which reference will answer it. Common failure reasons? Weak indexing, not enough hands-on with datasets, treating the course books like a novel instead of a searchable tool. Also, people underestimate fatigue. Four hours of decision-making is a grind that'll break your concentration if you're not ready for it.
GCFA prerequisites and recommended background
Official prerequisites? Basically "none."
Practical GCFA prerequisites are real though. You want comfort with Windows internals, event logs, file system artifacts, memory concepts, and investigative reasoning that doesn't crumble under pressure. Prior certs like GCIH or GCIA can help, but they don't replace host forensics reps. Nothing does.
Best GCFA study materials and practice tests
FOR508 courseware plus labs is the core foundation. Beyond that, GCFA study materials often include reference books, tool licenses, and practice datasets, and those costs add up fast. Some folks buy extra forensic tools or commercial parsers, others stick to built-in Windows artifacts plus community tools and get by fine.
The biggest "material" is your exam index--build it while you study, not the week before. Make it keyword-driven, include artifact names, error conditions, page references, and test it during practice exams. Speaking of which, use GCFA practice tests like a loop: take one timed, review every miss, fix your index, redo weak sections, then retest. If you also grab something like the GCFA Practice Exam Questions Pack, treat it as extra reps, not truth--just another data point in your prep strategy.
Budget planning and total cost reality check
Travel is the silent killer for in-person events--flights, hotel, food, and lost work time can add $1,000 to $3,000 depending on location and duration. OnDemand can save that while keeping access to the full FOR508 labs and the included exam attempt, which makes sense for most people.
If you're paying yourself, plan for the ugly scenario: standalone path means $979 exam, $119 practice test, maybe one retake at $979, plus the four-year renewal fee of $469 USD (about $117/year). That puts "ownership" over four years near $2,500 to $3,000 once you toss in a little extra for books or datasets. If you go FOR508 route, you're more like $9,000 to $10,000 once you include a practice test and that first renewal cycle.
Discounts exist sometimes. Organizations buying multiple seats may get volume discounts or team training rates, and government or military pricing can reduce per-student cost. Government employees, military personnel, and veterans may qualify through SANS Workforce Academy or government programs that offset some costs. Student pricing usually isn't a thing here since GIAC targets working pros.
Reimbursement policies vary wildly. Some employers only reimburse after you pass, which means you might float the cost upfront. Financing options through training providers or third-party education financing companies can spread payments out, if that's your only way to make it work. Vouchers can help too: GIAC exam vouchers sometimes show up during SANS conferences or special promos, and it's worth watching those if you're timing your attempt right.
GCFA renewal requirements
GCFA renewal requirements are simple to price and annoying to track over time. Renewal is every four years, the maintenance fee is $469, and you'll need CPEs from eligible activities like training, conferences, teaching, or certain work outputs that qualify. Keep documentation as you go--don't do the "scramble at month 47" thing.
GCFA FAQ (People Also Ask)
How much does the GIAC GCFA exam cost? $979 USD for a standalone attempt in 2026.
What is the passing score for the GCFA exam? GIAC sets it per version and shows it in your registration details, so check your exact attempt.
Is the GCFA certification hard to pass? Yes, mostly because of artifact depth and time management, not trick questions trying to confuse you.
What's the best way to study for GCFA (FOR508)? Do the labs, build a ruthless index, and take at least one practice test.
How do I renew my GCFA certification and maintain CPEs? Renew every four years, pay $469, and track CPEs with audit-ready proof documentation.
GCFA Passing Score and Scoring Methodology
Understanding the GCFA passing score threshold
The GIAC GCFA certification requires achieving 71% or higher on the 115-question examination. That translates to correctly answering approximately 82 or more questions. Simple math, right? But that 71% threshold carries way more weight than it might seem at first glance.
GIAC uses criterion-referenced scoring. What does that actually mean? Your performance gets measured against established competency standards rather than how other test-takers did. You're not competing with anyone else in the testing center or online proctoring session. The person sitting next to you could ace it with 95% or bomb it with 50%, and neither outcome affects your score one bit. This approach keeps the certification value consistent over time regardless of how many candidates attempt or pass the examination.
That 71% threshold makes sure certified individuals demonstrate sufficient knowledge and skills to perform forensic analysis tasks at a professional level. It's not arbitrary. GIAC designed it to accommodate the open-book format while still making sure candidates possess sufficient knowledge to locate and apply information effectively under time pressure. You can bring your entire indexed book set, but you still need to know where things are and how to apply them fast enough to finish 115 questions in four hours.
My cousin tried the exam last year with three full binders and a color-coded index system that would make a librarian weep with joy, but he still ran out of time on question 98 because he spent too long hunting for one obscure registry key reference. Sometimes having more material just means more places to get lost.
How the GCFA scoring methodology actually works
Each question carries equal weight regardless of difficulty, complexity, or domain. That Windows artifact question? Worth the same points as a basic timeline sequencing question. Makes every question equally important to the final score, which feels a bit weird when you're staring at a super technical memory forensics question versus something more straightforward.
Unanswered questions are scored as incorrect.
Period.
This makes it smart to answer every question even when uncertain rather than leaving items blank. No penalty exists for incorrect answers, encouraging educated guessing when time constraints or knowledge gaps prevent confident answer selection. I mean, if you're stuck between two answers with thirty seconds left before time runs out, pick one. Leaving it blank guarantees zero points while guessing gives you at least a shot.
GIAC doesn't disclose which specific questions were answered correctly or incorrectly. You'll get domain-level performance feedback in score reports, but never question-by-question breakdowns. This maintains exam security and question bank integrity, which makes sense from GIAC's perspective but can be frustrating when you're trying to figure out exactly what went wrong.
What your GCFA score report actually tells you
Score reports break down performance by exam domain, showing percentage correct in each area to identify strengths and weaknesses for failed attempts. Domain-level scoring helps candidates focus retake preparation on specific weak areas rather than reviewing all material equally. If you crushed Windows Forensics at 85% but tanked Timeline Analysis at 58%, you know exactly where to concentrate your study efforts.
The passing threshold has remained consistent at 71% for GCFA across multiple exam versions. Provides predictable performance expectations, which is pretty valuable when you're budgeting time and money for this certification. Not like some vendors who randomly adjust passing scores between versions.
Candidates scoring between 65% and 70% often fail by narrow margins, typically due to time management issues, index organization problems, or gaps in specific domain knowledge. That's rough because you're so close, but domain-weighted scoring means weak performance in heavily weighted areas like Windows Forensics at 30% has greater impact than weak performance in smaller domains. You can't just ignore the big sections and hope for the best.
High-performing candidates often achieve scores in the 80% to 90% range. Perfect scores? Extremely rare given the exam's technical depth and time constraints. The scoring methodology stresses practical competency rather than academic perfection, recognizing that working forensic analysts don't need 100% knowledge retention to be effective in real incident response scenarios.
Score reporting differences between pass and fail
Here's something interesting that catches people off guard. Score reports for passing candidates show only "Pass" status without specific percentage, while failed attempts receive detailed percentage scores by domain. If you pass, you'll never know if you squeaked by at 72% or crushed it at 89%. Only failures get the detailed breakdown showing exactly how you performed in each domain area.
GIAC doesn't provide question-level feedback or answer keys even after completing the examination. You won't get to review which specific questions you missed or see explanations for correct answers. This policy protects the question bank but means you're left doing some educated guesswork about what went wrong if you fail.
Preparing for the 71% threshold reality
Candidates should aim for 80% or better performance on practice tests before attempting certification. Provides a safety margin above the 71% passing threshold that accounts for exam day stress, time pressure, and those weird edge-case questions that always seem to pop up. If you're consistently hitting 75% on GCFA practice tests during preparation, you're cutting it too close for comfort.
Understanding the 71% threshold helps candidates develop realistic study goals and assess readiness through practice test performance before attempting certification. I've seen plenty of people rush into the exam after one practice test at 73% thinking they're ready, then come back shocked when they score 68% on the real thing. The practice environment's calmer, your index is fresh in your mind, and you're not dealing with proctoring stress.
The criterion-referenced approach means your GCFA certification holds the same value whether you earned it last year or five years ago, whether five people passed that month or five hundred. For candidates coming from related certifications like GCIH or GSEC, this consistency makes career planning more predictable. You know exactly what performance standard you need to hit, and that standard won't randomly change on you.
The 71% threshold's fair given the open-book format and professional-level expectations. It's achievable with proper preparation but high enough to maintain certification credibility in the digital forensics field.
GCFA Exam Difficulty: What Makes GCFA Challenging and How to Succeed
GIAC GCFA certification overview (GIAC Certified Forensics Analyst)
The GIAC GCFA certification is one of those digital forensics certification badges that actually means something when you put it on a resume. It focuses on incident response and forensics, not just theory, so you're expected to read artifacts, explain attacker behavior, and defend your conclusions like you're writing notes for court or a cranky internal audit.
Who's it for? IR analysts, obviously. Threat hunters who keep getting pulled into post-compromise work. DFIR folks who want a structured way to level up. Also sysadmins who somehow became "the forensics person." It happens more than you'd think.
Look, if you hate artifacts, skip it entirely.
GCFA exam details
The exam format's straightforward on paper: 115 questions in 180 minutes, delivered online with proctoring, open-book, mostly scenario-based with some direct knowledge checks. That timer? It's the real boss fight. You don't have time to casually flip through PDFs like you're reading on a Sunday morning. The questions often expect you to connect multiple clues across disk, logs, and memory while staying calm under pressure.
The GCFA passing score is set by GIAC and can vary by form, but you should treat it like you need to be comfortably above the line, not scraping by. Scoring's percent-based. If you walk in hoping your open-book stack will save you, the math gets ugly fast. Really ugly.
You'll see the GCFA exam objectives span Windows and Linux artifacts, file systems, timeline work, memory forensics, and handling evidence in a defensible way. The scope's big. The details? Even bigger. Like "which artifact tells you this exact thing" details that feel unnecessarily granular until you're actually investigating. Then it clicks.
GCFA cost: exam fees and training pricing
People ask about GCFA exam cost early, because yeah, it's not cheap. GIAC exams are premium-priced. The exam attempt's typically purchased standalone or bundled with training depending on your route.
SANS FOR508's the common path, and SANS FOR508 GCFA training's expensive but it comes with curated material, labs, and a structure that makes the chaos feel survivable. Self-study can work, but then you're building your own map from scattered sources. That's fine if you already have miles in DFIR, though it's definitely a harder road.
Budget for a retake. Just mentally. Not because you will fail, but because removing financial panic makes you study better. Also check what's included with your purchase, like practice tests, because those change your prep plan a lot.
GCFA exam difficulty: how hard is the GCFA exam?
GCFA exam difficulty is high. Like, among the hardest GIAC certs high. The open-book format doesn't lower the bar, it raises expectations, because you're supposed to perform like someone who already does this work, with references as backup, not as a crutch you lean on for every single question.
Breadth's the first punch. The breadth of forensic artifacts across Windows, Linux, browsers, email, and memory means you're dealing with hundreds of artifact locations, structures, and interpretations. The exam will happily ask you to choose between two answers that are both "kinda true" except one's correct for this specific artifact in this specific context. That's why forensic artifact analysis is the core skill, not memorizing a tool menu.
Depth's the second punch, especially Windows. I'm talking Registry analysis, event log interpretation, NTFS filesystem structures, MFT details, $LogFile, $UsnJrnl, shortcut files, prefetch, SRUM, Amcache, shimcache, and then correlating it all into a coherent story with timeline analysis and evidence handling. If you don't have a Windows internals background, you can still pass, but the learning curve's steep. You'll feel it when questions start stacking artifacts together and asking you what action happened first and what evidence supports it.
Time pressure's the third punch. 115 questions, 180 minutes. Do the math. You cannot "search" your way through the exam. You need an index that gets you to the right page fast, and you need to make calls quickly when a question's trying to bait you into overthinking. Open-book turns into a trap because people waste minutes hunting for the perfect line instead of using their notes to confirm what they already basically know. I watched a guy in my cohort spend 8 minutes on question 12 and then basically have a meltdown at question 90 when he realized he had 25 questions left and 11 minutes on the clock.
Then there's applied analysis. Scenario-based questions are everywhere. You'll be asked to interpret artifacts, identify attacker actions, and pick an investigation approach that makes sense. This is where people who only did flashcards get wrecked. The exam wants decision-making, not trivia night performance.
Memory forensics is its own mini-mountain. Volatility plugin knowledge, process analysis, signs of injection, persistence clues, suspicious network connections, and a basic understanding of what you're even looking at in memory structures. If you've never done memory analysis, it feels like learning a new language at speed, and the questions tend to be less forgiving because a wrong assumption early can poison your whole interpretation, which cascades into more wrong answers.
Common failure reasons? Bad indexing. Not enough hands-on. Spending too long per question. Also, treating "open-book" like "open-Google," which it absolutely isn't.
GCFA prerequisites and recommended background
Official GCFA prerequisites aren't rigid in the way some cert tracks are, but practical prerequisites are real. You want comfort with Windows internals, logs, file system basics, and at least a working familiarity with Linux artifacts. You also want to be able to build and defend a timeline, because correlation's the glue that holds everything together.
Helpful prior knowledge: GCIH-style IR thinking, basic networking, and any real ticket work where you had to prove what happened, not just guess. Hands-on experience beats pure study every time here.
Best GCFA study materials (FOR508 and beyond)
Your GCFA study materials should be artifact-first. FOR508 courseware's the obvious anchor if you take it. The labs matter more than people admit. Re-do them, break them, rebuild timelines from scratch until it becomes second nature.
Other references worth having? Tool docs for things you actually use. Artifact cheat sheets. Windows artifact deep references. Browser artifacts notes, email header basics, and a memory forensics quick reference that you've personally annotated.
The index is non-negotiable. Build an exam index that maps artifact to purpose to where-it-lives to "what question it answers," because in the exam you're not looking up definitions, you're verifying decisions you've already made.
GCFA practice tests and exam prep strategy
Use GCFA practice tests like diagnostics, not like a confidence boost. Take one timed. Review every miss thoroughly. Update your index based on what slowed you down, not only what you got wrong. Then retest after you've done hands-on work in the weak areas. This cycle's critical.
Hands-on matters. Pull timelines. Validate artifacts. Practice confirming a hypothesis with at least two sources. That habit maps directly to the scenario questions you'll face.
GCFA renewal requirements (maintaining GIAC certification)
GCFA renewal requirements are the normal GIAC pattern: a renewal cycle with a maintenance fee and continuing education credits. Track your CPEs as you earn them. Save proof. Keep it boring and organized, because the last thing you want is scrambling at renewal time with a half-remembered webinar and no documentation to prove attendance.
GCFA FAQ (people also ask)
How much does the GIAC GCFA exam cost?
The GCFA exam cost depends on whether you buy the exam alone or bundled with training, but plan for a high-end certification price tag, plus optional practice tests and a possible retake. Budget accordingly.
What is the passing score for the GCFA exam?
The GCFA passing score is set by GIAC and varies by exam form. Treat it like you need a comfortable buffer, because time pressure and scenario questions create mistakes even when you "know the material" cold.
Is the GCFA certification hard to pass?
Yes, absolutely. GCFA exam difficulty is high because of artifact breadth, Windows depth, memory forensics complexity, and brutal pacing despite being open-book. Don't underestimate it.
What's the best way to study for GCFA (FOR508)?
Anchor on FOR508 materials if you have them, build a ruthless index, and do hands-on labs with timelines. Reading alone won't cut it. You need practical application.
How do I renew my GCFA certification and maintain CPEs?
Meet the renewal cycle requirements, pay the maintenance fee, and log CPE activities with proof as you go. Keep a folder. Future you will be grateful you stayed organized.
Conclusion
Wrapping it all up
Real talk. The GIAC GCFA certification isn't something you wake up one day and knock out in a weekend. It's one of those digital forensics certifications that actually tests whether you can do the work, not just whether you memorized definitions. The GCFA exam cost is steep and the GCFA exam difficulty will push you, but honestly that's kind of the point. Employers know what this cert means.
If you've made it this far in researching GCFA, you probably already know whether incident response and forensics is your path. The GCFA passing score sits around 71%, which doesn't sound brutal until you're 90 minutes in, sweating over a registry artifact question while frantically flipping through your index. The time pressure's real. But if you've got decent experience with Windows internals, log analysis, and timeline analysis and evidence handling, you're not walking in blind.
Your study approach matters more than how many hours you log. Way more than people think when they're planning this out because you can waste weeks on the wrong materials and still bomb the practical scenarios. SANS FOR508 GCFA material is gold if you can swing it, but self-study with quality GCFA study materials and a solid lab environment can work too. Build that index methodically. Not just copying slides, but organizing by artifact type, tool output, and forensic artifact analysis concepts you actually understand. I've seen people pass with a mediocre index they knew inside-out, and I've seen people fail with a beautiful 200-page tome they couldn't work through under pressure.
Don't skip GCFA practice tests. They're your best diagnostic tool for finding gaps before exam day costs you a retake fee. Work them like the real thing: timed, index only, no Googling. Review wrong answers until you understand the artifact behavior, not just the "correct" letter.
One thing about GCFA prerequisites. There aren't formal ones, but walking in without solid IR experience or at least GCIH-level knowledge is asking for pain. I bombed a vendor cert once because I thought raw determination could replace actual hands-on time with the tools. Learned that lesson the expensive way. And once you pass, remember the GCFA renewal requirements kick in after four years, so track those CPEs from day one.
If you're serious about validating your forensics chops and want exam-realistic prep that mirrors actual question patterns and GCFA exam objectives, the GCFA Practice Exam Questions Pack gives you that final layer of confidence before test day. Real scenarios, proper difficulty curve, and the kind of artifact-level detail that separates passing from failing.
You've got this. Just respect the exam, prep smart, and go get certified.
Show less info
Hot Exams
Related Exams
GIAC Systems and Network Auditor
GIAC Secure Software Programmer – Java
GIAC Certified Project Manager Certification Practice Test
GIAC Information Security Fundamentals
GIAC Critical Controls Certification (GCCC)
GIAC GIAC Secure Software Programmer - C#.NET
GIAC Certified ISO-2700 Specialist Practice Test
GIAC Certified Enterprise Defender
GIAC Security Essentials
GIAC Certified Firewall Analyst
GCIA – GIAC Certified Intrusion Analyst Practice Test
GIAC Advanced Smartphone Forensics
GIAC Penetration Tester
GIAC GIAC Secure Software Programmer - C#.NET
GIAC Certified Perimeter Protection Analyst
GIAC Certified Incident Handler
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.