312-50v11 Practice Exam - Certified Ethical Hacker Exam (CEH v11)
Reliable Study Materials & Testing Engine for 312-50v11 Exam Success!
Exam Code: 312-50v11
Exam Name: Certified Ethical Hacker Exam (CEH v11)
Certification Provider: ECCouncil
Corresponding Certifications: CEH v11 , ECCouncil Other Certification

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
312-50v11: Certified Ethical Hacker Exam (CEH v11) Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 400 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena ECCouncil Certified Ethical Hacker Exam (CEH v11) (312-50v11) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
ECCouncil 312-50v11 Exam FAQs
Introduction of ECCouncil 312-50v11 Exam!
ECCouncil 312-50v11 is the Certified Ethical Hacker (CEH) v11 exam. It is a comprehensive exam that tests a candidate's knowledge and skills in areas such as system hacking, network scanning, cryptography, and more. The exam is designed to assess a candidate's ability to identify, analyze, and respond to security threats in an ethical manner.
What is the Duration of ECCouncil 312-50v11 Exam?
The duration of the ECCouncil 312-50v11 exam is 4 hours.
What are the Number of Questions Asked in ECCouncil 312-50v11 Exam?
There are a total of 125 questions in the ECCouncil 312-50v11 exam.
What is the Passing Score for ECCouncil 312-50v11 Exam?
The passing score for the ECCouncil 312-50v11 exam is 70%.
What is the Competency Level required for ECCouncil 312-50v11 Exam?
The ECCouncil 312-50v11 exam is designed to test the knowledge and skills of a Certified Ethical Hacker (CEH). To pass the exam, candidates must demonstrate a comprehensive understanding of the topics covered in the exam, including network security, cryptography, and ethical hacking. Candidates must also demonstrate the ability to apply their knowledge to real-world scenarios. The exam is designed to assess the competency level of a CEH, and the minimum competency level required to pass the exam is Expert.
What is the Question Format of ECCouncil 312-50v11 Exam?
The ECCouncil 312-50v11 exam consists of multiple-choice and multiple-response questions.
How Can You Take ECCouncil 312-50v11 Exam?
ECCouncil 312-50v11 exam can be taken both online and in a testing center. To take the exam online, you must register for and purchase the exam from the ECCouncil website. Then, you will be provided with a link to access the exam. To take the exam in a testing center, you must register for and purchase the exam at an ECCouncil approved testing center. You will then be provided with a voucher to take the exam at the testing center.
What Language ECCouncil 312-50v11 Exam is Offered?
ECCouncil 312-50v11 Exam is offered in English.
What is the Cost of ECCouncil 312-50v11 Exam?
The price for the ECCouncil 312-50v11 exam is $250 USD.
What is the Target Audience of ECCouncil 312-50v11 Exam?
The target audience of the ECCouncil 312-50v11 exam is experienced IT professionals and cybersecurity professionals who want to gain the Certified Ethical Hacker (CEH) certification. This certification is aimed at those who have knowledge of ethical hacking and penetration testing and want to demonstrate their skills and knowledge in this area.
What is the Average Salary of ECCouncil 312-50v11 Certified in the Market?
The average salary for a professional who has earned the ECCouncil 312-50v11 exam certification is around $75,000 - $90,000 per year.
Who are the Testing Providers of ECCouncil 312-50v11 Exam?
ECCouncil provides official 312-50v11 exam preparation materials and practice tests through their Proven Professional Learning Platform. They also offer online proctored exams for the 312-50v11 exam. Additionally, many third-party testing centers, such as Pearson VUE, provide testing for the ECCouncil 312-50v11 exam.
What is the Recommended Experience for ECCouncil 312-50v11 Exam?
The ideal experience for taking the ECCouncil 312-50v11 exam should include a comprehensive understanding of the topics covered in the exam. Candidates should have at least two years of information security experience, a strong foundation in security concepts, and experience with security technologies. Additionally, it is recommended that candidates have hands-on experience with the tools and techniques used in ethical hacking.
What are the Prerequisites of ECCouncil 312-50v11 Exam?
The ECCouncil 312-50v11 exam has no prerequisites. However, it is recommended that individuals have at least two to three years of experience in the field of ethical hacking before attempting the exam. Additionally, it is recommended that individuals have a good understanding of the topics covered in the EC-Council Certified Ethical Hacker (CEH) certification course.
What is the Expected Retirement Date of ECCouncil 312-50v11 Exam?
The official website for ECCouncil 312-50v11 exam is https://cert.eccouncil.org/312-50v11.html. You can find the expected retirement date for this exam on the same page.
What is the Difficulty Level of ECCouncil 312-50v11 Exam?
The difficulty level of the ECCouncil 312-50v11 exam is medium.
What is the Roadmap / Track of ECCouncil 312-50v11 Exam?
The EC-Council Certified Ethical Hacker (CEH) 312-50v11 certification track/roadmap is a comprehensive program designed to help IT professionals gain the knowledge and skills required to protect their organizations from cyber-attacks. It is a comprehensive certification program that covers topics such as ethical hacking, network security, cryptography, and malware analysis. The 312-50v11 exam is the final exam in the CEH certification track and is designed to test the candidate's knowledge of ethical hacking techniques, tools, and processes. Passing the 312-50v11 exam is the final step in achieving the CEH certification.
What are the Topics ECCouncil 312-50v11 Exam Covers?
The EC Council Certified Ethical Hacker (CEH) 312-50v11 exam covers a wide range of topics related to ethical hacking and information security. The topics covered in the exam include:
1. Footprinting and Reconnaissance: This topic covers techniques used to identify and gather information about a target system or network.
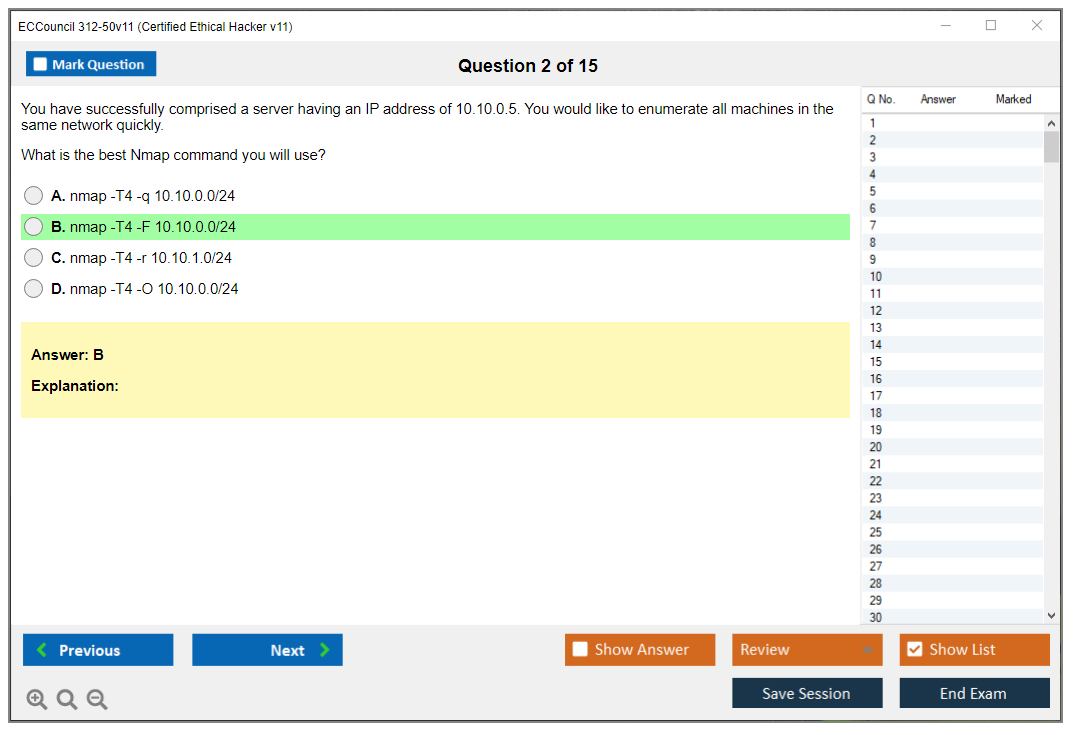
2. Scanning Networks: This topic covers techniques used to identify live hosts, open ports, and services running on a target system or network.
3. Enumeration: This topic covers techniques used to identify user accounts, shares, and other information related to a target system or network.
4. System Hacking: This topic covers techniques used to gain access to a target system or network.
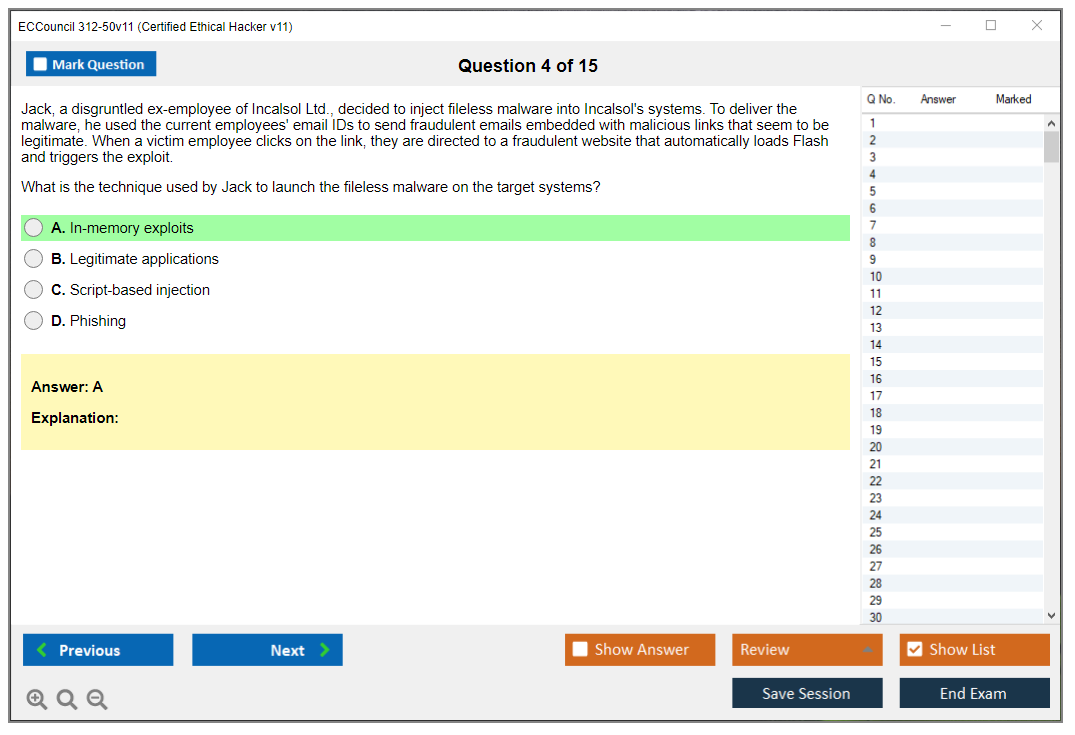
5. Malware Threats: This topic covers techniques used to detect and defend against malicious software.
6. Sniffing: This topic covers techniques used to intercept and analyze network traffic.
7.
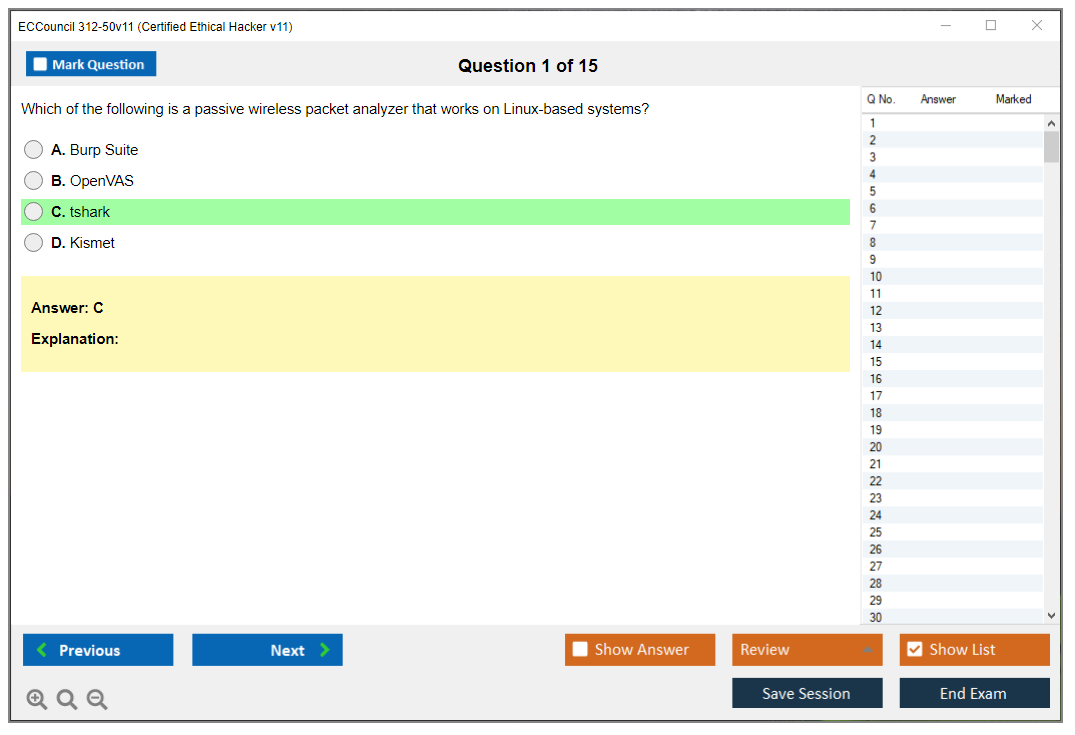
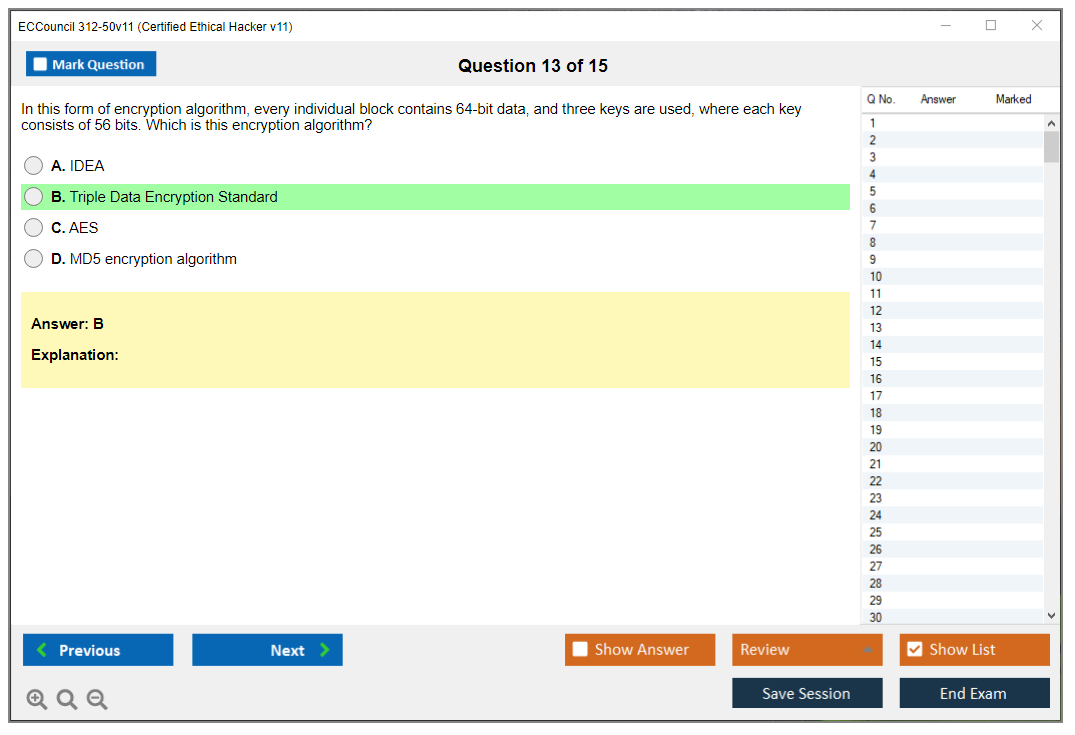
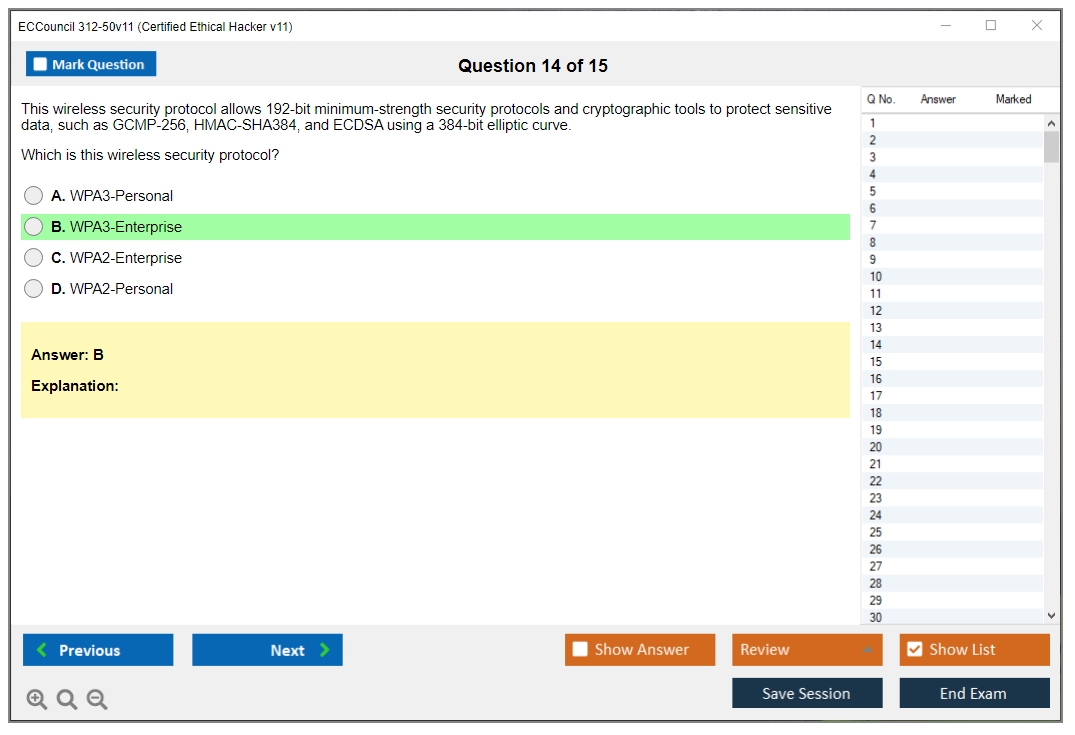
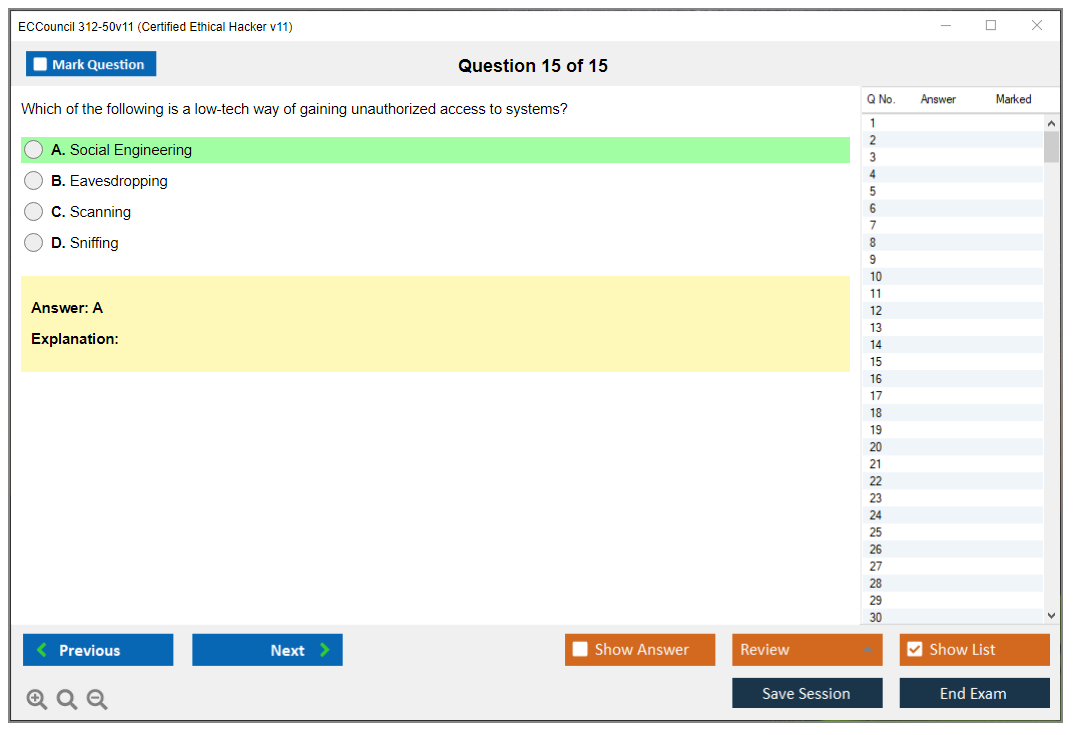
What are the Sample Questions of ECCouncil 312-50v11 Exam?
1. What is the purpose of the Network Security Policy?
2. What are the key components of a secure network architecture?
3. What is the difference between a firewall and an intrusion detection system?
4. What is the purpose of a honeypot?
5. What is the role of cryptography in network security?
6. How does a VPN work and what are its benefits?
7. What is the difference between symmetric and asymmetric encryption algorithms?
8. What is the purpose of a demilitarized zone (DMZ)?
9. What is the difference between authentication and authorization?
10. What is the purpose of a risk assessment and how is it conducted?
ECCouncil 312-50v11 (Certified Ethical Hacker Exam (CEH v11)) ECCouncil 312-50v11 (CEH v11) Exam Overview and Certification Value What is the CEH v11 certification? The 312-50v11 (Certified Ethical Hacker Exam (CEH v11)) is EC-Council's flagship offensive security certification that validates your ability to think like an attacker while operating within ethical boundaries. This isn't just another security cert. It's specifically designed to prove you understand penetration testing methodologies, attack vectors, and the tools hackers actually use in the wild, which makes it way more practical than half the credentials out there. Version 11 brought some serious updates to the table. Expanded cloud security coverage? Check. AWS, Azure, Google Cloud platforms all get attention now. IoT hacking, operational technology security, modern attack frameworks reflecting what's actually happening in corporate networks right now. What makes CEH v11 particularly valuable is its recognition by the... Read More
ECCouncil 312-50v11 (Certified Ethical Hacker Exam (CEH v11))
ECCouncil 312-50v11 (CEH v11) Exam Overview and Certification Value
What is the CEH v11 certification?
The 312-50v11 (Certified Ethical Hacker Exam (CEH v11)) is EC-Council's flagship offensive security certification that validates your ability to think like an attacker while operating within ethical boundaries. This isn't just another security cert. It's specifically designed to prove you understand penetration testing methodologies, attack vectors, and the tools hackers actually use in the wild, which makes it way more practical than half the credentials out there. Version 11 brought some serious updates to the table. Expanded cloud security coverage? Check. AWS, Azure, Google Cloud platforms all get attention now. IoT hacking, operational technology security, modern attack frameworks reflecting what's actually happening in corporate networks right now.
What makes CEH v11 particularly valuable is its recognition by the U.S. Department of Defense under Directive 8570.01-M, which basically means if you want certain government or contractor positions, you need this certification on your resume. ANSI accredited too. Another layer of legitimacy. Employers recognize it immediately.
The certification covers both theoretical knowledge and hands-on application. You're not just memorizing port numbers. You're learning the five-phase penetration testing methodology, understanding reconnaissance techniques, exploitation strategies, and post-exploitation activities that mirror real-world scenarios.
Who should take the 312-50v11 exam?
Security analysts looking to pivot into offensive security roles are the obvious candidates here. Network administrators? They'll benefit massively from this perspective shift. Defending networks becomes way easier when you've spent time thinking about how to break into them.
IT professionals seeking career advancement often grab CEH because it's one of those credentials that hiring managers explicitly request. Job postings literally say "CEH required" for penetration tester and security consultant positions. I've seen it dozens of times. Compliance and audit professionals need this too, especially when they're evaluating security controls and need to understand offensive capabilities to properly assess risk.
Military and government personnel fulfilling DoD 8570 requirements represent a huge chunk of CEH candidates. This cert checks specific boxes for information assurance positions that few other credentials satisfy, which makes it borderline required for those career paths.
CEH v11 exam cost
Expensive territory here. The CEH v11 exam cost varies depending on how you approach it, but you're typically looking at around $1,199 for the exam voucher if you go through EC-Council's official training. Not gonna lie, that's steep. If you already meet the work experience requirement (two years of information security work) you can challenge the exam without training, though you'll pay an additional non-refundable eligibility application fee of $100.
Retake fees? Equally painful. You'll pay the full exam price again if you fail, which is why proper preparation matters so much. Some people opt for training bundles that package the official courseware, labs, and exam voucher together, which can run anywhere from $2,500 to $3,000+ depending on delivery format. Self-paced versus instructor-led makes a difference. The training bundle makes sense if you're new to ethical hacking or your employer is footing the bill. Exam-only works fine for experienced security professionals who just need the credential.
My cousin actually works in procurement for a mid-sized consulting firm, and she says the number of people who expense these certs without doing proper research first is staggering. Half never finish the training.
Passing score for 312-50v11
Frustrating fact: the CEH v11 passing score isn't publicly disclosed by EC-Council, which is typical for vendor certs but annoying nonetheless. What we know from candidate reports is that you need to correctly answer approximately 60-70% of questions, though the exact threshold can vary slightly due to the adaptive nature of some question sets.
The exam uses a scaled scoring system. Your final score isn't just a raw percentage. It's adjusted based on question difficulty, which theoretically makes it fairer but also makes preparation targets hazier. You'll face 125 multiple-choice questions with a four-hour time limit, which gives you plenty of time if you've studied properly. Most people finish with 30-60 minutes to spare and use that time to review flagged questions.
CEH v11 difficulty level
How hard is CEH v11? Depends entirely on your background. If you're coming from a networking or systems administration role with some security exposure, you'll find it challenging but manageable with 4-6 weeks of focused study. Career changers or people new to IT will struggle more. This isn't an entry-level certification despite what some marketing materials suggest.
Common reasons candidates fail include inadequate hands-on practice with tools like Nmap, Metasploit, Wireshark, and various exploitation frameworks that show up constantly on the exam. It tests practical knowledge, not just theory, so reading about port scanning without actually running scans against vulnerable VMs leaves you unprepared. Another failure point? Neglecting newer domains like cloud security and IoT hacking that weren't emphasized in earlier CEH versions but now carry serious weight.
Compared to CompTIA Security+, CEH v11 is significantly harder and more specialized. Security+ covers broad security concepts while CEH dives deep into offensive techniques. Against CompTIA PenTest+, they're more comparable in difficulty, though CEH has broader global recognition while PenTest+ includes a required performance-based component that CEH lacks in the multiple-choice format. Either a pro or con depending on how you learn best.
CEH v11 exam objectives
The CEH v11 blueprint covers 20 modules spanning the entire attack lifecycle. High-weight topics you absolutely need to prioritize? Footprinting and reconnaissance, both passive and active information gathering. Scanning networks (Nmap mastery is non-negotiable here), enumeration techniques, vulnerability analysis, system hacking. Malware threats, sniffing, social engineering, denial of service attacks. Session hijacking, web application hacking, SQL injection, wireless network hacking, mobile platform security, IoT and OT hacking, and cloud computing security.
Heavy stuff. The exam aligns heavily with the MITRE ATT&CK framework and traditional kill chain methodology, which makes sense given current industry trends. You need to understand not just individual tools but how they fit into broader attack sequences. Reconnaissance leads to scanning, scanning reveals vulnerabilities, vulnerabilities allow exploitation, exploitation grants access, and access allows for privilege escalation and persistence.
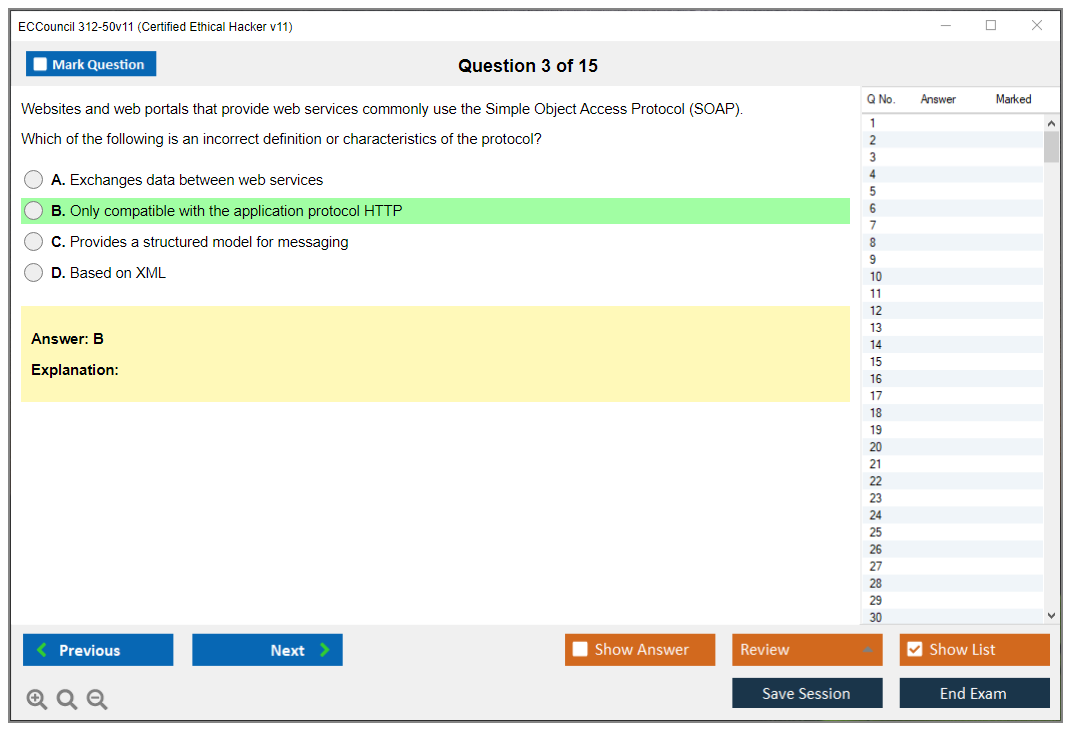
Tools covered include Nmap, Metasploit Framework, Burp Suite, Wireshark, Aircrack-ng, John the Ripper, Hashcat, SQLMap, and dozens of others across various attack categories. You don't need to be an expert in every tool, but you should understand what each does and when you'd use it during an engagement. That requires actual hands-on time rather than just reading documentation.
Prerequisites and eligibility requirements
EC-Council offers two eligibility paths for the 312-50v11 exam. You can attend official EC-Council training (either instructor-led, online self-paced, or through an authorized training center) which automatically qualifies you to sit for the exam. Pretty straightforward. Alternatively, if you have at least two years of work experience in information security, you can submit an eligibility application along with that $100 fee to challenge the exam without training.
Recommended prerequisite knowledge includes solid networking fundamentals like TCP/IP, routing, switching. Linux command-line proficiency, Windows system administration, and basic security concepts. If you're completely new to these areas, consider getting 212-82 (Certified Cybersecurity Technician (CCT)) first or spending time with foundational resources before jumping into CEH. Building on nothing is brutal.
Best CEH v11 study materials
Official EC-Council courseware includes full modules, hands-on labs through iLabs, and practice questions that closely mirror exam format and difficulty, which is probably their biggest selling point. The labs are particularly valuable because they provide pre-configured environments for practicing attacks without building your own infrastructure, saving you hours of setup frustration. That said, they're expensive and not strictly required if you're willing to self-study and build your own lab environment.
Third-party resources? Matt Walker's CEH v11 book gets recommended constantly for its clear explanations and full coverage. Video courses from platforms like Udemy and Cybrary, though quality varies. Check recent reviews before dropping cash. Community-created notes and cheat sheets that distill key concepts. For hands-on practice, build a home lab using VirtualBox or VMware with Kali Linux as your attack platform and vulnerable VMs like Metasploitable, DVWA, and HackTheBox machines as targets.
The key is balancing reading with doing. Don't just watch videos or read books passively. Actually run the tools, break things, understand why attacks succeed or fail. That builds the intuition you need for exam scenarios that don't perfectly match study materials.
CEH v11 practice tests
Best practice test sources include the official EC-Council practice exams if you purchased training. Boson ExSim-Max costs money but gets highly regarded for quality and detailed explanations that teach as much as the questions themselves. Various free question banks online exist, though quality is hit-or-miss. Stick with reputable sources. Use practice tests strategically. Take timed sets under exam conditions, thoroughly review every question whether you got it right or wrong, and maintain an error log of topics you consistently miss.
Target scores before scheduling the real exam should be consistently above 85% on practice tests. If you're scoring 70-75%, you're not ready yet. Keep studying weak areas. Retaking the same practice tests repeatedly inflates your scores artificially, so rotate between different question sources to get honest feedback on your preparation level.
CEH v11 renewal requirements
CEH certifications require renewal every three years through EC-Council's continuing education (ECE) credit system, which isn't too painful if you stay active in the field. You need to earn 120 ECE credits during your three-year cycle, which you can accumulate through attending security conferences, completing training courses, participating in webinars, publishing security research, or teaching security topics.
Renewal fees are currently $80 annually or $250 for three years if you pay upfront. The three-year option saves you $10, though the difference is negligible. This ongoing requirement frustrates some people, but it ensures certified professionals stay current as the threat space evolves, which matters when you're representing yourself as an ethical hacking expert. What counts for renewal includes attending events like DEF CON or Black Hat (earning significant credits), completing vendor training (even non-EC-Council courses often qualify), and participating in EC-Council's own webinars and training offerings.
The renewal cycle starts from your certification date, not the calendar year. Track your credits carefully. Submit them before your deadline, because letting it lapse means retaking the entire exam.
How CEH v11 fits in the certification pathway
CEH v11 is the entry point into EC-Council's offensive security track, though calling it "entry-level" is misleading given its difficulty and scope. Natural progressions include 412-79v10 (EC-Council Certified Security Analyst (ECSA) V10) for deeper penetration testing methodology and Licensed Penetration Tester (LPT) for advanced practical skills that go beyond what CEH covers. You might also consider 312-38 (Certified Network Defender (CND)) to balance offensive skills with defensive knowledge, or specialized credentials like 312-49v10 (Computer Hacking Forensic Investigator (CHFI-v10)) if forensics interests you.
Some people pursue CEH alongside or after 312-50v12 (Certified Ethical Hacker Exam (CEHv12)) or 312-50v13 (Certified Ethical Hacker Exam (CEHv13)) depending on when they start their certification path. Newer versions incorporate updated content, but v11 remains valid and recognized, so don't feel pressured to jump to the latest version immediately unless your employer requires it.
Career benefits and market demand
CEH-certified professionals command salaries ranging from $75,000 for entry-level positions up to $120,000+ for experienced penetration testers and security consultants, with significant geographic variation. Major metros pay more, obviously. The certification opens doors to roles explicitly requiring it. I've seen countless job postings where CEH is listed as required or strongly preferred for penetration tester, vulnerability assessor, security analyst, and security consultant positions. Makes it a practical investment if those career paths interest you.
Beyond salary, CEH demonstrates commitment to ethical hacking principles and professional development, which matters when clients or employers are evaluating who to trust with testing their systems. Wait, who to trust with deliberately breaking into their infrastructure to find weaknesses. It provides a foundation for pursuing more advanced certifications like OSCP, which is more hands-on and practical but also more difficult and time-consuming.
Not gonna lie, CEH alone won't make you a master penetration tester. You need practical experience, continuous learning, and ideally additional certifications. But it's a recognized credential that gets your resume past HR filters and proves you understand offensive security fundamentals at a professional level. That's half the battle in competitive job markets.
CEH v11 Exam Format, Structure, and Key Administrative Details
ECCouncil 312-50v11 (CEH v11) exam overview
Recruiters know CEH. That's the main thing. It's the EC-Council ethical hacking certification exam that HR filters still hunt for, even when the hands-on crowd gets a bit eye-rolly about it.
What's the CEH v11 certification? Okay, so Certified Ethical Hacker v11 is EC-Council's knowledge exam that focuses on attack phases, common tools, security concepts across the CEH blueprint and domains. Here's the critical bit: it's mostly about recognizing what's correct in a scenario instead of proving you can actually pop a box live. That throws some people off when they expect more practical validation, honestly.
Who should take the 312-50v11 exam? If you're aiming at SOC analyst, junior pentest, security analyst, or those "security engineer but early career" roles, the ECCouncil 312-50v11 CEH v11 exam helps you get past gatekeepers. Period. It also gives you structured vocabulary that shows up constantly in tickets and incident notes.
CEH v11 exam format and key facts
Exam code, name, and version (312-50v11). The official code is 312-50v11. The v11 denotes version 11 of the Certified Ethical Hacker exam. The full name you'll see on vouchers and registration screens is EC-Council Certified Ethical Hacker (CEH) version 11, which sounds formal but that's literally what appears. As of 2026, v11's still considered current, with periodic updates to the question pool and content. Two people can sit "v11" exams and still encounter completely different forms, which can be jarring. Previous versions like v10 and v9? Retired. They were similar in structure and difficulty, but the version number matters a ton when you're buying vouchers, scheduling with Pearson VUE, or seeking employer reimbursement. Wrong version? Wrong prep. Total pain.
Question types, duration, and delivery (Pearson VUE vs remote). The CEH format's 125 multiple-choice questions, four options per question (A, B, C, D), with a single correct answer. There aren't performance-based questions like you'd see in some competitor certs, even though the wording can feel "hands-on" because it references logs, scans, tool output. You'll encounter a mix: scenario-based questions making you interpret what's happening, knowledge-based questions about concepts and terminology, and tool identification questions where you're expected to recognize what a utility does. Like when a question drops a command snippet or scan result and asks what the next step is. Some questions carry different weights based on difficulty and domain importance, which explains why two people can hit the same raw percent and not share the same scaled outcome.
Time's four hours (240 minutes). That's roughly 1.9 minutes per question if you spread it evenly, but here's the thing: scenario-heavy stuff will absolutely devour time if you let it. I mean you need an actual pacing plan, not just vibes and hope. No scheduled breaks, and restroom breaks count against your clock. Annoying? Yes. Normal for this kind of ethical hacking certification exam? Also yes.
Delivery's through Pearson VUE only. You can choose a test center, which is the controlled environment option. Fewer home-internet surprises, usually less anxiety about whether your webcam framing is "good enough." Or you can do online proctoring (OnVUE) from home or office, which requires a webcam, microphone, stable internet, and a private space. The rules are strict: no notes, no extra monitors, no phone, no "my smart watch is just a watch," and yeah they can end your session if they suspect you're messing around. I've heard that happens more than you'd think. Both options have identical exam content and difficulty.
Passing score for 312-50v11 (how scoring works). The 312-50v11 passing score isn't a fixed percentage. This is where people get really salty about it. It's typically described as 60% to 85% depending on the exam form because scoring's scaled. Difficulty adjustments happen between different versions of the question set, which sounds fair in theory but feels arbitrary when you're the one waiting for results. Practically, most candidates report needing around 70% to pass. Your raw score gets converted to a scaled score on a 0 to 1000 scale, with passing often landing around 700+ out of 1000. No partial credit. Correct or incorrect.
exam duration, time management, and pacing strategies
Mark questions. Move on.
A good flow? Finish a first pass in about 2.5 to 3 hours, then keep 1 to 1.5 hours for review. Once fatigue hits hard, you start misreading "MOST likely" and "BEST next step," and that's exactly how people torch points they actually knew cold. Scenario questions are the time traps, especially ones showing tool output or a mini-story about a compromised host. Decide early if you're gonna spend 4 minutes wrestling it or flag it and come back when the easy points are already banked safely.
I remember one practice run where I got tunnel vision on a scanning question for like seven minutes trying to remember the exact syntax of an nmap flag. Seven minutes! Meanwhile I'd skipped three straightforward terminology questions I could have knocked out in thirty seconds each. Don't be that person.
score reporting and results delivery timeline
You get a preliminary pass/fail on screen right after you finish. Quick. Brutal.
The score report's typically available within 24 hours via the EC-Council ASPEN portal. It shows performance by domain rather than telling you exactly which questions you missed. Frustrating but normal for vendor exams, so don't expect granular feedback. If you pass, certification issuance is commonly 5 to 7 business days through ASPEN. You can usually grab a digital badge quickly while the physical certificate, if you request it, can take weeks in the mail.
CEH v11 exam cost (pricing breakdown)
CEH v11 exam cost's the question everyone asks first. It varies wildly based on whether you're buying an exam-only voucher, a training bundle, or getting a discount through an employer, academic program, or promo. Exam-only vouchers are often in the several-hundred-dollar range and can climb close to four figures depending on region and what's included. Don't assume the price you saw in a forum thread last year is still real in 2026.
Retakes also cost money. Policies can change, but expect a retake fee and expect waiting-period rules. If you're budgeting, budget for a retake even if you're confident because stress does really weird things on a four-hour multiple-choice sprint.
Training bundle vs exam-only. If you already have solid networking, Linux basics, and you've actually used tools, exam-only can make sense. If you're newer, the official CEH v11 training courseware and labs can be worth it just because it tells you what EC-Council thinks matters. Even if you supplement with better third-party material.
CEH v11 difficulty (how hard is it?)
CEH v11 difficulty level depends on your background more than your IQ. If you've worked tickets, read logs, touched Kali, and you know what common web app bugs look like, it's mostly "do I recognize this and can I pick the best answer." Wait, let me clarify. If you're coming in from zero, the terminology load's heavy and the questions are written to punish sloppy reading.
Common reasons people fail? Rushing and not reading qualifiers carefully. Memorizing tool names without understanding where they fit in the attack flow. And relying on CEH v11 practice tests that are basically brain dumps or low-quality questions that don't match the exam's style. Not gonna lie, that's a fast way to get a false sense of readiness.
CEH vs other certs. Compared to Security+, CEH's more attacker-tool flavored and more scenario-ish. Compared to PenTest+, CEH's typically less hands-on and more recognition-based, while PenTest+ leans more into methodology and practical decision-making. CySA+'s more defender and analysis oriented. Different vibes entirely.
CEH v11 exam objectives (domains and what to study)
CEH v11 exam objectives map to the CEH blueprint and domains. You should actually read that outline because it tells you what EC-Council expects you to know. It also tells you what they think "ethical hacking" includes, which is broader than just exploitation. Covers everything from recon to reporting. High-weight areas tend to include recon and scanning, common network and web attack concepts, basic crypto and auth ideas, wireless, cloud-ish concepts depending on updates, and incident-ish thinking in scenarios.
Tools and phases matter. Recon. Enumeration. Vulnerability assessment. Exploitation concepts. Post-exploitation ideas. Reporting and legality. That flow shows up in question framing constantly.
prerequisites and eligibility requirements
CEH v11 prerequisites are mostly about eligibility, not skill. There are typically two paths: go through official training, or apply via work experience. If you're using the experience route, you may need documentation. Check EC-Council's current rules before you pay for anything because those policies are the kind of thing that changes quietly.
Recommended prerequisite knowledge? Networking basics, TCP/IP, DNS, HTTP, Linux command line, security fundamentals. Missing those makes every question slower.
best CEH v11 study materials (official + third-party)
Official EC-Council courseware and labs are aligned with how the exam talks. That matters.
For third-party CEH v11 study materials, I like a mix. One solid video course for momentum. One book or structured notes for reference. Hands-on practice where you can. Tool questions make way more sense when you've actually run scans and seen messy output instead of just memorizing definitions. Home lab setup can be simple: Kali, a Windows VM, and a couple vulnerable VMs like Metasploitable or OWASP Juice Shop, plus a safe isolated network. Yeah, it's work, but it turns "remember this term" into "I know what that looks like."
CEH v11 practice tests (how to use them effectively)
CEH v11 practice tests are useful if you treat them like diagnostics, not like a scoreboard.
Do timed sets. Review every miss. Keep an error log with the concept you got wrong and why you picked the wrong option. The exam's full of tempting distractors, and your job is to spot the "best" answer, not just a technically possible one. As a readiness target, I'd want consistent scores well above the rough pass zone across multiple sets, not one lucky run.
Study plan (1 to 8 weeks) for the 312-50v11 exam
1-week crash plan: only if you already work in security and you're basically mapping existing knowledge to CEH v11 exam objectives, drilling weak areas, and doing timed practice.
4-week plan: most people. Week 1 and 2 cover domains and notes. Week 3 is labs plus practice questions. Week 4's mostly review and full timed exams.
8-week plan: beginners and career changers, because you need time for networking and Linux basics to stop being speed bumps. You need repetition so the tool names and attack flow stop feeling like random trivia.
CEH v11 renewal requirements (maintaining your certification)
CEH v11 renewal requirements are part of the deal, so don't ignore them until the last month. EC-Council uses ECE credits (continuing education units) on a renewal cycle. You typically report activities like training, webinars, conferences, or teaching, plus pay renewal fees by the deadline. What counts can be picky, so keep receipts and screenshots as you go.
FAQs (Quick Answers)
What's the CEH v11 passing score? The 312-50v11 passing score varies by form, roughly 60 to 85%, with scaled scoring often mapping to around 700/1000 as a typical passing bar.
How much does CEH v11 cost all-in? CEH v11 exam cost depends on voucher pricing, region, and whether you buy training bundles. You should also budget for a retake just in case.
Is CEH worth it for SOC / pentest roles? For SOC, it can help with screening. For pentest, it's more "gets you interviews" than "proves you can hack." Pair it with labs and real practice.
What are the best CEH v11 study materials? Start with CEH v11 exam objectives, mix official courseware with a good third-party course, and add hands-on labs so tool questions aren't pure memorization.
How do CEH renewals work? You renew on EC-Council's cycle with ECE credits plus fees, tracked through ASPEN. You'll want to log activities throughout the year instead of trying to scramble at the end.
CEH v11 Exam Cost and Complete Financial Investment Breakdown
Okay, real talk here. The CEH v11 exam isn't cheap. Not even close. If you're serious about the ECCouncil 312-50v11 CEH v11 exam, you need to understand exactly what you're getting into financially before you commit. I've watched way too many people get sticker shock halfway through their certification path and it honestly isn't pretty.
Standard CEH v11 exam voucher pricing and what's included
The exam-only voucher? $1,199 USD. That's when you buy directly through EC-Council, and yeah, that's the standard price they're sticking with. Some regions see it drop to $950 or fluctuate somewhere in that range depending on where you're purchasing and local economic factors that honestly seem pretty arbitrary to me. You get one exam attempt at a Pearson VUE testing center or through their online proctored delivery system.
Here's the thing that bugs me about this pricing model. You get literally nothing else with that voucher. Zero additional resources or support materials. No study materials, no practice tests, no courseware. Just the exam attempt. The voucher stays valid for 12 months from purchase, which is decent I guess, but if you're not ready within that window, you're out over a grand.
Regional pricing variations? They exist. I've seen colleagues in certain countries pay noticeably less through authorized local partners, which makes you wonder about the pricing logic. EC-Council occasionally runs promotional discounts during Cyber Security Awareness Month (October) or special events, but honestly these are unpredictable. Don't bank your budget on maybe catching a 10-15% discount that may or may not materialize.
My cousin tried waiting for one of those promos last year. Ended up missing the deadline because he kept refreshing the EC-Council site expecting some big announcement that never came. Finally just bought it at full price in February, annoyed and $1,199 poorer.
Official EC-Council training bundles and what actually makes sense
The iLearn self-study package runs $850-$1,200 for just the courseware. No exam voucher included, which feels a bit stingy. I mean, you're basically paying for digital content access and some structured learning paths.
Complete training bundles? $2,499-$3,499. They include courseware, labs, practice tests, and the exam voucher. If you're starting from scratch or transitioning into security, this is where the value calculation gets interesting. You're paying roughly double the exam-only cost, but you get everything needed to actually prepare.
Instructor-led training (ILT) pushes $3,500-$4,500 for a 5-day course with exam voucher. That's a serious investment, like mortgage-payment-level serious. The iWeek virtual instructor-led training sits around $3,200-$4,000 including your exam attempt. I've talked to people who swear by the structure and forced focus of ILT, but honestly, it depends on your learning style and whether you have that kind of time blocked off. Most working professionals really don't.
The Cyber Range labs add-on? Another $400-$600 for extended hands-on practice. Practice exam packages from EC-Council run $100-$200 for official practice questions. When you start adding these components separately, you quickly realize the bundles offer better math than buying everything individually. It's one of those situations where they've engineered the pricing to push you toward bundles.
Retake policies and the cost of failure
First retake costs $350-$500 depending on your region and when you purchase it. Not terrible compared to some other certification programs I've seen. Second retake? Same pricing structure. There's a mandatory 14-day waiting period between a failed attempt and your first retake, which gives you time to study but also extends your timeline and adds stress.
No limit exists on total retake attempts. Theoretically you could take this thing ten times if you really wanted to torture yourself, but each requires a new fee and another waiting period. You purchase retake vouchers separately through EC-Council or authorized partners. Some training bundles include one free retake voucher. Verify this before purchasing because it significantly changes the value proposition if you're not confident about passing on attempt one.
Retake vouchers stay valid for 12 months from purchase date typically. If you fail twice and need a third attempt, you're looking at $1,199 + $350 + $350 = $1,899 minimum just for exam attempts. That stings pretty bad.
Hidden costs nobody talks about until it's too late
Study materials from third-party sources run $50-$300 for books, video courses, and practice tests. Huge range. Honestly reflects wildly different quality levels. If you want quality resources like the 312-50v11 Practice Exam Questions Pack at $36.99, that's actually reasonable compared to some alternatives I've seen that charge triple that for questionable content.
Lab environment costs? Wildly variable. You might spend zero if you're comfortable setting up VMs locally and have the hardware to support it. Or $200+ for cloud resources or lab subscriptions if you need managed environments. Travel and lodging if your nearest testing center isn't local could add $50-$500+ depending on distance. I've known people who had to book hotel rooms to test in the nearest major city, which is just another financial hurdle nobody mentions upfront.
Time investment represents real opportunity cost that doesn't show up on any invoice. If you're studying 10-20 hours weekly for 4-8 weeks, that's time you're not working side gigs or spending with family or just living your life. Renewal fees hit $80-$100 annually for continuing education credits (ECE) after you're certified. EC-Council membership is optional but provides discounts and resources. Another potential recurring cost that adds up over years.
Practice test platforms from quality third-party providers cost $30-$100 for good question banks. Don't skip this expense just to save a few bucks. The CEH-v11 practice materials help you understand the question format and identify knowledge gaps before you're sitting in the testing center with sweaty palms.
Cost comparison: exam-only versus training bundle math
Exam-only approach totals $1,199 + $100-$300 self-study materials = $1,299-$1,499 total investment. This works for experienced professionals with strong security backgrounds who just need to validate existing knowledge. If you've been doing penetration testing or security analysis for years, this path makes sense and saves you money.
Training bundle approach at $2,499-$3,499 all-inclusive provides guided learning paths and reduces risk for beginners who need that structure. Better value for people requiring structured learning or those without strong technical foundations who'd otherwise be floundering with self-study materials.
Self-study with third-party materials costs $200-$400 for materials + $1,199 exam = $1,399-$1,599 total. Most cost-effective approach for disciplined self-learners with technical foundations who can create their own study schedules and stick to them without needing external accountability.
Consider retake probability honestly. Actually honestly assess your chances. If you estimate a 50%+ chance of needing a retake, bundles that include a free retake attempt suddenly save money and reduce stress. The 312-50v12 exam and 312-50v13 exam follow similar pricing structures, so if you're considering future version upgrades, factor that into your planning because these costs compound over time.
Ways to reduce CEH v11 exam costs without compromising quality
Employer sponsorship covers certification costs for many security staff. If you're already employed in IT, just ask. Worst case they say no and you're exactly where you started. GI Bill and veterans benefits apply to approved training programs. Worth investigating if you're eligible, since you've earned those benefits.
Student discounts exist through EC-Council for verified students. Group training discounts kick in when 3+ candidates from the same organization register together, so coordinate with coworkers if possible. The academia program offers educators and students special pricing that's significantly reduced from standard rates.
Promotional periods during Black Friday, Cyber Monday, and awareness month sales sometimes offer 10-20% discounts that actually make a noticeable difference in total cost. Authorized training centers occasionally offer competitive bundle pricing with added value like extended lab access or mentoring that the official packages don't include.
If you're considering other EC-Council certifications like the 212-82 (Certified Cybersecurity Technician) or 312-39 (Certified SOC Analyst), look into certification pathway discounts. Some training partners offer reduced rates when you commit to multiple certifications upfront, which spreads the investment but locks you into their ecosystem.
Bottom line? Budget $1,500-$2,000 minimum if you're going exam-only with self-study. Or $2,500-$3,500 if you want training bundles that hold your hand through the process. Factor in potential retake costs and ongoing renewal fees that extend beyond your initial certification. The CEH v11 isn't the most expensive certification out there. I've seen way worse. But it isn't cheap either. Plan accordingly, study hard, and make that first attempt count because retakes get expensive fast.
CEH v11 Difficulty Level and Realistic Expectations for Exam Preparation
ECCouncil 312-50v11 (CEH v11) exam overview
CEH is the Certified Ethical Hacker v11 credential, and honestly, the ECCouncil 312-50v11 CEH v11 exam is basically EC-Council's way of checking you can talk attacker, recognize common tooling, and reason through what happens during recon, exploitation, and post-exploitation without needing a live keyboard in front of you. It's an ethical hacking certification exam with a very "broad survey" vibe, which some people absolutely love and some people can't stand.
Who should take the EC-Council CEH 312-50?
Look. If your job path touches SOC-to-red-team, vulnerability management, security engineering, or you're a network admin trying to stop being the person who only patches after the incident, it fits. If you want a pure hands-on proving ground, that's not what this is.
CEH v11 exam format and key facts
Exam code, name, and version (312-50v11)
The exam code you'll see is 312-50v11, and yes, version matters because using older notes is one of the fastest ways to feel "prepared" and still get absolutely smacked by weird phrasing and newer tool references. Different blueprint. Different emphasis. Same brand.
Question types, duration, and delivery (Pearson VUE vs remote)
It's multiple-choice. No labs.
Time pressure is real but manageable, and most people don't fail because the clock nuked them. They fail because they read sloppy and second-guess themselves into oblivion. Pearson VUE testing center or remote proctoring depends on what EC-Council's offering where you are, but either way you need to be comfortable reading fast, spotting distractors, and making a decision without staring at a question for five minutes like it's a magic eye poster.
Short questions exist. Long scenario prompts too. Tool-output snippets show up frequently enough that you'll want familiarity, not just recognition.
Passing score for 312-50v11 (how scoring works)
The 312-50v11 passing score isn't a single fixed number publicly because EC-Council uses a scaled range and the threshold can vary by form. You'll commonly hear ranges like 60% to 85% depending on the exam set. Treat it like you need to be consistently hitting 80%+ on solid CEH v11 practice tests, because walking in hoping you got the "easy form" is not a plan, it's a prayer.
CEH v11 exam cost (pricing breakdown)
CEH exam voucher price (what you typically pay)
CEH v11 exam cost depends on whether you buy exam-only, a bundle, academic pricing, promos, all that. Many candidates end up in the several-hundred-to-over-a-thousand USD zone once training's involved. It's not cheap. That's why I'm pretty opinionated about doing readiness validation before you burn a voucher on wishful thinking.
It adds up fast.
Retake fees and retake policies (what to expect)
Retakes cost money. Policies can change, and sometimes there are waiting periods that'll mess with your timeline. Check EC-Council's current retake rules when you schedule, not when you start studying, because people get surprised and then rage-post online like the policy changed just to target them personally.
Training bundle vs exam-only cost (when each makes sense)
If your employer pays, bundles can be fine. If you're self-funding, exam-only plus carefully chosen CEH v11 study materials and labs can be the smarter move, as long as you're disciplined enough not to ghost the prep halfway through. The worst combo? Paying for everything and still doing zero hands-on.
CEH v11 difficulty (how hard is it?)
Here's my honest take on CEH v11 difficulty level: intermediate to advanced, but in a specific way that catches people off guard. It's broader than deep, so you're not doing exploit dev or reverse engineering assembly, but you are expected to recognize lots of moving parts across the CEH blueprint and domains, understand the "why" behind attacks, and not panic when a question drops a tool output you've only seen once in a screenshot during module seven at 2x speed.
Overall difficulty rating?
For a prepared candidate, I'd call it a 6.5 to 7.5 out of 10. What makes it challenging isn't raw technical complexity, it's the breadth, EC-Council's sometimes quirky terminology, and scenario-based questions that punish memorization-only studying because you have to apply the concept, pick the best next step, and avoid tempting answers that are technically true but wrong for that situation.
Tool familiarity is not optional. The exam expects recognition of 100+ security tools and their outputs, and not just "Nmap is a scanner" but what a SYN scan looks like, what a web app scan output implies, what a password cracking result means, what a Windows artifact suggests during forensic triage. That's why people who only read slides get absolutely wrecked.
Pass rates are hard to verify independently, but the common estimate you'll see floating around is around 60% to 75% first-time pass for people who prepared properly. That "properly" is doing a lot of heavy lifting in that sentence.
I once watched someone spend six weeks memorizing every slide deck word-for-word and then bomb the exam because they couldn't recognize an actual Wireshark capture. Meanwhile their coworker who'd only studied three weeks but ran through vulnerable boxes every evening passed on the first try. Repetition without context is just expensive theatre.
CEH v11 difficulty level by candidate background
Experienced penetration testers or security professionals usually rate CEH as moderate difficulty. They're already familiar with most tools and techniques, so the challenge becomes coverage and EC-Council-specific wording, plus remembering the exam wants the "most appropriate" option, not the "coolest" one you'd actually run in the field. Two to four weeks of focused study is often enough, mostly to map existing knowledge to CEH v11 exam objectives and clean up weak spots.
Network administrators with security exposure land in moderate-to-challenging territory. Strong networking helps a ton on recon and scanning modules, but you still need the attacker mindset, exploitation flow, and web app basics that pure network roles don't always touch. Four to eight weeks with hands-on lab practice is a normal runway.
Security analysts from defensive backgrounds often feel moderate difficulty, but there's a mental flip required. You know what an IOC is. You know what patching means. You know SIEM life. But CEH asks "how would the attacker do it" and "what's the next step after enumeration," and that's different muscle memory. Four to six weeks can work if you practice offensive workflows instead of just reading about them.
Career changers or entry-level candidates usually find it challenging, sometimes very challenging. You're building foundations and exam content at the same time, which is like learning to drive manual while taking a road test. Eight to twelve weeks is realistic if you also spend serious time in labs, not just videos on 1.5x while scrolling Twitter.
Common reasons candidates fail (and how to avoid them)
People fail for boring reasons.
Insufficient hands-on practice. Over-reliance on memorization. Gaps in networking, operating systems, or basic security concepts. Using outdated materials from older versions. Underestimating breadth and skipping "small" domains because they seem unimportant. Not learning EC-Council's question style and what they're really asking. Not practicing scenario-based analysis where you have to choose the best answer among four plausible options. Testing too early because someone said "CEH's easy." Weak understanding of attack methodology and kill chain phases beyond just memorizing the names.
The fix list isn't sexy, but it works consistently. Do 3 to 5 full-length practice exams and don't schedule until you score 80%+ consistently across different question pools. Build a home lab with Kali Linux, a Windows VM, and vulnerable targets like Metasploitable, OWASP Juice Shop, DVWA, plus a tiny AD lab if you can handle the resource overhead. Practice tools in real environments. Not just reading about flags and switches. The exam loves "what does this output mean" and "what should you do next" prompts that punish fake familiarity.
One more thing. Actually, this might be the most important thing. Review wrong answers like you're doing an incident postmortem, because the value isn't in the right answer you now know, it's in why you were tempted by the wrong one, what keyword you missed, and what the exam is really testing under the surface.
If you want extra timed reps, a pack like 312-50v11 Practice Exam Questions Pack can help with pattern recognition and pacing stress, but don't treat any CEH v11 practice tests as a substitute for understanding. That's how people memorize 500 questions and still fail.
CEH v11 vs other certs (Security+, PenTest+, CySA+)
Versus CompTIA Security+, CEH v11 is significantly more difficult. Security+ is foundational and broad, while CEH expects deeper technical comfort and more tooling awareness, plus an offensive focus instead of general security concepts.
Versus PenTest+, it's comparable difficulty but different flavor entirely. PenTest+ has more hands-on style questions even though it's still multiple-choice. CEH is purely traditional MC. CEH is broader across topics while PenTest+ tends to feel more "do the pentest process start to finish."
Versus CySA+, CEH feels harder if you're defensive-first because it pushes exploitation and attacker workflows more aggressively, while CySA+ lives more comfortably in detection and response territory.
Versus OSCP, CEH is significantly easier, like not even close. OSCP is a practical grind with real exploitation under time pressure and proof screenshots. CEH is knowledge verification and decision-making.
Versus GIAC GPEN, CEH is slightly easier overall. GPEN gets more technically rigorous in places, even though GPEN being open-book changes prep strategy completely.
CEH v11 exam objectives (domains and what to study)
CEH v11 objectives overview (blueprint summary)
Your north star is the CEH v11 exam objectives document. Print them. Track them. Map everything you study back to them. The CEH blueprint and domains cover recon, scanning, enumeration, system hacking, malware, sniffing, social engineering, DoS, session hijacking, web apps, SQL injection, wireless, mobile, IoT, cloud, cryptography, and operational stuff like methodology and documentation.
It's a lot. That's the point.
High-weight topics to prioritize
Scanning, enumeration, and system hacking are where many candidates either rack up points or bleed out slowly without realizing it. Web app basics matter too. So does networking fundamentals, which people skip because they think "I know networking" and then can't explain why a three-way handshake matters in a SYN flood scenario. DNS. HTTP headers. Ports. Services. Logs. Permissions. If you don't know why SMB signing matters or what a misconfigured S3 bucket implies for data exposure, you're going to feel the exam heating up around question 40.
Tools, techniques, and attack phases covered
Expect the classic phases: recon, weaponization-ish planning, delivery, exploitation, persistence, cleanup. Expect tool recognition across scanners, password attacks, web testing, wireless, and packet analysis. You don't need wizard-level depth, but you do need "I recognize this and can interpret it in context."
Wireshark output. Nmap flags. Hydra vibes. SQLi indicators. Metasploit module selection. You get it.
Prerequisites and eligibility requirements
Official eligibility paths (training vs work experience)
EC-Council typically allows eligibility through official training or via documented security work experience with an application fee. Rules change, so check current policy before you pay for anything.
Recommended prerequisite knowledge (networking, Linux, security basics)
CEH v11 prerequisites, unofficially, are comfort with TCP/IP fundamentals, subnetting basics, DNS resolution, HTTP request-response flow, Windows and Linux fundamentals including file systems and permissions, and baseline security concepts like confidentiality-integrity-availability. If you're shaky here, the exam feels unfair. It isn't. You're just missing the floor everyone else is standing on.
Required documentation (if applying via experience)
If you go the experience route, expect to provide proof of employment and role relevance. Keep it clean and official. HR letters, job descriptions, LinkedIn verification, that kind of thing.
Best CEH v11 study materials (official plus third-party)
Official EC-Council courseware and labs
CEH v11 training courseware is aligned with the exam style and terminology, which matters more than people admit when they're comparing cheaper options. Labs help if you actually do them instead of just clicking "mark complete."
Books, video courses, and notes (what to use and why)
Pick one primary track and one backup reference. A book plus a video course is fine. Ten resources is procrastination in a trench coat pretending to be thoroughness. Notes should be yours, not someone else's dump of facts you'll never internalize.
Hands-on labs and home lab setup (Kali, Windows, vulnerable VMs)
Kali, a Windows client, and a couple intentionally vulnerable boxes gets you 80% of the way for tool familiarity and workflow comfort. Add Burp Suite reps for web testing. Add basic Active Directory abuse concepts if you're aiming beyond entry-level understanding.
CEH v11 practice tests (how to use them effectively)
Best practice test sources (official and reputable alternatives)
Use official practice where you can, then reputable third-party sources with good question explanations. For extra timed reps, 312-50v11 Practice Exam Questions Pack is a cheap pacing tool at $36.99, and yes, pacing matters because reading slow is how people run out of time even when they "know the content."
Practice test strategy (timed sets, review, error log)
Timed sets. Then review. Then an error log with the topic, why you missed it, and the rule you'll remember next time. Do not just re-take until you memorize question 47.
Readiness checklist (target scores before scheduling)
Schedule only after you can hit 80%+ across multiple full exams, with different question pools, while timed. If your score swings wildly between 65% and 85%, you don't understand the material yet, you're pattern-matching.
Study plan (1 to 8 weeks) for the 312-50v11 exam
1-week crash plan (experienced candidates)
You already do the job daily. Spend the week mapping to CEH v11 exam objectives, fixing terminology gaps, and hammering timed questions to get used to EC-Council's phrasing. Lab only for tools you haven't touched recently.
4-week plan (most candidates)
Week 1: networking, recon, scanning. Week 2: enumeration, system hacking, password attacks. Week 3: web apps, wireless, sniffing. Week 4: mixed review, scenario questions, full-length exams, weak-domain repair.
Longer sessions on weekends. Short daily reps during the week. Consistency wins over heroic all-nighters.
8-week plan (career changers or beginners)
Two weeks on foundations that everyone assumes you have. TCP/IP, Linux, Windows basics. Then move into CEH domains with labs every single week, because otherwise it's just vocabulary study and you'll blank on scenario questions. Practice tests start around week 5, not week 1 when you're still learning what enumeration means.
Slow is fine. Random is not.
CEH v11 renewal requirements (maintaining your certification)
Renewal cycle and ECE credits overview
CEH v11 renewal requirements run on EC-Council's ECE credit system across a renewal cycle that's typically three years. You earn credits from training, events, webinars, teaching, and related professional activities.
Fees and timelines (what to renew and when)
There are annual maintenance fees and reporting timelines. Don't ignore them and then act shocked when your cert lapses and you need to re-test.
What counts for renewal (training, webinars, conferences, teaching)
Webinars count. Conferences can count. Teaching can count. Some work activities count if documented properly. Track it as you go, because backfilling a year of credits from memory is miserable.
FAQs (quick answers)
What is the CEH v11 passing score?
The 312-50v11 passing score is scaled and varies by exam form, so plan to be practice-testing at 80%+ consistently before scheduling.
How much does CEH v11 cost all-in?
CEH v11 exam cost depends on voucher, training, and retakes. Budget for the exam plus labs and practice exams, and assume "all-in" is higher than you want it to be.
Is CEH worth it for SOC or pentest roles?
For SOC, it helps you think like an attacker instead of just blocking alerts. For pentest, it's a checkbox cert and a vocabulary builder, not proof you can pop boxes. Still useful, depending on hiring market.
What are the best CEH v11 study materials?
Start with the CEH v11 exam objectives, pair one
CEH v11 Exam Objectives, Domains, and Complete Content Blueprint
Understanding the 312-50v11 CEH v11 exam structure
Real talk.
The ECCouncil 312-50v11 CEH v11 exam isn't just another security cert you cram for and forget. It's actually built around a 20-module structure that follows how real attacks happen, which makes way more sense than those random topic clusters you see elsewhere. Each module builds on the previous one, walking you through the complete lifecycle of a penetration test from the initial recon phase all the way through writing your final report.
The exam objectives align with frameworks you've probably heard about: NIST, NICE, and DoD 8570 requirements. That last one matters if you're targeting government contractor roles or military-adjacent positions. EC-Council updates this thing regularly to keep pace with current threats, so you're not studying outdated attack vectors from 2015.
Here's what trips people up though. The domains aren't weighted equally. Let me clarify that. Some modules represent 5% of your exam while others hit 10% or more. You need to know this distribution before you start studying because spending three weeks on a 5% module while glossing over a 10% domain is not smart.
Module 01 breakdown (5-8% of the exam)
Introduction to Ethical Hacking sets the foundation.
This section covers information security fundamentals, which sounds basic but it's where they test whether you actually understand the difference between vulnerability, threat, and risk. You'd be surprised how many people mix these up under pressure.
The ethical hacking terminology and scope questions are critical. They'll test your knowledge of information security controls across three categories: administrative (policies, procedures), technical (firewalls, encryption), and physical (locks, guards). You need to know which control fits which scenario. Context matters way more than memorization here.
The five hacking phases form the backbone of everything: reconnaissance, scanning, gaining access, maintaining access, and clearing tracks. Every subsequent module circles back to these phases. They'll also test you on hacker types beyond the basic white hat/black hat distinction. Script kiddies, suicide hackers, gray hat operators. Each with different motivations and skill levels.
Cyber kill chain methodology comes up here too. This overlaps with some Module 02 content, but they're testing whether you understand the attacker's perspective from the very first step.
Module 02: Footprinting and reconnaissance (8-10% of exam)
This module carries more weight, and for good reason. Reconnaissance is where most real-world attacks begin, and it's where you'll spend substantial time during actual penetration tests.
Passive versus active reconnaissance is a fundamental distinction they test heavily. Passive techniques leave no trace on target systems. You're gathering intel from third-party sources, public records, social media, DNS registries. Active reconnaissance involves direct interaction with target infrastructure, which creates logs and potential alerts.
Search engine footprinting using Google dorks is huge. You need to know operators like site:, filetype:, inurl:, intitle:, and how to chain them for effective reconnaissance. They might show you search results and ask what operator combination produced them, or give you an objective and ask which dork achieves it. Honestly, mastering this part feels like learning a new language at first, but once it clicks, you start seeing reconnaissance opportunities everywhere. My buddy spent two weeks just practicing Google dorks on random targets and ended up finding exposed configuration files on three Fortune 500 companies. Reported them, obviously.
Website footprinting digs into analyzing site structure, identifying technologies (web servers, frameworks, CMS platforms), and extracting metadata from documents. Tools like Netcraft, Shodan, and various WHOIS services come into play here. Email footprinting covers tracking techniques and harvesting email addresses from public sources, which feeds into later social engineering modules.
DNS footprinting? Critical.
DNS interrogation techniques matter more than most candidates expect. You should understand DNS record types (A, AAAA, MX, TXT, NS, SOA) and how tools like nslookup, dig, and host extract information. Zone transfers, DNS cache snooping, reverse DNS lookups are all fair game.
Network footprinting using traceroute and similar tools rounds out this domain. They test whether you can interpret traceroute output, understand TTL values, and identify network topology from trace results.
How the complete blueprint connects
The remaining 18 modules follow this same attack lifecycle progression. After reconnaissance, you move into scanning and enumeration (Module 03), then vulnerability analysis (Module 04). From there you get into system hacking, malware threats, sniffing, social engineering, denial of service, session hijacking, and so on. It's a complete path through the offensive security space.
Each module builds practical scenarios on top of theoretical knowledge. They might show you nmap output and ask what flags were used, or present a Wireshark capture and ask what attack you're witnessing. The exam leans hard on recognizing tools by their output, understanding when to use specific techniques, and identifying appropriate countermeasures.
The 312-50v11 exam covers approximately 125 questions in a four-hour window, though the exact count varies slightly. You need 70% to pass in most cases, but EC-Council uses scaled scoring so the actual passing threshold adjusts based on question difficulty. They don't publish exact cut scores, which is annoying but standard for adaptive-style exams.
Connecting to the broader certification path
CEH v11 sits in an interesting position within EC-Council's certification ecosystem. It's more advanced than the 212-82 Certified Cybersecurity Technician but less specialized than credentials like the 312-39 Certified SOC Analyst or 312-85 Certified Threat Intelligence Analyst.
If you're planning a penetration testing career path, CEH v11 typically comes before the 412-79v10 EC-Council Certified Security Analyst, which takes you deeper into advanced penetration testing methodologies. For forensics folks, the 312-49v10 Computer Hacking Forensic Investigator builds on CEH foundations but focuses on evidence collection and analysis.
One thing worth mentioning: EC-Council released 312-50v12 and more recently 312-50v13, but v11 remains valid and many organizations still specifically require it. The core concepts don't change dramatically between versions, though newer editions add emerging technologies and update tool references.
What the objectives really test
Beyond memorizing module content, the exam tests your ability to think like both attacker and defender. You'll see questions that present a scenario and ask what the attacker would do next, or what defensive measure would most effectively counter a specific threat.
The practical application scenarios matter more than pure memorization. Way more. Sure, you need to know definitions and concepts, but they're testing whether you can apply that knowledge in real situations. Can you look at a network diagram and identify the weakest entry point? Can you recommend appropriate security controls based on a threat model? Can you interpret tool output and determine what happened?
Small details matter.
Understanding the complete penetration testing methodology from reconnaissance through reporting means you'll face questions spanning the entire engagement lifecycle. They might jump from a reconnaissance question to a post-exploitation scenario to a reporting question, testing whether you understand how these phases connect in real engagements.
The exam blueprint demands both depth and breadth. You can't just master two modules and hope for the best. You need solid coverage across all 20 domains, with extra focus on the higher-weighted sections like reconnaissance, system hacking, web application attacks, and wireless security.
Conclusion
Not gonna lie here.
The ECCouncil 312-50v11 CEH v11 exam looks terrifying on paper, but once you actually sit down, break it into digestible chunks, and commit to a real study plan that doesn't involve just skimming PDFs the night before, it becomes totally manageable and way less scary than your brain's making it out to be. The CEH v11 exam objectives cover tons of ground. Reconnaissance, scanning, system hacking, malware threats, web app attacks, the whole nine yards. But that's honestly the entire point of it. It's testing whether you've got the ethical hacking certification exam mindset down and can think like an attacker (without, y'know, actually becoming one and ending up on the wrong side of some very serious legal consequences).
The CEH v11 difficulty level?
That really depends on your background. If you've already spent time doing SOC work or pentesting gigs, you'll recognize a lot of this stuff and might even find sections kinda familiar. But if you're newer to security, the sheer breadth can feel brutal at first. You're trying to memorize tool flags, attack phases, exploitation techniques, and understand the "why" behind each method, which honestly gets messy fast. That's where quality CEH v11 study materials and a solid, structured plan make all the difference. You can't just skim the official EC-Council CEH 312-50 courseware once and hope muscle memory kicks in during the exam.
The CEH v11 exam cost isn't cheap. We're talking around $950 just for the voucher alone, more if you bundle it with training options. You definitely want to pass on your first attempt and not hemorrhage money on retakes. Understanding the 312-50v11 passing score helps with planning: you need somewhere between 60-85% depending on which question set you get, but honestly? Aiming for "just barely passing" is a recipe for disaster and disappointment. You want to be consistently hitting 85%+ on CEH v11 practice tests before you even think about scheduling the real thing.
And speaking of practice tests, look, they're critical.
The Certified Ethical Hacker v11 exam isn't just about knowing concepts in some abstract, theoretical way. It's about recognizing scenarios quickly, eliminating obviously wrong answers under serious time pressure, and making smart decisions when two options look weirdly similar. That's a skill you build through repetition and exposure, not cramming. I spent way too long early on trying to "understand everything perfectly" when really I should've been drilling questions until patterns started clicking. Burned probably three weeks that way before I figured it out. If you're serious about passing and want questions that actually mirror what you'll see on exam day (not some outdated garbage from 2015), check out the 312-50v11 Practice Exam Questions Pack at /eccouncil-dumps/312-50v11/. It's one of the better resources out there for getting that realistic test experience without burning through expensive retake fees.
Don't forget the CEH v11 renewal requirements either. You'll need 120 ECE credits every three years to keep the cert active and current. But honestly? Cross that bridge when you get there. Right now, just focus on passing, getting that cert on your resume, and opening doors to better opportunities.
You've got this.
Show less info
Comments
This exam is designed to assess individuals’ knowledge and skills in configuring advanced 312-50v11 Exam Dumps Windows Server 2012 services, such as Hyper-V, clustering, and IP address management.
They provide an effective way to practice for 312-50v11 Exam Dumps the exam and familiarize
Hot Exams
Related Exams
Certified Network Defender (CND)
Certified EC-Council Instructor (CEI)
EC-Council Certified Security Specialist (ECSS) v10
Disaster Recovery Professional Practice Test
Ethical Hacking and Countermeasures V8
EC-Council Information Security Manager (E|ISM)
EC-Council Certified Security Analyst (ECSA)
Certified Ethical Hacker Exam
EC-Council Certified Encryption Specialist (ECES)
EC-Council Certified Secure Programmer (ECSP)
EC-Council Certified CISO (CCISO)
Computer Hacking Forensic Investigator
Certified Ethical Hacker CEH v11
Certified SOC Analyst (CSA)
Computer Hacking Forensic Investigator (CHFI-v10)
Certified Threat Intelligence Analyst (CTIA)
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.