EC-Council 212-81 (ECES) Certification Overview and Value Proposition
The EC-Council Certified Encryption Specialist (ECES) sits in this interesting space where it's super specialized but also incredibly practical. Everyone talks about encryption like it's this mysterious black box, but ECES actually forces you to understand what's happening under the hood. You can't just wave your hands and say "it's encrypted" anymore. This certification validates your expertise in cryptography fundamentals and encryption technologies through the EC-Council 212-81 ECES exam, and it's one of those credentials that immediately tells employers you know your stuff with protecting data.
Industry recognition meets real-world application
Look, ECES is vendor-neutral. That matters more than people realize. The thing is you're not learning how to click through some proprietary interface. You're learning symmetric vs asymmetric encryption, PKI and digital certificates, hashing and digital signatures, and encryption algorithms AES RSA ECC. The certification covers the foundational concepts that apply whether you're working in AWS, Azure, on-prem data centers, or some hybrid nightmare scenario that keeps everyone up at night.
Practical application wins here. You won't spend weeks proving mathematical theorems (thank god), but you'll learn how to actually implement encryption controls that work in production environments where things break at 3 AM and executives want answers. Part of EC-Council's specialized certification portfolio alongside CEH, CHFI, and other security credentials, ECES carves out its own niche for professionals who need deep expertise in data protection.
Who actually benefits from pursuing this certification?
Information security analysts implementing encryption controls in enterprise environments are the obvious candidates, right? But I've seen network administrators securing data in transit across corporate networks get massive value from this too. Suddenly they understand why certain protocols matter and how key management actually works instead of just following documentation blindly because their manager told them to.
Compliance officers ensuring regulatory requirements (GDPR, HIPAA, PCI-DSS) for data protection need this knowledge desperately. Not gonna lie, I've sat in meetings where compliance folks couldn't explain the difference between encryption at rest versus in transit, which makes audits painful for everyone involved and turns simple questions into hour-long tangents about documentation nobody can find. My previous manager once spent twenty minutes trying to explain TLS to a room of executives using a metaphor about locked briefcases that somehow made everyone more confused than when he started. Cloud security engineers protecting data in multi-tenant cloud environments find ECES particularly relevant since cloud providers give you encryption tools but expect you to understand how to use them properly.
Security consultants? They can charge more. When you've got verified credentials backing up your recommendations, clients actually listen instead of nodding politely then doing whatever their CIO's nephew suggested. Penetration testers needing to understand encryption vulnerabilities and proper implementation benefit too. You can't effectively test what you don't understand, which seems obvious but you'd be surprised how many pentesters struggle with crypto weaknesses.
IT auditors assessing cryptographic controls in organizational security programs round out the target audience, along with career changers entering cybersecurity with focus on data protection specialization. It's a solid entry point if you're transitioning from general IT.
Career impact and salary expectations
Encryption specialist positions? We're talking average salaries ranging $75,000 to $125,000 depending on experience. That's solid earning potential, though the wide range reflects geographic location, industry sector, and whether you're working for a startup burning through VC money or an established enterprise with actual budgets and processes.
Cryptography engineer roles pay well. Financial services, healthcare, and government sectors tend toward the higher end because the stakes are higher. Screw up encryption in healthcare and you're dealing with HIPAA violations that can shut down organizations and make the evening news. Security architect positions requiring encryption design and implementation expertise value ECES because it demonstrates you've gone beyond surface-level security knowledge into something actually useful.
Compliance analyst roles focused on data protection and privacy regulations increasingly list encryption certifications as preferred or even required qualifications. Differentiation in competitive job markets through specialized encryption knowledge matters when you're competing against candidates who only have generalist certifications like Security+ or even the Certified Ethical Hacker which, don't get me wrong, is valuable but covers a different skillset entirely.
Foundation for advanced work? ECES can be a stepping stone to more advanced work in blockchain, quantum-resistant cryptography, and zero-trust architectures. All the buzzwords executives love but need actual technical people to implement. These emerging technologies all depend on solid encryption fundamentals, and employers know that ECES holders have those fundamentals locked down.
How ECES fits within EC-Council's certification ecosystem
Complementary to CEH (Certified Ethical Hacker) for full security knowledge makes sense when you think about it. CEH focuses on offensive security and finding vulnerabilities, while ECES focuses on defensive security and data protection. It's the yin and yang of cybersecurity, I guess? Natural progression after EC-Council Security Analyst (ECSA) or alongside CHFI creates interesting certification paths depending on your career goals and frankly how much your employer's willing to spend on professional development.
Specialized track for professionals. You can pursue it independently or as part of broader EC-Council certification portfolio, which gives you flexibility based on budget and time constraints. Because let's be honest, not everyone has unlimited PTO to sit in bootcamps. Recognized by employers seeking candidates with verified encryption expertise, ECES carries weight in job applications and promotion discussions.
fits with industry demand. The market increasingly rewards depth in specific domains rather than collecting every generalist cert under the sun. Someone who holds both CEH and ECES signals they understand both offensive and defensive sides of cryptography, which is valuable for security architect and senior security engineer roles where you need to think about attacks AND defenses at the same time.
Why ECES matters in 2026's security space
Data breaches aren't slowing down. Every major breach report highlights failures in encryption implementation, not because the algorithms are weak, but because organizations don't properly manage keys, apply encryption inconsistently, or use outdated protocols while claiming everything's "encrypted" in board meetings.
Post-quantum cryptography preparations? That's becoming urgent. NIST has standardized quantum-resistant algorithms, and organizations need professionals who understand both current encryption technologies and migration paths to quantum-safe alternatives before quantum computers make current encryption look like a screen door on a submarine. Zero-trust security models emphasizing encryption everywhere principles make ECES knowledge fundamental rather than optional. You can't implement zero-trust without understanding how to encrypt data at every layer, which seems obvious but requires actual technical depth.
Cloud migration headaches. Multi-cloud and hybrid environments create constant challenges because each provider handles encryption slightly differently and expects you to know what you're doing. Privacy regulations worldwide mandating encryption for sensitive personal data mean compliance teams desperately need people who can implement and verify encryption controls rather than just checking boxes on spreadsheets.
Remote work isn't disappearing. End-to-end encryption for communications and data access has shifted from "nice to have" to "absolute requirement" for most organizations. IoT and edge computing creating new encryption implementation challenges means the skill set keeps expanding. Suddenly you're encrypting data on devices with minimal processing power and intermittent connectivity, which presents unique problems traditional enterprise encryption never dealt with.
The 212-82 CCT and 312-39 CSA certifications complement ECES by covering adjacent security domains, but none of them dive as deep into encryption specifics. That specialization is exactly what makes ECES valuable. It's not trying to cover everything like some certifications that end up being a mile wide and an inch deep, it's making you really competent in one critical area that touches every aspect of modern security.
Understanding the EC-Council 212-81 ECES Exam Structure and Requirements
What this exam is, in plain terms
The EC-Council 212-81 ECES exam tests the knowledge you'll need for the EC-Council Certified Encryption Specialist (ECES) credential. It covers cryptography basics, how encryption actually works in production environments, and the disasters that happen when organizations botch key management. This isn't a coding test. It's not penetration testing either. Think of it more like "do you actually understand what AES/RSA/ECC do under the hood, and can you pick the right solution without torpedoing your infrastructure."
Narrower than CEH. More targeted than Security+. Way more hands-on than you'd think.
What ECES is, and why anyone takes it
EC-Council Certified Encryption Specialist (ECES) targets security analysts, sysadmins, network engineers, application teams, and auditors who constantly face encryption choices and don't wanna fumble through technical discussions anymore. I mean, if your daily work involves TLS configurations, database encryption settings, those "should we build our own crypto" debates, or compliance inquiries about PKI and digital certificates, this credential basically gives you fluent technical vocabulary with real credibility.
The thing is, it's also a solid differentiator for people starting security careers because it makes you articulate clearly about symmetric versus asymmetric encryption, hashing and digital signatures, and how key rotation and revocation function beyond theoretical scenarios.
Who should take the 212-81 exam
You're the one who hears "is this data encrypted at rest and in transit" and responds with uncertain silence? This exam's calling your name. If you touch IAM systems, zero trust implementations, VPNs, certificates, or cloud KMS platforms, you'll recognize tons of the 212-81 exam objectives even if you've never labeled them that way.
Honestly, if you want pure career ROI for getting past HR keyword filters, this one's definitely more specialized. But specialized isn't bad. Encryption's literally everywhere, and organizations keep searching for "understands PKI" like it's some mythical ability.
Exam format and delivery details you should know
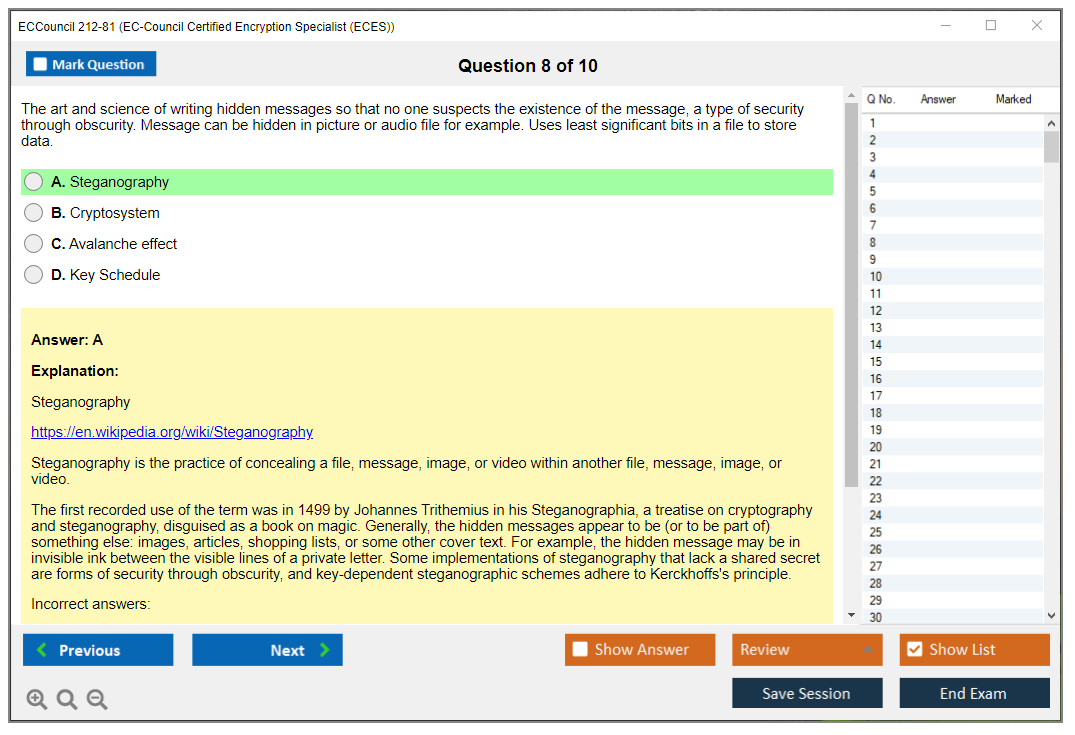
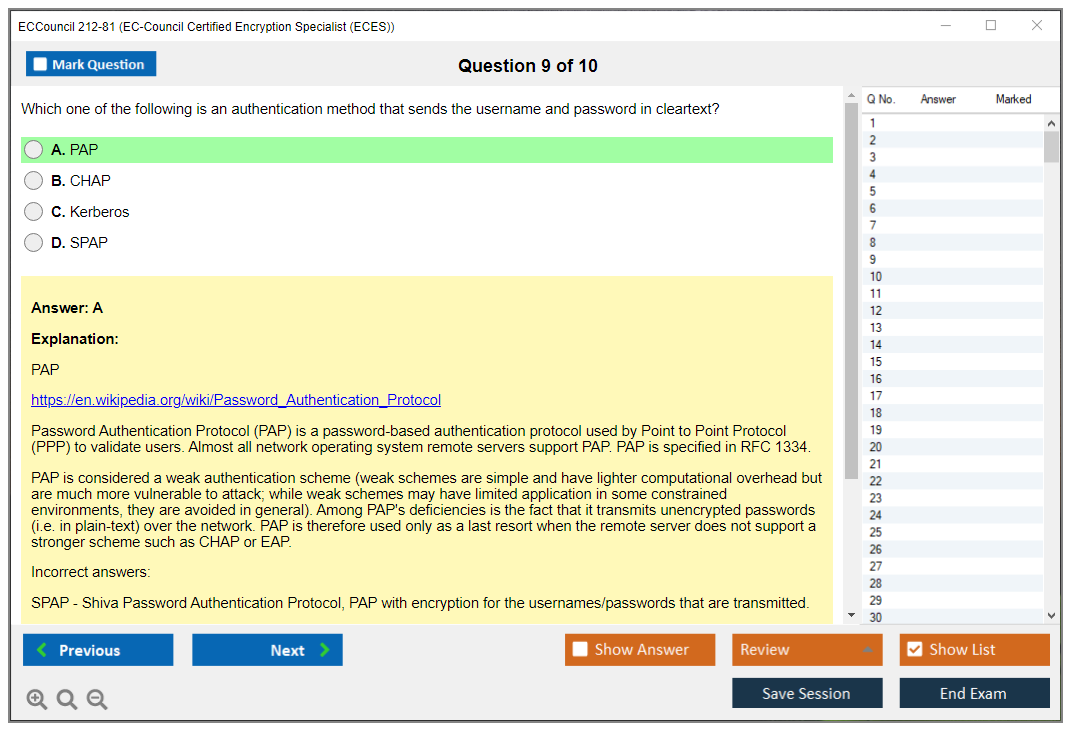
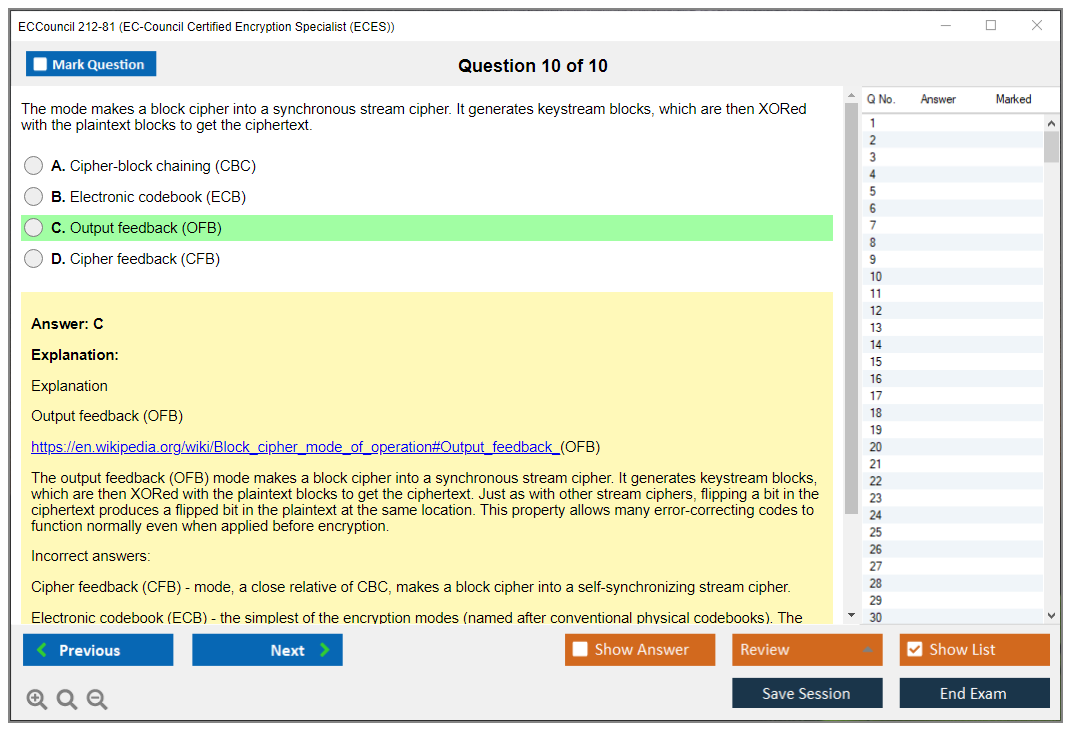
Multiple-choice format. The tricky part? Questions blend theory with scenario-based thinking, so you're not just regurgitating crypto definitions. You're applying knowledge to realistic situations like selecting between encryption algorithms AES RSA ECC, or identifying when hashing and digital signatures address completely different security challenges.
Standard length runs 50 to 75 questions, though you should confirm current numbers with EC-Council since exam vendors adjust question counts and formats more frequently than they publicize. Two hours total. That's 120 minutes. Enough time if you've practiced reading questions carefully, but tight if you're figuring things out mid-exam and questioning every technical abbreviation.
Delivery happens through computer-based testing at Pearson VUE testing centers globally. There's an online proctored version for remote convenience too, which sounds perfect until you discover online proctoring's incredibly particular about your environment, webcam positioning, and whether your housemate's cat decides to make a cameo appearance. I once watched someone get flagged because their desk lamp kept reflecting off their glasses in a way the software thought was suspicious. Took fifteen minutes to sort out while the exam clock kept ticking.
Non-adaptive structure. That's important. Question difficulty stays constant throughout your session, so you won't face progressively harder material just because you're performing well. Also, no bathroom breaks allowed during testing, so arrive properly hydrated but not recklessly so. Strategic fluid management matters.
212-81 exam cost, what you actually pay for, and the sneaky extras
The 212-81 exam cost typically falls between $250 to $350 USD for a standard voucher, with geographic pricing differences. Certain regions see inflated totals after taxes or local processing fees, so don't expect your colleague's price matches yours.
Your exam fee normally covers one testing attempt and an official score report. That's everything. No bundled ECES study materials, no official lab access, no practice environment credentials. Candidates assume vouchers include extras. They rarely do.
Cost options I've watched people overlook:
- Retake vouchers cost less when bought alongside your initial exam, which makes sense if you prefer having a backup plan
- Training packages combine official courseware with exam vouchers at bundled rates, and while I'm not pushing training here, the package occasionally works out financially if your employer's covering costs and wants consolidated billing
- Corporate volume pricing exists for companies certifying multiple staff members, but you'll need procurement involved to inquire, since it's not prominently advertised on consumer pages
Additional expenses escalate quickly. Optional official training can reach $1,000 to $2,500, third-party books and ECES study materials typically cost $50 to $200, and ECES practice tests commonly run $30 to $100 based on depth and explanation thoroughness. Visit the EC-Council site for current pricing and promotions, since voucher discounts appear and disappear.
Passing score and how scoring works
The 212-81 passing score usually sits around 70%, which means roughly 35 to 53 correct responses depending on whether your exam version contains 50 or 75 questions. Again, confirm the actual question total, because your "how many mistakes can I afford" calculation depends entirely on it.
EC-Council might adjust thresholds based on exam difficulty and psychometric evaluation. Sounds sophisticated, but here's what matters: don't view 70% as a comfortable buffer. Target higher scores, since your specific exam version might prove tougher than whatever practice materials you studied.
Scoring follows straightforward right-or-wrong logic per question. Zero partial credit. You'll typically receive a pass/fail result immediately at the testing facility, and score reports usually break down performance by domain so you'll see where you excelled or struggled badly. That domain-level feedback's really helpful if you need retaking because it reveals whether your weakness involves PKI and digital certificates, key lifecycle processes, or foundational cryptography fundamentals like symmetric versus asymmetric encryption.
Retake policy and attempt limits
Failed attempts? There's normally a mandatory waiting period before retesting, often 7 to 14 days depending on current policy versions. There's generally no strict cap on total attempts, but each try requires new exam fee payment, so unlimited retakes get financially painful quickly.
Your retake won't duplicate your original exam exactly. It pulls from the identical overall question bank, but your specific question selection changes. Helps because you're less tempted to memorize answers. Hurts because you can't rely on encountering identical weak areas.
One detail candidates forget: your most recent attempt becomes your official recorded score. So don't retake casually "just to see if I score better" unless you're confident you'll actually improve.
Exam day requirements and what to bring
Testing facilities enforce strict rules. Two government-issued IDs represent the standard requirement, with at least one displaying photo and signature. Show up 15 to 30 minutes early for check-in procedures, since Pearson VUE administrative processes move slowly sometimes, and tardiness can mean forfeiting your appointment.
Zero personal belongings in testing areas. Phones, bags, watches, study notes. Everything gets secured. The facility supplies scratch paper or a whiteboard with marker for quick calculations or working through concepts like key sizes and where hashing fits versus encryption.
Dress in comfortable layers. Testing room temperatures vary dramatically. Some feel like refrigerators. Others get unexpectedly warm. Either way you don't want "I'm uncomfortable" becoming why you missed a question about PKI and digital certificates.
For online proctored sessions, you'll need a quiet private location, functioning webcam, stable internet connection, and your government identification. You'll perform an environmental scan, and you'll face continuous monitoring. Complete the system compatibility check beforehand with the required browser and permissions settings, because troubleshooting moments before starting is how candidates waste money on exam vendors.
What the exam objectives usually cover
The 212-81 exam objectives focus on practical crypto comprehension. Expect cryptography fundamentals, symmetric versus asymmetric encryption, and standard topics like encryption algorithms AES RSA ECC. Hashing and digital signatures appear frequently, particularly where test-takers confuse integrity protection with confidentiality measures.
PKI and digital certificates carry significant weight. So does key management lifecycle work: generation, storage, distribution, rotation, backup procedures, revocation processes. If you can't articulate why key storage decisions outweigh cipher selection in most organizations, you'll struggle here.
Secure protocols and applications matter equally. TLS fundamentals. VPN architecture. Database and disk encryption approaches. Email encryption frameworks. Practical stuff you encounter professionally.
Prereqs, renewal, and the stuff people ask on Google
212-81 exam prerequisites lean more toward "recommended background experience" than rigid entry barriers, so you can attempt it without extensive crypto expertise. But you'll want foundational networking and security knowledge, plus enough mathematical comfort to stay calm when encountering discussions of entropy or key lengths.
ECES certification renewal exists within the EC-Council framework, and specifics can shift, so verify current ECE/CEU requirements and associated fees on the official website. Don't assume "I passed once so I'm certified forever." That's how credentials silently lapse.
Quick answers to the common questions
What is the EC-Council 212-81 (ECES) exam and who should take it? Professionals needing functional knowledge of encryption, PKI, and key management for security, IT operations, compliance, or engineering positions.
How much does the 212-81 ECES exam cost? Usually $250 to $350 USD for a voucher, plus optional training and supplemental study resources.
What is the passing score for the ECES (212-81) exam? Typically around 70%, with scoring methodologies and thresholds subject to EC-Council's modifications.
How hard is the ECES exam and how long should I study? If crypto's unfamiliar territory, plan weeks rather than days, since the concepts build progressively and questions reward precision over general understanding.
What are the best ECES study materials and practice tests? Official courseware if you want the vendor perspective, combined with reputable third-party crypto resources and practice exams with detailed explanations, since explanation quality transforms wrong answers into corrected understanding.
Full 212-81 Exam Objectives and Domain Breakdown
Cryptography isn't abstract anymore. It's literally everywhere in IT, and the EC-Council 212-81 ECES exam breaks down exactly what you need to know about encryption in the real world. We're talking about actual objectives that matter when you're implementing crypto systems, not just theory that sounds impressive in textbooks.
What makes this exam different from other security certs
Real talk here. The 212-81 exam objectives focus exclusively on encryption and cryptographic systems, which is pretty intense. Unlike broader security certs like the 312-50v13 (Certified Ethical Hacker Exam (CEHv13)) or 212-82 (Certified Cybersecurity Technician (CCT)) which touch on everything, ECES goes deep on crypto. You're expected to understand not just what AES or RSA is, but when to use which algorithm, why key sizes matter, and how to spot implementation flaws that make theoretically strong encryption completely useless in production environments.
The seven domains? They're wild. You need to understand classical ciphers and how cryptanalysis evolved, then jump to AES-256 in GCM mode for authenticated encryption. That range is honestly pretty insane.
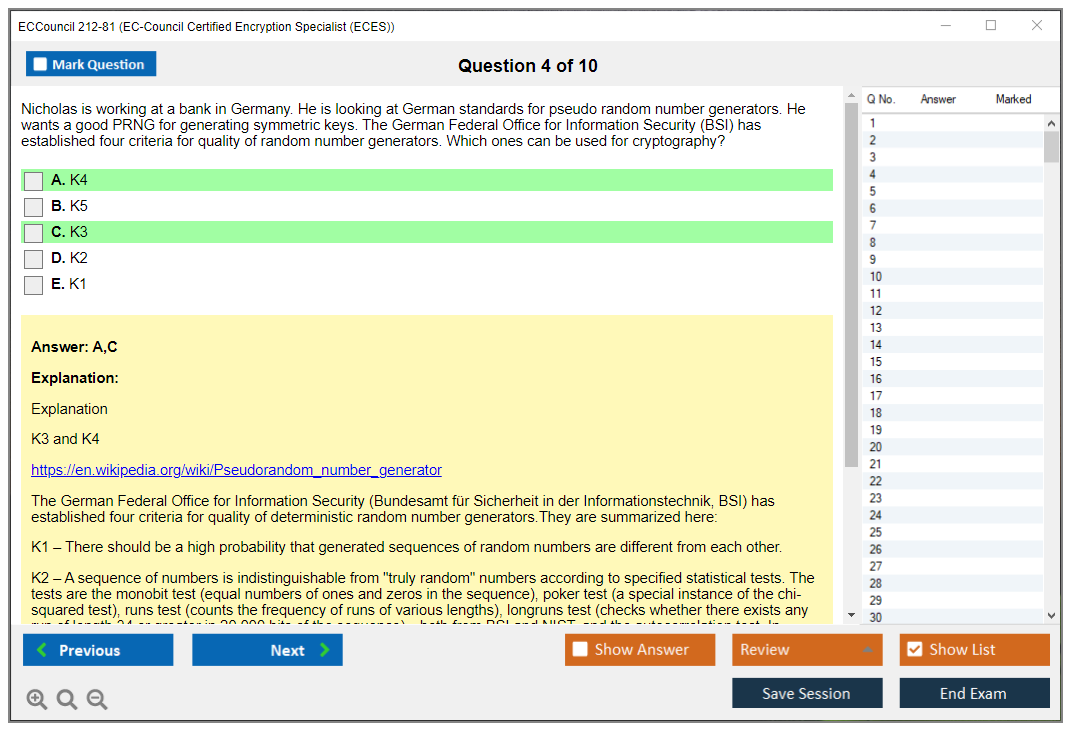
Cryptographic foundations that actually matter
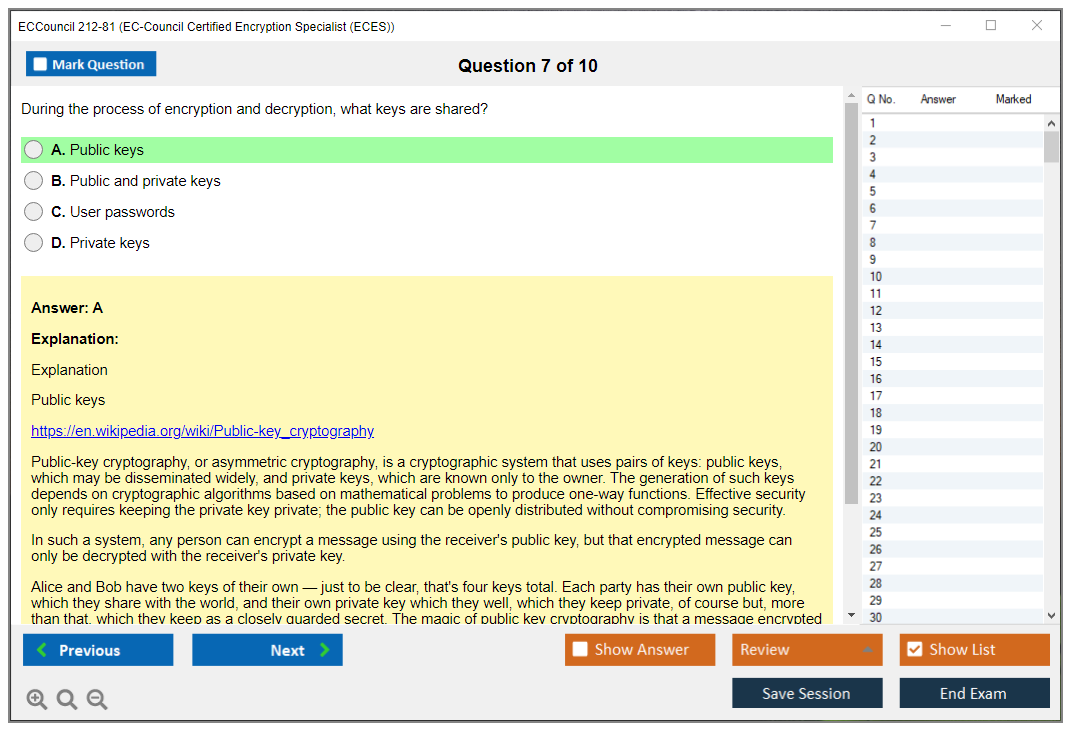
Domain 1 establishes conceptual groundwork. This is where loads of people stumble because they want to skip to "the cool stuff" like cracking encryption. But understanding symmetric versus asymmetric encryption at a fundamental level (not just "one uses one key, one uses two") is key. The thing is, you need to know why symmetric encryption's faster but requires secure key distribution, while asymmetric solves distribution but introduces computational overhead that can cripple performance if you're not careful.
The cryptographic principles aren't buzzwords. Confidentiality keeps data secret. Integrity ensures it hasn't been tampered with. Authentication proves who created it, and non-repudiation means they can't deny it later. These four concepts drive every crypto decision you'll make in production systems.
Kerckhoffs's principle? It basically says your encryption should remain secure even if everyone knows how it works. Only the key should be secret, which is why we use published algorithms like AES instead of "security through obscurity" nonsense. The exam tests whether you actually understand this or just memorized definitions from some outdated textbook.
Computational security versus information-theoretic security is a practical distinction that matters. Most systems use computational security. Breaking AES-256's theoretically possible but would take longer than the universe's age with current tech. Information-theoretic security like one-time pads is mathematically unbreakable but totally impractical for most use cases, which is frustrating but true.
Block ciphers and why mode selection breaks implementations
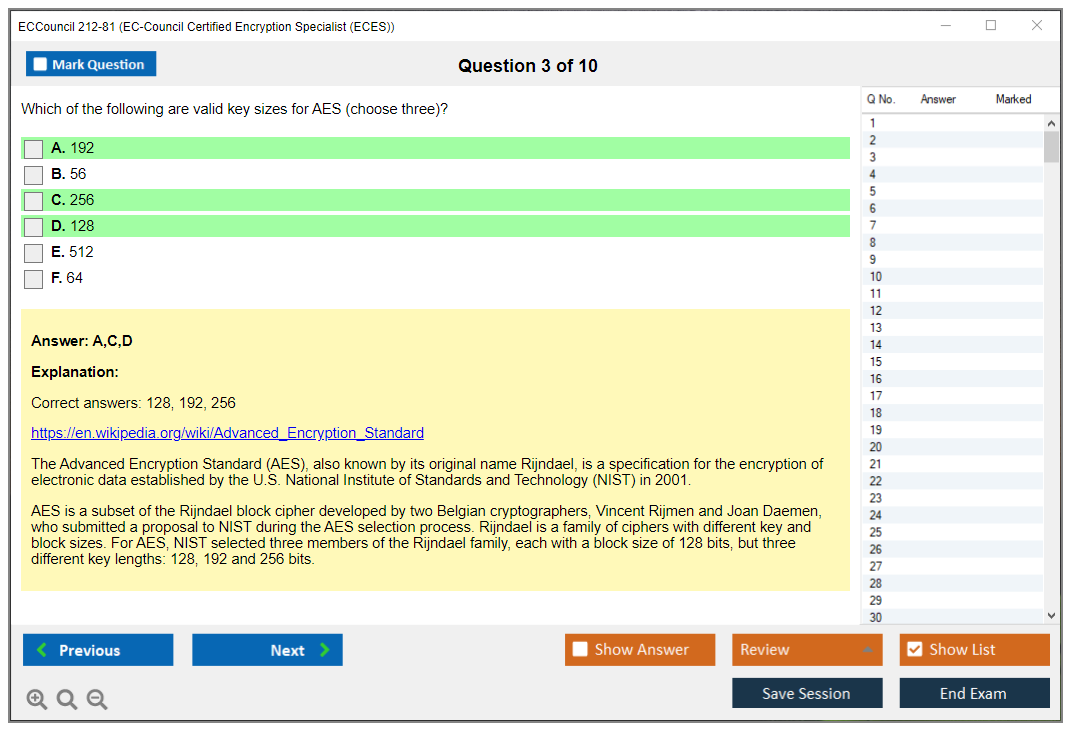
Domain 2 gets into symmetric encryption algorithms, and this is where the 212-81 Practice Exam Questions Pack becomes invaluable because you need to know specific implementation details that'll trip you up. AES with 128, 192, or 256-bit keys isn't just "bigger numbers are better." The security implications change. Performance changes. And compliance requirements might mandate specific key sizes depending on your industry.
Block cipher modes? Here's where I see the most real-world failures. ECB mode's insecure for almost everything because identical plaintext blocks produce identical ciphertext blocks. You can literally see patterns in encrypted images, which is terrifying. CBC requires an IV and chains blocks together. CTR turns a block cipher into a stream cipher. GCM provides authenticated encryption, which is what you actually want for most modern applications because it gives you both confidentiality and integrity in one operation, saving computational resources.
Initialization vectors confuse people. An IV prevents the same plaintext from producing the same ciphertext when encrypted with the same key multiple times. Without proper IV usage, attackers can spot patterns. The IV doesn't need to be secret, but it must be unpredictable and never reused with the same key for certain modes, or you're basically handing attackers the keys.
Stream ciphers like RC4 (now deprecated, thankfully) and ChaCha20 encrypt data bit-by-bit or byte-by-byte. They're fast and work well for streaming data, but RC4 has known vulnerabilities that make it dangerous. ChaCha20's what modern systems use, especially in environments where AES hardware acceleration isn't available.
Public key cryptography and the quantum threat
Domain 3 covers asymmetric encryption. Conceptually harder for most people, I'll admit. RSA's mathematical foundations involve prime factorization. Multiplying two large primes is easy. Factoring the result is computationally infeasible, which is the entire security model. Key generation, encryption, and decryption all rely on modular exponentiation, and you need to understand the process enough to explain why 2048-bit RSA's the current minimum recommendation in most security frameworks.
Elliptic Curve Cryptography? It provides equivalent security with much smaller key sizes, which is brilliant. A 256-bit ECC key offers similar security to a 3072-bit RSA key, which means faster operations and smaller certificates. This matters for mobile devices and IoT where computational resources are limited and every millisecond counts.
Diffie-Hellman key exchange lets two parties establish a shared secret over an insecure channel without ever transmitting the secret itself. Forward secrecy means that even if your long-term private key's compromised, past session keys remain secure because they were ephemeral. This is why modern TLS uses ECDHE variants instead of static RSA key exchange.
The quantum computing threat? It's real and coming faster than most people think. Shor's algorithm can break RSA and ECC on sufficiently powerful quantum computers, which keeps security folks up at night. Post-quantum cryptography candidates are being standardized now, and the exam expects you to understand why organizations need migration strategies. You can't just wait until quantum computers exist. Encrypted data captured today could be decrypted later, what security people call "harvest now, decrypt later" attacks.
I was reading about a major bank that's already budgeting for post-quantum migration even though practical quantum computers are still years away. That's how serious this threat is. They're treating it like Y2K but with actual teeth.
Hashing isn't encryption and signatures prove more than you think
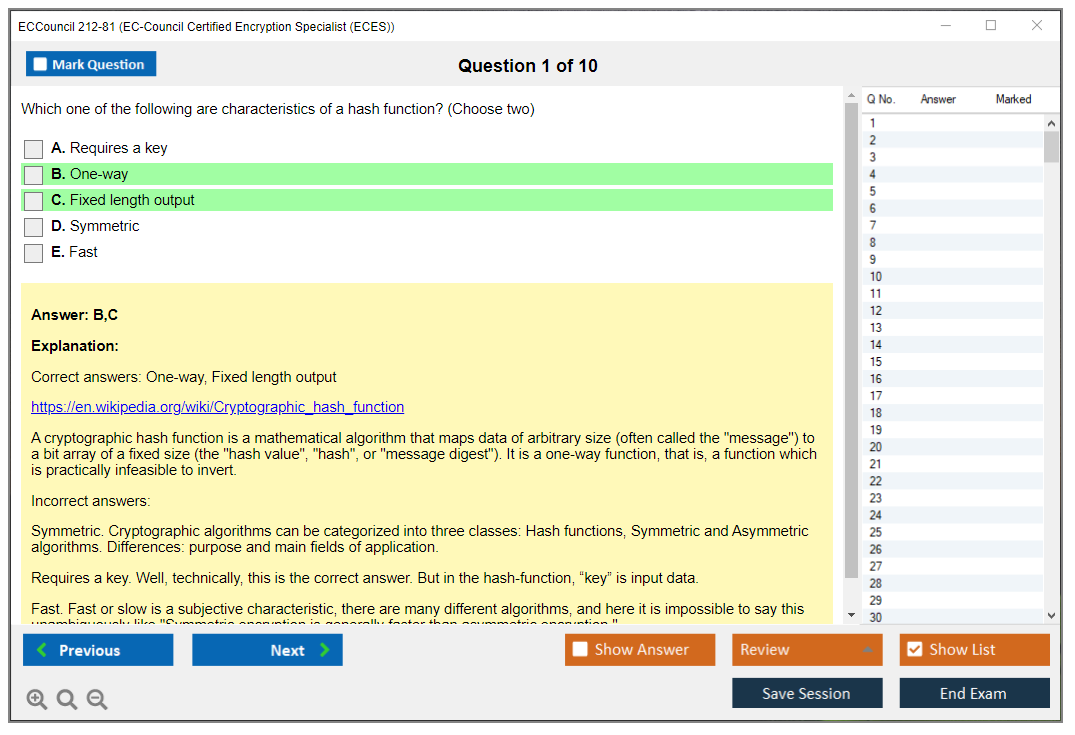
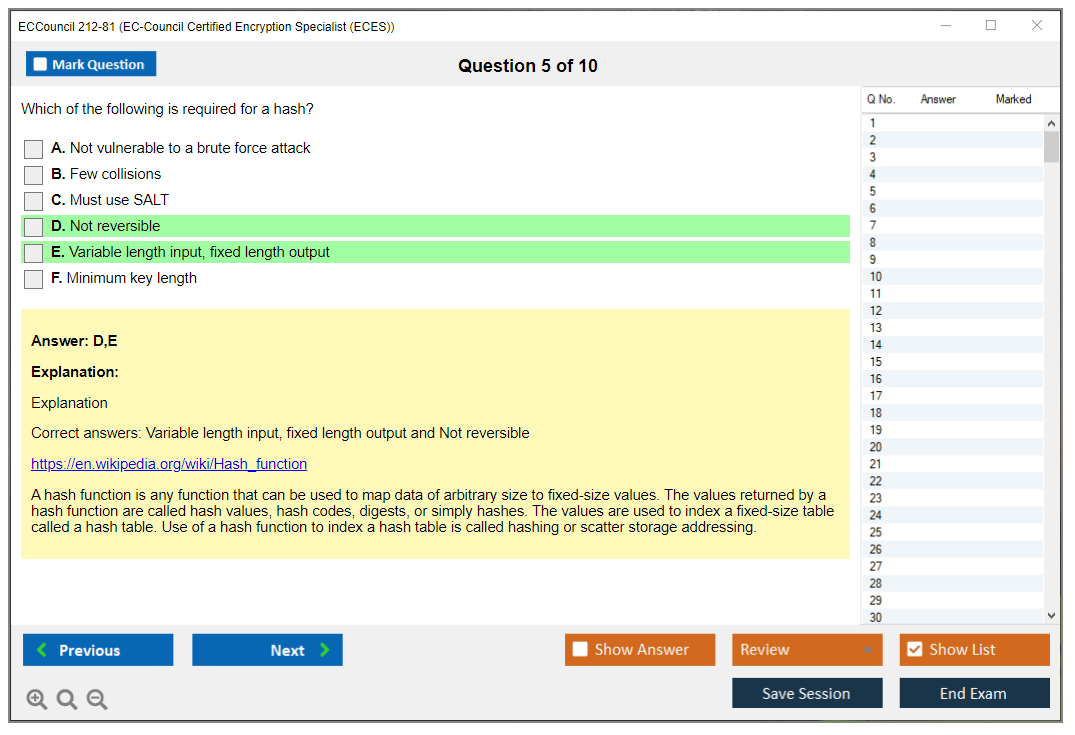
Domain 4 distinguishes hashing from encryption, which trips up beginners constantly. Hash functions are one-way. You can't decrypt a hash back to the original data, period. SHA-256 produces a 256-bit output regardless of input size. Collision resistance means finding two inputs with the same hash is computationally infeasible. Pre-image resistance means you can't work backward from a hash to find an input that produces it, which is fundamental to security.
HMAC combines a hash function with a secret key. It provides integrity and authentication. You know the message wasn't tampered with and it came from someone with the key.
Digital signatures? They use asymmetric cryptography to prove authenticity and non-repudiation in ways that hold up legally. You hash the message, encrypt the hash with your private key, and anyone with your public key can verify it came from you. RSA signatures, DSA, and ECDSA are the main algorithms, each with different performance and security characteristics that matter in specific contexts.
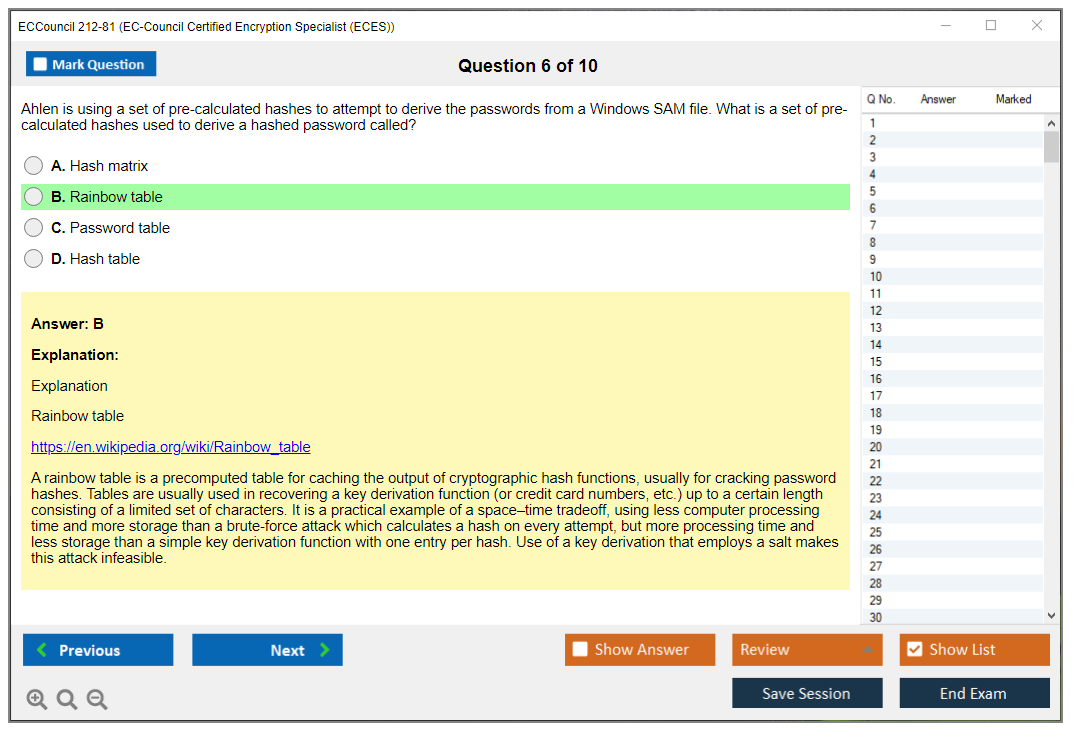
Password hashing's its own specialty. You never store passwords in plaintext or even encrypted. You hash them with algorithms designed to be slow, which sounds counterintuitive but makes sense. Bcrypt, scrypt, and Argon2 are purpose-built for passwords because they're computationally expensive, which makes brute-force attacks impractical even with modern GPU farms. Salting adds random data before hashing to prevent rainbow table attacks that'd otherwise compromise databases instantly.
PKI is the trust infrastructure nobody thinks about until it breaks
Domain 5 covers Public Key Infrastructure, which is one of those things that works invisibly until something goes catastrophically wrong. Certificate Authorities form a hierarchy. Root CAs at the top, intermediate CAs below them, and end-entity certificates at the bottom. Your browser trusts a few dozen root CAs, which is how it trusts millions of websites without individually verifying each one.
X.509 certificates contain the subject (who owns it), issuer (who signed it), validity period, public key, and signature. The entire internet runs on this structure, which is both impressive and slightly terrifying when you think about it. When you visit an HTTPS site, the server presents its certificate, your browser verifies the signature chain back to a trusted root, checks that it hasn't expired or been revoked, and establishes an encrypted connection.
Certificate revocation's messy in practice. CRLs are lists of revoked certificates that can get huge and require frequent downloads, which creates bandwidth issues. OCSP queries a responder in real-time but creates privacy concerns and single points of failure. OCSP stapling lets the server prove its certificate's valid, which is faster and more private, though adoption's still not universal.
Key management is where security actually lives or dies
Domain 6 might be most important from a practical standpoint. You can use AES-256 all day long, but if your key's "password123" or stored in plaintext in your source code, you've accomplished nothing except creating a false sense of security that's arguably worse than no encryption at all.
Key generation needs proper entropy sources. Weak random number generators have broken supposedly secure systems in embarrassing ways historically.
Hardware Security Modules provide tamper-resistant key storage and cryptographic operations. They're expensive but necessary for high-security environments. Cloud KMS services like AWS KMS or Azure Key Vault offer HSM-backed key management without buying physical hardware, which makes sense for most organizations. The exam covers when each approach makes sense based on threat models and compliance requirements.
Key rotation policies define how often keys should be changed, which varies wildly by use case. Cryptographic best practices recommend rotating symmetric keys periodically and after any suspected compromise. Asymmetric keys might rotate less frequently but need rotation schedules too, especially for long-lived certificates.
Key escrow and recovery mechanisms let authorized parties recover encrypted data if keys are lost. This is critical for business continuity but creates security risks if not implemented carefully. The tension between security and recoverability's a constant theme in enterprise crypto that doesn't have easy answers.
Protocols and encryption in actual production systems
Domain 7 connects everything to real protocols you'll implement, which is where theory meets reality. SSL/TLS is obviously huge. The handshake establishes keys, cipher suites define which algorithms are used, and perfect forward secrecy ensures session keys can't be compromised even if long-term keys are. Modern TLS 1.3 simplified the handshake and removed weak cipher suites entirely, which should've happened years earlier.
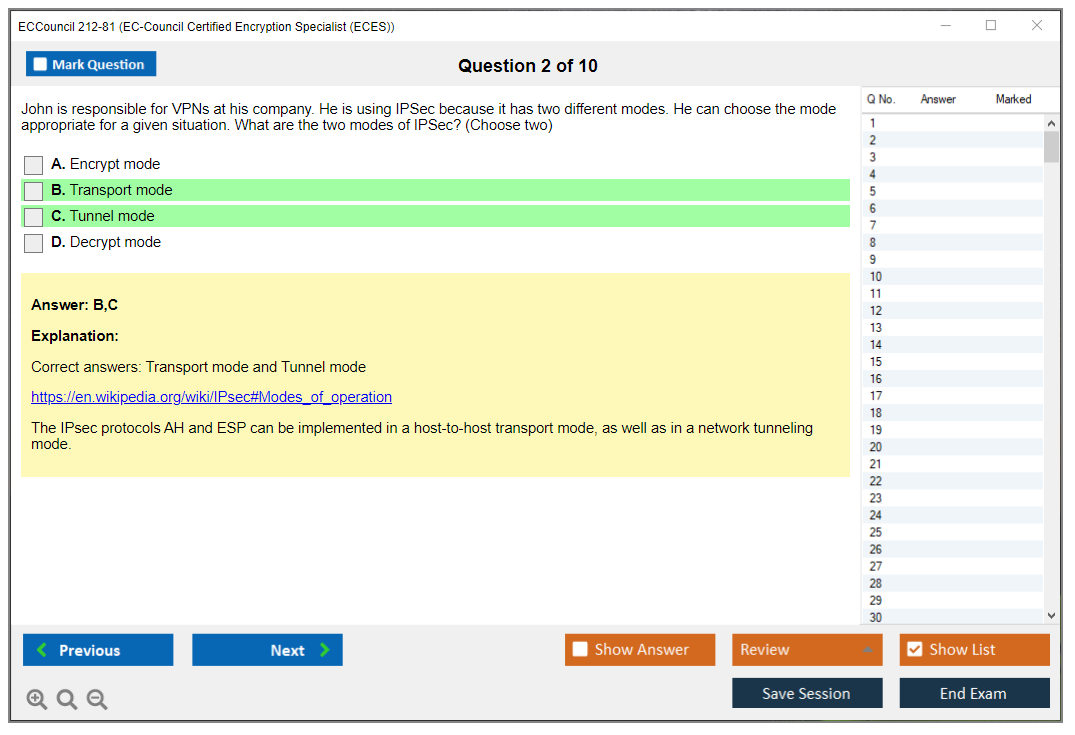
IPsec encrypts network traffic at the IP layer, which is different from application-layer encryption. Transport mode encrypts just the payload. Tunnel mode encrypts the entire packet and adds a new header. AH provides authentication, ESP provides encryption and optional authentication, and IKE handles key exchange. VPNs typically use IPsec in tunnel mode for site-to-site connections.
The exam also covers SSH for remote administration, S/MIME and PGP for email encryption, and wireless security protocols that most people don't think about. WPA3 fixed vulnerabilities in WPA2 and uses stronger encryption, but you need to understand both for the exam since WPA2's still everywhere in legacy deployments.
Full disk encryption versus file-level encryption? It's another practical decision with tradeoffs. BitLocker and FileVault encrypt entire volumes, protecting against physical theft when devices are powered off. File-level encryption lets you protect specific sensitive data and maintain different access controls, but it's more complex to manage and doesn't protect against all attack vectors.
If you're serious about passing, the 212-81 Practice Exam Questions Pack at $36.99 covers all seven domains with realistic questions that test actual understanding, not just definition memorization that fades after the exam. Other EC-Council certs like the 312-85 (Certified Threat Intelligence Analyst (CTIA)) or 212-89 (EC Council Certified Incident Handler (ECIH v3)) might have broader appeal, but if you're working with encrypted systems (and who isn't these days), ECES demonstrates specialized knowledge that sets you apart in ways that generalist certs can't.
Prerequisites and Recommended Background for 212-81 Success
Quick snapshot of what 212-81 is
The EC-Council 212-81 ECES exam is the vendor cert exam for the EC-Council Certified Encryption Specialist (ECES) credential, and honestly, it's EC-Council's way of testing whether you actually understand crypto or you're just throwing around terms like "military-grade encryption" without knowing what that even means.
People grab this cert for different reasons. Maybe your job suddenly got real with TLS configs, VPN troubleshooting, disk encryption rollouts, or key management nightmares and you're sick of pretending "just encrypt it" is a complete security strategy. Others chase it for resume padding. Security analyst roles. Sysadmins pivoting into infosec. Organizations drowning in compliance requirements that demand documented expertise.
What EC-Council actually requires (and what they just "recommend")
Look, the 212-81 exam prerequisites situation is way more straightforward than most EC-Council exams, which is honestly refreshing.
EC-Council does not mandate prerequisites. Zero. No "must have CEH first" gatekeeping. No required work history documenting five years in cryptographic implementations. You can pay the fee, book your slot, and attempt it tomorrow if you're feeling bold (or reckless). That's it.
EC-Council recommends candidates complete the official ECES study materials and training course, but that's a recommendation, not a hard requirement. The distinction matters if you're self-taught or your employer won't cough up training budget. If you prefer structured vendor-approved learning or you obsess over matching every exam topic to official wording, that training helps, but self-study folks pass without it constantly.
The thing is, age and educational requirements can shift based on country and testing center policies. Typically you're looking at 18+ with high school equivalency. Cross-border or under-18 situations? Verify local rules before assuming universal standards apply.
Exam details you should verify before you plan your timeline
Confirm current 212-81 exam objectives, format details, and delivery methods straight from EC-Council before locking your calendar. Vendors tweak blueprints constantly. Domains get renamed, weightings shift, new topics sneak in. It happens more than people think.
People obsess over 212-81 exam cost and 212-81 passing score, and I mean, yeah, budget matters, but pricing fluctuates with region, voucher bundles, training packages, seasonal promos, and the scoring model's rarely transparent enough to build strategy around. Treat cost and passing score as planning variables, not your prep foundation.
Retake policies matter too. So do exam-day ID requirements. Nothing kills momentum like showing up without proper identification or discovering your voucher has restrictions you never read.
Background knowledge that makes ECES prep way less painful
You don't need a PhD in number theory. But you absolutely need comfort with technical concepts that cryptography integrates into.
Networking basics are foundational. TCP/IP stack. OSI model layers. Common protocols like HTTPS, SSH, IPsec, SMTP. If someone asks what changes when traffic shifts from HTTP to HTTPS and you freeze, you'll burn half your ECES prep time backfilling fundamentals instead of learning applied cryptography.
Operating systems knowledge helps significantly. Windows and Linux basics at minimum. Command-line comfort is non-negotiable, not expert-level scripting, just enough that OpenSSL syntax, certificate stores, file permissions, or BitLocker commands don't trigger panic mode.
General security awareness forms the third pillar. CIA triad. Threat modeling. Security control frameworks. Not because ECES duplicates Security+, but because encryption IS a control, and the exam expects you to articulate which problems it solves and which problems it can't touch. Understanding that distinction separates people who pass from people who memorize definitions and still fail scenario questions.
Math. Yeah, it's present. But relax. You don't need advanced mathematics credentials. Understanding modular arithmetic, prime factorization, and exponentiation matters because it illuminates why encryption algorithms AES RSA ECC function the way they do and why key lengths aren't arbitrary marketing numbers, but you won't be constructing mathematical proofs like some graduate cryptography seminar. Algorithmic thinking beats raw math talent here.
Programming or scripting background is helpful, not mandatory. It accelerates understanding of implementation examples, especially around common key-handling mistakes, encoding gotchas, or how applications misuse hashing functions in authentication flows.
Crypto fundamentals self-check (be honest with yourself)
Here's what I actually ask people claiming they're "totally ready" for ECES.
Have you touched encryption tools professionally? GPG, OpenSSL, BitLocker, whatever, in any meaningful capacity. Even minimal exposure counts for something. If you've literally never generated a keypair, exported a certificate, or enabled full-disk encryption on a real system, you can still pass obviously, but expect serious hands-on practice during prep to fill that gap.
Do you know the actual difference between encryption, encoding, and hashing? This isn't negotiable territory. If those concepts blur together in your head, you'll confuse yourself constantly throughout the exam, particularly once hashing and digital signatures topics appear and you start mixing up confidentiality guarantees with integrity verification.
Can you articulate symmetric vs asymmetric encryption trade-offs and selection criteria? If your complete answer is "symmetric's faster" followed by awkward silence, you're not hopeless, but you need to construct that mental framework urgently. Key exchange problems. Session key generation. Hybrid encryption architectures. Where RSA/ECC actually belong in real implementations.
Are certificate warnings in browsers meaningful to you or just annoying popups? Expired certificates. Hostname mismatches. Untrusted certificate authorities. If you've spent years clicking through those warnings without curiosity, ECES is your wake-up call to stop ignoring them.
I once watched someone spend two weeks troubleshooting a production issue that turned out to be a certificate chain problem, and they still couldn't explain why intermediate CAs matter. Don't be that person.
If these concepts already feel comfortable, your ECES study time becomes mostly organizing existing knowledge and learning EC-Council's particular framing preferences. If not, budget a dedicated "crypto fundamentals" phase before touching exam-specific prep materials.
Who can still pass without prior cryptography experience
Motivated self-learners absolutely can pass. I've watched it happen repeatedly. But you need discipline, quality materials, and actual tool practice, not just passive reading that creates false confidence.
IT professionals with adjacent experience typically perform well. Network administrators. Systems administrators. Cloud infrastructure folks. SOC analysts. If you already wrestle with VPN configurations, TLS certificate troubleshooting, endpoint encryption policy enforcement, or even just managing internal application certificates, you're closer to ready than you realize because the exam weighs practical cryptographic decisions as heavily as textbook definitions.
Time expectations deserve honesty. Starting from near-zero crypto exposure? Plan 60 to 100 study hours across 6 to 12 weeks realistically. That's not some magic formula, it's a "don't kid yourself" baseline. Some weeks you'll fly through material, then PKI certificate chains will appear and suddenly you're rereading the same explanation four times because hierarchical trust models are really annoying until they click.
Memorization alone fails here. Understanding matters. Scenario analysis matters. You need to know why one answer's correct AND why the three wrong options are tempting but fundamentally flawed.
Certifications and experience that pair well with ECES
If you're stacking credentials strategically, several complement EC-Council Certified Encryption Specialist (ECES) preparation nicely.
CompTIA Security+ establishes baseline security vocabulary including foundational cryptography terminology. Network+ or CCNA helps because real-world encryption lives inside network protocols constantly, and that context removes unnecessary friction.
EC-Council CEH addresses crypto topics from an attacker perspective, which honestly provides useful contrast. CISSP covers cryptography as one domain within its massive scope, though if you're already CISSP-certified you're not questioning whether you CAN start ECES, you're questioning whether it's worth your time investment.
Practical work experience is the real force multiplier. Implementing SSL/TLS in production. VPN deployments. Enterprise disk encryption rollouts. Managing PKI and digital certificates across organizational infrastructure. Cloud platform certifications (AWS, Azure, GCP) also contribute because cloud providers discuss encryption-at-rest, KMS architectures, key rotation policies, and certificate services in ways that map directly to ECES conceptual frameworks.
Self-assessment before you start studying
Can you dedicate 8 to 15 hours weekly for 6 to 12 weeks consistently? Some people batch weekend study sessions. Others need daily momentum to maintain retention. Either approach works, but zero time equals zero progress regardless of talent.
Do you have access to study materials AND a practice environment? You need lab space. Virtual machines. OpenSSL installed. Maybe a basic web server with TLS configured. Somewhere to break things safely without consequences. Pure reading without experimentation is painfully slow learning.
Are you comfortable with self-directed learning, or do you need external structure? If structure keeps you accountable, consider official training seriously. If you're naturally self-driven, you can construct a personalized plan around 212-81 exam objectives and target specific knowledge gaps with focused resources.
Have you verified current blueprint alignment with your study resources? This matters enormously if you're purchasing third-party ECES practice tests or using older textbooks. Mismatched objectives equal wasted study hours chasing outdated content.
What's your actual goal here? Career advancement. Skill validation. Compliance checkbox. Different motivations should shift how deeply you engage with material and how much hands-on experimentation you prioritize.
Practice tests and targeted prep (what actually helps)
I'm a believer in practice questions, but only with correct usage. Take a diagnostic exam first. Study the explanations thoroughly, not just for questions you missed, but for ones you guessed correctly too. Then execute a hands-on task matching that concept. That feedback loop is where genuine learning solidifies.
If you want a dedicated question resource, the 212-81 Practice Exam Questions Pack offers a low-friction method to pressure-test understanding early, especially if you treat incorrect answers like a customized study roadmap instead of personal failure. I'd recommend using it once initially to identify weak areas, then again later after completing tool-based practice, and yes that means you'll probably cycle through the 212-81 Practice Exam Questions Pack multiple times if you're approaching this seriously.
Just don't let practice exams become your entire strategy. That's how people develop pattern recognition instead of actual cryptographic comprehension.
Renewal and keeping the cert active
EC-Council certifications typically involve continuing education requirements and maintenance fees, and specifics change periodically, so verify current ECES certification renewal policies directly with EC-Council. Don't assume it mirrors another certification you hold. Different programs, different requirements, different bureaucratic headaches.
If you approach it intelligently, renewal is manageable. Complete relevant training. Attend industry webinars. Document work projects involving encryption implementations. Keep receipts. Maintain organized notes. Administrative overhead? Sure. Still beats letting credentials lapse and starting over.
FAQ style quick hits people ask anyway
What is the EC-Council 212-81 (ECES) exam and who should take it? Professionals working around encryption and key management systems, or anyone needing to demonstrate practical crypto knowledge without pursuing academic cryptography degrees.
How hard is the ECES exam and how long should I study? Crypto beginners, expect 6 to 12 weeks with mandatory hands-on tool practice. Wait, let me rephrase that because it sounds too prescriptive. If you're experienced IT, you can compress the timeline, but don't rush PKI topics because they're deceptively complex.
What are the best ECES study materials and practice tests? Start with official courseware if vendor alignment matters to you, then layer in lab environments and question packs like the 212-81 Practice Exam Questions Pack to expose knowledge gaps quickly before they become exam-day disasters.
ECES Exam Difficulty Analysis and Study Timeline Recommendations
What actually makes this exam tough
The EC-Council 212-81 ECES exam sits in this weird middle ground. It's not as brutal as the Certified Ethical Hacker Exam (CEHv12) or Computer Hacking Forensic Investigator (CHFI-v10), but it's definitely not a walk in the park either.
I'd call it moderate difficulty overall. The thing is, it tests you on a specialized topic: encryption and cryptography. You can't just skim general security concepts and hope for the best. You need focused, systematic study.
What really sets ECES apart? It emphasizes conceptual understanding over rote memorization. Yeah, you need to know algorithm names and key sizes, but the exam wants to see if you actually understand why you'd choose AES-GCM over AES-CBC in a specific scenario. The mathematical foundations can scare people off. I mean, RSA and ECC have some pretty heavy math behind them, but the exam focuses on application rather than making you derive equations on paper.
Most candidates get tripped up by the breadth of encryption technologies. You're covering symmetric encryption, asymmetric encryption, hashing, digital signatures, PKI infrastructure, key management procedures, and secure protocol implementations. That's a lot of ground. My friend last year spent three weeks just on PKI and still felt shaky walking into the test center.
Practical implementation questions are where you'll really earn your passing score. These aren't "what does AES stand for?" questions but scenario-based challenges like: "A company needs to protect data at rest in their database while ensuring individual records can be quickly retrieved and decrypted. Which approach makes the most sense?" You've gotta apply theory to real-world situations.
Candidates with prior cryptography exposure have a much easier time. If you've implemented TLS, worked with certificate authorities, or configured encrypted storage solutions, you're already halfway there. Complete beginners need more runway.
Where people actually struggle
Distinguishing between similar encryption algorithms is harder than it sounds. AES, DES, 3DES, Blowfish are all symmetric block ciphers, but when do you use each? Well, you shouldn't use DES at all anymore, but the exam tests whether you know why and what replaces it.
Same with understanding the mathematical basis of RSA versus ECC without drowning in the actual math. You need to grasp that RSA uses factorization of large primes while ECC relies on elliptic curve discrete logarithm problems, but you don't need to solve those problems by hand.
PKI and digital certificates cause headaches. The hierarchy and trust chain validation process confuses people constantly. Is it a root CA or intermediate CA? How does certificate revocation actually work? What's the difference between CRL and OCSP, and when would network latency make one preferable over the other?
Block cipher modes of operation get tested heavily. ECB is insecure for most uses, CBC needs an IV, GCM provides authenticated encryption, CTR turns a block cipher into a stream cipher. You need to know appropriate use cases for each, not just definitions.
Key management lifecycle questions are sneaky difficult. They cover key generation, distribution, storage, rotation, revocation. Each phase has proper procedures, and a question might describe a scenario where keys need rotation and ask what went wrong in the current implementation.
Troubleshooting encryption implementation problems requires you to think diagnostically. "Users report intermittent authentication failures with the new certificate. What's the likely cause?" Could be time sync issues, could be revocation checking, could be trust chain problems.
Keeping current versus deprecated algorithms straight matters for passing. MD5 is cryptographically broken for collision resistance, SHA-1 is deprecated for digital signatures, DES and 3DES are legacy. The exam will absolutely test whether you'd recommend these for new implementations (you wouldn't) and what you'd use instead.
Quantum computing threat to cryptography is becoming more prominent, so you should understand that Shor's algorithm threatens RSA and ECC, and know that post-quantum cryptography standards are being developed. Not deep math, just awareness.
Mistakes everyone makes (including me when I was studying)
Confusing symmetric and asymmetric encryption use cases is probably the number one mistake. Symmetric is fast, uses same key for encryption and decryption, great for bulk data. Asymmetric is slower, uses key pairs, perfect for key exchange and digital signatures. People mix these up constantly under exam pressure.
Misunderstanding when hashing versus encryption is appropriate comes up all the time. Hashing is for integrity and password storage (one-way). Encryption is for confidentiality (reversible). You can't "decrypt" a hash, yet people answer questions as if you could.
Not recognizing deprecated algorithms happens because study materials vary in currency. Some older practice questions still treat MD5 as acceptable for certain uses. It's not. SHA-256 minimum for new implementations.
Key length confusion? Real problem. 128-bit AES versus 256-bit AES. 2048-bit RSA versus 4096-bit. The exam expects you to know appropriate lengths for different security requirements and compliance standards.
Certificate validation and revocation methods trip people up. CRL (Certificate Revocation List) is simple but doesn't scale well and can be stale. OCSP (Online Certificate Status Protocol) provides real-time checking but adds network dependency. The exam loves comparing these.
Rushing through scenario questions is how you fail. I've done it. You see keywords, think you know the answer, and move on. Wait, then you realize you missed a key detail like the question specified "offline environment" which eliminates OCSP as an option.
Prevention strategies that actually work: create comparison charts for similar concepts. I made a massive spreadsheet comparing symmetric algorithms, another for asymmetric, another for hashing functions. Build concept maps showing relationships between topics. PKI connects to asymmetric encryption, which connects to key exchange, which connects to hybrid cryptosystems.
Do hands-on labs with OpenSSL, create certificates, encrypt files, examine protocol handshakes. And please, use timed 212-81 practice tests to simulate exam pressure. That investment pays off when you're not seeing question formats for the first time on exam day.
Timeline if you're starting from scratch
Recommended 8 to 12 weeks with 10 to 15 hours weekly commitment. That's 80 to 180 total hours depending on your learning pace and how much sticks the first time.
Week 1 and 2 is cryptography fundamentals and historical context, where you'll learn basic concepts, understand why encryption exists, grasp the difference between encoding, encryption, and hashing. This foundation matters.
Week 3 and 4 covers symmetric encryption algorithms, block ciphers, and modes of operation. Deep-dive AES, understand DES history, learn when to use CBC versus GCM versus CTR. Do hands-on encryption and decryption exercises.
Week 5 and 6 tackles asymmetric encryption, RSA, ECC, and key exchange protocols, which is where the math appears. Focus on application and understand Diffie-Hellman, grasp why you'd choose ECC over RSA (smaller keys, same security).
Week 7 and 8 moves to hashing, digital signatures, and message authentication: SHA-2 family, SHA-3, HMAC construction, how digital signatures provide non-repudiation. Critical stuff.
Week 9 and 10 dives into PKI, digital certificates, and trust models. Certificate hierarchy, X.509 format, validation processes, revocation mechanisms. This section is dense.
Week 11 addresses key management lifecycle and secure protocols like TLS/SSL, IPsec, S/MIME, PGP and how protocols actually use the cryptographic primitives you've learned.
Week 12 is review, practice tests, and weak area reinforcement. Take full-length practice exams, identify gaps, drill those topics. The 212-81 Practice Exam Questions Pack helps here because you need exposure to the question style and tricky wording.
Adjust based on your pace. If you're crushing practice questions after 8 weeks, schedule the exam. If you're struggling, add another month.
Accelerated timeline for experienced folks
If you've already worked with cryptography (maybe you're a security engineer who's implemented encryption solutions or you've taken courses covering these topics) you can compress to 4 to 6 weeks with 10 to 15 hours weekly. That's 40 to 60 total hours.
Week 1? Rapid review of fundamentals, symmetric, and asymmetric encryption. You're refreshing, not learning from zero.
Week 2 focuses on gaps in your knowledge, because most experienced people know encryption basics but are weak on PKI details or specific protocol implementations. Identify and target those areas.
Week 3 is hands-on labs and scenario practice. Work through implementation problems, troubleshoot misconfigurations, practice with actual tools.
Week 4 (and potentially weeks 5 to 6) is practice exams and final review. Take multiple full-length tests, review every wrong answer, understand why the correct answer is correct.
This aggressive timeline works if you're honest about your baseline knowledge. If you took a cryptography course three years ago and haven't touched it since, you might need the full beginner timeline despite "experience."
Compared to something like the EC-Council Certified CISO (CCISO) which requires executive-level thinking across all security domains, or the Certified Threat Intelligence Analyst (CTIA) which demands deep threat space knowledge, ECES is narrower but deeper in its specific domain. That focus is actually helpful. You know exactly what to study, and if you put in the hours understanding encryption concepts rather than just memorizing facts, you'll pass.
Conclusion
Wrapping up your ECES prep
Okay, so here's the deal.
Snagging that EC-Council 212-81 ECES exam certification? It's actually a pretty smart move if you're already grinding in security or crypto fields, honestly. The cryptography fundamentals get seriously dense. I'm talking headache-inducing at times. Wrapping your head around the practical differences between symmetric vs asymmetric encryption or why PKI and digital certificates actually matter in real deployments takes genuine effort and focus. But here's the thing: that difficulty is precisely what makes it valuable in the marketplace. Employers definitely notice when you can discuss encryption algorithms AES RSA ECC intelligently and not just regurgitate buzzwords you memorized the night before.
The 212-81 exam cost isn't cheap. Neither's the time investment, obviously. You're probably staring down 4 to 8 weeks of solid prep depending on your starting knowledge. The 212-81 passing score sits at 70%, which sounds generous until you realize how incredibly specific some questions get about hashing and digital signatures or key management lifecycles. Wait, let me backtrack. You've really gotta understand the 212-81 exam objectives inside and out, not just memorize cookie-cutter definitions.
Mix it up.
Your study plan should blend official ECES study materials with hands-on practice because reading about RSA is one thing but actually working through examples and seeing how asymmetric encryption solves real problems? That's completely different territory. I once spent three hours just trying to wrap my head around elliptic curve cryptography before it finally clicked during a random YouTube video about Bitcoin wallets. Sometimes the best learning happens sideways. The best indicator you're ready is honestly how you're performing on quality ECES practice tests, the kind that explain why wrong answers are wrong, not just slap them with red marks and move on.
Don't forget about ECES certification renewal down the road, by the way. Most EC-Council certs need continuing education credits, so you'll wanna budget time and a bit of cash for that every three years. It's annoying but keeps the credential from becoming stale.
If you're serious about passing on your first attempt and want to test your readiness with realistic questions, I'd recommend checking out the 212-81 Practice Exam Questions Pack. It's built to mirror the actual exam topics. Cryptography fundamentals, PKI workflows, algorithm selection, all of it. Gives you that repetition you need to lock concepts in. The explanations help fill gaps you didn't even know you had.
The EC-Council Certified Encryption Specialist isn't just another line on your résumé. It's proof you understand the math and the practical side of keeping data safe. Put in the work now and you'll thank yourself later when you're the person everyone asks about TLS configs or certificate chain issues.