SUSE sca_sles15 (SUSE Certified Administrator in Enterprise Linux 15)
SUSE SCA SLES 15 Certification Overview
The SUSE SCA SLES 15 certification is a performance-based credential that proves you can actually handle real Linux administration work on SUSE Linux Enterprise Server 15. This is not one of those multiple-choice exams where you memorize answers and forget everything two weeks later. SUSE wants to see you configure systems, troubleshoot problems, and manage services like you would in an actual production environment. The certification validates that you have got the practical skills to install, configure, manage, and troubleshoot SLES 15 systems without needing someone looking over your shoulder constantly.
What is the SUSE Certified Administrator in Enterprise Linux 15?
This is the entry-level professional certification in the SUSE certification pathway, but do not let "entry-level" fool you into thinking it is easy. The SCA in Enterprise Linux 15 exam tests your ability to perform day-to-day system administration tasks that enterprises actually need. We are talking user and group management, file permissions, storage configuration, network setup, service management with systemd, and security implementations that will keep the auditors happy. You will work with YaST administration tasks alongside standard Linux command-line utilities, which gives you that SUSE-specific knowledge while keeping your skills vendor-neutral enough to be useful across different environments.
Real competency matters.
The certification demonstrates competency in the kind of work that keeps enterprise systems running smoothly. Companies using SUSE infrastructure need administrators who can jump in and solve problems without extensive handholding. This cert is designed to validate exactly that capability.
Who should take SCA SLES 15?
Linux system administrators managing SUSE environments in production are the obvious candidates. But I have seen IT professionals from all sorts of backgrounds benefit from this certification. Maybe you are transitioning from Red Hat or Ubuntu environments and need to prove you can handle SLES-specific tooling. DevOps engineers who need foundational SUSE administration knowledge before diving into container orchestration or automation work. Support engineers in mixed Linux enterprise environments where you are dealing with multiple distributions and need to demonstrate cross-platform competency.
Career changers entering Linux system administration roles find this particularly valuable because it is a concrete, verifiable skill demonstration. Students pursuing Linux certifications to build professional credentials should consider this alongside or after something like the SUSE Certified Administrator in Enterprise Linux 15 track. The certification fits with job requirements for junior to mid-level Linux administrator positions, which means it actually opens doors rather than just sitting pretty on your resume.
Look, if you are supporting SAP HANA or other enterprise applications on SLES, this certification basically becomes non-negotiable. Employers want proof you know what you are doing.
How SCA SLES 15 fits in the SUSE certification track
This is your foundation before moving up to the SUSE Certified Engineer (SCE) level or branching into specialized areas. Think of it as the base layer. Once you have got your SCA SLES 15, you can pursue the SUSE Certified Engineer in Enterprise Linux 15 for more advanced topics. Or you can specialize in areas like High Availability with the SCA+ in SUSE Linux Enterprise High Availability certification.
Storage specializations exist through certifications like SCA in SUSE Enterprise Storage 6. You can go the cloud-native route with SCA in SUSE Rancher 2.6.
The certification complements other Linux certifications like RHCSA, LPIC, or CompTIA Linux+. Not going to lie, having multiple Linux certs shows you are not just locked into one ecosystem, which employers appreciate more than they will admit. Recognition across industries using SUSE enterprise solutions means this cert actually carries weight when you are job hunting or negotiating salary. I once worked with a guy who had nothing but Ubuntu experience, decent skills really, but he could not get past the HR screening for enterprise roles until he picked up vendor-specific certifications that proved he understood production-grade tooling.
Key benefits of earning SUSE SCA SLES 15 certification
Career advancement opportunities in organizations using SUSE infrastructure are the big one. Salary differentiation compared to non-certified Linux administrators is real, even if HR departments do not always advertise it that way. Performance-based examination means you are validating practical skills rather than memorization ability.
You get access to the SUSE certified professional community and resources. Enhanced credibility when supporting enterprise SLES deployments. Demonstrated commitment to professional development in Linux administration, which matters when managers are deciding who gets promoted or who gets assigned to high-visibility projects.
I have seen people use this cert as a springboard into SAP-specific roles by following up with SCA+ in SLES for SAP Applications certification. The skills you learn managing SLES 15 storage and networking configuration directly apply to supporting business-critical applications that cannot afford downtime.
Differences between SUSE SCA and other Linux certifications
The performance-based practical exam versus multiple-choice testing is the biggest difference. You are not selecting answer C because it sounds right. You are actually configuring a system and if it does not work, you do not pass. SUSE-specific tools like YaST alongside standard Linux utilities means you need broader knowledge than just memorizing command syntax or regurgitating man pages. Focus on enterprise-grade SLES features and configurations rather than home lab scenarios.
Emphasis on real-world administrative scenarios over theoretical knowledge makes this more challenging but also more valuable. Integration with SUSE support and enterprise ecosystem requirements means the skills directly translate to actual job responsibilities rather than just cert hunting.
What employers look for in SCA-certified professionals
Proven ability to manage SUSE Linux Enterprise Server 15 administration in production systems. Competency in user management, permissions, and security configurations that actually protect sensitive data. Skills in storage management, file systems, and backup strategies because data loss is a career-ending event in enterprise environments.
Network configuration and troubleshooting capabilities. Service management using systemd services on SLES and SUSE-specific frameworks. Problem-solving abilities demonstrated through hands-on examination performance rather than just claiming you can troubleshoot on your resume.
Employers want someone who can walk into the data center (or SSH into the environment) and fix problems without needing extensive documentation or constant guidance. This cert proves you can do that.
Real-world applications of SCA SLES 15 skills
Managing multi-user enterprise server environments where dozens or hundreds of users need appropriate access without compromising security. Configuring and maintaining critical business services that support revenue-generating operations. Implementing security policies and access controls that satisfy compliance requirements and auditors. Troubleshooting system performance and availability issues before users start complaining or before SLAs get violated.
Automating routine administrative tasks through scripting because nobody has time to manually provision 50 user accounts. Supporting SAP HANA and other enterprise applications on SLES, which is where a lot of the high-paying jobs actually are. You might also branch into container management with SCA in SUSE CaaS Platform 4 or configuration management with SCA in SUSE Manager 4 once you have got this foundation.
The SLES 15 user and group management skills alone save countless hours when onboarding new employees or managing departmental access. Network troubleshooting capabilities mean you are the person who figures out why that critical application server suddenly cannot reach the database. These are the skills that make you indispensable rather than just another pair of hands in the IT department.
Exam Details: Format, Cost, and Passing Score
SCA in Enterprise Linux 15 exam format and structure
The SUSE SCA SLES 15 certification exam is practical. Hands-on work exclusively. You log into a live SUSE Linux Enterprise Server 15 administration environment and do admin work until the clock runs out.
This isn't multiple choice. The SCA in Enterprise Linux 15 exam is performance-based, meaning the only thing that matters is whether the system ends up configured the way the task requires. People who only read theory tend to get humbled fast when they hit networking, storage, and systemd services on SLES under time pressure. There's nowhere to hide when the system either works or it doesn't.
SUSE runs it as a remote proctored exam through their certification platform, so you're typically at home with a webcam, a decent mic, and a quiet room. There's also an in-person option in some major cities via partners, but most people I talk to do the online proctored route because it's easier to schedule and you don't lose half a day commuting. One exam, multiple independent objectives, different admin domains. Think SLES 15 user and group management, services, basic security settings, storage layouts, and SLES storage and networking configuration style tasks.
Real-world scenarios show up constantly. You get tasks that feel like "a ticket came in and you need to fix it now," which is why it's a solid filter for people who can actually run SLES. You'll do YaST administration tasks when it's the fastest path and drop to the CLI when YaST would take longer.
No breaks. Yep.
Exam duration and time management
You get 120 minutes officially. Two hours flat. That's your active working time for task completion, and it goes by weirdly fast because each objective has its own little trap where you can burn 10 minutes just rereading requirements or chasing a typo in a config file that you swear wasn't there two minutes ago.
There's extra time before the exam for the tutorial and system checks, like verifying your webcam, screen sharing, and making sure the proctor can see your workspace. That part isn't the exam. Still stressful though. You'll also do identity verification with a government-issued ID, and for remote proctoring you should expect a workspace scan where you show the desk and surrounding area.
Time management is where most people lose points. Not because they don't know Linux, but because they treat every task like it deserves the same attention. Some tasks are quick points if you're comfortable with the command line and can read requirements carefully.
My favorite strategy? Boring but effective. Skim all objectives first, tag the "easy wins" you can do in 2 to 5 minutes, knock those out immediately to secure baseline points, then come back for the longer tasks like storage, network changes, or anything involving services that must persist across a reboot. For medium tasks, set a timer in your head. Like 8 minutes max. If you're still stuck, park it and move on because the scoring's usually based on total points and you don't want to donate half your exam to one stubborn objective.
Actually, let me tell you what happened to a colleague last year. Guy I worked with spent 45 minutes on a single firewall rule that should've taken five. The wording threw him off and he kept second-guessing whether ports needed TCP or UDP. By the time he moved on, he had maybe 20 minutes left for six other tasks. He failed by three points. Three. Could've picked those up anywhere else if he'd just moved faster.
Another tip: verify as you go. After any change, check the service state, check the file, run the command that proves the outcome. If the objective smells like persistence, do the reboot test mentally and make sure you used the right tools like systemd enablement rather than just "it runs right now."
Cost of the SCA SLES 15 exam
The SUSE Certified Administrator SLES 15 cost is usually in the ballpark of $199 to $249 USD for a single exam attempt, depending on region and pricing at the time you register. Currency conversions can make it look higher or lower in local terms, and sometimes taxes get added at checkout, so don't be shocked if the final total shifts a bit.
Discounts exist. They're inconsistent. Sometimes you'll see deals via SUSE training bundles, learning credits, partner programs, or employer agreements. If your company already pays for SUSE subscriptions or training, ask your manager because there might be a voucher floating around that nobody's using.
Retakes are simple. You pay again. Unlimited attempts in practice, and typically no mandatory waiting period, though policy can change so check the portal before you plan a same-week retry. The retake fee structure's painful if you go in underprepared, so budgeting for "maybe I need a second attempt" is smart if you're new to SLES.
Training costs are a totally different tier. Official instructor-led SUSE courses can run roughly $2,000 to $3,500 depending on delivery and region, and that's not even about the exam fee. That's about the class itself. Self-study's way cheaper. More like $50 to $200 if you buy a couple of books, lab subscriptions, and decent SCA SLES 15 study materials. I'm opinionated here: unless your employer's paying, I'd rather see you build a home lab and grind tasks than drop three grand on a class you might not need.
Compared to other Linux certs? The exam fee's pretty normal. The bigger cost is time, and the opportunity cost of not practicing.
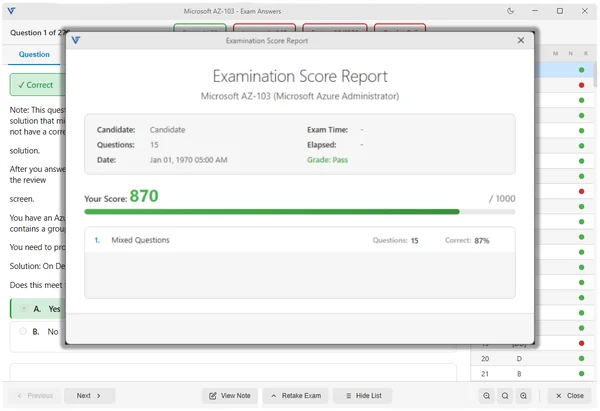
Passing score (and how scoring works)
The SCA SLES 15 passing score is typically around 70% of total available points. That threshold can vary slightly between exam versions, so treat 70% as the target, not a promise written in stone.
Scoring's based on outcomes. Final system state, automated checks. The platform verifies configuration files, service states, users and groups, and command outputs against what the objective asked for. If you got it right, you get the points. If you got it half right, you might still get partial credit, which is why it's worth doing the "good enough to score" version of a task rather than abandoning it completely when you're stuck on a tiny detail.
No penalty for wrong attempts is a nice detail. The system doesn't care how many times you edited the file, restarted the service, or flipped a setting back and forth. Only the end result matters when the grader runs. That said, you can absolutely dig yourself a hole and waste time, so "no penalty" doesn't mean "thrash around forever."
Persistence matters. If the exam tests whether your changes survive a reboot, it'll check that, so if you edited something that works until restart, you'll lose points when the verification runs. Also, documentation style and best practices aren't typically scored directly, so the grader won't reward you for pretty comments. It rewards you for a working config, even if you used a different method than the training course showed.
Results are usually immediate. You finish, you submit, and you get a score report that breaks down performance by objective domain. Actually useful for planning a retake because you can see if you're weak in services, networking, or storage.
Exam delivery methods and scheduling
Online proctored is the default. Webcam required, stable internet, a room where nobody walks in. You schedule through the SUSE certification portal or an authorized partner, and availability's often within 1 to 2 weeks, sometimes sooner if you're flexible on time slots.
Rescheduling and cancellation policies usually require 24 to 48 hours notice. Read the fine print. If you miss the window, you can lose the fee, and that's an expensive lesson.
Test centers exist in some areas. Mentioning it because some people hate remote proctoring, others love it. Pick your poison.
What to expect on exam day
ID check first. Then the proctor setup, then a workspace inspection if you're remote. It can feel awkward. It's normal.
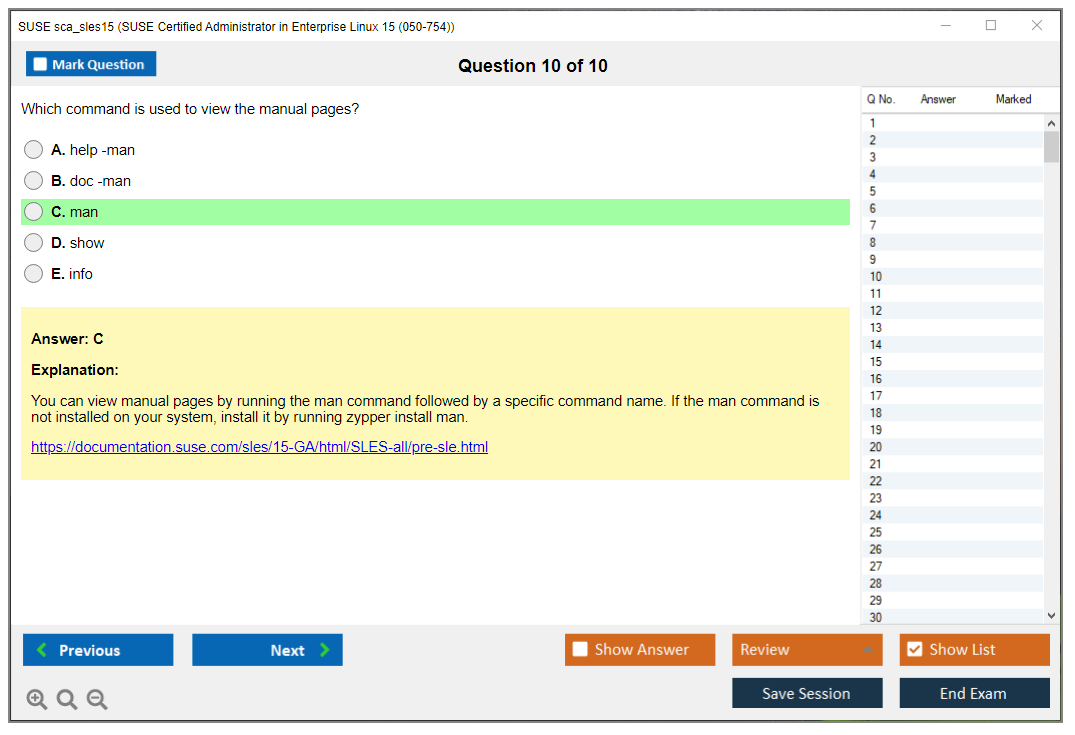
You'll get a tutorial on the interface and how to move between tasks, and then you're dropped into a live SLES 15 system with root access. Standard utilities are there, a basic text editor, man pages, the usual admin toolbox. External resources are typically restricted, so don't plan on googling error messages, don't plan on opening random docs on a second monitor, and don't plan on paper notes unless the rules explicitly allow it.
Retake policies and exam validity
Retakes are allowed as many times as you're willing to pay. Full fee each time. Different exam versions may show up on retake, so don't memorize one set of steps and assume the same SCA SLES 15 exam objectives appear in the same order.
The SCA SLES 15 renewal policy is usually tied to a validity window, often 3 to 5 years depending on SUSE's current program rules and how they treat versioned certs. The practical reality's that when SLES versions shift, employers care that you're current, not that you passed something a decade ago.
If you fail? Use the score report, fix gaps, build a lab. Run a mini SCA SLES 15 practice test routine by recreating tasks from memory, especially the ones you bombed, because the fastest improvement comes from repeating the exact admin motions until they're automatic.
SCA SLES 15 Exam Objectives and Domains
Official exam objective domains overview
The SUSE SCA SLES 15 certification exam splits into eight distinct domains, each carrying specific weight. System Installation and Deployment covers 10-15% of the test, dealing with installation methods and initial configuration. Software Management and Updates also takes 10-15%, focusing on package handling and updates. User and Group Administration jumps to 15-20%, reflecting how critical identity management is in enterprise environments. Storage and File System Management matches that at 15-20%, which honestly makes sense given how much disk work you'll do as a Linux admin. I mean, you're constantly dealing with filesystem issues, partition resizing, and storage allocation problems that demand immediate attention regardless of what else is burning.
Network Configuration and Services? That grabs another 15-20% of exam questions. System Services and Process Management drops back to 10-15%, covering systemd and process control. Security and Access Control sits at 10-15%, addressing firewalls, permissions, and basic hardening. System Monitoring and Troubleshooting rounds things out at 10-15%, testing your ability to diagnose problems and interpret system behavior.
Look, networking's everywhere in SLES administration. Can't avoid it.
The sca_sles15 certification validates foundational skills that every SUSE administrator needs daily. These domains aren't arbitrary. They mirror real-world tasks you'll encounter managing SUSE Linux Enterprise Server 15 in production environments.
System installation and configuration tasks
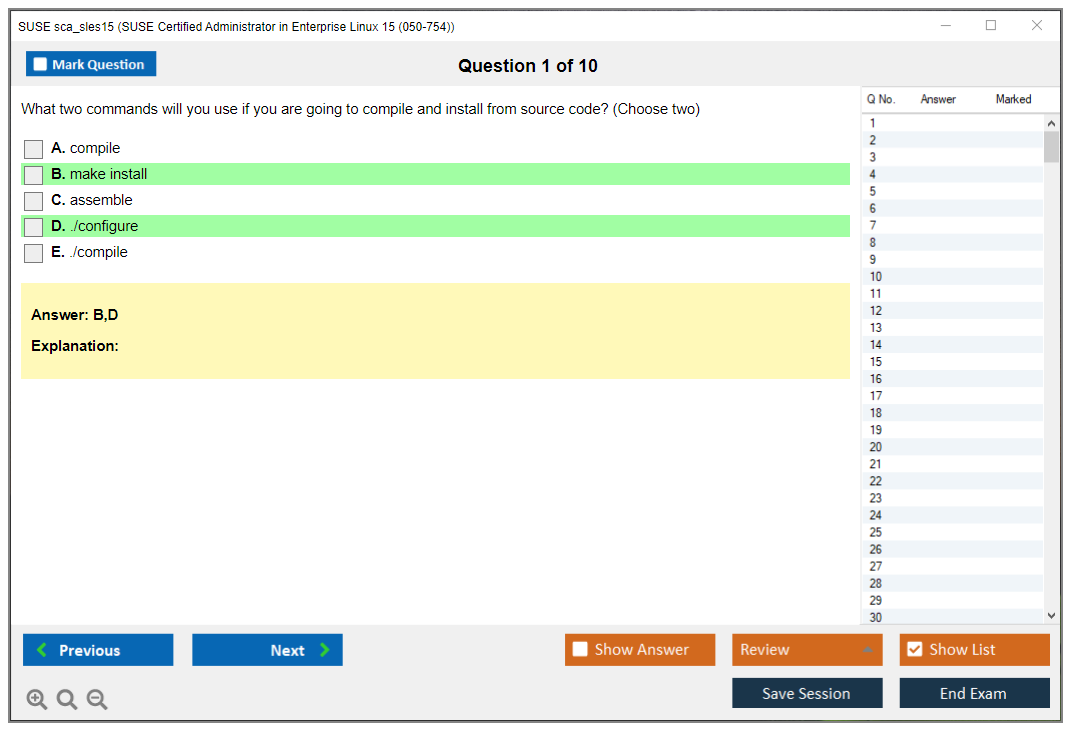
Installation methods for SLES 15 include DVD/ISO media, network-based PXE boot, AutoYaST for automated deployments, and virtual machine installations. You need to understand the boot process from BIOS/UEFI through GRUB2 to kernel initialization. Not gonna lie, the exam'll test whether you know how to troubleshoot boot failures, which means understanding GRUB2 configuration files and kernel parameters.
System registration with SUSE Customer Center (SCC) is mandatory for receiving updates and accessing repositories. You'll configure this during or after installation using SUSEConnect command-line tools or YaST. Repository configuration determines which software sources your system uses. This includes base repositories, update channels, and optional module repositories.
Boot targets in systemd replace the old runlevel concept. Understanding multi-user.target versus graphical.target matters for controlling what services start at boot. GRUB2 bootloader configuration lives in /etc/default/grub and requires running grub2-mkconfig after changes. The thing is, kernel parameter modification lets you pass boot options for troubleshooting or hardware compatibility, and honestly, knowing how to edit these at boot time can save your bacon during system recovery scenarios.
Software management using zypper and YaST
Zypper's SUSE's primary command-line package manager. Installing packages uses 'zypper install packagename', while updates apply with 'zypper update' or 'zypper patch' for security-specific fixes. Removing packages requires 'zypper remove packagename', but you've gotta watch for dependency warnings. Searching for packages uses 'zypper search' with various filters.
Repository management through zypper includes adding repos with 'zypper addrepo', listing them with 'zypper repos', and modifying priorities to control which sources take precedence during conflicts. I mean, repository priorities can get tricky when you've got multiple sources providing the same package. It's not always obvious which one'll win, and sometimes you'll need to manually intervene to prevent version conflicts that break critical services. The exam expects you to understand how zypper resolves these conflicts and how to override default behavior when needed.
YaST Software Management provides a GUI alternative that some admins prefer for complex dependency resolution. Package verification checks integrity using RPM signatures. Product migrations and service pack upgrades represent major version changes that require careful planning and testing, typically using 'zypper migration' workflows guided by SUSE documentation.
SLES 15 user and group management requirements
Creating user accounts happens with 'useradd' command or through YaST User and Group Management module. Modifying existing accounts uses 'usermod', while deletion requires 'userdel'. Password management involves 'passwd' for setting passwords and understanding aging policies configured in /etc/login.defs. Password expiration, minimum age, maximum age, and warning periods all come from these settings.
Groups organize users for access control purposes. Creating groups uses 'groupadd', modification uses 'groupmod', and you add users to groups with 'usermod -aG groupname username'. The files /etc/passwd, /etc/shadow, and /etc/group store user, password, and group information respectively, and you need to understand their format for troubleshooting.
Sudo configuration in /etc/sudoers grants privilege elevation without sharing root passwords. Use 'visudo' to edit this file safely. Home directories typically live under /home and get created from /etc/skel skeleton files that provide default configurations. Shell configuration files like .bashrc and .bash_profile set user environments. Account lockout policies prevent brute-force attacks by disabling accounts after failed login attempts, configured through PAM modules. Honestly, I've seen production systems get hammered because nobody bothered setting up account lockouts properly.
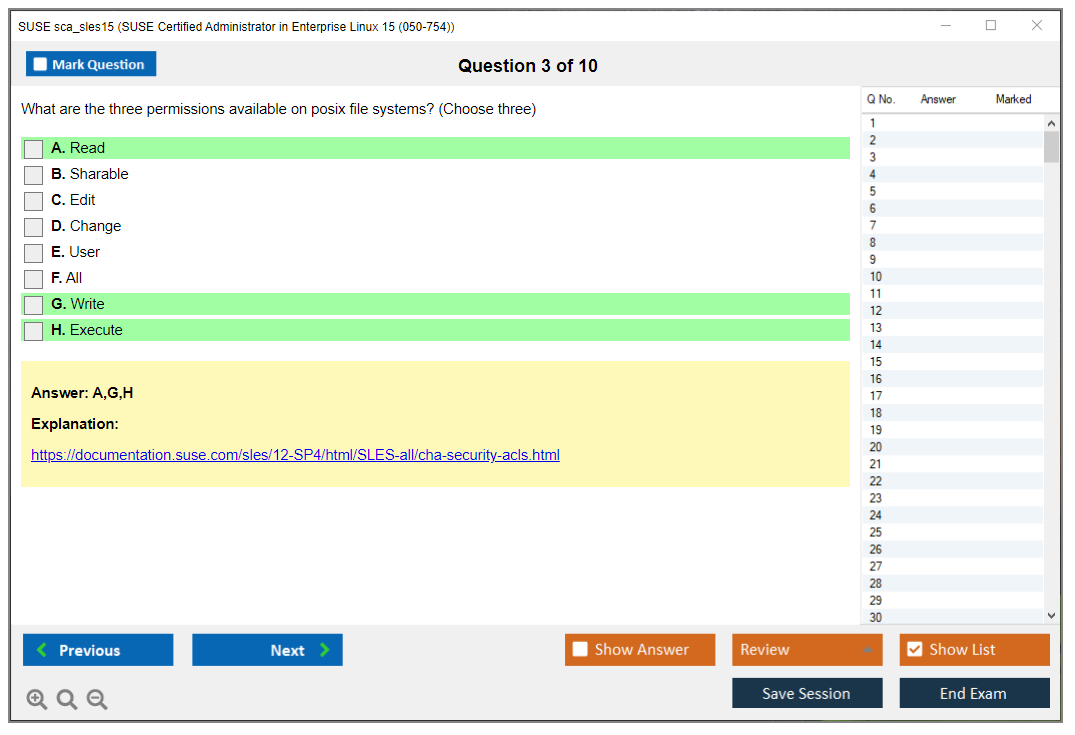
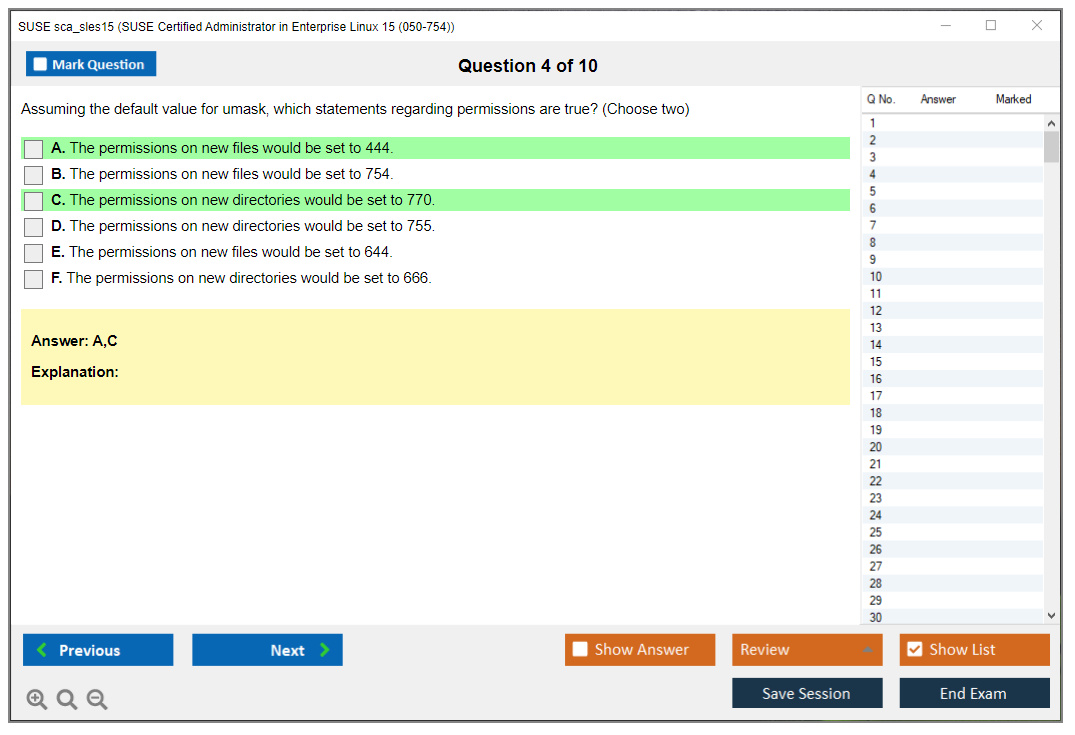
File permissions and ownership administration
Standard Unix permissions use read (4), write (2), and execute (1) bits for owner, group, and others. The chmod command modifies permissions using numeric (chmod 755 file) or symbolic (chmod u+x file) notation. Chown changes file ownership, chgrp changes group ownership, and you can combine them with 'chown user:group file'.
Special permissions include SUID (4000), SGID (2000), and sticky bit (1000). SUID on executables runs them as the file owner rather than the user executing them. SGID on directories makes new files inherit the directory's group. Sticky bit on directories prevents users from deleting files they don't own, commonly used on /tmp.
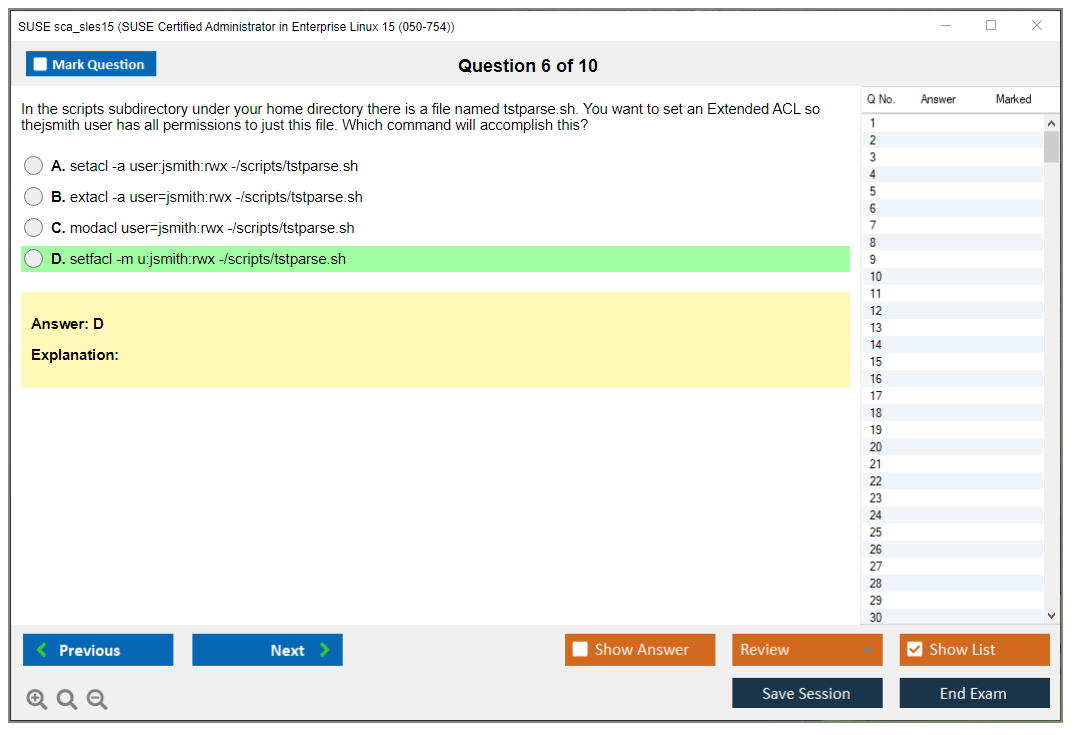
Access Control Lists (ACLs) provide fine-grained permissions beyond standard Unix permissions, using 'setfacl' and 'getfacl' commands. Default permissions come from umask settings that subtract from maximum permissions when creating new files. Troubleshooting permission issues requires checking ownership, permission bits, ACLs, and parent directory permissions systematically. Look, I've seen admins waste hours on permission problems only to discover the parent directory was blocking access the whole time.
SLES storage and networking configuration tasks
Disk partitioning tools include fdisk for MBR partitions, parted for GPT partitions, and YaST Partitioner for GUI-based management. LVM (Logical Volume Manager) provides flexible storage with physical volumes (PV), volume groups (VG), and logical volumes (LV). Creating LVM involves 'pvcreate', 'vgcreate', and 'lvcreate' commands, with resize capabilities that traditional partitions lack.
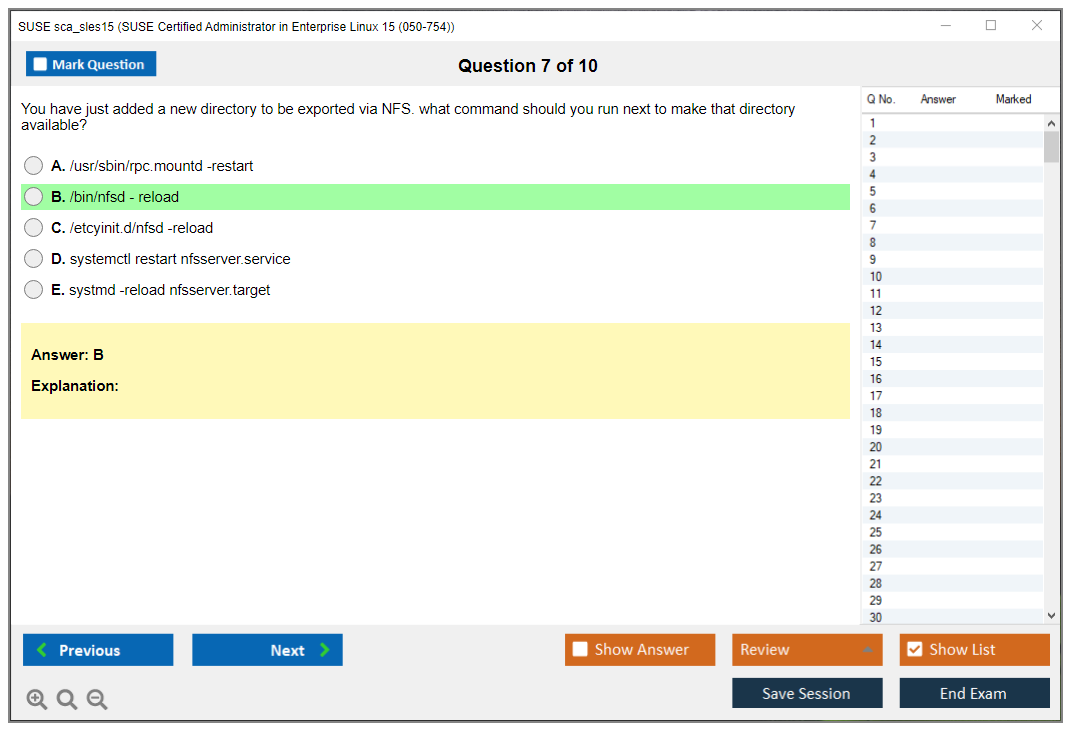
File system support includes ext4 for compatibility, XFS for large files and high performance, and Btrfs for advanced features like snapshots and copy-on-write. Formatting uses 'mkfs.ext4', 'mkfs.xfs', or 'mkfs.btrfs' commands. Mounting file systems manually uses the 'mount' command, while persistent mounts require entries in /etc/fstab. Each entry needs device, mount point, filesystem type, options, dump, and fsck fields.
Network configuration on SLES 15 uses Wicked as the network management framework. Configuring interfaces happens through YaST Network Settings or by editing files in /etc/sysconfig/network/. Static IP addresses, DNS servers, default gateways, and routing all configure here. Troubleshooting connectivity involves checking interface status with 'ip addr', testing with 'ping', verifying routes with 'ip route', and checking DNS resolution with 'nslookup' or 'dig'. Hostname configuration uses 'hostnamectl' and /etc/hostname.
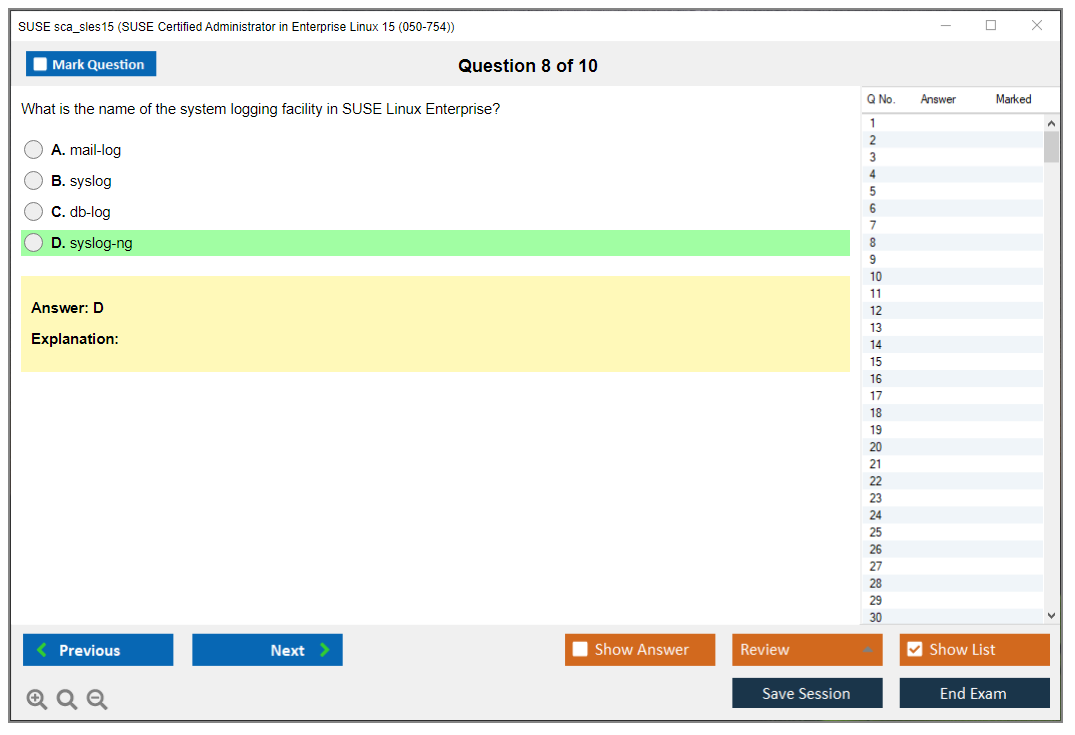
The sca_sles15 Practice Exam Questions Pack at $36.99 provides realistic questions covering storage and networking scenarios you'll face during the actual certification test.
systemd services on SLES administration
Systemd architecture uses units as the fundamental building block, with service units being most common for daemon management. Starting services uses 'systemctl start servicename', stopping uses 'systemctl stop', restarting uses 'systemctl restart', and enabling at boot uses 'systemctl enable'. Checking status requires 'systemctl status servicename' which shows current state, recent log entries, and process information.
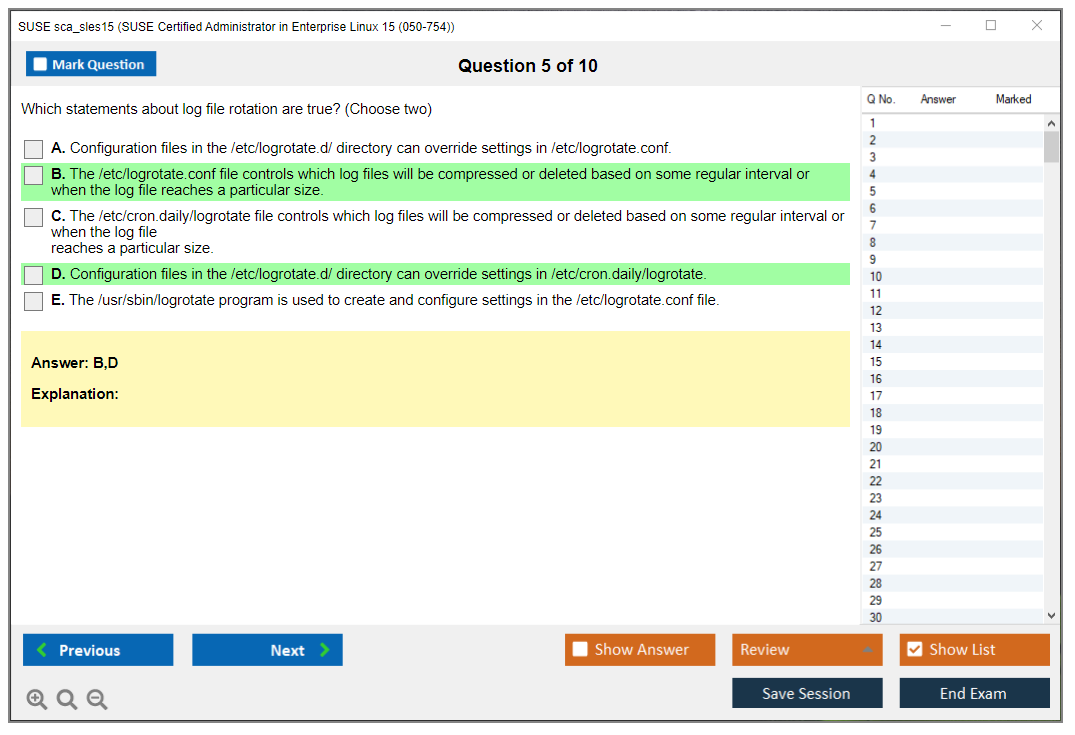
Service logs live in the systemd journal, accessed with 'journalctl' command. Viewing logs for a specific service uses 'journalctl -u servicename', while following logs in real-time adds the '-f' flag. Unit files define service behavior and live in /etc/systemd/system/ for custom units or /usr/lib/systemd/system/ for package-provided ones. Modifying unit files requires 'systemctl daemon-reload' to apply changes.
System targets group units for different system states. Multi-user.target provides command-line multi-user mode, while graphical.target adds GUI capability. Changing targets uses 'systemctl isolate targetname' or setting default with 'systemctl set-default'. Troubleshooting failed services involves checking status, reading journal logs, verifying dependencies with 'systemctl list-dependencies', and understanding unit file directives. Systemd timers replace traditional cron jobs with better logging and dependency handling.
YaST administration tasks and modules
YaST (Yet another Setup Tool) provides full system administration through text-based (ncurses) and graphical (Qt) interfaces. Launching YaST requires root privileges via 'yast2' command or menu shortcuts. Navigation differs between interfaces but covers identical functionality.
Network configuration through YaST Network Settings manages interfaces, routing, DNS, and hostname. Storage management via YaST Partitioner handles disk operations, LVM, and RAID configuration. User and Group Management provides GUI workflows for account administration. YaST Services Manager lists systemd services with start/stop/enable controls and runlevel configuration.
Software management modules include Software Management for package installation, Software Repositories for source management, and Online Update for patch application. Firewall configuration through YaST Firewall simplifies zone management and service rules. NTP time synchronization setup keeps system clocks accurate for logging and authentication. The thing is, understanding when to use YaST versus command-line tools depends on complexity, automation needs, and personal preference, but the exam tests both approaches equally.
Security fundamentals and firewall configuration
Firewalld provides dynamic firewall management on SLES 15 using zones, services, and rules. Zones define trust levels (public, internal, trusted, etc.), services represent predefined port/protocol combinations, and rules specify custom allow/deny logic. Managing firewalld uses 'firewall-cmd' command-line tool or YaST Firewall module.
AppArmor (not SELinux) provides mandatory access control on SLES 15, confining programs to limited resource sets through security profiles. Basic AppArmor administration involves checking status with 'aa-status', setting profiles to enforce or complain modes, and understanding profile locations in /etc/apparmor.d/.
SSH service security includes disabling root login, using key-based authentication instead of passwords, changing default port 22, and limiting access to specific users or groups in /etc/ssh/sshd_config. Host-based security measures cover firewall rules, service minimization, regular updates, strong authentication, and access logging. System logging to /var/log/ and journalctl provides audit trails for security analysis. Honestly, I've mixed feelings about how often admins ignore logs until something breaks, but that's another discussion entirely. Security patch compliance requires regular 'zypper patch' execution and monitoring security advisories from SUSE.
System monitoring and troubleshooting skills
Process monitoring commands include 'top' for interactive real-time view, 'htop' for enhanced interface (if installed), and 'ps' for snapshot listings. Common ps usage includes 'ps aux' for all processes or 'ps -ef' for full format. System logs in /var/log/ contain service-specific logs, while 'journalctl' accesses systemd journal with powerful filtering options.
Disk space monitoring uses 'df' to show filesystem usage and 'du' to calculate directory sizes. Finding large files or directories requires 'du -sh *' or 'find' commands with size filters. Network connection monitoring uses 'ss' (modern) or 'netstat' (legacy) to display listening ports, established connections, and routing tables.
Understanding resource utilization involves interpreting CPU load averages, memory usage (free vs cached), disk I/O wait, and network throughput. Boot troubleshooting requires accessing GRUB menu, selecting rescue or emergency targets, checking journal logs from previous boot with 'journalctl -b -1', and understanding systemd emergency mode for minimal system access. Basic performance tuning awareness includes identifying bottlenecks, adjusting service limits, and understanding when hardware upgrades make more sense than optimization. Sometimes throwing more RAM at a problem beats spending three days tweaking configuration files.
For those also interested in expanding their SUSE expertise, check out related certifications like sca_ses5 for storage administration or sca_suma4 for systems management. The broader SUSE ecosystem includes specialized tracks such as sca_caasp4 for container platforms and sca_ran2_6 for Rancher Kubernetes management.
Prerequisites and Recommended Experience
Prerequisites (required vs recommended)
SUSE's pretty laid-back about this. The official SCA SLES 15 prerequisites are basically.. well, there aren't any in the traditional gatekeeping sense. Zero formal prerequisites. No previous certifications you've gotta have. There's no "complete course X first" checkbox blocking your path. You can register for the SCA in Enterprise Linux 15 exam without a single badge on your LinkedIn, and SUSE won't bat an eye.
Training? Not required either. SUSE doesn't force you through official courses, and they're not gonna make you purchase their class before allowing exam access. Self-study and independent prep? Totally fine. Which honestly is fantastic if you're someone who learns best by building stuff, wrecking it, then fixing it at some ungodly hour with nothing but terminal windows and mounting existential dread.
Work experience minimums don't exist. Like, at all. Could be a student. Career changer. Help desk person plotting your escape. Someone whose only Linux exposure happened at home on a dusty laptop. The SUSE SCA SLES 15 certification is globally accessible regardless of educational history. No degree requirement, no mandated training provider in your region.
Language availability matters, though. The exam comes in multiple languages (English, German, Japanese, others), so if English phrasing trips you up, picking your native language can seriously change how the test feels. Different language options aren't exactly a "prerequisite," but accessibility counts, and it's worth verifying before scheduling.
Now. Required versus recommended? Different animals.
For a realistic baseline, you should already feel comfortable with Linux operating system concepts and architecture. Stuff like what processes are, how permissions function, typical config file locations, and system boot sequences at a conceptual level. You also need familiarity with command-line interfaces and shell navigation, because even with YaST available, you're living in that terminal. A lot. Basic networking knowledge helps tremendously too: TCP/IP fundamentals, DNS, routing basics. SLES admin work inevitably collides with networking, even when you're supposedly "just managing users."
Storage shows up more than expected. Understanding file systems, storage concepts, and partitioning becomes key for SLES storage and networking configuration, appearing in practical tasks like mounting drives, editing /etc/fstab, handling swap space, and not accidentally destroying systems because you confused device names.
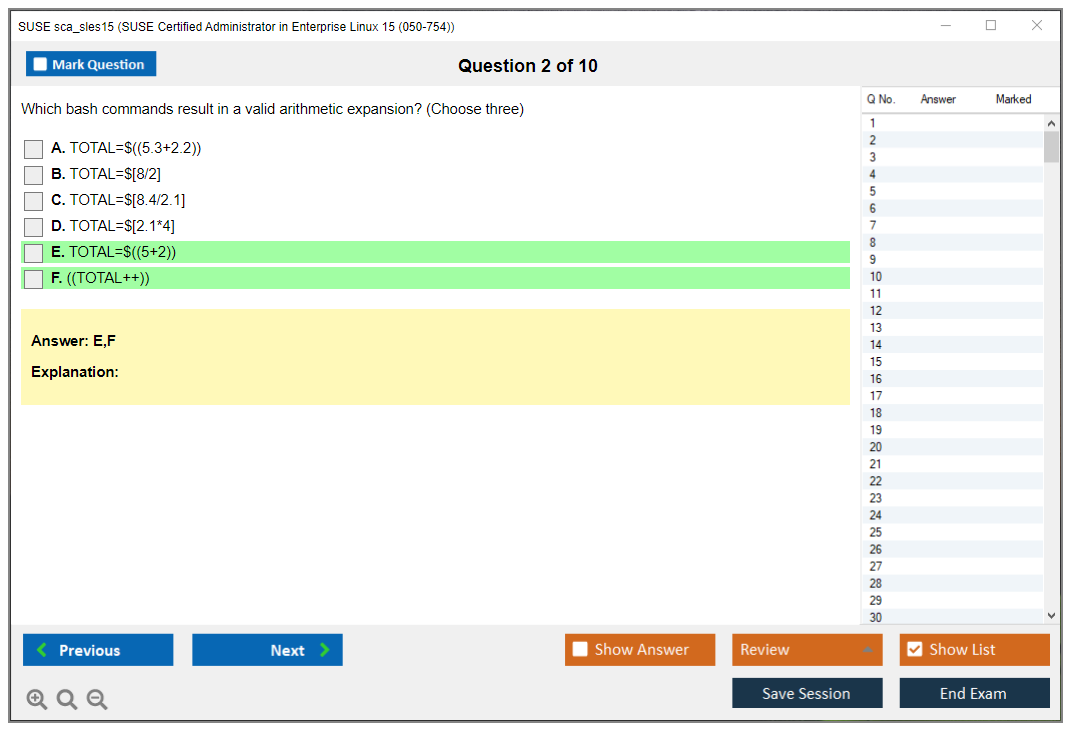
Scripting's optional, but bash awareness helps. Not "write complex 300-line scripts" level. More like you can read shell snippets, understand pipes, redirects, exit codes, maybe write quick loops without frantically Googling every symbol. Previous experience with any Linux distribution (Ubuntu, CentOS, Debian, whatever) puts you ahead since the mental model transfers even when tooling differs.
One more overlooked thing. General IT infrastructure and server administration concepts. Stuff like patch management windows, change control procedures, least privilege principles, log analysis, service dependencies, understanding what "idempotent" means practically even if you never vocalize the term. This is administration work. Not sorcery.
Also? If you're using prep products, treat them like mirrors, not crutches. I'll mention it since people constantly ask: the sca_sles15 Practice Exam Questions Pack can help sanity-check your recall speed, but it won't replace actual time spent doing YaST administration tasks, repairing broken repositories, and wrestling with systemd services on SLES when they refuse starting.
Recommended technical background and knowledge (what "ready" tends to look like)
Look. The exam's admin-focused, so "ready" typically means executing common tasks without panicking. You should comfortably work through filesystems, use ls, find, grep, sed at basic levels, and edit files with something. Anything. vi, nano, whatever functions under pressure.
Networking should hit "I can get hosts online." That means verifying IP configurations, understanding DHCP versus static assignments, confirming DNS resolution, checking routes, and wielding tools like ip, ping, ss or netstat, and curl for connectivity testing. Never diagnosed "it's always DNS" problems? You're about to learn the entertaining way.
Users and permissions? Non-negotiable. SLES 15 user and group management is constantly done on-the-job, and exams adore it because it's objectively gradable. You should create users, manage groups, set passwords, understand /etc/passwd and /etc/shadow fundamentally, and apply permissions plus ownership correctly without guessing.
Package management and updates matter considerably. On SLES that means comfort with zypper and repository management. Lived in apt or dnf previously? Fine, but don't assume identical flags and behaviors. Know how to refresh repos, install, remove, patch, verify installed packages, and know where you'd investigate when failures happen because repositories are misconfigured or unreachable.
This is where SCA SLES 15 exam objectives keep you brutally honest. Read that blueprint, then map each bullet to: "can I execute this cold?" not "have I read about it?" That's the difference between passing comfortably and having a really rough day.
Ideal hands-on experience before attempting the exam
Six to twelve months working with Linux systems in any capacity? Sweet spot. Not a hard rule. More like a consistent pattern I've observed. When you've spent months actually using Linux, even as junior admin or in lab-heavy roles, you stop treating the shell like hostile territory and start treating it like your natural workspace.
Three to six months specifically with SUSE Linux Enterprise Server 15 is the part people try skipping. And sure, you can skip it, but you'll pay through friction costs. SLES has distinct defaults, distinct tooling, and its own "SUSE way" for certain workflows. The exam expects comfort with that, not just "general Linux" vibes.
Daily command-line usage matters. So does comfort with terminal operations under time constraints, because the real challenge isn't knowing commands exist, it's remembering the correct one quickly and not making mistakes that consume five minutes undoing.
Hands-on tasks you should've done repeatedly before sitting:
User administration and permission management. Do it until tedious, then repeat, because tedious means you're fast and accurate.
Package management and system updates. Practice repository issues. Intentionally break a repo. Fix it.
Network configuration in lab or production environments. A second VM teaches what routing actually means.
Service management and troubleshooting. Start, stop, enable, check logs, interpret exit codes. Real scenarios.
Want a quick gut-check? Grab a SCA SLES 15 practice test style resource like the sca_sles15 Practice Exam Questions Pack and time yourself, but then recreate those same topics in a VM. Memorizing answers won't save you when actually configuring things.
Suggested hands-on experience and lab setup
Home labs are the cheat code. Won't lie, they're also where you build genuine confidence without risking production outages and extremely awkward meetings. Building home labs with SLES 15 virtual machines covers most admin tasks you'll encounter in exams and real junior admin work.
Minimum hardware: computer with 8GB RAM, 50GB disk space, virtualization support. More RAM's nicer. Disk is cheap. CPU matters less than you'd think unless running multiple VMs at once.
Virtualization platforms? Pick what actually runs on your setup:
VirtualBox: easiest for most, works fine.
VMware Workstation: smooth, excellent snapshots, costs money.
KVM: great if already on Linux.
Hyper-V: solid on Windows Pro.
Cloud alternatives are legitimate if your laptop's weak or you want "realistic-ish" networking. AWS EC2, Azure VMs, Google Cloud instances with SLES 15 all work, and you'll accidentally absorb cloud basics along the way. Never a bad career side effect.
Multiple VMs are recommended for networking practice. Two's enough. Three's better. One for "server," one for "client," one for "experimental destruction." Snapshot capabilities are required so you can experiment safely and rollback. You will break things, and that's precisely the point.
Also, plan for SUSE Customer Center access for registration and repositories, especially wanting authentic patching and repo experiences. Repository reality is part of SUSE Linux Enterprise Server 15 administration, and it's where tons of new admins get tripped up.
Free and trial resources to get experience (without spending a fortune)
SUSE Linux Enterprise Server 15 offers a 60-day free evaluation download. Perfect for labbing. Not ready for subscription dealings yet? OpenSUSE Leap is a free alternative for practice, and it's similar enough to SLES that your time won't be wasted, especially for CLI work, systemd, filesystems, and general admin habits.
SUSE documentation is legitimately good. The SUSE documentation portal has admin guides mapping cleanly to real tasks. Solid source of SCA SLES 15 study materials if you prefer official references over random blogs.
Community forums help when hitting weird errors. YouTube tutorials and free online Linux training resources are hit-or-miss, so be selective. GitHub repos with practice scenarios and scripts can be excellent, just don't copy-paste your way into false confidence.
Virtual lab platforms offering temporary SLES environments exist too. Nice when wanting clean sandboxes without building anything locally.
I spent three weeks once trying to troubleshoot why a particular kernel module wouldn't load on a test system, only to discover I'd been working on the wrong VM the entire time. That's the kind of mistake you make exactly once if your lab naming conventions are garbage, which mine were.
Optional SUSE training (worth it if your budget allows)
SUSE training's optional, but can seriously accelerate things. The SLE201v15: SUSE Linux Enterprise Server 15 Administration course is typically four to five days instructor-led or self-paced online, covering exam objectives with hands-on labs.
Cost usually runs $2,000 to $3,500 depending on format and region. Yeah, not cheap. People ask about SUSE Certified Administrator SLES 15 cost and often forget training's the real price tag, not the exam itself. Bundles sometimes combine training with exam vouchers at discounts. Self-paced e-learning can be cheaper.
Paying out of pocket? I'd rather see you build a serious lab and buy one quality practice resource than go broke on training. Employer paying? Take that class and don't feel guilty.
Skills assessment before you book the exam
Before committing, do self-evaluation checklists based on official SCA SLES 15 exam objectives. Rate your confidence per domain, then prove it in lab environments. Time yourself on common administrative tasks. Speed and accuracy matter more than people admit.
Review exam blueprints, build test scenarios, and take at least one timed run using something like the sca_sles15 Practice Exam Questions Pack to identify weak spots. Then go fix those weak spots with hands-on repetitions.
People also ask about SCA SLES 15 passing score and SCA SLES 15 renewal policy, and sure those details matter, but readiness is simpler than it sounds: can you execute admin tasks without help, under time pressure, on SLES 15, using both CLI and the tools SUSE expects? If the answer's "mostly," give yourself a few more weekends in the lab.
Difficulty Level and Common Challenges
Is the SUSE SCA SLES 15 certification difficult?
The difficulty? Intermediate territory. If you've done Linux admin work for a couple years, you'll find it challenging but totally doable. It's easier than RHCE, which is known for being absolutely brutal, but more demanding than CompTIA Linux+ which casts a wider net without going particularly deep into any one area.
Here's the thing though. Your mileage varies dramatically based on what you've actually been working with day-to-day. Someone who's been managing SLES 15 systems for six months will absolutely cruise through sections that make a Red Hat veteran sweat bullets. The SCA in Enterprise Linux 15 exam uses a performance-based format, meaning you're actually configuring real systems instead of just clicking through multiple choice questions where you can sometimes logic your way to the right answer, and that's where people either shine or crash hard.
Time pressure? Real.
You might know how to configure LVM inside and out, but can you do it correctly in 3 minutes while also thinking about the next seven tasks waiting for you? That's different than just knowing the concepts in theory. Pass rates hover around 60-70% for first-timers who actually prepare properly. Fair but definitely not a gimme. I mean, people who show up thinking "I use Linux every day, I'll wing it" usually regret that decision pretty quickly.
Reminds me of a guy at my last job who kept postponing his cert exam because he figured his daily work was enough prep. Eight months later he finally sat for it and failed by maybe three points. Came back shaken, muttering about how different exam pressure felt compared to fixing production issues where you can take a coffee break and think.
Who typically struggles with the SCA SLES 15 exam
The candidates who have the hardest time? Those with purely theoretical knowledge.
You know the type. They've read documentation, watched videos, maybe even memorized commands, but haven't actually broken and fixed a SLES system repeatedly. The exam doesn't care what you know in theory. It cares what you can demonstrate under pressure.
Administrators coming from other distributions face a specific challenge that catches them off guard. Look, if you've been running Ubuntu servers or CentOS for years, you're a competent Linux admin, no question. But SUSE does things differently in key areas that matter for the exam. YaST is the big one. This central configuration tool doesn't exist on other distros, and if you're unfamiliar with it, you're fighting the exam with one hand tied behind your back. I've seen RHEL experts stumble because they tried to do everything the Red Hat way instead of adapting to the SUSE approach.
Command-line proficiency matters more than people think. Not just knowing commands exist, but executing them quickly and accurately without hesitation. If you're the kind of person who needs to look up syntax for basic systemctl operations or fumbles through vim commands, you're burning precious minutes you can't get back. The exam doesn't give you time to be thoughtful about every single keystroke.
Self-taught administrators often have weird knowledge gaps. Wait, let me rephrase that. They know advanced stuff but miss fundamentals that everyone assumes they have. Maybe they never properly learned user and group management because they've always been the only person on their systems. Those gaps become obvious real fast when you're working through SCA SLES 15 exam objectives systematically.
Most challenging exam domains based on candidate feedback
Storage management consistently trips people up in ways that surprise them. LVM isn't conceptually difficult, but the practical implementation with all the correct flags, proper ordering of operations, and ensuring everything persists across reboots requires precision you don't always use in daily work. Add in advanced file system configurations, maybe some Btrfs snapshots or XFS specifics, and you've got a section where small mistakes cascade into bigger problems that eat your time.
Network configuration using the Wicked framework is SUSE-specific and many candidates underestimate it completely. If you're used to NetworkManager or traditional ifconfig-based approaches, Wicked feels foreign and slightly uncomfortable. You need to know configuration file locations, syntax, how to restart network services without losing your connection to the exam system (which is terrifying), and how to verify everything actually works. Not just "it looks right" but "I can ping the gateway and DNS resolves."
systemd service management seems straightforward until you're creating or modifying unit files under time pressure with your adrenaline pumping. The syntax is picky about details. Forgetting a single directive or putting options in the wrong section means your service won't start, and troubleshooting why takes time you don't have. People who've only ever done basic service start and stop and enable operations without diving into the actual unit file mechanics struggle here badly.
Troubleshooting scenarios? Brutal.
They require root cause analysis, not just following a recipe you memorized. The exam might present a broken system and you need to figure out what's wrong, fix it properly, and verify the fix actually works. This is where systematic troubleshooting methodology separates people who pass from people who don't. If you just start randomly trying fixes hoping something works, you'll run out of time before you solve anything.
YaST configuration tasks catch CLI purists off guard in amusing ways. Some folks have this attitude that real admins only use command line and YaST is for beginners who don't know better. Cool story, but SUSE wants you to know their tools regardless of your philosophical stance. If you've never configured storage or users or network settings through YaST, you're learning during the exam instead of executing, and that's not where you want to be.
Security implementations including firewall rules trip up people regularly. firewalld on SLES works similarly to other distros but has SUSE-specific quirks that matter. You need to know zones and services, how to make rules permanent instead of temporary, and how to verify they're actually working as intended. It's easy to add a firewall rule that looks right but doesn't actually allow the traffic because you put it in the wrong zone or forgot to reload.
Boot process troubleshooting and GRUB2 configuration requires knowledge that many admins never use in daily work because boots just work. Until they don't. Knowing how to interrupt the boot process, modify boot parameters, fix broken GRUB configurations, and understand the boot sequence becomes critical when exam tasks specifically test this area that you probably haven't touched in months.
Common technical pitfalls and mistakes
The single biggest mistake? Forgetting to persist configurations across reboots.
You make a change, it works right now, you move on feeling accomplished. Then if the exam scenario involves a reboot or if grading simulates one, your configuration is gone and you've failed that task. Network settings especially. If you only modify the running configuration without updating the persistent config files, you've failed that task even though it "worked" when you tested it initially.
Making changes that aren't saved to configuration files is similar but slightly different in execution. Maybe you edit /etc/hosts but forget to actually save the file before closing. Maybe you modify a service file but don't reload the systemd daemon afterward. These are careless mistakes that happen when you're rushing through tasks.
Typographical errors kill people's scores. A misspelled directory path. A wrong IP address where you transposed two digits. A service name with a typo. The thing is, the exam doesn't give partial credit for "close enough" or good intentions. Either the configuration works or it doesn't. And when you're moving fast, these errors creep in easily.
Not verifying task completion before moving to the next objective is a time management failure that becomes a technical failure down the line. You think you configured something correctly, you move on feeling confident, and you never actually tested whether it works. Then during grading, it doesn't work, and you have no idea because you never checked. Taking 30 seconds to verify each task saves you from having to come back and fix it later when you're panicking.
Misconfiguring permissions leads to service failures that aren't immediately obvious when you're rushing. You create a file that a service needs to read, but the permissions are wrong, so the service fails to start silently. You didn't check the service status. You just assumed it worked because you created the file, and now you've lost points. Or you set up a directory for users but the ownership is wrong so nobody can actually access it even though the directory exists.
Incorrect repository configuration preventing package installation is frustrating because it seems simple until it isn't and you're stuck. Maybe the repo URL is wrong. Maybe the GPG key isn't imported. Maybe the priority is misconfigured in ways you don't immediately recognize. You try to install a package and it fails, and now you're debugging repository configuration instead of completing the actual task you were assigned.
Firewall rules blocking required services happens all the time to otherwise competent admins. You set up a web server, you verify it's running with systemctl, but you forgot to allow HTTP through the firewall. From the exam system's perspective, the service isn't accessible, so the task is incomplete regardless of the service status. Always verify services are accessible, not just running locally.
Not enabling services to start automatically at boot is another persistence issue that costs points unnecessarily. You start the service manually. It's running right now. Task complete, right? Wrong. If the service doesn't survive a reboot because you didn't enable it properly, you failed that objective. systemctl start versus systemctl enable. Both are necessary, and forgetting one means failure.
Time management challenges
Spending too much time on difficult tasks early in the exam is a classic trap that snares people repeatedly. You hit a hard troubleshooting scenario in the first 20 minutes. You get fixated on solving it because you know you can. Suddenly 45 minutes are gone and you've completed one task out of twenty. Better to skip it, complete easier tasks, and come back if time permits at the end.
The exam objectives have different point values, but not everyone allocates time proportionally based on those values. If a task is worth 2% of your grade and another is worth 10%, don't spend equal time on them. That's inefficient. Knock out the high-value tasks first, ensure those are solid, then work through the smaller stuff that matters less.
Getting stuck on troubleshooting without moving forward is how people fail exams they could have passed if they'd just been strategic. You're stuck on one broken service. You keep trying different fixes methodically. Nothing works. You refuse to move on because you "should" be able to fix this simple thing. Meanwhile, there are fifteen other tasks you could be completing and earning points on right now. Learning when to cut your losses is hard but necessary for passing.
Rushing through easier tasks and making careless mistakes because you're trying to "bank time" for harder sections backfires spectacularly. You speed through user creation and make typos in usernames. You quickly configure a network interface and transpose digits in the IP address. These should be gimme points that boost your score, but rushing turns them into failures.
Not reading task requirements carefully before beginning wastes time on the back end when you realize your mistake. You configure something, then realize you misread the requirement and have to redo it completely. That's demoralizing. Take the extra 15 seconds up front to read carefully and understand exactly what's being asked. It'll save you minutes later and reduce stress significantly.
The SUSE Certified Administrator in Enterprise Linux 15 exam tests your ability to perform under pressure as much as your technical knowledge, and understanding these challenges helps you prepare more effectively than just studying technical content alone.
Conclusion
Wrapping up your SCA SLES 15 path
Look, the SUSE SCA SLES 15 certification isn't just another cert to toss on your resume. Honestly, it's proof you can actually manage SUSE Linux Enterprise Server 15 administration in real production environments, not just answer multiple-choice questions. The SCA in Enterprise Linux 15 exam tests you on stuff you'll use daily. YaST administration tasks, systemd services on SLES, and the kind of SLES storage and networking configuration that keeps systems running when everyone's counting on you.
Passing this exam takes more than reading docs for a week. You need hands-on time.
The SCA SLES 15 exam objectives cover everything from basic SLES 15 user and group management to troubleshooting services that mysteriously stop working at 3 AM. You'll encounter those exact scenarios once you're certified and actually doing the work. The SUSE Certified Administrator SLES 15 cost isn't cheap. You're looking at around $349, so going in unprepared is basically lighting money on fire.
Here's what I'd do if I were starting today. Build a lab. I can't stress this enough because you need actual SLES 15 machines to break and fix. The SCA SLES 15 prerequisites are pretty reasonable (basic Linux knowledge mostly), but that doesn't mean the exam's easy. Time management absolutely kills people on this one. You've got performance-based tasks, and if you spend twenty minutes fumbling through man pages for a systemd command you should've memorized, you're toast.
For SCA SLES 15 study materials, mix it up. Official SUSE training is solid but expensive. Community resources help. Practice tests matter a lot though, not the brain dump garbage, but actual scenario-based questions that make you think like you're solving a real problem. That's what separates people who pass from those who don't. The SCA SLES 15 passing score sits around 70%, which sounds generous until you realize how easy it is to mess up a few configuration tasks and tank your score.
I once watched a guy in a forum complain about failing because he configured permissions correctly but forgot to restart the service. Rookie mistake, but it happens when you're nervous.
Don't sleep on the SCA SLES 15 renewal policy either. Certs expire. Technology moves fast. SUSE releases new versions. Plan ahead or you'll be recertifying sooner than you expected.
If you're serious about passing on your first attempt, grab the sca_sles15 Practice Exam Questions Pack. It's one of the better SCA SLES 15 practice test resources out there. Questions that actually mirror the exam format and difficulty, not the watered-down stuff you find on random forums. Some folks combine this with video courses, which works too. Use it to identify your weak spots, then hit the lab hard on those areas. That's how you pass without retaking and paying that exam fee twice.