SPLK-3001 Practice Exam - Splunk Enterprise Security Certified Admin Exam
Reliable Study Materials & Testing Engine for SPLK-3001 Exam Success!
Exam Code: SPLK-3001
Exam Name: Splunk Enterprise Security Certified Admin Exam
Certification Provider: Splunk
Certification Exam Name: Splunk Enterprise Security Certified Admin

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
SPLK-3001: Splunk Enterprise Security Certified Admin Exam Study Material and Test Engine
Last Update Check: Mar 19, 2026
Latest 97 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena Splunk Splunk Enterprise Security Certified Admin Exam (SPLK-3001) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
Splunk SPLK-3001 Exam FAQs
Introduction of Splunk SPLK-3001 Exam!
The SPLK-3001 exam is an exam that tests an individual's knowledge of Splunk Enterprise Security (ES). It covers topics such as architecture, deployment, configuration, data collection, data analysis, threat detection, incident response, and compliance.
What is the Duration of Splunk SPLK-3001 Exam?
The duration of the Splunk SPLK-3001 exam is 90 minutes.
What are the Number of Questions Asked in Splunk SPLK-3001 Exam?
There are 90 questions in the Splunk SPLK-3001 exam.
What is the Passing Score for Splunk SPLK-3001 Exam?
The passing score required for the Splunk SPLK-3001 exam is 70%.
What is the Competency Level required for Splunk SPLK-3001 Exam?
The Splunk SPLK-3001 exam requires a Competency Level of Expert.
What is the Question Format of Splunk SPLK-3001 Exam?
The Splunk SPLK-3001 exam includes multiple-choice questions and scenario-based questions.
How Can You Take Splunk SPLK-3001 Exam?
Splunk SPLK-3001 exam can be taken online or in a testing center. The online version of the exam is administered by Pearson VUE and can be taken from any location with an internet connection. The in-person exam is administered by a proctor at a designated testing center.
What Language Splunk SPLK-3001 Exam is Offered?
The Splunk SPLK-3001 exam is offered in English.
What is the Cost of Splunk SPLK-3001 Exam?
The cost of the Splunk SPLK-3001 exam is $200 USD.
What is the Target Audience of Splunk SPLK-3001 Exam?
The target audience of the Splunk SPLK-3001 exam are IT professionals who want to demonstrate their expertise in Splunk Enterprise Security, Splunk Core Certified User, Splunk Core Certified Power User, and Splunk Core Certified Consultant.
What is the Average Salary of Splunk SPLK-3001 Certified in the Market?
The average salary for someone with Splunk SPLK-3001 certification is around $90,000 per year. This figure can vary depending on experience and location.
Who are the Testing Providers of Splunk SPLK-3001 Exam?
Splunk offers official practice tests for the SPLK-3001 exam. These practice tests are available for purchase on the Splunk website. Additionally, there are several third-party websites that offer practice tests for the SPLK-3001 exam.
What is the Recommended Experience for Splunk SPLK-3001 Exam?
The recommended experience for the Splunk SPLK-3001 exam is having at least two years of experience in Splunk Administration, including knowledge of Splunk architecture, data ingestion, data storage, indexing, search, and reporting. Additionally, experience with Splunk's distributed search and indexing, deployment server, and knowledge objects is recommended.
What are the Prerequisites of Splunk SPLK-3001 Exam?
The Prerequisite for Splunk SPLK-3001 Exam is having a basic knowledge of Splunk and its core features. Candidates should also have a basic understanding of the Splunk platform, including Splunk Enterprise and Splunk Cloud. Additionally, they should have a working knowledge of the Splunk Search Processing Language (SPL).
What is the Expected Retirement Date of Splunk SPLK-3001 Exam?
The official website for Splunk SPLK-3001 exam does not provide any information about the expected retirement date for the exam. However, you can contact Splunk Support for more information.
What is the Difficulty Level of Splunk SPLK-3001 Exam?
The difficulty level of the Splunk SPLK-3001 exam is considered to be intermediate. The exam is designed to test the knowledge and skills of Splunk professionals in the areas of Splunk core components, Splunk administration, Splunk data models, Splunk search language, Splunk data analytics, and Splunk security.
What is the Roadmap / Track of Splunk SPLK-3001 Exam?
The certification roadmap for Splunk SPLK-3001 exam is as follows:
1. Sign up for the Splunk Certified Architect (SCA) program.
2. Acquire the necessary experience and skills to pass the SPLK-3001 exam.
3. Register for the SPLK-3001 exam.
4. Study for the exam using the Splunk Certified Architect (SCA) study guide.
5. Take the SPLK-3001 exam.
6. Receive your Splunk Certified Architect (SCA) certification.
What are the Topics Splunk SPLK-3001 Exam Covers?
The Splunk SPLK-3001 exam covers the following topics:
1. Splunk Fundamentals: This section covers the basic concepts of Splunk, including installation, configuration, and data management. It also covers the Splunk Web UI, search and reporting, and data ingestion.
2. Splunk Administration: This section covers the administration of Splunk, including user management, security, and troubleshooting.
3. Splunk Dashboards and Visualizations: This section covers the creation of dashboards and visualizations in Splunk, including the creation of custom visualizations and dashboards.
4. Splunk Data Analysis: This section covers the analysis of data in Splunk, including the use of Splunk’s search language and the use of Splunk’s data analysis tools.
5. Splunk Machine Learning: This section covers the use of machine learning algorithms in Splunk, including the use of Splunk
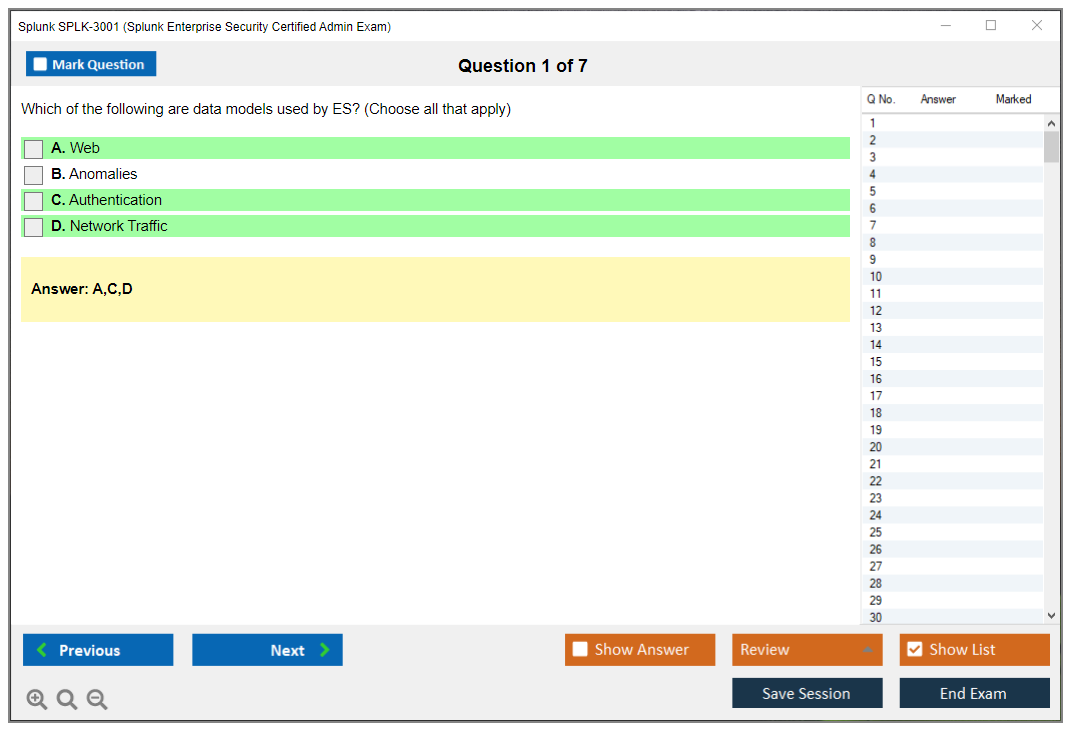
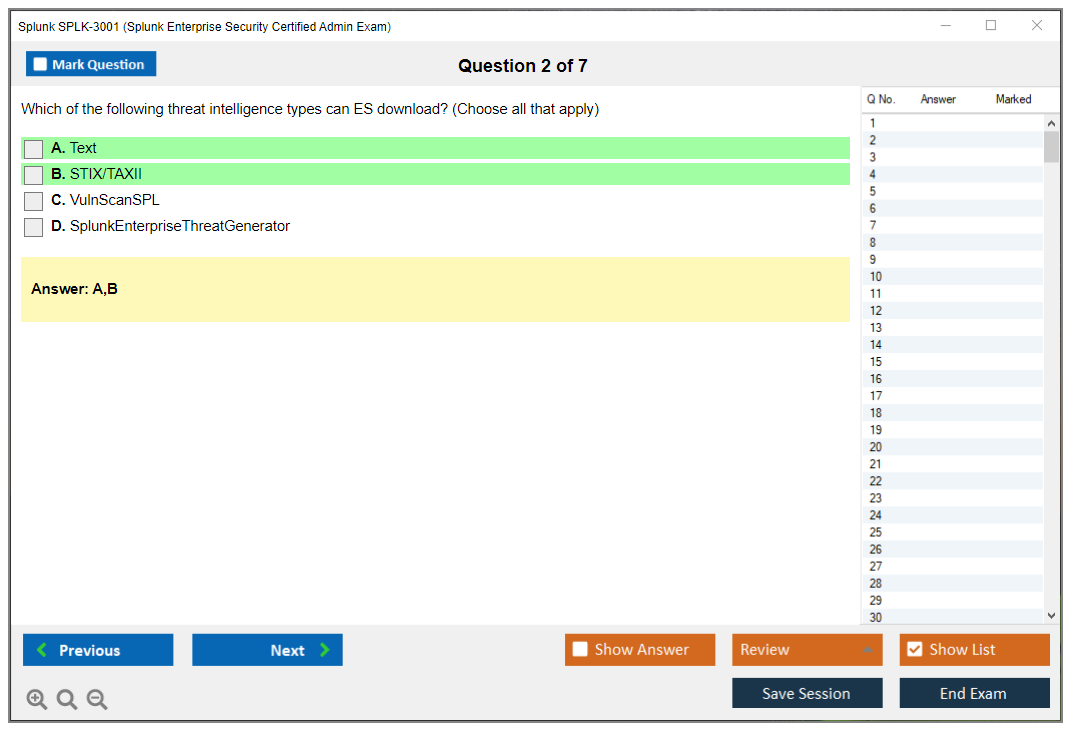
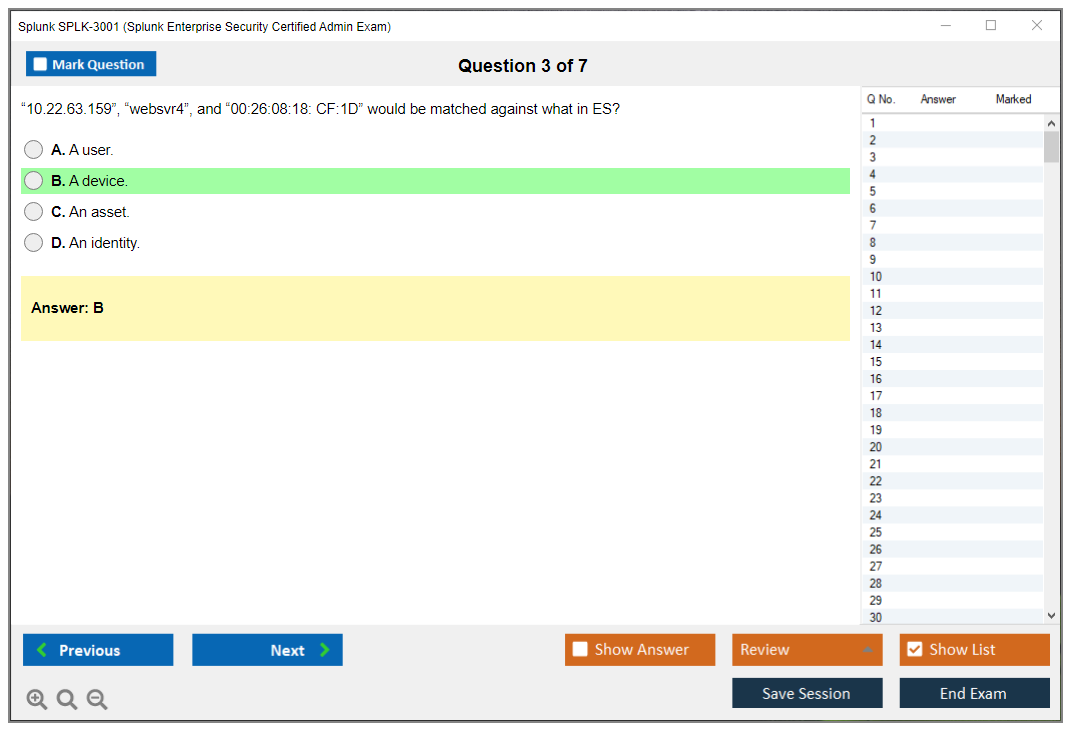
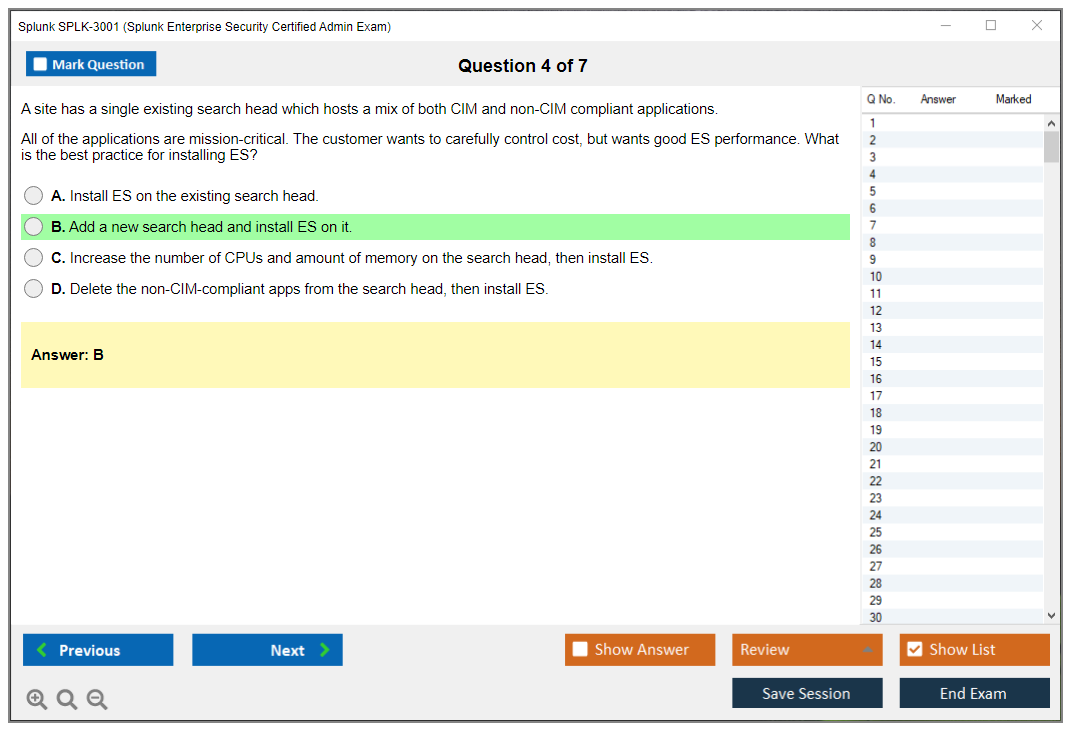
What are the Sample Questions of Splunk SPLK-3001 Exam?
1. What are the primary components of Splunk Enterprise?
2. How does Splunk Enterprise process and index data?
3. What are the main benefits of using Splunk Enterprise?
4. How do you configure Splunk Enterprise to collect data from different sources?
5. What are the different ways to search and analyze data in Splunk Enterprise?
6. What are the different ways to visualize data in Splunk Enterprise?
7. How do you set up alerting and reporting in Splunk Enterprise?
8. How do you monitor and manage Splunk Enterprise?
9. What are the best practices for security and managing user access in Splunk Enterprise?
10. How do you troubleshoot and optimize Splunk Enterprise performance?
Splunk SPLK-3001 (Splunk Enterprise Security Certified Admin Exam) Splunk SPLK-3001 Exam Overview: Splunk Enterprise Security Certified Admin Certification Introduction to the Splunk Enterprise Security Certified Admin certification The SPLK-3001 exam validates advanced administrative skills in Splunk Enterprise Security, which is Splunk's premium SIEM solution built specifically for security operations centers and threat detection teams. This is not your basic cert. This one's about running ES in production environments where real security incidents are happening and your tuning decisions directly impact whether your SOC drowns in false positives or actually catches threats before they cause damage. The kind of damage that gets people fired or makes headlines. Enterprise Security sits on top of Splunk Enterprise and provides pre-built security content, correlation searches, risk scoring frameworks, threat intelligence integrations, and incident review workflows that security teams... Read More
Splunk SPLK-3001 (Splunk Enterprise Security Certified Admin Exam)
Splunk SPLK-3001 Exam Overview: Splunk Enterprise Security Certified Admin Certification
Introduction to the Splunk Enterprise Security Certified Admin certification
The SPLK-3001 exam validates advanced administrative skills in Splunk Enterprise Security, which is Splunk's premium SIEM solution built specifically for security operations centers and threat detection teams. This is not your basic cert. This one's about running ES in production environments where real security incidents are happening and your tuning decisions directly impact whether your SOC drowns in false positives or actually catches threats before they cause damage. The kind of damage that gets people fired or makes headlines.
Enterprise Security sits on top of Splunk Enterprise and provides pre-built security content, correlation searches, risk scoring frameworks, threat intelligence integrations, and incident review workflows that security teams need. The SPLK-3001 certification proves you can deploy ES, configure its security-specific features, manage the detection content that generates alerts, tune risk-based alerting to reduce noise, and keep the whole system running smoothly while your security analysts hunt threats and respond to incidents.
If you're working with ES in any serious capacity (whether you're the admin keeping it running, the SOC engineer tuning detections, or the consultant implementing it for clients) this certification demonstrates you know what you're doing beyond just clicking through dashboards.
Certification positioning in Splunk's credential ladder
SPLK-3001 sits above foundational Splunk certifications in the credential hierarchy. You're expected to already understand core Splunk concepts like indexes, search processing language, data inputs, and basic administration before you tackle ES-specific topics. Most people pursuing this cert already have their Splunk Enterprise Certified Admin credential or equivalent hands-on experience, because ES administration builds directly on those foundational skills.
The certification targets professionals who deploy, configure, and maintain ES environments in production security monitoring operations. Not an entry-level cert. You need to understand both Splunk administration and security operations workflows to succeed here, which puts it firmly in the intermediate-to-advanced range of Splunk's certification portfolio.
Unlike the Splunk Core Certified Power User which focuses on search and reporting, or the Splunk Core Certified Consultant which covers implementation methodology, SPLK-3001 zeros in exclusively on security-specific ES features, content management, and SOC workflow optimization. The questions assume you're making decisions about correlation search tuning, risk scoring models, and security data onboarding, not just running reports or managing indexes. Actually, I spent three years working with a team that thought they could tune ES by adjusting index retention policies, which tells you something about how misunderstood the platform can be even by experienced Splunk people.
Primary audience and career stage
This certification is ideal for several distinct professional profiles. Splunk administrators transitioning into security roles make up a big chunk of candidates. They already know Splunk inside and out, and now they're taking on ES responsibilities as their organization builds out its SOC capabilities. These folks need to understand how security operations differ from general Splunk use cases.
SOC engineers managing ES deployments represent another core audience. They're responsible for keeping ES healthy, tuning detections, managing notable events, and ensuring analysts have the tools they need to investigate threats efficiently. For them, this cert validates the technical depth they've developed through daily hands-on work.
Security analysts responsible for ES tuning also pursue SPLK-3001, especially as they advance from Tier 1 reactive investigation work into Tier 2/3 roles where they're modifying correlation searches and optimizing detection logic. Consultants implementing ES for clients need this certification to demonstrate competency because clients paying for ES implementations expect certified professionals who can configure the system properly from day one.
If you're working in managed security services, this cert becomes almost required because you're deploying and maintaining ES across multiple client environments with different security requirements.
Certification value proposition
The SPLK-3001 demonstrates expertise in ES administration including correlation search management, risk-based alerting configuration, data onboarding for security use cases, and notable event workflow optimization. It covers the critical administrative functions that keep ES running effectively as a detection and response platform.
Correlation search management means you can create, modify, and tune the searches that generate security alerts. This is not just writing SPL. It's understanding how to structure searches for real-time detection, how to reduce false positives without missing real threats, and how to optimize search performance so you're not killing your search heads during peak hours.
Risk-based alerting configuration is where ES really differentiates itself from basic alerting approaches. Instead of generating a notable event every time a single suspicious activity occurs, RBA accumulates risk scores across multiple events and triggers alerts when cumulative risk crosses thresholds. Administering this framework requires understanding risk objects, risk modifiers, risk attribution, and how to tune risk scoring models to match your organization's threat profile.
Data onboarding for security use cases goes beyond basic Splunk data inputs. You need to map security data sources to the Common Information Model, validate field extractions match CIM expectations, and ensure data is properly normalized so correlation searches and data models work correctly. Get this wrong and your detections won't fire when they should.
Industry recognition and employer demand
Organizations running Splunk ES highly value this certification when hiring. Security service providers and managed security service providers specifically look for SPLK-3001 certified professionals because they need people who can hit the ground running on client ES deployments without extensive training. Enterprises with mature security operations programs also prioritize this cert when building internal SOC teams.
Demand for ES skills has grown significantly as more organizations adopt SIEM platforms and build out security operations capabilities. The certification provides a standardized way for employers to assess candidate skills without having to design complex technical interviews covering every ES administration topic.
Professionals with SPLK-3001 certification typically command higher compensation than general Splunk admins because they bring specialized security expertise. The intersection of Splunk technical skills and security operations knowledge is valuable, and the cert proves you have both.
Differentiation from other Splunk certifications
Unlike the Splunk Enterprise Certified Admin which covers general platform administration, SPLK-3001 focuses exclusively on security-specific ES features and workflows. You will not spend time on basic index management or deployment architecture. Those are prerequisites. Instead, you're deep in correlation searches, notable event workflows, threat intelligence integrations, and risk scoring frameworks.
The Splunk Certified Cybersecurity Defense Analyst certification focuses on using Splunk for security analysis and investigation, while SPLK-3001 focuses on administering and maintaining the ES platform itself. One is about being an effective analyst, the other is about keeping the platform running and optimized for analysts to do their jobs.
If you're comparing to Splunk IT Service Intelligence Certified Admin, that cert covers ITSI administration for IT operations use cases, while SPLK-3001 covers ES administration for security operations. Different premium apps, different use cases, different administrative challenges.
Real-world application
Certification holders can architect ES deployments from scratch, making decisions about search head clustering for ES, indexer tier sizing for security data volumes, and how to distribute ES components for high availability. These are not theoretical exercises. They're decisions that impact whether your ES environment can handle your security data at scale.
Tuning detection content to reduce false positives is probably the most valuable real-world skill validated by this cert. Every SOC struggles with alert fatigue, and knowing how to modify correlation searches, adjust thresholds, add filtering logic, and implement suppression rules without breaking detections is critical. You'll implement risk-based alerting frameworks that move beyond simple threshold alerting to more sophisticated risk accumulation models.
Integrating threat intelligence feeds and using those indicators in correlation searches and investigations extends your detection capabilities beyond internal data. You need to configure threat intelligence framework settings, manage threat intelligence sources, and create correlation searches that reference threat indicators appropriately.
Optimizing incident response workflows means configuring notable event fields, customizing incident review dashboards, implementing status workflows that match your SOC processes, and setting up automated response actions that execute when specific notable events are created.
Who should pursue this certification
Splunk administrators expanding into security represent an obvious candidate pool. If you've already earned your Splunk Enterprise Certified Admin credential and your organization is deploying ES or expanding ES usage, SPLK-3001 is the natural next step. You already understand Splunk fundamentals, so you can focus on learning ES-specific features and security operations workflows.
Security operations center analysts at Tier 2 or Tier 3 levels who are responsible for managing detection rules, tuning alerts, and maintaining ES infrastructure should pursue this certification. If you're the person other analysts come to when correlation searches are not working or when false positive rates are too high, formalizing that expertise with SPLK-3001 makes sense for career progression.
Security engineers and architects designing and implementing ES solutions need this certification to validate their technical depth. Whether you're building a new SOC from scratch or migrating from a legacy SIEM to Splunk ES, the cert demonstrates you understand the full range of ES capabilities and administration requirements.
Managed security service provider staff (consultants and engineers deploying and maintaining ES for multiple client environments) benefit significantly from SPLK-3001 certification. Clients expect certified professionals, and the cert provides credibility when you're making recommendations about ES architecture, data onboarding, and detection content tuning.
Skills and competencies validated
The exam validates your ability to deploy and configure Splunk Enterprise Security environments, including installation, initial configuration, distributed ES architectures, and performance optimization. You need to understand ES components like the correlation search scheduler, risk framework, asset and identity management, and how they interact with underlying Splunk infrastructure.
Managing security content and correlation searches covers creating, modifying, and tuning correlation searches for threat detection, managing notable event generation, and optimizing search performance for real-time security monitoring. This includes understanding correlation search types, scheduling considerations, throttling, and how to structure searches for efficiency.
Implementing and administering risk-based alerting means configuring risk objects, creating risk rules, tuning risk scoring models, and implementing adaptive response frameworks based on cumulative risk scores. You'll work with risk modifiers, risk attribution to systems and users, and risk notable event generation thresholds.
Onboarding security data sources and applying CIM normalization requires mapping diverse security data to the Common Information Model, validating data normalization, and ensuring proper field extraction for security analytics. This is where many ES implementations struggle. If your data does not map correctly to CIM, your out-of-the-box content will not work.
Configuring threat intelligence integrations involves integrating threat intelligence feeds, configuring threat intelligence framework settings, and using threat indicators in correlation searches and investigations. Managing incident review workflows includes configuring notable event workflows, implementing triage processes, customizing incident review dashboards, and optimizing analyst efficiency.
Administrative responsibilities covered
Administering ES user roles and permissions goes beyond basic Splunk role management. You're configuring ES-specific roles, managing access controls for sensitive security data, and implementing least-privilege access for security operations teams. ES has its own role structure that layers on top of Splunk roles.
Tuning and optimizing ES performance involves reducing false positives through correlation search tuning, optimizing data model acceleration, managing ES resource utilization, and improving detection accuracy. Performance issues in ES directly impact security operations. Slow searches delay threat detection, and resource contention affects the entire Splunk environment.
Implementing ES integrations and adaptive response actions means configuring automated response actions, integrating with SOAR platforms like Splunk SOAR, and implementing orchestrated response workflows that execute automatically when specific conditions are met. Maintaining ES content updates and upgrades requires managing ES content updates, testing new correlation searches before deployment, and performing ES version upgrades while maintaining operational continuity.
Troubleshooting ES issues includes diagnosing correlation search failures, resolving data model acceleration issues, troubleshooting notable event generation problems, and optimizing ES component health. You need to understand ES logs, health checks, and common failure modes.
Exam format and delivery
The SPLK-3001 exam is delivered online through Pearson VUE or at Pearson VUE testing centers. You'll have 57 minutes to complete approximately 50 questions, which makes time management critical. That's barely over a minute per question, and some questions require reading scenarios and analyzing configuration options.
Question types include multiple choice and multiple select, with scenario-based questions that present a situation and ask you to identify the correct administrative action or troubleshooting step. These scenario questions test applied knowledge, not just memorization of features.
The exam is proctored whether you take it online or at a testing center. Online proctoring requires a webcam, stable internet connection, and a quiet testing environment where the proctor can verify you're alone and not accessing unauthorized materials.
Exam cost and investment
The SPLK-3001 exam costs $125 USD as of current pricing, which is relatively affordable compared to some vendor certifications. Regional pricing variations may apply depending on your location, and taxes may be added at checkout based on your jurisdiction.
Compared to the value of the certification for career advancement and the relatively focused scope of the exam, $125 is reasonable. One successful job change or promotion enabled by the cert easily justifies the investment.
Retake costs are the same as the initial exam fee, so budget for potential retakes if you're not confident in your preparation. Some candidates pass on the first attempt, others need a second try, especially if they underestimate the depth of ES-specific knowledge required.
Passing score and results
Splunk uses scaled scoring for the SPLK-3001 exam with a passing score of 700 out of 1000. This scaled scoring approach means raw question counts do not directly translate to your final score. Question difficulty and importance are weighted in the scoring algorithm.
You'll receive your results immediately after completing the exam. Pass or fail, you'll know right away, and you'll get a score report showing performance in each exam domain. If you do not pass, the score report helps identify weak areas to focus on for a retake.
The scaled scoring system means you do not need to answer every question correctly to pass. You need to demonstrate sufficient competency across all exam domains, with stronger performance in heavily weighted areas compensating somewhat for weaker performance in lighter-weighted sections.
Exam objectives and domain breakdown
Security content and detections covers correlation searches, notable events, detection logic, search optimization, and content management. This domain typically represents the largest portion of exam questions because it's central to ES administration.
Risk-Based Alerting administration includes risk objects, risk rules, risk scoring models, risk attribution, risk notable events, and tuning risk thresholds. RBA is a defining feature of ES, so expect detailed questions about how the risk framework operates.
Data onboarding, CIM, and normalization covers mapping security data to CIM, validating field extractions, troubleshooting normalization issues, and ensuring data models accelerate correctly. CIM knowledge is critical here. If you do not understand CIM data models, you'll struggle with multiple exam domains.
Threat intelligence, ES inputs, and integrations includes threat intelligence framework configuration, threat intelligence sources, integrating threat feeds, and using threat indicators in detections. Incident review workflows, triage, and tuning covers notable event workflows, status management, incident review dashboard customization, and analyst workflow optimization.
Prerequisites and recommended preparation
There are no strict prerequisites for registering for the SPLK-3001 exam, but Splunk recommends six months of ES administration experience before attempting it. Trying to pass this without hands-on ES experience is tough. The scenario questions assume you've dealt with real ES administration challenges.
You should be comfortable with Splunk Search Processing Language, understand Splunk architecture, and have basic Splunk administration skills before focusing on ES-specific topics. The Splunk Enterprise Certified Admin certification or equivalent experience provides that foundation.
Familiarity with security operations workflows, common security data sources, and basic threat detection concepts helps significantly. If you've never worked in a SOC or do not understand how security analysts investigate incidents, some exam scenarios may be harder to parse.
Get hands-on practice with ES in a lab environment if you're not working with it daily. Build correlation searches, configure risk rules, onboard security data sources, and practice tuning detections. Reading documentation without practical application will not prepare you adequately for scenario-based questions.
SPLK-3001 Exam Details: Format, Cost, and Passing Score
Splunk SPLK-3001 exam overview (Splunk Enterprise Security Certified Admin)
The Splunk SPLK-3001 Splunk Enterprise Security Certified Admin exam is officially the Splunk Enterprise Security Certified Admin Exam (SPLK-3001), and it sits inside Splunk's professional certification program for people who run security operations on Splunk Enterprise Security. Advanced stuff. Professional-level. Not a "I watched a video" badge, honestly.
This cert's for security-focused Splunk admins who already live inside ES, and I mean really live there. People who've actually deployed it, upgraded it, fixed weird ingestion problems at 2 a.m., tuned noisy detections, and argued about CIM mapping with an engineering team that swears their logs are "already normalized" even though you both know that's complete nonsense.
It's also a very different vibe than generic Splunk admin tests. ES has opinions. SOC workflows have friction. And the exam expects you to know how ES behaves when the data's messy, the content's too loud, and the analysts are clicking "dismiss" on everything because they've lost trust.
Who the certification is for
Security-first Splunk administrators. ES platform owners. People who manage correlation searches, notable event rules, risk scoring, and the daily "why is incident review empty" drama.
Some consultants fit too, but honestly, if you haven't owned an ES deployment for real, the scenario questions will feel like a foreign language. The thing is, there's no substitute for actually dealing with production ES chaos.
Skills validated (what you'll be able to do after passing)
Passing the Splunk Enterprise Security Certified Admin certification signals you can administer ES like a grown-up. Not perfect. Just capable.
You should be able to manage Splunk Enterprise Security administration tasks across content, users, data onboarding, and operations. You should be able to reason through realistic SOC scenarios where the correct move isn't "restart Splunk and pray", it's understanding what knob to turn and what downstream thing you're about to break when you turn it.
SPLK-3001 exam details
This is the section everyone skims. Don't. The format matters.
You'll typically see 60 to 70 questions. Exact count can vary a bit by version. The time limit is 120 minutes. Two hours. No mercy. That works out to roughly 1.5 to 2 minutes per question, but that average's a lie because scenario questions will eat your clock if you let them.
Also, the exam delivery has evolved. You can take it at Pearson VUE testing centers or online via OnVUE. I mean, that flexibility's great, but online proctoring comes with its own nonsense, like being asked to show your desk, your wrists, your ears, your soul. Wait, what was I saying? Oh right, testing logistics.
Language-wise, it's primarily English. Splunk may add other languages depending on regional demand and their localization plans, but you should assume English unless Splunk's certification page says otherwise for your region.
Exam format (question types, time limit, delivery)
Question types include:
- multiple-choice single-answer
- multiple-choice multiple-answer
- scenario-based questions where you analyze an ES configuration, workflow, tuning choice, or troubleshooting path
The scenario-based emphasis's real. A significant chunk of the exam feels like "you're in a SOC, notables are spiking, risk scores are useless, and your CIM mapping's half-baked, what do you do first and why". Some questions are straightforward. Many aren't. Fragments. Screens-in-your-head type stuff.
Delivery options:
- In-person at Pearson VUE test centers worldwide
- Online proctored via OnVUE for remote testing
Online proctoring requirements are the usual checklist: reliable internet, webcam, microphone, private room, government-issued ID, and a system test before exam day. Do the system test. Seriously. Don't be the person troubleshooting browser permissions five minutes before check-in.
You can mark questions for review and come back to them. That's a lifesaver. There's no scheduled break, and if you do a bathroom run, the timer keeps going. Closed-book too, so no Splunk docs, no notes, no second monitor with CIM fields open. And a calculator's basically irrelevant here because this exam's about ES administration decisions, not math.
Exam cost
As of 2026, the SPLK-3001 exam cost is $250 USD. That can shift, so verify on Splunk's official certification site before you budget anything.
Regional pricing variations happen. Currency conversion, local taxes, maybe regional pricing policies. So you might see a slightly different total depending on country.
Payment methods typically include major credit cards like Visa, MasterCard, American Express, plus PayPal. Some corporate-sponsored folks can use purchase orders, depending on how their company buys training.
Retakes sting. If you fail, the retake fee's usually the same $250 USD, with a typical 15-day waiting period between attempts. Not gonna lie, that waiting period's long enough to forget exactly what hurt you, so take notes right after the attempt while the pain's fresh.
Employer sponsorship's common. If ES is part of your job, ask your manager. Training budget. Professional development funds. Whatever your org calls it.
Also, Splunk generally doesn't do public discount codes or random vouchers. Sometimes training bundles or corporate agreements include exam vouchers, but don't count on a coupon fairy.
Refund and rescheduling policies are usually Pearson VUE standard. You can often cancel or reschedule up to 24 to 48 hours before the exam. Miss that window and you might eat the fee, or get tagged as a no-show.
Passing score
People always ask for a number. The reality's messier.
Splunk typically uses scaled scoring, and while many candidates estimate you need roughly 70 to 75% correct to pass, the exact passing threshold's often not publicly disclosed in a simple "you need 72%" statement. The idea's that raw scores get converted to a scaled score to account for slightly different difficulty across exam versions.
What you will get is clear: pass/fail immediately at the end of computer-based testing.
Score report details matter. If you pass, you get confirmation. If you fail, you usually get a breakdown by exam domain that shows something like strong, moderate, weak. That's your map for round two.
No partial credit. If it's a multiple-answer question and you miss one option, it's wrong. Painful. Common.
SPLK-3001 exam objectives (domains & weighting)
Splunk doesn't always publish super granular weighting in a way that's easy to quote, but the SPLK-3001 exam objectives consistently orbit the same ES admin domains. Think "operate ES as a system", not "memorize a menu".
Security content and detections (correlation searches, notable events)
Correlation searches are where ES becomes ES. You need to understand how searches generate notables, what the scheduling and throttling implications are, and what happens when a detection's technically correct but operationally unusable.
You'll get questions that feel like: a notable rule's firing too often, analysts are overwhelmed, and the data's a mix of good and garbage. The right answer usually involves tuning at the right layer, and knowing whether to adjust the search logic, add suppressions, change notable event aggregation behavior, or fix the underlying data normalization. This is also where Splunk ES correlation searches and notable events show up as a practical skill, not trivia.
Risk-Based Alerting (RBA) administration
Splunk ES risk-based alerting (RBA) administration is one of the biggest "pro-level" signals on this exam. You need to know how risk events get created, how risk scores roll up, how to avoid inflating risk with junky signals, and how to keep RBA useful over time.
Honestly, RBA questions tend to punish hand-wavy understanding. If you've only read about RBA but never operated it, you'll struggle when the scenario asks you to choose between tuning the risk rule, adjusting the underlying detection, or fixing an identity mapping issue that's causing risk to attach to the wrong entity.
Data onboarding, CIM, and normalization
If you're weak on Splunk ES data onboarding and CIM mapping, you're playing on hard mode. ES content expects CIM compliant fields. If your data isn't mapped, detections miss. If your timestamps are off, everything looks dead. If your sourcetypes are inconsistent, you'll chase ghosts.
Expect questions about onboarding flows, field extractions, tags, eventtypes, data models, and how normalization impacts ES dashboards and detections. This is the "admin" part of the cert, and it's where folks who only do content management get exposed.
Threat intelligence, ES inputs, and integrations
Threat intel in ES isn't just "upload a feed". You need to know how intel inputs work, how matching behaves, what happens when feeds are stale, and how integrations affect performance and analyst workflows.
Some questions'll be more conceptual. Others'll be "which ES input or configuration choice solves this operational problem without creating five new ones".
Incident review workflows, triage, and tuning
This is where ES meets humans. Incident Review, notable status transitions, assignment, urgency, and triage flows. You'll also see tuning concepts tied to analyst pain, like why notables are duplicative, why the same host generates 400 notables, and how Splunk ES content management and tuning prevents alert fatigue.
One long rambling truth: ES admins who never sit with analysts tend to tune the wrong things, because they optimize for "fewer notables" instead of "better notables", and the exam scenarios often nudge you toward choices that preserve detection value while reducing noise in a controlled, auditable way that doesn't make your SOC manager want to throw a keyboard through a window.
User/role management and ES configuration
Roles. Capabilities. Access to ES views. Knowledge objects. Who can edit correlation searches. Who can manage notable event settings. Plus general ES configuration hygiene.
This part's less sexy. Still tested. It's also where production safety lives, because an overly permissive role can wreck your content, and an overly restrictive role makes the SOC blind.
Objectives checklist (downloadable)
If you want a quick checklist you can copy into a doc and track, here you go. Save it. Print it. Whatever.
- ES content: correlation search scheduling, throttling, suppression, notable creation rules
- Notable event management: statuses, assignments, urgency, aggregation behavior
- RBA: risk rules, risk objects, risk events, tuning risk scores, avoiding inflation
- CIM and normalization: tags, eventtypes, data models, field mappings, onboarding checks
- Threat intel: inputs, matching behavior, maintenance, integration impacts
- Incident review: triage workflow, tuning based on analyst feedback, operational metrics
- ES admin config: users, roles, capabilities, content permissions, safe change control
Prerequisites and recommended experience
You'll see people ask about Splunk ES admin prerequisites like there's a single gatekeeper requirement. In practice, Splunk may list recommended prior certs or training, but the real prerequisite's competence with both Splunk platform admin fundamentals and ES-specific administration.
Prerequisites
If Splunk publishes required prerequisites for sitting SPLK-3001, follow that list. If they don't, treat these as your baseline:
- solid Splunk admin knowledge (users/roles, knowledge objects, search basics, data onboarding concepts)
- real exposure to ES administration tasks, not just watching dashboards
Recommended hands-on experience
I'd want at least a few months of hands-on ES administration. Six months feels comfortable. Less than that and you're relying on memory instead of instinct.
You should also be able to read and reason about SPL, even if you're not writing monster searches daily, and you should understand SOC workflows like triage, escalation, and tuning cycles because the exam's scenarios are written in that language.
Difficulty and what makes SPLK-3001 challenging
Difficulty
Difficulty rating: high, but fair. It's advanced because it tests operational thinking, not clickpaths.
Scenario questions are the driver. Tuning's the driver. CIM and data model dependencies are the driver. RBA's the driver. And the worst part's that multiple answers often feel "kind of right" unless you've seen the real-world consequences.
This isn't trivia.
It's applied admin work.
Pace matters.
Common reasons candidates fail
Big one: misunderstanding ES workflows. People know Splunk, but not ES. Another: weak CIM knowledge, where they can't connect "field mapping" to "detection works".
Limited tuning experience's huge. If you've never reduced noise without destroying coverage, the exam scenarios'll corner you. Also, folks who never managed permissions and roles in ES get tripped up on who can do what and where.
Best study materials for SPLK-3001
Official Splunk training
Start with official training paths for ES administration. Splunk updates course names over time, so I'm not gonna pretend a specific catalog's frozen forever, but you're looking for ES admin focused courses, plus any recommended prerequisites that cover Splunk core admin and searching.
If your employer'll pay for training, push for it. ES is expensive software, and training's cheaper than misconfiguring it in production. True story.
Documentation to prioritize
Prioritize docs you'll actually use on the job:
- ES admin documentation for configuration and content management
- CIM documentation for data model expectations and field naming
- Correlation search and notable event docs
- RBA docs, especially risk event generation and scoring behavior
- Incident review workflows and notable management docs
Read release notes too.
Hands-on labs (recommended)
Hands-on wins. Always.
Build and tune a correlation search. Configure RBA rules and watch risk scores change with different signals. Onboard a data source, map to CIM, and verify the data model acceleration and dashboards behave. Then break something on purpose and fix it. That's how you learn what ES is actually doing.
SPLK-3001 practice tests and exam prep strategy
Practice tests
Official sources first. If Splunk offers sample questions or official prep guidance, use that.
For extra drilling, a focused pack can help if you treat it as a feedback tool, not a cheat sheet. The SPLK-3001 Practice Exam Questions Pack is priced at $36.99, and it's the kind of thing I'd use to identify weak domains fast, then go back to docs and a lab to actually fix the underlying understanding.
Avoid sketchy dumps. You know the ones. Besides ethics, they train you to memorize instead of reason, and this exam punishes that because scenarios are about choosing the best operational move, not recalling a phrase.
When you review missed questions, don't just note the right answer. Write down why the wrong answers are wrong in an ES context. That's where the learning is.
2 to 4 week study plan (fast track)
Week 1: refresh ES architecture, content management, notable workflows, and permissions. Week 2: deep focus on CIM mapping and onboarding, then correlation searches and tuning. Week 3: RBA administration, threat intel inputs, and incident review scenarios. Week 4: timed practice sets, review weak domains, rebuild a couple detections in a lab.
If you're using the SPLK-3001 Practice Exam Questions Pack, do small timed blocks, then stop and lab the topic you missed. Don't grind 200 questions in a night. That's how you learn nothing.
6 to 8 week study plan (standard)
Weeks 1 through 2: Splunk fundamentals you actually use in ES, plus ES configuration basics. Weeks 3 through 4: data onboarding, CIM normalization, data models, validation. Weeks 5 through 6: correlation searches, notable event rules, tuning patterns, SOC workflows. Weeks 7 through 8: RBA administration, threat intel, integrations, plus full review and timed practice.
Long rambling advice: schedule two lab sessions per week where you do something end-to-end like onboard a log source, map fields, validate the data model, enable or tune a detection, then confirm notables appear correctly in incident review with the right urgency and ownership behavior, because that single workflow hits half the exam in one shot and you'll actually remember how the pieces connect instead of treating them as isolated menu clicks.
Last-week checklist
Sleep. Seriously.
Do two timed runs. Review domain weaknesses. Re-read the objectives list. Confirm you can explain, in plain words, how CIM impacts detections and how RBA turns noisy signals into something analysts can act on. If you want one more quick diagnostic, do a final set from the SPLK-3001 Practice Exam Questions Pack and only focus on the questions you miss.
Registration, scheduling, and exam-day tips
How to register and schedule
You register through Splunk's certification portal, then schedule with
SPLK-3001 Exam Objectives: Domains, Topics, and Weighting
What the SPLK-3001 exam actually tests
The SPLK-3001 Splunk Enterprise Security Certified Admin exam isn't your typical vendor cert where you memorize menu locations and feature lists. This thing measures whether you can actually run ES in a real security operations center, handling the daily grind of building correlation searches, tuning notable events, managing risk-based alerting, and keeping security content from drowning your analysts in false positives.
The exam blueprint divides into six major domains. Each domain carries specific weighting that directly impacts how you should allocate study time. Understanding these percentages matters because you're not gonna pass by deep-diving into low-weight topics while ignoring the heavy hitters.
What's interesting is that these objectives reflect ES 7.x and 8.x capabilities as of 2026, incorporating modern security operations practices that weren't even part of the exam a few years back. Risk-based alerting's grown significantly in weighting. Splunk updates exam objectives periodically to match new ES features, evolving threat landscapes, and changes in how security teams actually work.
Domain 1: Security content and correlation searches (roughly 28-30%)
Heaviest weight here. Makes total sense.
Correlation searches are literally the detection engine of ES, so you need to understand out-of-the-box content structure. The dashboards, reports, data models, and correlation searches that ship with ES. But memorizing what exists isn't enough, not even close. The exam tests whether you can dissect correlation search anatomy: search logic using SPL, triggering conditions, throttling settings, how notable events get generated, and how adaptive response actions fire.
Creating custom correlation searches from scratch comes up repeatedly. You'll need to build detection rules using proper SPL, define scheduling intervals that balance detection speed against system load, set appropriate severity levels, and configure notable event fields correctly. I've seen people nail the SPL but completely mess up the scheduling, causing searches to skip or stack up during peak hours. It's frustrating to watch.
Modifying existing searches is trickier than it sounds. You can't just edit the default content directly. You need to clone and customize while preserving upgrade paths. I mean, Splunk releases content updates regularly, and if you've modified default searches incorrectly, those updates won't apply cleanly.
Performance optimization separates mediocre admins from good ones. Correlation searches run constantly, so inefficient searches kill ES performance. Techniques like using summary indexing, using data model acceleration instead of raw searches, and optimizing time ranges to search only necessary data.
Throttling and suppression configuration prevents alert fatigue. Set throttling wrong and your analysts get buried in duplicate notable events for the same incident. Suppression periods need careful tuning based on attack patterns and analyst workflows.
Notable event configuration goes beyond just generating alerts. You're customizing fields, setting urgency and severity that actually reflect business risk, configuring automatic owner assignment rules, and defining status workflows that match your team's investigation process.
Domain 2: Risk-based alerting framework (roughly 20-22%)
RBA fundamentally changes how ES detects threats compared to traditional correlation searches. Instead of alerting on single events, RBA accumulates risk scores over time for objects like users and systems.
Framework fundamentals include understanding risk objects (systems, users, other entities), how risk scores get assigned, and how risk attribution works. A single suspicious event might not warrant a notable, but ten suspicious events from the same user in an hour definitely should.
Configuring risk rules involves creating and modifying rules that assign risk scores to objects based on suspicious activities or indicators. Risk scoring methodology requires defining appropriate score values. Assign too little and threats slip through, too much and everything triggers notables.
Risk notable events generate when cumulative risk scores exceed thresholds you define. Setting these thresholds requires understanding your environment's baseline activity and organizational risk tolerance. I've seen environments where thresholds were set so low that legitimate power users constantly triggered risk notables, which defeats the whole purpose. Like, I once worked with a company where their top sales rep hit the risk threshold every single Monday morning just from normal travel patterns and accessing customer files. Nobody wants to be the admin explaining why the CEO's name keeps showing up in the threat dashboard.
Threat object framework integration lets you use threat intelligence to modify risk scores. If a user contacts a known C2 domain, that should carry more risk weight than contacting an unknown external IP.
RBA tuning's ongoing work. You adjust risk rules to reduce false positives, calibrate thresholds based on actual incidents, and validate that risk scoring actually correlates with real threats. Risk incident response workflows need integration with your incident review processes.
Domain 3: Data onboarding and CIM compliance (roughly 18-20%)
The Common Information Model normalizes diverse security data sources into standardized field names and data models. Without proper CIM mapping, correlation searches won't work correctly.
You need solid understanding of CIM data models for security. Authentication, Change Analysis, Network Traffic, Intrusion Detection, Malware, Vulnerability, and Web are the big ones. Each data model defines standard fields that correlation searches expect.
Field mapping and normalization involves translating vendor-specific field names to CIM-compliant names using field aliases, calculated fields, and eval statements in props.conf and transforms.conf. This is hands-on configuration work, not theoretical knowledge.
Data model acceleration configuration directly impacts correlation search performance. Accelerated data models let searches run against summarized data instead of raw events, improving speed by orders of magnitude, but acceleration has storage costs and needs proper management.
Validating CIM compliance requires using ES tools and searches to verify data sources populate data models correctly. The exam tests whether you can identify and fix broken CIM mappings.
Onboarding new data sources follows a process: parsing, field extraction, CIM mapping, and validation. Tag-based field extraction uses tags like authentication, malware, and network to enable data model population. Troubleshooting data normalization issues when fields don't extract properly or data models don't populate is essential admin work.
Domain 4: Threat intelligence and integrations (roughly 12-15%)
ES threat intelligence framework includes threat lists, threat intelligence downloads, and threat artifacts. Configuring threat intelligence sources means integrating external feeds using STIX/TAXII or custom feed formats, setting download schedules, and managing threat list updates.
Threat intelligence collections cover different indicator types: IP addresses, domains, file hashes, URLs, email addresses. Each type requires different handling and lookup configurations.
Threat matching in correlation searches leverages threat intelligence lookups to identify known malicious indicators in your security data. The exam covers how to properly implement these lookups without killing search performance.
Asset and identity correlation enriches detections with business context. Knowing which systems are critical and which users have privileged access changes alert prioritization, which honestly makes a huge difference in how you respond. Third-party security tool integration brings data from firewalls, IDS/IPS, endpoint security, and vulnerability scanners into ES.
Adaptive response actions automate responses triggered by correlation searches. Creating tickets, sending email notifications, or integrating with SOAR platforms for complex response workflows.
Domain 5: Incident review and notable event management (roughly 10-12%)
Incident Review dashboard navigation might seem basic, but efficient triage requires knowing keyboard shortcuts, filter combinations, and how to quickly pivot to investigation dashboards.
Notable event lifecycle covers status progression from new through in progress, pending, resolved, and closed. Understanding appropriate status transitions and when to use each status matters for accurate metrics.
Triage processes and prioritization involves systematic approaches to handle notable event volume. You prioritize based on urgency, severity, and business impact rather than just handling events chronologically.
Ownership and assignment includes configuring automatic assignment rules that distribute workload appropriately and manually assigning notables when needed. Disposition and status management means setting correct dispositions (true positive, false positive, benign positive) with proper documentation.
Suppression management lets you suppress known false positives while maintaining audit trails. Custom notable event actions extend Incident Review functionality for analyst workflows.
Domain 6: ES configuration and administration (roughly 8-10%)
ES-specific user roles include built-in roles like ess_admin, ess_analyst, and ess_user, each with different permissions. Role-based access control configures appropriate access to ES features and sensitive security data based on job function.
ES configuration settings manage default time ranges, notable event retention, and system configurations. Glass table configuration sets up SOC visualization displays.
ES health monitoring uses dashboards to track data input health, correlation search execution, and system performance. Content update management involves applying ES updates, testing in non-production, and managing update schedules carefully.
ES upgrade procedures require understanding prerequisites, testing approaches, and rollback procedures. Backup and disaster recovery strategies protect ES configurations, custom content, and notable event data.
Troubleshooting common issues like data model acceleration failures, correlation search errors, notable event generation problems represents real admin work you'll face.
Why domain weighting actually matters for your study plan
Look, if you spend equal time on every domain, you're studying inefficiently. The security content and correlation searches domain at 28-30% deserves significantly more study time than ES configuration at 8-10%.
I'd recommend spending roughly 40% of your study time on domains 1 and 2 combined since they represent nearly half the exam. Data onboarding and CIM (domain 3) deserves another 25% of study time because it's foundational, and if you don't understand CIM, correlation searches won't make sense.
The remaining domains are important but carry less weight. Don't skip them, but don't obsess over memorizing every glass table configuration option when you haven't mastered correlation search throttling yet.
How objectives connect to actual ES admin work
These objectives aren't academic exercises. Every domain maps directly to daily ES admin responsibilities. When you're supporting a security operations center, you'll spend significant time tuning correlation searches to reduce false positives, onboarding new security data sources, investigating why data models aren't populating correctly, and helping analysts manage notable event queues.
Hands-on emphasis is real. You can't pass this exam by reading documentation alone. You need actual ES configuration experience, building correlation searches, configuring RBA, mapping data sources to CIM, managing threat intelligence feeds, and working through incident review workflows.
If you're coming from the SPLK-1003 (Splunk Enterprise Certified Admin) background, you'll find SPLK-3001 builds on that foundation but adds significant security-specific depth. The SPLK-5001 (Splunk Certified Cybersecurity Defense Analyst) cert focuses on using ES from an analyst perspective, while SPLK-3001 tests whether you can administer and tune the platform those analysts depend on.
Content evolution and staying current
Splunk doesn't publish exact exam update schedules, but ES itself releases new versions regularly with updated content packs, new correlation searches, enhanced RBA capabilities, and improved data models. The exam objectives evolve to reflect these changes.
For 2026, risk-based alerting's grown significantly in the exam blueprint compared to earlier versions. Threat intelligence integration has expanded beyond simple IP lookups to include more sophisticated threat object frameworks. Data model coverage has increased as CIM has matured and added new models.
This evolution means study materials from 2022 or 2023 might miss newer objective areas. Focus on documentation and training materials that explicitly cover ES 7.x and 8.x capabilities.
Using a full objectives checklist
Honestly, one of the most useful study tools is a detailed objectives checklist where you can self-assess your proficiency for each topic. Rate yourself as beginner, intermediate, or advanced for each objective, then focus study time on areas where you're weakest.
For example, you might be advanced at building correlation searches but only intermediate at RBA configuration and beginner at threat intelligence integration. That tells you exactly where to focus. Reassess every couple weeks as you study to track progress and identify remaining gaps.
The exam tests breadth across all six domains, so you can't afford major weak spots. Better to be intermediate across all areas than advanced in three domains and clueless in three others.
Conclusion
Wrapping up your SPLK-3001 prep
Look, here's the deal. The Splunk SPLK-3001 Splunk Enterprise Security Certified Admin exam isn't something you can cram for over a weekend and hope for the best. You need actual, real-world hands-on experience with Splunk Enterprise Security administration, the kind where you've built correlation searches that don't flood your SOC team with false positives, tuned notable events until they're really actionable, and wrestled with CIM mapping for data sources that refuse to fit the model. The exam objectives cover everything from risk-based alerting administration to threat intelligence integrations. Those scenario-based questions? They'll expose any gaps in your practical knowledge pretty fast.
The thing is, the SPLK-3001 exam cost and time investment make this certification a serious commitment. You're not just memorizing configurations here. You've gotta understand why you'd configure ES a certain way, how data onboarding impacts your correlation searches downstream, and what happens when your asset and identity correlation isn't dialed in correctly. The Splunk ES admin study guide and official documentation? They're your foundation, sure. But reading alone won't cut it. You need lab time where you're actually managing ES content and tuning detections.
Your study approach matters way more than how many weeks you block off on your calendar. Real talk? Some folks with heavy SOC experience might nail the SPLK-3001 passing score after a focused month of review and practice tests, while others coming from pure platform admin roles might need two months to really internalize the security workflows and ES-specific concepts. The RBA framework trips up a ton of candidates who haven't actually implemented it in production, and the questions about notable event lifecycle management require you to think like both an admin and an analyst.
Practice tests matter.
I've seen people waste good money on brain dumps that basically teach you to parrot answers without understanding the underlying logic. That approach falls apart the second you hit a question framed differently than you expected.
When you're in that final prep phase, practice tests become incredibly valuable for identifying your weak spots and getting comfortable with how Splunk frames scenario questions. The SPLK-3001 practice test options vary wildly in quality, though. You want questions that mirror the actual exam's complexity and focus areas because surface-level quizzes won't prepare you for the depth the real exam demands.
If you're serious about passing on your first attempt and want practice questions that actually reflect what you'll face on exam day, the SPLK-3001 Practice Exam Questions Pack gives you realistic scenarios covering all the exam domains with detailed explanations that help you understand the reasoning behind correct answers. It's one of the better prep resources I've seen for bridging that gap between knowing ES concepts and applying them under exam conditions.
Show less info
Hot Exams
Related Exams
Developing Solutions for Microsoft Azure
ACI Operations Certificate challenging
GIAC Security Essentials
Professional VMware vRealize Automation 8.3
Managing Supply Chain Risk
Implementing Cisco Collaboration Cloud and Edge Solutions (300-820 CLCEI)
Looker LookML Developer Exam
Splunk Core Certified Power User Exam
Splunk SOAR Certified Automation Developer Exam
Splunk Core Certified User
Splunk Core Certified Consultant
Splunk Enterprise Certified Architect
Splunk IT Service Intelligence Certified Admin Exam
Splunk Enterprise Certified Admin
Splunk Enterprise Security Certified Admin Exam
Splunk Certified Developer Exam
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.