PCS Practice Exam - Pulse Connect Secure (PCS): Administration and Configuration
Reliable Study Materials & Testing Engine for PCS Exam Success!
Exam Code: PCS
Exam Name: Pulse Connect Secure (PCS): Administration and Configuration
Certification Provider: Pulse Secure

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
PCS: Pulse Connect Secure (PCS): Administration and Configuration Study Material and Test Engine
Last Update Check: Mar 21, 2026
Latest 100 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena Pulse Secure Pulse Connect Secure (PCS): Administration and Configuration (PCS) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
Pulse Secure PCS Exam FAQs
Introduction of Pulse Secure PCS Exam!
The Pulse Secure PCS Certified Professional Exam is a certification exam designed to test the knowledge and skills of IT professionals who install, configure, and manage the Pulse Secure PCS product.
What is the Duration of Pulse Secure PCS Exam?
The duration of the Pulse Secure PCS exam is 90 minutes.
What are the Number of Questions Asked in Pulse Secure PCS Exam?
The exact number of questions that appear on the Pulse Secure PCS exam varies depending on the version of the exam. Generally, the exam consists of 50 multiple-choice questions.
What is the Passing Score for Pulse Secure PCS Exam?
The passing score for the Pulse Secure PCS exam is 70%.
What is the Competency Level required for Pulse Secure PCS Exam?
The Competency Level required for the Pulse Secure PCS exam is Professional.
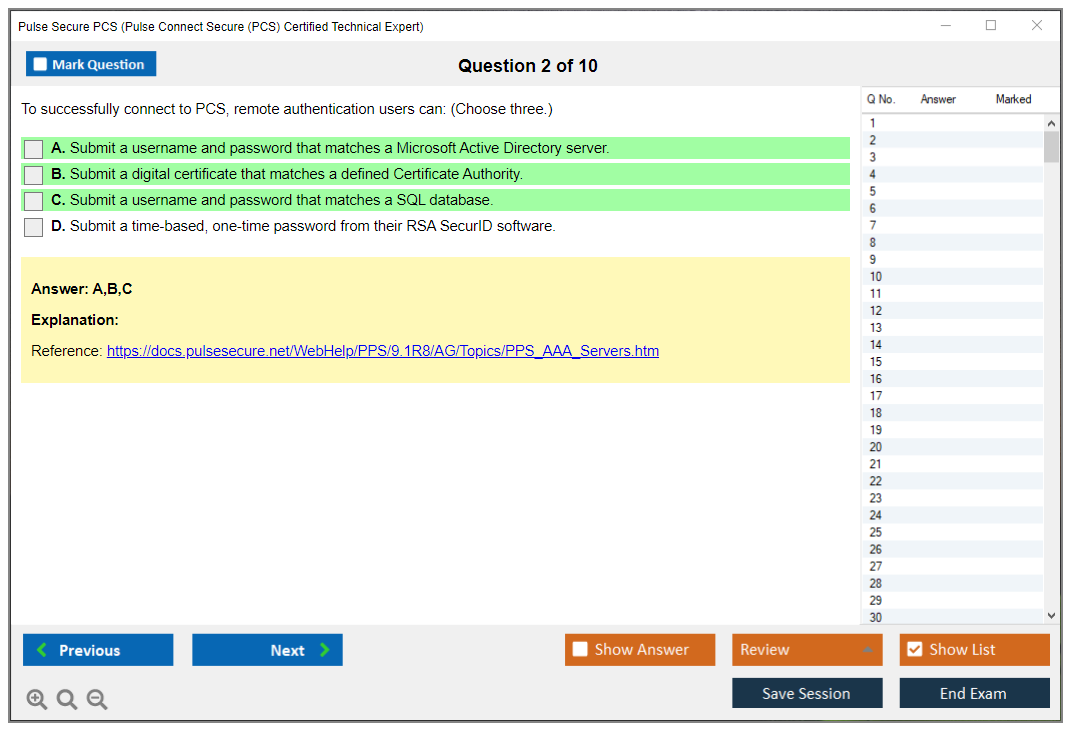
What is the Question Format of Pulse Secure PCS Exam?
The Pulse Secure PCS exam consists of multiple-choice, drag-and-drop, and fill-in-the-blank questions.
How Can You Take Pulse Secure PCS Exam?
The Pulse Secure PCS exam can be taken either online or in a testing center. To take the exam online, you must first register with the Pulse Secure website, and then purchase the exam. Once you have purchased the exam, you will be given instructions on how to access the exam and complete it. To take the exam in a testing center, you must first contact a Pulse Secure authorized testing center and arrange for an appointment. At the testing center, you will be given instructions on how to complete the exam.
What Language Pulse Secure PCS Exam is Offered?
Pulse Secure PCS certification exams are offered in English.
What is the Cost of Pulse Secure PCS Exam?
The cost of the Pulse Secure PCS exam is $150 USD.
What is the Target Audience of Pulse Secure PCS Exam?
The target audience for the Pulse Secure PCS exam is IT professionals who are responsible for the implementation, configuration, and maintenance of Pulse Secure PCS solutions. It is recommended that individuals have at least two years of experience with Pulse Secure PCS solutions before attempting the exam.
What is the Average Salary of Pulse Secure PCS Certified in the Market?
The average salary for someone who has achieved Pulse Secure PCS certification varies depending on the individual's experience and the region they are located in. Generally speaking, Pulse Secure PCS certified professionals can expect to earn anywhere from $50,000 to $90,000 per year.
Who are the Testing Providers of Pulse Secure PCS Exam?
Pulse Secure offers a certification program for its PCS product. The certification exams are administered by Pearson VUE, a global leader in computer-based testing. Pearson VUE provides a secure network of testing centers around the world, where you can take the Pulse Secure PCS certification exam.
What is the Recommended Experience for Pulse Secure PCS Exam?
The recommended experience for Pulse Secure PCS Exam is a minimum of one year of hands-on experience with Pulse Secure PCS and related technologies. Additionally, candidates should have a good understanding of networking technologies and protocols, as well as experience with network security concepts.
What are the Prerequisites of Pulse Secure PCS Exam?
The Pulse Secure PCS exam requires that you have a basic understanding of networking, routing, and security concepts. Additionally, it is recommended that you have experience with the Pulse Secure PCS product and have completed the Pulse Secure PCS training course.
What is the Expected Retirement Date of Pulse Secure PCS Exam?
Unfortunately, there is no official website that provides this information. You may need to contact Pulse Secure directly for more information.
What is the Difficulty Level of Pulse Secure PCS Exam?
The difficulty level of the Pulse Secure PCS exam can vary depending on the individual. The exam covers a wide range of topics related to the Pulse Secure PCS product, so it is important to have a good understanding of the product before taking the exam. Additionally, it is recommended to have some experience in network security and/or network administration before taking the exam.
What is the Roadmap / Track of Pulse Secure PCS Exam?
The certification roadmap for the Pulse Secure PCS Exam includes the following steps:
1. Complete the Pulse Secure PCS Training Course.
2. Pass the Pulse Secure PCS Exam.
3. Receive the Pulse Secure PCS Certification.
4. Maintain your certification by completing the Pulse Secure PCS Continuing Education Program.
What are the Topics Pulse Secure PCS Exam Covers?
1. Network Security: This topic covers the fundamentals of network security, including firewalls, intrusion detection systems, encryption, and authentication. It also covers the different types of attacks, such as man-in-the-middle, denial of service, and malicious code.
2. Access Control: This topic covers the different types of access control systems, such as role-based access control, identity and access management, and network access control. It also covers the various methods for managing access to resources, such as authentication and authorization.
3. Data Protection: This topic covers the different methods for protecting data, such as encryption, authentication, and data loss prevention. It also covers the different types of data breaches, such as insider threats and external threats.
4. Application Security: This topic covers the different types of application security, such as application firewalls, application whitelisting, and application hardening. It also covers the different methods for protecting applications
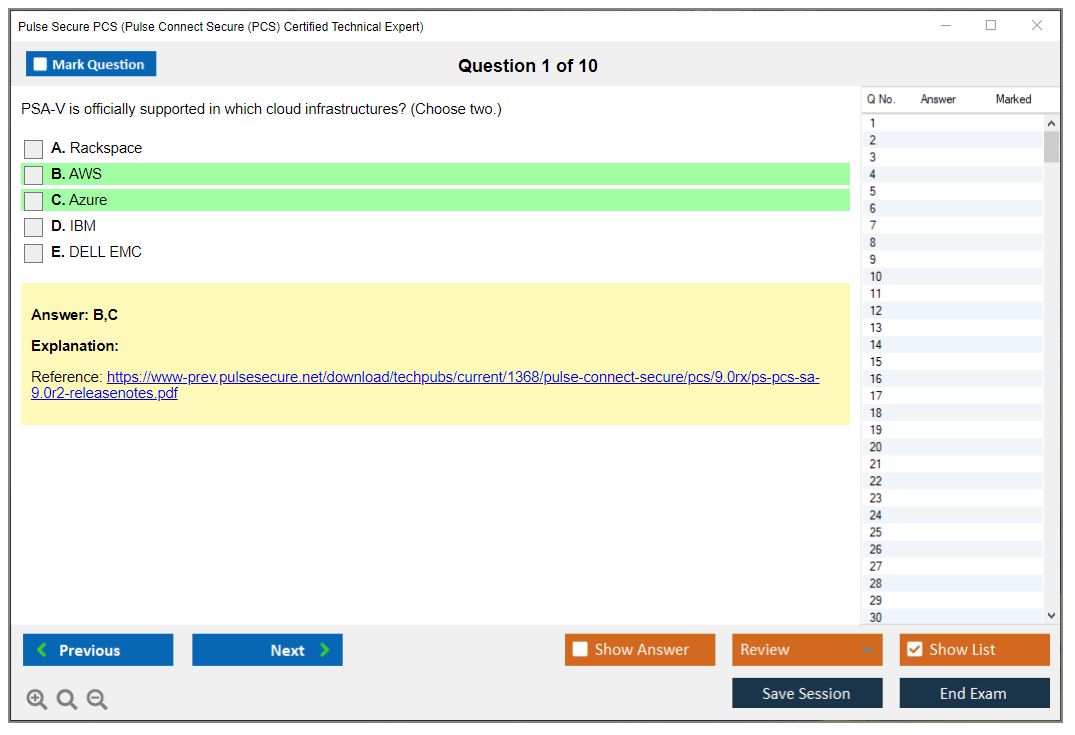
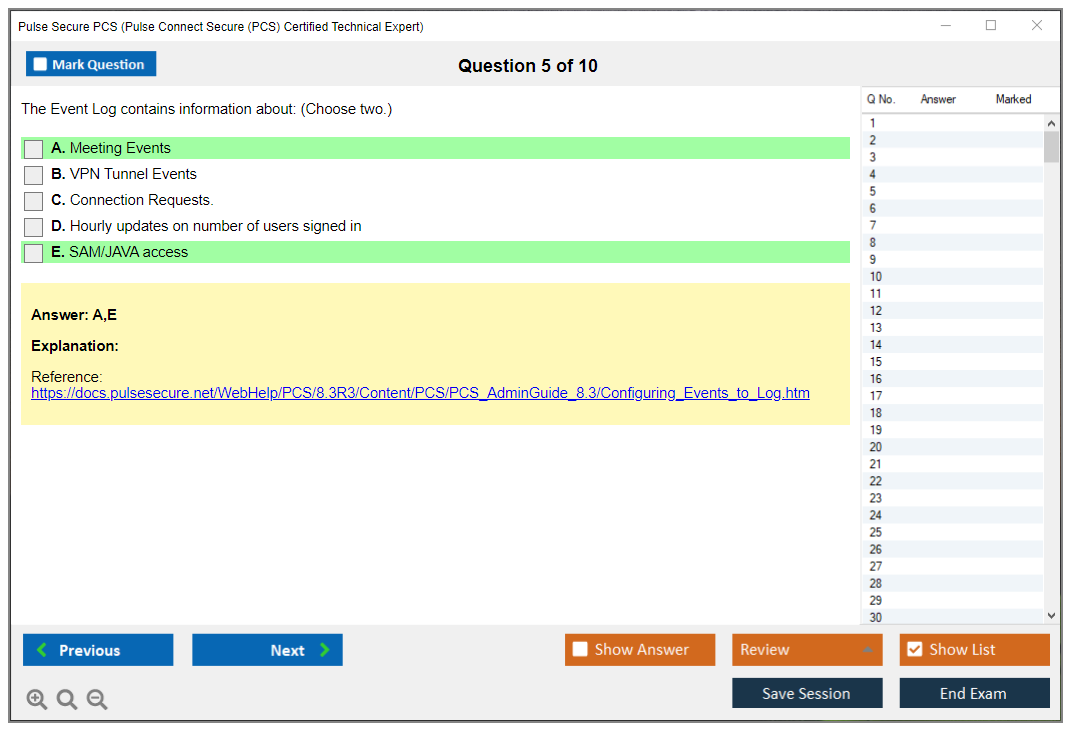
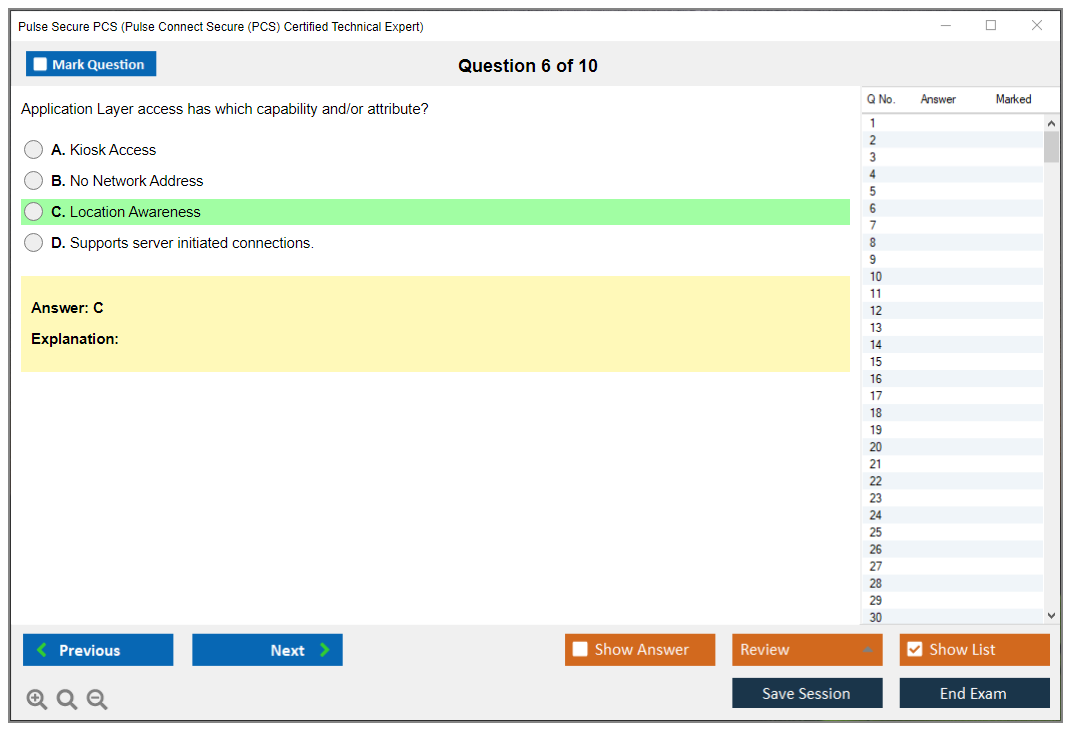
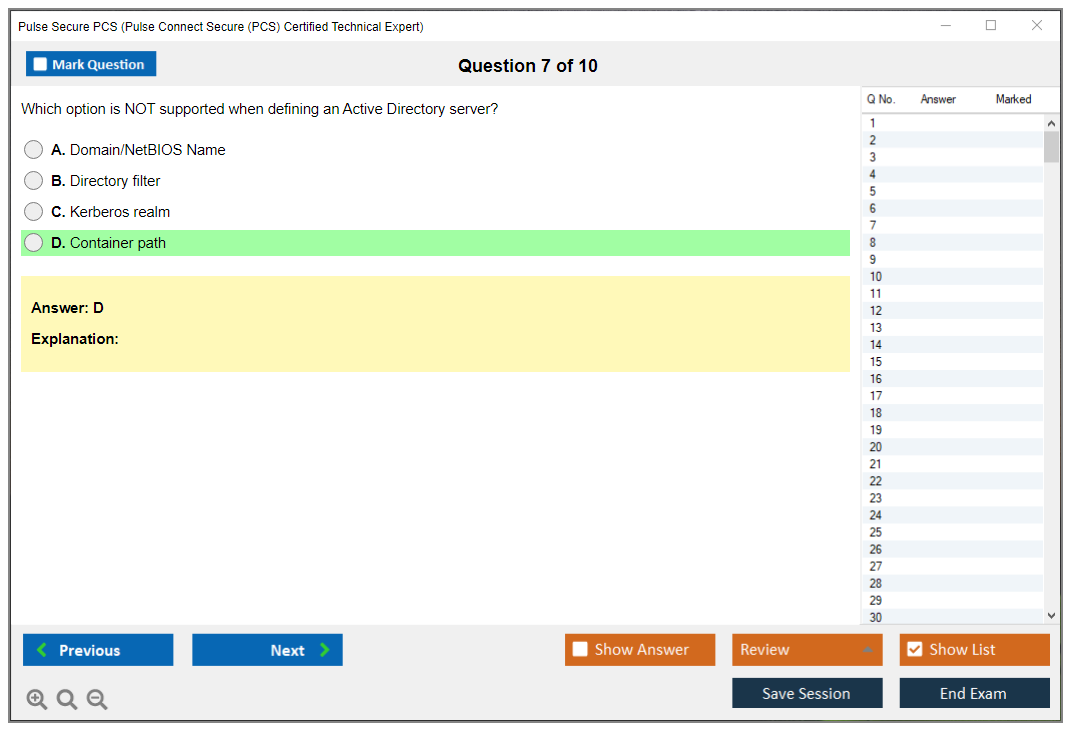
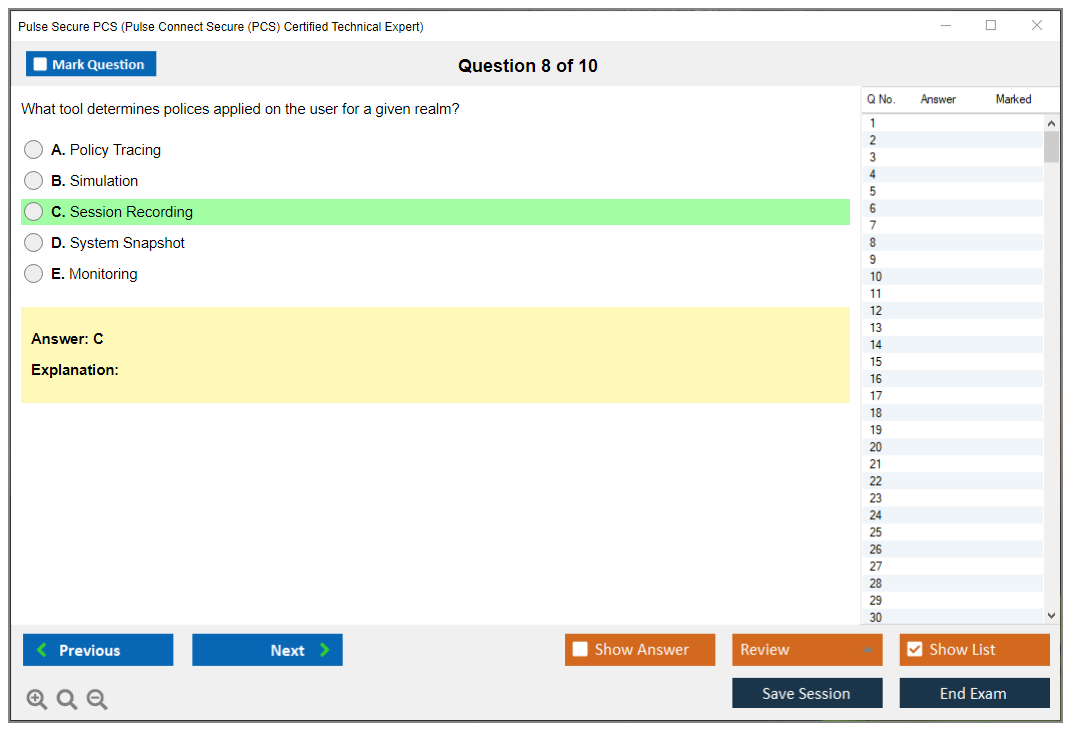
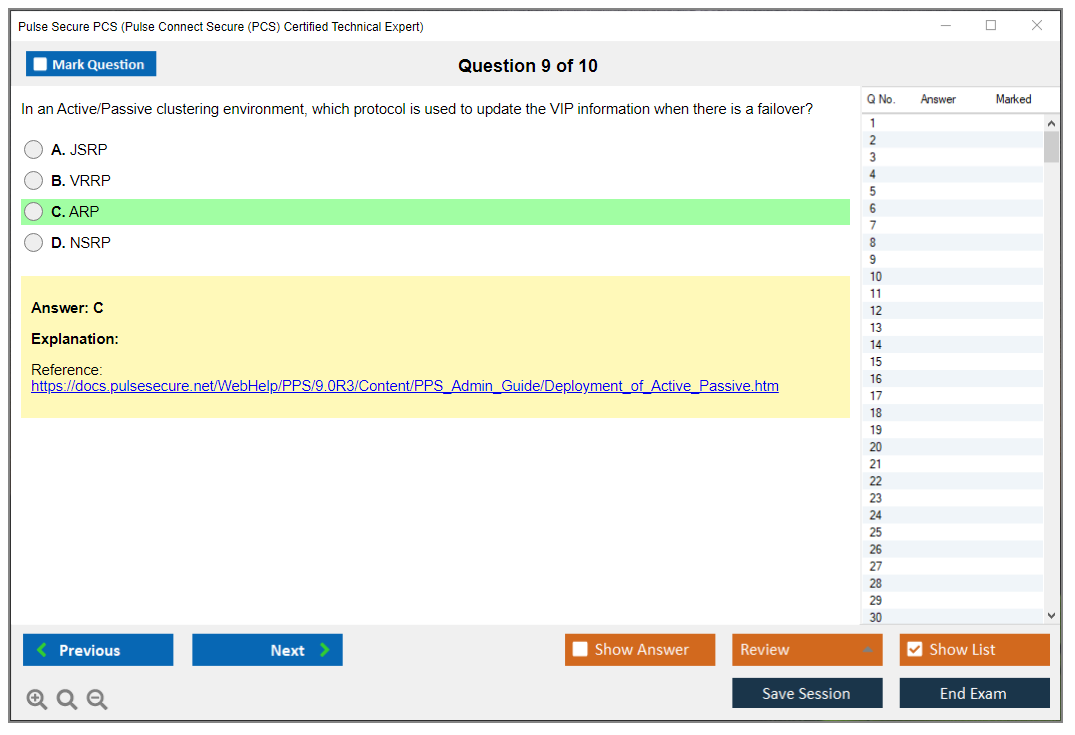
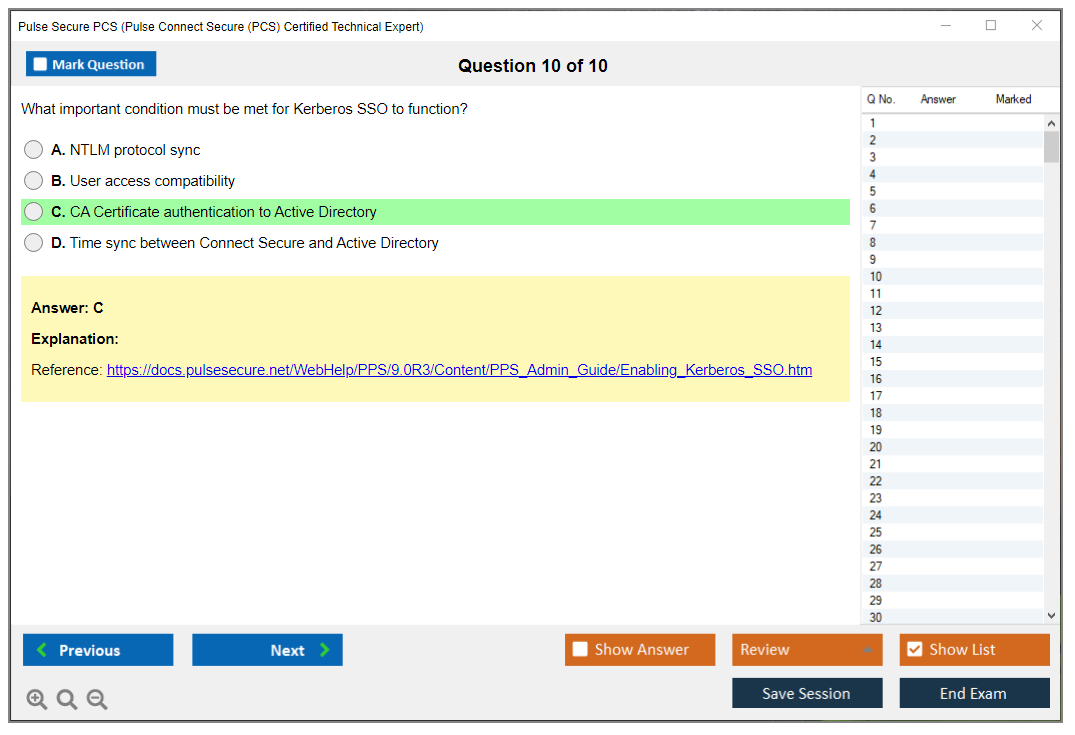
What are the Sample Questions of Pulse Secure PCS Exam?
1. What is the purpose of the Pulse Secure Policy Secure (PCS) platform?
2. What are the different components of the Pulse Secure PCS architecture?
3. How does Pulse Secure PCS provide secure access to applications and resources?
4. What are the different authentication methods available with Pulse Secure PCS?
5. How can Pulse Secure PCS be used to enforce security policies?
6. What are the benefits of using Pulse Secure PCS for network access control?
7. How can Pulse Secure PCS be used to monitor user activity?
8. What are the different types of reports available with Pulse Secure PCS?
9. How can Pulse Secure PCS be used to troubleshoot network issues?
10. What are the different deployment options available with Pulse Secure PCS?
Pulse Secure PCS Administration and Configuration Certification Why enterprises still bet on Pulse Connect Secure Remote access isn't disappearing. Even with everyone talking about zero-trust architectures and cloud-native everything, tons of organizations still run critical apps that need SSL VPN gateways. Pulse Connect Secure handles that job for massive enterprises across healthcare, finance, government, and manufacturing sectors where you can't just throw everything into SaaS and call it a day. The platform gives remote users secure access to internal resources through web browsers or native clients without exposing your entire network. It's basically the gatekeeper between your remote workforce and everything they need to actually do their jobs. Applications, file shares, legacy systems that'll probably outlive us all. What this certification actually proves you can do The Pulse Secure PCS Administration and Configuration certification shows you know how to deploy, configure, and... Read More
Pulse Secure PCS Administration and Configuration Certification
Why enterprises still bet on Pulse Connect Secure
Remote access isn't disappearing. Even with everyone talking about zero-trust architectures and cloud-native everything, tons of organizations still run critical apps that need SSL VPN gateways. Pulse Connect Secure handles that job for massive enterprises across healthcare, finance, government, and manufacturing sectors where you can't just throw everything into SaaS and call it a day.
The platform gives remote users secure access to internal resources through web browsers or native clients without exposing your entire network. It's basically the gatekeeper between your remote workforce and everything they need to actually do their jobs. Applications, file shares, legacy systems that'll probably outlive us all.
What this certification actually proves you can do
The Pulse Secure PCS Administration and Configuration certification shows you know how to deploy, configure, and manage these appliances in real production environments. Not just theory.
You're proving hands-on skills with authentication frameworks, resource policies, endpoint compliance enforcement, and troubleshooting connectivity problems when everyone's panicking because remote access is down. It covers system installation, initial configuration, user authentication setup, authorization rules, resource policy creation, client deployment across different platforms, endpoint security, and the maintenance tasks that keep everything running smoothly. Like, all the stuff that actually matters when systems go sideways at 3 AM.
This is intermediate-level territory. You'll need working knowledge of SSL VPN technology, how authentication frameworks actually work (not just "it talks to Active Directory"), and endpoint security concepts beyond just installing antivirus.
The people who should actually care about this exam
Network administrators? Security engineers? Obvious candidates here. If you're responsible for remote access infrastructure or VPN administration, this certification speaks directly to your daily work. Systems integrators who deploy Pulse solutions for clients need this credibility too.
I mean, if your job description includes "maintain secure remote access for 500+ users" or "integrate VPN with enterprise identity providers," you're in the target demographic. IT professionals managing hybrid work infrastructure will find this proves exactly the skills they're using every week. It's pretty niche compared to something like CCNA, but that specificity is actually valuable when you're applying for roles that explicitly need Pulse Connect Secure expertise.
There's this weird disconnect sometimes between what certifications test and what vendors actually support long-term. I've seen people grind through exam prep only to find out six months later the product line gets acquired or rebranded. Not saying that's happening here, but it's worth checking the vendor's roadmap before you invest serious time.
Career impact and what it's actually worth
Vendor-specific certifications? They're hit or miss depending on your market. But Pulse Connect Secure gets deployed in enough large organizations that having proven expertise opens doors. Enterprises using PCS need people who can configure authentication areas without breaking everything, create role-based access controls that actually make sense, and integrate with existing identity providers like Active Directory, LDAP, RADIUS, or SAML systems.
The certification shows you're not just winging it. You understand resource policies, client deployment strategies, Host Checker configurations for endpoint compliance, and how to troubleshoot when someone in accounting can't reach the ERP system. That's worth something when companies are hiring for specialized roles. Potential salary bump depends heavily on your market and existing skills, but specialized knowledge in widely-deployed platforms typically commands better compensation than generic networking skills alone.
How this fits into the bigger certification picture
This is foundation-level for Pulse Secure product specialization. Think of it as the prerequisite knowledge for more advanced security and deployment certifications in the Pulse ecosystem. You've also got related credentials like PPS (Pulse Policy Secure) that handles network access control, and the vADC Administration/Configuration track if you're working with application delivery controllers.
The PCS cert stands on its own, but it positions you to branch into those other areas if your organization uses multiple Pulse products. Many environments run both PCS for remote access and PPS for NAC, so understanding how they work together is valuable.
Real-world scenarios this training prepares you for
Managing remote workforce access is the big one, obviously. You're setting up authentication areas that connect to your existing identity providers, creating user roles that map to job functions, and defining resource policies so marketing can access what they need without seeing engineering's stuff.
Role-based access controls get complicated fast when you've got contractors, full-time employees, vendors, and partners all needing different permission levels. The exam covers how to structure that logically. Or actually it shows you how to avoid the disasters that happen when permissions overlap in weird ways. You'll also work with endpoint compliance policies, checking that connecting devices meet security requirements before granting access, then forcing remediation when they don't.
Integration is huge. PCS doesn't live in isolation. It talks to Active Directory for user authentication. LDAP directories. RADIUS servers, SAML identity providers for SSO, PKI infrastructure for certificate-based authentication, SIEM platforms for security event correlation, and endpoint management solutions for device compliance checks. Understanding those connection points matters.
What the exam blueprint actually covers
System installation and initial setup includes deploying appliances (physical or virtual), licensing, network settings, and updates. You'll need to know authentication and authorization inside out. Configuring authentication areas, connecting auth servers, setting up user roles, and mapping users to those roles correctly.
Resource policies control what users can access. You're creating web bookmarks, file share connections, application access rules, and split tunneling configurations. Client deployment means pushing out the Pulse Secure client software to Windows, Mac, Linux, and mobile platforms with the right settings pre-configured.
Endpoint security gets into Host Checker policies that verify devices meet requirements before allowing connections. Troubleshooting covers reading logs, understanding common connectivity failures, certificate problems, authentication errors, and policy conflicts. Some exam versions include high availability and clustering basics for redundancy scenarios.
Study time expectations based on your background
Already administered VPNs? Worked with authentication systems? You're looking at maybe 40-60 hours of combined study and lab practice. Someone coming from general networking without much VPN experience should plan for 60-80 hours, maybe more.
The learning curve is moderate but don't underestimate the hands-on component. You absolutely need lab time with actual PCS appliances, whether physical hardware or virtual machines. Reading documentation won't cut it. You have to configure authentication areas, create policies, deploy clients, and break things to understand how they fail.
Why this matters in 2026 and beyond
Hybrid work isn't disappearing. Organizations still need solid, secure remote access that puts zero-trust principles into practice. I mean, look around. Companies are maintaining distributed workforces indefinitely, which means remote access infrastructure remains critical.
The shift toward zero-trust architectures actually increases demand for properly configured SSL VPN solutions that verify user identity, check device posture, and enforce granular access controls. Pulse Connect Secure fits squarely into that model when configured correctly.
How this differs from generic VPN certifications
Generic network security? VPN certifications? They teach broad concepts. The PCS Administration and Configuration exam focuses specifically on Pulse Connect Secure administration. The actual product interfaces, configuration syntax, policy logic, and troubleshooting workflows unique to this platform.
That specificity cuts both ways. It's more valuable when applying to organizations running Pulse, less useful elsewhere. But if you're already working in a Pulse environment or targeting roles that explicitly require it, generic certifications won't demonstrate the hands-on product expertise employers actually need.
What happens after you pass
You're qualified to design and put together enterprise remote access solutions using Pulse Connect Secure. You can serve as the subject matter expert when problems arise or when planning expansions. Organizations with Pulse deployments will value your expertise for migrations, upgrades, and optimization projects.
Vendor partnership opportunities open up too if you're working for a systems integrator or consulting firm. Many Pulse partners require certified staff to maintain partnership status. The post-certification opportunities depend heavily on market demand in your region and industry vertical, but government, healthcare, and finance sectors consistently need qualified administrators for their secure access infrastructure.
Pulse Connect Secure PCS Exam Details and Logistics
What the certification proves
The Pulse Secure PCS Administration and Configuration certification is basically the vendor saying you can run a Pulse Connect Secure box without guessing. Configure it. Keep it stable. Lock it down. Fix it when someone breaks authentication five minutes before a board meeting.
This exam's about secure remote access appliance administration in the real world. That means SSL VPN configuration and policies, user roles areas authentication servers, endpoint security host checker checks, and the stuff that causes tickets like split tunneling bookmarks and resource policies to blow up at 2 a.m.
Who this is for
Network admins who got handed the VPN.
Security folks who inherited PCS. Helpdesk leads moving up.
Also consultants. And MSP engineers. If you touch areas, roles, auth servers, or client settings, the Pulse Connect Secure PCS exam maps pretty cleanly to your day job, which makes studying less painful.
Official exam name and code
The official designation is Pulse Connect Secure (PCS): Administration and Configuration.
The vendor exam number's typically published in the current certification page and candidate guide, and it can change when they refresh versions. Don't rely on some random blog screenshot from 2019. Check the listing when you buy the voucher, because that's the exam code Pearson VUE or PSI will show in your account.
How you actually take it
Delivery's computer-based and proctored.
Most candidates'll see it offered as:
- Online proctored testing through Pearson VUE or PSI
- In-person at authorized testing centers worldwide
Online's convenient, but it's picky. Testing centers are boring. Also predictable, which matters more than you'd think when you're already nervous.
What the exam looks like
The PCS Administration and Configuration exam format's mostly objective questions, with a twist.
Expect:
- Multiple-choice questions
- Multiple-select questions
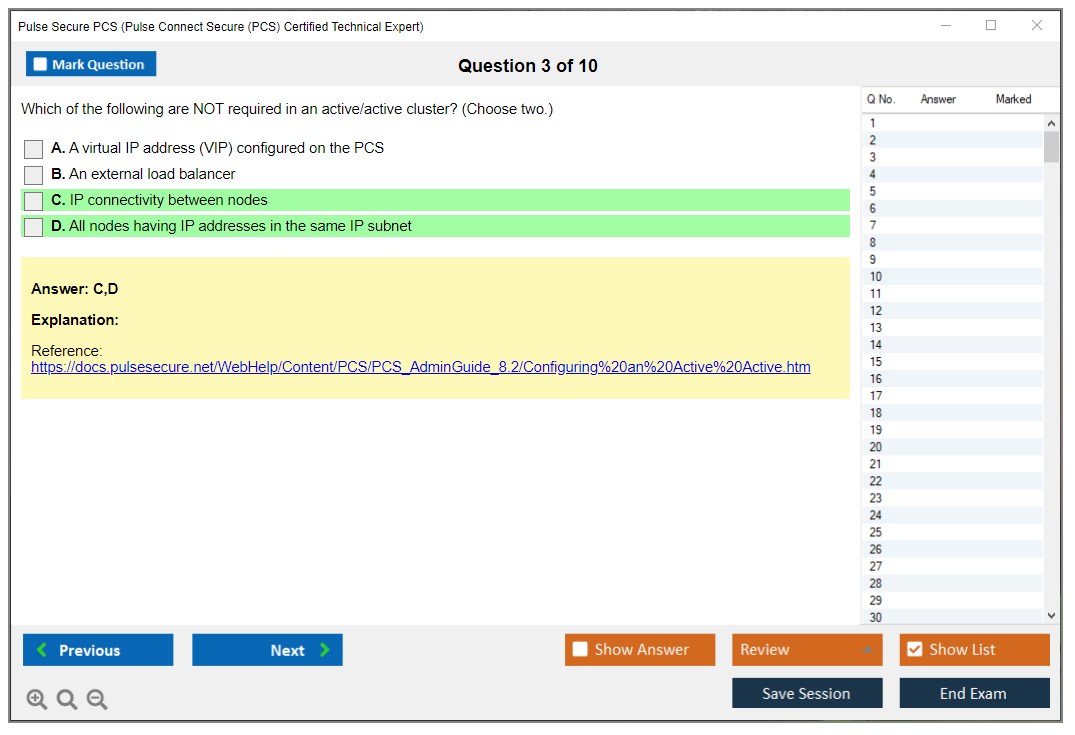
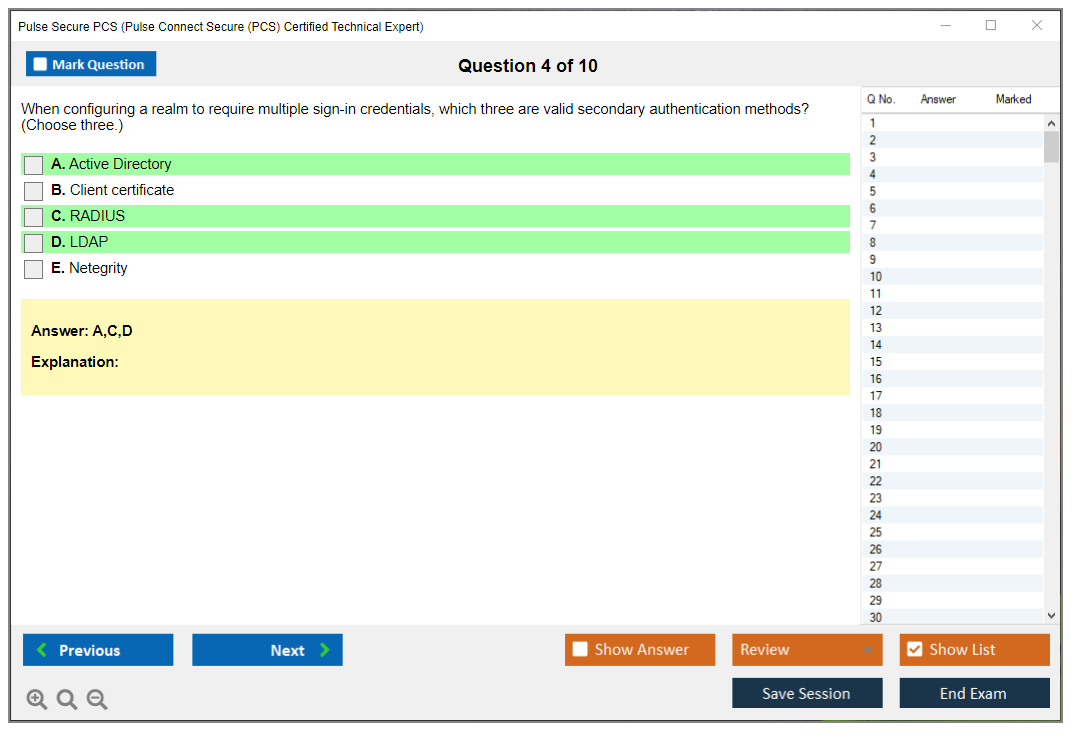
- Situation-based questions where you read a config scenario and decide what setting, policy, or auth flow explains the behavior
Some questions are straight recall. Many aren't. You'll get "user can sign in but can't see bookmarks" type prompts, and you've gotta reason through role mapping, area order, and resource policy evaluation. This's where people who only memorized definitions start sweating.
Question count and timing
Total questions are typically 60 to 75, pulled across the PCS exam objectives with a weighted distribution.
Time allocation's usually 90 to 120 minutes, depending on the exact form and question mix. Not gonna lie, 60 questions in 90 minutes is comfortable if you know the UI and concepts. But 75 questions with more scenarios can feel tight if you second-guess every multi-select. I once watched someone burn 20 minutes on three questions because they kept changing answers, which is a terrible strategy but incredibly common.
Cost, vouchers, and discounts
The standard registration fee's commonly $300 to $400 USD, and yes it varies by region and whether you're booking through Pearson VUE vs PSI.
A few money notes that matter:
- Training bundle packages sometimes knock 10 to 20% off versus buying a course and voucher separately. If your employer's paying, this's usually the easiest way to justify it.
- Corporate volume discounts exist for orgs buying multiple vouchers, but you usually've gotta go through vendor sales or an authorized training partner. It's not a coupon code situation.
- Exam vouchers are typically valid for 12 months from purchase date. They're usually non-transferable and non-refundable, so don't stockpile 'em like airline miles.
Refund and transfer policies are generally strict.
Once bought, you own the decision.
Passing score and score reports
Passing score's usually a scaled 700 to 750 out of 1000, which works out to roughly 70 to 75% correct, depending on the form and scoring model.
Score reporting's quick:
- Immediate preliminary result on screen for computer-based exams
- Official score report typically within 48 hours by email or in your testing account portal
If something goes sideways and you want a score appeal, don't expect miracles. There's usually a limited score appeal process for specific situations, and you'll need to file within the stated window with details that sound like an incident report, not vibes.
Domain weighting (what matters most)
This's the part people ignore and then regret.
The weighting's usually presented like this, give or take a few points depending on blueprint updates:
- System administration (15 to 20%): upgrades, licensing, base networking, admin access
- Authentication and authorization (20 to 25%): areas, auth servers, role mapping, maybe some SSO options
- Resource policies (15 to 20%): bookmarks, web access, application access logic
- Client access (15 to 20%): Pulse client behavior, SSL VPN vs network connect settings
- Endpoint security (10 to 15%): endpoint security host checker, remediation, posture rules
- Troubleshooting (15 to 20%): logs, user session tracing, common misconfig patterns
If you want the easiest points, system admin basics and "where do I find the log for X" are usually simpler than auth edge cases. The hardest points, for most people, are auth flows and policy logic because PCS lets you build a perfectly valid configuration that still does the wrong thing.
Language and blueprint changes
English's the primary language.
Select additional languages may exist in specific regions, but don't assume. Verify at registration.
Blueprint updates happen periodically to align with major releases and best practices. That means older Pulse Secure PCS study guide PDFs and random PCS practice test questions dumps can drift out of date fast, especially around UI labels, default TLS behavior, or client versions.
Retakes, scheduling, and cancellations
Retake policy usually reads like:
- Wait 14 days after a failed attempt before the first retake
- Wait 30 days before later attempts
- A maximum attempts per year rule may apply depending on the program terms
Rescheduling and cancellation rules are the usual exam industry deal.
You typically must change or cancel 24 to 48 hours before the appointment or you forfeit the fee or voucher. Read the fine print for your provider, because PSI and Pearson VUE don't always match.
Online testing environment rules
For online proctoring, they want a controlled environment. Private quiet room. Door closed. Clear desk. Webcam on. Stable internet. Government-issued ID.
Prohibited items are exactly what you'd expect and then some:
- Reference materials, printed notes, sticky notes
- Phones, smartwatches, tablets, "but it's face down" devices
- Secondary monitors, even ones turned off
- Unauthorized software, remote desktop tools, screen sharing utilities
- Any communication device or someone else in the room
If you like to think out loud, don't.
Proctors can flag you for mumbling at the screen.
Special accommodations are available with documentation, but you need to request 'em in advance through the testing provider. That can mean extra processing time, so don't book the exam for next week and then try to backfill paperwork.
Validity, renewal, and verification
Certification validity's typically 2 to 3 years from the pass date, then you renew or recertify based on the vendor's current policy.
Sometimes that means retaking the same exam, sometimes passing a newer version, sometimes a higher-level track if they offer it.
Employers can verify status through the vendor certification database using your candidate ID. That's useful when HR asks you to "send proof" and you're tired of forwarding PDFs.
Beta exams (when they exist)
Beta exams pop up occasionally when a new version's released.
Reduced cost. More uncertainty.
The tradeoff's score timing. Beta scores can be delayed 8 to 10 weeks while they validate questions and set the scaled passing score, so don't take beta if you need the credential for a job requirement next month.
Quick answers people always ask
How much does the Pulse Secure PCS exam cost?
Usually $300 to $400 USD, with possible training bundle savings.
What's the passing score for the PCS Administration and Configuration exam? Commonly 700 to 750 out of 1000 scaled.
How hard's the Pulse Secure PCS exam? Intermediate, but it spikes if you've never built areas and role mappings from scratch and then debugged 'em under pressure.
What're the best study materials for Pulse Connect Secure PCS? Official admin guides plus hands-on lab time, and a PCS Administration and Configuration training course if your background's light.
Are there PCS practice tests or sample questions available? Sometimes official prep exists, but be careful with third-party dumps. If it's too cheap and too specific, it's probably trash or worse.
If you're serious about passing, treat the blueprint like a checklist and map every objective to a config screen, a log location, and one troubleshooting story you can explain. That's how this exam thinks.
PCS Administration and Configuration Exam Objectives and Domains
Okay, real talk. If you're getting serious about Pulse Connect Secure administration, you need to know what you're walking into with this certification exam. The PCS Administration and Configuration test isn't just some checkbox exercise. It's a proper deep-dive into how these SSL VPN appliances actually work in production environments, and the thing is, the exam objectives tell you exactly where Pulse Security thinks you should be spending your brain cycles.
What you're actually validating when you pass
So this certification proves you can deploy and manage Pulse Connect Secure appliances from the ground up. We're talking initial network setup, authentication integration with your existing directory services, building out user access policies that actually make sense, and let's be real here, troubleshooting when things inevitably break at 2 AM. The exam measures whether you understand not just the "what" but the "why" behind configuration decisions. That honestly matters way more than people realize in production scenarios. Can you explain why you'd choose RADIUS over LDAP for a particular authentication scenario? Do you know when split tunneling makes sense versus full tunnel mode?
That's the level they're testing at.
System administration and getting the appliance running
Right out of the gate, 15-20% of the exam focuses on basic system admin tasks. This means you're configuring IP addresses, setting up DNS and NTP (because time sync matters way more than people think when you're dealing with certificate validation and log correlation), and getting your routing tables sorted.
Licensing? Bigger deal than it sounds.
Node-locked versus subscription models have different implications for your deployment, and you need to know how to import, renew, and manage those licenses without taking your VPN offline.
Firmware upgrades sound simple until you're dealing with version compatibility between your PCS appliance and the clients your users are running. You need to understand the upgrade path, when to apply security patches immediately versus waiting for a maintenance window, and also how to roll back if something goes sideways. Administrative access configuration includes setting up admin users with appropriate permissions, maybe using certificate-based authentication for admins (which is honestly best practice but a lot of shops skip it), and configuring those network interfaces properly: management, internal, external, VLAN tagging, the whole nine yards.
System certificates deserve special attention because certificate issues cause probably 40% of the support tickets I've seen in production PCS deployments. You're importing server certificates, building proper CA chains with intermediates, setting up renewal procedures before things expire. Standard stuff but critical. SNMP configuration lets you integrate with your monitoring stack, whether that's v2c with community strings or v3 with proper authentication.
And backup procedures? Not sexy, but absolutely critical when you need to restore a configuration at 3 AM because someone fat-fingered a policy change. Actually reminds me of this one time a junior admin decided to "clean up" old authentication areas on a Friday afternoon without checking what was still mapped to active roles. Took down VPN access for about 800 remote users. That was a fun weekend. Anyway, backups matter.
Authentication areas and making identity actually work
This domain grabs 20-25% of the exam weight, and for good reason: authentication is where most real-world complexity lives. You're dealing with Active Directory, LDAP, RADIUS, certificate-based auth, SAML federation, OAuth, and honestly the list keeps growing based on what enterprises need. Each authentication server type has specific use cases. AD integration means understanding domain controllers, getting your search base configuration right, mapping attributes properly, dealing with nested groups (which trip people up constantly).
LDAP configuration requires you to know bind DNs, craft search filters that actually work, figure out which attributes map to username and group membership, and set up SSL/TLS connections because nobody should be sending credentials in cleartext. RADIUS authentication involves configuring primary and secondary servers for redundancy, shared secrets, timeout and retry settings. All that jazz. Certificate-based authentication opens up a whole world of PKI complexity: client certificates, CA trust chains, CRL and OCSP validation for revocation checking.
SAML federation for single sign-on is increasingly common, especially in enterprise environments where users expect to authenticate once and access everything. You need to understand IdP integration, how assertion mapping works, what attribute statements are and how they flow through the authentication process. It's not rocket science but there's detail. Multi-factor authentication integration brings in token servers, push notifications, OTP methods. And then you're building authentication policy rules that consider device type, location, time-based restrictions, all layered together.
The PCS Practice Exam Questions Pack at $36.99 covers these authentication scenarios pretty thoroughly, which matters because this stuff gets complicated fast.
Password management features include caching decisions, password change redirection to your directory servers, account lockout policies. You might configure anonymous authentication areas for limited guest access, depends on your use case. When you've got multiple areas configured, area mapping and precedence rules determine which area gets tried first, and understanding that logic is critical for troubleshooting authentication failures.
User roles and actually controlling who gets access to what
Another 15-20% of exam content focuses on roles and resource policies. Role mapping is conceptually simple: users authenticate, the system looks at their attributes (group membership, certificate fields, authentication server responses), and assigns them to roles. But implementation details matter.
You're creating custom roles with specific permissions and restrictions. Configuring role mapping rules that evaluate LDAP/AD groups or certificate attributes.
The General role is a default, but most real deployments need custom roles with adjusted access based on job function or security clearance. Role inheritance and precedence determine what happens when a user matches multiple roles. Within each role, you're defining resource policies: web resources with URL patterns and rewriting options, file resources for SMB/CIFS access, Network Connect policies for layer-3 VPN with IP pools and split tunneling configurations, application bookmarks with SSO integration.
Web resource policies use URL patterns with wildcards, and you need to understand rewriting options and caching policies. Network Connect policies control IP address assignment. DNS settings, routing tables, access control lists. Basically everything that makes the VPN tunnel actually useful. Bookmarks can auto-launch applications, pass parameters, integrate with SSO systems. Session timeout settings per role include idle timeout, maximum session length, concurrent session limits. Selective rewrite policies handle Java, ActiveX, cookies, headers for application compatibility. Not gonna lie, getting rewrite policies right for complex web apps is more art than science sometimes.
Client access and VPN configuration details
Client access and VPN configuration takes up 15-20% of the exam. You're deploying Pulse Secure clients through various methods: manual downloads, automatic installation, pre-configured packages with connection profiles baked in. Connection profiles specify server lists, certificate validation requirements, protocol preferences. All the settings users shouldn't have to think about. Network Connect provides layer-3 VPN functionality with IP address assignment, DNS settings, routing tables.
Split tunneling versus full tunneling is a classic decision point with security implications. Split tunnel routes only specific traffic through the VPN, full tunnel forces everything through. Each has trade-offs. You need to understand route tables, traffic steering, when each approach makes sense for your environment. Clientless access via web browser works for some applications but has rewriting limitations and compatibility issues. Secure Application Manager provides granular application-level control, which some orgs prefer. Mobile device access for iOS and Android involves native clients, MDM integration, per-app VPN configurations.
Connection sets group VPN resources and policies logically. Client-side certificate deployment and validation tie back to that PKI knowledge. Compression and encryption settings affect performance. You're balancing security and speed, choosing algorithms appropriately based on your threat model and performance requirements. IPv6 support matters in dual-stack environments. Client update and version enforcement policies make sure users aren't running ancient vulnerable clients.
If you're studying for this section, the PPS deployment exam covers some related concepts around policy enforcement that might help build context.
Endpoint security and Host Checker policies
Host Checker grabs 10-15% of exam weight but punches above that in real-world importance. This is pre-connect and post-connect endpoint compliance checking: is the user's device running current antivirus, is the OS patched, are there prohibited applications running? Host Checker operates agentlessly in most cases, which is architecturally interesting.
You're creating endpoint security policies that check operating system versions, validate antivirus status (definition file age, real-time protection enabled), verify patch levels. Supported antivirus vendors are specific. You need to know which ones Host Checker can actually query, because it won't magically detect every security product out there. Custom Host Checker rules use registry keys, file existence checks, running process verification. When endpoints fail compliance checks, remediation actions kick in: quarantine roles with limited access, remediation instructions directing users to fix their systems, maybe complete access denial depending on your security posture.
Integration with third-party endpoint compliance solutions like OPSWAT or NAC platforms extends Host Checker's capabilities beyond what it can do natively. Cache Cleaner policies remove sensitive data after session termination, important for shared or untrusted devices. Secure Virtual Workspace isolates user sessions to prevent data leakage. Expression-based policies let you build complex compliance logic with AND/OR conditions and multiple criteria, which you'll need for sophisticated security requirements. Getting these policies right requires understanding both the technical capabilities and your organization's security requirements.
Logging, monitoring, and fixing things when they break
The final 15-20% covers logging, monitoring, and troubleshooting. Arguably the most practical domain, honestly. You're dealing with multiple log types: system logs, event logs, user access logs, admin access logs. Each serves different purposes for auditing and troubleshooting. Configuring syslog forwarding to external SIEM platforms requires understanding facility codes, severity levels, message formats.
User access monitoring tracks active sessions. Historical access patterns, bandwidth usage. Simple stuff but key.
The system monitoring dashboard shows real-time statistics: CPU, memory, concurrent user counts, throughput. Common authentication failures have recognizable patterns like area misconfiguration, authentication server connectivity issues, credential problems. Client connectivity troubleshooting follows a methodology: check connection logs, capture network traces, validate certificates, verify routing.
Resource access problems require diagnosing policy conflicts, rewriting issues, application compatibility problems. Performance tuning involves adjusting connection limits, caching settings, compression parameters. Tweaking things until performance meets your SLA. Certificate-related issues are everywhere: expiration, chain validation failures, name mismatches, revocation checking problems. Debug logging and packet captures become necessary for advanced troubleshooting. Can't avoid it when weird issues pop up. Interpreting log messages and error codes for root cause analysis is a skill that only comes with practice and exposure to real production issues.
The PCS Practice Exam Questions Pack for $36.99 includes scenario-based troubleshooting questions that mirror the kind of thinking you'll need on exam day and in production environments. Honestly, the troubleshooting domain is where practical experience really shows. You can memorize configuration steps all day, but diagnosing why authentication is failing for users in one AD group but not another requires understanding how all the pieces fit together.
Prerequisites and Recommended Experience for PCS Exam Success
Pulse Secure's Pulse Secure PCS Administration and Configuration certification is one of those credentials that sounds narrow, but honestly maps to a bunch of real enterprise problems: remote access, identity, certificates, endpoint posture, and the "why is Bob locked out again" support grind. It's a vendor exam, sure. Still. If you've ever babysat an SSL VPN during a patch window, you already know this is less about memorizing buttons and more about understanding flows.
Short version. You need hands-on time. Paper knowledge cracks fast.
What this certification actually proves
The PCS Administration and Configuration cert validates that you can administer a Pulse Connect Secure appliance in a real environment, not just click through a wizard and hope. The exam tends to poke at the stuff you touch during deployments and outages: areas, roles, authentication servers, client delivery, certificates, endpoint checks, and log-based troubleshooting.
You're basically proving you can handle secure remote access appliance administration, including SSL VPN configuration and policies, plus the ugly bits like certificate chains and auth failures that only show up at 2 a.m. in the logs.
Who this is for (and who will hate it)
If your job title is network admin, security admin, IAM-adjacent sysadmin, or you're the "VPN person" by accident, this fits. It's also a good match if you're chasing a Pulse Connect Secure VPN admin certification to align with a role that owns remote access.
Brand new to networking? Don't. Not yet. This exam assumes you can reason about TCP/IP behavior and security controls without getting lost in vocabulary.
The stuff everyone asks about the exam
Cost and passing score are the two "People Also Ask" items that never go away, and vendors change these details more often than they should. Pulse Secure has historically delivered exams through their certification program and partners. Pricing can vary by region and delivery method, so you'll want to verify in the current exam listing or your test provider portal. If you're budgeting, assume "professional cert pricing," not "cheap practice quiz pricing."
Passing score? Same deal. Many vendor exams don't publish a fixed passing score publicly, or they change scoring models between versions. You plan for competence, not for gaming a number. The thing is, if you're searching "PCS exam objectives" and "passing score" at the same time, that's usually a sign you should spend more time in logs and less time in forums.
What the exam tends to cover (so your prep isn't random)
Most PCS blueprints cluster into a few buckets:
System setup basics cover licensing, updates, base networking, admin access. Identity and auth include user roles, areas, authentication servers, plus SSO options like SAML or RADIUS flows. Policy and access means roles, bookmarks, resource policies, split tunneling, and least-privilege decisions. Client access involves Pulse client deployment, SSL VPN behavior, troubleshooting client connections. Endpoint posture addresses endpoint security, host checker policies, remediation actions, what happens when a device fails checks. Certificates and crypto deal with X.509, trust chains, SSL/TLS, the practical consequences of getting these wrong. Troubleshooting requires logs, event views, report interpretation, isolating whether the problem is DNS, auth, routing, or policy.
High availability and enterprise infrastructure comes up too, depending on your exam version. If you've seen PCS behind load balancers or reverse proxies, you know why this matters. The "works internally but not externally" tickets often come from that layer, not the VPN itself.
Official prerequisites (what the vendor says)
Here's the clean part: Pulse Secure PCS prerequisites are basically "none." No formal prerequisite cert. No mandatory course requirement. Officially, you can register and take it.
Realistically, that's marketing. Practical IT experience is strongly recommended if you want to pass without brute-force memorization. The exam is allergic to pure theory.
Recommended experience (what actually makes you exam-ready)
Sweet spot's around 6 to 12 months of hands-on administration of Pulse Connect Secure appliances or something similar in the SSL VPN family. That can be supporting an existing deployment, assisting on a rollout, or owning change requests and troubleshooting.
Even better if you've done these tasks repeatedly, because repetition teaches you the "why," and the exam loves "why" disguised as "which setting fixes this symptom."
Install and do initial appliance setup, including network interfaces and admin access. Configure authentication areas with the right auth server mappings. Create roles and resource policies that don't accidentally over-grant access. Deploy clients and deal with the weird client-side compatibility problems. Implement Host Checker policies and understand what a failure looks like for the user. Troubleshoot common issues using logs, client logs, packet-level thinking.
One sentence reality check. If you've never built roles. Expect pain.
Networking fundamentals you need (not optional)
You need to be comfortable with TCP/IP, DNS, routing, NAT, firewalls, VLANs, basic troubleshooting. Not "I read a Network+ book once," but "I can explain why DNS split-horizon breaks bookmarks" level. PCS issues often look like "VPN is down," when it's really a routing asymmetry, a firewall rule, or NAT rewriting something that breaks the return path.
If you want a foundation cert, CompTIA Network+ or CCNA knowledge maps well here. You'll be translating symptoms into network causes while thinking about policy at the same time.
Operating systems (because endpoints are messy)
Windows, Linux, macOS. You don't need to be a kernel wizard, but you should know how to troubleshoot client connectivity and compatibility. Certificate stores, browser behavior for web portals, local firewall conflicts, how endpoint posture checks behave differently per OS.
Half of "PCS configuration and troubleshooting" is figuring out whether the appliance is lying or the endpoint is lying. Usually it's neither. It's just assumptions.
Authentication and directory services (where most configs go sideways)
Active Directory and LDAP basics matter a lot. Directory structure, group membership, nested groups (and whether your auth method resolves them), how users get mapped into roles. Understanding RADIUS and SAML flows helps too, because misconfigurations often show up as redirects, assertion issues, or "authentication succeeded but authorization failed" weirdness.
If you've never traced a login attempt across IdP logs, PCS logs, and directory logs, the exam's scenario questions will feel unfair. They're not unfair. They're normal.
PKI and certificates (the silent exam boss)
PCS lives and dies on certificates. You need a working understanding of X.509 certificates, CAs, intermediates, trust chains, lifecycle management like renewals and revocation. Also, practical stuff: SANs, key sizes, what breaks when you swap a cert, why clients suddenly throw warnings after "a simple change."
This is where many candidates lose time. They memorize terms, but the exam wants you to recognize outcomes. Handshake failure, browser warnings, client trust issues, or SAML failures triggered by cert mismatches.
Security concepts you're expected to already know
SSL/TLS basics, encryption purpose, authentication methods (RADIUS, SAML), hardening principles. You should understand least privilege and policy enforcement, because PCS is basically RBAC expressed through areas, roles, resource policies.
Compliance awareness helps too. HIPAA, PCI-DSS, SOX. You don't need to quote controls, but you should understand why access policies get stricter, why logging matters, why endpoint posture exists beyond "security theater."
Actually, funny thing about compliance. I once watched a consultant spend four hours trying to justify why they needed 90-day cert rotation when the actual requirement was just "valid certificates," which, you know, could've been annual with proper lifecycle management. But the client heard "strict" and went full paranoid. Sometimes the toughest part of security work isn't the tech, it's walking people back from overkill without sounding like you don't care. Anyway.
Web technologies (yes, really)
PCS touches HTTP/HTTPS behavior constantly. Cookies, sessions, URL rewriting, web app structure. If you've ever debugged a web bookmark that fails only after login, you've already used this knowledge. If you haven't, you'll meet it on the exam.
Scripting (not required, still helpful)
No one's saying you need to write Python tooling to pass. But basic awareness of PowerShell, bash, or Python helps when you're automating checks, parsing logs, validating certificate chains quickly.
Short note. It's a bonus. Not a gate.
Training, labs, and the prep time that actually works
If you can swing it, the official PCS Administration and Configuration training course (often 3 to 5 days, instructor-led or self-paced) lines up tightly with how vendors think. It's not magic, but it reduces wandering.
Labs matter more. Minimum 40 hours hands-on is a good target, and you can burn through that quickly if you practice real workflows. Build areas, break areas, fix areas, rotate certs, simulate auth server outages, test Host Checker failures, practice reading logs until it's boring.
Also, read the official Pulse Connect Secure Administration Guide for your exam version. Not skimming. Actually reading. Vendor exams love vendor wording, and the Pulse Secure PCS study guide you build from official docs is often better than any random summary online.
Time commitment: budget 60 to 100 hours total across training, self-study, labs, practice exams. Less if you already run PCS weekly. More if you're learning PKI from scratch.
Practice tests and sample questions (what to trust)
PCS practice tests can help with pacing and identifying weak areas, but be picky. Bad questions teach bad habits. Look for questions that explain why an answer's right and reference documentation or a config outcome.
If you want something quick for drilling, the PCS Practice Exam Questions Pack is priced at $36.99 and can be useful for repetition, especially when you pair it with lab verification instead of treating it like truth from the sky. Treat it as a checkpoint, not a replacement for lab time. Later in prep, loop back and run the PCS Practice Exam Questions Pack in timed sets, then rebuild the scenario in your lab until the reasoning feels automatic.
What makes the exam hard (and how to lower the difficulty)
"How hard is the Pulse Secure PCS exam?" comes down to whether you can think in systems. The tough parts are usually policy logic (how areas and roles interact, how a small mismatch blocks access), auth flows (successful authentication vs failed authorization, where to look for proof), troubleshooting (interpreting logs without guessing, knowing what layer to test next).
A systematic troubleshooting methodology's your advantage. Start with the user story, confirm network reachability, validate DNS, check cert validity, verify auth server responses, confirm role mapping, document what you changed. That last part matters. The exam likes clean thinking.
Exam day tips that save points
Don't rush. Read the scenario twice. Watch for "best next step."
Role and area mapping mistakes are the classic trap, along with certificate pitfalls like incomplete chains or wrong CN/SAN. If a question mentions browsers, think cookies and HTTPS. If it mentions "works for some users," think group membership, role mapping rules, endpoint posture differences.
Renewal and staying current (what you can control)
Pulse Secure's renewal rules can vary by program version, and some vendor tracks change names or policies over time. Check the current policy for validity period, recertification options, whether higher-level exams count.
Practical advice: keep up with release notes and security advisories, because PCS is security infrastructure and the threat model changes. Stay comfortable with vendor documentation and knowledge base articles, because that's what you'll use at work anyway.
Community helps. Forums, user groups, professional networks. Not for "answers," but for patterns and war stories that make exam scenarios feel normal.
One last nudge. Build a lab. Break it on purpose.
And if you want extra repetition toward the end, the PCS Practice Exam Questions Pack can be a decent way to pressure-test your readiness, as long as you're still validating everything against the docs and, honestly, your own configs.
Difficulty Level Assessment and Common Exam Challenges
Real talk about where this exam sits on the difficulty scale
Okay, so here's the deal. The Pulse Secure PCS Administration and Configuration exam? It's intermediate territory, honestly. Definitely tougher than your basic CompTIA Network+ or those entry-level vendor certs, but it won't absolutely destroy you like some of the advanced security architect exams out there. Those things are brutal. Industry chatter suggests somewhere around 60-70% of people pass on their first attempt, which sounds about right if you've actually spent time in the product and didn't just skim a PDF the night before.
I've talked to admins who walked in thinking "hey, I configure VPNs all day, how hard can this be?" and then got absolutely wrecked by the authentication flow questions. The exam assumes you know the difference between setting up a basic SSL VPN and actually understanding how Pulse Secure's architecture works under the hood. And I mean, there's a gap between clicking through the admin console and truly grasping why your configuration does what it does.
The authentication maze that trips everyone up
The single biggest challenge area?
Authentication flows. No question.
You need to understand how areas, authentication servers, role mapping, and policies all interact in these multi-tier scenarios, which gets complicated fast because it's "user logs in, gets access." It's more like: user hits this area, which checks this auth server, which returns these attributes, which map to this role through this logic, which then applies these policies.. and oh yeah, there might be secondary auth and step-up authentication involved too.
The exam loves throwing scenarios where multiple authentication servers are configured and you need to figure out which one actually processes the request. Or they'll give you a user who should have access but doesn't, and you need to trace through the entire area-to-role-to-policy chain to spot where it breaks. This stuff requires actual understanding of the architecture, not memorization. The thing is, you can't fake your way through it.
And role mapping?
That's where people really start sweating. When you've got users coming from different directory sources, with overlapping group memberships, and multiple role mapping rules that might apply.. determining which role actually gets assigned requires knowing the precedence rules cold. The exam will absolutely test whether you understand what happens when rules conflict.
Policy logic is its own special nightmare
Here's where it gets fun.
You might have resource policies, role-based policies, selective rewrite policies, and caching policies all potentially applying to the same user session. Which ones take precedence? What happens when a user has multiple roles? Do the policies merge or does one win? The exam doesn't just ask you to configure these things. It asks you to predict outcomes when configurations overlap or conflict, and honestly, that's where a lot of people stumble.
I've seen scenario questions that give you a full configuration dump and ask why a specific user can access Resource A but not Resource B when both seem to have similar policy assignments. You need to work through the logic systematically, checking role assignments, resource policies, URL matching patterns, and policy precedence.
Takes time. Takes focus. Takes actually knowing how the evaluation engine works.
Troubleshooting scenarios separate the doers from the readers
The exam loves throwing log excerpts at you. Like, here's 15 lines from the system log with some authentication failures and SSL errors mixed in, now tell us what's actually broken. If you've never stared at Pulse Secure logs during a real outage, these questions are brutal. The log format, the error codes, the timing of events.. you need familiarity that only comes from hands-on work.
Configuration snippets are another favorite. They'll show you a partial config and ask what's wrong or what it will actually do. Sometimes the issue is subtle, like an incorrect DN format in an LDAP server configuration or a missing certificate in the trust chain. Other times it's about understanding the implications of a setting, like what happens to existing sessions when you change a role mapping rule. Wait, do existing users get booted or grandfathered in? You need to know.
Certificate and PKI knowledge is non-negotiable
Certificate questions destroy people.
Not the basic "what's a certificate" stuff, but real scenarios. Why is certificate validation failing for this specific user? What's wrong with this certificate chain? How do you properly configure intermediate CAs? What happens when certificate revocation checking is enabled but the CRL is unreachable?
The exam tests whether you understand the full PKI implementation, not just how to upload a certificate file, because there's a massive difference between those two things. You need to know about certificate purposes, extended key usage, subject alternative names, and how Pulse Secure actually validates certificates during different authentication scenarios.
SAML federation adds another layer here, with certificate-based assertion signing and encryption. I spent probably three hours one night trying to figure out why SAML assertions kept failing validation in a test environment, and it turned out the IdP's signing certificate had been renewed but the metadata hadn't been updated. Stuff like that doesn't show up in the documentation flowcharts.
Host Checker expressions require actual syntax knowledge
Creating Host Checker policies with complex Boolean logic isn't intuitive, and the exam knows it. You might need to write or debug an expression that checks for antivirus software AND a specific OS version AND registry keys AND file versions, with proper parentheses and operators. Get the syntax wrong and the whole policy fails. The exam will show you expressions and ask what they actually check, or give you requirements and ask you to identify the correct expression.
I've seen questions where the logic is subtly wrong. Like using OR when AND is needed, or checking for the existence of a file when you should be checking its version. If you've never actually built and tested Host Checker policies in a lab, you're guessing, plain and simple.
Split tunneling configuration is deceptively complex
Everyone thinks they understand split tunneling.
Then the exam asks about routing implications.
it's "enable split tunnel, add some networks." You need to understand what happens to DNS requests, how the routing table gets modified on the client, what traffic actually goes through the tunnel versus direct, and the security implications of each configuration choice. And I mean, these choices matter way more than people realize.
Questions might present a scenario where users report they can't access internal resources even though split tunneling is configured. Is it the routing configuration? DNS resolution? The resources policy? The client-side network adapter settings? You need to think through the entire packet flow. Honestly, understanding the difference between full tunneling, split tunneling with DNS tunneling, and split tunneling without DNS tunneling requires more than reading a feature description.
SAML federation isn't just checkbox configuration
SAML integration questions go deep.
Attribute mapping, claim rules, IdP versus SP configuration, metadata exchange, assertion validation.. the exam tests whether you actually understand federated authentication or just followed a setup wizard once. Troubleshooting SAML failures requires knowing what's in the assertion, how attributes map to roles, where certificate validation happens, and what each error message actually means.
I've talked to people who failed specifically on SAML questions because they'd never seen a SAML assertion or debugged attribute mapping issues. The product documentation explains how to configure it, but the exam asks why it's not working when something's misconfigured. Totally different skill set.
Time pressure is real with scenario questions
You've got 90 to 120 minutes for 60 to 75 questions, which works out to roughly 90 seconds per question. Sounds reasonable until you hit the multi-part scenario questions that require reading through configurations, analyzing symptoms, and selecting the correct diagnosis and remediation. Those can easily eat five minutes if you're thorough. Rush them and you'll miss critical details. Spend too long and you'll run out of time.
The exam doesn't evenly distribute difficulty. You might cruise through 15 questions in 20 minutes, then hit a complex troubleshooting scenario that demands serious analysis. Time management matters. Some people recommend flagging the lengthy scenarios and coming back after finishing the quicker questions, but that only works if you're disciplined about actually returning to them.
Product terminology isn't generic networking terms
Here's something that catches people: Pulse Secure uses specific terminology that doesn't always align with generic VPN concepts. Areas aren't the same as domains. Roles aren't exactly the same as groups. Resource profiles, bookmarks, connection profiles.. these have specific meanings in the Pulse Secure context. The exam uses product-specific terminology throughout, and if you're translating in your head from generic concepts, you'll misunderstand questions.
Someone coming from Cisco ASA or Palo Alto VPN experience needs to learn Pulse Secure's vocabulary and architecture. The concepts might be similar, but the implementation and terminology differ enough that assumptions will hurt you. The PCS certification track really emphasizes product-specific knowledge over general VPN theory.
Study time varies wildly by background
If you're already administering Pulse Secure in production and deal with authentication, policies, and troubleshooting regularly? You're probably looking at 40-60 hours of focused study to fill gaps and formalize knowledge. You know the product but need to systematize your understanding and cover edge cases you haven't encountered.
IT professional new to Pulse Secure but with solid networking and security background?
Plan for 80-100 hours.
You need to learn the product architecture, get hands-on with configurations, understand the terminology, and build troubleshooting experience. Reading documentation isn't enough, you need lab time.
Entry-level candidate without deep networking or VPN experience?
Honestly, you're looking at 120+ hours and that needs to include extensive lab practice. You're learning fundamental concepts and product specifics simultaneously. The exam isn't designed for entry-level folks, even if nothing technically prevents you from taking it.
Hands-on practice isn't optional
The gap between theoretical knowledge and practical application is massive with this exam. You can read about how role mapping works, but until you've actually configured authentication servers, created mapping rules, tested with different user accounts, and debugged why a particular user gets the wrong role.. you don't really understand it. The exam asks questions that assume you've done this stuff, not just read about it.
Configuration syntax precision matters too. Some questions test whether you know the exact steps, menu paths, or configuration options. Not just the general concept of "configure LDAP authentication" but the specific fields, formats, and sequence of steps. The thing is, this knowledge only comes from actually using the admin console or CLI repeatedly.
People who study exclusively from dumps or practice tests without lab work consistently struggle with the practical troubleshooting and configuration questions. And look, compared to something like Pulse Policy Secure or the vADC Administration track, the PCS exam is more focused on real-world admin tasks than abstract concepts, which means hands-on experience matters even more.
Conclusion
Wrapping up your PCS prep
Okay, real talk here.
The Pulse Secure PCS Administration and Configuration certification? it's gonna fall into your lap. You're dealing with a legit test of whether you actually understand secure remote access appliance administration, not just whether you can fumble through some GUI like it's 2015. This exam digs deep into user roles areas authentication servers in ways that'll wreck you if all you've done is surface-level config work.
The thing is, the policy logic trips up most people. You might know how to set up SSL VPN configuration and policies inside and out, but then the exam hits you with this scenario involving overlapping resource policies and split tunneling bookmarks. Suddenly you better really understand that evaluation order or you're toast. I've watched admins with two solid years of PCS experience just completely bomb questions about endpoint security host checker remediation flows because they'd never actually troubleshooted a failed posture check in the wild.
What matters now? Hands-on time.
Real time, not theoretical BS. Spin up a VM, configure areas with different auth servers, break things intentionally, then read those logs like your job depends on it. Because eventually it might. The official documentation's solid but dry as hell. You'll be snoring halfway through the certificate chain validation section, I promise. Instructor-led training helps if your budget can handle it. But honestly? Most of what you need's already sitting in the admin guide and your own glorious lab mistakes.
Practice questions though, they're huge. Really big for your score. You can know the material backwards and forwards but still freeze up completely when a question asks about the difference between user roles and resource policies in some weird edge case you've never considered. Timed practice sets reveal where your gaps actually are. Maybe you're totally fine on authentication flows but embarrassingly shaky on high availability clustering or logging troubleshooting.
I spent three days last month just messing around with role mapping before it finally clicked. Sometimes you need that kind of repetitive, slightly tedious practice.
That's exactly where the PCS Practice Exam Questions Pack comes in clutch. Third-party practice tests? They vary wildly in quality, trust me. But a good question bank mirrors the actual exam objectives and difficulty pretty faithfully. You want questions that make you think about PCS configuration and troubleshooting the way the real exam does, not just those brain-dead memorization dumps everyone pretends work.
Don't wait until exam day to discover you'd completely misunderstood how role mapping works with SAML assertions. Test yourself right now. Identify those weak spots, patch them up. You've already put in the study time, so make sure it counts when you're sitting in that testing center staring at the screen. The Pulse Connect Secure VPN admin certification's worth having, but only if you actually earn it instead of winging it.
Show less info
Hot Exams
Related Exams
Whole Life Asset Management
Red Hat Certified Specialist in Virtualization exam(RH318)
Infor Certified OS Associate
LPIC-1 Exam 101, Part 1 of 2, version 5.0
CIW v5 E-Commerce Designer
Oracle Fusion HCM Base Cloud Service 2016 Implementation Essentials
Salesforce - Implementing Field Service Lightning
Implementing Data Engineering Solutions Using Microsoft Fabric
SAP Certified Associate - Backend Developer - SAP Cloud Application Programming Model
Designing HPE Hybrid IT Solutions
Splunk Enterprise Certified Architect
Certified Lean Six Sigma Black Belt (CLSSBB)
Cisco Certified Design Expert Practical Exam
EC-Council Certified Security Analyst (ECSA)
Pulse Connect Secure (PCS): Administration and Configuration
Pulse Policy Secure (PPS) Deployment Implementation and Configuration
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.