PRMIA 8008 Exam III Overview and Structure
Okay, real talk here. If you've made it through the first two PRM exams, you already know the drill with quantitative methods and financial theory. PRMIA 8008, that's PRM Exam III, is where things get real, where you actually learn how risk managers do their jobs in banks, asset managers, and corporate treasury departments. Not just calculating Value at Risk or understanding bond math anymore but dealing with governance frameworks, operational loss events, credit portfolio models, counterparty exposure calculations, and balance sheet management all at once. The thing is, it's not theoretical anymore.
The Professional Risk Manager Exam III is the third and final core exam in PRMIA's certification pathway. It synthesizes everything from Exam I and Exam II and applies it to enterprise risk management frameworks across all major risk domains. We're talking operational risk, credit risk, counterparty credit risk (CCR), market risk, asset-liability management (ALM), and funds transfer pricing (FTP). That's a lot to cover. The breadth is what trips up most candidates, honestly.
What the 2015 Edition means for today's candidates
The 2015 Edition curriculum came out in the aftermath of the financial crisis, when regulators were still tightening screws on banks. Basel III was rolling out. Enhanced counterparty credit risk standards were becoming the norm. Operational risk measurement got more sophisticated with better loss data and scenario analysis frameworks, and ALM and liquidity risk management moved from back-office afterthoughts to C-suite priorities.
Now it's 2026. But don't dismiss this.
The 2015 content isn't outdated. The foundational frameworks haven't changed that much. Sure, we've added FRTB for market risk, IFRS 9 and CECL for credit provisioning, climate risk considerations, and machine learning applications, but the core principles of operational risk measurement, credit portfolio models (PD/LGD/EAD estimation), CVA/DVA calculation, VaR and stress testing, and ALM/FTP concepts remain base knowledge. Any risk manager who doesn't understand these frameworks is going to struggle regardless of what fancy AI tools their firm adopts.
Not gonna lie, you should verify with PRMIA if there've been curriculum updates since 2015. They might've incorporated post-crisis regulatory changes or new industry practices, but the exam designation is still PRMIA 8008, and the structure remains focused on integrated risk frameworks.
How the exam is actually delivered
PRMIA 8008 is a computer-based test. Administered at Pearson VUE centers worldwide. You'll sit in a testing cubicle, headphones optional, with a basic calculator function on screen. The format typically includes 60-80 multiple-choice questions, and you get somewhere between 120-150 minutes to complete it. That's roughly 1.5-2 minutes per question. Sounds generous until you hit a scenario-based operational risk question that requires you to evaluate governance structures, control effectiveness, and risk mitigation strategies all in one go.
Questions span all risk domains. They're weighted according to industry relevance. Expect heavier stuff on operational risk and credit risk compared to, say, FTP, which is more specialized. But you can't skip any domain. There will be questions on every topic, and you need a solid grasp across the board to pass.
Some questions are straightforward recall. What's the definition of Loss Given Default? How is CVA calculated? What are the three lines of defense in operational risk governance? Others are application-based. You might get a scenario about a bank's trading desk that suffered operational losses, and you need to identify which risk indicators failed, what controls should've been in place, and how the loss should be categorized under Basel operational risk event types.
Building on the PRM pathway foundations
If you're coming straight from Exam I and Exam II, you've already covered quantitative methods. Probability, statistics, time series, derivatives pricing. You know financial instruments inside and out. Exam III takes those tools and shows you how they fit into enterprise risk frameworks.
I mean, Exam II taught you Monte Carlo simulation. Exam III asks you to apply Monte Carlo to credit portfolio risk modeling, operational risk capital calculation, or market risk stress testing. You learned option pricing models earlier. Now you're using them to value counterparty credit exposure with collateral and netting agreements. The math isn't harder, but the context is way more complex.
This integration is what makes Exam III valuable. You're not just a quant who can code a VaR model. You understand how that VaR model fits into the bank's risk appetite framework, how it's governed by the CRO's office, how it gets reported to the board, and how it interacts with credit risk limits and operational risk controls. That complete view is what senior risk roles require.
Actually, funny story. I knew this guy who spent six months building the most beautiful VaR model you've ever seen, mathematically perfect, until the CRO asked him how it aligned with the firm's risk appetite statement and he just stared blankly. That's the kind of thing Exam III prevents.
Who should actually take this exam
PRMIA designs Exam III for risk professionals with a few years of experience already. If you're fresh out of school, you can take it, but you'll find the governance and practical application questions harder without real-world context. The sweet spot is 2-5+ years in financial institutions, corporate treasury, consulting, or regulatory roles.
Credit analysts take this exam to broaden into market risk and operational risk. Market risk quants take it to understand credit counterparty exposure and ALM. Operational risk managers take it to round out their knowledge of credit and market risk frameworks. Treasury professionals take it because ALM and FTP are directly relevant to their daily work.
The exam also appeals to consultants and auditors who need to evaluate risk frameworks across multiple institutions. If you're advising a bank on Basel compliance, you need to understand operational risk measurement, credit risk modeling, counterparty risk capital, and balance sheet management. Exam III gives you that breadth.
Seven major domains you need to master
Let's break down what's actually on the exam.
Risk governance and frameworks comes first. That's your risk appetite statements, three lines of defense, board oversight, risk culture, all that stuff. Qualitative but critical, because every other domain operates within these governance structures.
Operational risk management and measurement is huge. You need to know the Basel Advanced Measurement Approaches (AMA), loss data analysis, scenario analysis, risk control self-assessment (RCSA), key risk indicators (KRIs), and the seven Basel operational risk event types. This domain trips up a lot of candidates from market or credit backgrounds who've never dealt with operational loss databases or control testing.
Credit risk modeling and portfolio management covers rating systems, PD/LGD/EAD estimation, credit portfolio models like CreditMetrics and CreditRisk+, concentration risk, credit migration, and Basel IRB approaches. If you're from an operational risk or treasury background, this section requires serious study time.
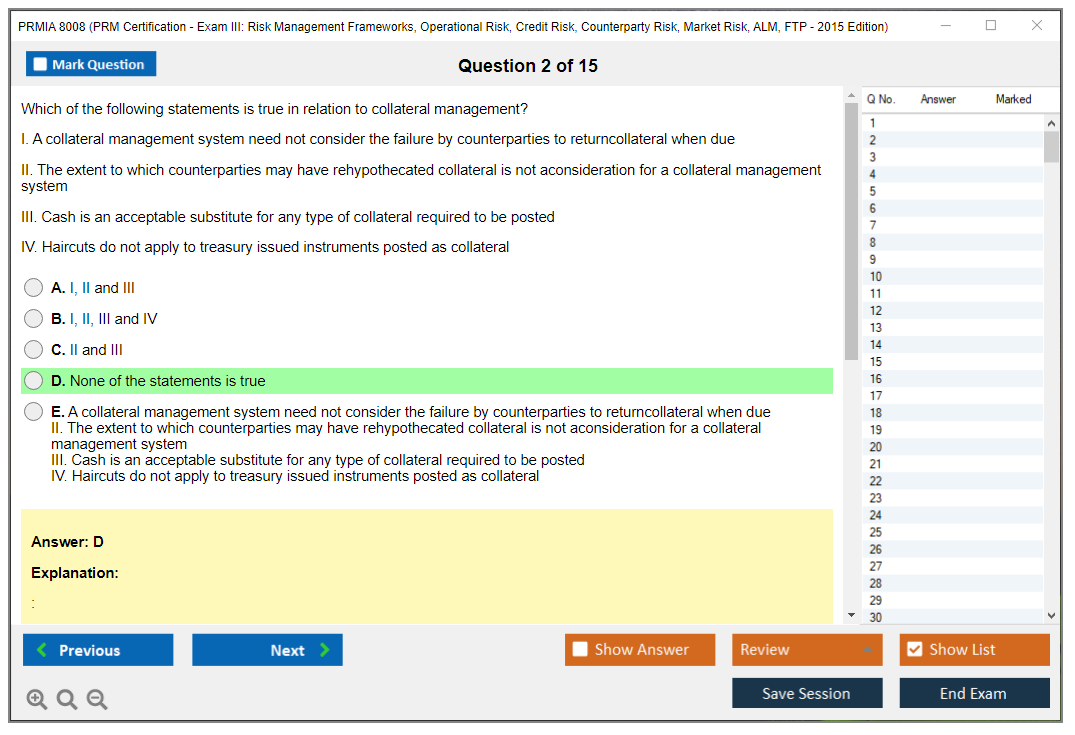
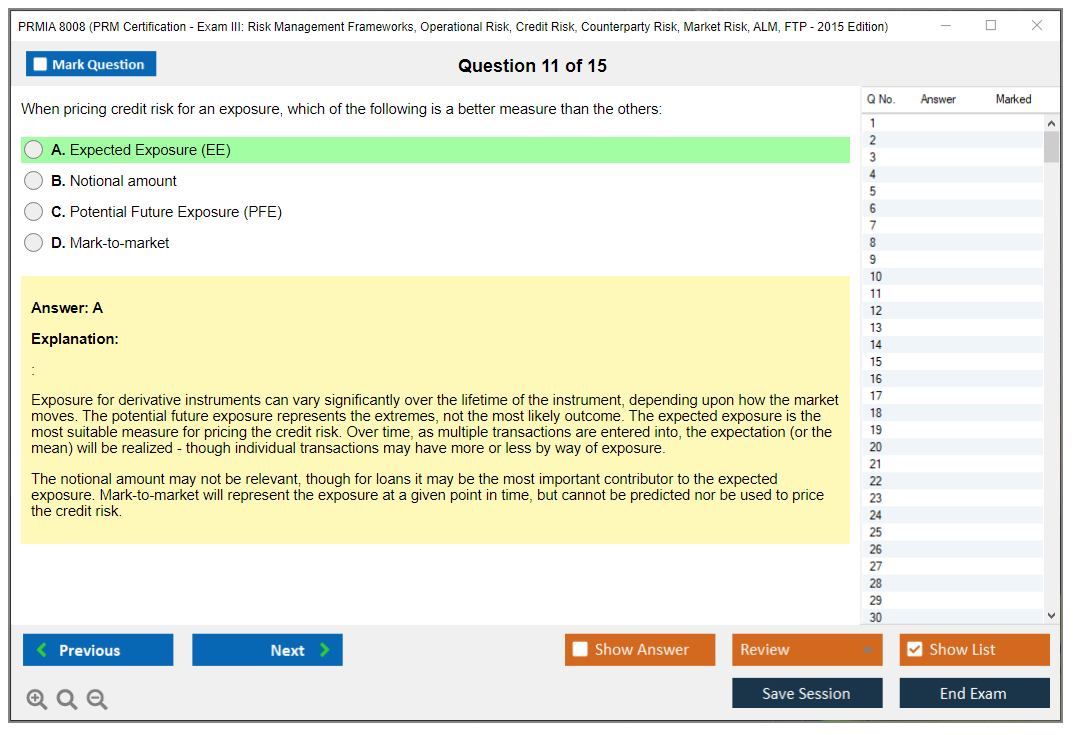
Counterparty credit risk and CVA/DVA is where derivatives and credit risk intersect. You calculate potential future exposure (PFE), expected positive exposure (EPE), credit valuation adjustment (CVA), debit valuation adjustment (DVA), and understand netting agreements, collateral management (CSA agreements), and wrong-way risk. This material is technical and requires comfort with derivatives pricing.
Market risk measurement and stress testing includes VaR (historical, parametric, Monte Carlo), expected shortfall (ES/CVaR), backtesting, stress testing frameworks, model risk management, and Basel market risk capital approaches. If you've worked in a trading risk role, this should be familiar, but you need to understand the governance and validation aspects too.
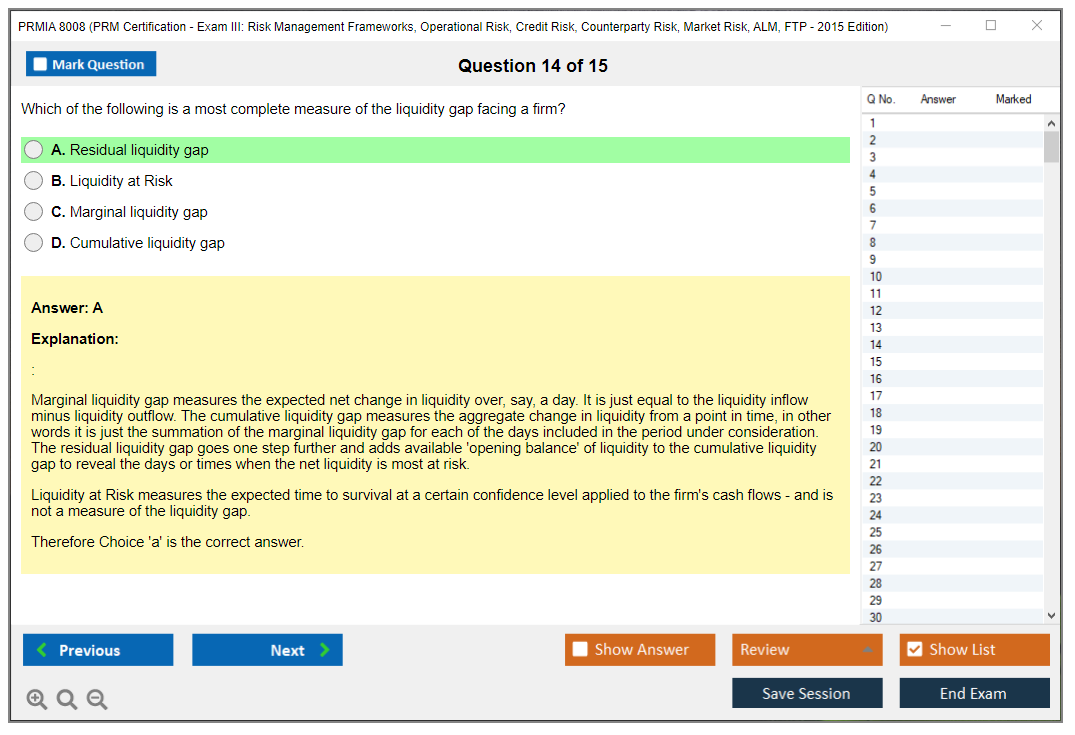
Asset-liability management covers interest rate risk in the banking book (IRRBB), liquidity risk management, balance sheet structure, duration gap analysis, earnings-at-risk, and economic value of equity (EVE) sensitivity. ALM is often new territory for market risk and operational risk professionals, so budget extra time here.
Funds transfer pricing is the most specialized domain, covering FTP frameworks, matched-maturity transfer pricing, liquidity cost allocation, option cost calculation, and how FTP supports risk-adjusted performance measurement. Not every institution uses sophisticated FTP, so this might be entirely new material depending on your background.
Alignment with regulatory standards
The curriculum reflects Basel II/III guidelines extensively. Operational risk measurement approaches, credit risk IRB formulas, counterparty credit risk capital (SA-CCR, IMM), market risk standardized and internal models. You'll see BCBS 239 principles on risk data aggregation and reporting, which became critical after the crisis when banks couldn't even aggregate their exposures properly.
International Association of Credit Portfolio Managers (IACPM) best practices show up in credit risk content. Financial Stability Board recommendations on risk governance and risk appetite frameworks are embedded throughout. The exam isn't just teaching you to pass a test. It's aligning your knowledge with what regulators expect and what international banking standards require.
Career impact and role positioning
Look, certifications don't automatically get you promoted. But PRM with Exam III completion signals that you understand enterprise risk management at a senior level. You're not just a specialist in one risk type. You can speak the language of operational risk with the OpRisk team, discuss credit portfolio models with the credit risk head, evaluate counterparty exposure with the derivatives desk, and contribute to ALM discussions with treasury.
This positions you for roles like Chief Risk Officer (at smaller institutions), Head of Market/Credit/Operational Risk, Risk Analytics Director, ALM Manager, and senior risk advisory positions in consulting. I've seen Exam III help candidates transition from specialist roles (like market risk analyst) into broader risk leadership positions where they oversee multiple risk types.
The certification is recognized globally. North America, Europe, Asia-Pacific, Middle East. PRMIA's international membership base means the credential travels well if you're looking at opportunities across regions or with multinational institutions.
How this differs from FRM and other certifications
FRM (Financial Risk Manager) puts heavy weight on market risk and credit risk, with lighter coverage of operational risk. PRMIA 8008 gives balanced treatment to operational risk, which is critical if you're working in operational risk management or need to understand OpRisk frameworks for governance roles.
CERA (Chartered Enterprise Risk Analyst) comes from the actuarial world and focuses on insurance and actuarial risk. PRM is banking and financial markets oriented.
The PRM pathway's three-exam structure (quantitative foundations, financial theory, risk frameworks) is thorough but requires more time investment than single-exam certifications. However, Exam III's breadth across operational, credit, counterparty, market, ALM, and FTP gives you coverage that most other certifications don't match.
Preparation realities and time investment
Most candidates need 150-250 hours of focused study. That range is wide because it depends heavily on your background. If you're an operational risk manager, you'll breeze through OpRisk but need serious time for credit portfolio models and counterparty CVA calculations. If you're a credit analyst, you'll need to learn operational risk measurement and ALM/FTP from scratch.
The domains that typically require the most attention? Operational risk (for non-OpRisk professionals), credit portfolio modeling (technical and math-heavy), counterparty risk (complex derivatives knowledge required), and ALM/FTP (new concepts for many). Market risk is often the most familiar domain for candidates coming from trading or market risk roles.
Don't sleep on the qualitative governance material. It's easy to focus on the quantitative stuff because that's more concrete, but governance questions can make or break your score. Understand risk appetite frameworks, three lines of defense, board reporting, risk culture, and regulatory expectations.
Pass rates and what to expect
PRMIA doesn't publish official pass rate statistics, which is frustrating. Based on industry feedback and candidate forums, first-time pass rates seem to be in the 50-65% range. That's not terrible, but it's not a gimme either. Thorough preparation matters a lot.
The exam uses a scaled scoring approach, so there's no published "you need 70% to pass" threshold. PRMIA sets the passing standard based on the difficulty of the specific exam form you receive. This means your raw score gets converted to a scaled score, and you either pass or you don't. You won't get a numeric score report, just pass/fail with maybe some domain-level feedback.
Candidates with practical experience in multiple risk domains tend to perform better because they can contextualize the questions. If you've actually implemented an operational loss database or calculated CVA for a derivatives portfolio, you'll recognize the scenarios and understand the details better than someone who's only studied theory.
Practical applications in daily work
Here's where Exam III really shines compared to earlier PRM exams. The content directly supports what you do on the job. If you're in risk model validation, you need to understand credit risk models, operational risk AMA approaches, market risk VaR models, and counterparty exposure calculations. All covered.
Managing operational loss data analysis? Exam III teaches you loss distribution approaches, scenario analysis frameworks, and risk control self-assessment methodologies. Working in credit portfolio management? You learn concentration risk measurement, credit migration models, and portfolio credit risk approaches. If you work in treasury, the ALM and FTP content is directly applicable to interest rate risk management and liquidity risk assessment.
The exam also complements other credentials well. If you have a CFA charter, adding PRM gives you risk management depth that CFA doesn't cover in detail. If you have FRM, PRM's operational risk and ALM content fills gaps. If you're a CPA or CA working in financial services audit, PRM helps you understand the risk frameworks you're evaluating.
Staying current beyond 2015
The 2015 Edition is still relevant, but you should be aware of developments since then. FRTB (Fundamental Review of the Trading Book) changed market risk capital calculation. IFRS 9 and CECL introduced expected credit loss provisioning that differs from Basel incurred loss approaches. Climate risk has become a material consideration in risk frameworks. Model risk management has gotten more sophisticated with regulatory scrutiny increasing.
Machine learning and AI applications in risk measurement are emerging. Credit scoring models using alternative data, operational risk indicator monitoring with ML, market risk scenario generation with AI. These aren't likely tested heavily on a 2015-based exam, but understanding where the industry is headed helps you contextualize the foundational material.
Check PRMIA's website for any curriculum updates or supplemental materials they've released. The Exam IV case studies exam might also incorporate more current examples of risk management failures and best practices.
Cost-benefit for employers and candidates
Organizations that sponsor PRM candidates get staff with standardized knowledge across all risk domains. That's valuable for regulatory compliance, risk reporting, and strategic risk decision-making. Instead of having siloed specialists who only understand their narrow domain, you develop professionals who can integrate operational risk controls with credit risk limits with market risk stress testing.
For candidates, the time and financial investment (exam fees, study materials, preparation time) pays off through career advancement opportunities and salary increases associated with senior risk roles. PRM certification is recognized by major banks, asset managers, insurance companies, and regulatory bodies as evidence of solid risk management competency.
The certification also provides structured learning that's hard to get through on-the-job experience alone. Unless you've worked across multiple risk domains, you won't naturally develop expertise in operational risk and counterparty risk and ALM/FTP. The exam forces you to build that breadth, which makes you more versatile and valuable.
Risk Management Frameworks and Governance
Where Exam III fits (2015 edition)
PRMIA 8008 Exam III is the "how a bank actually runs risk" exam. Not math-only, not policy-only. It sits right in the middle where governance, limits, models, controls, and reporting all collide, and the 2015 Edition framing matters because it leans hard on Basel-era thinking (Pillar 2, ICAAP, stress testing discipline) while still expecting you to understand day-to-day workflows like operational risk RCSAs, market risk limits, and counterparty exposure management.
People ask, What's covered in PRMIA 8008 (PRM Exam III)? Look, it's a big sweep: risk management frameworks and governance, PRMIA 8008 Operational Risk, PRM Exam III Credit Risk, PRMIA 8008 Counterparty Risk, PRM Exam III Market Risk, plus balance sheet stuff like PRM ALM and FTP exam content. It's the exam where you stop thinking in isolated silos and start thinking "enterprise".
Really broad stuff.
This one's huge.
Board governance and the risk appetite backbone
Enterprise risk management begins at the board. Not in the risk team. Not in Internal Audit. The board sets direction, approves the risk appetite framework, and then holds management to it, which sounds obvious until you see how many firms treat appetite as a poster on the wall instead of a set of decision rules that actually bite when P&L is tempting. That's where things fall apart in real crisis moments, I mean really fall apart.
Risk appetite's the aggregate level and types of risk the organization's willing to accept while chasing strategy, and in PRM Exam III Risk Management Frameworks terms you should be able to describe it in both quantitative and qualitative ways. Quantitative's where you see VaR limits, economic capital targets, earnings volatility bands, liquidity buffers, concentration limits, and stress loss tolerances. Qualitative's the stuff that makes or breaks you in real life: risk culture expectations, acceptable practices, prohibited activities, escalation norms, and "we don't do that here" lines around conduct and reputational risk.
Here's the part candidates miss: appetite isn't capacity. Capacity's the max risk you can take before you threaten viability or breach hard constraints like regulatory capital, liquidity survival horizons, debt covenants, or even operational resilience. Appetite sits inside capacity. Capacity's a cliff. Appetite's the guardrail you agree not to push against every day, because living on the cliff edge is how institutions end up in weekend resolutions. I watched a desk at my last shop slowly drift toward their capacity limit over six months while claiming they were "optimizing". Nobody thought they'd actually hit it until they did.
Three lines of defense (and why it still shows up everywhere)
The three lines of defense model's basically the default governance org chart in finance for a reason. It separates ownership, oversight, and assurance, so when something goes wrong you can trace accountability without finger-pointing theater.
First line's the business. They take risk. They own it. Trading desks, lending teams, treasury, operations. They manage controls, monitor their limits, and escalate issues.
Second line's independent risk management and compliance. They set policies, define frameworks, monitor, challenge, and decide whether the first line's story makes sense.
Third line's internal audit, which gives independent assurance that the first and second lines are doing what they claim, and that the control environment actually works.
This model breaks when escalation paths are fuzzy, or when second line "advises" but can't challenge, or when audit gets pulled into running controls. The thing is, Exam III likes crisp delineation. Clear accountability. Documented handoffs. And a real breach process, not vibes.
What a good risk appetite statement actually includes
A risk appetite statement isn't a single sentence like "we're conservative". That's useless. A workable statement's got components you can test.
- Strategic context tying appetite to the business model, growth plans, and constraints. If you're pushing into used lending, your credit appetite and underwriting standards have to admit that reality instead of pretending you're still a prime-only shop.
- Quantitative metrics with thresholds and limits across risk types. You'll see VaR or expected shortfall in market risk, stress loss limits, PD/LGD concentration caps in credit, liquidity ratios, operational risk tolerance for downtime, plus triggers that force escalation before you breach.
- Risk capacity boundaries, which are the "do not cross" survival constraints.
- Qualitative standards on conduct and culture. Things like: how sales incentives work, when to stop trading a product, what behaviors are prohibited even if profitable, and expectations for transparency.
- Governance process covering monitoring, reporting, breach handling, and who approves temporary exceptions.
Two details matter. First, limits should cascade. Second, breaches should have teeth.
Cascading appetite into real limits
Board-level appetite's abstract until it turns into desk limits and portfolio constraints. Risk appetite cascading's the translation layer: enterprise metrics become business unit limits, then portfolio limits, then trader or product limits, and you keep doing that until someone can actually act on it at 9:15 a.m.
Limit frameworks usually include hard limits (can't exceed), soft limits (early warning), and triggers (force review). Breaches need defined escalation: who gets notified, how fast, what remediation's acceptable, and when you shut down activity. Not gonna lie, a lot of "limit management" in the wild's just email threads and delayed approvals. Exam III wants the clean version: documented governance, monitoring cadence, and evidence of challenge.
Risk identification, taxonomy, and the risk register habit
Risk identification's where frameworks either become real or become a binder. A standardized risk taxonomy's the glue that lets a global firm talk consistently about exposures across businesses and legal entities. Typical categories you should know cold: market, credit, operational, liquidity, strategic, reputational, and compliance. You can add model risk, conduct risk, and third-party risk depending on the firm, but the point's consistency.
A risk register's the working inventory: identified risks, owners, inherent risk assessment, key controls, residual risk, KRIs, and mitigation plans. It also forces clarity on scope. Which legal entity owns the risk. Which process. Which system. Which vendor.
Ownership matters here.
Controls too.
Evidence seals it.
This ties straight into PRMIA 8008 study materials that talk about operational risk measurement and loss data, because you can't measure what you haven't classified, and you can't aggregate losses if every team calls the same event by a different name.
Assessment methods: qualitative to quantitative
Exam III expects you to match method to risk type and data quality.
Qualitative assessment's common for strategic and emerging risks. Likelihood-impact matrices show up here, and you're grading severity without pretending you've got clean distributions. Semi-quantitative scoring's common in operational risk management, where you might score frequency and impact bands, factor in control strength, and track changes over time through RCSAs and KRIs. Fully quantitative modeling's where market and credit live: VaR/ES, backtesting, sensitivities, PD/LGD/EAD frameworks, portfolio models, and counterparty exposure simulations.
Frequency matters too. High-velocity risks like trading portfolios might be monitored daily with intraday triggers, while slower-moving risks like strategic shifts might be quarterly, with ad-hoc reviews when the environment changes fast.
Committees: who decides what
Board Risk Committee oversight's the top layer. They review whether the framework's effective, whether the firm's inside appetite, and whether big exposures make sense. Management committees do the heavy lifting, and PRMIA 8008 (PRM Exam III) loves to test whether you understand their mandates and escalation.
Common ones include ALCO, which handles balance sheet risk, liquidity, and interest rate risk, and it gets messy fast because ALM and FTP choices affect product pricing, deposit strategy, and hedging behavior across the whole bank. This is where theory meets uncomfortable reality, where a decision about funding credit gets tangled up with what the mortgage desk can actually offer customers.
Credit Risk Committee covers underwriting standards, portfolio concentrations, watchlists, and big-name exposures.
Market Risk Committee focuses on limits, model performance, stress results, and concentration.
Operational Risk Committee tracks incidents, control issues, remediation, and KRIs.
ALCO deserves detail. It's where treasury meets business reality, and where asset-liability management funds transfer pricing decisions can quietly change incentives, like making a business line "look profitable" because FTP credits them for sticky deposits, even if the liquidity assumptions are too optimistic.
Reporting and MI that people actually read
Risk reporting and management information should show risk profile against appetite. Limit utilization. Stress test results. KRI trends. Incidents and near misses. Emerging risks. And it should be calibrated to audience, because the board needs material themes and boundary breaches, while a desk head needs granular limit usage and drivers.
Good MI's got lineage.
And definitions.
Bad MI's got 14 versions of "exposure".
This is where BCBS 239 comes in. Risk data aggregation and reporting expectations push accuracy, completeness, timeliness, and adaptability, plus data governance, documentation, and controls around data quality. The exam angle's usually: can the firm aggregate exposures across legal entities quickly during stress, and can it explain where the numbers came from without hand-waving.
Stress testing, scenario analysis, and economic capital
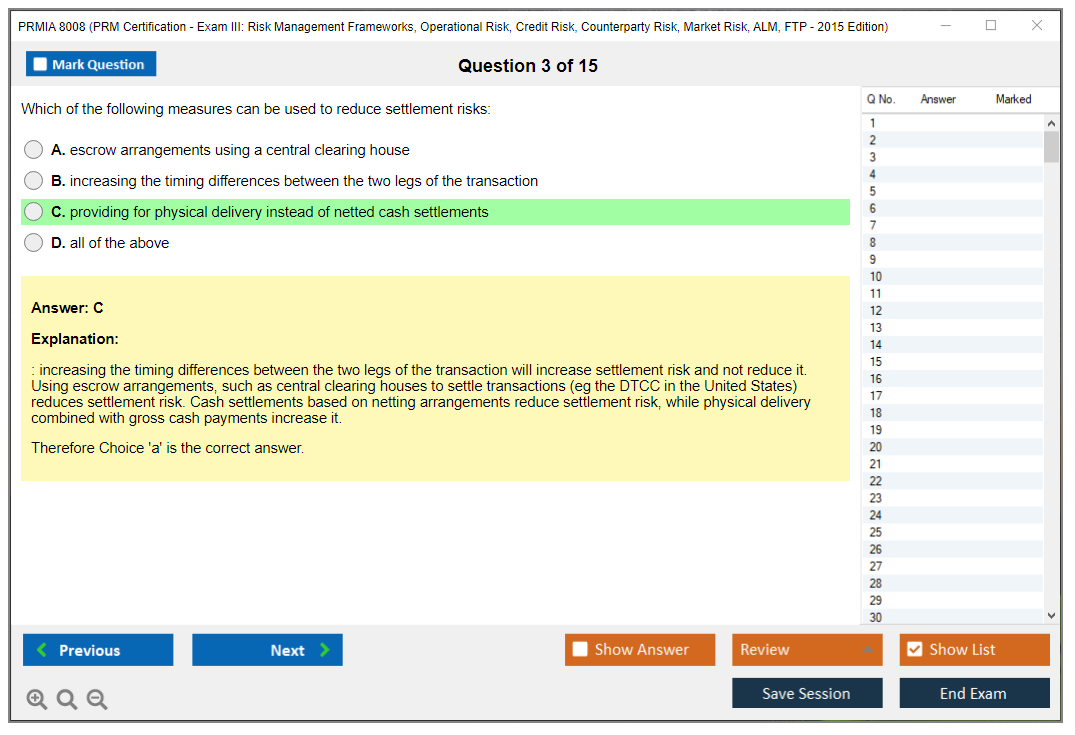
Statistical measures like VaR are backward-looking. Stress testing's forward-looking. Enterprise-wide stress testing asks what happens to capital, liquidity, and earnings under severe but plausible scenarios, and it forces you to see correlations across PRM Exam III Market Risk, PRM Exam III Credit Risk, and liquidity all at once. Scenarios can be macro (rates spike, recession, commodity shock), idiosyncratic (fraud, cyber outage), or combined.
Economic capital frameworks sit alongside that. You allocate capital based on risk contribution, typically using VaR or expected shortfall at a high confidence level over a one-year horizon, and then you can do risk-adjusted performance like RAROC. This is where governance meets budgeting: capital becomes a scarce resource, and business lines either earn their keep or they don't.
Model risk management and "correct model, wrong use"
Model risk management's a governance framework for model development, implementation, validation, and ongoing monitoring. The big three sources of model risk are worth memorizing: wrong model, correct model used incorrectly, and implementation errors. Counterparty risk's a classic trap here because exposure models, netting sets, collateral rules, and CVA assumptions can all be "mostly right" while producing dangerously wrong decisions if someone applies them outside their intended scope.
This ties into Basel credit risk and counterparty credit risk content: CCR add-ons, netting and collateral, wrong-way risk, and the governance around who can approve model changes and overrides.
Emerging risks and control effectiveness
Emerging risks are the stuff not in your historical dataset. Tech disruption, regulatory shifts, geopolitics, climate transition. You manage them with horizon scanning, expert judgment, scenario analysis, and early warning indicators, and you revisit them when signals change.
Fast.
Risk mitigation's controls. You evaluate design effectiveness (does the control address the risk) and operating effectiveness (does it work consistently). Control testing, key control indicators, and control self-assessments feed remediation plans. This is where PRMIA 8008 Operational Risk tends to live on the exam, along with operational risk measurement and loss data and how incidents map back to processes and controls.
Regulatory expectations: Pillar 2, ICAAP, SREP
Supervisors care less about your pretty framework slides and more about whether you can prove you understand your own risk profile. Pillar 2 of Basel's the Supervisory Review Process, and it pushes banks to run an ICAAP: assess capital adequacy relative to risks, strategy, and stress results. In many jurisdictions the supervisor runs an SREP, reviewing governance, risk management, capital planning, and liquidity, then applying requirements or guidance.
Policies change, though.
So do fees.
For People Also Ask items like the passing score for PRM Exam III, best PRMIA 8008 practice questions, and whether PRM certification needs renewal or CPD, PRMIA doesn't always publish a fixed percentage pass mark and policies can shift, so you should verify current details directly in PRMIA candidate guidance and pricing pages.
Global firms add another twist. Subsidiary governance, regional risk committees, outsourced function oversight, and third-party risk controls all need to fit into the same framework without turning into duplicated bureaucracy. Hard. Necessary. Exam-worthy.
Operational Risk Management and Measurement
Why operational risk matters on the PRMIA 8008
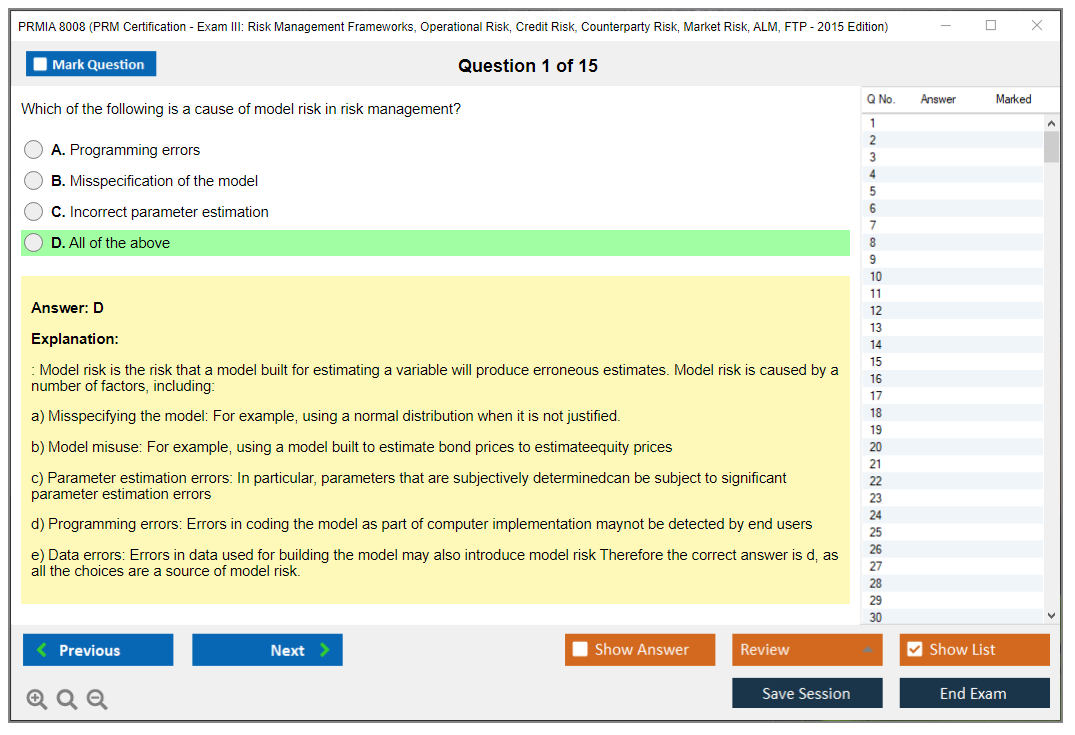
Okay, so operational risk? It's one of those areas where everyone nods along until you ask them to actually measure the damn thing. The Basel Committee definition is where you start: operational risk is "risk of loss resulting from inadequate or failed internal processes, people and systems or from external events." That exact wording shows up on exam questions, so yeah, memorize it word-for-word.
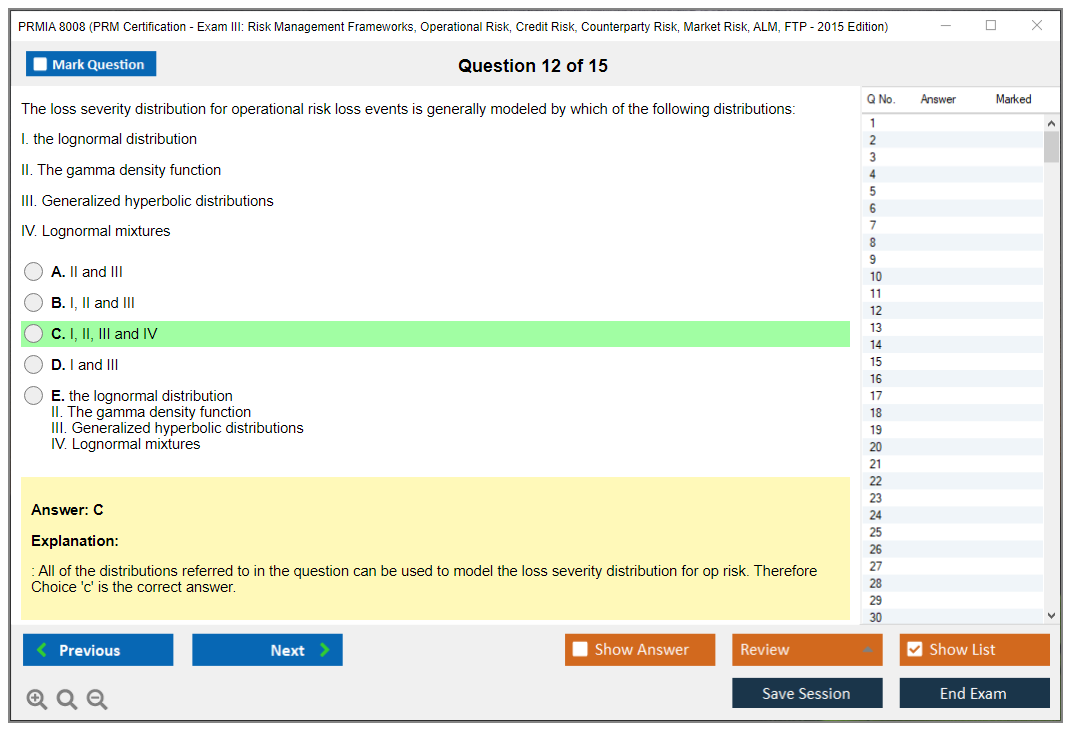
Here's the thing that gets people twisted up though. It definitely tripped me up at first. The definition includes legal risk (that's explicitly stated), but it excludes strategic and reputational risk, which honestly feels weird when you first encounter it. You might think a massive reputational hit from a data breach counts as operational risk, and the breach itself definitely does, but the follow-on reputation damage? Technically that's a separate bucket. The Basel framework groups operational losses into seven event types: internal fraud, external fraud, employment practices and workplace safety, clients/products/business practices, damage to physical assets, business disruption and system failures, and execution/delivery/process management failures.
Know those cold.
You'll get scenario questions asking you to classify an event. Trickier than they sound.
Collecting loss data without going crazy
Internal loss data collection forms the foundation for any serious operational risk program. You're capturing event date (when it actually happened), discovery date (when someone finally noticed), accounting date (when it hit the books), gross loss amount, recoveries like insurance payouts or clawbacks or whatever you managed to get back. Business line, event type from those seven categories, and a narrative description round it out. The narrative part? It matters way more than you'd think because it drives root cause analysis later, and that's where you actually learn something useful rather than just filling out forms.
The big debate is always the threshold. Set it too low and you're drowning in paperwork for every $500 stapler theft. Set it too high and you miss important patterns in mid-sized losses that might signal bigger control weaknesses. Most firms land somewhere between $10,000 and $25,000 as the minimum reportable loss. That balances comprehensiveness against administrative burden, though honestly, some banks go lower for specific event types they're particularly worried about.
Not gonna lie, getting business units to actually report losses consistently is harder than the technical setup. You need clear policies, training, a user-friendly system, and frankly some enforcement when people conveniently "forget" to log things. I once worked with a desk that somehow went nine months without a single reportable event, which would be impressive if it were true. It wasn't.
The Loss Distribution Approach and why it's complicated
The LDA is the quantitative heart of Advanced Measurement Approach (AMA) models for operational risk capital. You're modeling frequency and severity separately, then combining them. Wait, let me back up. Frequency is usually Poisson or negative binomial, which tells you how many loss events you'd expect in a year. Severity is trickier because operational losses have fat tails that stretch way beyond normal distributions. A lognormal distribution works okay for the body, but for the tail you need something heavier like Weibull or generalized Pareto distribution.
Once you've got your frequency and severity distributions fitted to historical data, you run Monte Carlo simulation to generate the aggregate loss distribution. Draw a random number of events from your frequency distribution, then draw that many loss amounts from your severity distribution, sum them up. That's one simulated year. Do that 100,000 times and you've got your loss distribution. Capital gets set at the 99.9th percentile or whatever your risk appetite dictates.
The challenge?
You rarely have enough data, especially for severe events. If you've only got five years of internal loss data and you're trying to estimate a 1-in-1000 year loss, you're extrapolating way beyond your data. That's statistically sketchy. That's where external data and scenario analysis come in.
Scenario analysis for the tail
Scenario analysis is structured expert judgment. You get subject matter experts like business heads, control owners, maybe external consultants in a room and walk through plausible but rare operational risk events. What if a rogue trader bypassed all controls? What if ransomware took down core systems for two weeks? What if a regulatory investigation led to a massive fine?
For each scenario you're estimating potential loss frequency (how often could this plausibly happen?) and severity (how bad would it actually be?). The estimates feed into your capital model, particularly for low-frequency/high-severity tail risks that don't show up in your 5-10 years of internal loss data.
Good scenario analysis requires careful facilitation. Anchoring bias is real. If you throw out "$500 million" as an example, everyone's estimates cluster around that number. You want independent initial estimates, then discussion, then re-estimation. Document assumptions thoroughly because auditors and regulators will absolutely challenge them.
RCSA and KRIs for forward-looking risk management
Risk Control Self-Assessment is your bottom-up process where business units identify operational risks, assess inherent risk before any controls, evaluate control effectiveness, and determine residual risk after controls. You're typically doing this annually with quarterly updates, though high-risk areas might need more frequent cycles.
The output is usually a heat map: inherent risk on one axis, residual risk on the other. Control effectiveness gets implied by the gap. For residual risks above appetite you develop action plans with owners and deadlines. It's actually useful when done honestly, but in many firms it becomes a check-the-box exercise where everyone rates their controls as "highly effective" and their residual risks as "low." Obviously nonsense.
Key Risk Indicators are your early warning system. These are forward-looking metrics like staff turnover rates (lose experienced people, errors go up), transaction error rates, system downtime, audit findings, customer complaints, training completion rates. You set thresholds (green, amber, red) and when a KRI trips into amber or red, someone investigates and potentially escalates to management.
The trick with KRIs?
Avoiding indicator overload. Some firms track 500+ KRIs and nobody actually monitors them because it's just noise. Better to have 30-50 really meaningful indicators that people watch closely and act on.
External data and why your losses aren't enough
Consortium databases like ORX, OpRisk Analytics, and SAS OpRisk Global Data aggregate anonymized operational loss data from member institutions. This is incredibly valuable for low-frequency/high-severity events and for firms with limited loss history. If you're a mid-sized regional bank, you've probably never had a $100 million+ rogue trading loss, but you still need to model that risk because it could happen. External data shows you what happened at other firms.
The challenge is scaling. A $500 million fraud at a $2 trillion bank doesn't map directly to your $50 billion balance sheet. You need scaling algorithms based on revenue, assets, or transaction volumes. There's no perfect approach and the choice materially affects your capital number.
You also need to think about relevance. A major retail mis-selling scandal at a UK bank might not be relevant if you don't have that product or that regulatory environment. Filtering external data appropriately requires judgment calls that aren't always clear-cut.
Basel capital approaches from simple to complex
The Basic Indicator Approach is dead simple: operational risk capital equals 15% of average gross income over three years.
That's it.
No modeling, no data collection beyond what you already report financially. It's crude but some small institutions still use it.
The Standardized Approach breaks gross income into eight business lines (corporate finance, trading and sales, retail banking, commercial banking, payment and settlement, agency services, asset management, retail brokerage) with beta factors ranging from 12% to 18%. You apply the beta to each business line's gross income and sum them up. Slightly more risk-sensitive than BIA but still pretty rough.
The Advanced Measurement Approach lets you use internal models combining internal loss data, external loss data, scenario analysis, and Business Environment and Internal Control Factors. You get to "prove" your capital requirement rather than using a formula, which sounds great until you realize the trade-off is massive complexity, data requirements, and regulatory approval processes that take forever. Post-2008 crisis, regulators got more skeptical of banks' AMA models because many underestimated actual losses. Basel III tightened requirements and added a standardized floor under AMA capital.
BEICFs and adjusting for current risk environment
Business Environment and Internal Control Factors let you adjust capital based on your current risk profile beyond what historical losses indicate. Staff experience levels, control quality scores, business complexity metrics, rate of change (new products, systems, M&A integration). These qualitative and quantitative indicators can increase or decrease your modeled capital.
The idea makes sense. If you just acquired another bank and you're integrating systems, your operational risk is higher than historical losses suggest. Obviously. BEICFs should capture that forward-looking shift. In practice, calibrating BEICF adjustments is subjective and regulators often challenged banks that used them to significantly reduce capital.
Mitigation strategies and the role of insurance
You've got four classic strategies. Risk avoidance means exiting high-risk activities, maybe you shut down a product line that's causing too many compliance headaches. Risk reduction is process improvement, automation, enhanced controls, the stuff that actually prevents losses. Risk transfer includes insurance and outsourcing with contractual protections. Risk acceptance is for residual risks within appetite.
Insurance is interesting for operational risk because it can provide capital relief under AMA, subject to regulatory requirements. Fidelity bonds cover employee dishonesty. Professional indemnity covers errors and omissions. Property and casualty covers physical damage. Directors and officers liability covers, well, that. Cyber insurance has exploded in importance over the last decade.
For capital relief, regulators want to see that risk transfer is real: policy limits adequate, insurer creditworthy, terms don't have huge exclusions, premium paid is market-rate. You typically can't recognize more than 20% capital offset from insurance, and that's with a pretty solid policy that actually pays out when you need it.
Cyber risk as a specialized category
Cyber and technology risk deserve special attention because they're growing fast and the tail is getting fatter every year. Information security breaches, ransomware, DDoS attacks, data theft, system failures, technology project blow-ups. These are all operational risk events but they need dedicated governance frameworks that go beyond traditional operational risk management.
You need threat intelligence to understand the attack space, which changes constantly. Vulnerability management to patch systems before someone exploits them. Incident response capabilities to contain breaches quickly when they happen. Regular penetration testing that simulates real attacks. Cyber insurance to transfer tail risk. And honestly, board-level oversight because this stuff can blow up spectacularly and end up on the front page.
The measurement challenge with cyber? The threat environment evolves faster than your historical loss data. What happened three years ago might not predict what's coming at all. Scenario analysis becomes even more important here than in other operational risk areas.
Conduct risk and culture issues
Conduct risk is operational risk from inappropriate behavior that delivers unfair customer outcomes or breaches market integrity. Think mis-selling, market manipulation, LIBOR rigging, predatory lending, the stuff that generates massive fines and congressional hearings. Regulators have hammered banks on this post-crisis.
You measure it through conduct risk indicators: complaint rates, product suitability metrics, sales practice reviews, whistleblower reports. Root causes often trace back to incentive structures and risk culture, which is uncomfortable to acknowledge. If you pay salespeople based purely on volume with no quality metrics, you're going to get conduct issues. It's just math and human nature.
Culture is hard to quantify but it matters enormously for operational risk outcomes. A speak-up culture where people report concerns catches problems early when they're fixable. A cover-your-ass culture where people hide mistakes lets small issues become huge losses.
Third-party and business continuity risks
Third-party risk arises from reliance on vendors and outsourced functions. Cloud providers, payment processors, data centers, call centers. If they fail, you've got a problem that's outside your direct control. Manage it through due diligence before onboarding, contractual protections (SLAs, liability caps, audit rights), ongoing monitoring, and exit strategies in case things go south.
Critical service providers need special attention. If one vendor handles all your payment processing and they go down, you're in serious trouble fast. Concentration risk is real and often underestimated.
Business continuity and disaster recovery ensure you can maintain critical operations during disruptions. Fires, floods, cyberattacks, pandemics, whatever. Business impact analysis identifies time-sensitive processes and sets recovery time objectives. You need alternate facilities, data backup and recovery capabilities, and regular testing that actually simulates realistic scenarios. Pandemic planning got a lot more real after COVID-19 showed that your entire workforce might not be able to come to the office for months.
Model risk and validation challenges
Operational risk models are hard to validate because you don't have enough data to backtest properly. If your model says a $100 million loss should happen once every 50 years, how do you validate that with 10 years of data? You can't really, which is the fundamental problem.
This means solid sensitivity analysis, expert challenge, conservative parameter selection, and acknowledgment of uncertainty become critical parts of model governance. Regulators expect you to understand your model's limitations and hold extra capital if uncertainty is high. If you're preparing for the PRMIA 8008 Exam III, expect questions on model risk and validation approaches because it's a key supervisory focus area.
Reporting and regulatory expectations
Regular reporting flows loss events, KRI trends, RCSA results, scenario outcomes, and capital model outputs to senior management and the Risk Committee. Drill-down capabilities matter. If you see operational losses spiking in one business line, you want to understand why quickly rather than waiting for the quarterly deep dive.
Supervisory guidance from the Basel Committee, EBA guidelines, and regulatory expectations for operational resilience set the bar that firms need to meet. Industry benchmarking through ORX and similar consortia shows you where your peers are and informs practice evolution, though honestly everyone's struggling with the same data limitations.
Regulators increasingly expect operational resilience, not just managing individual risks but ensuring you can withstand and recover from severe disruptions that hit multiple areas simultaneously.
If you're tackling the full PRM curriculum, you've likely already covered foundational material in Exam I and Exam II, and operational risk frameworks build on that quantitative base you established there. The 8008 Practice Exam Questions Pack at $36.99 gives you scenario-based questions that test whether you can apply these frameworks, not just memorize definitions and regurgitate them. After you nail Exam III, Exam IV covers case studies and governance that pull everything together into integrated risk management. For those interested in specialized certifications, the Operational Risk Manager exam goes even deeper on these topics.
Credit Risk Modeling and Portfolio Management
Why this topic matters on PRMIA 8008
Credit risk modeling is one of those Exam III areas where the math's straightforward, but judgment calls aren't. Stuff breaks. Models trained on yesterday's crises miss tomorrow's.
For PRMIA 8008 Exam III, you need clean definitions, basic formulas, and the way banks stitch them into a portfolio view that actually drives limits, pricing, provisions, and capital. Honestly, you've also gotta keep exam context in your head, because PRM Exam III Risk Management Frameworks is about connecting dots across governance, credit, market, PRMIA 8008 Counterparty Risk, and even balance sheet topics like PRM ALM and FTP exam content, not treating credit as some standalone quant toy.
What credit risk is (and how PRM frames it)
Credit risk's the potential loss when a borrower or counterparty fails to meet contractual obligations. That's the umbrella. Under it, the exam wants you to break credit risk into three parts that map directly to modeling workstreams:
Default risk. That's the probability the obligor defaults over a horizon, usually 1 year for regulatory capital.
Exposure risk. How much you're actually on the hook for at the moment of default.
Recovery risk. How much you lose after recoveries, collateral, and workout.
Once you internalize that PD, EAD, and LGD are separate knobs with different data, different biases, and different "oops" failure modes, a lot of PRM Exam III Credit Risk questions get easier. You stop trying to force one model to answer all three.
Expected loss is priced and provisioned. Unexpected loss? That's what capital's for. Examiners love that distinction. They'll test it.
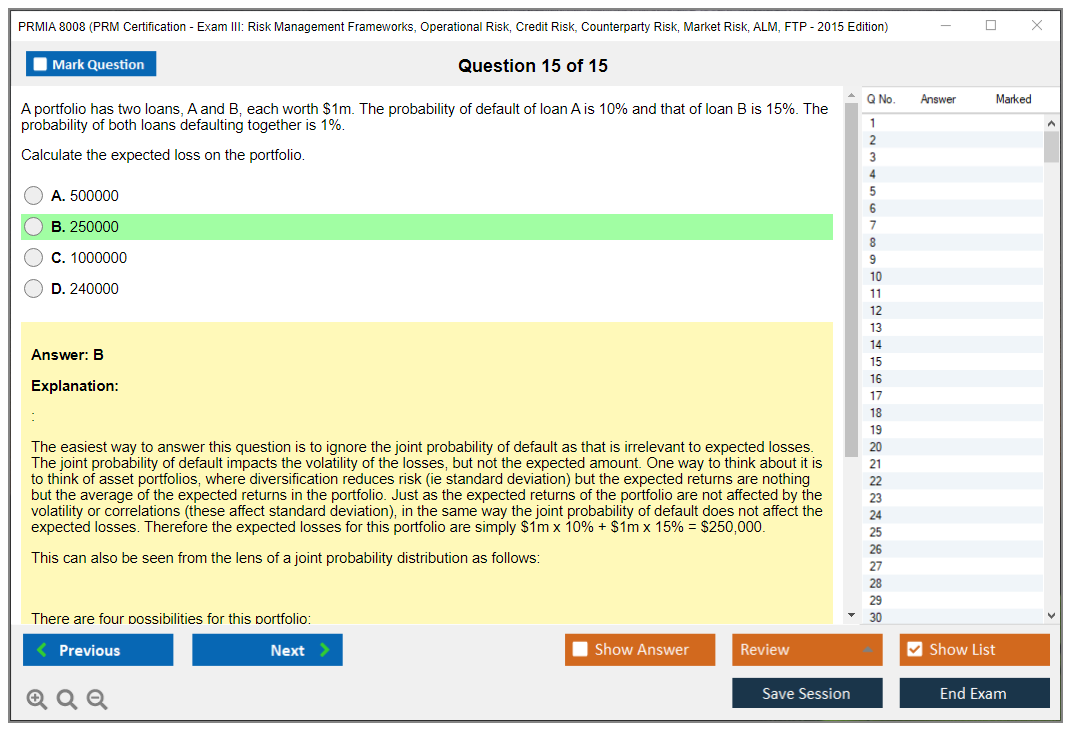
Expected loss vs unexpected loss (the capital story)
Expected loss is the mean of the credit loss distribution:
EL = PD × LGD × EAD.
That's the number you should expect to lose on average, and it belongs in loan pricing, credit spreads, fees, and provisioning. It's not "free." It's baked into the business economics, and it also shows up in accounting and allowance frameworks depending on the regime.
Unexpected loss? The volatility around EL. Not a separate "type" of loss but dispersion, and economic capital's typically set using a high percentile of the loss distribution, often 99.9% in banking contexts, then subtracting expected loss. Capital covers the tail beyond what pricing and provisions already addressed. That sounds academic, but it's the whole reason portfolio correlation matters. Correlation fattens the tail even when average loss looks fine.
One sentence version: EL's the bill, UL's the panic buffer.
PD estimation (how you actually get a default probability)
PD modeling can be done a few common ways, and PRMIA 8008 study materials usually present them as a menu because the "best" method depends on data availability, product type, and whether you need point in time sensitivity.
Some main approaches you're expected to recognize:
- Historical default frequency analysis. Simple cohort method: count defaults over exposures in a grade and get a rate. Great when you've got long, clean internal history. Awful when the portfolio changed, underwriting shifted, or the last recession's missing from your dataset.
- Credit scoring models like logistic regression and discriminant analysis. This is bread and butter for retail and SME. You take borrower attributes, transform, fit, and map to PD. The exam'll often keep it high level, but you should know logistic regression outputs odds, and you still need calibration to real-world default rates.
- Structural models like Merton distance-to-default. Equity value as a call option on assets, default when assets fall below liabilities. Useful conceptually and sometimes in traded firms, but in banking credit books it's often more of a conceptual anchor than the daily PD engine.
- Reduced-form or intensity models. Default arrives as a jump process with a hazard rate that can depend on covariates. This is common in credit derivatives pricing and Basel credit risk and counterparty credit risk discussions, because it ties into spreads and survival probabilities.
- Rating migration matrices. You model transitions across rating states (including default) using a Markov chain approach. Core to portfolio models like CreditMetrics.
Through-the-cycle vs point-in-time PD's a classic Exam III angle. TTC smooths the economic cycle and is stable for capital planning and long-horizon risk appetite. PIT responds to current conditions and is more useful for short-horizon pricing tweaks, limit tightening, and some impairment style thinking, but it can whipsaw. "More responsive" isn't always "more correct."
Random aside: I've seen banks argue over TTC vs PIT for months, only to realize their data quality problem was bigger than their methodology debate. Fix the input before you obsess over the formula.
LGD modeling (recoveries are messy)
LGD's the economic loss as a percentage of exposure at default. In practice it's "one minus recovery rate," but the exam wants you to remember it's collateral value, it's the whole recovery process.
Collateral matters. Haircuts matter.
Liquidation discounts matter. Time matters, because the longer it takes to recover, the more discounting and legal or workout cost you eat. Seniority and security provisions matter, because a first lien term loan isn't the same universe as an unsecured claim sitting behind everyone else.
Here's the part people forget: LGD's cyclical. Downturn LGD's higher because collateral prices fall, buyers disappear, and courts get slow. Recoveries get delayed and discounted harder. Workout teams get overloaded. You can model this with explicit downturn adjustments, regime switching, or conservative calibration, but the exam mostly wants the intuition and the directionality: bad economy, worse LGD.
Also, "economic LGD" isn't always "accounting LGD." Indirect costs show up. Servicing costs show up. Even opportunity cost can be argued, though you usually keep the exam answer to workout costs and recovery delays.
EAD calculation (where exposure surprises happen)
EAD's the amount at risk at default. For a plain term loan, EAD's usually close to the outstanding balance, maybe with accrued interest depending on the definition. Easy.
Revolvers are where things get interesting. For revolving facilities, EAD's current utilization plus an estimate of additional drawdown before default, and that extra piece is captured through a credit conversion factor (CCF). Borrowers draw when stressed. They do it right before default. That's why CCFs exist, and why banks obsess over them.
For derivatives and securities financing, EAD's current exposure plus potential future exposure over the margin period of risk, netting and collateral considered. This is where PRMIA 8008 Counterparty Risk overlaps hard with credit risk modeling, because the exposure profile's driven by market moves, collateral terms, netting sets, and margining frequency. Your "credit" model's partly a market model wearing a credit label.
Short sentence: EAD's not static.
Internal ratings and validation (Basel IRB style thinking)
Internal credit rating systems assign obligors to grades, and each grade maps to a PD (either directly or via a calibration curve). This is at the heart of IRB style frameworks. Governance matters here. Model risk matters here. And yes, risk governance and risk appetite framework language shows up because ratings drive underwriting and limits, not just reporting.
Validation's got a few classic pillars that show up in PRM Exam III practice questions:
Backtesting. Compare realized default rates to predicted PDs by grade over time. If a grade's "1% PD," you can't have it default at 4% year after year without explaining what changed.
Discriminatory power: can the model rank-order risk? Accuracy Ratio and ROC/AUC are common metrics. High AUC means good separation between defaulters and non-defaulters, even if calibration's off.
Calibration testing. This is about level, not ranking. You can have a model that ranks perfectly but predicts PDs that're too low across the board. Calibration fixes that, often with scaling to long-run average default rates or to a target cycle position.
Also worth saying out loud: a rating system isn't only a model. It's policies, overrides, review cadence, documentation, and auditability. That's why this topic lives comfortably next to PRMIA 8008 Operational Risk themes like controls and governance, even if the math looks different.
Portfolio credit risk and correlation (the tail is the problem)
Single-name credit's intuitive. Portfolio credit's where people get wrecked.
Defaults are correlated through systematic factors: economy, industry cycles, regional shocks, commodity price moves, and sometimes plain old crowded exposures. Correlation creates clustering. Clustering creates tail risk. Tail risk's what capital's paying for.
Basel-style approaches embed asset correlation assumptions in the IRB formula. Portfolio models can do it more explicitly using factor models, copulas, or correlated asset returns, and you don't need to become a PhD for Exam III, but you do need to know that correlation drives diversification benefits in the middle of the distribution and concentration pain in the tail. Those two facts can both be true at once.
One more blunt take: "Diversified" isn't a vibe. It's a correlation structure.
Credit portfolio models you're expected to recognize
You'll see a few names come up in the Professional Risk Manager Exam III syllabus style materials.
CreditMetrics's the classic. It models changes in credit quality via rating migrations, and values instruments under different rating states using spread curves, then produces a distribution of value changes and losses. It's intuitive for bonds and loans marked with credit spreads, and it makes migration risk feel real, not just default-or-not.
CreditRisk+ is more actuarial, focusing on default counts and loss distributions with sector factors, often using a Poisson mixture style setup.
KMV-like approaches tie back to structural distance-to-default concepts. Mention those casually, know the vibe, and for the exam, understand what input each family wants most: migrations and spreads, default intensities and exposures, or asset value dynamics.
How portfolio management ties it together (limits, pricing, and capital)
Portfolio management's where PD, LGD, and EAD stop being separate spreadsheets and start becoming decisions. Limits by obligor and sector. Concentration limits. Risk-adjusted pricing and RAROC type thinking. Stress tests that push PD and LGD up together because recessions don't politely affect one parameter at a time.
This is also where cross-topic Exam III stuff sneaks in: market risk shocks change derivative EAD and CCR, liquidity stress affects collateral calls, ALM affects funding and balance sheet capacity, and asset-liability management funds transfer pricing can change which businesses look "profitable" after you charge them for funding, liquidity, and capital. That's why the exam's broad, and why people call it hard.
Quick exam reality check (the "people also ask" stuff)
What's covered in PRMIA 8008 (PRM Exam III)? Risk frameworks plus PRM Exam III Market Risk, operational risk basics including operational risk measurement and loss data, credit and counterparty mechanics, and bank balance sheet topics like ALM and FTP.
What's the passing score for PRM Exam III? PRMIA uses a scaled approach and doesn't usually publish a fixed percent you can game, so you plan like you need to be strong across sections, not perfect in one.
How hard's it compared to other exams? Moderate-to-high, mostly because of breadth and the way questions mix concepts rather than asking you to recite definitions.
Best PRMIA 8008 study materials and practice tests? Start with PRMIA's own readings and sample questions if you can get them, then add a question bank that forces you to compute EL and reason about correlation, validation, and CCR exposure profiles. Do timed sets. Review mistakes brutally.
Does PRM require renewal or continuing education? Policies can change, so check PRMIA directly for current CPD expectations. Don't trust random forum posts from 2017.
That's the credit risk modeling core for Exam III: PD, LGD, EAD. EL vs UL. Correlation and portfolio tails. Then governance and validation so it's math on a slide.
Conclusion
Wrapping up your PRMIA 8008 game plan
Okay, real talk. Passing the PRMIA 8008 Exam III isn't some impossible mountain to climb, but it's also not a walk in the park. You're dealing with everything from operational risk measurement and loss data analysis to Basel credit risk frameworks, counterparty credit risk details, market risk VaR models, and the whole asset-liability management funds transfer pricing universe all crammed into one sitting. That's a lot. The breadth alone? It makes this exam a genuine test of whether you can actually apply risk governance and risk appetite framework concepts across multiple domains, not just parrot back definitions like some trained seal.
The 2015 edition content still holds up for foundational risk management frameworks, even though the field keeps evolving. What really matters is how you prepare, honestly. Scattered reading won't cut it. You need structured PRM Exam III practice questions that mirror the scenario-based, application-heavy style PRMIA loves. Drill your weak spots relentlessly. If counterparty risk and CVA/DVA calculations trip you up? Hit those hard. If operational risk governance and RCSA processes feel fuzzy, spend extra cycles there instead of reviewing what you already know.
Your PRMIA 8008 study materials should include a mix of official readings and real-world case applications, because the thing is, the exam won't just ask you to define credit risk portfolio models. It'll ask you to interpret results, spot weaknesses, recommend controls. Practice tests are non-negotiable here. Timed sets. Full simulations. Error logs you actually review, not just glance at and forget two seconds later.
Time management on exam day separates people who know the material from people who pass. Flag tough questions. Come back. Don't spiral into panic mode. And remember, the Professional Risk Manager Exam III syllabus is designed to test synthesis, not just memorization, so think like a risk manager solving real problems, not a student cramming formulas at 3 AM. I've seen people who knew the content cold still run out of time because they got stuck arguing with themselves over one tricky question in the credit section.
Before you sit for the exam, I'd really suggest working through a solid question bank that covers all the domains. Operational, credit, counterparty, market, ALM, FTP. You need that exposure. The 8008 Practice Exam Questions Pack gives you that end-to-end drill with explanations, so you're not just guessing your way through blindly. It's honestly one of the better ways to identify gaps and build exam-day confidence without wasting time on generic prep that doesn't match PRMIA's style. I mean, not gonna lie, targeted practice is what turns "I think I'm ready" into "I know I've got this."