PCSAE Practice Exam - Palo Alto Networks Certified Security Automation Engineer
Reliable Study Materials & Testing Engine for PCSAE Exam Success!
Exam Code: PCSAE
Exam Name: Palo Alto Networks Certified Security Automation Engineer
Certification Provider: Palo Alto Networks
Corresponding Certifications: Palo Alto Certifications and Accreditations , Paloalto Networks Certification

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
PCSAE: Palo Alto Networks Certified Security Automation Engineer Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 165 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena Palo Alto Networks Palo Alto Networks Certified Security Automation Engineer (PCSAE) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
Palo Alto Networks PCSAE Exam FAQs
Introduction of Palo Alto Networks PCSAE Exam!
Palo Alto Networks Certified Security Automation Engineer (PCSAE) is an exam designed to assess and validate the knowledge, skills, and abilities required to configure, deploy, and troubleshoot Palo Alto Networks Next-Generation Firewall and Panorama.
What is the Duration of Palo Alto Networks PCSAE Exam?
The duration of the Palo Alto Networks PCSAE exam is 2 hours.
What are the Number of Questions Asked in Palo Alto Networks PCSAE Exam?
The Palo Alto Networks PCSAE exam consists of 60 multiple-choice questions.
What is the Passing Score for Palo Alto Networks PCSAE Exam?
The passing score for the Palo Alto Networks PCSAE exam is 80%.
What is the Competency Level required for Palo Alto Networks PCSAE Exam?
The Palo Alto Networks PCSAE exam requires a competency level of advanced.
What is the Question Format of Palo Alto Networks PCSAE Exam?
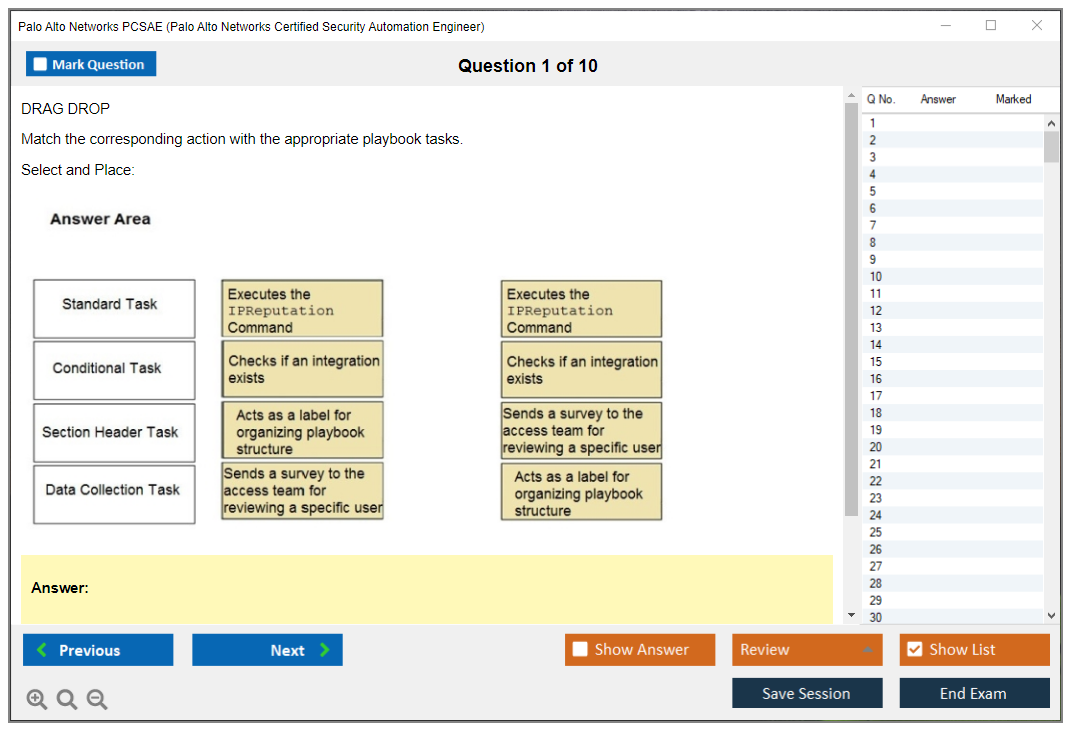
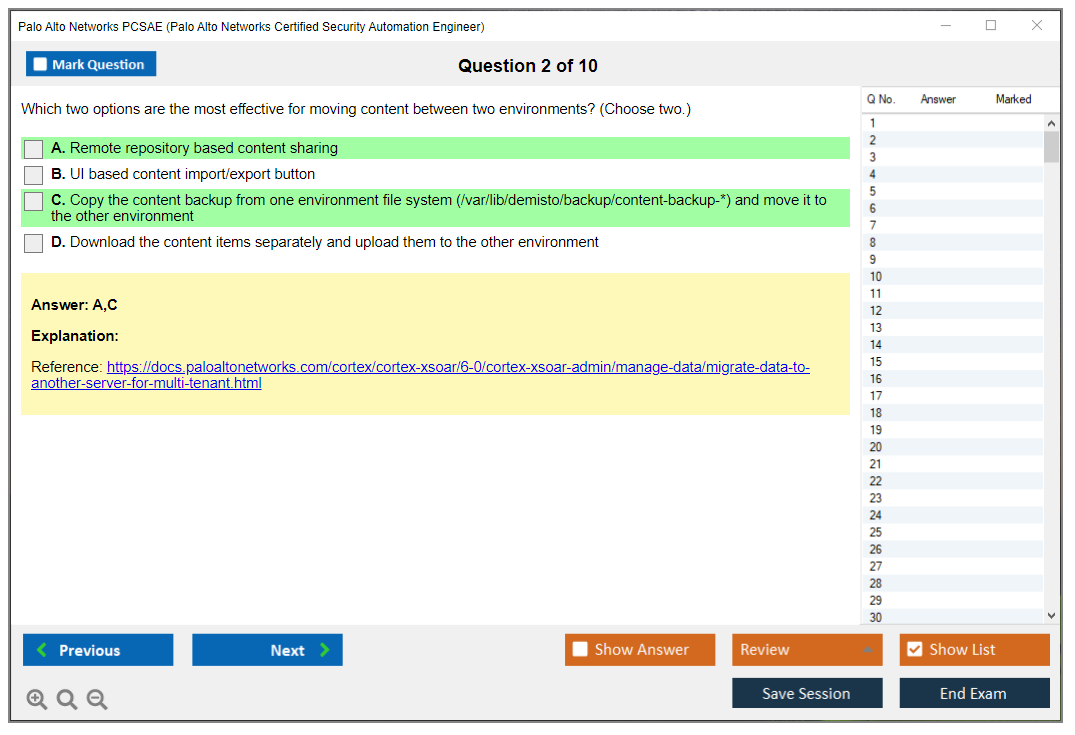
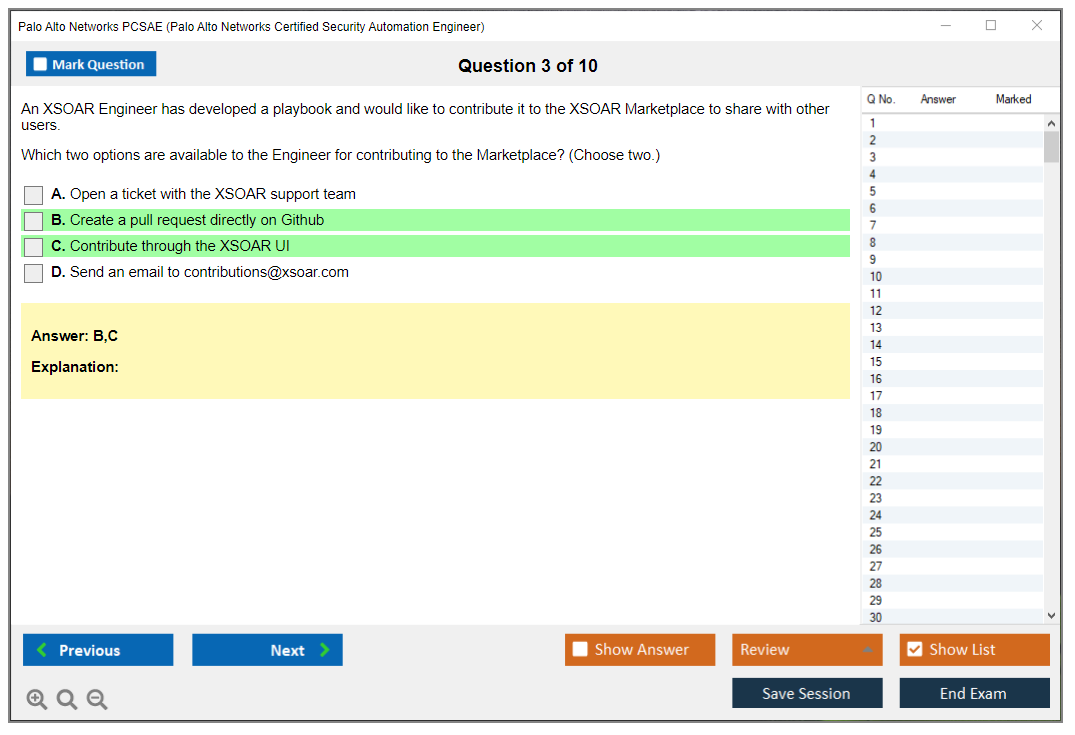
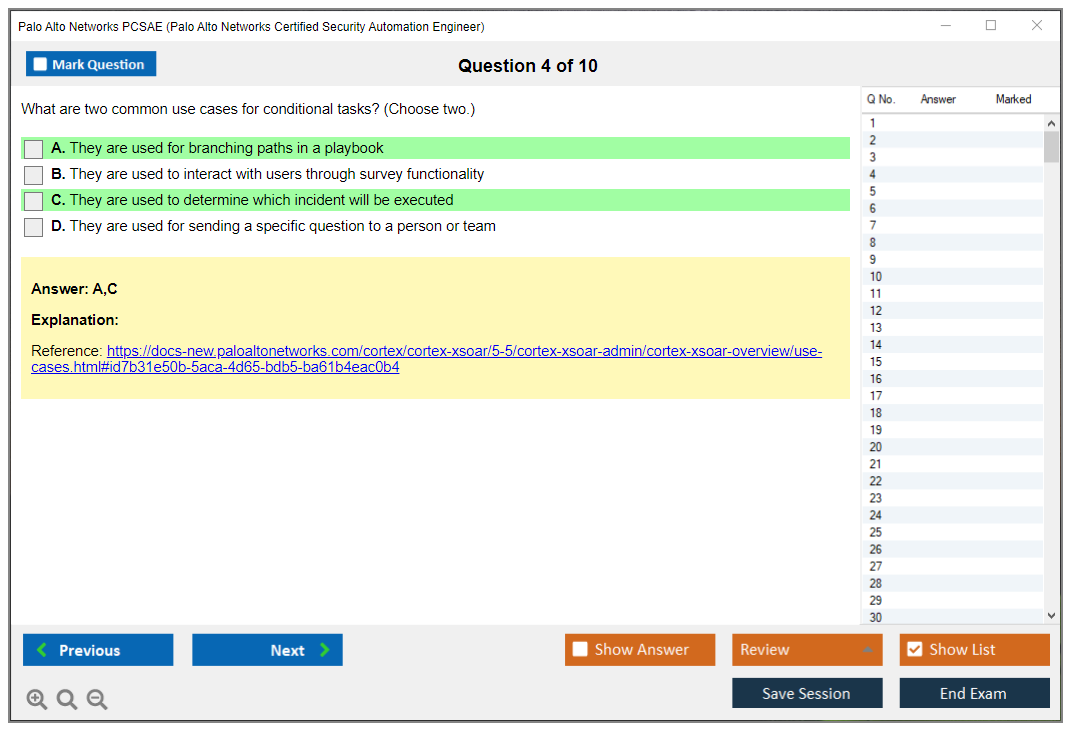
The Palo Alto Networks PCSAE exam consists of multiple-choice and drag-and-drop questions.
How Can You Take Palo Alto Networks PCSAE Exam?
The Palo Alto Networks PCSAE exam can be taken online or in a testing center. For online exams, you will need to register for an exam through the Palo Alto Networks website and then follow the instructions to complete the exam. For in-person exams, you will need to contact a local testing center to schedule an appointment.
What Language Palo Alto Networks PCSAE Exam is Offered?
The Palo Alto Networks PCSAE exam is offered in English.
What is the Cost of Palo Alto Networks PCSAE Exam?
The cost of the Palo Alto Networks PCSAE Exam is $150 USD.
What is the Target Audience of Palo Alto Networks PCSAE Exam?
The target audience for the Palo Alto Networks PCSAE Exam is IT professionals who are looking to gain certification in Palo Alto Networks' Platform Certified Security Automation Engineer (PCSAE) program. This certification is designed for IT professionals who have a deep understanding of the Palo Alto Networks platform, as well as a strong understanding of automation and scripting. The PCSAE certification is ideal for IT professionals who want to become experts in automating and scripting the Palo Alto Networks platform.
What is the Average Salary of Palo Alto Networks PCSAE Certified in the Market?
The average salary for a Palo Alto Networks Certified Security Automation Engineer (PCSAE) is approximately $90,000 per year. However, salaries can vary widely depending on experience, location, and other factors.
Who are the Testing Providers of Palo Alto Networks PCSAE Exam?
The Palo Alto Networks Certified Security Automation Engineer (PCSAE) exam is administered by Pearson VUE. You can register for the exam and find testing centers at their website.
What is the Recommended Experience for Palo Alto Networks PCSAE Exam?
The recommended experience for the Palo Alto Networks PCSAE exam is two or more years of experience in network security, including experience with Palo Alto Networks technologies. Experience in deploying, configuring, and managing Palo Alto Networks solutions is also recommended.
What are the Prerequisites of Palo Alto Networks PCSAE Exam?
The Prerequisite for Palo Alto Networks PCSAE Exam is to have a valid Palo Alto Networks Certified Network Security Administrator (PCNSA) certification.
What is the Expected Retirement Date of Palo Alto Networks PCSAE Exam?
The official website for Palo Alto Networks PCSAE exam is https://www.paloaltonetworks.com/services/education/certification/certification-exams/palo-alto-networks-certified-security-automation-engineer.html. On this page, you can find information about the exam, such as the expected retirement date.
What is the Difficulty Level of Palo Alto Networks PCSAE Exam?
The difficulty level of the Palo Alto Networks PCSAE exam is considered to be moderate.
What is the Roadmap / Track of Palo Alto Networks PCSAE Exam?
The certification roadmap for the Palo Alto Networks PCSAE Exam includes the following steps:
1. Complete the Palo Alto Networks Certified Security Automation Engineer (PCSAE) training course.
2. Pass the PCSAE exam.
3. Obtain the PCSAE certification.
4. Maintain the PCSAE certification by completing the annual continuing education requirements.
What are the Topics Palo Alto Networks PCSAE Exam Covers?
The Palo Alto Networks PCSAE exam covers topics related to the installation, configuration, and management of Palo Alto Networks security solutions. The following are the topics covered in the exam:
1. Network Fundamentals: This section covers topics such as network architecture, routing and switching, and IP addressing.
2. Security Fundamentals: This section covers topics such as security threats and vulnerability management, security policy enforcement, and security operations.
3. Firewall Management: This section covers topics such as configuring and managing Palo Alto Networks firewalls, managing security policies, and troubleshooting.
4. Advanced Security: This section covers topics such as application identification and control, user identification and control, and content security.
5. Network Security: This section covers topics such as network segmentation and secure access control.
6. Threat Prevention: This section covers topics such as malware prevention, URL filtering, and data loss prevention.
What are the Sample Questions of Palo Alto Networks PCSAE Exam?
1. What is the best method for configuring a Palo Alto Networks firewall?
2. What are the key features of the Palo Alto Networks Panorama management platform?
3. How does the Palo Alto Networks App-ID feature work?
4. What are the benefits of using the GlobalProtect feature of Palo Alto Networks?
5. What is the process for creating a security policy in the Palo Alto Networks firewall?
6. What are the different types of threats that can be mitigated by Palo Alto Networks?
7. How can the WildFire feature of Palo Alto Networks be used to detect and prevent malicious activity?
8. What are the different types of logging available on Palo Alto Networks firewalls?
9. What is the best way to troubleshoot an issue with a Palo Alto Networks firewall?
10. What are the different components of the Palo Alto Networks architecture?
What is the Palo Alto Networks PCSAE Certification? Why automation engineering is becoming non-negotiable in security operations The Palo Alto Networks PCSAE certification validates your expertise in security automation engineering using Palo Alto Networks technologies, with a laser focus on the Cortex XSOAR platform. Not just resume filler. It's designed for security professionals who architect, deploy, and maintain automated security orchestration, automation, and response (SOAR) solutions in enterprise environments where every second counts during an incident. If you're still manually copying indicators from one tool to another or spending 45 minutes enriching a single phishing email, you already know why this certification exists. It's basically become survival skills at this point. The PCSAE confirms you can build playbooks, integrate security tools that were never meant to talk to each other, automate incident response workflows, and actually optimize security operations center... Read More
What is the Palo Alto Networks PCSAE Certification?
Why automation engineering is becoming non-negotiable in security operations
The Palo Alto Networks PCSAE certification validates your expertise in security automation engineering using Palo Alto Networks technologies, with a laser focus on the Cortex XSOAR platform. Not just resume filler. It's designed for security professionals who architect, deploy, and maintain automated security orchestration, automation, and response (SOAR) solutions in enterprise environments where every second counts during an incident.
If you're still manually copying indicators from one tool to another or spending 45 minutes enriching a single phishing email, you already know why this certification exists. It's basically become survival skills at this point. The PCSAE confirms you can build playbooks, integrate security tools that were never meant to talk to each other, automate incident response workflows, and actually optimize security operations center (SOC) efficiency instead of just talking about it in meetings.
What makes this credential different? The Palo Alto security automation engineer designation demonstrates proficiency in reducing those manual security tasks that eat up 70% of your SOC's time, accelerating threat response from hours to minutes, and implementing scalable automation frameworks that don't break when your environment grows. It's recognized industry-wide as validation of hands-on skills in Cortex XSOAR automation certification and advanced security orchestration capabilities.
This certification marks you as someone qualified to design complex automation architectures, troubleshoot integration issues when vendors blame each other, and implement best practices for SOAR playbooks and integrations that actually work in production. Not gonna lie, it fits with growing industry demand for automation-skilled security professionals who can maximize ROI from the pile of security technology investments your organization made last year.
Who actually benefits from earning PCSAE
Security automation engineers responsible for building and maintaining security orchestration automation and response (SOAR) platforms in production environments are the primary audience. These folks live in Cortex XSOAR daily. Building playbooks at 2 AM when incidents hit.
Worth the investment?
SOC analysts and incident responders seeking to advance their careers by specializing in automation and orchestration technologies should seriously consider this path. You can stay in tier-1 alert triage forever, or you can become the person who automates away 80% of those alerts. Honestly, the choice seems pretty obvious when you frame it that way. Security architects designing automated response frameworks and integrating multiple security tools into cohesive workflows need this validation when pitching automation projects to leadership.
DevSecOps engineers implementing security automation within CI/CD pipelines and cloud-native environments find this cert bridges the gap between traditional security and modern development practices. Security consultants who implement Cortex XSOAR for clients absolutely need validated expertise to demonstrate capabilities. Clients want proof you know what you're doing before you touch their production environment.
IT professionals transitioning from general automation roles (Ansible, Python scripting) into specialized security automation positions can use PCSAE as their entry ticket. Security operations managers responsible for optimizing team efficiency through automation technology adoption benefit from understanding what's actually possible versus vendor marketing promises.
Threat intelligence analysts automating enrichment, correlation, and dissemination of threat data across security infrastructure will find this certification validates their technical approach. Compliance and governance professionals automating audit workflows, evidence collection, and remediation tracking can benefit too, though that's admittedly a smaller use case.
This works best for professionals with 2-5 years security operations experience looking to differentiate themselves in competitive job markets. Also good for individuals already working with Palo Alto Networks products seeking to expand expertise into the automation domain. Career changers with strong programming backgrounds entering cybersecurity through the automation specialization pathway fit here too.
Random tangent, but I've noticed people with infrastructure-as-code backgrounds (Terraform, CloudFormation) tend to pick up SOAR concepts faster than traditional security folks. Something about thinking in workflows and state management just translates well.
The technical skills PCSAE actually tests
You need proficiency in designing, building, testing, and deploying automated playbooks for common security use cases including phishing response, malware analysis, and vulnerability management. Not just toy examples. Production-ready automation that handles edge cases and doesn't wake you up at 3 AM because it failed.
Real-world application matters.
Expertise in integrating diverse security tools through APIs, webhooks, and custom connectors to create unified automation workflows is critical. You'll configure and optimize SOAR playbooks and integrations that orchestrate actions across SIEM, EDR, firewall, threat intelligence, and ticketing platforms that all use different authentication mechanisms and data formats. The thing is, none of these vendors ever designed their products to actually play nicely together.
The certification validates understanding of incident classification, triage automation, enrichment processes, and automated containment strategies that actually work when threats are actively moving through your network. Knowledge of Python scripting for custom automation development, API interaction, and extending platform capabilities beyond out-of-box functionality is tested extensively.
Skills in troubleshooting integration failures, debugging playbook logic errors, and optimizing automation performance separate passing candidates from those who just memorized documentation. Competency in content lifecycle management including version control, testing methodologies, migration strategies, and governance frameworks matters more than most people expect.
You need understanding of security operations workflows and how automation fits into broader incident response, threat hunting, and vulnerability management programs. The ability to design scalable automation architectures that accommodate organizational growth, tool additions, and evolving threat landscapes gets tested through scenario-based questions.
Knowledge of authentication mechanisms, API security, role-based access control, and secure automation design principles ensures you're not creating security holes while trying to improve security. Expertise in metrics collection, reporting automation effectiveness, and demonstrating ROI from automation investments helps justify continued investment. Understanding of collaboration features, case management automation, and workflow orchestration across distributed security teams rounds out the competency model.
Breaking down the PCSAE exam format and logistics
The exam costs $250, which is actually pretty reasonable compared to some vendor certifications that charge $400+ for similar technical depth. The passing score sits at 70%, meaning you need to get 70% of questions correct to earn the certification. Sounds generous until you realize the questions test practical implementation knowledge, not just conceptual understanding.
Intermediate to advanced difficulty.
The difficulty level is intermediate to advanced. If you're coming from a PCCET or PCCSA background, expect a big step up in technical depth. This isn't memorizing security concepts. It's demonstrating you can actually build and troubleshoot automation in production environments where real money's on the line. Most candidates with solid Cortex XSOAR experience report the exam is fair but requires thorough preparation.
The exam format includes multiple choice and scenario-based questions that test your ability to apply knowledge to real-world situations. You'll see questions about troubleshooting failed integrations, optimizing playbook performance, and selecting appropriate automation approaches for specific use cases. Time management matters because some scenario questions require careful analysis.
What the PCSAE exam objectives cover in detail
The core automation concepts domain covers SOAR fundamentals, playbook design principles, workflow orchestration, and automation theory. You'll need to understand when automation makes sense versus when human judgment is required, how to design playbooks that handle exceptions gracefully, and how to structure automation architectures that scale.
Integrations get technical fast.
Integrations and APIs testing gets deep into technical implementation. Expect questions about REST API interaction, authentication methods (API keys, OAuth, tokens), webhook configuration, custom connector development, and troubleshooting integration failures. This section separates people who've actually done the work from those who just read about it. You'll need to understand how different tools expose their functionality through APIs and how to chain actions across multiple platforms.
The incident response use cases domain tests your ability to apply automation to real security scenarios. This includes automated triage of alerts from SIEM platforms, enrichment of indicators using threat intelligence feeds, containment actions like isolating endpoints or blocking IPs at firewalls, and remediation workflows that actually fix the underlying issue. You need to know which actions should be fully automated versus requiring human approval.
Content management and best practices questions focus on the operational aspects of running automation in production. Version control for playbooks, testing strategies before deploying to production, migration approaches when upgrading platforms, governance frameworks for who can create and modify automation, and incident post-mortems when automation fails are all covered.
Prerequisites and recommended background for success
There are no strict prerequisites for taking the PCSAE exam, but that doesn't mean you should jump in without preparation. Recommended background includes 6-12 months of hands-on experience with Cortex XSOAR or similar SOAR platforms. Also helpful: familiarity with security operations workflows and incident response processes, basic Python scripting skills for custom automation development.
Build your foundation first.
If you're working toward PCSAE as part of your Palo Alto Networks certification path, consider completing PCNSA first to understand Palo Alto's overall security approach. The PCDRA certification complements PCSAE nicely if you're focused on the Cortex product family. Some candidates pursue PCNSE before PCSAE to build broader security engineering skills, though that's not required. Depends on where your career's headed.
Understanding of REST APIs, JSON data formats, and basic programming logic will make your preparation much easier. Previous experience with security tools like SIEM, EDR, firewalls, and threat intelligence platforms helps because you'll need to understand what these tools do before you can automate them effectively.
Study materials that actually prepare you for the exam
Official Palo Alto Networks training includes instructor-led courses designed for PCSAE preparation. The "Cortex XSOAR: Automation and Orchestration" course covers playbook development, integration configuration, and automation best practices. These courses aren't cheap (typically $3000-4000), but they include hands-on labs that are incredibly valuable.
Documentation becomes essential reading.
The Cortex XSOAR product documentation should become your best friend during preparation. The Administrator Guide, Playbook Developer Guide, and Integration Reference documentation contain the technical details you'll need, the kind of stuff that actually shows up on exam questions. The API reference documentation is particularly important for understanding how to interact with the platform programmatically.
Hands-on practice is non-negotiable for this certification. You need to build actual playbooks, configure real integrations, and troubleshoot actual failures. Palo Alto offers trial versions of Cortex XSOAR that you can use for lab practice. Focus on building automation for common use cases like phishing response, malware analysis, and vulnerability management.
The Cortex XSOAR community forums and GitHub repositories contain example playbooks and integrations you can study and modify. Looking at how experienced automation engineers solve problems teaches you patterns and approaches that documentation doesn't cover.
How to use practice tests effectively in your preparation
PCSAE practice tests help you identify knowledge gaps before you spend $250 on the real exam. Use practice tests diagnostically. Take one early in your preparation to see which domains need the most work, then focus your study efforts accordingly.
Don't just memorize answers.
Sample questions typically cover playbook logic troubleshooting, integration configuration scenarios, automation architecture design, and best practices for production deployments. Don't just memorize answers from practice tests. Understand why each answer is correct and what concepts the question is testing, because the real exam will phrase things differently anyway.
A realistic study plan depends on your current experience level. If you're already working with Cortex XSOAR daily, 2-4 weeks of focused preparation covering weak areas might be sufficient. For someone new to SOAR but with strong security and automation backgrounds, plan for 6-8 weeks of study including significant hands-on practice. Complete beginners should budget 10-12 weeks to learn both the platform and automation concepts from scratch.
Understanding PCSAE renewal requirements
The PCSAE certification is valid for two years from the date you pass the exam. To maintain your certification, you'll need to recertify before it expires by either retaking the current exam or completing continuing education requirements if Palo Alto offers that option in the future.
Stay current or recertify.
Most certified professionals choose to recertify by retaking the exam because it ensures their knowledge stays current with platform updates. Cortex XSOAR evolves rapidly, adding new integrations, automation capabilities, and features that change how you approach security automation. The thing is, what worked two years ago might not even be best practice anymore. The recertification process validates you've kept pace with these changes.
Where PCSAE fits in your certification strategy
The Palo Alto Networks certification path offers multiple directions depending on your career focus. PCSAE is part of the Cortex product family certifications, alongside PSE-Cortex for systems engineers. If you're building a security automation specialty, PCSAE is your primary target.
Multiple paths available here.
For SOC professionals, combining PCSAE with PCDRA creates a powerful credential set covering both detection/response and automation. Network security engineers might pursue PCNSE or PCNSC alongside PCSAE to demonstrate breadth across Palo Alto's product portfolio.
Cloud-focused professionals should consider PCCSE or PSE-PrismaCloud to complement PCSAE automation skills with cloud security expertise. The combination of automation and cloud security skills is particularly valuable as organizations migrate security operations to cloud-native architectures.
Quick answers to common PCSAE questions
How much does the Palo Alto Networks PCSAE exam cost? The exam costs $250, which is standard for Palo Alto Networks professional-level certifications. This is the only fee. No hidden costs for study materials or mandatory training, though official courses cost extra if you choose them.
What is the passing score for the PCSAE exam? You need to achieve 70% correct answers to pass. The exam doesn't use scaled scoring. Your percentage is straightforward. You'll receive your score immediately after completing the exam.
Realistic difficulty assessment here.
How hard is the PCSAE certification? It's intermediate to advanced difficulty, requiring both conceptual understanding and practical implementation experience. Anyone telling you it's easy is either lying or has been living in Cortex XSOAR for years. Candidates with 6-12 months of hands-on Cortex XSOAR experience generally find it challenging but passable with proper preparation. Complete beginners struggle without significant study and lab practice.
What are the PCSAE exam objectives and domains? The exam covers automation concepts and SOAR fundamentals, integrations and API implementation, incident response use cases and automation workflows, content management and best practices, troubleshooting and optimization techniques. Each domain receives roughly equal weight in the exam.
How do I prepare for PCSAE (study materials and practice tests)? Start with official Palo Alto Networks training courses if budget allows. Study the Cortex XSOAR product documentation thoroughly. Build hands-on lab experience with actual playbook and integration development. Use practice tests to identify weak areas. Join the Cortex XSOAR community to learn from experienced practitioners. Plan 4-12 weeks of preparation depending on your current experience level.
PCSAE Exam Overview
What this cert is, really
The Palo Alto Networks PCSAE certification proves to hiring managers you can automate security ops without torching the entire SOC. It tests both theory and hands-on chops for Palo Alto security automation engineers, especially in Cortex XSOAR.
Not a beginner thing. Not some "I watched videos" badge. More like "I can debug a broken playbook."
If you've done security orchestration automation and response (SOAR) in production environments, honestly, a lot of the exam content feels familiar, almost natural because you've lived through similar chaos. If you haven't, the scenario questions can feel like you're deciphering someone else's terrible runbook at 2 a.m., which, I mean, is basically what they're testing: the messy, real-world troubleshooting that happens when automations go sideways and nobody's around to help.
Who should take it
This is for SOC folks already exhausted from clicking identical enrichment steps constantly, and for automation engineers wanting a vendor-backed credential mapping to actual job tasks. It also fits incident responders who keep hearing "can we just automate that?" and now gotta answer with something better than "maybe."
If you're earlier in the Palo Alto Networks certification path, look, don't force it. Start with something like PCCET or PCCSA to nail the basics, then circle back when XSOAR concepts stop sounding like gibberish.
What skills it validates
PCSAE tests whether you can reason about SOAR playbooks and integrations, work with APIs, handle data mapping, and troubleshoot automation workflows. Not just "can you click around XSOAR" but "can you design and debug workflows under constraints," like credentials, rate limits, inconsistent JSON, flaky integrations, and those delightful edge cases where an incident field is empty and your entire branch logic just collapses.
You'll see Cortex XSOAR automation certification themes everywhere. Content packs. Tasks. Commands. Context. Incident types. Layouts. All the stuff you're touching when building something a SOC will really use.
What to expect when you sit the exam
PCSAE gets administered through Pearson VUE testing centers globally, and it's also available as an online proctored exam if you'd rather do it from home. Both work fine. Testing center's less stressful because you're not worried about your webcam freezing mid-question, but online's convenient if your nearest center's a long drive and you'd prefer suffering in your own chair.
The exam's 75 questions in 90 minutes. That works out to roughly 72 seconds per question, which sounds tight until you realize a bunch are quick wins, and then a few scenario-based monsters devour your time if you're not careful. Time allocation's generally fair. It gives you enough breathing room to read carefully, analyze exhibits, and pick the best answer without that "rush rush rush" panic you get on some vendor exams.
No breaks during the 90-minute window. Restroom breaks happen. Timer keeps ticking.
Question styles and the interface
You're dealing with multiple-choice, multiple-select, and scenario-based questions. The scenario ones are the whole point. They'll give you a playbook excerpt, an integration configuration, a workflow diagram, an API response sample, maybe a screenshot of a task setup, and then ask what happens next, what's broken, or what you should change.
Random question order. Random answer ordering. So memorization-based cheating's harder.
The exam UI's standard Pearson VUE stuff: you can work through freely, mark questions for review, see time remaining, and there's a basic calculator inside the interface. In a testing center you get scratch paper and a pen or pencil. Online proctoring usually allows a single blank sheet and pen, but check the rules for your region because proctors can get picky.
No notes. No docs. No "quick Google."
Rules you can't ignore
Before you start, you're signing a non-disclosure agreement. That NDA's serious. You can't share specific question content or exam materials, even if you think you're being "helpful" in a forum post.
Identification's mandatory. You need a government-issued photo ID matching your registration name. Testing center rules are strict: no phone, no smartwatch, no bags, no study sheets, no electronics. Online proctored exams require a webcam, microphone, stable internet, and a private room with a closed door, plus a room scan so they can confirm you're not surrounded by sticky notes and extra monitors.
Scoring and results timing
Results show immediately after you submit. You'll see pass or fail on the screen for computer-based testing. Then the official score report arrives within 24 to 48 hours, typically via email, and it includes a domain-level breakdown like "above target," "near target," or "below target."
Answer every question. There's zero penalty for incorrect answers, and unanswered questions are automatically wrong, so even if you're guessing, guess. Multiple-select questions have no partial credit, which is brutal. If you select one extra wrong option, the whole thing's counted wrong.
PCSAE exam cost and payment details
The PCSAE exam cost is $200 USD as of 2025-2026, with regional pricing differences and currency exchange doing their usual chaos. Taxes may apply depending on where you live. Pearson VUE processes payment and registration through their website, and you can pay with credit card, debit card, or voucher codes from authorized training partners.
One attempt per fee. Retakes require paying again. No refunds for no-shows, late cancellations under 24 hours, or failing. Rescheduling's allowed up to 24 hours prior without penalty, but late reschedules usually forfeit the fee.
Organizations can get volume discounts and voucher bundles, and sometimes training bundles include an exam voucher for less than buying separately. Also, some employers reimburse exam fees, so look, ask your manager before you pay out of pocket. It's awkward for five minutes, and then it might save you $200.
Passing score and what "70%" really means
The PCSAE passing score is 70% or higher. With 75 questions, that's at least 53 correct, but don't treat it like simple math because the scoring's scaled. Scaled scoring means your raw score gets converted to a standardized scale accounting for question difficulty variation, and not all questions are necessarily weighted the same. Harder questions or areas testing deeper knowledge can carry more impact.
Score reports don't tell you which questions you missed. They also don't show exact raw scoring details. If you fail, you get diagnostic feedback by domain so you know what to fix for the retake. If you pass, you get the digital certificate and badge in about 5 to 7 business days, and your certification status can be checked through Palo Alto Networks' credential verification portal.
No appeals process for "I got a 69%." Retake the full exam. That's it.
How hard it feels in practice
PCSAE difficulty is intermediate to advanced. If you've got 6 to 12 months of Cortex XSOAR work plus 2+ years of security operations experience, you're in the sweet spot. If you're missing the hands-on part, the exam gets annoying fast because it expects you to interpret how XSOAR behaves, not just regurgitate definitions.
Python matters. A lot. You don't need to be a software engineer, but you do need to understand basic scripting concepts, API interaction patterns, how to read code snippets, and what breaks when data types don't match. Questions also hit integration troubleshooting, which is basically: auth failures, connectivity, proxy weirdness, SSL issues, bad tokens, wrong instance parameters, and data formatting problems like JSON paths that don't match what the playbook expects.
Playbook design shows up too: sequencing tasks, conditional branching, transformers, filters, error handling, and what to do when an integration returns empty results. People who only study theory tend to struggle because the exam loves real-world automation scenarios where you're applying knowledge, not just recalling facts.
Common failure points I keep hearing: authentication methods, integration configuration details, advanced playbook techniques, and time management when a scenario includes multiple exhibits. First-time test takers also underestimate how "platform specific" it is beyond basic playbook building. Oh, and speaking of things people don't expect, I once spent three hours in a Pearson VUE center where the AC was broken in July and the proctor kept offering me water like that would somehow help me remember JSON syntax. It didn't. But I passed anyway, probably out of spite. The thing is, the exam's designed to catch people who only know surface-level concepts.
Where the exam objectives come from
The PCSAE exam objectives are aligned with job tasks performed by working security automation engineers in production environments. And yes, you should read the exam blueprint. Palo Alto Networks publishes it, and it details domain weightings and specific objectives tested, which is your best hint about what to spend time on and what not to obsess over.
Questions test breadth across automation domains and depth in the areas that matter for enterprise SOAR. You can't just be good at playbooks and ignore integrations, or be great at APIs and ignore content management. The exam'll find that gap.
Core automation concepts you'll see
Expect SOAR fundamentals like incident lifecycle thinking, how Cortex XSOAR handles context, and how playbook tasks pass data around. You'll also see workflow logic problems where the "right" answer's the one that handles messy reality.
One area worth over-prepping is conditional logic and error paths. Honestly, most broken automations in production aren't broken because someone didn't know what a playbook is, they're broken because nobody planned for null values, partial enrichment, rate limits, or an integration returning a different schema after a vendor update.
Other topics show up too: automations vs scripts, when to use sub-playbooks, how to keep playbooks maintainable. Those tend to be more straightforward.
Integrations and APIs
Integrations and APIs are a big slice. SOAR playbooks and integrations are where real value happens, and also where the pain lives. You'll need comfort with authentication approaches, instance configuration, command execution, error interpretation, and data mapping into incident fields and context keys.
Know what an API response looks like. Know JSON basics. Know where XSOAR stores outputs.
You may get exhibits like API responses, integration configuration examples, or error messages, and then you've gotta decide the fix. That's not trivia. That's "can you troubleshoot like a grown-up."
Incident response use cases
The exam likes practical incident response flows: triage, enrichment, correlation, containment, notifications, and ticketing. Think about how you'd automate phishing triage, endpoint isolation, blocking indicators, or escalating to a human when confidence is low.
You don't need to memorize every vendor command. You do need to understand patterns, like enrichment first, decision second, action third, and rollback or human approval where it makes sense.
Content management and best practices
This part's less flashy but it's what keeps teams sane: versioning, testing changes, governance, content packs, deployment practices. Also permissions. Who can edit what. How to avoid "random intern edited the prod playbook."
It's not the hardest domain. It's easy to neglect. Don't.
Prerequisites and recommended experience
Officially, PCSAE prerequisites aren't usually framed as hard requirements like "you must hold X cert," but practically, you want experience. Real experience. Palo Alto Networks designed this as a job-role exam, so it assumes you've been in the tool.
Recommended background includes security operations knowledge, basic scripting, comfort with APIs, and at least some Cortex XSOAR time. Helpful adjacent certs depend on your path. If you're coming from firewall or network security, you might've done PCNSA or PCNSE. If you're more SOC-focused, PCDRA pairs nicely because detection and response thinking transfers well.
Study materials that actually help
PCSAE study materials should be a mix of official training and real docs. Official Palo Alto Networks training's great if you can get your employer to pay, and the product documentation matters a ton: admin guides, integration docs, API references.
Read what you touch. Skip what you don't. Be strategic.
Hands-on labs are the difference-maker. Build a playbook from scratch, then intentionally break it. Change an integration parameter and see how errors show up. Map a JSON response into context, then write conditions based on that context. Add retries. Add timeouts. Add a manual approval task. You learn faster when you watch something fail and then fix it.
Practice tests and pacing strategy
A good PCSAE practice test helps you learn timing and identify weak domains. Use it like a diagnostic tool, not like a memorization engine, because the real exam randomizes question and answer ordering anyway, and scenario questions require interpretation.
If you want something focused for drilling, the PCSAE Practice Exam Questions Pack is $36.99 and can be useful for building speed, especially if you keep missing the same themes like integrations, auth, and playbook branching. I'd treat it as a checkup after you've done labs, not as your only prep, because look, you can't fake "platform feel" with pure Q&A.
Stuff to drill hard: interpreting playbook snippets, troubleshooting integration setup, reading API samples, understanding how XSOAR context keys drive decisions. Other topics like content management and governance, incident types, permissions show up too, but they're usually less time-consuming once you've seen them once.
Study plan ideas that don't assume you've got infinite time. One to two weeks only makes sense if you already work in XSOAR daily, and you're mainly tightening weak spots with docs and a PCSAE Practice Exam Questions Pack. Four to six weeks is best for most people: mix labs plus blueprint-based reading, then practice tests for pacing. Eight plus weeks if you're new to SOAR or shaky on Python and APIs, take it slow and build small automations weekly.
Renewal basics
PCSAE renewal policies can change, so verify the current timeline in the official certification portal. Typically, Palo Alto Networks certifications require periodic renewal, and you maintain status either by retaking the exam or meeting whatever current recertification rules apply at the time.
Don't assume it's forever. Track your expiration. Plan ahead.
How it fits with other Palo Alto certs
PCSAE's specialized. It sits closer to Cortex and SOAR roles than firewall admin tracks. If you're mapping a Palo Alto Networks certification path, think of it as "automation engineer lane," while PCNSE and PCNSA sit more in the network security lane, and PSE-Cortex is more pre-sales systems engineer territory.
If your job's SOC automation, PCSAE's the clean signal.
FAQs people keep asking
Cost, passing score, difficulty
How much does the Palo Alto Networks PCSAE exam cost? $200 USD (2025-2026), with regional pricing and taxes possible.
What's the passing score for the PCSAE exam? PCSAE passing score is 70% or higher, and scoring's scaled.
How hard's the PCSAE certification? PCSAE difficulty is intermediate to advanced, mainly because scenario questions require real Cortex XSOAR familiarity plus Python and API comfort.
Objectives, prerequisites, renewal
What're the PCSAE exam objectives and domains? The PCSAE exam objectives are listed in the public blueprint, with domain weightings and task-focused skills like playbooks, integrations, incident response workflows, content management.
Are there PCSAE prerequisites? No strict "must-have" credential in most cases, but hands-on XSOAR experience is the practical requirement.
How's PCSAE renewal work? Check the current Palo Alto Networks policy, since renewal timelines and methods can change.
Study materials and practice tests
How do I prepare for PCSAE (study materials and practice tests)? Mix official training, XSOAR documentation, hands-on labs, timed practice. If you want extra repetition for pacing, the PCSAE Practice Exam Questions Pack is a decent add-on for $36.99, especially after you've already built and troubleshot a few playbooks yourself.
PCSAE Exam Objectives (Domains)
How exam domains structure your preparation roadmap
The PCSAE exam objectives split into four primary domains. They cover the complete security automation engineering lifecycle, though I spent weeks confused about what that phrase actually meant. Turns out it's just Palo Alto's way of saying they test everything from conceptual understanding through hands-on implementation and ongoing management. Seems unnecessarily complicated at first.
Domain weighting? Critical.
It determines how many questions you'll see from each area. Understanding this weighting completely changed how I approached my study plan because I was initially spending equal time on everything like some optimistic fool who thought fairness mattered.
The objectives reflect real-world job tasks performed by security automation engineers in enterprise SOC environments, which makes this certification way more valuable than some of the purely theoretical stuff I've seen. Each domain contains multiple sub-objectives detailing specific knowledge areas and skills tested within broader categories.
Here's what matters: the exam blueprint gets updated periodically to reflect platform updates, emerging automation techniques, and evolving industry practices. You can't just rely on old study guides and hope for the best. I've seen folks fail because they studied outdated material that didn't account for Cortex XSOAR feature changes from six months prior. Seems unfair but that's how certification exams work nowadays.
Questions get distributed across domains according to published weighting percentages, which ensures you face testing across multiple areas instead of getting lucky with your strongest topic. You must demonstrate proficiency across all domains because weakness in a single area can prevent passing even with strong performance elsewhere. You can't just master playbooks and ignore integrations. They'll catch you.
Breaking down Domain 1: Security orchestration automation fundamentals
This domain covers understanding fundamental security orchestration automation and response (SOAR) principles, benefits, and use cases in modern security operations.
Foundational stuff. Critical though.
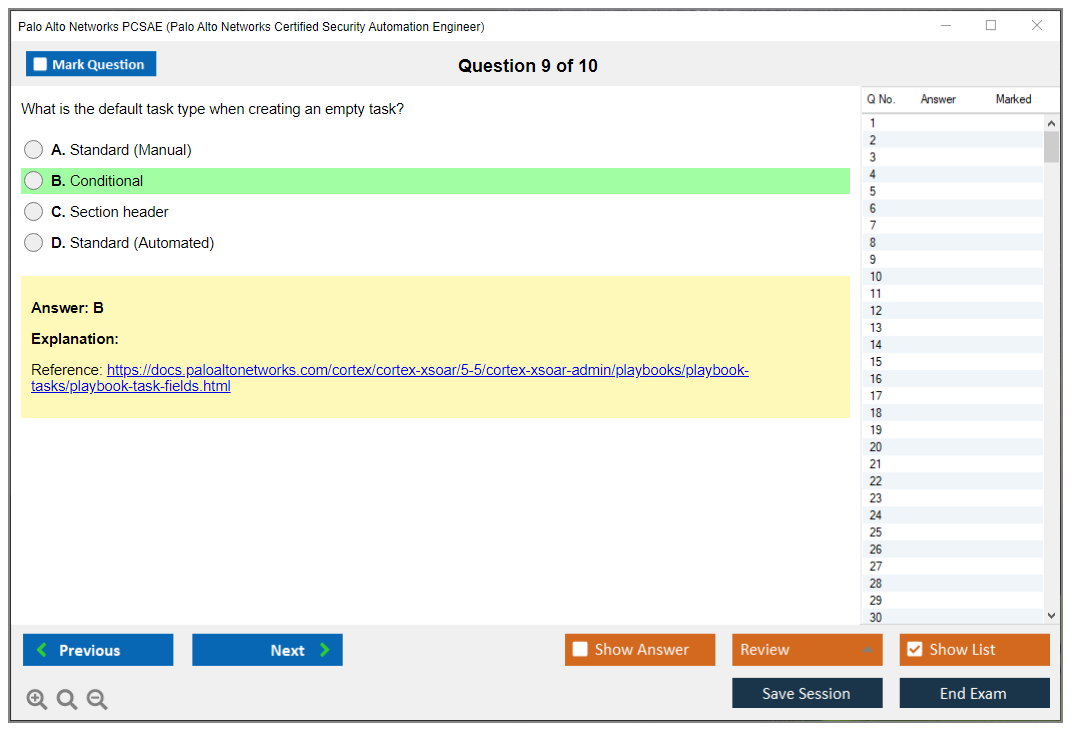
You need knowledge of playbook architecture including tasks, conditions, loops, sub-playbooks, and error handling mechanisms that can get confusing when you're first learning them. The ability to design workflows that automate incident triage, enrichment, investigation, containment, and remediation processes gets tested heavily here. I saw at least eight questions on my exam specifically about workflow design decisions. Maybe more if I'm being honest, but definitely eight because I remember counting them during the break.
Understanding automation triggers matters more than you'd think. Manual execution behaves differently than scheduled tasks, which behave differently than event-driven activation from integrations. Knowledge of data flow through playbooks is essential. Context data, inputs, outputs, and data transformation operations come up constantly in scenario questions.
Proficiency in conditional logic separates people who actually build automations from those who just read about them. Branching strategies and decision trees within automated workflows? Same deal. Understanding playbook testing methodologies, debugging techniques, and troubleshooting failed automation executions will save you on practical scenario questions where they describe broken automations and ask what's wrong.
You need knowledge of built-in automation capabilities versus custom scripting requirements for specialized use cases. This tripped me up initially because I kept trying to script everything when XSOAR had native features that would've saved me hours. The ability to identify appropriate automation opportunities and recognize scenarios where human judgment remains necessary shows up in questions about automation boundaries and limitations.
Understanding playbook performance optimization comes up less frequently. Parallel execution and resource management considerations still appear though. Knowledge of playbook documentation standards, naming conventions, and maintainability best practices matters for governance-focused questions.
The exam tests understanding of how automation integrates with broader incident response processes and security operations workflows that extend beyond just the XSOAR platform itself. Ability to design reusable playbook components, sub-playbooks, and modular automation building blocks appears in architecture questions. Knowledge of playbook versioning, change management, and controlled deployment to production environments connects to the content management domain but gets introduced here, which seems like odd placement.
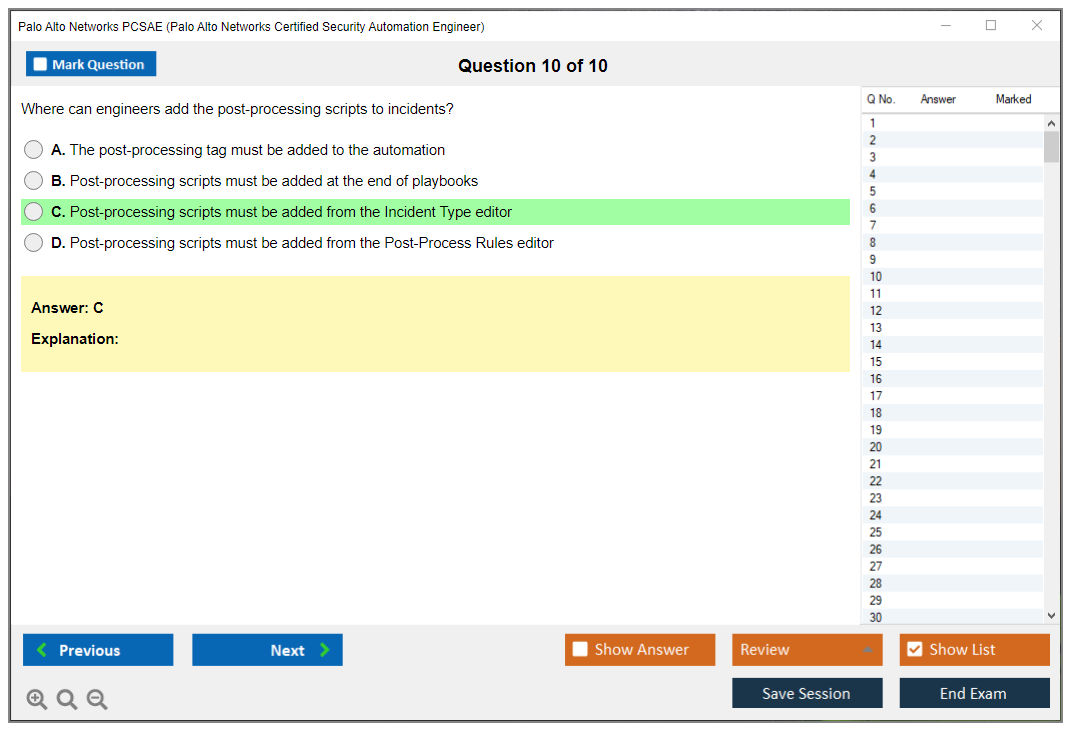
Understanding collaboration features that let multiple analysts work within automated investigation workflows shows practical SOC experience rather than just lab practice. Knowledge of case management automation, evidence collection, and audit trail generation for compliance requirements rounds out this domain.
Domain 2: Integration configuration and API connectivity
This domain focuses heavily on proficiency in configuring integrations connecting Cortex XSOAR with SIEM, EDR, firewall, threat intelligence, and ticketing platforms.
Dozens of different integration types exist.
You need to understand them conceptually even if you haven't configured every single one, which honestly feels impossible but that's the expectation. There's a running joke in the XSOAR community that knowing every integration is like memorizing the phone book, but somehow they still expect it.
Understanding API fundamentals is mandatory. REST versus SOAP, HTTP methods like GET, POST, PUT, DELETE, and status codes all appear regularly. Knowledge of authentication mechanisms including API keys, OAuth 2.0, basic authentication, and token-based authentication comes up constantly because authentication failures represent the most common integration issues in production environments. Probably 60% of tickets I've seen involve auth problems.
The ability to troubleshoot integration failures related to connectivity, authentication, permissions, and API rate limiting gets tested through scenario questions where they describe error messages and ask you to identify the root cause. This can be tricky when multiple answers seem plausible. Understanding data formatting, including JSON and XML parsing, data extraction, and transformation operations matters because real integrations rarely return data in exactly the format you need.
Knowledge of custom integration development using Python for tools lacking pre-built connectors shows advanced capability that separates senior engineers from junior ones. Proficiency in configuring integration parameters like credentials storage, proxy settings, and SSL certificate validation appears in configuration-focused questions.
Understanding bi-directional integrations that allow both data retrieval and action execution on external platforms demonstrates comprehension beyond simple data ingestion. Knowledge of integration testing methodologies ensuring reliable connectivity and expected behavior separates theoretical understanding from practical implementation experience.
The ability to interpret API documentation, construct proper requests, and handle response data appropriately gets tested through questions showing actual API documentation snippets that you'll need to parse quickly. Understanding webhook configurations for real-time event ingestion from external platforms comes up for event-driven automation scenarios.
Knowledge of integration instance management shows enterprise-level thinking. Multi-tenancy considerations? Credential rotation procedures? Same category. Proficiency in mapping external platform data fields to Cortex XSOAR incident fields and custom attributes appears in data normalization questions.
Understanding API pagination matters more than you'd expect. Batch operations and strategies for retrieving large datasets efficiently demonstrate performance awareness. Knowledge of error handling for API failures, timeouts, and malformed responses within automation workflows connects integration reliability to playbook design in ways that aren't immediately obvious. The ability to optimize integration performance through caching, request throttling, and efficient query design rounds out this domain.
Domain 3: Implementing security use cases through automation
This domain tests understanding of automated phishing response workflows including email analysis, URL and attachment detonation, and user notification.
Phishing automation? Everywhere.
It represents one of the most common SOAR use cases so expect multiple questions here. Maybe five or six minimum.
Knowledge of malware investigation automation shows practical security operations experience. Hash lookups, sandbox analysis, and IOC extraction all fall here. Proficiency in vulnerability management automation including scan result ingestion, prioritization, and remediation tracking demonstrates understanding beyond incident response.
Understanding automated threat intelligence enrichment using multiple TI sources and correlation logic appears frequently because enrichment workflows form the foundation of effective triage. If you don't nail enrichment, everything downstream falls apart. Knowledge of automated containment actions like endpoint isolation, firewall rule creation, and account disabling tests your understanding of response automation capabilities and limitations.
The ability to design automated triage workflows that classify, prioritize, and route incidents based on severity and type is fundamental to SOC automation. This is the core value proposition. Understanding data enrichment strategies pulling context from multiple sources to support investigation decisions connects to the integration domain.
Knowledge of automated evidence collection from endpoints, network devices, and cloud platforms for forensic analysis shows investigative workflow comprehension. Proficiency in designing escalation workflows that engage appropriate teams based on incident characteristics demonstrates organizational awareness beyond technical implementation.
Understanding automated notification and communication workflows keeping stakeholders informed throughout the incident lifecycle matters for collaboration and compliance, though it's less exciting than the technical stuff. Knowledge of automated remediation actions, including patch deployment, configuration changes, and access revocation tests your understanding of response automation scope.
The ability to implement automated false positive reduction through correlation logic and validation checks separates effective automation from noisy automation that nobody trusts and eventually gets disabled. Understanding automated reporting workflows generating executive summaries, metrics dashboards, and compliance documentation shows end-to-end lifecycle comprehension.
Knowledge of threat hunting automation extends beyond reactive incident response. Hypothesis testing, data correlation, anomaly detection. These all fit here. Proficiency in designing automated response playbooks that balance speed with safety through approval gates and validation steps demonstrates mature automation thinking rather than just "automate everything possible" mentality.
Understanding post-incident automation, including lessons learned documentation, indicator extraction, and defensive measure implementation shows continuous improvement mindset that enterprises value even if it's not the flashiest capability.
Domain 4: Content lifecycle and governance practices
This final domain covers understanding of content lifecycle management from development through testing, staging, and production deployment.
Less exciting than building playbooks, sure.
Critical for enterprise environments though. This is where a lot of SOAR implementations fail because people focus on the flashy automation stuff and ignore governance.
Knowledge of version control practices for playbooks, integrations, scripts, and other automation content prevents the chaos I've seen in unmanaged SOAR deployments where nobody knows which version is production. Proficiency in testing methodologies like unit testing, integration testing, and end-to-end workflow validation ensures automation reliability.
Understanding development, staging, and production environment separation with controlled promotion processes shows enterprise change management awareness that smaller organizations might not have. Knowledge of content backup strategies, disaster recovery procedures, and rollback capabilities protects against automation failures becoming business disasters.
The ability to implement governance frameworks defining content standards, approval workflows, and change control procedures demonstrates organizational maturity beyond individual technical skills. Understanding documentation requirements for playbooks matters. Purpose, inputs, outputs, dependencies. All this makes automation maintainable by teams rather than individuals, which matters when your automation engineer quits and nobody knows how anything works.
Knowledge of code review practices ensuring quality, security, and adherence to organizational standards appears in governance questions. Proficiency in content migration strategies when upgrading platforms or moving between environments shows practical deployment experience.
Understanding performance monitoring demonstrates operational thinking. Metrics collection and continuous improvement processes for automation content fall here too. Knowledge of security considerations including credential management, least privilege access, and audit logging protects automation infrastructure itself from becoming an attack vector.
The exam tests ability to implement content reusability through libraries, sub-playbooks, and shared components that reduce duplication and improve consistency across automation workflows. This should be everyone's goal but surprisingly isn't.
If you're also pursuing the PCDRA certification, you'll notice overlap in incident response concepts but PCSAE goes way deeper on automation implementation. The PSE-Cortex track covers broader Cortex portfolio knowledge while PCSAE focuses specifically on XSOAR automation engineering.
Understanding these domain objectives helps structure your study plan, identify knowledge gaps, and allocate preparation time effectively. The official exam blueprint available from Palo Alto Networks Education portal provides detailed breakdown of testable topics with even more granular sub-objectives than I've covered here.
Conclusion
Wrapping up: is PCSAE worth the investment?
Okay, real talk.
The Palo Alto Networks PCSAE certification isn't for everyone, honestly. If you're just dipping your toes into cybersecurity, you're gonna have a rough time with this one. But here's the thing: if you've logged serious hours in a SOC or you're already neck-deep in security orchestration automation and response (SOAR) platforms every single day, this cert can really catapult your career into a completely different place.
The PCSAE exam cost? Not cheap. And the PCSAE difficulty level means you absolutely can't just coast through after binge-watching a handful of YouTube tutorials over the weekend. You need actual hands-on experience with Cortex XSOAR automation certification concepts. Building SOAR playbooks and integrations, understanding incident workflows inside-out, troubleshooting API connections when they inevitably break at 3am (because they always do). I mean the exam objectives cover real-world scenarios that'll absolutely wreck you if you've only read case studies instead of actually rolling up your sleeves and doing the work yourself.
What's compelling here?
PCSAE validates skills companies desperately need right now. Security teams are drowning in alerts. Literally buried. Automation engineers who can build effective playbooks, create custom integrations that actually work, and legitimately reduce mean time to respond? Those folks get recruited hard. The Palo Alto security automation engineer role's exploding, and having this cert on your resume shifts you into a different conversation during interviews.
Your study strategy matters. Like, really matters. Sure, official Palo Alto Networks certification path materials are key foundational stuff, but you've also gotta supplement with hands-on labs and realistic practice scenarios that mirror what you'll actually face. The PCSAE study materials from Palo Alto give you the framework, but building actual content in a lab environment? That's where everything suddenly clicks and makes sense.
You can't memorize your way through questions about debugging a failed integration or optimizing playbook logic under pressure. And I've seen people try. One guy I worked with thought he could just cram the week before, spent maybe six hours total on labs, and walked out of that exam looking like he'd been hit by a truck.
Not gonna sugarcoat it: the PCSAE passing score requirement means you need solid knowledge across all domains. Weak spot in one area? The exam's gonna sniff it out immediately. That's exactly why drilling with quality practice questions becomes so important before test day rolls around.
If you're serious about passing, honestly check out the PCSAE Practice Exam Questions Pack. It's one of the better resources for identifying knowledge gaps before you drop serious cash on the actual exam attempt. The questions mirror real exam scenarios around playbook design, integration troubleshooting, and incident response automation. Precisely what you'll face when it counts and the pressure's on.
Stop overthinking it.
Stop obsessing over PCSAE prerequisites and renewal policies. Start building stuff. Start practicing consistently, and actually commit to understanding security automation at a deeper level than surface knowledge. The certification follows naturally when you really put in that work.
Show less info
Hot Exams
Related Exams
Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0
Palo Alto Networks System Engineer Professional - Strata
PSE Palo Alto Networks System Engineer Professional - Prisma Cloud
Palo Alto Networks Certified Cybersecurity Entry-level Technician
PSE: Endpoint Associate training for Traps 4.0
Palo Alto Networks System Engineer Professional - Strata Data Center
Palo Alto Networks System Engineer - Cortex Professional
Prisma Certified Cloud Security Engineer
Palo Alto Networks Certified Cybersecurity Associate
Palo Alto Networks System Engineer Professional - SASE Exam
Palo Alto Networks Systems Engineer (PSE) - Strata Associate
Aviatrix Certified Engineer (ACE) program
Palo Alto Networks Certified Network Security Consultant
Palo Alto Networks Certified Network Security Administrator (PAN-OS 10.0)
Palo Alto Networks Certified Security Automation Engineer
Palo Alto Networks Next-Generation Firewall Engineer
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.