PCNSE Practice Exam - Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0
Reliable Study Materials & Testing Engine for PCNSE Exam Success!
Exam Code: PCNSE
Exam Name: Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0
Certification Provider: Palo Alto Networks
Certification Exam Name: Palo Alto Certifications and Accreditations

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
PCNSE: Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0 Study Material and Test Engine
Last Update Check: Mar 15, 2026
Latest 500 Questions & Answers
Training Course 142 Lectures (25 Hours) - Course Overview
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Printable PDF & Test Engine Bundle
Dumpsarena Palo Alto Networks Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0 (PCNSE) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
Palo Alto Networks PCNSE Exam FAQs
Introduction of Palo Alto Networks PCNSE Exam!
Palo Alto Networks PCNSE (Palo Alto Networks Certified Network Security Engineer) is a certification exam that tests an individual's knowledge and skills in designing, deploying, configuring, and managing Palo Alto Networks Next-Generation Firewalls. The exam consists of multiple-choice and scenario-based questions.
What is the Duration of Palo Alto Networks PCNSE Exam?
The duration of the Palo Alto Networks Certified Network Security Engineer (PCNSE) exam is 2 hours.
What are the Number of Questions Asked in Palo Alto Networks PCNSE Exam?
The total number of questions on the Palo Alto Networks PCNSE exam is 75.
What is the Passing Score for Palo Alto Networks PCNSE Exam?
The passing score required to pass the Palo Alto Networks PCNSE (Palo Alto Networks Certified Network Security Engineer) exam is 80%.
What is the Competency Level required for Palo Alto Networks PCNSE Exam?
The Palo Alto Networks PCNSE exam requires a high level of professional competency. Candidates must demonstrate a deep understanding of the Palo Alto Networks platform, including the configuration of its products, deployment, and troubleshooting. Candidates must also demonstrate an understanding of the underlying networking concepts and technologies associated with the products, as well as the ability to interpret and apply the relevant security best practices.
What is the Question Format of Palo Alto Networks PCNSE Exam?
The Palo Alto Networks PCNSE exam consists of multiple-choice and multiple-response questions.
How Can You Take Palo Alto Networks PCNSE Exam?
Palo Alto Networks PCNSE exams can be taken online or at a testing center. The online exam is a proctored exam that is administered remotely. The testing center exam is a proctored exam that is administered in-person at a Pearson VUE testing center.
What Language Palo Alto Networks PCNSE Exam is Offered?
The Palo Alto Networks PCNSE exam is offered in English.
What is the Cost of Palo Alto Networks PCNSE Exam?
The cost of the Palo Alto Networks PCNSE exam is $599 USD.
What is the Target Audience of Palo Alto Networks PCNSE Exam?
The target audience of the Palo Alto Networks PCNSE Exam is IT professionals who have experience in the configuration, management, and troubleshooting of Palo Alto Networks Next-Generation Firewalls and Panorama.
What is the Average Salary of Palo Alto Networks PCNSE Certified in the Market?
The average salary for someone with a Palo Alto Networks PCNSE certification is approximately $125,000 per year.
Who are the Testing Providers of Palo Alto Networks PCNSE Exam?
Palo Alto Networks offers official practice tests and certifications for the PCNSE exam. They can be found on their website or through their authorized training partners.
What is the Recommended Experience for Palo Alto Networks PCNSE Exam?
The recommended experience for Palo Alto Networks PCNSE exam is at least one year of hands-on experience with Palo Alto Networks technologies and a solid understanding of network security concepts. Additionally, candidates should have experience configuring, managing, and troubleshooting Palo Alto Networks next-generation firewalls.
What are the Prerequisites of Palo Alto Networks PCNSE Exam?
The Prerequisite for Palo Alto Networks PCNSE Exam is to have a minimum of 6 months of experience with Palo Alto Networks technologies.
What is the Expected Retirement Date of Palo Alto Networks PCNSE Exam?
The official website for Palo Alto Networks PCNSE exam information is https://www.paloaltonetworks.com/services/certification/pcnse.html. On this page, you can find information about the exam, including the expected retirement date.
What is the Difficulty Level of Palo Alto Networks PCNSE Exam?
The difficulty level of the Palo Alto Networks PCNSE exam is considered to be moderate to difficult. It is recommended that candidates have at least one year of experience in configuring, managing, and troubleshooting Palo Alto Networks security solutions.
What is the Roadmap / Track of Palo Alto Networks PCNSE Exam?
The Palo Alto Networks PCNSE certification roadmap is as follows:
1. Complete the Palo Alto Networks PCNSE online training course.
2. Pass the PCNSE exam.
3. Receive your PCNSE certification.
4. Maintain your certification by attending the annual Palo Alto Networks PCNSE Symposium.
5. Renew your certification every three years by taking the PCNSE recertification exam.
What are the Topics Palo Alto Networks PCNSE Exam Covers?
The Palo Alto Networks PCNSE exam covers a variety of topics related to Palo Alto Networks technology and architecture. These topics include:
1. Firewall Fundamentals: This topic covers the basics of firewall technology, including the types of firewalls, how they work, and their security benefits. It also covers the various features and capabilities of Palo Alto Networks firewalls.
2. Network Security: This topic covers the different security measures used to protect networks, such as intrusion prevention, antivirus, and content filtering. It also covers the different types of attacks and how to defend against them.
3. Virtualization: This topic covers the basics of virtualization and how it can be used to improve network security. It also covers the different types of virtualization technologies, such as cloud-based and container-based virtualization.
4. Security Policies and Best Practices: This topic covers the different security policies and best practices used to secure networks.
What are the Sample Questions of Palo Alto Networks PCNSE Exam?
1. What is the purpose of App-ID in Palo Alto Networks firewalls?
2. Describe the differences between User-ID and User-Fingerprinting.
3. How does GlobalProtect secure remote access?
4. What is the purpose of the Threat Prevention feature in Palo Alto Networks?
5. How does the WildFire service detect and prevent malicious files?
6. What is the purpose of the Panorama management tool?
7. How does the URL Filtering feature work in Palo Alto Networks?
8. Describe the different components of the Next-Generation Firewall architecture.
9. What is the purpose of the GlobalProtect Gateway?
10. How does the Content-ID feature work in Palo Alto Networks?
Palo Alto Networks PCNSE (Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0) What is the Palo Alto Networks PCNSE (PAN-OS 11.0) Certification? The PCNSE PAN-OS 11.0 certification is pretty much the gold standard if you're working with Palo Alto Networks firewalls. Other security certs exist, sure, but this one proves you actually know how to deploy, configure, and troubleshoot next-gen firewalls in real production environments. It's not some entry-level check-the-box thing. This is for engineers who live and breathe firewall operations. The Palo Alto firewall certification space has evolved over the years, and PAN-OS 11.0 represents the latest version. What makes this different? The exam fits with PAN-OS 11 training content and covers all the enhanced security features that came with this release. If you're managing enterprise security infrastructure, this credential tells employers you understand current platform capabilities and can implement them properly, not just... Read More
Palo Alto Networks PCNSE (Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0)
What is the Palo Alto Networks PCNSE (PAN-OS 11.0) Certification?
The PCNSE PAN-OS 11.0 certification is pretty much the gold standard if you're working with Palo Alto Networks firewalls. Other security certs exist, sure, but this one proves you actually know how to deploy, configure, and troubleshoot next-gen firewalls in real production environments. It's not some entry-level check-the-box thing. This is for engineers who live and breathe firewall operations.
The Palo Alto firewall certification space has evolved over the years, and PAN-OS 11.0 represents the latest version. What makes this different? The exam fits with PAN-OS 11 training content and covers all the enhanced security features that came with this release. If you're managing enterprise security infrastructure, this credential tells employers you understand current platform capabilities and can implement them properly, not just legacy concepts that stopped being useful five years ago.
What the PCNSE actually validates
This cert proves you can do the job. Period.
We're talking full knowledge of next-generation firewall operations, security policy implementation, threat prevention mechanisms, and network segmentation strategies that work in the real world. The exam tests whether you can configure interfaces, set up routing, create security rules that make sense, and troubleshoot when things go sideways. Because they will.
The global recognition matters more than people realize. I've seen hiring managers filter specifically for PCNSE-certified candidates because they know these folks have proven expertise in vendor-specific implementations, not just theoretical nonsense. One thing to say you understand firewalls conceptually. Another to demonstrate you can work through the Palo Alto Networks platform and solve real problems under pressure.
Who this certification is actually for
Network security engineers who deploy and manage Palo Alto Networks firewalls in production should absolutely pursue this. If you're the person responsible for keeping those firewalls running and secure, this cert validates what you're already doing daily. It also fills knowledge gaps you didn't know you had, which is kinda scary but useful.
Security architects designing next-gen firewall solutions need this too. When you're planning enterprise network security, understanding the platform's capabilities at this level lets you design better architectures that won't fall apart under real conditions. Systems administrators transitioning into specialized firewall roles will find the PCNSE gives them credibility they lack without hands-on firewall experience.
SOC analysts benefit massively. You can't analyze logs and investigate incidents properly if you don't understand how the firewall works underneath. Network engineers expanding into security technologies should consider this certification. It's a natural progression that opens doors you didn't know existed.
Consultants providing Palo Alto Networks services basically need this credential to maintain credibility with customers who know what they're talking about. Pre-sales engineers with PCNSE certification can demonstrate technical expertise during customer engagements in ways that generic security knowledge can't match.
Ideal candidates?
Typically 3-5 years of networking experience plus 6-12 months of hands-on work with PAN-OS platforms gets you there. If you're coming in with foundational certs like PCCSA or the PCNSA, you're probably in good shape. Career changers with strong networking fundamentals can succeed here too, but expect to invest serious lab time. Like, actual dedicated hours, not just casual reading.
Skills you'll prove you have
The certification demonstrates proficiency across a ridiculous range of capabilities that feels overwhelming at first. You'll need to show you can deploy Palo Alto Networks next-gen firewalls in various network topologies. Not just simple edge deployments but complex distributed architectures with multiple sites, cloud integrations, and hybrid environments. Configuring network interfaces, virtual routers, security zones, and layer 3 routing protocols is table stakes.
Creating and managing security policies based on applications, users, and content is where things get interesting. App-ID technology identification and control matters because applications don't respect traditional port-based rules anymore. They just don't. User-ID configuration maps IP addresses to usernames for identity-based policy enforcement, which is critical in modern environments where IP addresses mean basically nothing.
Content-ID features cover antivirus, anti-spyware, vulnerability protection, and file blocking. You need to understand when and how to apply each without creating bottlenecks. SSL/TLS decryption policies let you inspect encrypted traffic, but here's the thing: you also need to know privacy compliance considerations because you can't just decrypt everything without thinking about regulations like GDPR or HIPAA.
VPN configuration includes both site-to-site IPsec and GlobalProtect remote access solutions. High availability configurations for active/passive and active/active scenarios prevent downtime that'll get you paged at 3 AM. Panorama centralized management keeps policy consistent across distributed deployments, which becomes essential once you're managing more than a handful of firewalls.
Log analysis, report generation, and monitoring tools provide security visibility you can't get any other way. Without proper logging you're flying blind. Troubleshooting using CLI commands, packet captures, and system diagnostics separates engineers who can fix problems from those who just open support tickets and hope for the best. Threat intelligence integration and automated security updates through dynamic content keep your defenses current without manual intervention that nobody has time for. Then there's QoS policies that prioritize critical applications, and NAT configurations including source NAT, destination NAT, and NAT64 for IPv6 transitions.
My old boss used to say logging was optional until the day something broke and legal got involved. Then suddenly everyone cared about those reports they'd been ignoring for months.
How the exam actually works
The Palo Alto Networks PCNSE exam format includes 75 multiple-choice questions you'll complete in 90 minutes, which sounds generous until you're actually in there. The PCNSE exam cost runs $200, which is pretty reasonable compared to some vendor certs that charge $300+ for similar exams. Cisco's basically printing money at this point. You can take it at Pearson VUE testing centers or through online proctoring if you prefer testing from home in your pajamas.
The PCNSE passing score is 70%.
Sounds manageable until you realize how specific some questions get. They're not asking generic "what is a firewall" questions. They want to know exactly which CLI command you'd use in a specific troubleshooting scenario or how a particular feature behaves when configured a certain way. That requires actual knowledge, not guessing.
What makes the PCNSE challenging
The difficulty level is no joke. Some of these questions made me second-guess myself even after years of experience. The PCNSE exam objectives cover deployment, initial configuration, interfaces, zones, routing, security policies, NAT, App-ID, Content-ID, User-ID, threat prevention, security profiles, decryption concepts, VPNs, high availability, logging, monitoring, reporting, troubleshooting, and Panorama management. When listed out like that it feels absolutely massive.
What trips people up is the depth of knowledge required beyond surface-level understanding. You can't just understand concepts theoretically. You need to know implementation details, configuration syntax, and how different features interact in ways that aren't always documented clearly. Questions often present scenarios where multiple answers seem plausible, but only one reflects how PAN-OS actually behaves in production.
Prerequisites and what you actually need
Official PCNSE prerequisites are minimal. Palo Alto doesn't mandate specific prior certifications, which is refreshing. But recommended background includes solid networking fundamentals, understanding of security concepts, and hands-on experience with PAN-OS platforms that you can't fake. If you're coming in cold without touching a Palo Alto firewall, you're gonna struggle hard.
Six to twelve months of hands-on NGFW operations experience makes a huge difference between passing and failing. That doesn't mean you need to work exclusively with Palo Alto firewalls full-time, but you should have configured policies, set up VPNs, implemented security profiles, and troubleshot real issues where things broke unexpectedly. Lab experience helps. Production experience where your configurations actually matter teaches you things labs never will, like how to fix mistakes before anyone notices.
Starting with the PCCET or working your way through the PCNSA first makes sense for many people who aren't masochists. The progression from associate-level to engineer-level certification builds knowledge incrementally rather than trying to absorb everything at once and hoping your brain doesn't explode.
Study materials that actually help
Official Palo Alto Networks training courses provide the foundation you can't get elsewhere. The EDU-210 course covers PAN-OS 11.0 configuration and management in detail. Yeah, the courses cost money, sometimes significant money, but the structured curriculum and hands-on labs speed up learning compared to piecing together random YouTube videos of varying quality.
PCNSE exam preparation resources should include official documentation and admin guides for PAN-OS 11 that cover every feature exhaustively. The technical documentation library contains detailed explanations of every feature, configuration examples, and best practices that work. Read the release notes too. Understanding what changed in PAN-OS 11 versus earlier versions helps contextualize features and explains why certain things work the way they do.
Lab options matter enormously.
Hardware firewalls are ideal if you have access through work or can afford them, but VM-Series virtual firewalls work great for self-study on a budget. Cloud deployment options exist, and third-party virtual lab platforms offer pre-configured environments that save setup time. The key is getting hands-on time configuring features, not just reading about them passively and hoping knowledge osmosis happens.
Making practice tests work for you
PCNSE practice tests are valuable but only if you use them correctly. Most people don't. Don't just memorize answers, that's pointless and you'll fail the real exam when questions are worded differently or scenarios change slightly. Instead, use practice tests to identify knowledge gaps in a systematic way. When you miss a question, research why the correct answer is right and why the others are wrong, then lab it out if possible.
High-quality practice test providers explain answers thoroughly rather than just marking them right or wrong like you're in elementary school. Look for sets that reference official documentation so you can verify information independently. Taking a practice test, scoring 60%, then immediately retaking the same test until you score 90% teaches you nothing except how to recognize specific questions. That helps nobody.
Measure readiness by objective area rather than overall score alone. If you're crushing questions about security policies but struggling with high availability configurations, you know exactly where to focus study time instead of wasting effort on stuff you already know. Common weak areas are decryption policy details, Panorama template and device group hierarchies, and advanced troubleshooting scenarios that require multiple steps.
Renewal and staying current
PCNSE renewal policy requires recertification every two years, which keeps happening faster than you'd expect. You can retake the current PCNSE exam or pursue higher-level certifications like the PCNSC to extend validity and show career progression. The two-year cycle makes sense given how rapidly PAN-OS evolves. What you learned for PAN-OS 11.0 will need updating as 11.1, 11.2, and eventually 12.0 releases introduce new features that change how things work.
Keeping skills current between recertifications matters more than just maintaining the credential on paper. Following Palo Alto Networks community discussions, testing new features in lab environments when they're released, and implementing updated security profiles in production keeps your knowledge relevant rather than outdated. The certification distinguishes professionals who commit to staying current with evolving network security technologies rather than letting expertise stagnate into irrelevance.
Is the PCNSE worth pursuing?
If you work with Palo Alto Networks firewalls or want to specialize in next-gen firewall technologies that actually pay well, absolutely yes. The credential opens doors, proves expertise employers value when hiring, and validates skills that directly translate to job performance and problem-solving ability. Just don't underestimate the preparation required. This isn't a weekend study cert you can cram for. It's a serious engineering credential that demands serious preparation and actual hands-on experience.
PCNSE PAN-OS 11.0 Exam Overview
What is the Palo Alto Networks PCNSE (PAN-OS 11.0) certification?
The PCNSE PAN-OS 11.0 certification is the Palo Alto firewall credential that shows you can actually run next-generation firewall operations, not just click around the WebUI hoping nothing breaks.
PCNSE isn't entry level. It sits higher than stuff like PCCET or PCCSA, and honestly it's closer to "you're on the hook for production security policies" territory than "you watched a few videos and know what App-ID is."
Who the PCNSE is for (roles and experience level)
Firewall admins. Network security engineers. People who get paged at 2am.
Also folks moving up from PCNSA who want to prove they can handle more than baseline config and day-one rules. If you're a consultant, it pairs nicely with things like PCNSC depending on what your shop expects. I've seen people treat this cert like a magic resume bullet, but without the real work behind it, interviews expose that pretty quickly.
Skills validated (PAN-OS 11 administration and operations)
This exam tests your ability to configure, manage, and troubleshoot Palo Alto Networks next-generation firewalls. That "troubleshoot" part? Where people get humbled. The Palo Alto Networks PCNSE exam covers both theoretical knowledge and practical application of security concepts, so you need to know what features do, when to use them, and how to prove they're working using logs, CLI, and packet flow logic.
PCNSE PAN-OS 11.0 exam overview
The exam focuses specifically on PAN-OS 11.0 features, functionality, and administrative workflows. If your experience is mostly on older PAN-OS, you'll feel little paper cuts everywhere. Naming changes. UI flow differences. Those "wait, where is that setting now" moments.
Random order questions. Zero mercy.
Exam format and key details
Expect multiple-choice and multiple-select questions testing conceptual understanding and practical application. Scenario-based questions present real-world situations requiring analysis and appropriate solution selection. Total's usually 75 to 80 questions covering all PCNSE exam objectives domains, with a 90-minute time limit. That sounds fine until you hit long scenarios with exhibits, diagrams, or configuration snippets that force you to slow down and actually read.
No breaks allowed. NDA required before content shows. Computer-based testing through Pearson VUE at a testing center or online proctoring. Pearson VUE gives you a short tutorial before the clock starts so you can get used to the navigation and how multiple-select works. Results are immediate at the end. Pass/fail plus domain-level performance feedback, which's useful because it tells you where you were weak without giving you the exact questions you missed.
PCNSE exam cost
The PCNSE exam cost is $200 USD per attempt. Pricing's mostly consistent globally, but your local currency conversion can make it look slightly different at checkout. Payment happens when you schedule in Pearson VUE. No refunds if you miss your appointment or cancel inside 24 hours.
Retake fees? Same price. Not gonna lie, that part stings if you go in underprepared.
Training's separate. Official instructor-led PAN-OS 11 training can run $3,000 to $4,500 USD. Self-paced subscriptions exist through Palo Alto Networks' Learning Center. Practice exam purchases are another line item, usually $50 to $150 depending on who's selling them. Lab costs range from "free community scraps" to paid lab platforms. Total spend for the full certification push can be $500 to $5,000. Employers often pay if you make a decent case that it reduces risk and improves incident response.
PCNSE passing score (what to know)
People always ask about the PCNSE passing score. The common guidance's around 70% correct, so roughly 53 to 56 correct out of 75 to 80. Palo Alto Networks doesn't publicly lock an exact threshold and it can vary by exam form. Scaled scoring's used to keep different versions fair.
Multiple-select has no partial credit. Brutal. Miss one option, you miss the whole thing.
You don't get penalized for wrong answers, so answer everything. The score report won't show your exact percent correct, just pass/fail and domain-level breakdown. If you fail, that breakdown's your map for round two.
PCNSE difficulty level (what makes it challenging)
"How hard is the PCNSE PAN-OS 11.0 exam" depends heavily on whether you've actually operated these firewalls under pressure. The exam assumes networking fundamentals are already in your bones. Routing and switching basics. TCP/IP behavior. How NAT interacts with sessions. What happens when asymmetric routing shows up and ruins your afternoon.
Scenario-based questions carry real weight. You'll see stuff that forces you to combine packet flow, security policy logic, NAT rules, zone design, routing decisions, App-ID behavior, and logging interpretation, all while the clock keeps moving. If you've only memorized terms from a PCNSE PAN-OS 11 study guide without touching a lab, it gets ugly fast.
PCNSE exam objectives (PAN-OS 11.0)
Candidates must demonstrate skill across all major domains of firewall administration and security operations. Questions are designed to catch memorization. They want comprehension.
Deployment and initial configuration
Day-one setup stuff. Licensing, updates, basic hardening, admin access methods. Understanding how PAN-OS thinks about objects and policy evaluation. Simple, until you're asked what choice matches a specific security requirement and "best practice" expectation.
Interfaces, zones, and routing
This's where you either have clean mental models or you don't. Interfaces, VLANs, virtual routers, static routes, dynamic routing awareness, zone design.
The exam loves to test whether you understand why a rule "should" match but doesn't. Half the time it's because traffic never hit the expected zone pair due to routing or interface assignment.
Security policies and NAT
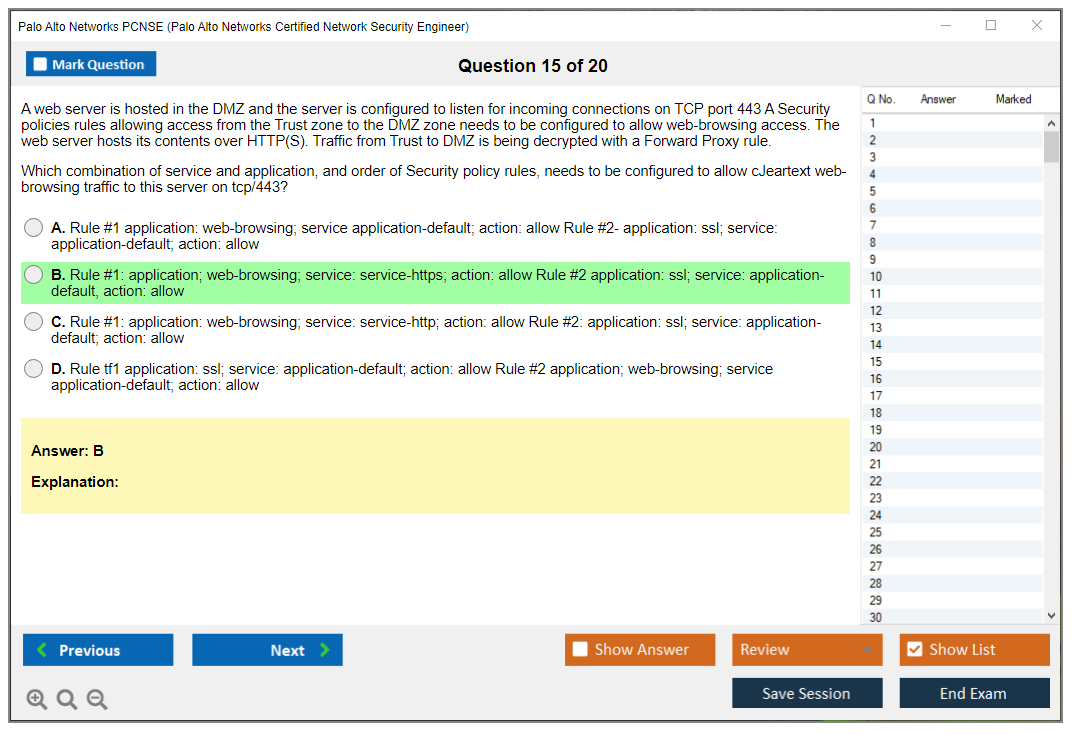
Security policy ordering. Rule shadowing. Service vs application usage. NAT types and how they affect what you see in logs.
One detailed tip: get comfortable predicting session behavior. If you can't explain pre-NAT vs post-NAT values, and you don't know which one shows up where, you'll waste minutes on every scenario that includes a NAT twist. Those minutes add up fast inside 90 minutes.
Other bits show up too. Rulebase structure, object reuse, tags, policy cleanup.
App-ID, Content-ID, User-ID fundamentals
These're table stakes. App-ID behavior, dependencies, what happens when apps shift ports. How to write policies that don't collapse into "any any allow."
User-ID's always part concept, part reality. Mapping sources, group usage, what breaks when identity isn't learned.
Threat prevention and security profiles
Security profiles're where "checkbox security" gets exposed. You need to know how profiles attach, how they trigger, what logs look like when they do.
Second detailed tip: understand what you're trying to prevent and what data proves the control worked. It's one thing to say "attach Anti-Spyware," and another to read threat logs and know whether the action was alert, block, reset-client, reset-server, or reset-both. What that means for the user experience and your incident response steps matters.
The rest's there too. WildFire basics, URL filtering logic, file blocking, vulnerability profiles, profile groups.
Decryption concepts and policy considerations
Decryption's a favorite pain point. You need to balance security requirements with privacy and compliance, and the questions often force a tradeoff. Certificate handling, exclusion logic, what breaks with pinned certs. How to troubleshoot when users scream "the site's broken."
VPNs (site-to-site and remote access) overview
IPsec basics, IKE concepts, operational troubleshooting awareness. Remote access shows up too depending on the objective mix, but usually from the angle of "can you interpret what's wrong" rather than "can you build a full design from scratch."
High availability (HA) concepts
HA configuration, state sync expectations, failover behavior. What you should check first when a pair behaves weird. Split brain scenarios. Link monitoring. Path monitoring. Fun stuff.
Logging, monitoring, and reporting
You need to read logs fast. Traffic logs, threat logs, system logs. Knowing where in the UI you'd validate a claim from a scenario.
Also, yeah, you should know what an exhibit's trying to tell you. Those screenshots aren't decoration.
Troubleshooting and operations (CLI/WebUI workflows)
CLI commands matter. Basic operational commands, session inspection, routing checks, interpreting counters.
Packet flow knowledge's essential. If you don't know the order of operations well enough to reason about where a drop might happen, you'll guess. Guessing burns attempts.
Panorama and centralized management (as applicable)
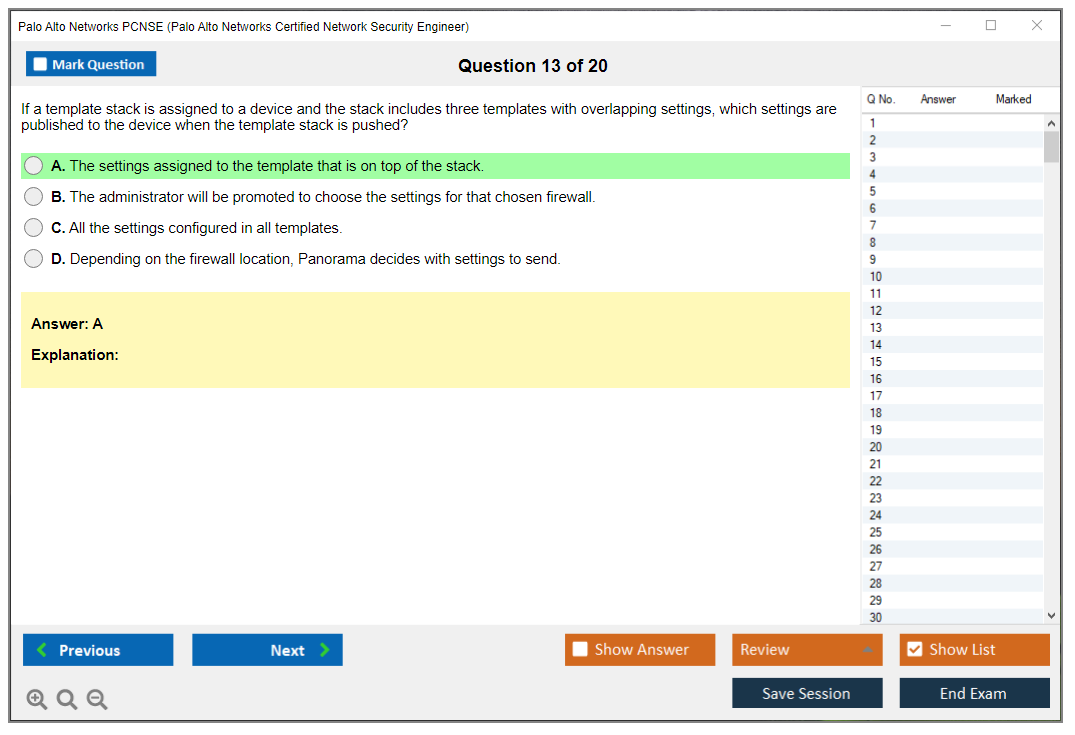
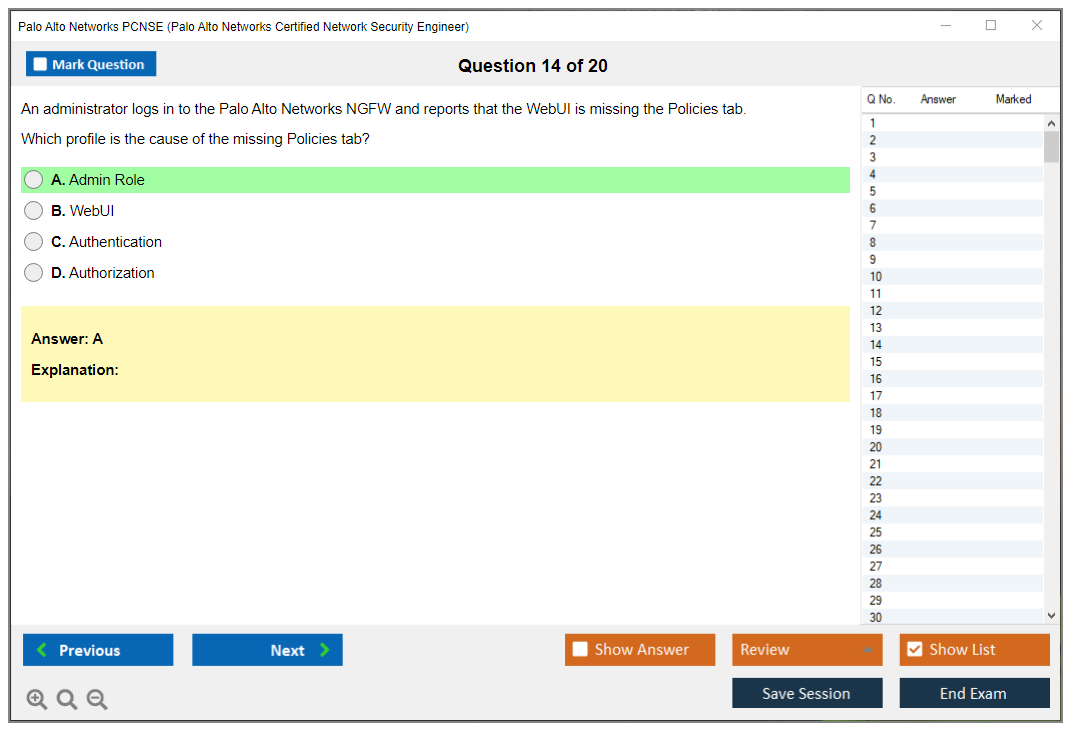
Panorama tends to show up as "do you understand centralized policy management." Device groups, templates, template stacks, how overrides work. You don't need to be a full-time Panorama admin, but you do need to understand what goes where and why.
PCNSE prerequisites and recommended experience
There aren't hard official PCNSE prerequisites like "must have X cert first," but recommended background's real-world work on Palo Alto firewalls plus general networking fundamentals. If you've never built zones, written policies, troubleshot NAT, and validated security profile actions in logs, you're trying to sprint before you can walk.
Hands-on matters. A lot.
If you're brand new to the Palo Alto Networks certification path, starting at PCCSA or PCNSA is usually a better move than jumping straight into PCNSE and hoping vibes carry you.
Best study materials for PCNSE PAN-OS 11.0
Official courses're expensive, but they're structured. Documentation's free, but it's on you to turn it into a plan.
Official Palo Alto Networks training courses
Instructor-led's pricey. $3k to $4.5k. Self-paced's cheaper. If your employer pays, awesome. If not, you can still get there with docs plus labs, but it takes discipline.
Official documentation and admin guides (PAN-OS 11)
Admin guides're boring. They're also where the exam's phrasing often comes from. Read them like a tech would, not like a student. Try a feature. Break it. Fix it.
Lab options (hardware, VM-Series, cloud, or virtual labs)
Home lab hardware's nice if you can swing it. VM-Series can work if you've got compute. Cloud labs're convenient. Community labs exist too, just don't expect them to be stable.
Study plan (2 to 6 weeks / 6 to 12 weeks options)
If you work with Palo Alto daily, 2 to 6 weeks of focused review plus practice scenarios can be enough. If you're learning while working a different role, 6 to 12 weeks is more realistic. You need repetition and time to build intuition.
PCNSE practice tests and exam prep strategy
Practice tests help. Bad practice tests hurt.
Practice tests: how to choose high-quality sets
Pick ones that explain why an answer's right. Avoid anything that looks like leaked questions. Seriously. Aside from ethics, it trains you to memorize junk instead of learning the skill. The exam rotates.
What to measure: readiness checklist by objective
Map your results to PCNSE exam objectives. If you keep missing decryption, stop pretending it'll "probably be fine." Fix it.
Other areas people ignore? HA edge cases, Panorama placement logic, detailed log interpretation.
Common weak areas and how to fix them
Decryption, packet flow, and troubleshooting methodology show up a lot. Build mini-scenarios in your lab where you intentionally misconfigure one thing and then prove you can find it quickly using the tools PAN-OS gives you.
Final-week revision plan
Last week's for tightening. Re-read your weak domains. Do timed sets. Practice reading exhibits fast. Sleep.
PCNSE renewal and recertification
People forget this part until LinkedIn nags them.
Renewal cycle and validity (what to verify)
The PCNSE renewal policy can change, so verify the current validity period and recertification rules on Palo Alto Networks' certification portal before you plan your timeline.
Recertification options (retake vs. higher-level/updated exams)
Often your path's retake the current exam version or pass a newer version when it releases. Sometimes a higher credential can renew lower ones, depending on the program rules at the time.
Keeping skills current with PAN-OS releases
PAN-OS keeps moving. If you stop touching the platform, you get rusty fast. Keep reading release notes. Keep building small labs when new features land.
FAQs about PCNSE PAN-OS 11.0
Is PCNSE worth it for firewall engineers?
If you manage enterprise firewalls, yes. It signals you can make configuration decisions based on security requirements and best practices. Passing shows readiness to manage enterprise-grade Palo Alto Networks security infrastructure and implement defense-in-depth using NGFW capabilities.
How long should I study for PCNSE?
Two buckets. 2 to 6 weeks if you're hands-on daily. 6 to 12 weeks if you're not.
Can I pass PCNSE without real firewall experience?
Possible, but honestly rough. Scenario-based questions punish "book-only" prep. The testing methodology's built around analysis and problem-solving, not flashcards.
What score do I need to pass PCNSE?
Plan for about 70% as a target, even though the exact passing threshold isn't published and may vary by version. Answer everything. No wrong-answer penalty.
What's the best way to use practice exams without memorizing answers?
Use them like diagnostics. After every set, write down which objective you missed. Actually recreate the scenario in a lab if you can. Then prove the fix by checking the exact logs and commands you'd use on the job, because that's what the next-generation firewall engineer certification vibe's really testing.
PCNSE Exam Objectives (PAN-OS 11.0)
Breaking down the PCNSE exam objectives for PAN-OS 11.0
Here's the thing about PCNSE exam objectives for PAN-OS 11.0: they're actually full. We're talking everything from basic device setup through advanced troubleshooting scenarios that'll show up in your production environment. Not theoretical fluff.
The blueprint organizes into domains that mirror how you'd actually deploy and operate Palo Alto Networks firewalls in enterprise settings. Each domain carries different weight, which helps when you're planning study time. Understanding these weightings saves you from burning weeks on topics that represent maybe 5% of the questions. I once spent three weeks obsessing over a minor feature only to see one question about it on exam day.
Initial deployment and system configuration fundamentals
You've gotta start somewhere. The exam tests whether you can perform initial device setup: configuring management interfaces, creating administrator accounts with proper role-based access controls, foundational stuff. Might seem basic, but I've watched engineers completely botch licensing activation procedures or forget to register devices with the support portal. Creates massive headaches later when they desperately need threat prevention updates.
Licensing types matter here. Dynamic updates for applications, threats, antivirus, URL filtering all require active subscriptions you can't skip. Bootstrap configuration? Huge for cloud deployments because it automates initial config delivery through cloud-init or user-data, eliminating tedious manual setup steps.
Certificate management gets tested too. Device certificates, certificate authorities, understanding certificate chains for secure administrative access. All fair game. Expect scenarios where you're troubleshooting certificate validation issues or configuring enterprise CA integration under pressure.
Network configuration domains covering interfaces and routing
Physical interface configuration seems straightforward until you're dealing with aggregate ethernet bundles, VLAN subinterfaces, and interface management profiles controlling which administrative protocols can reach specific interfaces. Security zones segment your network and create enforcement boundaries. Every interface must belong to a zone, and traffic between zones? That requires security policy evaluation. Period.
Virtual routers handle routing logic. Static routes, default gateways, dynamic routing protocols like OSPF and BGP get tested thoroughly. You should know route redistribution between protocols and how policy-based forwarding can steer traffic based on application or user criteria, completely ignoring routing table entries when necessary.
Layer 2 deployments using virtual wires or transparent mode show up because they're common in environments where you absolutely cannot change IP addressing schemes. Understanding when to use tap mode versus inline deployment modes is critical for proper traffic visibility without disrupting production flows.
The exam covers interface types beyond standard ethernet. HA interfaces, log forwarding interfaces, tunnel interfaces all serve specific purposes you need to recognize. MTU settings and jumbo frame support impact performance in high-throughput environments, so expect questions about optimizing these parameters.
Security policy and NAT configurations that matter
Security policies? Core of any firewall deployment. The exam tests policy rule ordering extensively because rule shadowing can completely destroy your intended security posture without you realizing it. Understanding how the firewall evaluates rules from top to bottom until finding a match is fundamental knowledge you can't skip.
Application-based policies using App-ID give you granular control that traditional port-based rules just can't match. You should know how to create policies based on zones, addresses, applications, users, services in various combinations. The exam definitely includes scenarios where you're determining the most efficient policy structure under specific constraints.
NAT gets complicated fast. Source NAT with dynamic IP and port (DIPP) is common for outbound internet access, but you need to understand dynamic IP translation and static IP scenarios too. Destination NAT for publishing internal services requires understanding port forwarding and bidirectional NAT considerations when external users need to reach internal servers through multiple layers.
Policy-based NAT adds another layer where translation decisions depend on specific traffic criteria beyond just source and destination zones. Gets confusing. The relationship between NAT policy processing and security policy evaluation trips people up constantly. NAT happens first, then security policy evaluates the post-NAT addresses. Not the other way around.
Security policy actions include allow, deny, drop, reset options with different behaviors. Log forwarding profiles determine where policy match events get sent for compliance and incident investigation purposes. Managing large rulesets? Policy tags and filtering become essential organizational tools that the exam covers in detail.
App-ID, Content-ID, and User-ID integration points
App-ID technology identifies applications regardless of port or protocol, which fundamentally changes how you write security policies compared to legacy approaches. The exam tests your understanding of how App-ID works under the hood. Signature matching, protocol decoding, behavioral analysis all contribute to accurate identification in ways that matter operationally.
Custom application creation lets you define proprietary apps that App-ID doesn't recognize natively. Huge for enterprises with custom software. Application filters and groups simplify policy management when you're dealing with hundreds of applications across your environment.
Content-ID covers multiple security profiles: antivirus, anti-spyware, vulnerability protection, file blocking. Each profile type serves different purposes, and the exam expects you to know appropriate use cases cold. Antivirus scans files for known malware, anti-spyware blocks command-and-control traffic, vulnerability protection prevents exploit attempts, and file blocking restricts file types by application or direction.
User-ID integration brings identity awareness into security policies. Incredibly powerful. Deploying User-ID agents for Active Directory integration, configuring captive portal authentication for guest users, setting up multi-factor authentication with SAML or RADIUS providers are all testable topics. Group mapping creates dynamic address groups based on user identity, eliminating the need to maintain static IP lists that become outdated instantly.
Terminal Services and Citrix environments require special User-ID handling because multiple users share the same session host IP address. Complicates everything. GlobalProtect integration with User-ID ensures remote users are properly identified regardless of their connection location.
Threat prevention profiles and security mechanisms
Security profile configuration is where you start seeing real protection value. Antivirus profiles need proper protocol decoder configuration and file type restrictions that make sense for your environment. Anti-spyware profiles with DNS sinkholing can block command-and-control traffic before malware establishes communication channels with external attackers.
Vulnerability protection profiles defend against known exploits in common software. Managing exceptions for false positives without weakening overall protection requires understanding threat severity levels and attack characteristics. It's a balancing act.
URL filtering uses categories to control web access. Custom URL categories let you define organization-specific allow or block lists beyond standard categorization.
Data filtering profiles prevent sensitive information exfiltration by detecting patterns like credit card numbers or social security numbers in outbound traffic before they leave your network. File blocking restricts file types based on direction and application. Maybe you allow PDF downloads but block executable uploads through webmail applications.
DoS protection and zone protection profiles defend against volumetric attacks and reconnaissance attempts that could compromise your perimeter. Understanding the difference between aggregate versus classified DoS protection helps you configure appropriate thresholds without generating false alarms.
WildFire integration sends unknown files for cloud-based malware analysis. Game-changing. Automated signature generation means new threats get blocked across all WildFire subscribers within minutes of initial detection anywhere in the world. The exam covers WildFire configuration, custom signature creation, threat exception handling.
SSL/TLS decryption architecture and policy design
Decryption is essential for inspecting encrypted traffic, which now represents over 90% of web traffic in most environments. You can't ignore it. The exam tests forward proxy decryption for outbound traffic and inbound inspection for encrypted connections to internal servers.
Decryption policy processing happens before security policy evaluation. Makes sense because you need to decrypt traffic before inspecting application content hidden inside encrypted tunnels. Certificate management becomes critical here. You need enterprise CA integration so client devices trust the firewall's decryption certificates without generating browser warnings that train users to click through security alerts.
Decryption exclusions handle privacy requirements, compliance restrictions, technical compatibility issues that inevitably arise. Some applications break when traffic is decrypted, and certain destinations like banking or healthcare sites require exclusion for privacy reasons or regulatory compliance.
Performance implications of decryption are significant. Hardware acceleration and dedicated decryption modules in newer firewall models help, but you still need to understand throughput impacts on your specific model. Decryption profiles control TLS versions and cipher suites, letting you block weak cryptography while maintaining compatibility with legacy systems.
SSH proxy configuration extends decryption to encrypted administrative sessions. The exam might test scenarios where you need to inspect SSH traffic without breaking legitimate administrative access.
VPN technologies for site-to-site and remote access
IPsec site-to-site VPNs connect offices or data centers securely across untrusted networks like the internet. You need to understand IKE gateway configuration, crypto profiles defining encryption and authentication algorithms, tunnel interfaces that route traffic through VPN connections. Route-based VPNs use tunnel interfaces and routing protocols, while policy-based VPNs use proxy IDs to match interesting traffic that should traverse the tunnel.
GlobalProtect provides remote access VPN functionality for mobile users. Portal and gateway configurations work together. The portal provides client configuration, and gateways terminate actual VPN connections from end users.
Multi-factor authentication integration strengthens security for remote access scenarios where users are connecting from potentially compromised networks.
Split tunneling versus full tunneling impacts which traffic routes through VPN tunnels. Strong opinions on both sides. Full tunneling sends all remote user traffic through the corporate firewall, while split tunneling only routes corporate-bound traffic through the VPN. The exam covers configuration implications and security considerations for both approaches without being pushy about it.
Certificate-based authentication provides stronger security than pre-shared keys for VPN connections in production environments. Large-scale deployments benefit from Panorama's centralized VPN management, which the exam touches on.
High availability configurations and failover mechanisms
Active/passive HA provides redundancy. One device actively processes traffic while the peer stands ready for failover when disaster strikes. Active/active HA distributes load across both devices while maintaining redundancy. Best of both worlds. Understanding HA link types is essential: control links for configuration sync, data links for session sync, backup links for redundancy when primary links fail.
Session synchronization mirrors connection states between HA peers so failover doesn't break active sessions and disrupt user experience. Path monitoring checks upstream and downstream connectivity, triggering failover when critical paths fail even if the firewall itself remains operational.
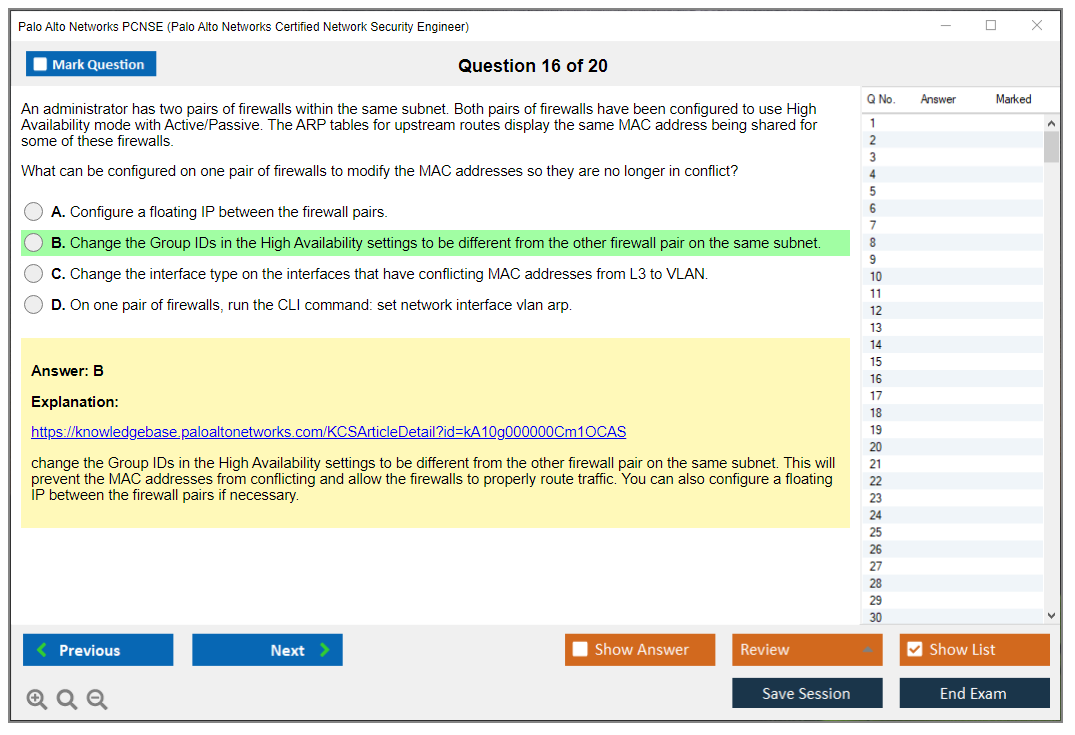
Preemptive versus non-preemptive failover behavior affects whether a recovered primary device automatically takes over processing again or waits. Virtual MAC addressing and gratuitous ARP ensure smooth failover at layer 2 without requiring routing updates that take time to propagate.
Common HA troubleshooting scenarios definitely appear on the exam. Split-brain conditions, synchronization failures, misconfigured monitoring settings that cause unnecessary failovers. You need to diagnose these quickly.
Logging, monitoring, and operational visibility
Multiple log types serve different purposes, and you need to know which is which. Traffic logs show allowed and denied sessions, threat logs record security events and attempted attacks, system logs capture administrative actions and system events, configuration logs track changes to device configuration over time. Understanding what each log type contains helps with troubleshooting and compliance reporting when auditors come knocking.
Log forwarding to external SIEM platforms or syslog servers centralizes log collection across multiple devices in distributed environments. The ACC dashboard provides traffic visualization that helps identify top applications, users, threats without diving into raw logs and going cross-eyed.
Custom reports and scheduled report generation support compliance requirements and executive reporting needs when management wants pretty charts. Log filtering and correlation techniques help investigate security incidents efficiently. Finding related events across multiple log types reveals attack patterns that individual log entries miss.
Packet capture configuration lets you capture traffic matching specific filters for deep analysis when you're really stumped. Performance monitoring tracks session counts, throughput, resource utilization to identify capacity issues before they impact production and users start complaining.
Troubleshooting methodologies and CLI workflows
Common CLI commands like "show session all", "show routing route", "show interface all" provide quick verification of operational status when the GUI is too slow. Understanding packet flow through the firewall helps diagnose where traffic is getting dropped or blocked unexpectedly. Like detective work.
The session browser shows active connections with details like application, user, security policy rule, NAT translation. Session end reasons explain why connections terminated: timeout, policy deny, reset, application protocol issues all have different implications for troubleshooting.
System logs reveal configuration errors, licensing problems, operational issues that might not be obvious from traffic behavior alone. Sometimes you need to dig deeper. Tech support files bundle diagnostic information for Palo Alto Networks support cases when you need vendor assistance and you've exhausted your own troubleshooting.
Configuration commits apply pending changes to the running system. Commit validation checks for errors before actually implementing changes that could break everything. Rollback procedures let you revert to previous configurations when changes cause problems you didn't anticipate.
Software and content update troubleshooting includes verifying subscription status, checking connectivity to update servers, understanding the update installation process that sometimes fails mysteriously. The exam covers scenarios where updates fail and how to resolve them without panicking.
Panorama centralized management architecture
Panorama manages multiple firewalls from a single platform. Essential for large deployments. Template stacks push interface and network configurations consistently across managed devices, while device groups handle security policy and objects. Understanding when to use shared objects versus local objects helps design scalable management hierarchies that don't become nightmares.
Log collection aggregates logs from distributed firewalls for centralized analysis and reporting across your entire infrastructure. Centralized reporting across multiple devices provides organization-wide visibility that individual firewalls just can't deliver.
Panorama high availability protects the management plane with redundant Panorama appliances or virtual machines because losing your management platform is catastrophic. The exam covers Panorama HA configuration and failover behavior.
Putting exam objectives into study perspective
The PCNSE Practice Exam Questions Pack helps you assess readiness across all these domains effectively. Practice questions reveal weak areas faster than reading documentation alone. You might think you understand NAT policy processing until practice questions expose gaps in your knowledge that you didn't know existed.
The breadth of PCNSE exam objectives means you can't focus on just a few areas and hope for the best. Questions come from across the entire objective spectrum, so weak spots in any domain will cost you points when it matters. I've seen people who aced the networking domains but struggled with threat prevention profiles or User-ID integration. Balanced preparation across all objectives is essential for passing.
Coming from PCNSA certification? You'll recognize many fundamental concepts, but PCNSE dives much deeper into operational scenarios and advanced configurations that separate engineers from administrators. The jump from associate to engineer level requires hands-on experience with complex deployments and troubleshooting methodologies you can't learn from books alone.
Comparing PCNSE to other Palo Alto certifications like PCCSE or PCSAE, the PCNSE focuses specifically on firewall engineering rather than cloud security or automation specializations. Different skill sets for different roles. Each certification validates different competencies aligned with specific job functions in the security field.
The objectives reflect what you actually do as a security engineer managing Palo Alto Networks firewalls in production environments where mistakes have real consequences. Understanding deployment modes, configuring policies, implementing threat prevention, troubleshooting operational issues. This is the day-to-day work that PCNSE certification validates you can perform competently under pressure.
PCNSE Prerequisites and Recommended Experience
What is the Palo Alto Networks PCNSE (PAN-OS 11.0) Certification?
The PCNSE PAN-OS 11.0 certification is Palo Alto Networks' "prove you can run the firewall" badge. Not theory stuff. Not brand trivia either. It expects you to be comfortable living in PAN-OS day to day, making changes without breaking production, and knowing where to look when traffic does something weird that nobody can explain at first.
Who the PCNSE is for (roles and experience level)
This is for firewall admins, security engineers, and network folks who got "voluntold" into owning a Palo Alto. MSSP engineers too. The ones who jump between customers and need repeatable workflows. If you're a junior analyst who's never built policy and never troubleshot NAT? I mean, you can still study, but the exam will feel like it's written in a different dialect entirely.
Some people take it as their first Palo Alto firewall certification. That's fine. Just don't confuse "first Palo Alto cert" with "entry-level networking cert". Different animal.
Skills validated (PAN-OS 11 administration and operations)
PCNSE validates you can configure and operate PAN-OS 11. Stuff like zones, routing, security rules, NAT, security profiles, decryption concepts, VPNs, HA, logging, and basic troubleshooting across WebUI and CLI. It also touches centralized management, so yes, Panorama shows up even if your day job barely uses it and you've been avoiding it.
Short version? You're expected to drive.
PCNSE PAN-OS 11.0 Exam Overview
Exam format and key details
The Palo Alto Networks PCNSE exam is proctored and timed, and it's scenario-heavy in ways that catch people off guard. Not a "what does this acronym mean" vibe. More like, "here's what the admin did, here's what broke, what do you check next and why." You want the current PCNSE exam objectives printed or pinned somewhere because the questions tend to map to them pretty cleanly, more than you'd expect.
The vendor changes delivery details sometimes. Always confirm the current blueprint and exam page right before you schedule, or you'll regret it.
PCNSE exam cost
People ask constantly. PCNSE exam cost is typically around the same ballpark as other pro security exams, but it can vary by country, testing provider, and any bundles your employer buys through partnerships. Check the official Palo Alto Networks certification site for the current price, because guessing wrong here is how you end up arguing with procurement for two weeks and missing your prep window.
PCNSE passing score (what to know)
PCNSE passing score details aren't always presented like a simple "700 out of 1000" you can game through strategy. Treat it like most pro cert exams: you pass by being consistently competent across objectives, not by maxing one domain and praying the rest doesn't hurt you too badly. If you're weak on troubleshooting or NAT, that "I'll make it up elsewhere" plan usually fails spectacularly.
PCNSE difficulty level (what makes it challenging)
So, how hard is the PCNSE PAN-OS 11.0 exam? Hard in a very specific way. The challenge isn't memorizing menu paths or regurgitating definitions. The challenge is that PAN-OS features connect in ways that matter operationally, and the exam pokes those connections deliberately. A security rule interacts with App-ID behavior. NAT interacts with routing and zones. Decryption changes what threat profiles can see. Panorama changes how policy is pushed and where you troubleshoot failures.
Another issue? Time. You can't ponder every question like it's a philosophy class discussion.
I once watched a colleague who could recite the admin guide verbatim completely bomb this exam because he'd never actually fixed anything under pressure. Book knowledge gets you maybe halfway.
PCNSE Exam Objectives (PAN-OS 11.0)
You should treat the PCNSE PAN-OS 11 study guide as a map, not a novel you read cover-to-cover. The objectives are the map. Here's what you need to be comfortable with, not just familiar.
Deployment and initial configuration
Device onboarding basics. Admin access. Licenses and subscriptions. Updates. Baseline settings that matter. Also common gotchas like committing, candidate config versus running behavior, and what happens when you change management settings the wrong way and lock yourself out.
Interfaces, zones, and routing
L3 interfaces, subinterfaces, VLANs, virtual routers, static routes, dynamic routing awareness, and how zones control policy evaluation in ways that aren't always obvious. This is where people who "only do security policy" get exposed, because the firewall still routes and you still own the consequences.
Security policies and NAT
Rulebase logic. Rule order. Application behavior. Service ports. NAT types you actually see in real networks, not textbook examples. If you can't read a flow and predict pre-NAT and post-NAT addresses quickly, you're not ready yet.
App-ID, Content-ID, User-ID fundamentals
App-ID behavior, dependencies, what happens with unknown apps, and how User-ID mapping impacts policy in ways that break silently. Content-ID overlaps with profiles and inspection workflows. You don't need to be a PhD here. You do need working instincts.
Threat prevention and security profiles
Anti-spyware. Vulnerability protection. URL filtering. Wildfire concepts. File blocking. Profile attachment strategy that doesn't create bottlenecks. Also alert versus block decisions and their operational consequences. This is where "security engineer" shows up on your resume for real.
Decryption concepts and policy considerations
SSL forward proxy versus inbound inspection basics, certificate handling, and the operational reality: decryption breaks things if you don't plan exclusions and troubleshoot cert errors proactively. The exam likes policy logic here and tests your judgment.
VPNs (site-to-site and remote access) overview
IPSec concepts, tunnel interfaces, proxy IDs versus route-based thinking, GlobalProtect basics, and "why can't I reach the remote subnet" troubleshooting patterns that eat your afternoon.
High availability (HA) concepts
Active/passive fundamentals, timers, link and path monitoring, failover behavior, and what state sync does and doesn't do reliably. Not every HA edge case documented. The common ones that actually happen.
Logging, monitoring, and reporting
Traffic logs. Threat logs. URL logs. HIP logs if applicable. Knowing where to check session details when something's wrong. Also how to filter effectively, because scrolling is not troubleshooting no matter what your junior admin thinks.
Troubleshooting and operations (CLI/WebUI workflows)
This domain is where theory-only folks get absolutely smoked during the exam. Session table checks. Packet captures. Log correlation. Commit errors. Basic CLI commands you'd use under pressure when management's breathing down your neck. You don't need to memorize every command's syntax. You need to know the moves that actually solve problems.
Panorama and centralized management (as applicable)
Device groups, templates, commits versus pushes, policy inheritance, and where objects live in the hierarchy. Panorama is its own mindset entirely, and the exam expects you to have at least basic competence even if you've been avoiding it.
PCNSE Prerequisites and Recommended Experience
This is the part everyone wants straight answers on, because nobody wants to waste an exam fee and feel stupid. PCNSE prerequisites are less about "what Palo Alto allows" and more about "what reality requires to actually pass."
Official prerequisites (if any) vs. recommended background
Officially, there are no mandatory prerequisites to register and attempt the PCNSE PAN-OS 11.0 exam. Zero. No prior cert required. No training completion gate. You can book it today if you want and have the budget.
Practically though? Passing is a completely different story. Palo Alto Networks recommends the Firewall Essentials: Configuration and Management (EDU-210) course pretty strongly. It's a solid baseline and it gets you speaking PAN-OS fluently instead of guessing. They also suggest Panorama: Managing Firewalls at Scale (EDU-220) if your exam prep includes centralized management topics, and it should, because Panorama questions aren't rare and they're definitely not "free points" you can skip studying.
Prior completion of Palo Alto training or equivalent experience matters more than people admit publicly. Not because the course is magical. But because it forces you through the workflow muscle memory: build zones, attach profiles, read logs, fix what you broke, repeat until it's automatic.
Hands-on experience expectations (PAN-OS and NGFW operations)
Here's my take: hands-on experience can't be substituted with theory alone for this practical certification. Period. You can read docs for a month straight and still freeze when a question asks what you'd check first, because you've never actually followed the breadcrumb trail inside Monitor, Traffic, ACC, session browser, and packet capture under real pressure.
A realistic bar for "I'm ready"? Something like this. You've configured security and NAT policies from scratch. You've done at least one VPN type end to end. You've attached and tuned security profiles without just copying examples. You've troubleshot a few real outages or lab breakages where you didn't immediately know the answer. You've spent time in Panorama if your environment uses it. Not years of experience. But enough reps that you stop guessing blindly.
This is why understanding official requirements versus practical experience needed for exam success matters so much. The registration page won't warn you about this gap. Your score report will.
Best Study Materials for PCNSE PAN-OS 11.0
Proper preparation foundation increases first-attempt pass rates and reduces study time dramatically. That's not motivational poster stuff. It's just math: fewer gaps means fewer rabbit holes means less wasted time relearning fundamentals.
Official Palo Alto Networks training courses
EDU-210 is the cleanest starting point if you're new-ish to PAN-OS. EDU-220 is worth it if Panorama is part of your job or you keep dodging it hoping it'll go away. If you can't take the classes due to budget or time, replicate the outline with labs and the admin guides systematically.
Official documentation and admin guides (PAN-OS 11)
The PAN-OS 11 admin docs are where the exam writers actually live and pull material. Focus on features that show up in the objectives: policy, NAT, decryption, profiles, VPN, HA, logging, and operations workflows. Don't read every page like a novel. Pick what you can test in a lab the same day and make it stick.
Lab options (hardware, VM-Series, cloud, or virtual labs)
A home lab can be physical hardware if you have it collecting dust, but VM-Series or vendor-provided virtual labs are usually easier and cheaper. Cloud works too if you're comfortable with network plumbing and don't mind the billing. The key is repetition with variation: build, break, fix, document what happened.
Other options exist. Community labs. Work dev environments. Partner sandboxes. Mentioning them because someone will ask in the comments.
Study plan (2 to 6 weeks / 6 to 12 weeks options)
If you already run PAN-OS at work daily, 2 to 6 weeks is realistic: align to objectives, lab weak spots hard, take targeted PCNSE practice tests, then loop back to labs for every single miss. If you're learning PAN-OS from near-zero, 6 to 12 weeks is more sane and less stressful, because you need time for basic networking plus firewall behavior to click naturally.
Building prerequisite knowledge through structured learning paths saves you from panic-studying random YouTube playlists at midnight three days before your exam.
PCNSE Practice Tests and Exam Prep Strategy
Practice tests are useful tools. Also dangerous traps.
Practice tests: how to choose high-quality sets
High-quality PCNSE practice tests explain why an answer is right and why the others are wrong specifically, and they reference docs or behaviors you can reproduce in a lab. Low-quality sets feel like trivia dumps and push you into memorization mode without understanding. If the questions look nothing like the PCNSE exam objectives or feel weirdly disconnected, toss them immediately.
What to measure: readiness checklist by objective
Measure readiness by domain separately. Can you configure it. Can you troubleshoot it. Can you explain it without hand-waving or "I think maybe." Realistic self-assessment of skills prevents premature exam attempts and wasted resources, especially when you're paying out of pocket or burning limited company training budget.
Common weak areas and how to fix them
NAT plus security policy order? Classic weak spot that kills people. Decryption is another, mostly because people avoid it in production until they're forced by compliance or an incident. Fix it by doing tiny focused labs: one app, one rule, one profile, one expected log outcome, then change one variable and observe what breaks.
Panorama confusion is common too. Templates versus device groups. Commit versus push. Where objects live and inherit. Build a lab with one firewall and Panorama and practice "where do I change this" until it stops being annoying guesswork.
Final-week revision plan
Final week is not for "new chapters" or panic-learning features you ignored. It's for tightening what you know. Re-read objectives, redo labs you struggled with, and do timed question sets without pausing or Googling. Sleep properly. Seriously, sleep matters.
PCNSE Renewal and Recertification
Renewal cycle and validity (what to verify)
For PCNSE renewal policy, always verify on the official certification page because vendors adjust rules and timelines more often than you'd expect. Don't trust old blog posts, including mine from five minutes ago if Palo Alto updates the program tomorrow morning.
Recertification options (retake vs. higher-level/updated exams)
Usually you renew by retaking the current PCNSE or passing a newer or higher exam that refreshes the status automatically, depending on program rules at the time you're reading this. If PAN-OS versions shift dramatically, your best move is aligning to the newest blueprint and treating it like a skills refresh, not a checkbox exercise.
Keeping skills current with PAN-OS releases
PAN-OS changes constantly. Features move around. Defaults change silently. Keep a small "release notes habit" and rebuild a couple of labs when a new version drops, even if you're not upgrading production immediately. That's how you stay employable long-term, not just certified temporarily.
FAQs About PCNSE PAN-OS 11.0
Is PCNSE worth it for firewall engineers?
If you touch Palo Alto firewalls at work regularly, yes absolutely. It's recognized widely, and it maps to real tasks that matter. If you never touch PAN-OS and don't plan to, it's harder to justify unless you're targeting a role that will require it specifically.
How long should I study for PCNSE?
Two tracks here. Experienced admins can do 2 to 6 weeks if focused. Newer folks should plan 6 to 12 weeks minimum. Your lab time matters more than your reading time.
Can I pass PCNSE without real firewall experience?
You can pass without production experience if your lab work is serious and you actually troubleshoot failures, not just follow steps robotically. But without any hands-on at all? Odds drop fast. This exam punishes guessing harder than most.
What score do I need to pass PCNSE?
The vendor doesn't always present a simple universal number publicly, so treat PCNSE passing score as "you must be solid across objectives consistently." Confirm current scoring guidance on the official exam page before test day or you're flying blind.
What's the best way to use practice exams without memorizing answers?
Use them like diagnostics for weak spots. After every practice set, recreate the topic in a lab and prove the behavior yourself. If you can't reproduce it independently, you didn't learn it properly. You just recognized it temporarily. That's the trap everyone falls into.
Conclusion
So is PCNSE PAN-OS 11.0 actually worth your time?
Okay, real talk here.
The Palo Alto Networks PCNSE exam isn't something you knock out in a weekend with a bunch of brain dumps and hope. I mean, you could try, but you'd be setting yourself up for a pretty embarrassing fail that'll cost you another couple hundred bucks and a bruised ego. It's a serious certification that validates real skills on next-generation firewall operations, and honestly that's what makes it valuable in the first place. That and the fact hiring managers actually recognize it when they're scanning resumes for NGFW talent. If you're working with Palo Alto firewalls or you wanna break into roles that involve NGFW engineering, this cert opens doors that CompTIA or generic vendor-neutral credentials just don't.
The PCNSE exam cost runs around $200-$225 depending on your region. You need that 70% PCNSE passing score to walk away certified, which is fair considering what you're proving here: deployment skills, policy management, threat prevention configuration, VPN setup, HA concepts, Panorama centralized management. All the stuff that separates someone who clicked through a GUI once from an engineer who actually knows what App-ID and Content-ID are doing under the hood. The exam objectives for PAN-OS 11.0 are full. You get everything from initial interface configuration and routing to decryption policies and troubleshooting workflows in both CLI and WebUI.
The renewal policy keeps you sharp too. You've gotta recertify every two years, which sounds annoying but actually forces you to stay current as Palo Alto releases new PAN-OS versions with features you'll be expected to deploy. The Palo Alto Networks certification path doesn't end here either. You can stack credentials and specialize further once you nail the PCNSE.
I knew a guy who let his PCNSE lapse for three years and had to basically start over. He said the exam had changed so much he felt like a beginner again. Not ideal when you're trying to prove expertise.
Your next move: practice like you mean it
Here's the thing.
About PCNSE exam preparation resources, I mean. Official training's great, documentation's essential, lab time's non-negotiable, but practice tests are where you find out if you're actually ready or just think you are because you watched some videos and felt confident. You need quality questions that mirror the exam's scenario-based format, not just keyword matching garbage that teaches you nothing except how to waste time.
Before you schedule that exam, grab the PCNSE Practice Exam Questions Pack and run through it like it's the real deal. Time yourself. Note which PCNSE exam objectives trip you up, then go back to your lab and fix those gaps with actual firewall config work, not just re-reading the same study guide section for the fourth time hoping it'll magically click. That's how you pass without retakes and without that sinking feeling halfway through when you realize you memorized facts but can't apply them.
The PCNSE PAN-OS 11.0 certification proves you know your stuff.
Go earn it properly.
Show less info
Hot Exams
Related Exams
Palo Alto Networks Systems Engineer (PSE) - Strata Associate
Palo Alto Networks Certified Network Security Administrator (PAN-OS 10.0)
Palo Alto Networks Certified Network Security Consultant
Palo Alto Networks System Engineer Professional - Strata Data Center
Palo Alto Networks System Engineer - Cortex Professional
Prisma Certified Cloud Security Engineer
Palo Alto Networks Certified Security Automation Engineer
Palo Alto Networks System Engineer Professional - Strata
Palo Alto Networks Certified Detection and Remediation Analyst
PSE: Endpoint Associate training for Traps 4.0
Palo Alto Networks Certified Security Engineer (PCNSE) PAN-OS 11.0
Palo Alto Networks Certified Cybersecurity Entry-level Technician
Palo Alto Networks Certified Cybersecurity Associate
PSE Palo Alto Networks System Engineer Professional - Prisma Cloud
Palo Alto Networks Network Security Professional
Palo Alto Networks System Engineer Professional - SASE Exam
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.