CKS Practice Exam - Certified Kubernetes Security Specialist (CKS)
Reliable Study Materials & Testing Engine for CKS Exam Success!
Exam Code: CKS
Exam Name: Certified Kubernetes Security Specialist (CKS)
Certification Provider: Linux Foundation
Corresponding Certifications: Kubernetes Security Specialist , Kubernetes System Administration

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
CKS: Certified Kubernetes Security Specialist (CKS) Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 48 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena Linux Foundation Certified Kubernetes Security Specialist (CKS) (CKS) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
Linux Foundation CKS Exam FAQs
Introduction of Linux Foundation CKS Exam!
The Linux Foundation Certified Kubernetes Security Specialist (CKS) exam is a performance-based certification exam that tests a candidate's ability to secure a Kubernetes cluster and the applications running on it. The exam covers topics such as authentication, authorization, network security, image security, and more.
What is the Duration of Linux Foundation CKS Exam?
The Linux Foundation Certified SysAdmin (CKS) exam is a two-hour, multiple-choice exam.
What are the Number of Questions Asked in Linux Foundation CKS Exam?
The Linux Foundation Certified Kubernetes Administrator (CKA) exam consists of a total of 24 questions.
What is the Passing Score for Linux Foundation CKS Exam?
The passing score required for the Linux Foundation Certified Kubernetes Security Specialist (CKS) exam is 70%.
What is the Competency Level required for Linux Foundation CKS Exam?
The Competency Level required for the Linux Foundation Certified Kubernetes Security Specialist (CKS) exam is Experienced. This certification is designed for those who have at least one year of hands-on experience with Kubernetes security.
What is the Question Format of Linux Foundation CKS Exam?
The Linux Foundation Certified Kubernetes Administrator (CKA) exam consists of performance-based items that require you to solve a given problem in a command-line environment. The exam consists of twenty-four (24) performance-based tasks that must be completed within three (3) hours. Each task will have a specific set of requirements that must be met.
How Can You Take Linux Foundation CKS Exam?
The Linux Foundation Certified System Administrator (CKS) exam can be taken online or at a testing center. To take the exam online, you must register with the Linux Foundation and purchase an exam voucher. Once you have your voucher, you can schedule your exam and take it at your convenience. To take the exam at a testing center, you must register for the exam with a testing center and pay the associated fees.
What Language Linux Foundation CKS Exam is Offered?
The Linux Foundation Certified SysAdmin (LFCS) exam is offered in English.
What is the Cost of Linux Foundation CKS Exam?
The Linux Foundation Certified Kubernetes Administrator (CKA) exam currently costs $300 USD.
What is the Target Audience of Linux Foundation CKS Exam?
The target audience of the Linux Foundation Certified Kubernetes Security Specialist (CKS) exam is system administrators, DevOps engineers, and other IT professionals who are responsible for the security of Kubernetes clusters.
What is the Average Salary of Linux Foundation CKS Certified in the Market?
The average salary for a Linux Foundation Certified System Administrator is $98,000 per year in the United States.
Who are the Testing Providers of Linux Foundation CKS Exam?
The Linux Foundation does not provide testing for the CKS exam. The exam is administered by the Linux Professional Institute (LPI) and can be taken at an LPI-approved testing center.
What is the Recommended Experience for Linux Foundation CKS Exam?
The Linux Foundation recommends that individuals taking the CKS exam have at least three years of experience working with Linux systems, including experience with command line tools and shell scripting. Additionally, it is recommended that individuals have a solid understanding of Linux system administration, network management, security, and system operations.
What are the Prerequisites of Linux Foundation CKS Exam?
The Prerequisite for Linux Foundation Certified Kubernetes Security Specialist (CKS) Exam is that you must have a valid Certified Kubernetes Administrator (CKA) certification.
What is the Expected Retirement Date of Linux Foundation CKS Exam?
The Linux Foundation does not provide an online website to check the expected retirement date of the CKS exam. You can contact the Linux Foundation directly for more information.
What is the Difficulty Level of Linux Foundation CKS Exam?
The Linux Foundation Certified System Administrator (CKS) exam is a challenging exam with a difficulty level of intermediate to advanced. It is designed to test a candidate's knowledge of Linux system administration and the ability to troubleshoot and solve problems.
What is the Roadmap / Track of Linux Foundation CKS Exam?
The Certification Track/Roadmap Linux Foundation CKS Exam is a certification program offered by the Linux Foundation. It is designed to help IT professionals gain skills and knowledge in the areas of Linux system administration, network administration, and security. The exam covers topics such as system administration, network administration, and security. It also includes hands-on labs and exercises to help test-takers apply their knowledge. Upon successful completion of the exam, the test-taker will receive a Linux Foundation Certified System Administrator (CKS) certification.
What are the Topics Linux Foundation CKS Exam Covers?
The Linux Foundation Certified System Administrator (CKS) exam covers a wide range of topics related to administering Linux systems. These topics include system architecture, system installation, system configuration, system management, system security, network administration, system troubleshooting, scripting, and automation.
System Architecture: This topic covers the basics of Linux system architecture, including kernel, user space, system libraries, and system tools. It also covers the structure of the Linux file system, as well as the different types of hardware and software components used in a Linux system.
System Installation: This topic covers the process of installing the Linux operating system, including partitioning, file system creation, and package installation. It also covers the basics of booting and shutting down a Linux system.
System Configuration: This topic covers the basics of configuring a Linux system, including setting up user accounts, configuring system services, and managing system resources.
System Management: This topic covers the basics of managing
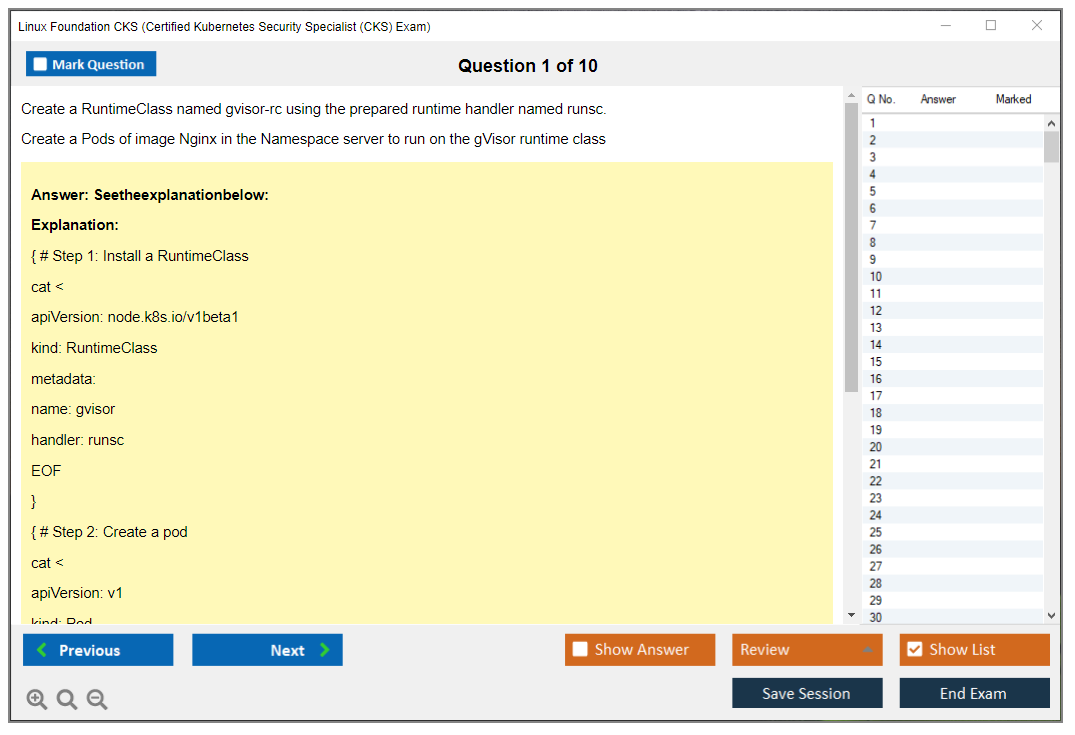
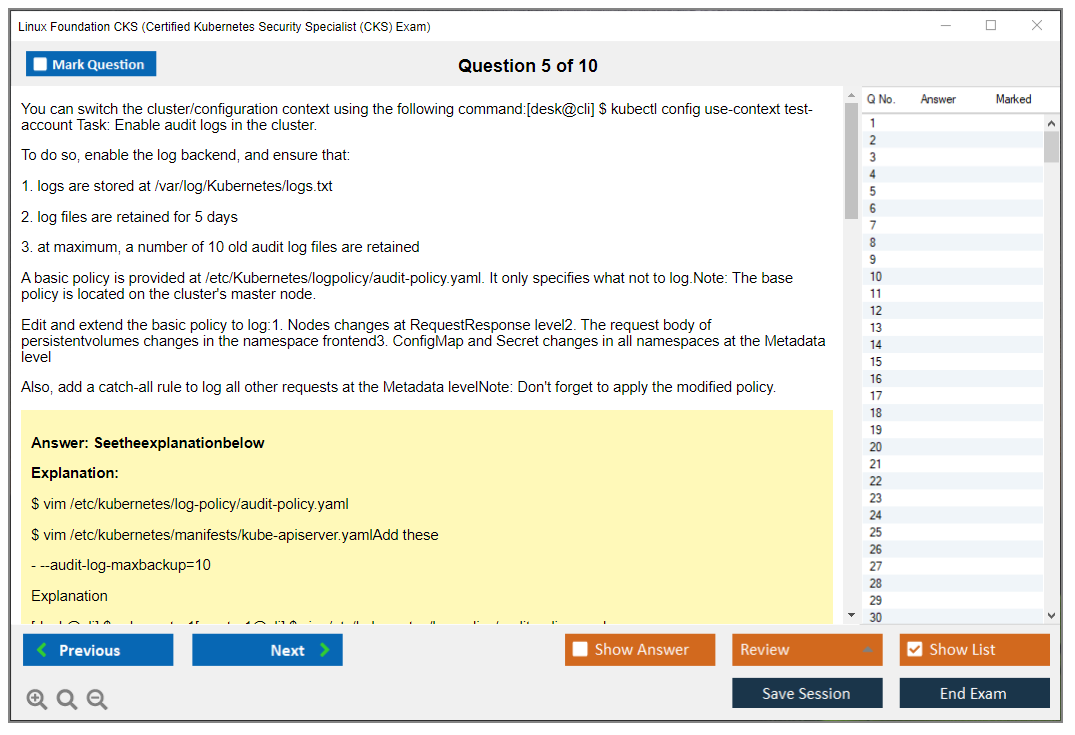
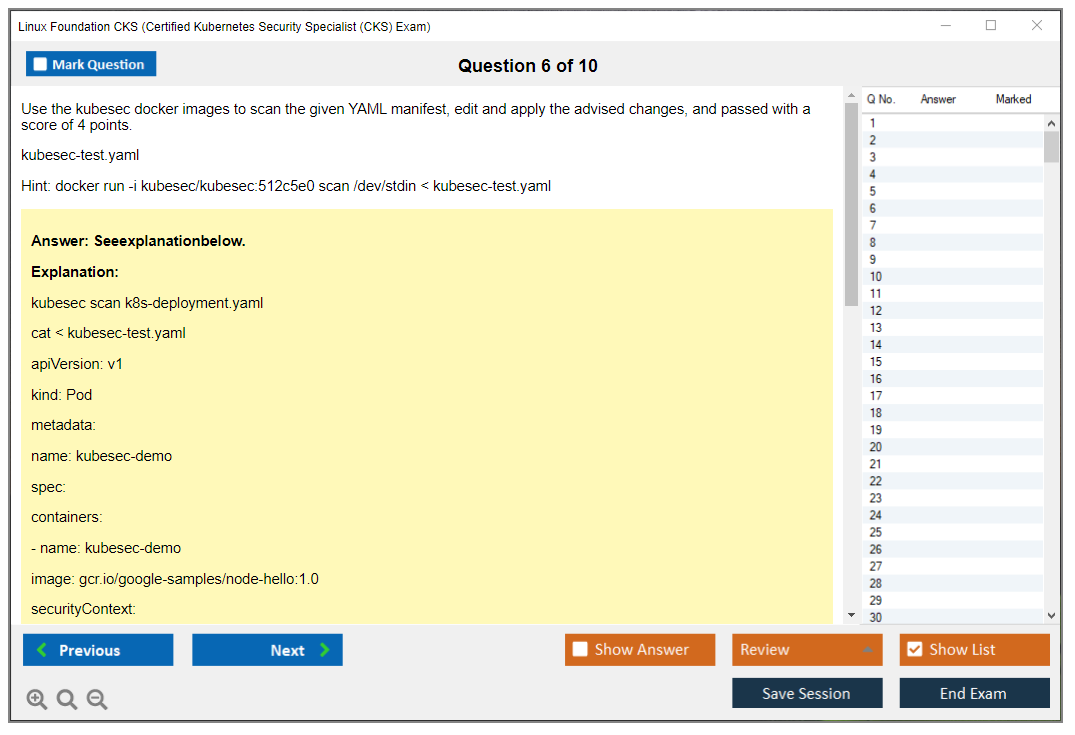
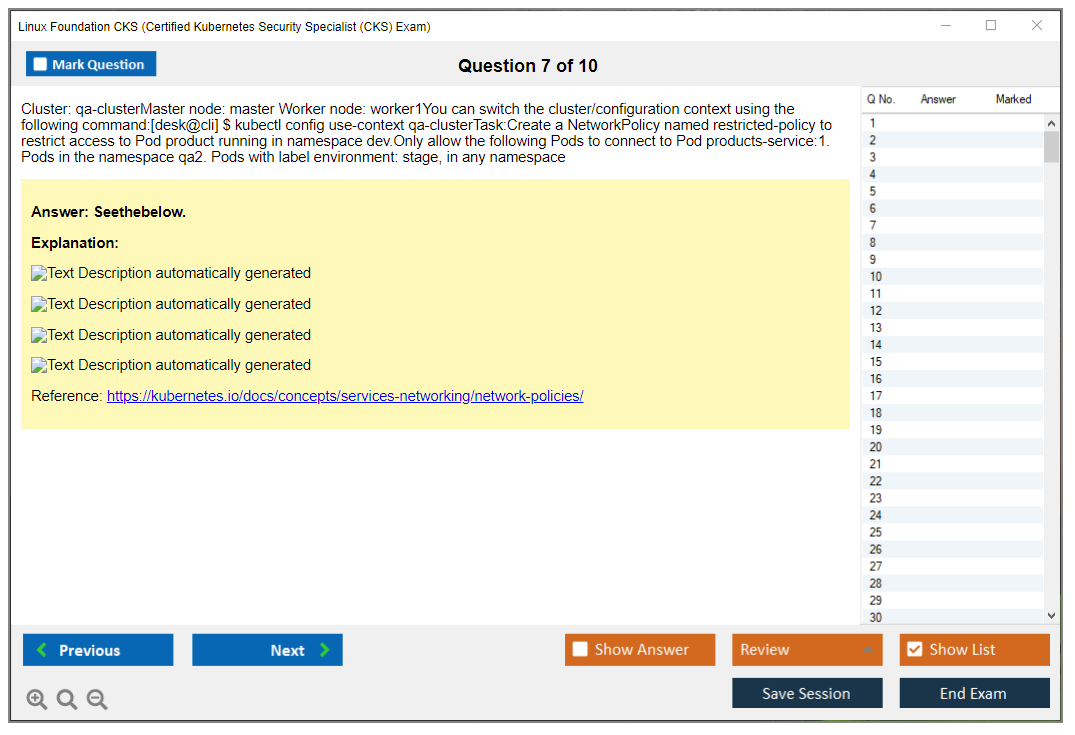
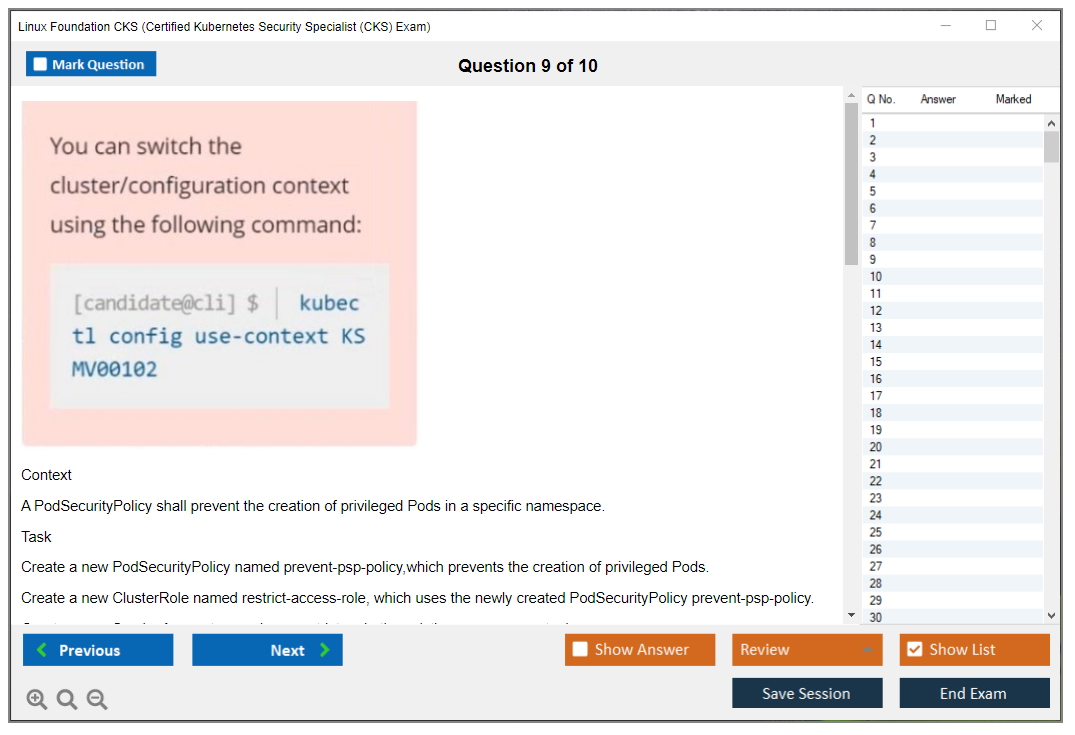
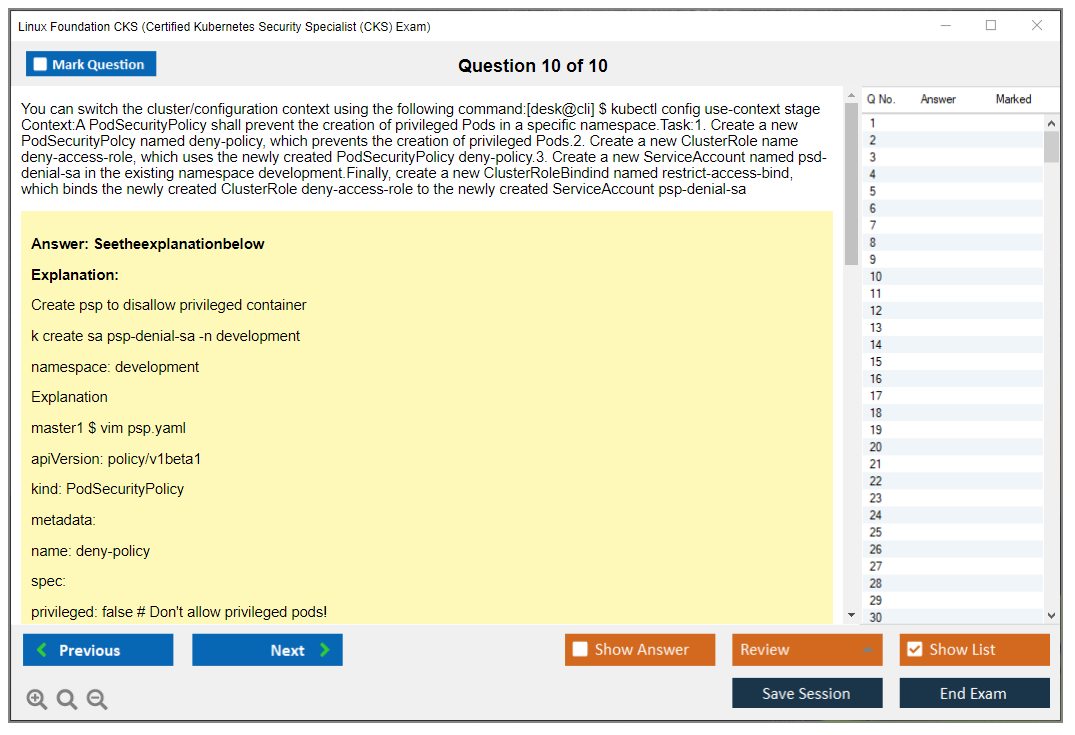
What are the Sample Questions of Linux Foundation CKS Exam?
1. What is the purpose of the Linux Foundation Certified System Administrator (CKS) program?
2. What are the requirements for taking the Linux Foundation CKS exam?
3. What topics are covered in the Linux Foundation CKS exam?
4. How is the Linux Foundation CKS exam administered?
5. What are the benefits of becoming a Linux Foundation Certified System Administrator?
6. What are the best practices for preparing for the Linux Foundation CKS exam?
7. What are the different types of questions on the Linux Foundation CKS exam?
8. What is the passing score for the Linux Foundation CKS exam?
9. What resources are available to help with preparing for the Linux Foundation CKS exam?
10. How often is the Linux Foundation CKS exam updated?
Linux Foundation CKS (Certified Kubernetes Security Specialist (CKS)) What is the Linux Foundation CKS Certification? What is the Linux Foundation CKS certification? The Certified Kubernetes Security Specialist (CKS) is an advanced, performance-based certification offered by the Linux Foundation and Cloud Native Computing Foundation (CNCF). This isn't your typical multiple-choice test where you're just guessing your way through security concepts. It's way more demanding than that. It's a hands-on Kubernetes security lab exam where you actually configure security controls, harden clusters, and detect threats in real time, dealing with the same messy scenarios you'd encounter when production environments are under attack. CKS validates hands-on skills in securing container-based applications and Kubernetes security certification platforms throughout the development lifecycle. If you're already comfortable managing Kubernetes clusters and want to prove you can lock them down properly,... Read More
Linux Foundation CKS (Certified Kubernetes Security Specialist (CKS))
What is the Linux Foundation CKS Certification?
What is the Linux Foundation CKS certification?
The Certified Kubernetes Security Specialist (CKS) is an advanced, performance-based certification offered by the Linux Foundation and Cloud Native Computing Foundation (CNCF). This isn't your typical multiple-choice test where you're just guessing your way through security concepts. It's way more demanding than that. It's a hands-on Kubernetes security lab exam where you actually configure security controls, harden clusters, and detect threats in real time, dealing with the same messy scenarios you'd encounter when production environments are under attack.
CKS validates hands-on skills in securing container-based applications and Kubernetes security certification platforms throughout the development lifecycle. If you're already comfortable managing Kubernetes clusters and want to prove you can lock them down properly, this is your path. No shortcuts. The certification focuses on security aspects of Kubernetes clusters, from hardening configurations to runtime threat detection. Not just surface-level checkbox security.
This Linux Foundation security exam differs from CKA (Certified Kubernetes Administrator) and CKAD (Certified Kubernetes Application Developer) by concentrating on security domains rather than general administration or development. CKA covers broad cluster operations. CKAD focuses on application deployment. CKS dives deep into threat models, attack surfaces, and defense tactics specific to containerized environments. You need CKA before you can even attempt CKS, which tells you something about the expected skill level. They're not messing around with prerequisites.
The certification proves your ability to reduce vulnerabilities in Kubernetes environments, implement security best practices, and respond to security incidents. Enterprises adopting Kubernetes for production workloads are desperate for security-conscious infrastructure teams, and CKS is recognized globally as the standard for proving you actually know what you're doing with container security. Not just theory from a textbook.
Who should take CKS?
Security engineers are the obvious candidates. DevSecOps practitioners too. But platform engineers and cloud architects responsible for securing production clusters benefit from the validation CKS provides. I mean, if you're designing the infrastructure, you better understand the security implications, right?
Site reliability engineers (SREs) managing secure, compliant Kubernetes infrastructure benefit from CKS validation because they're often the ones on call when something goes wrong. And security incidents do go wrong. Security consultants advising organizations on Kubernetes deployments gain immediate credibility through this certification, since clients want proof you've actually configured RBAC and network policies under pressure, not just read about them in documentation.
DevOps engineers transitioning to security-focused roles find CKS necessary for career advancement. Cloud security specialists working with container orchestration platforms need CKS to validate container-specific security knowledge that traditional security certs don't cover. The skills gap between understanding firewalls and understanding pod security admission is massive, and CKS bridges that gap in ways generic certifications can't. Once you've dealt with legacy Windows firewall rules for years, jumping into Kubernetes network policies feels like learning a different language entirely, even though the underlying concepts overlap more than you'd think.
What skills the CKS validates (Kubernetes security in practice)
The exam tests real-world scenarios including cluster hardening, system hardening, supply chain security, monitoring, and runtime security. You'll implement cluster hardening techniques such as API server security, RBAC configuration, and network policy enforcement. Actually writing policies and verifying they work, not just describing them.
System hardening capabilities include host operating system security, reducing attack surfaces, and securing container runtimes. This gets technical fast. Candidates must demonstrate proficiency with security tools like Falco, AppArmor, seccomp, and native Kubernetes security features. Container runtime security (Falco/AppArmor/seccomp) implementation means you're detecting and preventing malicious behavior at runtime, not just hoping your static scans caught everything beforehand.
kubectl security hardening proficiency covers securing workloads through security contexts, pod security standards, and admission controllers. Supply chain security skills involve image scanning, signing, and secure software delivery pipelines. Basically making sure nobody sneaks compromised containers into your cluster without you knowing.
Network security through NetworkPolicies matters because default Kubernetes networking is wide open, which is terrifying. You need to configure ingress and egress controls, understand service mesh security, and actually test that your policies work in realistic scenarios. Secrets management using Kubernetes Secrets, encryption at rest, and external secret management integration is critical since hardcoded credentials are everywhere in real environments. I mean everywhere.
Monitoring and logging configuration for security event detection, audit logging, and forensic analysis means setting up the observability you'll need when (not if) something suspicious happens. Vulnerability assessment and remediation workflows for containers and Kubernetes components round out the practical skills you're expected to demonstrate. Incident response procedures specific to containerized environments prepare you for the chaos of actual security breaches in production Kubernetes clusters, which can be pretty overwhelming without proper training.
CKS Exam Overview
What is the Linux Foundation Certified Kubernetes Security Specialist (CKS) certification?
The Certified Kubernetes Security Specialist (CKS) is the Linux Foundation's Kubernetes security certification, aimed at people who already run clusters and now need to lock them down without breaking production. It's a Kubernetes security certification that cares about what you can actually do at a terminal, not what you can recall from flashcards.
Who should take it? Platform engineers, SREs, DevSecOps folks, and Kubernetes admins who get pulled into "why did this pod get compromised" calls. It's also for anyone who already has CKA (Certified Kubernetes Administrator (CKA) Program) and wants a security-focused next step without switching tracks entirely, which makes sense if you're already neck-deep in K8s work.
This cert validates practical skills like RBAC cleanup, network policy work, pod security controls, image and supply chain checks, and container runtime security (Falco/AppArmor/seccomp). The kind of stuff you only learn by breaking a few clusters in a lab first. I've watched people try to shortcut this part, and it never works out well for them.
CKS exam overview
Exam format (performance-based, hands-on)
The CKS exam is performance-based and hands-on. That's the whole point and the main reason people respect it.
There aren't any multiple-choice questions at all, so you don't get to "recognize" the right answer. You've gotta produce it, verify it, and move on while the clock keeps ticking down.
You'll be dropped into a hands-on Kubernetes security lab exam where you get access to multiple pre-configured Kubernetes clusters, and every task is done through terminal access with real Kubernetes objects that behave like production workloads. It feels like a mini on-call shift: you read a requirement, you inspect what's deployed, you change YAML, you apply a policy, you confirm the expected outcome. You don't get points for good intentions or "almost there" attempts.
Tasks typically include configuring security features, troubleshooting security issues, implementing policies, and hardening systems. That can mean kubectl security hardening work like tightening RBAC, updating service accounts, or restricting permissions. It can also mean checking runtime configurations or hunting down why a workload violates a security control that someone implemented three sprints ago. Some tasks are very "do X", others are "something's wrong, fix it", and those are the ones that eat time if your workflow's sloppy or you second-guess yourself.
You can use official Kubernetes docs during the exam. That mirrors real work conditions, because nobody memorizes every flag forever. But if you rely on docs for basic syntax, you'll burn minutes fast, and 120 minutes isn't generous by any stretch.
Scoring's objective-based. Each task states requirements and expected outcomes, and the environment has verification baked in. You get points for completing objectives, and partial credit's possible for partially completed work, so it's worth leaving something half-done rather than staring at it for 20 minutes in stubborn silence while other points slip away.
Time limit and environment (Linux, Kubernetes CLI)
You get 2 hours.
That's it.
120 minutes means time management is a skill being tested right alongside security knowledge. Quick decision-making matters because you won't finish by being "careful" on every single item like you're defusing a bomb or something.
The environment is Ubuntu Linux in a browser-based terminal. No GUI, no IDE, just you, the shell, and your ability to move quickly with grep, find, and a text editor like vim or nano. Fragments of commands. Muscle memory. This is where people with solid Linux habits quietly win without breaking a sweat. I once saw someone spend eight minutes trying to exit vim, which is funny until it's your exam time disappearing.
You'll likely see multiple Kubernetes clusters, sometimes on different versions, and you'll need to context switch with kubectl without getting lost in which cluster you're even touching. kubectl is the primary tool, with other utilities showing up depending on tasks, like crictl, etcdctl, and sometimes security scanners that you may or may not have touched before. Copy-paste exists, but it can be finicky, so assume you'll type more than you want.
Remote proctoring requirements
The Linux Foundation security exam delivery is proctored through PSI Secure Browser. Expect strict rules: government-issued photo ID, webcam on the whole time, and a private well-lit room with a clear desk that looks like nobody actually works there.
Only one monitor's allowed. Dual screens? Nope. No headphones, no phone within reach, no smartwatch, no random notes taped to the wall like you're in A Beautiful Mind. You'll do a room scan before the exam starts, and the proctor can message you via chat and pause your session if something looks off or suspicious.
Bathroom breaks are allowed, but the timer keeps running, so plan accordingly.
Tech requirements matter more than people admit. Stable internet (think 5 Mbps minimum), working webcam/mic, and you should run PSI's compatibility check before exam day because troubleshooting proctoring software at T-minus 3 minutes is a bad time for everyone involved.
CKS exam cost
People always ask about CKS exam cost.
Pricing changes, but it typically sits in the few-hundred-dollar range and often includes one retake within a window, depending on what bundle or promo you buy. Sometimes training's packaged with it, sometimes not, it varies.
Discounts happen. Vouchers show up. Employer reimbursement is common if you can explain why your cluster risk goes down when you pass. Make the business case: fewer incidents, better controls, cleaner audits, less time spent putting out fires.
CKS passing score
CKS passing score is set by the Linux Foundation and is expressed as a percentage threshold that you'll either hit or you won't. The key detail is how you earn it: task-based points from completing objectives in the live environment, with partial credit on some items if you got halfway there.
If you fail, you use your retake (if included) and you come back smarter, more focused. No shame. But do review what domains you bled time on, because the exam punishes slow troubleshooting more than "not knowing" outright.
CKS exam difficulty (honest assessment)
CKS exam difficulty is real.
Time pressure plus troubleshooting plus security-specific details is a rough combo, and it's harder than CKAD (Certified Kubernetes Application Developer (CKAD) Program) for most people. Usually feels more stressful than CKA too, especially when you're 90 minutes in and realize you've got four tasks left.
Common failure points? RBAC that looks right but isn't, network policies that accidentally block DNS and everything breaks, and runtime controls like container runtime security (Falco/AppArmor/seccomp) where one wrong profile or path breaks the requirement in ways that aren't immediately obvious. Also, context switching mistakes. So painful.
CKS prerequisites and objectives
CKS prerequisites include having a valid CKA.
Full stop.
If you're earlier in your path, look at KCNA (Kubernetes and Cloud Native Associate (KCNA)) or LFCS (Linux Foundation Certified System Administrator) first, then circle back when you've got the foundation skills locked in.
CKS exam objectives cover cluster setup and hardening, system hardening, minimizing microservice vulnerabilities, supply chain security, and monitoring/logging/runtime security that actually catches threats. In practice, that maps to tasks like admission control configs, PSP replacements, secrets handling, image policy checks, and verifying everything actually works after you "secure" it. Because securing something that then breaks prod is not a win.
CKS study materials, practice tests, and renewal
Good CKS study materials are labs first, notes second, theory maybe third. Docs familiarity matters. Timed drills matter more. For CKS practice tests, you want mock scenarios on real clusters, not quizzes that test your ability to recognize definitions.
CKS certification renewal follows Linux Foundation recert rules and validity windows, so check the current policy on the official page and set a calendar reminder. Or you'll forget. Everyone forgets, I've seen it happen.
If you want the official program page details and updates, keep CKS (Certified Kubernetes Security Specialist (CKS)) bookmarked.
CKS Exam Cost and Pricing Details
Current price range and what's included
$395 USD.
That's the CKS exam cost for a single attempt as of 2026. Not gonna lie, it's a chunk of change. But here's what you're actually getting: one exam attempt you can schedule anytime within 12 months of purchase, which honestly gives you plenty of breathing room to actually prepare instead of cramming like some college all-nighter.
Look, if you bomb the exam (happens to the best of us), the retake option costs an additional $100. So you're looking at potentially $495 if you need that second shot, which stings, but at least you're not starting from scratch financially. The exam voucher stays valid for a full year from purchase date, meaning you control when you're ready instead of feeling rushed because some arbitrary deadline is breathing down your neck like a micromanaging project manager.
Now here's where it gets interesting.
Bundle packages exist that combine the exam with Linux Foundation training courses, and the math actually works out in your favor. The CKS + CKS Course Bundle typically runs around $695-$795. Includes video courses, hands-on labs, practice environments, and the exam voucher. Buying separately would cost you way more than that, so if you need structured training anyway, the bundle makes sense. Some bundle purchases even throw in one free retake, giving you two exam attempts without that extra $100 hit.
Once you pass? The certification stays valid for 3 years from your passing date. No annual maintenance fees. No recurring subscriptions. Just three years of being able to slap that CKS credential on your resume and LinkedIn profile.
Pricing occasionally varies by region with purchasing power parity adjustments for certain countries, though the $395 baseline remains standard for most buyers in North America and Europe.
Discounts, vouchers, and employer reimbursement tips
The Linux Foundation regularly offers promotional discounts during holidays, KubeCon events, and other special occasions. We're talking discount codes ranging from 20-40% off during Black Friday, Cyber Monday, and end-of-year sales. Honestly, if you're not in a rush, waiting for one of these sales can save you a hundred bucks or more. Maybe even closer to $150 if the stars align.
Newsletter subscribers receive exclusive discount codes and early notification of upcoming promotions. Sign up. Check your spam folder. Those codes show up and they're legit, not some phishing scam. I once missed a 35% discount code because it landed in my spam filter, and I'm still bitter about it.
Here's something most people don't think about until it's too late: employer reimbursement programs. Technology companies investing in employee skill development commonly cover certification costs when aligned with job responsibilities. Request reimbursement approval before purchasing, not after. Trust me on this one. Provide business justification tied to role requirements like "improving our cluster security posture" or "meeting compliance requirements for our Kubernetes infrastructure" or "boosting team capability for incident response." Document how the certification benefits the organization, not just your career trajectory.
Some employers purchase bulk vouchers at discounted rates for team certification initiatives. If you're leading a platform team or security group, pitching a group certification plan might get you better pricing than individual purchases, plus you look like a leader who invests in team growth. Conference attendance sometimes includes certification vouchers as part of registration packages, which is basically free money if you were attending anyway.
Training platforms occasionally bundle Linux Foundation vouchers with subscription packages. Group discounts become possible for organizations certifying multiple team members at once, though you'll need to contact Linux Foundation sales directly for those arrangements. It's not advertised on their main pricing page.
Student discounts? Not typically available for professional certifications like CKS, but academic programs may offer alternatives if you're currently enrolled somewhere. Tax deduction potential exists for self-employed professionals investing in career development, though you should definitely consult a tax advisor because I'm not giving tax advice here. That's above my pay grade.
Payment plans aren't offered directly through Linux Foundation, but your credit card might have installment options available through your financial institution. The thing is, consider the total cost of ownership when budgeting: exam fee, supplementary study materials beyond the official curriculum, practice exam platforms, lab environment subscriptions if you're not building your own. Budget somewhere between $500-$1000 total when accounting for exam, additional resources, and potential retake.
Look, if you're already working toward CKA or have it, the CKS becomes a natural progression. The prerequisite requirement means you're already invested in the Kubernetes certification path anyway. Just watch for those promotional periods and don't pay full price unless your employer's footing the bill or you absolutely need to test immediately for some job requirement.
CKS Passing Score and Scoring Mechanics
CKS passing score and scoring mechanics
The Certified Kubernetes Security Specialist (CKS) exam has a pretty clear bar. The CKS passing score is set at 67%. That's the minimum to earn the cert, and yes, it basically means you need to successfully finish about two-thirds of what the exam is trying to get you to do.
67% sounds simple. Honestly though? It's complicated.
In point terms, the minimum score required to pass translates to 67 out of 100 possible points across all domains. Not "67% of questions" like a multiple-choice test. Points. A task can be worth more, or less, depending on what it's testing and how long it should take, so your goal is "collect 67 points," not "complete 67 tasks." That passing threshold stays consistent across exam versions, even though the exact mix of tasks can shift around a bit.
Minimum score required to pass
Look, people get tripped up by the wording.
Your score is the percentage of total possible points earned, not the percentage of tasks you touched. If you complete 10 tasks but they were all low-value, you can still fail. If you nail a handful of chunky high-value items and scoop partial credit elsewhere, you can pass without "finishing everything." The thing is, I always tell folks to stop thinking like it's a classroom test and start thinking like it's a points game with a clock running. The mindset shift alone can save you from burning through precious minutes on tasks that won't move the needle enough to justify the time investment.
My old manager used to say the CKS felt more like triage than testing, and after you've watched enough people panic over a single misconfigured webhook for twenty minutes, you start to see his point.
Also, the exam doesn't care about your style. It cares about the end state.
How scoring works in a hands-on exam (task-based points)
This is a Linux Foundation security exam, meaning it's a performance-based, hands-on Kubernetes security lab exam. You're changing real cluster resources. You're writing YAML. You're running commands. You're fixing broken security stuff. And the scoring? Automated.
Each task has a specific point value tied to complexity, time requirements, and how important the security concept is. Some tasks are "quick wins" like tightening RBAC or locking down a pod spec. Others are longer, fiddlier things like policies and runtime controls, where one typo can burn five minutes and your confidence.
Scoring is typically done via verification scripts that check the cluster state against expected results. Final state is what matters, not the process you used to get there. You can solve something with kubectl, editing manifests, kustomize, whatever. Multiple approaches work as long as the final configuration meets the requirement. Documentation use doesn't change scoring either, so don't get weirdly proud about memorizing flags. Just ship the correct config.
Partial credit exists. I mean, it's one of the few "nice" parts of the exam. If you mostly complete a task but have a minor config error, you may still get some points, depending on what the checker validates. That said, incomplete tasks can still effectively be a zero if the check requires a specific outcome and you didn't produce it.
Time management? Real boss fight.
Spend 18 minutes stuck on one complex scenario and you might walk away with nothing, while you could've banked points by knocking out two smaller tasks and then coming back. Strategic task selection matters. Verification matters too. Run your own checks before moving on, like confirming an RBAC binding actually grants the intended verb or resource, or that a NetworkPolicy is selecting the right pods, or that your kubectl security hardening changes didn't break a namespace you still need.
Dependencies are another sneaky scoring thing. Some tasks build on earlier configs. If you skip a prerequisite, the dependent task might never validate, so you lose points twice. Frustrating. Common. Avoidable.
If you want realistic drills for this style of scoring, a pack like CKS Practice Exam Questions Pack is useful because you can practice the "read, implement, verify, move on" loop, not just memorize theory. It's not about trivia. It's about execution under pressure.
Task-based points across domains (where the points usually sit)
The exam spreads task-based points across five main domains with weights that usually look like this:
Cluster setup and hardening grabs about 10%. Quick mention, but don't ignore it.
System hardening takes about 15%. This is where Linux basics show up.
Minimize microservice vulnerabilities sits at roughly 20%, and it can be a time sink if you're slow with pod specs.
Supply chain security also lands around 20%. Image provenance, scanning, admission type thinking.
Monitoring, logging, and runtime security pulls about 20%, including stuff like container runtime security (Falco, AppArmor, seccomp).
The remaining percentage is basically extra security concepts and troubleshooting sprinkled across tasks. Not every version feels identical, but the overall distribution stays familiar if you've read the CKS exam objectives.
What happens if you fail (retake policy basics)
Failing isn't the end. It's annoying. That's it.
If you don't hit the CKS passing score (67%), you get a score report showing your overall percentage and performance by domain, which is actually helpful because it tells you where you bled points. Retakes depend on what you bought. Sometimes you have an included retake in a bundle, otherwise you purchase another attempt, which ties back to CKS exam cost and whether your employer reimburses it.
No mandatory waiting period, so you can reschedule as soon as there's availability. The retake version uses different tasks but tests the same objectives. I can't stress this enough: don't "study the questions," study the skills. This is where CKS Practice Exam Questions Pack can help again, because repeating timed labs builds the muscle memory that fixes speed, accuracy, and the whole "verify before you move on" habit.
Not gonna lie, that's the game. Score points. Don't chase perfection. Hit 67.
CKS Exam Difficulty - Honest Assessment
CKS exam difficulty, honestly, it's brutal
The CKS exam difficulty consistently gets rated among the most challenging Kubernetes certifications by candidates and industry professionals, and I'm not gonna sugarcoat it. This exam separates people who've actually secured production clusters from those who've just read about it. You're staring down two hours of intense hands-on work where every minute counts and mistakes compound fast.
I mean, look. I've talked to folks who breezed through CKA and felt pretty confident, then they hit CKS and got absolutely humbled. Hard.
Why candidates find CKS challenging
The difficulty stems from this nasty combination of time pressure, breadth of security topics, and troubleshooting complexity that honestly feels overwhelming until you've practiced enough. That two-hour time limit? Creates crushing pressure.
You need rapid problem identification, solution implementation, and verification. And verification takes way longer than you think when you're dealing with security controls.
Security domain breadth spans cluster hardening, system security, application security, supply chain, and runtime monitoring. Tasks require not just configuration knowledge but actual troubleshooting skills when security controls create unexpected behaviors. Real-world scenarios include debugging RBAC permission issues, investigating security policy violations, and remediating vulnerabilities. Basically everything that can go wrong in a production cluster, compressed into 120 minutes.
The thing is, you gotta balance speed with accuracy. Rushing leads to mistakes while perfectionism wastes precious time. I've seen people spend 15 minutes making one NetworkPolicy perfect when they should've moved on after 7 minutes with a working solution.
Documentation navigation skills matter more than most people realize. Knowing where to find specific security configuration examples saves minutes per task. Command-line efficiency? Not negotiable. Slow typing, unfamiliarity with vim, or inefficient kubectl usage consumes valuable time you simply don't have.
The multi-cluster environment requires constant context awareness and switching, adding cognitive load and error potential. Security tools like Falco, AppArmor, and seccomp have steep learning curves with syntax-sensitive configurations where one wrong character breaks everything. Actually, breaks is too gentle. One typo and you're toast.
Troubleshooting security-related issues is way more complex than functional problems due to less obvious error messages. A pod not starting because of AppArmor? Good luck figuring that out quickly if you haven't seen it before.
Difficulty vs CKA/CKAD (what's different)
The CKS exam difficulty exceeds both CKA and CKAD due to specialized security knowledge requirements and narrower, deeper focus. CKA focuses on cluster administration and general operational tasks with broader scope but less depth. CKAD emphasizes application deployment and development workflows from a developer perspective.
CKS assumes CKA-level knowledge as baseline, building advanced security practices on top of foundational administration skills. You already need to know how Kubernetes works. CKS isn't teaching you the basics.
Security concepts are inherently more complex than general administration, involving threat modeling and defense-in-depth strategies that require understanding attack vectors and mitigation techniques. You need to grasp security architecture decisions that go way beyond just following configuration steps. CKS candidates must understand not just how to configure features but why specific security controls matter in production environments facing real threats. Attack surface analysis, vulnerability assessment, and security trade-offs require higher-level thinking than configuration tasks.
Time pressure feels more intense in CKS because security tasks often involve multiple steps and verification requirements. Fewer candidates pass CKS on first attempt compared to CKA/CKAD, reflecting that elevated difficulty level. Not gonna lie, the pass rates speak for themselves.
Common failure points (RBAC, network policies, runtime security)
RBAC (Role-Based Access Control) complexity with Roles, ClusterRoles, RoleBindings, and ServiceAccount configurations trips many candidates up. Understanding RBAC verb permissions, resource scoping, and troubleshooting "forbidden" errors requires deep knowledge that goes beyond memorization. You can't just memorize your way through this stuff.
NetworkPolicy implementation? Serious challenges.
NetworkPolicy includes ingress/egress rule syntax, label selectors, and testing connectivity restrictions that can make your head spin. Candidates often struggle with NetworkPolicy debugging when pods cannot communicate as expected after policy application. Testing network policies under time pressure is stressful as hell.
Runtime security tools like Falco require understanding rule syntax, event detection, and integration with Kubernetes in ways that aren't immediately intuitive. AppArmor and seccomp profile creation and application to pods involves unfamiliar syntax and troubleshooting that feels foreign if you come from a purely containerization background. I remember spending an entire weekend just getting comfortable with AppArmor profiles, and that was outside the exam pressure cooker.
Admission controllers configuration presents real complexity, particularly webhook setup and policy enforcement. Image scanning and supply chain security tasks require familiarity with multiple tools and vulnerability assessment workflows.
Audit logging configuration and analysis demands understanding of audit policy rules and log interpretation. Secrets encryption at rest using KMS providers involves multiple configuration steps prone to errors. One misconfiguration and nothing works.
Pod Security Standards implementation replacing deprecated PodSecurityPolicies confuses candidates familiar with older approaches. The ecosystem moved on, and if your study materials are even slightly outdated, you're learning the wrong thing.
Honestly? The Certified Kubernetes Security Specialist (CKS) exam pushes you harder than most cloud certifications. It's designed to validate real capability under pressure, and that design works. If you pass, you've earned it.
CKS Prerequisites and Preparation Requirements
What is the Linux Foundation CKS certification?
Certified Kubernetes Security Specialist (CKS) is the Kubernetes security certification that actually makes you do the work. Not theory. Not multiple choice. You sit in a Linux terminal, inside a live cluster, and you harden things, lock things down, and fix insecure stuff fast enough to beat the clock.
Who should take it? Platform engineers, SREs, DevSecOps folks, and Kubernetes admins who already touch clusters and now get pulled into security reviews, incident follow-ups, or "why is this container running as root" arguments. Also anyone tired of being the person who says "we should add security" without knowing the exact kubectl and YAML to back it up.
What skills does it validate? Real kubectl security hardening, reading manifests under pressure, and container runtime security (Falco/AppArmor/seccomp) type tasks that show up in real environments, not lab-only fantasies. It's a Linux Foundation security exam, and yes, it feels like a hands-on Kubernetes security lab exam.
CKS exam overview
Performance-based exam. Terminal only. You get a set of tasks mapped to the CKS exam objectives, and scoring is basically task-based points. Some items are quick wins, some are time traps. The difference between passing and failing usually comes down to speed plus verification habits.
Time limit and environment: you're in a Linux CLI, using kubectl constantly, editing YAML by hand, and bouncing between logs, events, and component config files. Remote proctoring is part of the deal, so you need a quiet room, stable internet, and a machine that won't decide to update right then. Small stuff, but it can wreck your day.
CKS exam cost
CKS exam cost changes with promos, bundles, and regional pricing, so I'm not gonna pretend one number lasts forever. Expect a typical certification price range, sometimes with a retake included depending on current Linux Foundation policies. Look for vouchers, employer reimbursement, and team training budgets, because this is one of those certs companies actually pay for when your job touches clusters.
If you want extra drilling, a paid question pack can be helpful as long as it focuses on hands-on steps, not trivia. I've seen people pair their lab time with something like the CKS Practice Exam Questions Pack when they want more "prompt style" tasks to run through on a timer.
CKS passing score
CKS passing score is published by the Linux Foundation and has historically been 67%. Check the exam page before you schedule because policies can change, but that number is the one most candidates plan around.
How scoring works: tasks carry weights, and you don't need perfection on every item. Partial completion can still matter, but only if you verify what you changed actually works. If you fail, you follow the retake policy tied to your purchase or bundle. Not fun. Still normal.
CKS exam difficulty (honest assessment)
Real talk? CKS exam difficulty is no joke. Time pressure gets brutal, and the tasks are the kind where one wrong indentation or one missed namespace wastes minutes you don't have. Troubleshooting is constant. So is documentation searching, because memorizing every flag is a losing game.
Compared to CKA/CKAD, CKS is narrower but sharper. CKA proves you can run Kubernetes. CKS assumes you can, then asks you to secure it, which means you're touching RBAC, admission controls, network policies, secrets encryption, runtime monitoring, and supply chain checks while the clock yells at you.
Common failure points? RBAC from memory, NetworkPolicy logic, and runtime security setups. Also people underestimate how much Linux they need. Permissions. Processes. File edits. Basic stuff. Until it's 2 minutes left and you're staring at a permission denied error wondering if you forgot sudo or if AppArmor is blocking you or maybe both.
CKS prerequisites
CKS prerequisites have two layers: the mandatory cert dependency, and the experience you really need to not get wrecked by the exam.
Required prerequisite certification (CKA requirement)
This is the big one. CKS is unique among Kubernetes certifications because it has a formal dependency: you must hold a valid CKA (Certified Kubernetes Administrator) before you can even attempt it. No CKA, no CKS. No exceptions or waivers, even if you have ten years in security or other certs stacked up.
Your CKA must be current, not expired, at the time you schedule and complete the CKS exam. The Linux Foundation verifies your CKA status through their certification system before allowing CKS registration, so you can't "just book it and figure it out later." That prerequisite filters candidates. Honestly it's fair, because CKS assumes you already understand cluster architecture, networking, storage, and troubleshooting from CKA. That baseline is what makes the security material make sense, because security is usually "same thing, stricter," not a totally separate world.
If you don't have CKA yet, plan for extra time and cost. Training, practice, exam fee, maybe a retake. That's part of the CKS preparation math.
Recommended experience (clusters, Linux, containers)
Now the unofficial part. I mean, the paper prerequisite is CKA, but the practical prerequisite is real hands-on time.
I'd call 6 to 12 months of Kubernetes in production or production-like clusters the minimum where CKS feels doable, because you need instincts for what's normal, what's broken, and where to look first when a policy blocks traffic or a pod won't start after you tightened security contexts. The thing is, you can't fake that muscle memory under pressure. Deep Linux admin skills matter too: users/groups, permissions, file systems, processes, and logs. Containers matter beyond "docker build": know containerd and CRI-O basics, and have opinions about runtime risk. Network fundamentals are non-negotiable, because NetworkPolicy tasks are basically TCP/IP, DNS, and troubleshooting in Kubernetes clothing.
Also: bash and text processing. grep, awk, sed. Fast terminal navigation. YAML without an IDE. You will fat-finger things. You need to recover quickly.
Skills checklist before scheduling the exam
Quick gut check. If several of these feel shaky, delay scheduling and drill.
Can you configure RBAC (Roles, ClusterRoles, RoleBindings, ServiceAccounts) from memory? This one is pure time savings, because RBAC tasks tend to be multi-step, and you'll lose minutes if you're hunting syntax while also trying to reason about least privilege.
Are you comfortable creating NetworkPolicies with more involved ingress/egress rules? You need to read the question carefully, validate with a test pod, and confirm traffic behavior, because "looks right" isn't the same as "works."
Other items to be honest about: Pod Security Standards and admission controller config, audit logging policy rules, secrets encryption at rest with encryption providers, Falco rule syntax, AppArmor and seccomp profiles, image scanning workflows, TLS cert troubleshooting. Security contexts like runAsUser and capabilities. Fast docs navigation. Editing in vim or nano. Finishing typical security tasks in under 10 minutes, with verification.
If you want more timed prompts to rehearse that pace, the CKS Practice Exam Questions Pack can fit nicely alongside labs. Same idea if you're building your own mock exam: timer on, no IDE, verify everything. And if you're the type who needs structured repetition, looping the CKS Practice Exam Questions Pack a couple times can expose the gaps you didn't know you had.
CKS Exam Objectives and Security Domains
CKS exam objectives organized by security domains
The Certified Kubernetes Security Specialist (CKS) exam breaks down into five primary security domains that cover the complete Kubernetes security lifecycle. These aren't random topics. The Linux Foundation actually publishes a detailed exam blueprint that gives you percentage weights and specific subtopics for each domain, so you know exactly where to focus your study time. Though most people still waste hours on stuff that barely shows up.
The exam blueprint is your roadmap. Each domain carries different weight. Some are 10%, others hit 20%. Ignoring these percentages? Bad move. You'll burn time on low-value topics while missing critical areas that could've secured you five extra points.
Cluster Setup and Hardening domain basics
Cluster Setup and Hardening accounts for 10% of the exam and focuses on securing the Kubernetes control plane plus cluster-wide configurations. You're dealing with stuff like using CIS Benchmarks to harden cluster components, restricting API server access, and properly configuring authentication mechanisms. This domain also covers network security implementation using NetworkPolicies to restrict pod-to-pod communication and isolate workloads.
NetworkPolicies trip up tons of people because the YAML syntax feels backwards at first. Like you're defining what's allowed instead of what's blocked. Messes with your intuition if you're coming from traditional firewall configs.
You'll also work with Ingress objects, GUI tools for firewalls, service meshes sometimes. The point is controlling traffic flow at multiple layers. Exactly what real Kubernetes security certification demands you understand in practice.
System Hardening (15% weight)
System Hardening takes 15%. Goes beyond Kubernetes itself into the underlying Linux hosts. You're minimizing the host OS footprint, managing kernel-level security with AppArmor and seccomp profiles, and restricting syscalls that containers can make. This is where container runtime security (Falco/AppArmor/seccomp) really shines because you're not just configuring Kubernetes. You're locking down the entire stack, which honestly feels more like traditional sysadmin work than cloud-native stuff.
I've seen candidates spend weeks on RBAC and totally ignore AppArmor profiles, then get destroyed by two or three tasks they can't even attempt. The Linux Foundation security exam expects you to work across layers, not just kubectl commands. Mixed feelings about this. It's thorough but also means you're studying way more surface area than other certs.
Minimize Microservice Vulnerabilities (20% of total)
At 20%, Minimize Microservice Vulnerabilities is your biggest domain. Covers Pod Security Standards (the replacement for deprecated PodSecurityPolicies), OPA Gatekeeper for policy enforcement, managing secrets securely, and implementing least-privilege configurations using SecurityContext settings. You'll configure service accounts properly. Avoid running containers as root. Use read-only root filesystems.
This domain also hits container image security. Scanning for CVEs. Using private registries. The whole supply chain thing before it became its own domain (more on that in a sec). If you can't nail SecurityContext and Pod Security Standards cold, you're gonna struggle because they appear in multiple scenarios throughout the exam. Not just once or twice, but woven into like half the questions.
Supply Chain Security weighs in at 20%
Supply Chain Security also grabs 20%. Focuses on the software supply chain from image creation through deployment. You're working with image scanning tools, signing and verifying container images, using admission controllers to block unsigned or vulnerable images, and generally making sure nothing sketchy enters your cluster.
Static analysis of YAML manifests falls here too. You might need to identify misconfigurations in deployment specs or scan Dockerfiles for security issues. Actually, speaking of Dockerfiles, I once spent an entire afternoon debugging a build that kept failing because someone had embedded credentials in an ENV variable like three layers deep. Turned out the scanner flagged it but the alert got buried in 200 other warnings about outdated base images. That whole experience taught me why these supply chain checks matter, even when they feel tedious during the exam prep.
Make sure you know the difference between build-time and runtime scanning because they test both. The hands-on Kubernetes security lab exam format means you're not just answering multiple choice. You're actually running tools, interpreting output, and fixing problems under time pressure.
Monitoring, Logging, and Runtime Security (20%)
The final domain rounds out the last 20%. Monitoring, Logging, and Runtime Security. This is where Falco becomes your best friend (or worst enemy, depending on how much you practiced). You'll detect threats using behavioral monitoring, analyze container syscalls, investigate security events in logs, and respond to runtime security incidents.
Audit logging configuration matters here. You need to know how Kubernetes audit policies work, where logs live, and how to query them effectively. kubectl security hardening techniques help you work faster. Aliases, imperative commands, and knowing which flags save you precious minutes when you're already behind schedule.
How these objectives map to real work
The beauty of CKS exam objectives is they mirror actual security engineering tasks. You're not memorizing trivia. Every domain connects to something you'd do protecting production clusters: implementing RBAC policies, hardening nodes, validating images, catching runtime anomalies.
The Linux Foundation weights these domains based on industry priorities, so passing proves you can handle the security challenges platform engineers and DevSecOps folks face daily. If you've already earned your CKA certification, you know the drill. The CKS exam difficulty comes from combining deep security knowledge with speed and accuracy in a live terminal environment.
Each domain builds on the others too. Network policies (Cluster Setup) work with Pod Security Standards (Microservices) which connect to runtime detection (Monitoring). It's integrated, which makes studying kinda brutal but also way more valuable than isolated cert tracks.
Conclusion
Wrapping this up
Look, the Certified Kubernetes Security Specialist (CKS) isn't one of those certifications you can memorize your way through on a weekend. Real deal here. It's a hands-on Kubernetes security lab exam that puts you in front of real clusters with real security problems to solve, and that's what makes it valuable. You're actually doing the work, not bubbling in answers on some scantron sheet. The CKS exam difficulty keeps people honest. You either know how to harden a cluster, configure RBAC properly, and troubleshoot runtime security tools like Falco and AppArmor, or you don't.
The CKS exam cost runs around $395. Yeah, that's steep. But given that the CKS passing score sits at 67% and the exam format's purely performance-based, you're paying for something that actually proves competence rather than test-taking skills. You get one retake included, which is good because a lot of people need it the first time around. I've seen folks struggle with the time pressure more than the actual tasks.
Since CKS prerequisites include holding an active CKA certification, you're already supposed to know kubectl security hardening basics and cluster operations before you even schedule this thing. The exam objectives span five domains: cluster setup, system hardening, microservice vulnerabilities, supply chain security, and runtime monitoring. Each one demands actual command-line muscle memory, not just conceptual understanding. Can't fake it.
Your success really comes down to hands-on practice. The official CKS study materials from Linux Foundation are solid, but you need to supplement with timed lab drills and repetition until commands become automatic. Container runtime security configurations take practice to get right under pressure, especially when you're juggling seccomp profiles and admission webhooks while watching the clock tick down.
One thing that helped me and a lot of others I've talked to: working through realistic CKS practice tests that mirror the actual exam environment. Not multiple-choice quizzes. Actual scenario-based labs where you configure network policies, set up admission controllers, and scan images for vulnerabilities against the clock.
I remember spending an entire Saturday just drilling network policy syntax because I kept mixing up the ingress and egress selectors. Stupid mistake, but those are the things that'll burn you when you're already nervous and the timer's counting down. Repetition fixes that.
Before you schedule your exam date, I'd recommend checking out the CKS Practice Exam Questions Pack at /linux-foundation-dumps/cks/. Worth it. It's structured around the real exam domains and gives you that hands-on practice with the specific tasks you'll face, which is what you need to build speed and confidence.
The CKS certification renewal happens every three years, same as other Linux Foundation security exam credentials. That gives you time to use the skills professionally and stay current with Kubernetes security patterns as they evolve, which they do constantly. This cert opens doors in platform engineering and DevSecOps roles where security hardening's non-negotiable. Get your hands dirty with real practice environments and you'll be fine.
Show less info
Comments
Hot Exams
Related Exams
VMware Carbon Black Portfolio Skills
Certified Professional Ethical Hacker (CPEH)
HCIP-Datacom-Advanced Routing & Switching Technology V1.0
Cisco Video Infrastructure Design
Certified Fraud Examiner (CFE) - Law
SAP Certified Application Professional - Financials in SAP S/4HANA 1709 for SAP ERP Financials Experts
Specialist - Implementation Engineer, PowerEdge MX Modular
SAP Certified Application Associate - SAP Fieldglass Services and External Workforce
Oracle Hyperion Financial Management 11 Essentials
Palo Alto Networks Certified Detection and Remediation Analyst
Automation Anywhere Certified Advanced RPA Professional (V11)
Certified Kubernetes Administrator (CKA) Program
Linux Foundation Certified System Administrator
Kubernetes and Cloud Native Associate (KCNA)
Certified Kubernetes Security Specialist (CKS)
Certified Kubernetes Application Developer (CKAD) Program
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.