ISC2 CSSLP (Certified Secure Software Lifecycle Professional)
What Is the ISC2 CSSLP Certification?
The ISC2 CSSLP certification is a globally recognized credential that proves you know how to bake security into software from day one, not slap it on after everything breaks. I mean, if you've spent any time in application development or security, you've seen what happens when security becomes an afterthought. Complete disaster. The Certified Secure Software Lifecycle Professional exam tests whether you actually understand secure software concepts across eight full domains that cover everything from initial requirements gathering through post-deployment monitoring.
This secure software development certification isn't just another piece of paper. It distinguishes professionals who can design, develop, implement, and maintain secure software systems throughout the entire lifecycle. People who understand that security requirements matter just as much during the planning phase as they do when you're writing code or pushing to production. The industry needed something like this because too many organizations were hiring developers who could build features fast but had no clue about injection flaws or authentication bypasses.
Why ISC2 created this credential
Back in 2007, ISC2 launched CSSLP to address a growing problem that wasn't getting better on its own. Software vulnerabilities were (and still are) responsible for most successful cyberattacks, and throwing security teams at the problem after development was done wasn't working. The software security lifecycle (SDLC) certification focuses on universal security principles rather than specific technologies or programming languages, which makes it vendor-neutral and applicable whether you're building mobile apps, web services, or embedded systems.
The timing was smart. DevSecOps wasn't even a buzzword yet, but the writing was on the wall that security needed to shift left. Way left. The application security certification ISC2 offers validates that you can identify and mitigate security vulnerabilities throughout the entire development process, from threat modeling during design to incident response post-deployment.
What CSSLP actually validates
Real deal here.
CSSLP certification holders understand secure coding practices, threat modeling, security testing methodologies, and compliance requirements. But it goes deeper than that. The credential validates knowledge of authentication, authorization, cryptography, input validation, error handling, and secure communication protocols. All the stuff that keeps your applications from ending up on the evening news or worse, becoming someone's case study in "what not to do." You need to know how to implement these controls properly, not just recognize the terms on a multiple-choice question.
Professionals with CSSLP certification can bridge the gap between development teams and security operations. They speak both languages fluently, which is rare. I've worked with plenty of developers who think security folks are paranoid killjoys, and security people who think developers are reckless cowboys. CSSLP-certified professionals understand both perspectives and can translate security requirements into actionable development tasks without starting interdepartmental warfare.
Who should pursue CSSLP
Software developers and engineers who want to specialize in building secure applications and systems from the ground up are obvious candidates here. If you're tired of fixing the same vulnerabilities in code review after code review, CSSLP gives you the framework to prevent them in the first place.
Application security engineers responsible for evaluating code, conducting security reviews, and implementing security controls in software need this credential. It validates that you know what you're looking for and why it matters. DevSecOps professionals integrating security practices into CI/CD pipelines find CSSLP particularly useful because it covers automation of security testing, continuous monitoring, and rapid response to vulnerabilities in production environments.
Security architects designing secure system architectures benefit from the full coverage of secure design principles and patterns. The certification helps you articulate why certain architectural decisions matter from a security perspective. This can be the difference between getting buy-in from stakeholders or watching your recommendations get ignored. Quality assurance and testing professionals focusing on security testing, penetration testing, and vulnerability assessment get a structured approach to application security testing that goes beyond running automated scanners.
Project managers and team leads overseeing software development projects need to ensure security is properly integrated. CSSLP gives them the knowledge to ask the right questions and evaluate security deliverables. IT auditors and compliance professionals evaluating software security controls can use the CSSLP framework to assess whether organizations are following secure development practices or just checking boxes. My old boss used to joke that auditors treated security like a game of bingo, but the good ones actually understand what they're looking at.
Security consultants advising organizations on secure software development practices find CSSLP adds credibility when recommending process improvements. Technical risk managers assessing software security risks can use the CSSLP domains as a checklist for full risk assessment. Career changers from traditional development roles seeking to specialize in application security discover that CSSLP provides a clear learning path. It tells you exactly what you need to know.
Industries and career levels
The certification appeals particularly to professionals in industries with strict security requirements. Finance, healthcare, government, defense, and critical infrastructure all have regulatory requirements that make secure software development non-negotiable. If you work in these sectors, CSSLP often shows up in job descriptions and procurement requirements.
Most CSSLP candidates are mid-career professionals with 3-7 years of experience looking to validate and advance their security expertise. You're not fresh out of college (though technically you could be), and you're not a CISO yet. You're in that zone where you've seen enough broken software to know why security matters, but you want formal recognition of your skills and maybe a salary bump to go with it.
What skills you'll demonstrate
Understanding of the eight ISC2 CSSLP CBK domains forms the foundation here. These domains cover secure software concepts, secure software requirements, secure software design, secure software implementation and coding, secure software testing, secure software lifecycle management, software deployment and operations and maintenance, and supply chain and software acquisition. Each domain has specific knowledge areas that build on each other.
You'll demonstrate ability to incorporate security considerations during requirements gathering. This means understanding how to elicit security requirements from stakeholders, analyze threats to the system, and document security acceptance criteria. Proficiency in secure software design principles including least privilege, defense in depth, fail-safe defaults, and separation of duties comes through in how you approach architecture and design decisions.
Knowledge of secure coding standards and practices across multiple programming languages matters because CSSLP isn't tied to a specific tech stack. Whether you're writing C++, Java, Python, or JavaScript, the principles of input validation, output encoding, and error handling apply universally. Expertise in security testing methodologies including static analysis, dynamic analysis, fuzzing, and penetration testing shows you can verify that security controls actually work, not just assume they do.
Understanding of software acceptance criteria, security verification, and validation processes before production deployment is huge. This is where a lot of organizations fail. They don't have clear criteria for when software is "secure enough" to ship, so they either ship insecure code or delay releases indefinitely. Skills in post-deployment security operations including patch management, vulnerability management, and incident response for applications prove you understand that security doesn't end at deployment.
Knowledge of supply chain security and third-party component risk assessment has become incredibly important with modern dependency management. Most applications pull in dozens or hundreds of third-party libraries, and you need to assess the risks. Familiarity with compliance frameworks and regulatory requirements affecting software development (GDPR, HIPAA, PCI-DSS, and others) helps you build compliance into the development process rather than retrofitting it later.
Technical depth across domains
Ability to conduct threat modeling exercises to identify potential attack vectors and prioritize security controls is a core skill here. Threat modeling isn't just drawing diagrams. It's systematically identifying what could go wrong and deciding what to do about it. Understanding of cryptographic concepts and proper implementation of encryption, hashing, and key management in applications matters because cryptography is easy to get wrong.
Deep stuff.
Knowledge of authentication and authorization mechanisms, session management, and access control implementation shows up in every domain because these are fundamental to application security. Expertise in secure database design, SQL injection prevention, and data protection throughout the application lifecycle is tested thoroughly because database security remains a common weakness.
Skills in secure API design, web services security, and microservices architecture security considerations reflect modern development patterns. If you're still thinking about security in terms of monolithic applications, you're behind. Containerization, serverless, and distributed systems introduce new security challenges. Understanding of mobile application security, cloud-native application security, and containerization security practices acknowledges that development has moved beyond traditional server deployments.
Ability to communicate security risks and requirements to both technical and non-technical stakeholders might be the most underrated skill CSSLP validates. You can know everything about buffer overflows and race conditions, but if you can't explain to a product manager why a feature request creates security risks without sounding like you're speaking Klingon, your knowledge doesn't help much.
The relationship between CSSLP and other ISC2 certifications is worth understanding. While CISSP covers broad security management and strategy, CSSLP dives deep into application security specifically. If you're looking at SSCP as a stepping stone, CSSLP represents deeper specialization in one particular domain. The CC certification is an entry point, but CSSLP requires significant experience and domain expertise.
The CSSLP certification validates that you can think like both a developer and a security professional, which is what the industry needs more of right now.
CSSLP Exam Overview
What is the ISC2 CSSLP certification?
The ISC2 CSSLP certification targets folks building software who need a security credential that actually mirrors how software gets made, shipped, patched, and supported. Real-world stuff. Not just theory.
If you're living in Jira, Git, CI pipelines, architecture reviews, and those lovely "why's prod on fire" incident calls, CSSLP fits. AppSec engineers use it. Security-minded devs grab it. Architects too. QA people who suddenly got yanked into security testing - yeah, them. Even product managers constantly fielding "can we do this securely by Friday?" questions find value here.
What CSSLP validates is simple to articulate and hard to execute: you understand how security weaves into every phase of the SDLC, and you can make reasonable calls when security, usability, and business goals collide. Tradeoffs. Constraints. Real teams with real deadlines.
CSSLP exam overview
The CSSLP exam tests candidates across all eight domains of the ISC2 CBK, and it's deliberately broad. That's kinda the whole point. You're not getting rewarded for memorizing one OWASP Top 10 list and calling it done. You're being tested on how security shows up in requirements, architecture, implementation, testing, deployment, and the messy operational life after release.
ISC2 regularly updates exam content to reflect changing threats, technologies, and "what people actually do now" in secure software development. Cloud-native patterns appear. Containers show up. Supply chain risk's become a bigger deal than it used to be. The exam content tracks industry best practices, current standards, and frameworks you'll recognize from modern professional environments, or at least that's the intent.
This exam measures theoretical knowledge AND practical application. That practical part? Matters a lot. Lots of questions present situations where multiple answers feel decent, and you've gotta pick the BEST one - the one balancing security requirements with functionality, usability, and business objectives. Not gonna lie, that style can be super annoying if you're used to clean, textbook questions. It's also way closer to real work, which I mean - that's the trade-off. I once watched a colleague spend fifteen minutes arguing with a proctor about whether "most secure" and "best practice" meant the same thing in a scenario question. They don't, by the way.
Short version. Broad coverage. Applied thinking required.
Exam format (questions, time, delivery)
The exam's 125 questions total, made up of multiple-choice and "advanced innovative" questions that test applied knowledge. You've got 3 hours (180 minutes), which works out to roughly 1.4 minutes per question. That's enough time if you keep moving and don't spiral on the tricky scenario prompts.
Only 100 questions count. The other 25 are unscored pretest questions that ISC2's evaluating for future exams, and they're randomly mixed in so you can't identify them. Treat every question like it counts, 'cause you won't know which ones don't.
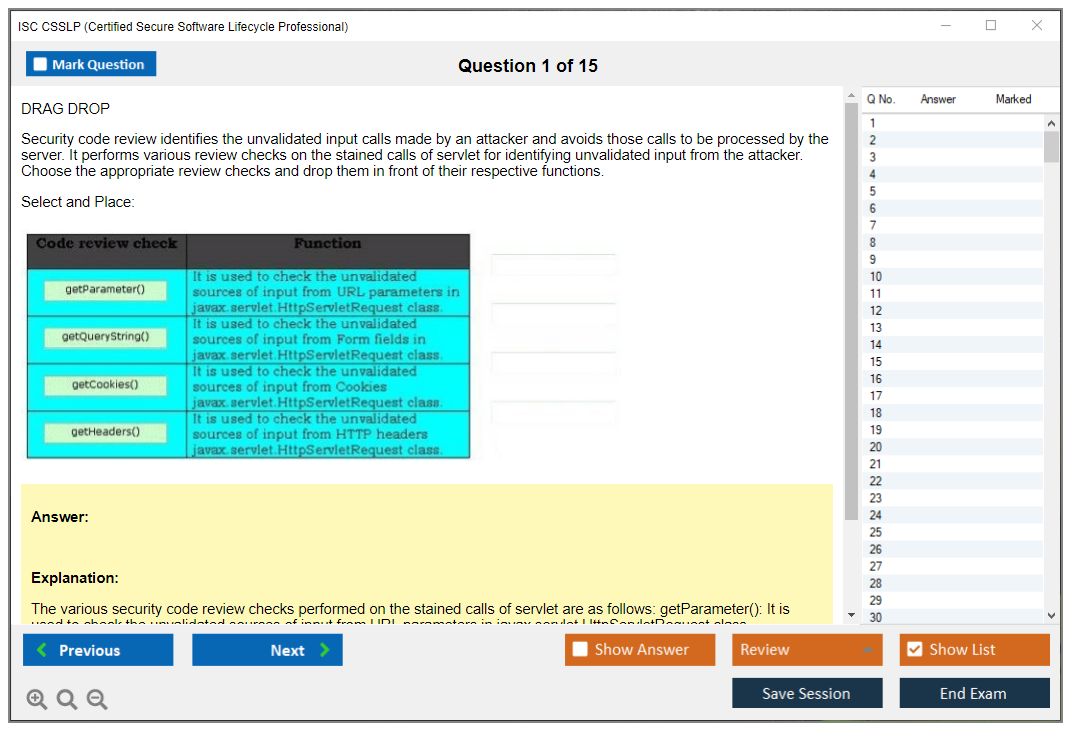
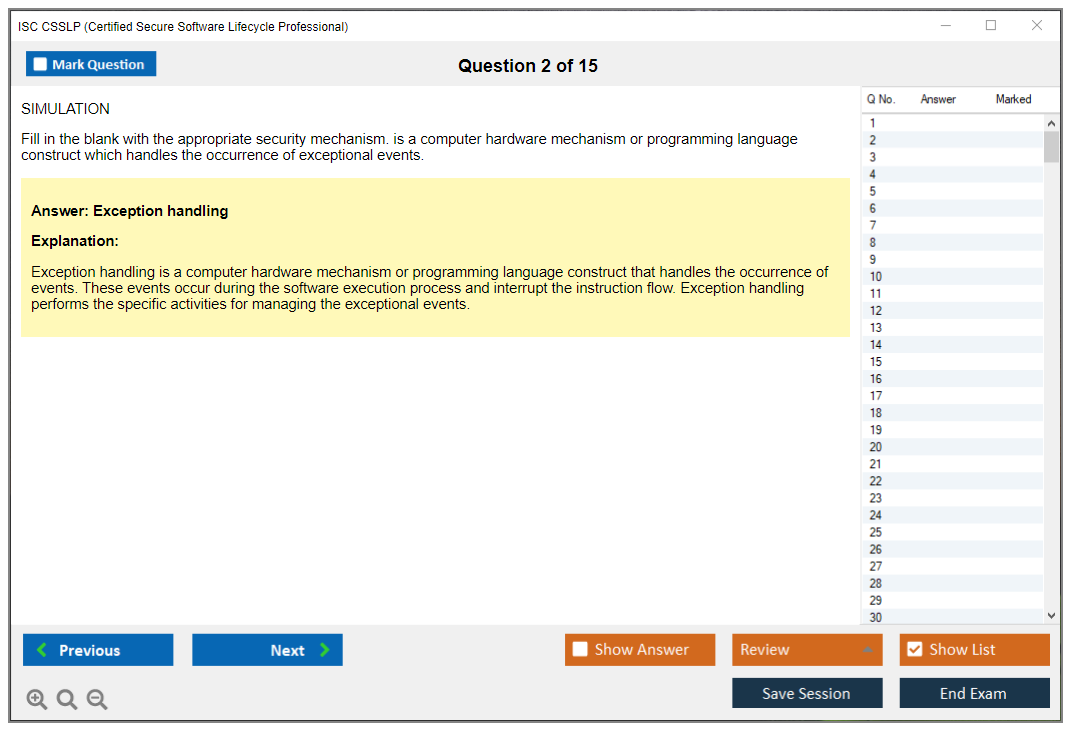
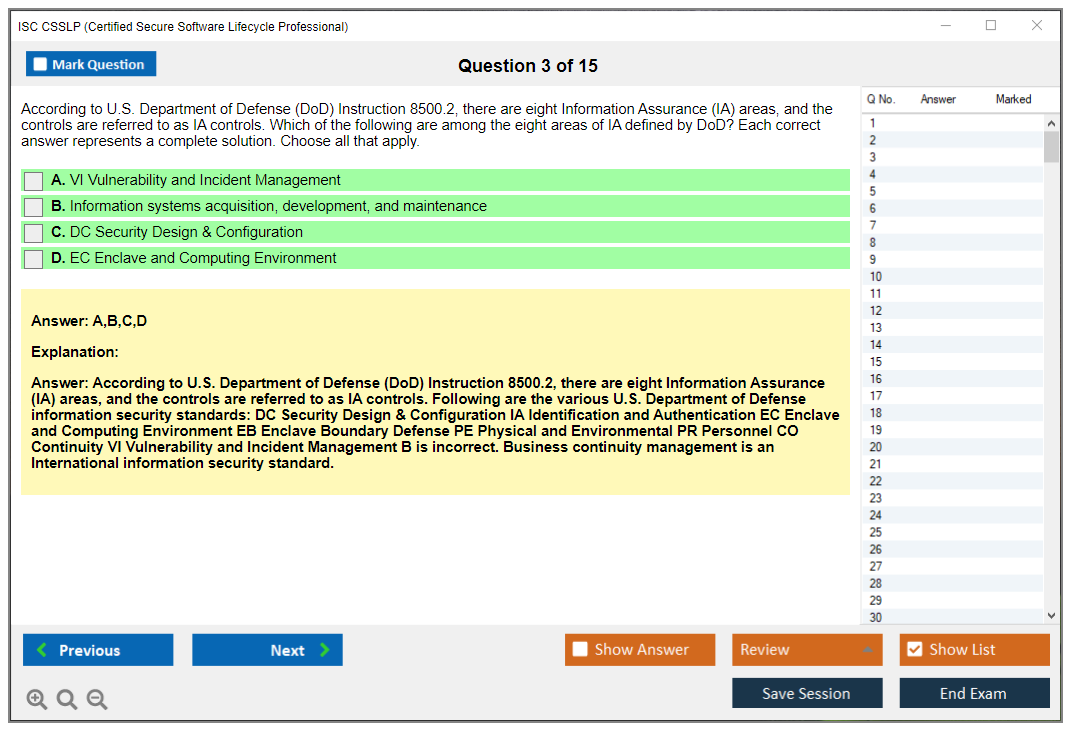
Most questions are multiple-choice with four options and a single best answer. The advanced ones might be drag-and-drop, hotspot identification, or scenario-based formats that feel more interactive. Same idea though - applied judgment, not trivia night.
Delivery's computer-based through Pearson VUE testing centers worldwide, or via online proctoring. Online proctored exams let you test from home or your office with live remote supervision, but you're gonna want a clean desk and a quiet room, because they do NOT play around with the rules. Testing center exams are the classic controlled environment with on-site proctoring and standardized conditions, which some people prefer because it's less "will my internet betray me today."
Arrive early. Check-in includes identity verification and storing personal items in a secure locker. No notes. No reference materials. No devices. Nothing whatsoever. The testing interface is pretty standard: highlight, strikethrough, mark for review, and a simple calculator for the few questions where that matters.
Breaks aren't scheduled during the 3-hour window, and leaving the testing area can get you disqualified. Plan your coffee like an adult.
Results show immediately at the end as a preliminary pass/fail. Official confirmation and your digital badge come after the endorsement process and paying the annual maintenance fee.
CSSLP exam objectives (domains/CBK)
The ISC2 CSSLP CBK domains are eight domains, and the exam weights them, which means your study time should follow that weighting even if your favorite domain's architecture or testing.
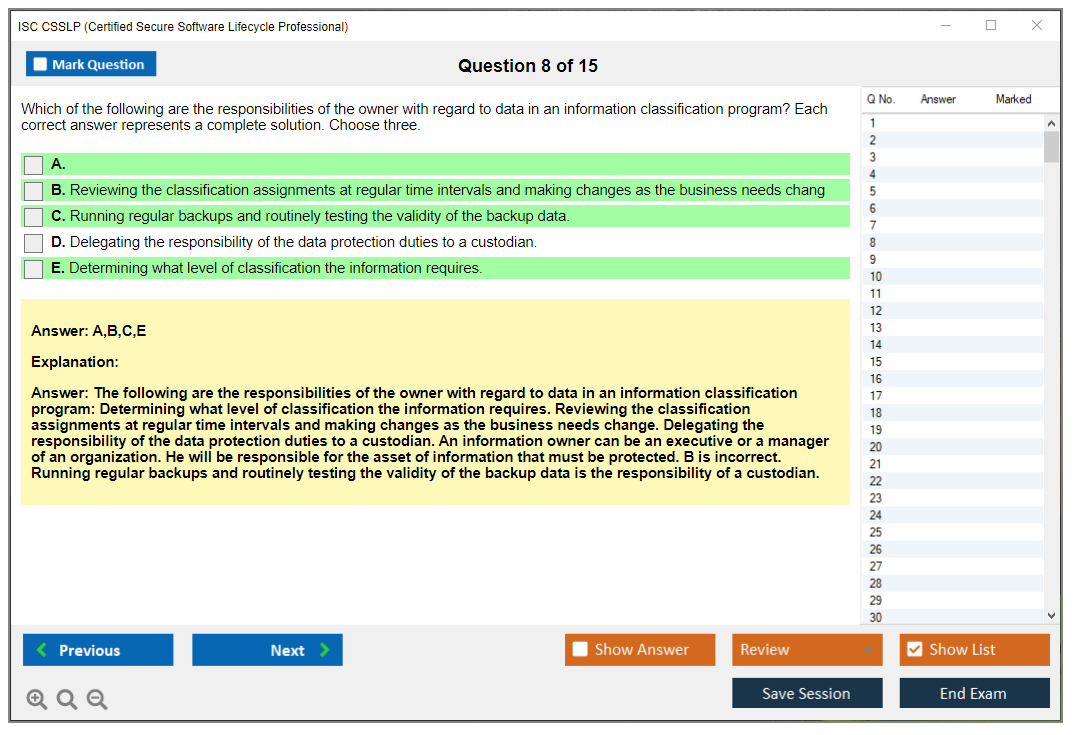
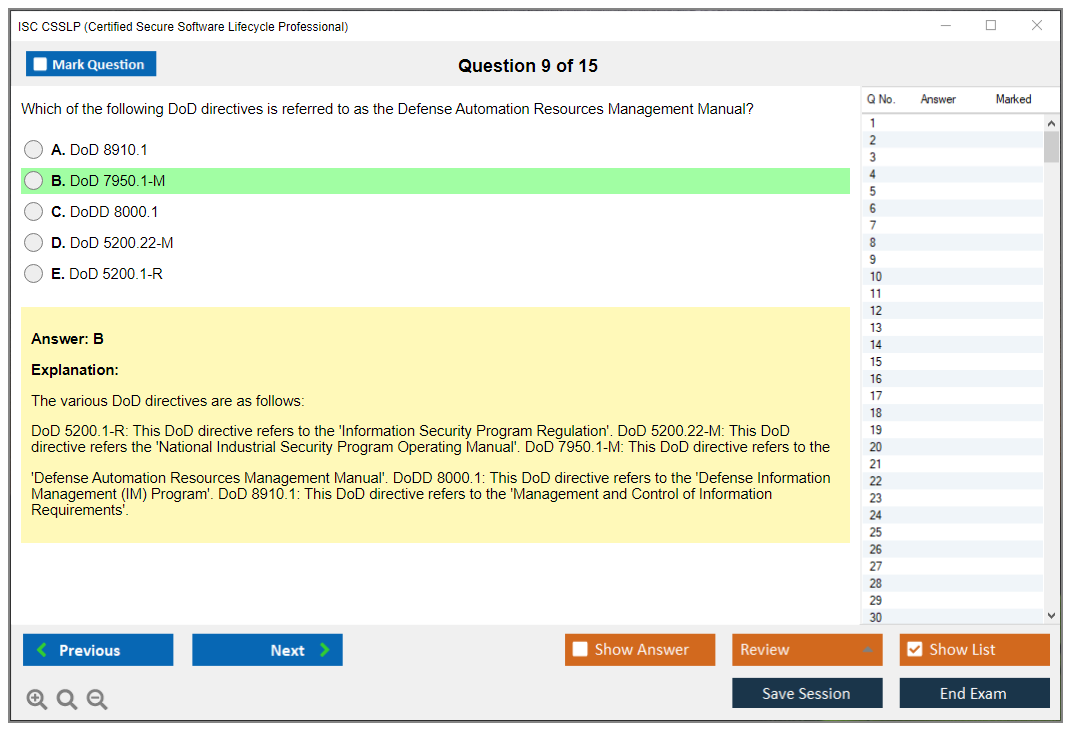
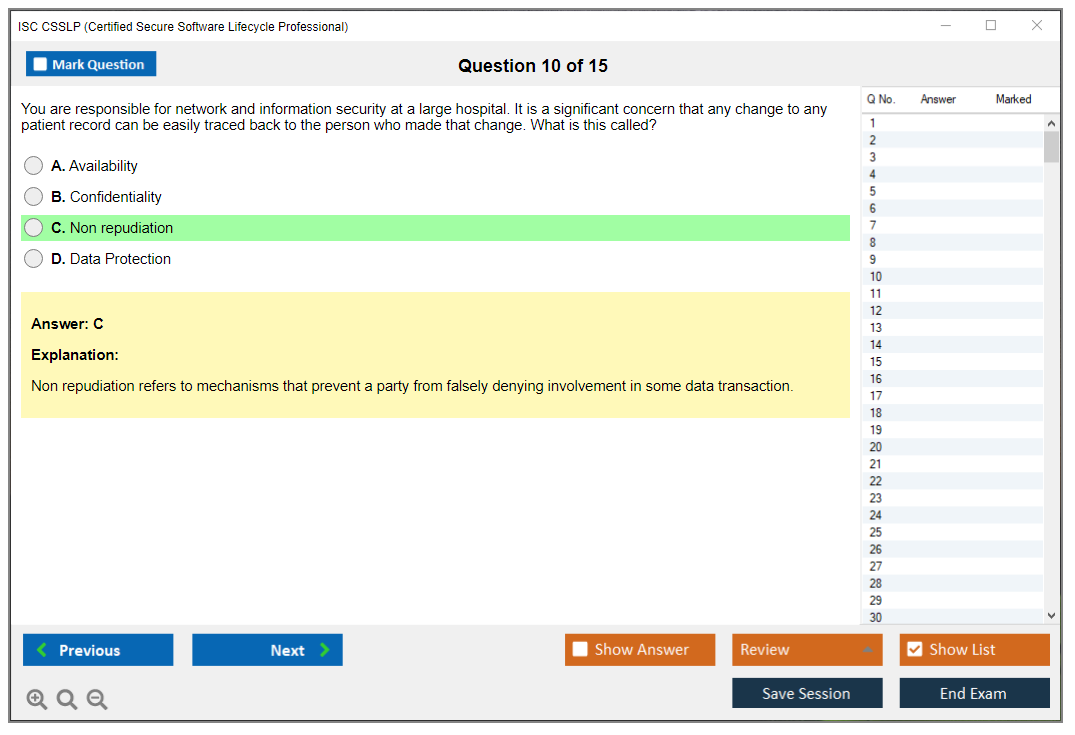
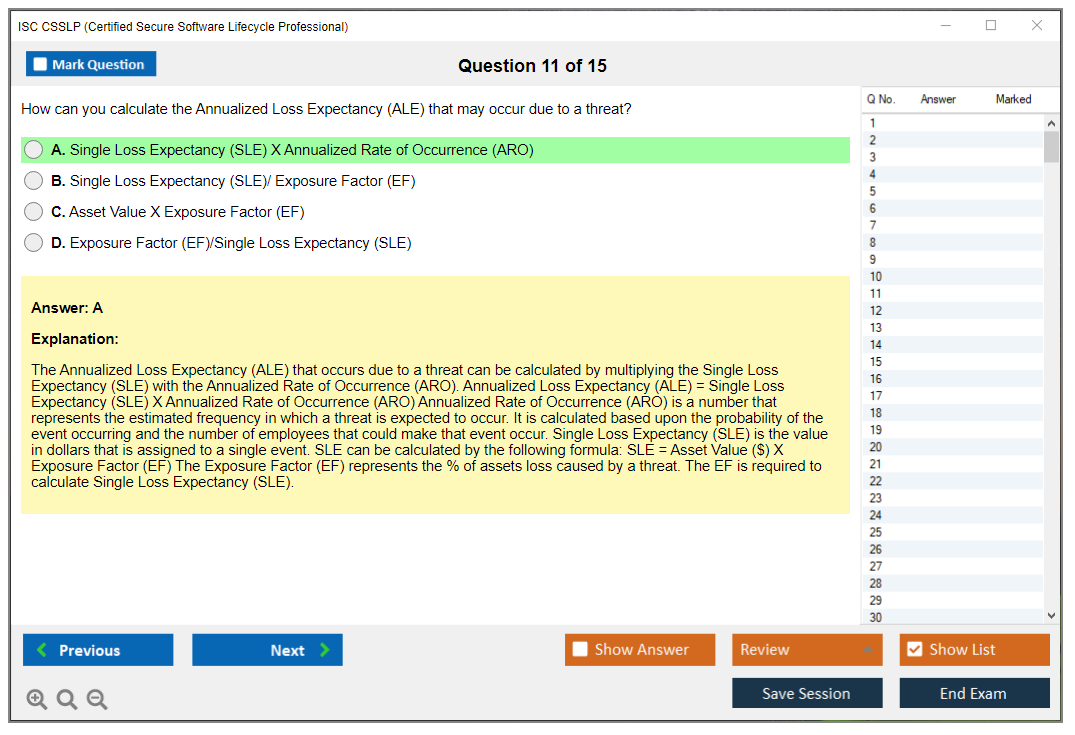
Domain 1: Secure software concepts (10%) covers confidentiality, integrity, availability, and core principles like authentication, authorization, accountability, non-repudiation, and privacy. This domain can feel "basic" until the exam starts asking you to apply those ideas in design choices and process decisions, where the wrong choice is subtle. Like, really subtle. Design principles show up here too, and you're expected to think like someone who's seen systems fail spectacularly.
Domain 2: Secure software requirements (14%) looks at defining security requirements early. Requirements gathering. Policy decomposition. Data classification. Privacy requirements. Regulatory compliance stuff. The thing is, this is where projects either get sane or get doomed, because if the requirements are fuzzy, the "security testing" later becomes a blame game nobody wins.
Domain 3: Secure software architecture and design (14%) digs into secure architecture patterns, threat modeling, and architectural risk assessment. This is a domain where you need to be comfortable reading a scenario and spotting where the trust boundaries are, what the threat actors can do, and which mitigations make sense without turning the system into a museum piece nobody can deploy.
Domain 4: Secure software implementation (14%) handles secure coding, defensive practices, secure coding standards, common vulnerabilities, and configuration management. This is where you'll see things that smell like OWASP, but don't expect it to be "name the vuln." Expect "what d'you do next" or "which control best addresses this risk in this context."
Domain 5: Secure software testing (14%) includes functional testing plus security testing methods, coverage analysis, and bug tracking and resolution processes. This isn't only about tools. It's about how testing fits in the lifecycle, how findings get triaged, and what "done" means when a security bug isn't fully fixable before release. Which happens more than anyone wants to admit.
Domain 6: Secure software lifecycle management (11%) gets into governance, project management integration, risk management, personnel security, and vendor or supplier management. It's the "process and people" glue. Some candidates ignore it because it feels less technical, then they get absolutely smoked by scenario questions about who owns what decision and how you manage risk without blocking delivery.
Domain 7: Software deployment, operations, and maintenance (11%) tackles post-deployment security: secure installation, operations, monitoring, incident management, and problem management. This is where secure software development becomes secure software survival. Logging. Patch management. Handling incidents without destroying evidence. Operational reality bites here.
Domain 8: Supply chain and software acquisition (12%) deals with third-party software, supplier risk assessment, acquisition processes, transitions, and managing third-party security. With today's dependency graphs and vendor sprawl, this domain's not optional, and the exam treats it that way.
CSSLP passing score (what ISC2 discloses)
The CSSLP passing score is 700 on a scaled score range of 100 to 900. That scaled scoring exists because different exam forms can vary in difficulty, and ISC2 wants a consistent standard across versions.
Your raw score (how many you got correct) gets converted to the scaled score using psychometric analysis and statistical modeling. ISC2 doesn't disclose the exact number of correct answers needed to pass, which frustrates people. People often estimate it's around 70% of the scored questions, but it can vary depending on the form, so don't build your plan around a magic number.
Each domain contributes based on its weighting in the blueprint. If you pass, you don't get a domain-by-domain breakdown, just pass/fail. If you fail, you get a diagnostic report showing performance as above, near, or below proficiency by domain, which's honestly useful for a retake plan.
Also worth knowing: exam difficulty's calibrated before questions go live, and ISC2 uses subject matter experts plus psychometricians to keep the exam defensible and consistent.
CSSLP exam difficulty (what makes it challenging)
The CSSLP exam difficulty is mostly about breadth and judgment. Eight domains is a LOT. The questions often blend multiple domains in one scenario, so you've gotta bounce between requirements, design, implementation, and operations in your head, then pick the most reasonable next step.
The exam tests application more than memorization. You'll see fine distinctions between similar controls, and you'll have to decide when to apply which one. Plenty of distractors look plausible, and you get those "all of these could work" situations where you're being graded on prioritization and decision-making, not on being clever.
Methodologies show up too. Agile, Waterfall, DevOps. The questions poke at what changes when your release cadence's weekly, when you've got legacy systems, when you're containerized, when you're partly cloud, and when compliance requirements get involved across different industries and regions.
Time pressure's real. Not brutal, but real. Long scenarios can slow you down, so pacing matters a lot.
Compared to other ISC2 certs, CSSLP's often described as moderately difficult: more technical than CISSP but narrower in scope, and more SDLC-specific than something like SSCP. If you're coming from cloud security, you'll recognize overlaps with CCSP, but CSSLP stays focused on software lifecycle work rather than broader cloud governance.
Cost, prerequisites, renewal, and the stuff people ask first
People always ask about money and eligibility before they ask about domains. I totally get it.
CSSLP exam cost varies by region and currency, and ISC2 changes pricing sometimes, so you should confirm in your ISC2 account before you schedule. Retakes cost money too, obviously, so budget like you plan to pass the first time. Training, books, and CSSLP practice tests can add up fast, especially if you buy multiple question banks and a video course. Some people spend almost nothing and use a couple solid references plus hands-on practice, others drop a lot because they want structure.
CSSLP prerequisites are experience-based. CSSLP isn't meant to be a "zero experience" exam. If you don't meet the experience requirement yet, ISC2 has the Associates of ISC2 pathway, which basically lets you pass the exam first and complete experience later. Endorsement's part of the process after passing, and then you pay the annual maintenance fee before you're fully certified.
Renewal's the normal ISC2 rhythm: CPEs plus annual maintenance fees. CSSLP renewal requirements aren't hard if you already work in software security or SDLC-adjacent roles, because your work activities, training, conferences, and even some content creation can count. But you still need to track and report it, which nobody enjoys.
One more opinion. Don't cram only. Build SDLC instincts.
If you want more context on the credential itself, the CSSLP (Certified Secure Software Lifecycle Professional) page's a good hub, and if you're deciding between tracks, it helps to compare it with CC (Certified in Cybersecurity) for entry-level direction or CISSP if your path's moving toward broad security leadership.
FAQ (People also ask)
How much does the ISC2 CSSLP exam cost?
It depends on your region, and ISC2 pricing changes, so check the current fee in your ISC2 account before scheduling. Budget extra if you think you might reschedule or retake.
What is the passing score for the CSSLP exam?
The CSSLP passing score's 700 on a scaled range of 100 to 900. ISC2 doesn't publish the raw number of correct answers required.
How hard is the CSSLP compared to CISSP?
CSSLP's usually seen as more technical and SDLC-focused than CISSP, but narrower. CISSP's broader across security management and architecture, CSSLP keeps pulling you back to software lifecycle decisions.
What are the CSSLP prerequisites and required experience?
CSSLP expects professional experience related to secure software lifecycle work. If you don't have it yet, the Associates of ISC2 option can let you pass the exam first and earn the experience afterward.
How do I renew my CSSLP certification and maintain CPEs?
You renew by earning and reporting CPE credits during the cycle and paying the annual maintenance fee. Track your activities as you go, because reconstructing a year of learning from memory's a pain.
CSSLP Cost and Fees
Understanding what you're actually paying for
Look, the ISC2 CSSLP certification price? Seems simple at first. But there's way more involved than just that exam fee. You've got registration costs, training, study materials, practice exams, and those ongoing maintenance fees that absolutely blindside people. Nobody warns you about those. Your total investment could be under $1,000 if you're resourceful and strategic about it, or it'll balloon to $5,000+ if you spring for official training packages and all the premium resources available out there.
The thing is, grasping the complete financial picture lets you budget intelligently. Some people get their employer covering every single expense. Others are self-funding and need to be ruthless about resource allocation.
The base CSSLP exam cost
The CSSLP exam cost varies based on ISC2 membership status. Non-members pay $749 USD for exam registration as of 2024-2026 pricing. Standard rate. But become an ISC2 member first, and you're only paying $599 USD. That's $150 savings immediately. Membership itself? Just $50 annually.
Quick math here. You save $100 right away by joining before registering. Plus you're getting member resources, webinars, networking events, and training material discounts. Skipping membership makes zero financial sense unless you're certain you'll never pursue another ISC2 cert down the road. Eyeing CISSP or CCSP eventually? That membership pays for itself repeatedly.
ISC2 adjusts pricing periodically, so verify current fees on their official website before committing. Currency exchange rates matter if you're paying from outside the US. That $599 fluctuates depending on payment processing timing.
What happens if you need to reschedule or retake
That exam fee? Non-refundable once paid. ISC2 does allow rescheduling if life interferes, though. Timing matters enormously. Reschedule more than 30 days before your exam date and there's no extra charge. Within that 30-day window costs you $50. Wait until 48 hours before? Jumps to $100.
Failed? Wait 30 days. Pay the full exam fee again. There's no retake discount, which is why I always stress investing properly in preparation upfront rather than rushing. Paying $599 twice because you weren't adequately prepared means you've spent $1,198 instead of maybe $800 total with better study materials initially. I once watched a colleague fail three times before finally passing, and by then he'd spent more than people who went the bootcamp route.
Some training providers bundle exam vouchers with courses, occasionally offering slight discounts. Group registrations might get reduced rates if your employer's sponsoring multiple candidates at once. Veterans, active military personnel, and students should investigate ISC2's special programs. Discounted exam fees appear sometimes.
Training costs add up fast
Official ISC2 CSSLP training? Ranges from $2,500 to $3,500 depending on format. Self-paced online training typically runs $2,500-$2,800 and provides lifetime access to materials and updates. Instructor-led formats, whether live online or in-person, cost $2,800-$3,500 and include interactive instruction, lab exercises, and direct access to experienced instructors answering your specific questions.
Bootcamp-style training condenses everything into 3-5 intensive days. These usually hit the higher pricing spectrum but work brilliantly if you need certification quickly for job requirements or project deadlines.
Third-party training providers offer alternatives spanning $500 to $2,000. Quality varies wildly. Some are exceptional and taught by professionals with genuine secure development experience. Others? Basically someone reading slides verbatim. You get what you pay for, mostly, though not always.
Books, practice tests, and supplementary materials
The official ISC2 CSSLP textbook costs approximately $80-$100 printed, $60-$80 digital. You'll probably want one or two supplementary reference books covering secure coding practices, threat modeling, or specific CSSLP exam objectives more thoroughly. Those add another $40-$60 each.
CSSLP practice tests are absolutely essential for preparation. Reputable question banks with 300-1,000 practice questions typically cost $50-$150. Premium platforms with performance analytics, adaptive learning features, and detailed wrong-answer explanations range from $100-$200. This isn't where you skimp. A solid CSSLP Practice Exam Questions Pack for $36.99 can determine whether you pass or fail, especially understanding how ISC2 phrases questions and what they're actually testing.
Hands-on lab environments and secure coding practice platforms might run $30-$100 monthly for subscription access. Video courses from Udemy, Pluralsight, or LinkedIn Learning range from $30 to $500 depending on comprehensiveness and instructor expertise.
Budget-conscious and self-disciplined? You can prepare with $200-$300 in materials beyond exam fees by using free resources, open-source tools, and community study groups. I've seen people pass spending under $1,000 total. Full preparation including official training and multiple premium resources might push your total to $3,000-$4,500 beyond exam fees.
The annual maintenance fee nobody mentions upfront
Here's the surprise: Annual Maintenance Fee (AMF). For CSSLP? $85 USD yearly, due every year maintaining certification status. This is completely separate from ISC2 membership fees and applies specifically to maintaining the CSSLP credential.
Your first AMF comes due once you complete endorsement, before ISC2 issues your digital badge. After that? Due on your certification anniversary date annually. ISC2 sends reminders, but you're responsible for timely payment.
Miss it? You'll pay a $50 reinstatement fee on top of the $85 AMF if you catch it within 90 days of suspension. Let it slide beyond 90 days and your certification might be revoked entirely. That means you'd retake the exam to recertify. Brutal and expensive mistake.
Holding multiple ISC2 certifications, say CSSLP and SSCP, means paying separate AMF for each credential. Over a three-year cycle, you're looking at roughly $770-$920 for members (exam fee plus three years of AMF). Many employers cover AMF as professional development budget items, so ask about reimbursement policies before assuming you're paying indefinitely.
Employer reimbursement and tax considerations
Lots of organizations offer certification reimbursement programs or professional development budgets covering exam and training costs. Some cover everything upfront, others reimburse after passing, and some require you staying employed for specific periods or repaying them if you leave.
Get this documented before registering. I've heard stories about people assuming employer coverage, only discovering program restrictions they didn't know existed.
Tax deductions may be available for professional certification expenses if they're related to maintaining or improving skills in your current profession. The AMF, exam fees, training courses, and study materials might all qualify, but tax law is complicated and changes, so consult with a tax professional about your specific situation rather than assuming everything's deductible.
Is the investment worth it?
The certification investment should be weighed against career benefits including salary increases, job opportunities, and professional recognition in secure software development. CSSLP holders often see salary bumps of $10,000-$20,000 or more, especially moving into application security roles, secure DevOps positions, or security architecture. Over several years? That completely justifies the initial $1,000-$4,000 investment.
Job opportunities expand noticeably too. Many organizations specifically require CSSLP for senior development roles, security engineering positions, or government contracts. The certification demonstrates expertise across the entire secure software development lifecycle, increasingly valuable as organizations prioritize application security.
Budget appropriately, prepare thoroughly with quality CSSLP study materials and practice tests, and plan for long-term maintenance costs. The credential continues providing career benefits and professional recognition only if you keep it active, so factor that AMF into your calculations forever, or until you retire or shift careers entirely, I guess.
Look, if you're serious about application security or secure development? CSSLP's probably worth the investment. Just go into it with your eyes open about the complete financial picture.
CSSLP Prerequisites and Eligibility
What is the ISC2 CSSLP certification?
The ISC2 CSSLP certification is a security credential for people who live close to the software delivery process. Not "I ran a Nessus scan once" security. This one's about building and shipping software without turning your SDLC into an exploit factory.
CSSLP's for folks who have to care about security earlier than prod. AppSec engineers, secure SDLC leads, security architects who actually read design docs, developers who got pulled into threat modeling, QA people who got tired of testing only happy paths, and even product or delivery managers who own gates like "no release without security signoff". Different titles. Same headache.
CSSLP validates you understand secure software development as a process, not a tool. Requirements that don't create vulnerabilities, design that doesn't assume trust, code that gets reviewed with intent, testing that finds real issues, deployment and ops that don't undo everything, and yeah, governance stuff, because someone always asks "who approved this" after an incident.
CSSLP exam overview
You're taking the Certified Secure Software Lifecycle Professional exam to prove you can reason across the lifecycle, not just spit out OWASP Top 10 definitions. Broad? Yeah. That's why people trip on it.
Exam format's pretty standard for ISC2. Computer-based testing at Pearson VUE, multiple-choice questions, and a time limit that's generous until you realize you're rereading questions because two answers both sound "kinda right". The exact current numbers (question count and minutes) should be verified on ISC2's site before you schedule, because vendors tweak formats and I'm not here to sell you outdated trivia.
CSSLP exam objectives (domains/CBK)
The CSSLP exam objectives map to the ISC2 CSSLP CBK domains, which are basically the lifecycle phases plus the governance glue. You'll see themes like secure requirements, secure design, secure implementation, testing, deployment/ops, and supply chain and environment issues that affect software. The wording shifts over time, but the idea stays the same: security across the SDLC.
One domain'll click fast if you already do AppSec. Another'll feel like reading a policy binder. That's normal.
CSSLP passing score (what ISC2 discloses)
People ask about the CSSLP passing score like it's a video game high score. ISC2 uses a scaled scoring model and doesn't publish "you need X out of Y questions correct" in a way that's useful for test-taking strategy, so you can't really game it. Treat it like this: you need solid performance across the domains, and weak spots can sink you.
CSSLP exam difficulty (what makes it challenging)
The CSSLP exam difficulty is less about math and more about judgment. Questions often describe a scenario and ask what you should do next, what's the best control, or who owns a decision point. If you only studied flashcards, you'll feel it.
Also, it's not CISSP-hard in the same way. CISSP's huge and management-heavy, CSSLP's narrower but deeper in SDLC thinking. If you've never been in the room when requirements were written or when a release got blocked, you'll be guessing a lot. Not fun.
CSSLP cost and fees
CSSLP exam cost (registration and retake considerations)
The first "am I doing this" question's usually money. How much does the ISC2 CSSLP exam cost? Price changes, promos happen, and regions vary, so check ISC2 directly for the current CSSLP exam cost. Retakes matter too. If you're budgeting, assume you might pay again, because plenty of smart people underestimate the breadth and show up underprepared.
Exams aren't cheap.
Additional costs (training, books, practice tests)
You can spend $0 beyond the exam fee if you're disciplined and already have a strong background. Most people don't. Training, a reference book, and CSSLP practice tests can add up fast.
Here's my take: buy one solid book, one question bank, and use the rest of your budget for hands-on practice you can explain in an interview. Fancy bootcamps're fine, but they don't replace experience. I once watched someone drop three grand on a week-long course, then fail because they'd never actually dealt with a threat model in the wild. Money doesn't fix gaps that only real work fills.
Membership/annual maintenance fees (AMF) and budgeting
ISC2 certifications come with annual maintenance fees. Plan for it. If your employer reimburses, great. If not, treat it like a subscription you must keep paying if you want the credential to remain active, along with CPE reporting.
CSSLP prerequisites and eligibility
ISC2 maintains specific CSSLP prerequisites that make sure certified professionals possess genuine practical experience in secure software development. That's the core point. This isn't meant to be a "pass an exam and you're instantly senior AppSec" situation, and honestly, thank god, because the industry already has enough paper cert chaos.
The prerequisite requirements protect the credential's integrity and make sure CSSLP holders can apply knowledge in real-world situations. I mean, if you've ever worked with someone who can recite controls but can't explain how to fix a broken auth flow without breaking the product, you already understand why experience gates exist.
Understanding eligibility criteria before beginning exam preparation prevents disappointment and allows proper career planning. People'll spend weeks grinding CSSLP study materials, book a test slot, then realize they can't get endorsed because their "security work" was basically running a scanner once a quarter. Don't be that person. Check your timeline first, then study.
Required work experience (and acceptable experience types)
The big rule: candidates must have a minimum of four years cumulative paid work experience in one or more of the eight CSSLP CBK domains. Paid matters. Cumulative matters. And it doesn't have to be four years of doing the exact same thing.
The four-year requirement can be fulfilled through full-time, part-time work. Contracting counts if it's paid and real, mixed roles count if the tasks map to the domains. So if you were a developer for two years doing secure code reviews and handling vulnerability remediation, then moved into QA with security test cases and release gates for two more, you may be in great shape. Document it.
What tends to qualify, in plain language:
- Writing or reviewing security requirements, abuse cases, privacy requirements, acceptance criteria tied to security
- Threat modeling, architecture reviews, design-level security decisions (especially if you can show artifacts)
- Secure coding, code review focused on security, dependency management, fixing vulnerabilities end to end
- Security testing like SAST/DAST, but also test strategy, manual verification, regression proof
- Release and deployment controls, secrets management, CI/CD security checks, incident response tied to application issues
- Governance things that touch software (policies, standards, metrics, risk signoff that actually affects how teams build)
Stuff that's weak on its own: generic IT support, network-only roles with no software lifecycle involvement, or "I attended a secure coding webinar" energy. Helpful background, sure. But the bar's experience you can explain, defend, and tie to the CBK.
Be honest with yourself. Be specific in documentation. Save evidence. The thing is, people forget employment letters and role descriptions until they need endorsement, then scramble.
Degree/waiver options (if applicable)
ISC2 often offers a one-year experience waiver for certain degrees or approved credentials, depending on the certification. For CSSLP, confirm the current waiver policy on ISC2 before assuming you get a reduction, because these policies can change and the fine print matters. If you do qualify for a waiver, it typically reduces the required experience but doesn't remove the need for real work history and endorsement.
Endorsement process and timelines
The endorsement process verifies experience claims, making accurate self-assessment of eligibility necessary before registering. This's where people get stuck. Passing the exam's not the final step. You need an endorser, usually an active ISC2 credential holder in good standing, who vouches that your experience is legit.
Look, endorsements aren't a vibe check. They're asking, "Did you actually do this work, and can you prove it?" You should be ready with role descriptions, dates, employer info, and bullet points mapping what you did to the CBK domains. If you're sloppy here, you slow everything down, and you risk getting rejected or audited later, which's a stress you don't need.
Timelines vary wildly. Sometimes it's quick. Sometimes it drags because HR can't confirm employment or your endorser goes quiet. Plan for that lag if you need the cert for a job deadline.
Associates of ISC2 pathway (if you don't meet experience yet)
If you don't have the four years yet, you can still take the exam and become an Associate of ISC2 (assuming that path's currently available for CSSLP, which you should verify on ISC2's site). Then you've got a window of time to earn the required experience and convert to full certification.
This's the "I'm close, but not there" option. It's also a career planning tool. You can prove exam knowledge now, keep building hands-on work, and convert later without pretending you already meet CSSLP prerequisites.
Best CSSLP study materials
You'll see a ton of CSSLP study materials online, and a lot of 'em are recycled notes that don't match the current outline. Stick to sources that track the latest domains and terminology.
Official ISC2 training exists. It's expensive, but structured. A good CSSLP book plus real SDLC experience can be enough, though, and people who do the work daily often learn faster from mapping concepts to their own pipelines and incidents than from watching slide decks.
For CSSLP practice tests, use them like a diagnostic, not a confidence booster. One question bank, used well, beats five banks you skim.
CSSLP practice tests: how to use them effectively
Do a baseline set early. Then review misses by domain mapping. You want to know if you're struggling in, say, requirements or deployment, not just "I got 72%".
A schedule that works's messy but practical: short quizzes during the week, longer sets on weekends, then at least one full-length simulation before exam day. And when you review wrong answers, don't just memorize the "right" option. Write why the other options're wrong in that scenario. That's where the exam lives.
Common pitfall: treating this like trivia. CSSLP questions usually reward lifecycle reasoning. What happens first. Who owns it. What reduces risk without breaking delivery. That kind of thinking.
CSSLP study plan (4,12 weeks)
If you already work in AppSec or secure SDLC, four to six weeks's realistic. If you're coming from general security or general dev with limited exposure to governance and process, eight to twelve's more honest.
Keep it simple. Align your weeks to domains, read the official outline, do targeted questions, and connect every topic to something you've seen at work. If you can't connect it, go find a lab or a small project where you can.
Final week checklist: one full practice run, review weak domains, skim notes, and stop trying to cram brand-new material the night before. Sleep matters.
CSSLP renewal requirements (CPEs and maintenance)
The CSSLP renewal requirements are the usual ISC2 model: earn and report CPEs over the cycle, pay annual maintenance fees, and keep documentation in case of audit. If you're already attending security talks, doing internal training, writing postmortems, or building secure SDLC improvements, you can often turn that into CPEs. Just track it as you go, because backfilling a year of CPE evidence's miserable.
CSSLP vs other security certifications
CSSLP vs CISSP: CSSLP's SDLC-focused and expects you to understand software delivery reality. CISSP's broader and more managerial across security domains. Which's "harder" depends on your background, but CSSLP can feel sharper if you're not used to software lifecycle decisions.
CSSLP vs Security+ or SSCP: those're earlier-career and broader. CSSLP's for people already doing software work and wanting an application security certification ISC2-style, with lifecycle coverage.
FAQ (People also ask)
How much does the ISC2 CSSLP exam cost?
Check ISC2 for the current CSSLP exam cost, because pricing can change and varies by region. Budget for a retake just in case.
What is the passing score for CSSLP?
ISC2 uses scaled scoring and doesn't give a simple "X questions correct" target. Focus on solid performance across domains instead of chasing a magic number.
Is CSSLP hard?
The CSSLP exam difficulty comes from scenario judgment across the SDLC. If you've done secure requirements, design reviews, remediation, and release gates, it's fair. If not, it's rough.
What are the CSSLP prerequisites?
Minimum four years of cumulative paid work experience in one or more of the eight domains, with experience allowed from full-time or part-time work. Then you complete endorsement to validate that experience.
How do I renew CSSLP?
Meet the CSSLP renewal requirements by earning CPEs during the cycle, paying the annual fee, and keeping records. Treat CPE tracking like a routine task, not a once-a-year scramble.
Conclusion
Wrapping up: is the ISC2 CSSLP certification worth it for you?
Okay, so here's the deal. If you're legitimately serious about software security and you've actually been working in the secure SDLC space, the ISC2 CSSLP certification can absolutely move your career forward in ways that matter. It's not one of those easy weekend certs you knock out on a whim, y'know? The CSSLP exam difficulty is real. We're talking four hours, 175 questions covering everything from secure design principles to testing methodologies and deployment security. The passing score threshold means you've gotta really understand how security fits into every phase of development, not just memorize a few flashcards and hope for the best.
The CSSLP exam cost isn't trivial either.
You're looking at $599 for the exam itself, plus annual maintenance fees once you're certified, so factor that into your budget if you haven't already because it adds up faster than you'd think. But honestly, the bigger investment? Time. Between reviewing CSSLP exam objectives across all eight domains, working through quality CSSLP study materials, and drilling with CSSLP practice tests, you're probably looking at 60 to 100 hours if you've got solid security fundamentals already.
Less experience?
Add another 40 to 60 hours, maybe more depending on how rusty you are with certain concepts or, wait, actually scratch that. It could be even longer if secure coding practices aren't something you've been doing day-to-day recently.
I mean the prerequisites alone tell you this isn't entry-level stuff. Four years of cumulative paid work experience in one or more of the CSSLP CBK domains, though you can waive a year with a degree which helps some people. That endorsement process adds a few weeks after you pass, so plan accordingly if you've got a timeline in mind. Once you're in, the CSSLP renewal requirements kick in: 40 CPEs every three years, which keeps you sharp but also means you can't just coast and forget everything you learned.
Here's the thing about prep materials. Official ISC2 training is solid but pricey. Books give you depth. But CSSLP practice tests are where you figure out if you actually understand the material or if you're just fooling yourself into thinking you're ready when you're not.
You need both breadth and the ability to apply secure SDLC thinking under pressure.
Not gonna lie, comparing this application security certification ISC2 offers to something like CISSP or CEH is tricky because they overlap but target different roles entirely. CSSLP is narrower, focused entirely on building secure software, which makes it more relevant if you're a developer, architect, or DevSecOps engineer who needs to prove specialized knowledge rather than general security awareness. The thing is, specialized certs carry more weight in niche roles. Mixed feelings on that but it's reality.
Speaking of reality, I once watched a senior dev with 15 years of experience completely bomb a practice test because he'd been working in legacy systems so long that modern threat modeling approaches felt like a foreign language. Guy was brilliant at what he did, but the exam doesn't care about your war stories. It wants to know if you understand current best practices across the entire lifecycle, not just the corner of it you've been living in.
If you've made it this far and you're ready to tackle the Certified Secure Software Lifecycle Professional exam, start with a solid practice question set honestly. The CSSLP Practice Exam Questions Pack at /isc2-dumps/csslp/ gives you realistic scenario-based questions that mirror the actual exam format, helping you identify weak domains early and drill until the software security lifecycle concepts become second nature instead of something you're frantically Googling the night before. Don't wait until two weeks before your exam date to test yourself. Start now, fail early on practice tests, learn from it, and show up ready.