ISC2 CISSP-ISSEP (Information Systems Security Engineering Professional)
What is the ISC2 CISSP-ISSEP Certification?
Here's the deal. If you've already snagged your CISSP and you're in a position where building secure systems from scratch is your daily reality, the CISSP-ISSEP certification could be exactly what you're after. it's some fancy acronym you slap on your LinkedIn profile to impress recruiters. The Information Systems Security Engineering Professional designation? It's one of three advanced concentrations ISC2 dangles in front of CISSP holders, and it's probably the most hardcore technical one they offer.
What makes ISSEP different from regular CISSP
The ISC2 CISSP-ISSEP targets people who exist at that weird crossroads of cybersecurity and systems engineering. You know, that sweet spot where theory meets actual implementation. We're talking professionals who don't just sit around assessing risk or cranking out policy documents all day long, but folks designing entire systems, handpicking controls, weaving security into every phase of the lifecycle from conception through retirement. Think Information System Security Officers (ISSOs), security architects, systems security engineers, technical consultants grinding away on DoD contracts or working critical infrastructure projects where mistakes have real consequences.
This systems security engineering credential enjoys massive popularity within government and defense communities. If you've ever wrestled with NIST SP 800-160 or dealt with CNSS standards in your career, you get what I'm saying. The certification syncs directly with those frameworks, plus ISO/IEC 15288 standards. It demonstrates you can bring engineering discipline to security challenges. Not just spot threats and rattle off control names.
The technical depth is real
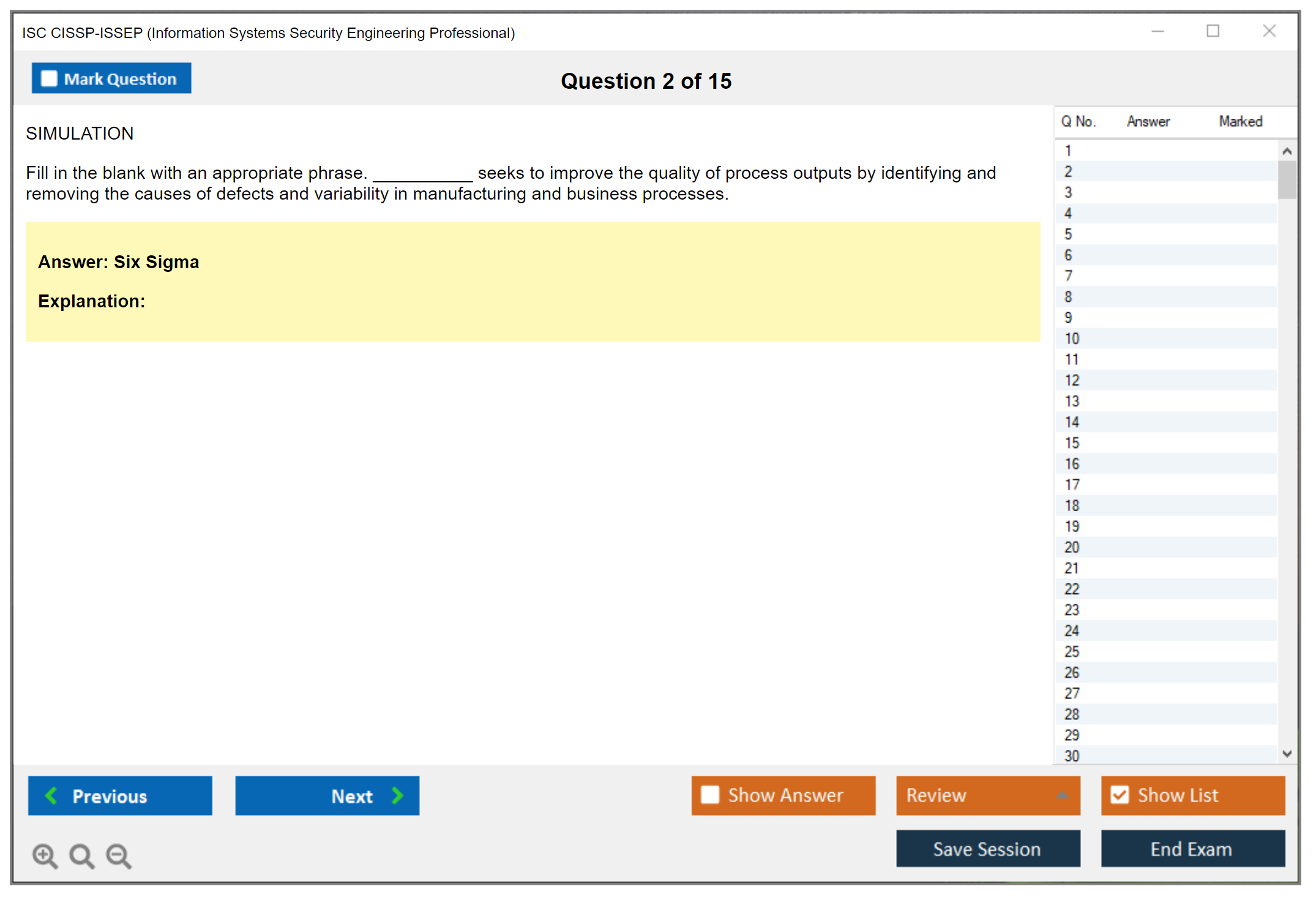
Here's what separates ISSEP from base CISSP: breadth versus depth. CISSP sprawls across eight domains at a mile-wide, inch-deep coverage level. ISSEP? It plunges way deeper into engineering processes and methodologies. You're expected to really understand the secure systems engineering lifecycle from initial requirements gathering straight through eventual decommissioning. Requirements derivation. Threat modeling exercises. Security architecture design patterns. Secure coding principles. Testing and evaluation methodologies. Continuous monitoring strategies that actually work.
The exam tests application ability. It's scenario-heavy as hell, full of questions about juggling operational requirements against security controls while staying within budget constraints and meeting compliance mandates that keep shifting. Real-world engineering challenges. The stuff that keeps you up at night.
Who actually needs this credential
If you're a security manager focused on governance and policy development, maybe CISSP-ISSMP makes more sense for your career. If enterprise architecture and designing full security frameworks gets you excited, check out CISSP-ISSAP instead because that's more your lane. But ISSEP? It's for technical people who get their hands dirty with actual implementation work. Not just theoretical frameworks.
Career-wise, we're talking senior security engineer roles, lead architect positions, ISSO jobs, technical program managers, chief security architects. Particularly in spaces where you're directly supporting federal agencies, intelligence community operations, or critical infrastructure environments where downtime equals disaster. I've seen too many outages blamed on "security measures" that were implemented without proper engineering discipline. Many government contracting positions either flat-out require or strongly prefer ISSEP holders. The salary premium is legit too. Organizations value professionals who can bridge that frustrating gap between security policy, architecture, and actual implementation teams who build stuff.
Prerequisites you need to know about
You can't just casually walk in and sit for the ISC2 concentration exam (ISSEP) on a whim. First off, you need an active CISSP in good standing. That's completely non-negotiable. Beyond that baseline requirement, ISC2 doesn't technically mandate specific years of engineering experience, but you'll struggle with this exam if you haven't actually worked hands-on in systems security engineering roles where these concepts matter daily. The questions assume you've lived this stuff.
The endorsement process? Same as other ISC2 credentials. You need someone to vouch for your experience and agree to uphold the code of ethics. Pretty standard.
What the exam actually covers
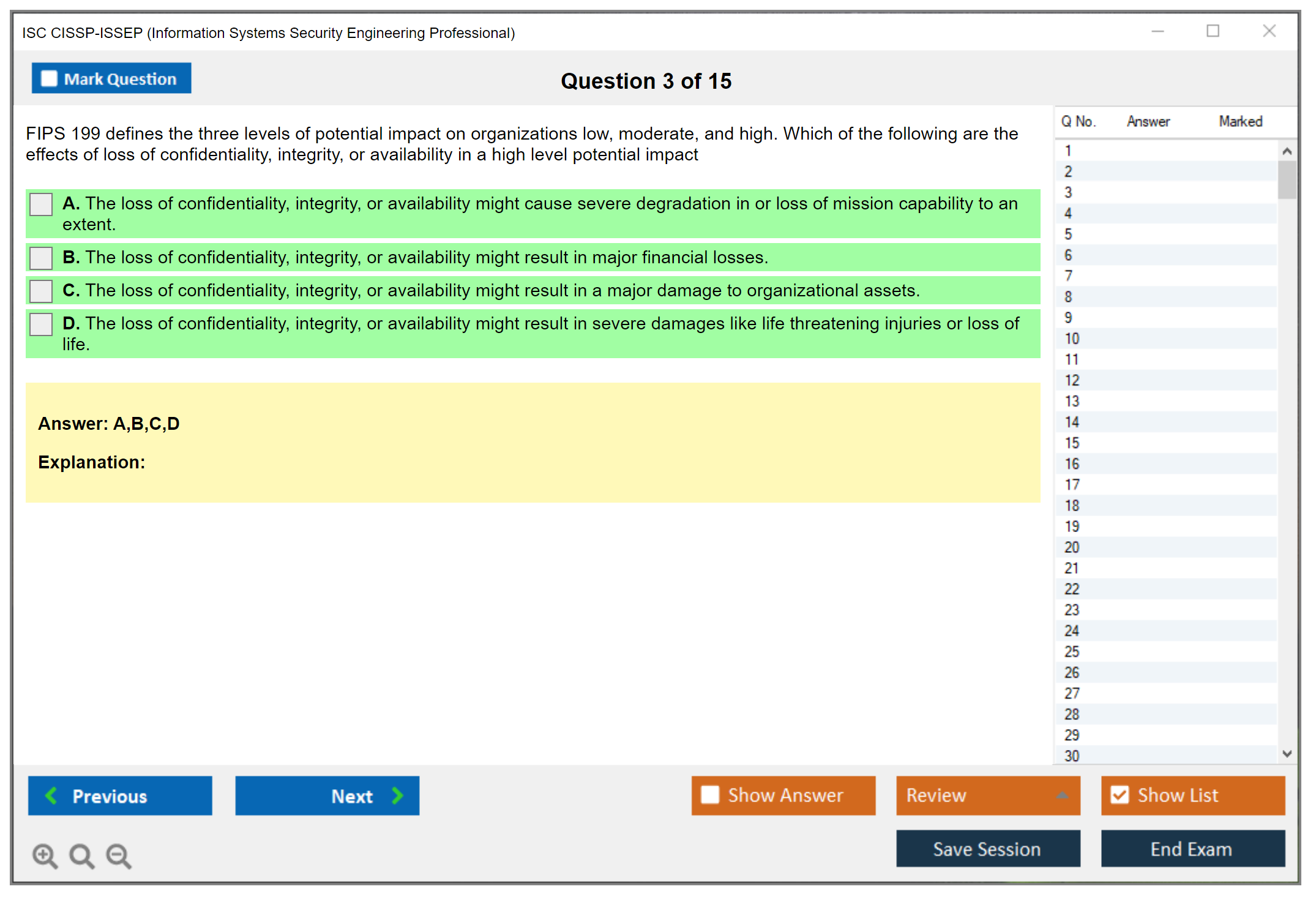
The ISSEP exam breaks down into four distinct domains. Systems Security Engineering Foundations covers basic engineering principles, lifecycle models, frameworks that guide everything. Risk Management dives into threat modeling approaches, risk assessment methodologies, control selection criteria. Security Planning, Design, and Implementation is where you prove you can actually build secure systems: requirements analysis, architecture development, implementation execution, testing protocols. Secure Operations, Maintenance, and Disposal handles everything after go-live through end-of-life.
Each domain carries different weight, but ISC2 uses scaled scoring methods, so the exact passing score remains unpublished mystery. You'll know pass or fail status immediately when you finish, but your numerical score stays hidden.
Study approach and what it costs
The exam fee runs around $599 for ISC2 members (bumps higher if you're not currently a member). Training costs vary wildly depending on your approach. Self-study using the official ISC2 outline and reference materials might cost just a few hundred bucks for full books and resources. Bootcamps can easily hit $2,000 to $3,000 if you want that structured classroom experience. Practice tests from reputable vendors tack on another $100 to $200 typically.
Most people need roughly 6 to 10 weeks of focused study time if they're already working day-to-day in engineering roles with relevant exposure. The exam itself? 125 questions, 4 hours total. Computer-based testing at Pearson VUE centers nationwide.
Renewal happens on the identical three-year cycle as your CISSP maintenance requirements, and you'll need 40 CPEs specific to ISSEP domains (plus the mandatory 20 for CISSP maintenance at the same time). Annual maintenance fee stays the same amount. You're not paying double fees, which is actually nice considering how expensive these credentials get.
CISSP-ISSEP Exam Overview and Structure
CISSP-ISSEP exam overview and structure
The CISSP-ISSEP certification (aka the ISC2 CISSP-ISSEP / Information Systems Security Engineering Professional) targets folks who don't just "understand security" but actually engineer it into systems that deploy, get maintained, receive patches, earn accreditation, and eventually face retirement.
Here's the thing: this credential focuses on systems security engineering, not memorizing facts. The exam structure pushes you hard toward lifecycle thinking and real tradeoffs instead of regurgitating definitions you crammed the night before.
Can't just register randomly. Candidates must already hold an active CISSP certification in good standing before they're allowed to register, which is the biggest CISSP ISSEP prerequisites gate out there. No CISSP? No ISSEP exam slot.
Exam format, length, and delivery (Pearson VUE)
The CISSP-ISSEP exam consists of 125 multiple-choice and advanced innovative questions administered over a 3-hour testing window. Delivered through Pearson VUE testing centers worldwide as computer-based testing (CBT), so you're getting the usual proctored environment with standard rules, lockers for your stuff, ID checks, and all that business you already experienced with ISC2 exams.
English is primary. The exam format follows ISC2's standard concentration exam (ISSEP) structure, though some regions might offer additional language options. Don't bank your entire plan on a specific language being available at your nearest site. I mean, check Pearson VUE availability early, because your study schedule can get wrecked if the only appointment slot is six weeks out.
CAT's part of this. The exam employs Computer Adaptive Testing (CAT) methodology, adjusting question difficulty based on your performance to assess competency efficiently. So the "feel" of the exam can shift as you progress. You can't really comfort yourself with "the next batch will be easier" thinking. Every question carries equal weight, there's no penalty for guessing, and you should answer every question even when you're uncertain, because leaving anything blank is the only guaranteed method to lose points you might've earned.
Exam objectives (domains) and what they cover
ISC2 maps the exam to a secure systems engineering lifecycle, from initiation through disposal. Four major domains. Depth wins over breadth.
Systems Security Engineering Foundations is where security engineering principles and concepts appear, plus stakeholder requirements and security objectives, and you'll encounter threat modeling and attack surface analysis used like actual tools, not corporate buzzwords. One detail people miss: scenarios often mix IT with OT, IoT, and cyber-physical systems, so you're expected to reason about constraints like safety, availability, and physical process impact, not just "add encryption" and declare victory.
Risk Management is the domain that gets very "real meeting energy." You'll tackle security engineering governance and risk, risk assessment methodologies for engineered systems, risk treatment and mitigation strategies, plus compliance and regulatory requirements. Security control frameworks and baselines show up here too. Security metrics and measurement can be baked into questions in sneaky ways. Also, certification and accreditation processes like RMF and NIST 800-37 matter, because authorization decisions are part of engineering outcomes, not just paperwork at the end.
Security Planning, Design, and Implementation is where most candidates either feel at home or get exposed completely. Security requirements analysis and derivation. Security architecture and design principles. Security control selection and tailoring, secure design patterns and anti-patterns, security in the SDLC, integration of security controls. Security testing and evaluation planning, plus configuration management and change control. This is where "textbook correct" answers get punished, because the question will force you to pick what fits the constraints, budget, operational impact, and regulatory expectations at the same time, and you've got to defend an engineering decision, not recite a slogan. Once had a colleague swear he knew this domain cold until he hit a question about selecting controls for a legacy industrial system with zero downtime tolerance. Textbook went out the window fast.
Secure Operations, Maintenance, and Disposal rounds it out with security operations and continuous monitoring, incident response and recovery for engineered systems, maintenance and patching strategies, security impact analysis for changes, system decommissioning and data sanitization, lessons learned and continuous improvement, and supply chain security throughout operations. Underrated domain. People forget disposal exists. Just straight-up forget.
How questions are written (and why it feels different)
Questions are scenario-based and application-focused, requiring you to apply engineering principles to realistic security challenges rather than recall facts you memorized. Expect complex prompts where multiple answers look "fine," but only one best fits the engineering tradeoff. Like when technical feasibility is high but operational impact is unacceptable, or when the cheapest option breaks compliance, or when the most secure control kills maintainability and continuous monitoring.
This is why people ask "How hard is the CISSP-ISSEP compared to CISSP?" and the honest answer is: different hard. CISSP is wide. ISSEP is deep into the secure systems engineering lifecycle and expects you to think like someone building and accrediting systems, not just advising on them. If you're more architecture-focused, you might also compare it with CISSP-ISSAP or if you live in the authorization world, CAP can feel adjacent in parts.
Practical notes people always ask about
How much does the CISSP-ISSEP exam cost? That's the CISSP ISSEP exam cost question, and you should check the current ISC2 fee listing because it changes, plus your real budget includes training, books, and maybe travel expenses. What is the CISSP ISSEP passing score? ISC2 uses scaled scoring concepts and doesn't make it a simple "X out of 100" situation you can game, so treat "CISSP ISSEP passing score" searches as informational, not a strategy you can exploit.
Study materials matter. Practice tests matter. But pick ones that explain rationale, really dig into the "why." CISSP ISSEP study materials that read like flashcards won't carry you through tradeoffs, and CISSP ISSEP practice tests are only useful if you review misses like an engineer, asking "what requirement did I ignore" instead of "what term did I forget." For related stepping stones, SSCP and CC aren't replacements, but they can be good context for teammates earlier in their careers.
Don't ignore maintenance. CISSP ISSEP renewal requirements track with keeping your CISSP active, paying fees, and earning CPEs, because ISC2 treats concentrations like extensions of the core credential, and if your CISSP drops, your ISSEP status is going to have a bad day too. For the official exam page, see CISSP-ISSEP or the shorthand ISSEP.
CISSP-ISSEP Exam Cost and Total Budget Planning
CISSP ISSEP exam cost: the $599 investment
The CISSP ISSEP exam cost? $599 USD. As of 2026, anyway. You'll pay this upfront when registering. No payment plans, no negotiating, just straight-up $599. This fee is completely separate from whatever you already dropped on your baseline CISSP certification, so don't expect some kind of bundle discount or anything.
That $599 gets you one shot at the ISSEP exam plus application processing. Walk in unprepared and bomb it? You're shelling out another $599 for attempt number two. ISC2 doesn't even cut members a break on concentration exams, which seemed weird to me when I first researched this whole thing. Member pricing only applies to the associate-level CISSP exam, not advanced concentration credentials like CISSP-ISSAP or ISSEP.
Exam pricing stays fairly consistent worldwide when converted to local currency. You might notice small differences based on exchange rates and whatever regional tax rules exist where you're testing.
Training costs that actually add up fast
Look, that $599 exam fee? Just your entry ticket. Official ISC2 CISSP-ISSEP training courses cost anywhere from $2,500 to $3,500 for instructor-led bootcamp formats. I've seen some climb even higher depending on who's running it and whether they bundle extras like practice exams or post-course mentoring into the package.
Self-paced online training runs cheaper but still hits hard. Typically $800 to $1,500 depending on content depth and platform quality. Some candidates ditch formal training entirely, going pure self-study mode, which can work if you've got solid engineering experience and enough discipline to wade through NIST publications and DoD frameworks solo.
Study materials? Budget another $200 to $500 total. CISSP ISSEP study materials like books, practice exams, reference guides all add up. Engineering reference materials such as the NIST SP 800 series, ISO standards, DoD publications are often free online, but full collections or printed versions will set you back $100 to $300. Practice test platforms and question banks range from $50 to $200 based on quality.
Total self-study budget typically lands between $1,000 and $1,500 when combining exam fee and materials. Bootcamp-based preparation including exam fee? You're staring down $3,500 to $4,500 total.
Retake fees and rescheduling penalties
Failed attempts? Full $599 examination fee again. Every single retake. No partial refunds, no "we feel bad for you" pricing. Just another $599 gone. ISC2 mandates a 30-day waiting period between failed attempts to give you study time, though 30 days isn't much if you're trying to fill knowledge gaps in systems engineering lifecycle or security governance frameworks. I knew a guy who failed twice and basically lived in the NIST documentation for three months straight before his third attempt. Not fun.
Candidates failing three times face a 90-day wait before attempt four. At that point you've burned nearly $2,400 on exam fees alone, completely separate from study materials and training investments.
Rescheduling within 48 hours of your scheduled exam? $50 fee. Rescheduling more than 48 hours out is typically free, but policies vary by testing center so check the fine print. No-show for a scheduled exam forfeits the entire $599 exam fee. Zero refund, zero transfer option. Just gone.
Retake fees should absolutely factor into your budget planning, particularly if you're coming from a non-engineering background or haven't worked extensively with NIST 800-53 controls and security engineering frameworks.
The ongoing costs nobody warns you about
Annual Maintenance Fee (AMF)? $125 for ISSEP is in addition to the $125 CISSP AMF, totaling $250 annually for both credentials. Not gonna lie, that invoice stings every year, especially if you're juggling other certs like CCSP or CSSLP too.
Travel and accommodation costs matter if your nearest Pearson VUE testing center's not local. Some people end up driving two hours each way or booking hotel rooms just to sit for the exam. There's also time away from work for exam preparation and test day itself, which represents opportunity cost even when employers support certification pursuits.
Continuing education courses to maintain both certifications post-exam? Anywhere from free webinars to $500+ conference registrations, depending on how you prefer earning CPEs.
CISSP-ISSEP Passing Score and Scoring Methodology
What is the ISC2 CISSP-ISSEP certification?
The CISSP-ISSEP certification is ISC2's concentration for people who live in the systems world. Security engineers, mostly. Security architects, ISSOs, and folks who get pulled into programs where "build it right" matters more than "patch it later". Serious credential. Niche. Worth it.
ISSEP is also an ISC2 concentration exam (ISSEP), meaning you already need the CISSP baseline and then you prove you can apply security to the secure systems engineering lifecycle, not just talk about policy at a high level. Honestly, less trivia. More engineering thinking. More "show your work" energy, even though it's still multiple choice.
CISSP-ISSEP exam overview
Pearson VUE delivers it like the other ISC2 exams. You show up, lock your stuff away, and grind through questions that feel like systems design reviews with governance and risk stapled on. Long day, honestly. Bring water.
The objectives cluster around systems security engineering foundations, risk management, security planning, design and implementation, plus secure operations, maintenance, and disposal. Look, that last part is where a lot of candidates get lazy, because disposal and lifecycle end states sound boring until you realize, wait, actually that's where data spills and compliance failures love to hide, so maybe don't skip it.
CISSP-ISSEP cost (exam fees and total budget)
Exam fee varies by region, and ISC2 updates pricing, so check the official listing when you're budgeting your CISSP ISSEP exam cost. Taxes in some locations. Add travel if your local test center availability is bad. It happens.
Training cost is where people torch money, the thing is. Self-study can be cheap if you already work in engineering governance and risk and you're comfortable reading dry references, but bootcamps can get expensive fast, and honestly they only help if you already have the base knowledge and need structure. Retakes also cost real cash, plus the time hit, plus the mental tax. Plan like you want one attempt.
CISSP-ISSEP passing score (and how scoring works)
Here's the part everyone Googles: the CISSP ISSEP passing score is not publicly disclosed by ISC2 as a specific number or percentage. Zero magic "700 equals pass" statement like some other exams. Just pass or fail.
ISC2 uses scaled scoring. The scaled score ranges from 0 to 1000 points, and candidates need to hit a passing scaled score that ISC2 sets using psychometric analysis. That's a fancy way of saying they run statistics to keep the standard consistent, and the exact cut score stays internal.
So what does "scaled scoring" mean for candidates? Your raw performance, meaning how many questions you got right, is converted to a standardized scale that accounts for question difficulty. Not all questions carry equal weight. More difficult questions contribute more to the scaled score than easier questions when answered correctly, which is why two people can feel like they had totally different exams and still land in the same pass bucket.
Also, ISC2 doesn't provide a raw score or percentage correct. You don't get a "72%" printout. You get "Pass" or "Fail". That's it. I mean, it's brutal for the anxious types, but it keeps people from building a whole test-taking strategy around minimum passing rather than mastery. Same logic as why ISC2 won't tell you exactly how many CPEs you need in each domain until you're already tracking them.
How CAT and difficulty adjustments change what you see
Computer Adaptive Testing (CAT) is part of how ISC2 keeps exams consistent across versions. CAT adjusts question difficulty based on your performance, presenting harder questions to candidates who answer correctly and easier questions to those struggling.
Candidates performing at the passing threshold tend to see a lot of medium difficulty questions. People exceeding the threshold? Progressively harder questions. And yeah, the adaptive nature means that struggling on early questions may push you into easier subsequent questions, which can limit the maximum achievable score. That's why "start strong" is more than motivational poster advice.
This methodology is designed by psychometricians so the scoring is valid, reliable, and defensible. Translation: if someone challenges results, ISC2 can back it up.
Is the passing score published by ISC2?
No. ISC2 keeps the exact passing threshold confidential on purpose. The reason is simple: they don't want candidates aiming for the minimum. They want competency across the exam objectives.
You'll still see estimates online, though. Industry experts and test-takers often guess that 65 to 75% correct tends to pass, but that is not official guidance, and honestly it can mislead you because of weighting and difficulty. Study like you need to own the material. Especially if you're treating this as a certification for security architects and engineers, not a badge for LinkedIn.
What you get after the exam
You receive an immediate preliminary pass/fail at the test center when you finish. Official results? Confirmed within 4 to 6 weeks after ISC2 finishes quality assurance review.
If you fail, you get diagnostic feedback by domain, listed as above, near, or below proficiency. That's actually useful. It tells you where your CISSP ISSEP study materials should focus next, instead of rage-reading everything again.
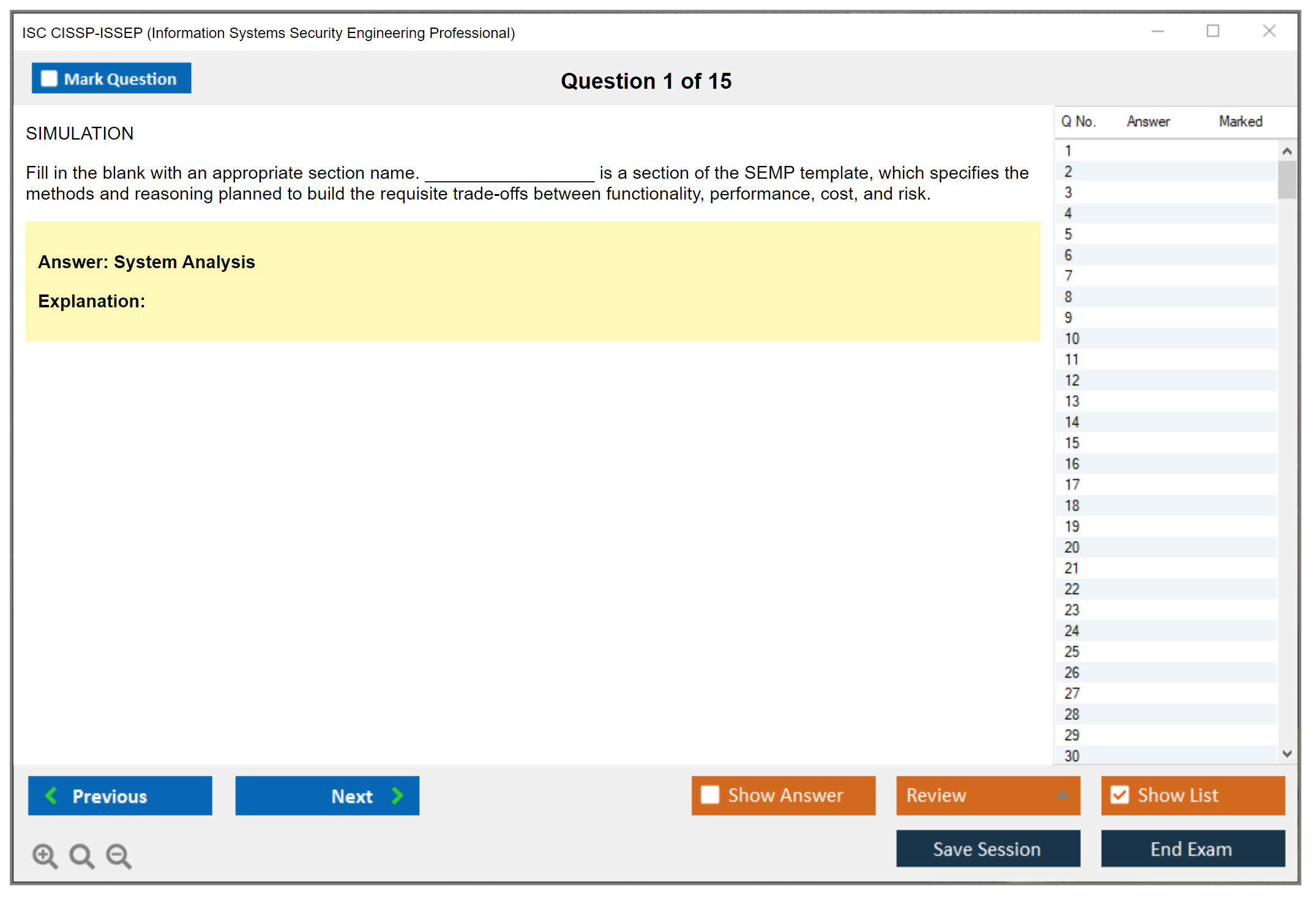
Practice questions and a realistic prep angle
I like practice tests, but only if you review the why. Engineering rationale beats memorization. If you want a targeted option, the CISSP-ISSEP Practice Exam Questions Pack is $36.99 and can help you pressure-test weak areas, especially if you pair it with your notes and go back to the objective you missed. Use it like a diagnostic. Not a cheat code. You can loop it again a week later and see if your reasoning improves with the same CISSP-ISSEP Practice Exam Questions Pack before you book a retake.
FAQs
How much does the CISSP-ISSEP exam cost? It depends on region and current ISC2 pricing, plus whatever you spend on training and CISSP ISSEP practice tests like the CISSP-ISSEP Practice Exam Questions Pack.
What is the passing score for CISSP-ISSEP? Not published. Scaled scoring, 0 to 1000, pass/fail only.
How hard is CISSP-ISSEP compared to CISSP? CISSP is broader. ISSEP goes deeper into systems security engineering credential territory.
What are the CISSP ISSEP prerequisites? You need CISSP first, plus the experience expectations ISC2 lists, endorsement, and the ethics agreement.
How do I renew CISSP-ISSEP and maintain CPEs? Follow ISC2's renewal cycle, pay AMF, earn CPEs, and keep both CISSP and ISSEP in good standing, because letting one slip is a mess.
CISSP-ISSEP Difficulty Level and What Makes It Challenging
How hard is the CISSP-ISSEP compared to CISSP?
Okay, so here's the deal. ISSEP's a different beast entirely. It's narrower, yeah, but the technical demands? Honestly, they're brutal. The CISSP covers breadth across eight security domains. Management stuff, operations, governance, you name it. You're supposed to know a bit about everything.
ISSEP completely flips that script. It digs into depth around systems security engineering principles and how you actually apply them in real scenarios.
Think about it like this. CISSP's asking what you should do when faced with a situation. ISSEP wants to know how you'd engineer a complete solution that satisfies these ultra-specific requirements and constraints while juggling stakeholder needs, budget limitations, operational requirements, and all that technical debt nobody wants to talk about. It's never just "implement MFA." It's more like "design an authentication architecture meeting NIST 800-63 requirements for AAL3, integrating with those legacy LDAP systems everyone hates, supporting mobile devices, staying within a $200K budget while maintaining 99.9% availability."
The engineering rigor's what trips people up. CISSP holders often struggle here because they're conditioned to think about security from a management or operational lens. Policies, incident response, risk frameworks, that whole world. ISSEP demands you shift into engineering mode completely. You're designing systems, deriving requirements, justifying architectural decisions based on quantitative tradeoffs. That's a mental shift requiring serious time investment.
My old manager used to joke that CISSP taught you what to worry about, but ISSEP taught you how to actually fix it. He failed ISSEP twice before passing, which probably explains the bitterness in that observation.
Engineering rigor, lifecycle, and governance form the core difficulty
This is where candidates hit the wall hard. The exam assumes you've already got the foundational security knowledge from CISSP and then it builds upon that with formal engineering methodology that's honestly pretty unforgiving. You've gotta understand systems engineering lifecycle integration. Specifically where and how security fits into each phase from initial concept through disposal.
Requirements derivation and traceability's massive here. You're translating those vague stakeholder needs like "we need this to be secure" into specific, measurable security requirements that actually mean something. Then tracking those requirements through design, implementation, testing, and operations without losing your mind.
Security architecture design means creating defensible architectures that balance security, functionality, cost, and operational constraints at the same time. Real-world tradeoffs that hurt.
Risk-based decision making goes way beyond "high, medium, low" labels. You're applying quantitative and qualitative risk assessment to engineering decisions in ways that actually matter. Understanding residual risk dynamics. Calculating annualized loss expectancy when deciding between architectural options that all kinda suck.
Compliance mapping's another beast entirely. Understanding how NIST RMF, ISO 27001, and DoD 8500 series apply to engineered systems in practice. If you haven't worked with these frameworks hands-on, the questions feel weirdly abstract and confusing as hell.
The technical depth catches people off guard every time. Cryptography implementation details. Not just "use AES-256" but actually understanding key management architectures, hardware security modules, cryptographic agility concepts, and when to use symmetric versus asymmetric approaches in specific scenarios with real constraints. Secure protocols, access control mechanisms, security testing methodologies. All at an implementation level, definitely not a conceptual one.
Supply chain security considerations throughout the system lifecycle matter way more than most people realize until they're sitting for this exam. Certification and accreditation processes specific to government and high-security environments come up frequently, which makes sense given where ISSEP originated, I guess.
Difficulty versus CISSP manifests in question complexity
ISSEP scenarios involve multiple stakeholder requirements, constraints, and technical considerations that must be balanced at once without dropping any balls. A single question might present a scenario with conflicting requirements from the business owner, compliance team, and operations staff who all want different things. You're expected to engineer a solution satisfying all of them (or explain why you can't and what the tradeoffs look like when you inevitably disappoint someone).
The CISSP-ISSAP focuses on architecture, which is adjacent territory but different. ISSEP goes deeper into the engineering process itself. The how and why of building secure systems from the ground up, brick by brick.
Who typically passes on the first attempt
Security engineers with hands-on experience in systems development and implementation consistently do well. If you've actually performed security requirements analysis, designed architectures, and conducted security testing (not just managed people who did those things), you're in good shape going in.
Professionals with DoD, intelligence community, or critical infrastructure backgrounds often find the content strangely familiar. They've lived through RMF processes that felt endless. They've dealt with DIACAP or its successors and survived.
Those with formal systems engineering education or training have clear advantages understanding lifecycle processes and requirements traceability matrices that confuse everyone else.
ISSOs and security architects who actively participate in system development projects perform noticeably better than those in purely operational or policy roles where they never touch actual systems. The exam heavily favors practitioners over managers. No question about that. If your daily work involves reviewing system designs, writing security requirements, or evaluating technical controls in real environments, you'll recognize the scenarios immediately.
Candidates who struggle typically have primarily audit, compliance, or management backgrounds without hands-on engineering experience to draw from. I've seen plenty of seasoned security professionals with CISSPs absolutely struggle with ISSEP because they've never actually engineered a system from scratch in their careers.
First-attempt pass rates aren't published by ISC2 (they keep that close), but industry estimates suggest 60-70% pass rates for well-prepared candidates with relevant experience backing them up. Candidates without engineering backgrounds should expect to invest significantly more study time. We're talking 100-150 hours versus 60-80 hours for experienced engineers who've done this stuff. The technical depth and scenario complexity make cramming completely ineffective here. You need deep understanding developed over time, not memorized facts you'll forget immediately.
CISSP-ISSEP Prerequisites and Eligibility Requirements
What is the ISC2 CISSP-ISSEP certification?
The CISSP-ISSEP certification is ISC2's systems security engineering credential for people who already live in the CISSP world, but want to prove they can carry security through engineering decisions, not just write policies and point at frameworks.
Security engineers. Architects. ISSOs. That crowd.
ISSEP's one of the ISC2 concentration exam options tied to CISSP, which means you're not starting from zero. You're stacking a specialty on top of a credential you already earned and keep active.
CISSP-ISSEP exam overview
ISC2 CISSP-ISSEP gets delivered through Pearson VUE, and the content's mostly security engineering governance and risk plus the secure systems engineering lifecycle, with more "show your work" thinking than the average memorization-heavy cert. Expect foundations, risk management, planning and design and implementation, and then the operational tail end like maintenance and disposal.
CISSP-ISSEP cost (exam fees and total budget)
People always ask about CISSP ISSEP exam cost, and honestly the exam fee's only part of what you'll spend, because most candidates end up buying training, books, and some kind of question bank to stop guessing. Self-study can be cheap. Bootcamps can get wild fast. If you want something lightweight to sanity-check readiness, I mean, a focused set like the CISSP-ISSEP Practice Exam Questions Pack can be a decent add-on, especially when you're trying to find gaps before you pay for a retake.
CISSP-ISSEP passing score (and how scoring works)
The CISSP ISSEP passing score question comes up constantly, and look, ISC2 doesn't publish a simple "get X% and you're done" statement for every situation because they use scaled scoring concepts. Actually, the thing is, what you should take from that is this: aim for mastery across domains, not perfection in one and weakness in another. The exam's built to punish lopsided prep.
CISSP-ISSEP difficulty: how hard is it and why?
Different pain entirely.
CISSP's broad and managerial, while Information Systems Security Engineering Professional goes deeper into engineering rigor, lifecycle integration, and making security requirements real when systems are being built, tested, accredited, and operated. The folks who pass first try are usually already doing security architecture reviews, requirements work, RMF packages, or test and evaluation. Not just reading about it at night.
CISSP-ISSEP prerequisites and eligibility
This is where the rules are refreshingly clear. The CISSP ISSEP prerequisites begin with one mandatory gate: you must hold an active CISSP certification in good standing. Full stop. No active CISSP, no ISSEP attempt, because the required baseline credential means you already passed the CISSP exam and completed the endorsement process before you even apply for ISSEP, and your CISSP's gotta be current and not suspended or revoked at the time of application and examination.
No extra years get added. That surprises people.
There's no additional work experience requirement beyond what was needed for CISSP, meaning the same baseline applies: 5 years of paid security work experience, or 4 years with a qualifying degree waiver. So if you're thinking ISSEP's gonna demand, say, another two years in a lab or on a defense program, it doesn't, at least not on paper. However, ISC2 strongly recommends practical experience in systems security engineering roles before attempting ISSEP, and not gonna lie, that recommendation's doing a lot of work here because the exam expects you to think like someone who's actually participated in engineering decisions and tradeoffs, not someone who only knows terms.
Experience expectations and recommended background
Even though there's no new formal experience requirement, the realistic expectation's hands-on work in at least a couple areas. Things like security requirements analysis and engineering. Security architecture design and review. SDLC security integration. Security testing and evaluation. Risk assessment and management for complex systems. Certification and accreditation processes. Security controls implementation and validation.
Requirements work's a big one. If you've never translated mission needs into security requirements, traced them through design, and then argued about verification evidence with engineering and test teams, you're gonna feel the exam pushing back. ISSEP questions love the "what's the right engineering artifact at this point in the lifecycle" angle.
SDLC integration also matters more than people admit. I'm not talking about "we have a DevSecOps tool," I mean you've been in the room when design reviews happened, you've seen how security gets watered down under schedule pressure, and you've had to pick compensating controls or change the architecture so the system can actually be approved and operated. Had a colleague once who kept claiming she knew the lifecycle cold from her PMP studies, then bombed the exam because she'd never actually sat through a single painful requirements negotiation meeting. Paper knowledge doesn't cut it here.
Helpful backgrounds include computer science, information systems, and systems engineering, plus familiarity with NIST SP 800-series, especially SP 800-160. Government and defense contractors should be comfortable with RMF and DoD security requirements. ISSO, security engineer, or security architect experience's ideal, and you should've lived through at least one complete system lifecycle from a security perspective, including disposal. Also, understanding both IT and OT security's becoming less optional every year.
Endorsement requirements and ethics agreement
After you pass, you still gotta finish an endorsement process similar to CISSP. The endorsement requirements and ethics agreement include having an active CISSP holder in good standing vouch for your professional experience and character, and the endorser needs to review your experience and confirm it fits with ISSEP domain requirements. Not just "yeah they work in security."
You also agree to the (ISC)² Code of Ethics. That applies to all ISC2 certs. No shortcuts here.
Timing-wise, the endorsement process typically takes 4-6 weeks after exam passage, and during that period ISC2 may audit your application. Around 10-15% get randomly selected, and if you're audited you may need detailed work history, references, and documentation. Be accurate. Misrepresentation can lead to denial or revocation, and that's the kind of career bruise that doesn't heal quickly.
No specific training's mandatory, but ISC2 recommends formal prep through official or approved providers, and I'd add that practice questions help you adjust to the engineering style, like the CISSP-ISSEP Practice Exam Questions Pack if you want a targeted way to pressure-test weak spots before exam day.
Best CISSP-ISSEP Study Materials and Resources
Official ISC2 resources (outline, references, training)
The materials you pick? They're everything. You need real engineering depth here, not just that broad management stuff you grabbed from CISSP).
Start with ISC2's CISSP-ISSEP Exam Outline. Free download. This thing becomes your roadmap because it lays out exactly which domains they're testing and what subtopics hide under each one. People skip this step constantly and then wonder why they're grinding through the wrong material, wasting hours on content that won't even show up. The outline is the authoritative source for what gets tested and should guide all study planning. Everything else you consume needs to map back to these domains.
That exam outline has a bibliography of reference materials forming the body of knowledge for this certification. The thing is, that reference list is pure gold. NIST SP 800-series publications pop up constantly, especially 800-160 on systems security engineering. ISO/IEC 15288 for system lifecycle processes. These aren't just suggested reading. They're literally where exam questions get pulled from.
ISC2's Official CISSP-ISSEP Training Course is the most aligned resource you'll find, whether you go instructor-led or self-paced. The official training includes practice questions, case studies, and instructor insights into common misconceptions that trip people up. It's pricey, not gonna lie, but you're getting content matching exam objectives exactly. The case studies especially help because ISSEP loves scenario-based questions where you apply engineering rigor to messy real-world problems.
Books and engineering-focused references to consider
The official training's great, but you need deeper engineering perspective. Like, way deeper.
"Systems Security Engineering" by Nancy Mead is solid for understanding the engineering foundations domain. It gets into capability engineering, security design principles, and how to actually build security into systems from day one. Some chapters drag. The practical frameworks? Worth it.
NIST SP 800-160 Volumes 1 and 2 deserve multiple read-throughs, I mean it. Volume 1 covers engineering trustworthy secure systems, Volume 2 dives into cyber resiliency. These publications inform a huge chunk of exam content, especially around lifecycle integration and design principles. I've seen people skip Volume 2 thinking it's optional. Bad move.
For risk management, lean on NIST 800-37 (Risk Management Framework) and 800-39 (Managing Information Security Risk). You probably touched these for CISSP, but ISSEP expects you to apply them at the engineering level. How do you actually implement these frameworks when designing systems? That's the question.
The DoD's "Systems Security Engineering: An Integrated Approach to Building Trustworthy Resilient Systems" is another one showing up in the reference bibliography. Dense stuff. If you're working in government or defense, you've probably seen this already.
Study plan (4,8 weeks vs 8,12 weeks)
Plan for 60-150 hours of focused study depending on background. Experienced security engineers sit at the lower end and those new to engineering roles need more time.
Already doing systems security engineering work? You might knock this out in 4-6 weeks with 2-3 hours daily. Coming from pure management or analyst background? Plan for 8-12 weeks minimum.
Week one's for outline review and self-assessment. Figure out which domains you already know versus which ones need heavy lifting. Most people struggle with the engineering foundations domain if they haven't done actual systems engineering work. Risk management usually feels familiar if you passed CISSP, but applying it to engineering contexts is a different beast entirely.
Spend weeks 2-4 working through each domain systematically. Read the reference materials. Take notes on frameworks and processes. Then do practice questions to test understanding.
Weeks 5-6 should be practice test heavy. Our CISSP-ISSEP Practice Exam Questions Pack at $36.99 gives you scenario-based questions that mirror the actual exam format.
Week 7-8 is review and weakness targeting. Go back to domains where you're scoring below 70% on practice tests. Focus on understanding why answers are correct, not just memorizing them.
Create a study checklist mapped to each domain and subdomain from the exam outline. Check off topics as you master them. This keeps you honest about coverage and prevents that last-minute panic when you realize you completely skipped a subdomain.
Join online study groups or forums where people discuss ISSEP-specific challenges. The CISSP-ISSAP and CISSP-ISSMP communities overlap a bit, but ISSEP has unique engineering focus that benefits from peer discussion.
Don't skimp on hands-on application if you can help it. Try mapping a real project at work to the systems security engineering lifecycle. Walk through how you'd apply security governance at each phase. That practical application makes the concepts stick way better than just reading about them. The exam tests your ability to apply engineering rigor to security problems, not just regurgitate definitions.
Conclusion
Wrapping up: is CISSP-ISSEP worth it for you?
Honestly? Not everyone needs this.
The CISSP-ISSEP certification's incredibly niche. Systems security engineering lifecycle, governance, risk frameworks. If you're not elbow-deep in that world daily, it'll feel like massive overkill. I mean, why torture yourself with something that doesn't match your actual job responsibilities or career trajectory when there are dozens of other certs that might serve you better depending on where you're headed professionally? My old manager kept pushing for everyone on the team to get it, but half of us were doing basic vulnerability scans and writing incident reports, not designing secure architectures from the ground up.
But here's the thing: if you're designing secure architectures, leading engineering teams, or trying to break into an ISSO or security architect role, it's one of the best credentials out there. It validates that you understand the engineering side of security, not just policy or compliance checkboxes.
The exam's brutal. You already know that from the CISSP grind, but this one demands depth in a narrower band of topics. The questions assume you've actually lived through some of these engineering challenges in production environments, not just read about them in a textbook or Wikipedia article. The CISSP ISSEP exam cost (around $599 last I checked, plus AMF and any training you invest in) isn't trivial either, so you'll want to walk in prepared. That means treating CISSP ISSEP study materials seriously, pulling from official ISC2 references, solid engineering texts, and ideally some hands-on projects or job experience that maps to the domains.
Won't sugarcoat it.
The passing score mystery (ISC2 doesn't publish the exact number because of scaled scoring) stresses people out completely. But if you're consistently hitting 75 to 80% on reputable CISSP ISSEP practice tests and you can explain why wrong answers are wrong, you're in decent shape. Most folks I know who passed spent 6 to 10 weeks of focused study. They reviewed missed questions like their career depended on it (because, well, it kinda does). They scheduled the exam when they felt ready, not when some arbitrary deadline forced them.
Don't forget the CISSP-ISSEP prerequisites: you'll need an active CISSP first, plus ideally 2 to 5 years in security engineering or a related role. Wait, actually the prerequisites are a bit flexible depending on your background, but you get the idea. And after you pass, the CISSP-ISSEP renewal requirements kick in. CPEs every three years, AMF annually. If you're staying current in the field that's usually not a problem.
If you're serious about nailing this thing, grab a quality resource like the CISSP-ISSEP Practice Exam Questions Pack. Practice tests are where the rubber meets the road. They expose your weak spots, force you to think like ISC2 wants you to think, and build the stamina you'll need for 125 questions over 3 hours.
Good luck.