GPEN Practice Exam - GIAC Penetration Tester
Reliable Study Materials & Testing Engine for GPEN Exam Success!
Exam Code: GPEN
Exam Name: GIAC Penetration Tester
Certification Provider: GIAC
Corresponding Certifications: Security Administration , GPEN

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
GPEN: GIAC Penetration Tester Study Material and Test Engine
Last Update Check: Mar 19, 2026
Latest 385 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena GIAC GIAC Penetration Tester (GPEN) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
GIAC GPEN Exam FAQs
Introduction of GIAC GPEN Exam!
GIAC GPEN is an exam that tests a candidate's knowledge and skills related to the secure administration of a variety of platforms, including Windows, Linux, UNIX, Mac OS X, and mobile devices. It is designed to verify that the candidate has the ability to configure and maintain secure systems, perform security assessments, and respond to security incidents.
What is the Duration of GIAC GPEN Exam?
The GIAC GPEN exam is a 4-hour long exam.
What are the Number of Questions Asked in GIAC GPEN Exam?
The GIAC GPEN exam contains 125 questions.
What is the Passing Score for GIAC GPEN Exam?
The passing score required for the GIAC GPEN exam is 74%.
What is the Competency Level required for GIAC GPEN Exam?
The GIAC GPEN exam is designed to assess a candidate's knowledge and skills in the areas of penetration testing and ethical hacking. The exam is intended for individuals who have a minimum of two years of experience in the information security field. Candidates should possess a basic understanding of networking, operating systems, and scripting, as well as the ability to use current tools and techniques to identify and exploit vulnerabilities.
What is the Question Format of GIAC GPEN Exam?
The GIAC GPEN exam consists of multiple-choice and lab simulations.
How Can You Take GIAC GPEN Exam?
The GIAC GPEN exam can be taken either online or in a testing center. To take the exam online, you must have access to a computer with a webcam and a reliable internet connection. You will need to create an account on the GIAC website and purchase the exam. Once you have purchased the exam, you will be able to access the exam from your account. To take the exam in a testing center, you must register for the exam on the GIAC website and then locate a testing center near you. You will need to bring a valid form of identification to the testing center on the day of the exam.
What Language GIAC GPEN Exam is Offered?
The GIAC GPEN exam is offered in the English language.
What is the Cost of GIAC GPEN Exam?
The GIAC GPEN exam is offered for a fee of $799 USD.
What is the Target Audience of GIAC GPEN Exam?
The GIAC GPEN exam is targeted towards IT professionals who wish to demonstrate their knowledge and experience in the area of penetration testing and ethical hacking. The exam is designed to assess an individual’s ability to identify security vulnerabilities and develop strategies to mitigate them.
What is the Average Salary of GIAC GPEN Certified in the Market?
The average salary for a GIAC GPEN certification holder is approximately $90,000 per year. However, salaries can vary significantly based on a variety of factors, such as experience, location, and industry.
Who are the Testing Providers of GIAC GPEN Exam?
GIAC offers the GPEN exam through Pearson VUE. Pearson VUE is a global leader in computer-based testing for certification and licensure exams.
What is the Recommended Experience for GIAC GPEN Exam?
The recommended experience for the GIAC GPEN exam is a minimum of two years of experience in the field of penetration testing. This experience should include the ability to demonstrate a comprehensive understanding of the tools and techniques used to conduct penetration testing, as well as the ability to interpret the results of such tests. Additionally, candidates should have experience in the areas of network security, computer forensics, and vulnerability assessment.
What are the Prerequisites of GIAC GPEN Exam?
The Prerequisite for GIAC GPEN Exam is that the candidate must have a minimum of two years of information security experience. The candidate should also have a solid understanding of the topics covered in the exam, including network security, cryptography, authentication and authorization, web application security, and system security.
What is the Expected Retirement Date of GIAC GPEN Exam?
The official website to check the expected retirement date of GIAC GPEN exam is https://www.giac.org/certification/retirement-dates.
What is the Difficulty Level of GIAC GPEN Exam?
The GIAC GPEN exam is considered to be moderately difficult. It is designed to test the knowledge and skills of a security professional in the areas of network penetration testing, vulnerability assessment, and security auditing.
What is the Roadmap / Track of GIAC GPEN Exam?
The GIAC GPEN certification roadmap consists of the following steps:
1. Become familiar with the GIAC GPEN exam objectives.
2. Take the GIAC GPEN practice exam to assess your knowledge and identify areas for improvement.
3. Purchase the GIAC GPEN study guide and read through it thoroughly.
4. Take the GIAC GPEN exam and pass with a score of at least 70%.
5. Receive your GIAC GPEN certification and add it to your professional credentials.
6. Maintain your GIAC GPEN certification by taking continuing education courses and attending conferences.
What are the Topics GIAC GPEN Exam Covers?
The GIAC GPEN exam covers the following topics:
1. Network Security: This topic covers topics such as network security architecture, network security technologies, network security policies and procedures, and network security threats and vulnerabilities.
2. System Security: This topic covers topics such as system security architecture, system security technologies, system security policies and procedures, and system security threats and vulnerabilities.
3. Application Security: This topic covers topics such as application security architecture, application security technologies, application security policies and procedures, and application security threats and vulnerabilities.
4. Data Security: This topic covers topics such as data security architecture, data security technologies, data security policies and procedures, and data security threats and vulnerabilities.
5. Compliance and Auditing: This topic covers topics such as compliance and auditing standards, compliance and auditing processes, and compliance and auditing tools.
6. Incident Response: This topic covers topics such as incident response planning,
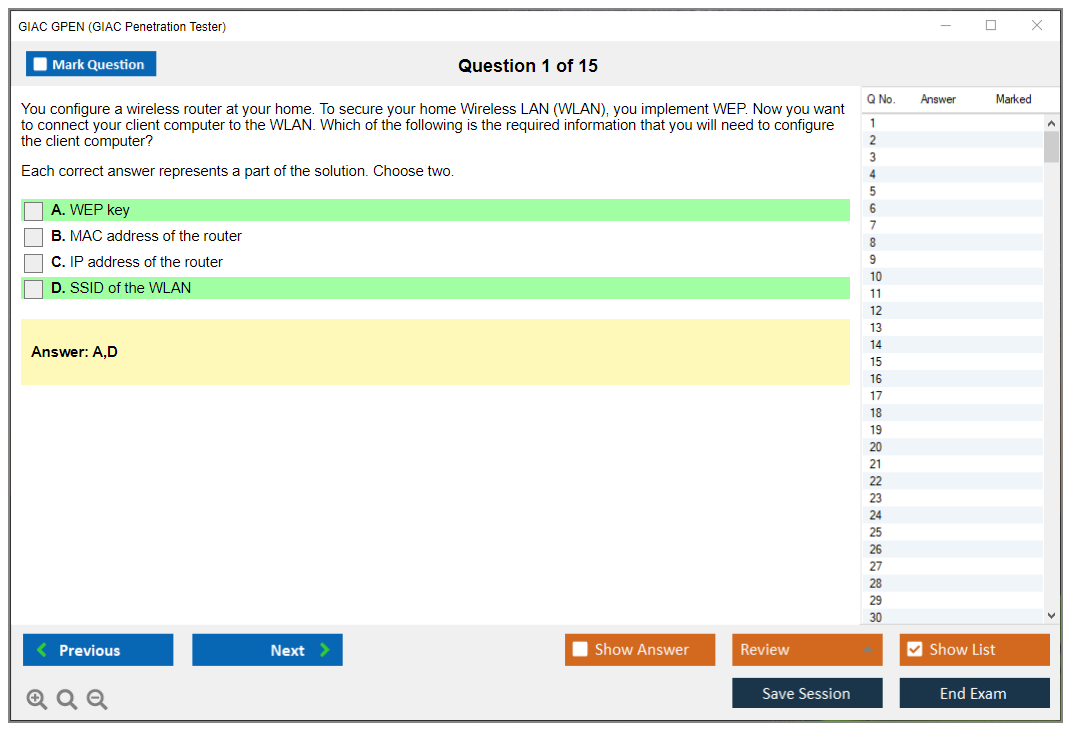
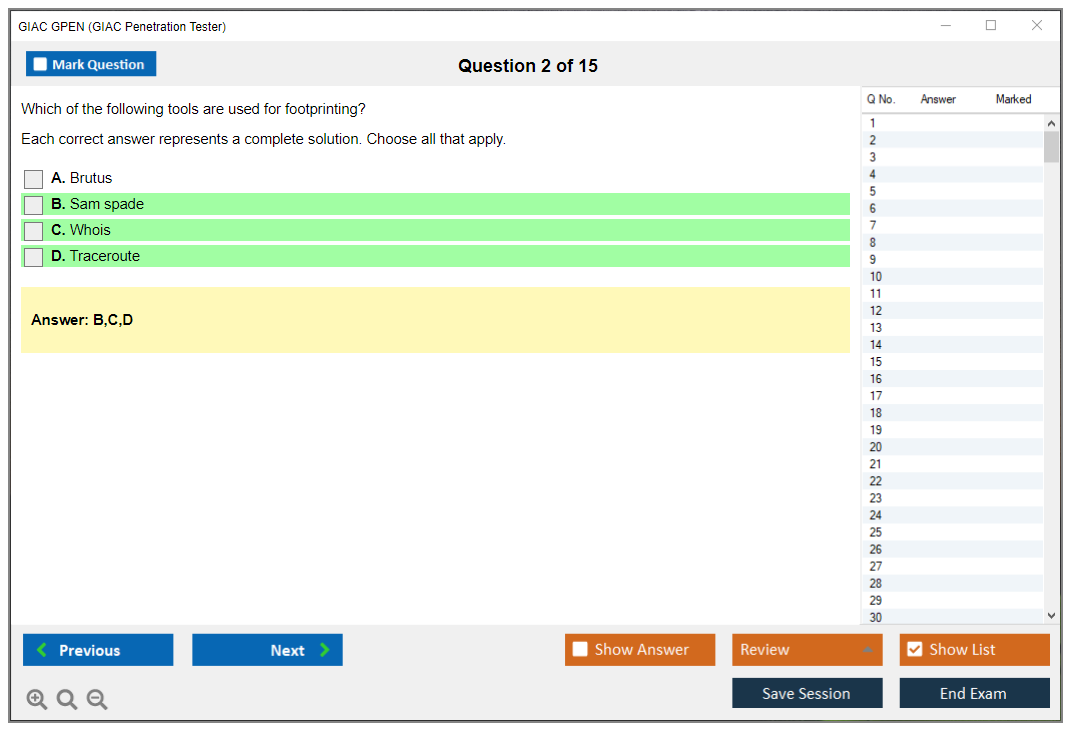
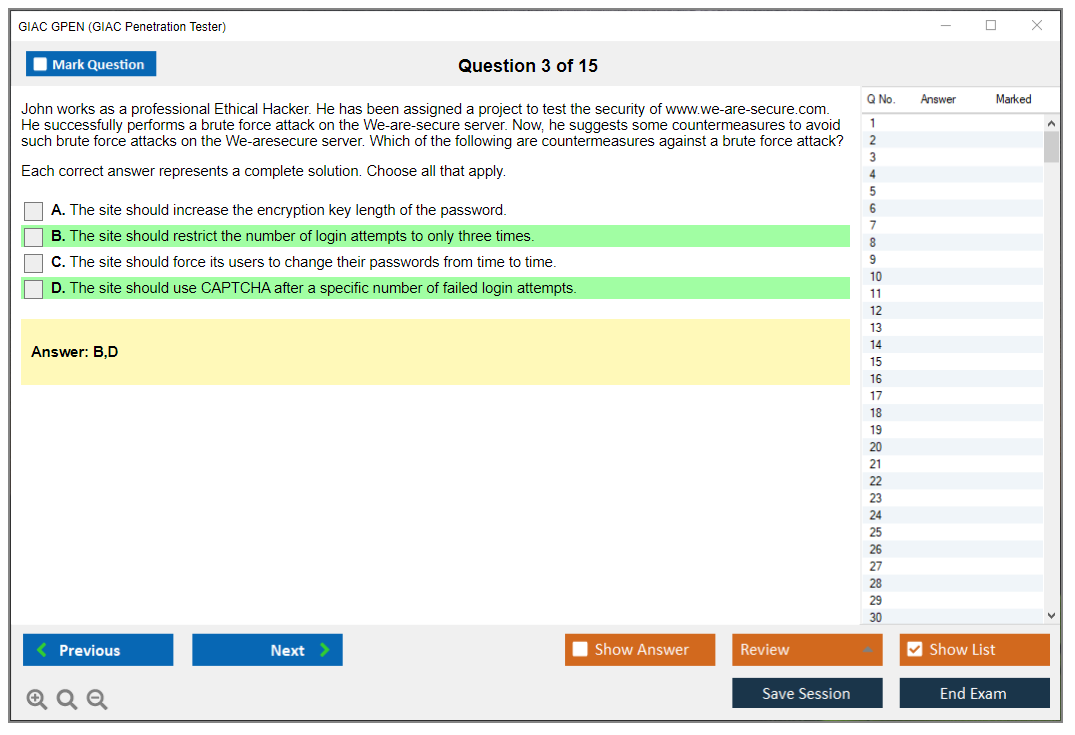
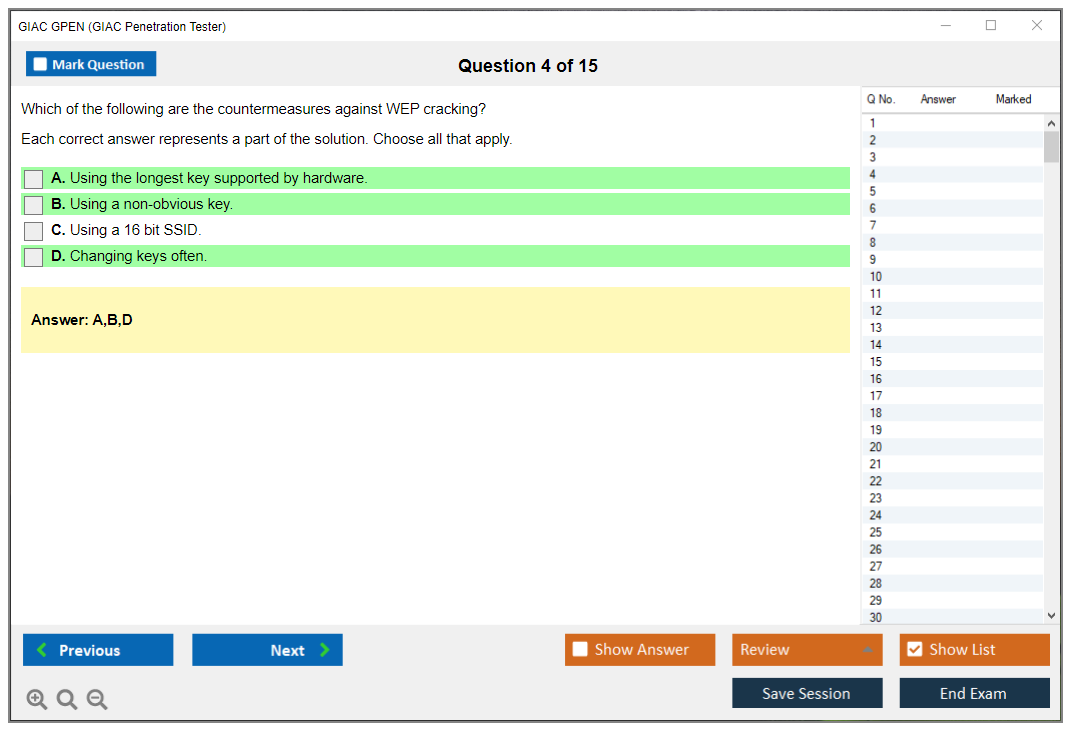
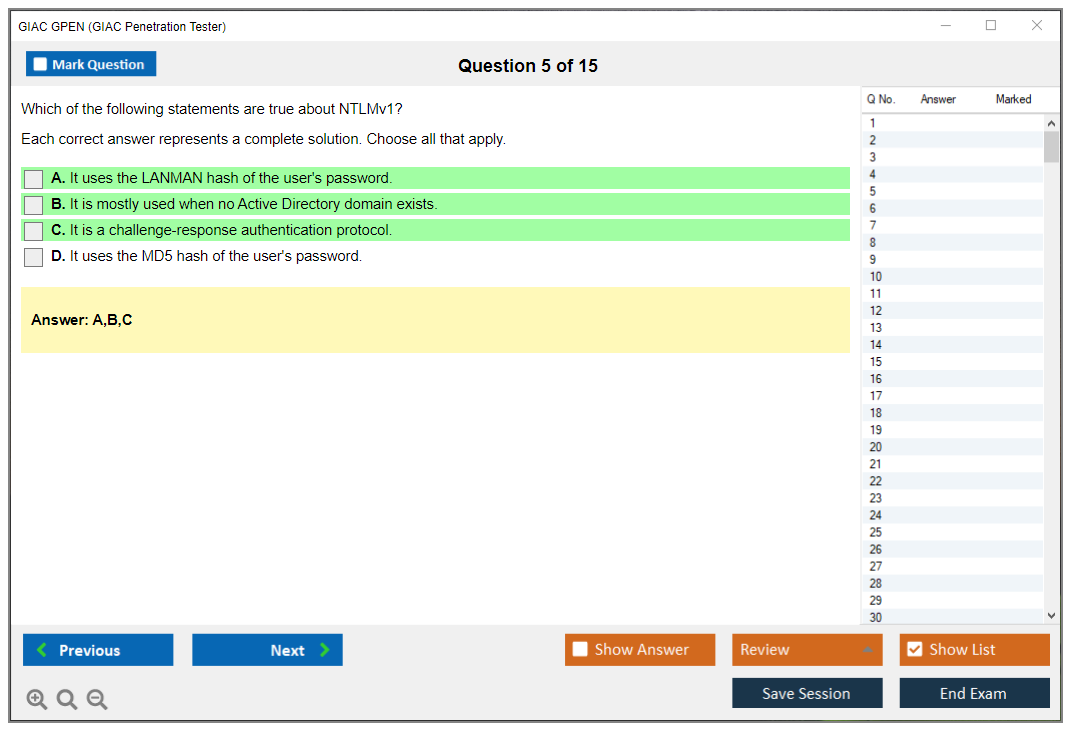
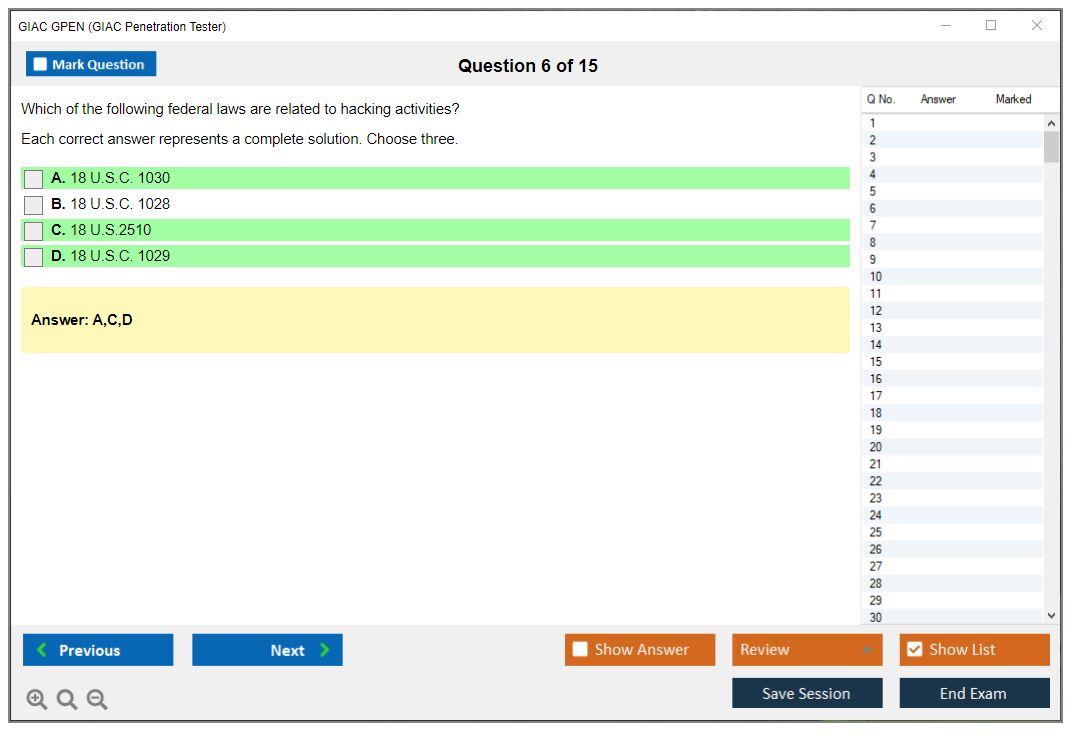
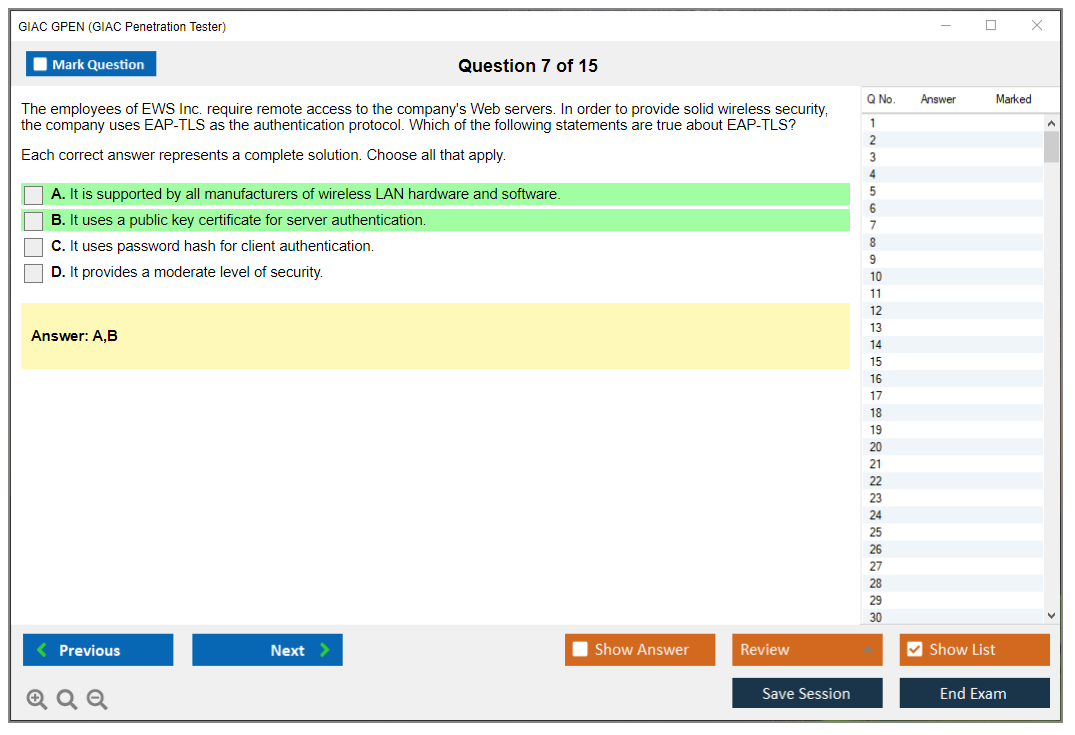
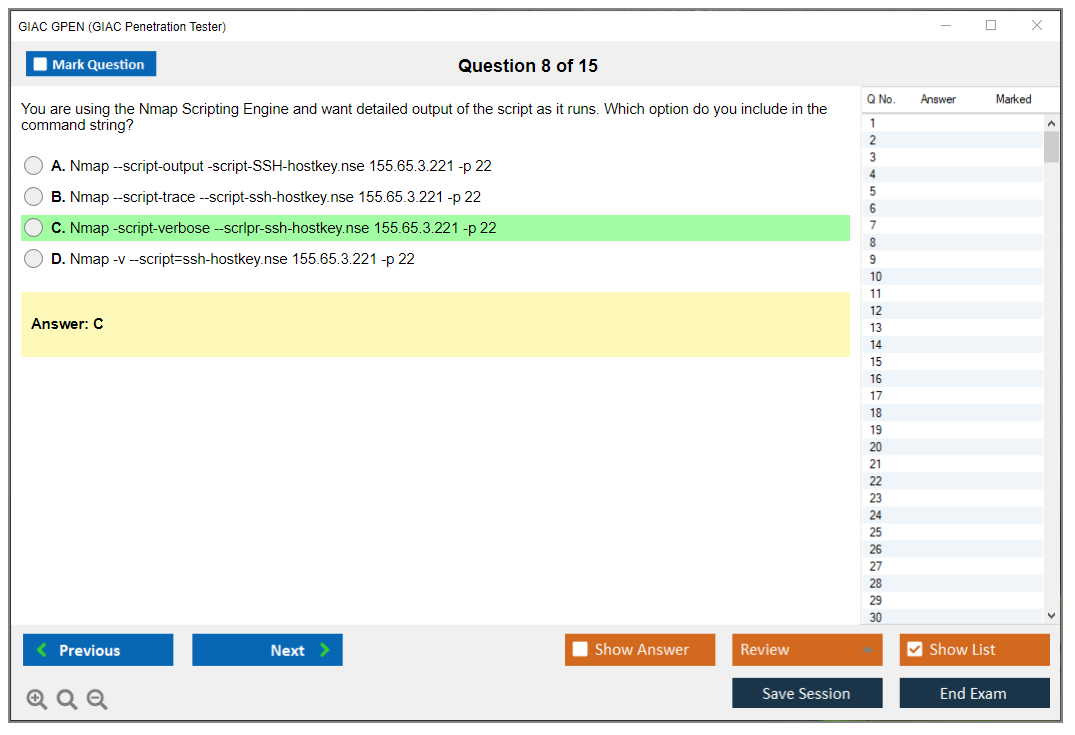
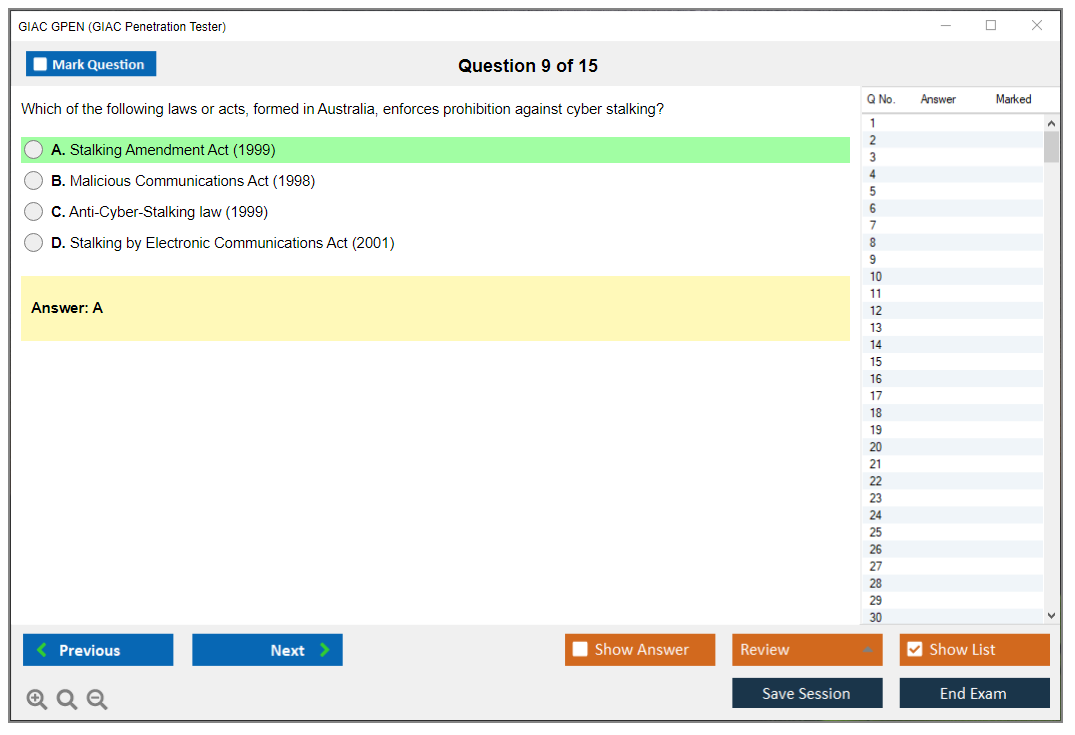
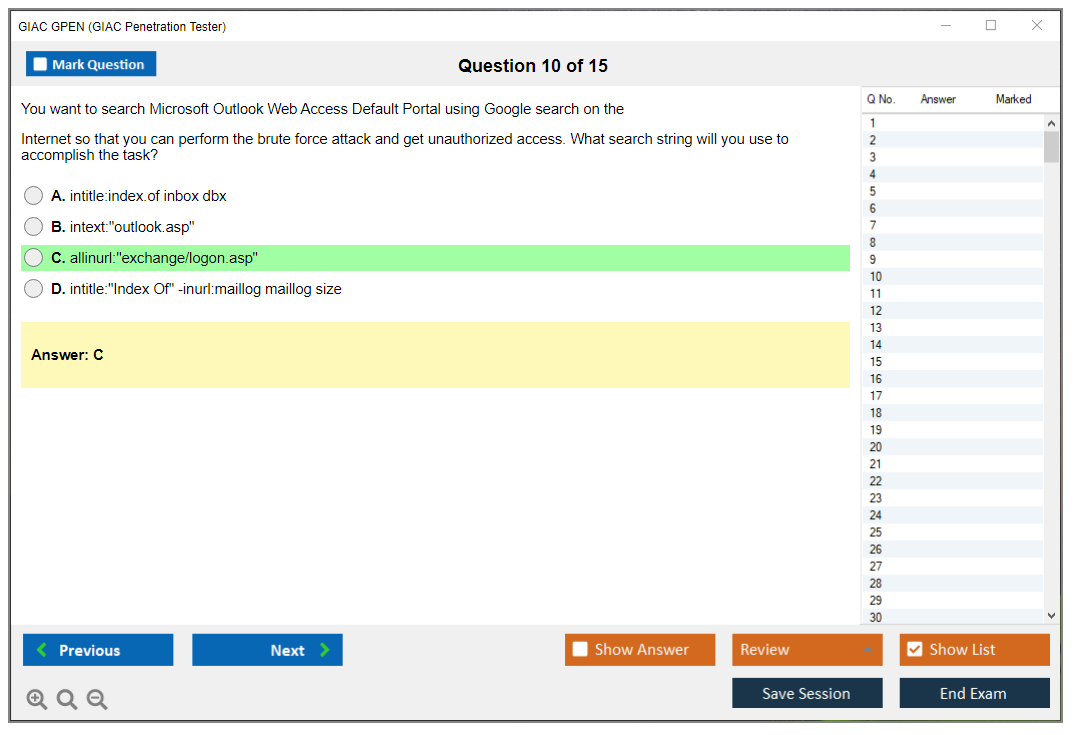
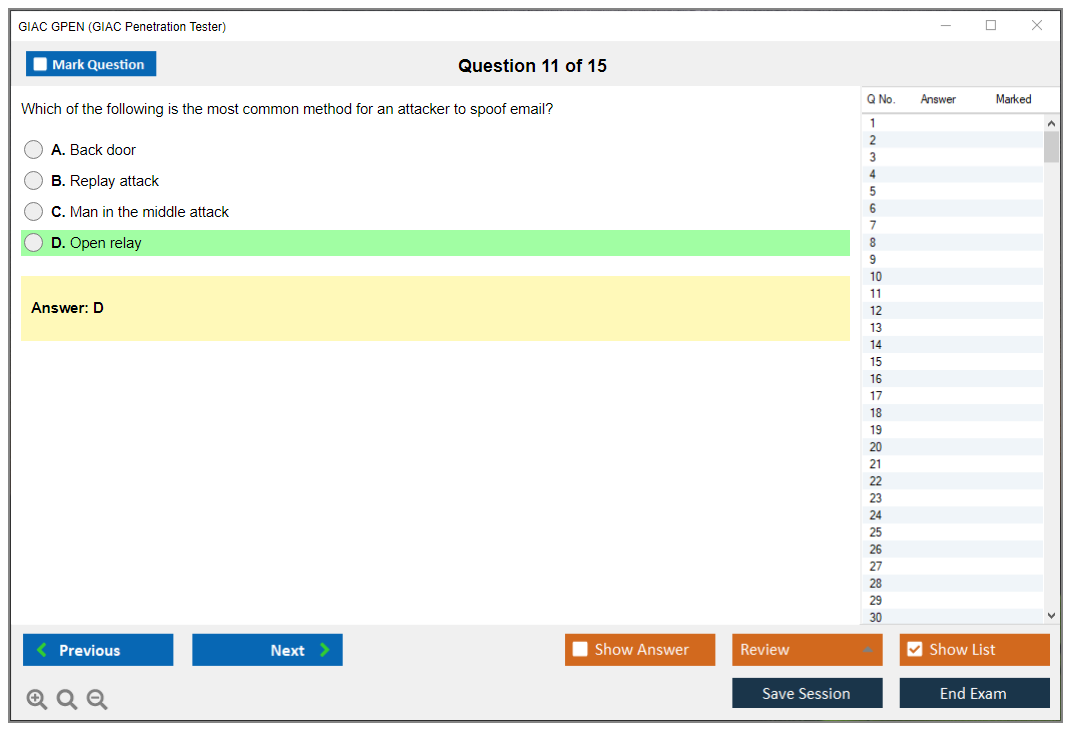
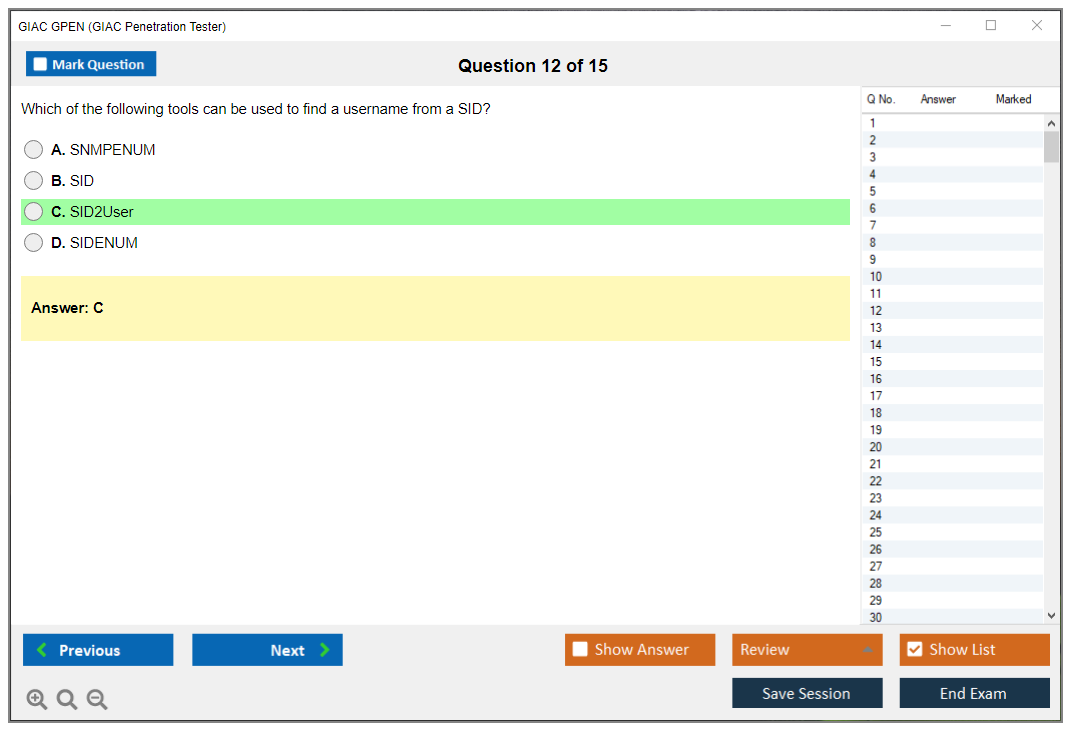
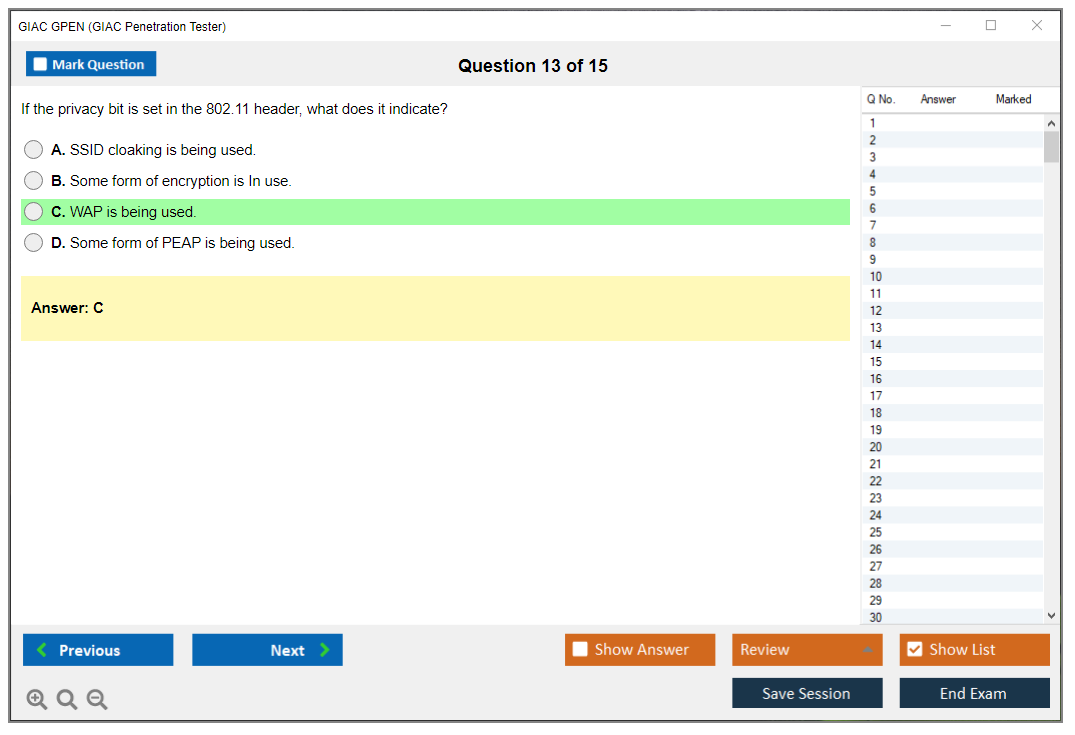
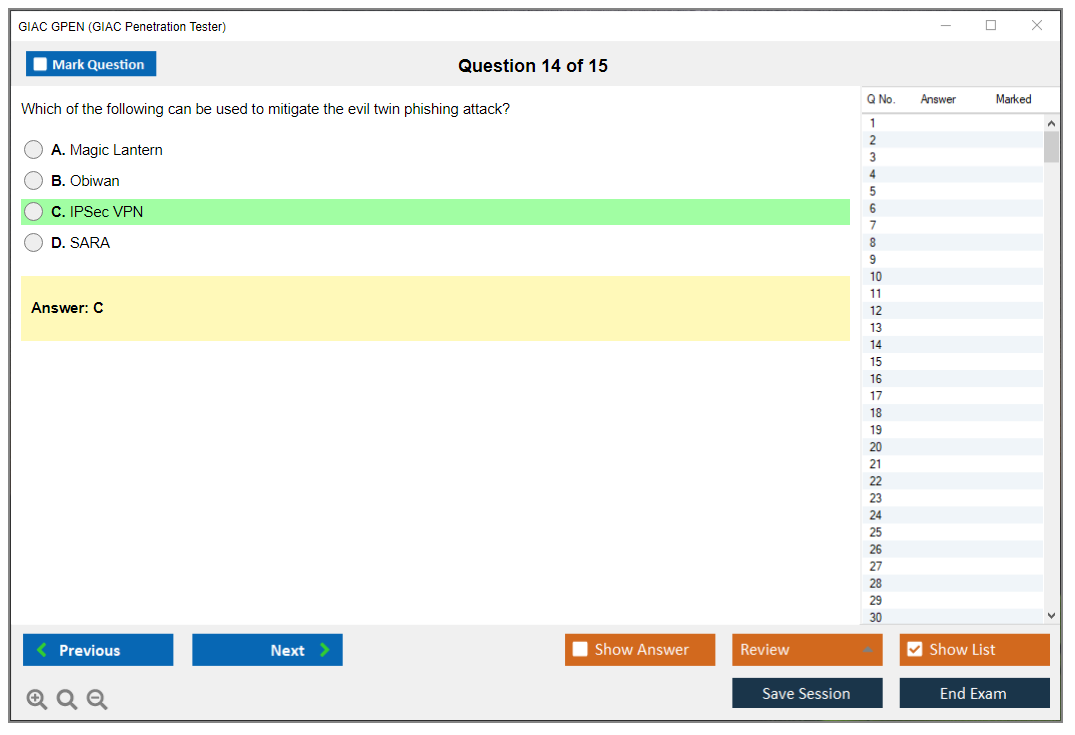
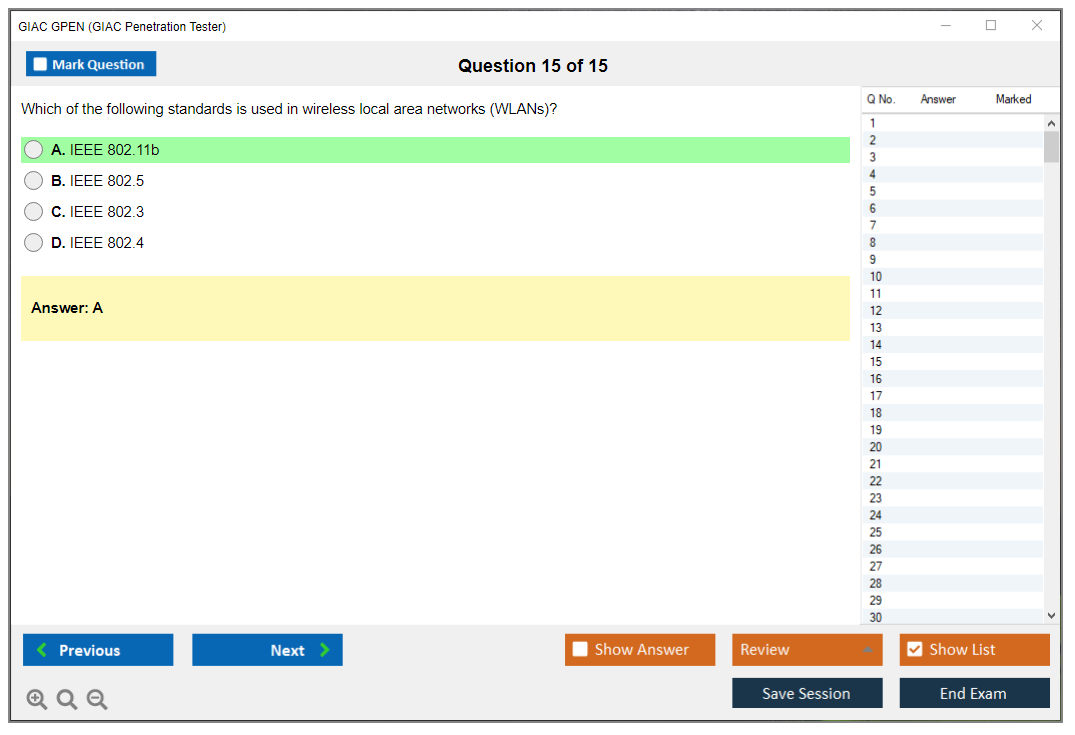
What are the Sample Questions of GIAC GPEN Exam?
1. What is the purpose of a vulnerability assessment?
2. How can a network be protected from malicious code?
3. What is the difference between a false positive and a false negative in a vulnerability scan?
4. What is a honeypot and how is it used to detect malicious activity?
5. How can an organization protect itself from phishing attacks?
6. What is the difference between a penetration test and a vulnerability assessment?
7. What is the purpose of a port scanner?
8. What is the most common type of attack used to exploit a system?
9. How can a system administrator detect suspicious network traffic?
10. What is the best way to respond to a security incident?
GIAC GPEN (GIAC Penetration Tester) What Is the GIAC GPEN (GIAC Penetration Tester) Certification? What Is the GIAC GPEN (GIAC Penetration Tester) Certification? The GIAC GPEN certification is one of those offensive security credentials that actually carries weight when you're trying to prove you can break into systems ethically. This isn't another multiple-choice exam where you memorize facts and forget them three weeks later. This thing actually tests whether you understand penetration testing methodology from the initial reconnaissance phase through exploitation, post-exploitation activities, and then writing reports that clients can use to fix their security posture instead of filing them away. GIAC stands for Global Information Assurance Certification. They've been around since 1999, started by SANS Institute (you know, the folks who run those week-long training bootcamps that'll cost more than a decent used car but actually teach practical skills instead of theoretical nonsense... Read More
GIAC GPEN (GIAC Penetration Tester)
What Is the GIAC GPEN (GIAC Penetration Tester) Certification?
What Is the GIAC GPEN (GIAC Penetration Tester) Certification?
The GIAC GPEN certification is one of those offensive security credentials that actually carries weight when you're trying to prove you can break into systems ethically. This isn't another multiple-choice exam where you memorize facts and forget them three weeks later. This thing actually tests whether you understand penetration testing methodology from the initial reconnaissance phase through exploitation, post-exploitation activities, and then writing reports that clients can use to fix their security posture instead of filing them away.
GIAC stands for Global Information Assurance Certification. They've been around since 1999, started by SANS Institute (you know, the folks who run those week-long training bootcamps that'll cost more than a decent used car but actually teach practical skills instead of theoretical nonsense nobody uses). The GIAC Penetration Tester exam sits in their offensive operations track alongside other certs like GWAPT for web app testing and GXPN for exploit development, but GPEN's the foundational one most people start with when making that transition from blue team to red team work.
GPEN fits into GIAC's broader portfolio as the go-to credential for general penetration testing. Compare it to something like GCIH which focuses on incident handling, or GSEC covering security fundamentals. GPEN's squarely in the "I break things professionally" category. It's recognized by DoD for 8140/8570 compliance, which matters a lot if you want government contracts or work with federal agencies. Private sector employers in finance, healthcare, and tech also respect it because it's tied to SANS GPEN training, which has this reputation for being brutally practical.
The core focus here? Validating you can actually perform security assessments in the real world, not just talk about them at conferences. We're talking actual workflows: scoping an engagement properly, running Nmap scans without getting caught by IDS systems, exploiting vulnerable services when you find them, escalating privileges on Windows and Linux boxes, cracking passwords. Then documenting everything so a non-technical executive understands why they should care enough to allocate budget. It's about demonstrating you understand attacker methodology and can apply it ethically without causing damage. Not memorizing CVE numbers or knowing every single Metasploit module by heart.
Who GPEN is for
This certification targets penetration testers, security consultants, and red team members who need to prove they know their stuff beyond just saying so on LinkedIn. If you're already doing pentests professionally, GPEN validates what you're doing and often helps with salary negotiations or promotions. That certification bonus is real at many companies, I'm not gonna lie.
But it's also huge for people transitioning into offensive security from other IT roles. Network administrators who want to understand the attacker perspective find it valuable. Suddenly all those firewall rules and network segmentation decisions make way more sense when you've actually tried to bypass them yourself during labs. Security analysts working on the defensive side benefit too because understanding how exploitation actually works in practice changes how you prioritize vulnerabilities and write detection rules. You stop just trusting CVSS scores blindly.
Incident responders need offensive security knowledge. How else can you understand what attackers are doing during investigations? Consultants performing vulnerability assessments want to go deeper than just running automated scanners and copy-pasting findings. All these folks are the target audience for GPEN.
Experience-wise, you should have at least 2-3 years in IT security or networking before attempting GPEN. Maybe more, honestly. Jumping straight into this without understanding TCP/IP fundamentals, basic Windows and Linux administration, and general security concepts is going to be rough. Really rough. You need intermediate to advanced practitioner-level knowledge coming in, not beginner stuff. If you're still learning what a subnet mask is or how DNS resolution works, maybe start with GISF or GSEC first to build that foundation.
Career paths that benefit? Pretty much any role in offensive security benefits from GPEN. Security consulting firms. Managed security service providers doing penetration testing. Internal security teams at larger organizations who run their own red team operations. Government contractors love it because of the DoD directive compliance making you billable on certain contracts. Finance and healthcare sectors value it because they need regular penetration testing for compliance requirements and actually want people who know what they're doing instead of script kiddies running automated tools.
What skills GPEN validates
The ethical hacking certification GIAC philosophy behind GPEN is about full understanding of the entire penetration testing lifecycle, not just the "cool" exploitation part everyone wants to do. You need to know how to properly scope an engagement, get authorization in writing, and understand legal boundaries before you even think about launching tools. Because going to prison for unauthorized access isn't a great career move.
Technical proficiency starts with reconnaissance. Passive information gathering. Active scanning. Enumeration techniques across different protocols and services. You're expected to know how to use Nmap effectively, not just run default scans and hope for the best. Understanding what ports, services, and banners tell you about a target system matters way more than memorizing syntax or command flags.
Exploitation skills cover Windows, Linux, and network environments pretty thoroughly. Common vulnerabilities. How to find them without automated scanners holding your hand. How to exploit them using frameworks like Metasploit or manual techniques when Metasploit doesn't work. Password attack methodologies are a big focus: credential stuffing, hash cracking, pass-the-hash, Kerberos attacks, all that fun stuff that actually works in real engagements instead of just CTF competitions.
Web application security testing fundamentals get covered too, though you're not going as deep as GWAPT would take you. You need to understand OWASP Top 10 issues, how to use Burp Suite effectively, and basic injection attacks that still work surprisingly often because developers don't validate input properly. I've seen SQL injection on production banking apps in 2024, which would be funny if it wasn't terrifying.
Post-exploitation is where things get interesting. This is where you demonstrate actual business impact instead of just finding vulnerabilities. Privilege escalation techniques on both Windows and Linux systems. Lateral movement across networks. Persistence mechanisms so you can maintain access. Credential harvesting from memory, registries, and configuration files. Everything you do after you get that initial foothold to demonstrate why this matters to the business, not just IT.
You also need to analyze and interpret security findings in context, write professional reports that communicate technical vulnerabilities to different audiences (executives care about different things than sysadmins), and understand remediation strategies that are actually practical. Being able to break in is one thing. Explaining what it means and how to fix it without breaking production systems is what clients actually pay for.
Command-line proficiency? Essential. Bash and PowerShell, because you're not always going to have GUI access during engagements. Actually, you usually won't. Basic scripting helps automate repetitive tasks so you're not manually doing the same thing across 50 systems. Tool expertise includes the usual suspects: Metasploit, Nmap, Burp Suite, Wireshark, Hashcat, John the Ripper, and various custom tools SANS teaches in their courses that don't have public documentation. You should be comfortable with network protocol analysis, packet inspection, and understanding what's happening at the wire level instead of just trusting what application layers tell you.
GPEN demonstrates competency in offensive security operations better than most certifications out there because it's tied directly to SANS training courses that emphasize hands-on labs over theory and actually update their content regularly based on current attack techniques.
GPEN Exam Overview and Format
GPEN exam overview and format
The GIAC GPEN certification exam is not just memorization. Actually, it's way more than that. This thing really tries to check if you can think like a penetration tester in real scenarios, not just parrot back definitions you crammed the night before. It mixes theoretical knowledge with practical "what would you do next" decision-making, and honestly that blend is why people walk out surprised even though it's open-book. The full design catches folks off guard.
It's the GIAC Penetration Tester exam, delivered on a computer-based testing platform with a locked-down, proctored setup. You can take it remote-proctored from home or book an in-person slot at a testing center if you prefer somebody else worrying about the room, the lighting, and whether your webcam hates you today. Remote proctoring's available, but you need a clean desk, a stable connection, a working webcam/mic, and a system that passes the vendor's pre-checks. Plus you'll do the usual ID verification and room scan. Testing centers are the other option, and look, for some folks that's less stress because you don't have to troubleshoot your own setup five minutes before the clock starts.
The structure is simple enough. 115 questions. 3 hours total. Do the math and you're sitting at roughly 1.5 minutes per question, which sounds fine until you hit a long scenario stem. Then you realize you're second-guessing a command flag, and suddenly you're "borrowing" time from later questions. Time pressure's real.
Question types include multiple choice (one correct answer), multiple select (pick all that apply), and matching. A chunk of the exam's scenario-based, with realistic penetration testing situations where you're reading a short story about a target environment, constraints, scan output, or tool results. Then you choose the next step, the safest interpretation, or the best technique given scope and rules of engagement. Some items get very specific. Command syntax and tool usage comes up. Output interpretation too. Nmap results, service banners, web responses, auth failures. Little details matter.
Open-book changes everything, though not always in the "easy mode" way people assume. You can reference your materials during the test. Your notes, printed books, and the stuff you've prepared for quick lookup are fair game. But the questions tend to be deeper because GIAC knows you can search. That's the open-book paradox: more complex prompts, more "which option is best" logic, and less mercy for vague understanding, because you can't look up comprehension under a timer. Indexing becomes the whole game, not optional. If you're flipping through binders like you're trying to find a lost receipt, you're done.
Here's what I'd expect in the 115-question mix, even if GIAC doesn't publish a neat public pie chart for every version: lots of standard multiple choice to verify concepts, a chunk of multiple select that punishes sloppy reading, and a steady stream of scenarios that blend penetration testing methodology with practical constraints like scoping, evidence, and what you can ethically do. Some questions are short. Others are long and technical, with stems that read like a mini ticket from a pentest engagement. You'll need to notice the one line that changes the answer.
Multiple select has no partial credit. That matters. If you pick three options and only two are correct, you get zero for that question, so you don't shotgun it. Still, there's no penalty for guessing overall, so the strategy's answer everything. Flag the ones you're unsure about, keep moving, and come back when you've harvested easier points.
The interface includes flag-for-review functionality. You should use it, but with a plan: flag only when you've got a specific next action, like "verify the meaning of this HTTP status in my web notes" or "check my index for this meterpreter alternative." Random flagging turns into a panic review pile at the end, and that's how people burn the last 15 minutes rereading the same scenario four times. I've watched it happen through glass windows at testing centers, and the frustration's visible from the hallway.
Difficulty's mixed. Some easy. Some moderate. Some challenging, though not a perfect spread. Also, your background changes the feel: Windows-heavy admins often fly through AD-ish and host concepts, Linux folks feel comfy with command lines, web testers spot the app logic faster. GPEN expects breadth across Windows, Linux, web, and network security, so a weak area will get poked.
The GPEN passing score is 73%, which works out to about 84 correct answers out of 115. GIAC scoring's straightforward with no curving, no scaling, and the passing threshold's consistent even when exam versions rotate questions. You'll get a preliminary result immediately after you finish, then an official score report later that includes your percentage, pass/fail, and a domain-level breakdown so you can see where you were strong or where you face-planted. Those performance indicators are useful if you're planning a retake, or if you're mapping your skills to GPEN exam objectives for the job hunt.
Scheduling happens through the GIAC portal, and 2026 availability's usually pretty flexible, but you still want to book early if you need a specific week for work or travel. Remote delivery often gives you more date options, while testing centers depend on local seat availability. If you don't pass, GIAC retake policies apply, and this is where budgeting matters because GPEN exam cost plus a retake isn't a fun surprise. Your results remain accessible in your account for a good while, so you can reference the report when you're planning next steps.
A quick opinion on GPEN exam difficulty. People compare it to hands-on practical exams like OSCP, and the honest answer's they're hard in different ways. GPEN vs OSCP comes down to this: OSCP's a lab grind and proof-by-exploit, GPEN's broad, timed, and detail-heavy, with an open-book format that rewards prep and punishes slow lookup. Some candidates find GPEN tougher than expected because they over-rely on an index without understanding the concepts, or because they underestimate how much command-line precision and output interpretation shows up. The thing is, you can't fake your way through scenarios when you're under time pressure.
If you want a smoother ramp, pairing prep with adjacent cert context helps. Stuff like GSEC (GIAC Security Essentials) for fundamentals, GCIH (GIAC Certified Incident Handler) for attacker behavior and response context, and of course the dedicated GPEN (GIAC Penetration Tester) track if you're aligning to SANS GPEN training and the exam blueprint. Also worth knowing: GPEN prerequisites aren't formal gatekeeping, but practical experience's the real requirement, and your future planning should include GPEN practice tests, solid GPEN study materials, and a plan for GPEN renewal requirements after you pass, because GIAC maintenance's part of the deal with any ethical hacking certification GIAC puts its name on.
GPEN Exam Cost and Pricing Breakdown
The standalone exam fee and what you're actually getting
Okay, so here's the deal. The GPEN exam cost for 2026 sits at approximately $2,099 USD for the standalone exam registration. That's just the exam itself, nothing else bundled in, no extras whatsoever. What does that money get you? One exam attempt, remote or in-person proctoring (your choice, no price difference), two practice test attempts, your score report, and access to the GIAC certification portal where you can track everything and manage your credentials. If you pass, you get a digital badge, a certificate, public listing in the GIAC directory, and four years of certification validity before you need to worry about renewal.
The exam voucher's typically valid for four months from purchase. Miss that window? You'll need to look into extension options, which honestly can get messy. Not gonna lie, two grand is steep for a single exam attempt. Way steeper than some other security certs I've seen, especially when you compare it to something like the GSEC which follows similar GIAC pricing but validates different skills.
Training bundles versus going it alone
Here's where it gets expensive if you want the full package. We're talking serious money here. SANS GPEN training bundled with the exam runs around $7,470 USD for the OnDemand course package, which includes the course materials, exam attempt, practice tests, four months of online lab access, and those thick SANS workbooks everyone talks about indexing constantly. Live online training hits similar pricing with instructor interaction thrown in, while in-person training events command premium pricing because you get hands-on labs in a classroom setting.
Is training necessary?
Depends on your background. If you're already doing penetration testing professionally and you know your way around Metasploit, web app testing, and post-exploitation techniques, self-study might work. The exam-only route saves you over five grand. That's a massive difference we're talking about here. But if you're newer to penetration testing methodology or coming from a different security domain like incident handling (GCIH territory), that structured training might be worth the investment. I've seen people debate this for weeks in study groups.
Third-party training exists but GIAC really designs their GPEN exam objectives around SANS course content, which makes studying without it harder than some other certs. Community resources and free materials are out there, sure. Study groups help. But you're indexing blind without the official books.
The retake reality and budgeting for failure
Retakes cost the full $2,099.
No discount. None. GIAC doesn't do you any favors if you fail the first time, which is honestly frustrating when other certification bodies offer reduced retake pricing or at least some kind of consideration for people who came close. There's also a waiting period between attempts, so failing doesn't just cost money, it delays your timeline.
Pass rates aren't publicly published by GIAC, but anecdotally the GPEN exam difficulty is real. Like, seriously challenging, not some joke certification you can breeze through. This isn't a memorization test you can cram for over a weekend while binging energy drinks and hoping for the best. You need to understand penetration testing concepts deeply enough to apply them in scenario-based questions. The GPEN passing score threshold means you can't just squeak by.
Build a contingency budget. If you're self-funding, assume you might need that retake. Better safe than sorry, right? If your employer's sponsoring you, clarify their policy on failed attempts upfront. Some companies cover one attempt, period. Others will fund a retake if you were close. Get it in writing before you schedule.
Total cost of ownership and hidden expenses
The sticker price isn't everything. The thing is there's all these additional expenses people don't think about initially. You need GPEN study materials beyond what comes with the exam registration. If you went exam-only, you're buying or borrowing SANS books, maybe purchasing additional practice tests, potentially paying for lab access somewhere. Time is money too, whether that's unpaid study hours or taking time off work to attend training.
Used SANS materials float around on eBay and forums, but check the edition because exam objectives shift. An outdated book won't help you with current GPEN exam objectives content. You'll be studying irrelevant material and wasting your time. Virtual lab subscriptions for practicing exploitation techniques run $30-100 monthly depending on the platform.
Equipment matters. You need a decent computer to run VMs for practice, a webcam and reliable internet for remote proctoring, and enough disk space to handle multiple operating systems and tools at once. These aren't huge costs but they add up if you're starting from scratch.
Making the financial case to your employer
Employer sponsorship is your best bet financially. Hands down, no question. The justification angle depends on your role. If you're already in security and penetration testing's part of your job description, the ROI is straightforward. You're validating skills you use daily, the cert proves competency to clients and auditors, and GIAC credentials carry weight in government and regulated industries.
For those trying to break into pentesting, the case is trickier.
You're asking for seven grand to train for a role you don't have yet. That's a tough sell. Frame it around skill development and career progression within the company. Maybe your organization needs penetration testing capabilities and you're volunteering to build that expertise, position yourself as the solution to a problem they haven't fully recognized yet. Connect it to specific business needs, not just your personal career goals.
Group pricing exists for organizations buying multiple seats. If your team's pursuing certifications, bundle purchases and save. Academic pricing helps students and faculty, government pricing covers federal employees, but verify eligibility before assuming you qualify.
International pricing and payment logistics
GIAC prices everything in USD but accepts major credit cards regardless of your location. International candidates pay currency conversion fees on top of the exam cost. Wait, actually depending on exchange rates and your bank's policies, that can add another hundred dollars or more to your total, which nobody mentions upfront.
Tax deductibility is worth exploring. In many jurisdictions, professional development expenses are deductible if they maintain or improve skills required for your current job. Consult a tax professional because rules vary, but keep all receipts and documentation either way.
Payment plans?
Not really. GIAC wants the full amount upfront when you purchase the exam voucher or training bundle. They're not running a financing operation here. Some employers have training budget processes that spread costs across fiscal periods, but that's internal to your organization, not a GIAC financing option.
Smart money strategies for certification pursuit
Save money by studying efficiently, maximizing every resource you've got. Take both GPEN practice tests seriously as readiness indicators. They're there for a reason. Failing a practice test with a 60% score means you're not ready for the real thing, and scheduling anyway wastes two grand you'll never get back. Practice tests are included, use them strategically about two weeks and one week before your planned exam date.
Index your materials thoroughly if you went the SANS route. This is critical, not optional. The exam's open-book, and a well-organized index saves time hunting for answers when you're under pressure. Time spent indexing isn't wasted, it's studying and building your reference tool at the same time.
Consider the GPEN vs OSCP cost comparison. OSCP's cheaper upfront but requires different skills and has that brutal 24-hour practical exam where you're literally hacking machines for an entire day straight. Neither's objectively better, they validate different approaches to penetration testing. Your career goals and learning style matter more than price alone.
The four-year certification validity means you're spreading that cost over time. Compare that to certifications requiring annual renewal, and suddenly the upfront investment looks different. Still expensive, yeah, but the per-year cost is more palatable when you break it down.
GPEN Exam Objectives and Domains
GPEN exam objectives and domains (2026 view)
The GIAC GPEN certification? It's GIAC's way of confirming you won't accidentally nuke production during a real penetration test. The GPEN exam objectives are your only controllable variable here. If you map your study to them like a checklist, you'll work smarter and skip wasting hours on random rabbit holes that never appear on test day.
Six domains total. They flow like an actual engagement lifecycle, kickoff through final report delivery. That's exactly why GPEN connects with folks doing actual security work instead of just grinding CTF boxes for Internet points. Exam questions? They're scenario-heavy: what's your next move, which option keeps you out of legal trouble, what does this tool output actually mean, which finding deserves executive attention.
Short questions. Tricky wording. You're hunting "best" answers constantly.
Here's a practical breakdown for 2026, including typical weighting patterns worth planning around. Now, GIAC does shift objectives as attacker tradecraft evolves, new misconfiguration patterns emerge in the wild, and tooling standards change, so you should definitely verify against their current blueprint. But these core buckets remain pretty stable year over year.
domain 1: methodology, scoping, and rules (about 15%)
This domain owns penetration testing methodology. Pre-engagement choreography, how you scope penetration tests properly, defining constraints and what "success" even means. Plus all the legal landmines. Rules of engagement, communication protocols, safety considerations, risk management frameworks, documentation requirements including what you capture during active testing and how you escalate "holy crap this is critical" discoveries without causing panic.
White box, gray box, black box testing models. PTES framework. OSSTMM. NIST guidance documents. The actual difference between vulnerability assessments and penetration testing (they're NOT the same, despite what vendors claim). Time management when you've got limited hours. How to allocate resources across target scope.
This domain shows up in exam questions as "what's permitted under ROE," "what's the appropriate next step," "who gets notified first," and "what evidence collection is acceptable." Not glamorous content, I mean, but it's literally how you keep clients happy and avoid lawsuits.
Mapping to SANS GPEN training (SEC560): this aligns heavily with day-one process content, planning frameworks, professional conduct discussions, plus the mindset of building repeatable engagement phases. I remember spending way more time on the ROE sections than I expected during my first pass through the material, thinking it was just filler. Turns out those boring procedural details matter more than the flashy exploit chains when a client's legal team starts asking pointed questions about your authorization scope.
domain 2: reconnaissance and enumeration (about 20%)
OSINT and passive recon come first. WHOIS lookups, domain registration breadcrumbs, search engine reconnaissance and Google dorking techniques. Social media intelligence gathering with social engineering context, usually framed as "what intel can you collect without ever touching target infrastructure." Then you've got active reconnaissance. Target profiling. DNS enumeration including zone transfer attempts when admins screw up configurations. Nmap scanning strategy covering TCP versus UDP, scan type selection based on stealth needs, timing templates, and how to actually interpret results instead of just collecting pretty output.
Service enumeration and version detection techniques. OS fingerprinting approaches. Banner grabbing from services. SNMP enumeration when you find community strings (still shockingly common). NetBIOS and SMB enumeration patterns. LDAP enumeration and Active Directory reconnaissance workflows. Web application reconnaissance and technology stack identification.
This domain translates into questions showing tool output fragments. "Which Nmap flag achieves this," "what does THIS response indicate," "which service is vulnerable based on this banner." Fast wins? Do timed drills until your eyes bleed. Build index entries for common Nmap scan patterns because you'll reference them constantly under time pressure.
domain 3: exploitation and post-exploitation fundamentals (about 20%)
Exploit development basics, but we're not talking "write a zero-day from scratch." More like understanding exploitation mechanics at a conceptual level, verifying public exploits actually work as advertised, and adapting small details (payloads, ports, encoding) without accidentally bricking the target system.
Metasploit usage patterns. Exploit selection based on environmental context and vulnerability characteristics. Payload selection and delivery mechanisms. Reverse shells. Command-and-control infrastructure concepts. Pivoting through compromised hosts to reach additional network segments.
Post-exploitation enumeration workflows. Privilege escalation on both Windows and Linux systems (totally different approaches). Lateral movement strategies once you've established initial access. Credential harvesting techniques and password dumping from memory. Persistence mechanisms. Covering tracks and anti-forensics considerations, though usually discussed as "what's ethical and allowed under your SOW" rather than Hollywood hacker nonsense. Data exfiltration methods, again framed with safety guardrails.
In the real world? This domain is where people get absolutely reckless. GPEN pushes methodical approaches because you're supposed to produce documented evidence and demonstrate business impact, not create an unplanned outage that gets you fired or worse, sued.
domain 4: password attacks and authentication weaknesses (about 15%)
Password attack methodology selection based on scenario constraints. Dictionary attacks versus brute force approaches. Rainbow tables conceptually (less practical now, but still tested). Online attacks against live services. Offline cracking of captured hashes. Tools like John the Ripper, Hashcat, Hydra, Medusa. Knowing which tool fits which situation.
Windows authentication: NTLM and Kerberos basics, pass-the-hash attacks, pass-the-ticket techniques, Kerberoasting workflows, AS-REP roasting when pre-auth is disabled. Linux password handling: /etc/shadow structure and hash cracking approaches. Default credentials (still everywhere, tragically). Password spraying campaigns. Credential stuffing attacks. Password policy analysis to inform attack selection. MFA bypass concepts, usually presented carefully at conceptual level rather than detailed exploitation. Wireless password attacks like WPA2 and WPA3 handshake captures, more as "what's operationally feasible" than complete walkthroughs.
This area often becomes "identify the most effective attack for THIS specific situation" instead of "memorize every tool flag."
domain 5: web application testing fundamentals (about 20%)
OWASP Top 10 themes running throughout. SQL injection in various contexts. XSS variants: reflected, stored, DOM-based. CSRF vulnerabilities. Authentication and session management flaws. IDOR vulnerabilities. Security misconfigurations at multiple layers.
Burp Suite workflow patterns. Manual testing versus automated scanning trade-offs. Directory traversal attacks, LFI, RFI exploitation. Command injection vectors. XXE attacks. SSRF vulnerabilities. API testing approaches and REST endpoint security assessment.
Expect questions formatted like mini-triage scenarios: here's a request fragment, here's the response, what vulnerability is most likely present, what's the safest next test to confirm, what's the actual business impact, what mitigation approach makes sense. They love showing you request/response snippets. Screenshot-style descriptions are common.
domain 6: reporting, remediation, and communication (about 10%)
Professional report structure that clients actually read. Executive summary targeting non-technical stakeholders. Technical findings sections with clear reproduction steps so developers can actually fix things. Risk rating methodologies. CVSS basics and vulnerability prioritization frameworks. Actionable remediation recommendations instead of "fix it" laziness. Evidence collection: screenshots, sanitized logs, proof-of-concept code. Professional tone throughout (angry rants about "stupid developers" don't belong here). Debriefing sessions and knowledge transfer to client teams. Follow-up validation testing after remediation.
This domain's criminally underrated. Look, you can be a technical wizard, but if your report reads like a ransom note written by an angry teenager, you'll lose client trust permanently.
using objectives as your study plan (and tying to SEC560)
Use the objectives as your study spine. One objective, one page of concentrated notes, one set of essential tool commands, and one "what does the exam actually ask about this" section. Build cross-references between domains because GPEN absolutely does. Reconnaissance output directly informs exploit selection. Exploitation results drive post-exploitation enumeration priorities. Technical findings become reporting language and risk ratings.
For practice approaches, I like mixing official practice tests with targeted skill drills. Not gonna lie, if you want extra repetition on question style without burning your best material too early, the GPEN Practice Exam Questions Pack offers cheap pressure-testing for weak spots. Same link if you need it later: GPEN Practice Exam Questions Pack. The $36.99 price point makes it stupid easy to justify as "one more round of realistic reps."
quick comparisons and the stuff people ask anyway
GPEN vs OSCP: OSCP is way more hands-on exploitation grinding with extensive lab time requirements. GPEN offers broader professional engagement coverage with open-book exam format, plus way more emphasis on methodology, documentation quality, and making correct judgment calls under operational constraints.
GPEN exam cost varies wildly depending on exam-only versus SANS course bundle. GPEN passing score gets published by GIAC on their exam page, and you should treat it like a minimum target but honestly aim higher because nerves and time pressure mess with everyone. GPEN prerequisites are officially light, but practically you want solid networking fundamentals, Windows/Linux comfort, and basic scripting skills. GPEN renewal requirements follow GIAC's standard model: accumulate CPEs or eventually retake.
Resources per domain: SEC560 books and labs first (obviously), your own personalized index second, then curated tool documentation, OWASP testing guides for web app coverage, and timed mixed-question sets like the GPEN Practice Exam Questions Pack when you're ready to simulate actual exam pacing pressure.
GPEN Prerequisites and Recommended Experience
Official prerequisites versus practical reality
GIAC's official stance? Refreshingly simple.
No prerequisites whatsoever.
You can register for the GPEN exam right now, pay your money, and schedule your attempt. Nobody's checking your resume or verifying your years of experience or asking for proof of other certifications. GIAC lets you attempt the exam regardless of background, which is technically accurate but practically misleading because here's the thing: just because you can take the exam doesn't mean you should.
I've seen people attempt GPEN with minimal security background. It rarely ends well. The exam cost isn't cheap, and burning through $2,000+ only to fail because you thought "open book means easy" is a painful lesson I wouldn't wish on anyone. The practical reality? GPEN requires significant technical knowledge. Attempting it without foundational skills is setting yourself up for disappointment and an empty wallet.
What you actually need to know before starting
The recommended minimum is 2-3 years in IT security, but that's somewhat flexible depending on what you did during those years. Help desk time doesn't count the same as actively working with security tools or administering systems. If you've spent two years analyzing logs and running vulnerability scans, you're probably in decent shape. Two years resetting passwords? You need more groundwork.
Networking fundamentals are non-negotiable.
I mean really understanding TCP/IP, not just memorizing that it exists or whatever. You need to know subnetting cold, understand routing and switching concepts, and be comfortable with protocols like HTTP/HTTPS, DNS, SMB, SSH, RDP, and FTP. When the exam asks about exploitation paths through a network, you can't fake protocol knowledge. You either understand how traffic flows or you don't.
Operating system familiarity matters immensely. I'm talking Windows and Linux administration experience basically being required here. You need command-line proficiency in both environments: PowerShell and cmd on Windows, bash on Linux. If typing net user or grep feels foreign, you're not ready. The exam assumes you can work through file systems, understand permissions, manage services, and troubleshoot basic issues without hand-holding.
You know what else trips people up? They study the protocols but never actually use them. I once spent an entire weekend just playing around with DNS queries, watching how different record types behave, breaking things intentionally. Seemed like wasted time until the exam threw me a question about AXFR transfers and I knew exactly what was happening because I'd seen it fail spectacularly in my own lab.
Building blocks that make or break your success
Scripting ability separates candidates who struggle from those who breeze through sections. Bash, PowerShell, and Python are all helpful. You don't need to be a developer, but you should understand what scripts do, how to modify basic examples, and how automation works in security contexts. When you see exploit code or enumeration scripts in the course materials or GPEN Practice Exam Questions Pack, recognizing syntax and logic helps tremendously.
Packet analysis basics using Wireshark and tcpdump? They come up repeatedly.
You should be comfortable capturing traffic, applying filters, and understanding what you're seeing in packet captures. Windows Active Directory concepts matter too: domains, forests, trusts, Group Policy. Tons of real-world pentests target AD environments, and GPEN reflects that reality.
Web technologies knowledge helps with several exam domains. Understanding HTML, JavaScript, HTTP methods and headers, and basic database interaction through SQL queries gives you context for web application testing questions. You don't need to build websites, but you should understand how they work under the hood.
Self-assessment before committing money
Honestly assess your current skill level before dropping serious cash. Can you subnet in your head? Do you understand three-way handshakes? Can you write a basic bash loop? Do you know what Metasploit is and roughly how it works? If you're answering "sort of" or "not really" to multiple questions, you need more foundation.
Setting up a lab environment before studying reveals gaps quickly. Build a virtual network with vulnerable machines, install Kali Linux, try basic enumeration with Nmap, attempt to exploit a deliberately vulnerable web app. If this feels overwhelming or you're constantly Googling every single step, the thing is you need more hands-on time before GPEN.
The difference between passing the exam and being job-ready is real, but you need enough baseline knowledge to even engage with the material. Taking GSEC or CompTIA Security+ first isn't a bad idea if you're starting from scratch. Network+ helps tremendously with the networking foundations. These aren't mandatory, but they build knowledge you'll absolutely need.
When foundational certifications make sense
If you're brand new to security, jumping straight to GPEN is like learning to drive in a Formula 1 car. Possible? Technically. Smart? Not even a little bit, I mean come on.
Starting with GSEC gives you broad security fundamentals that GPEN builds upon. The GSEC covers defensive concepts, basic security operations, and foundational knowledge that makes GPEN's offensive content more digestible.
Some people take CEH first, which provides ethical hacking foundations. Others prefer the GPEN before OSCP timing approach where GPEN gives you theory and methodology, then OSCP forces you to apply it practically. There's no single correct path. Your background dictates the best progression.
Government and DoD roles often have specific certification requirements that influence timing. If your employer's paying for training and needs you certified within a certain timeframe, that changes calculations. Budget considerations matter too when planning multiple certifications. GIAC certs aren't cheap, and strategic sequencing prevents redundant spending.
Time investment based on where you're starting
Coming in with solid foundations?
Figure 4-6 weeks of focused study.
Starting from scratch or with gaps? You're looking at 3-6 months of prep work before even beginning GPEN-specific study, and that's not including the actual exam preparation time.
Building complementary skills through targeted learning accelerates readiness. Spend time with GCIH materials if incident response concepts are weak. Look at GCIA resources for deeper packet analysis understanding. Use the GPEN Practice Exam Questions Pack to identify specific weak areas, then address them systematically rather than hoping open-book access will save you.
The practical skills required for GPEN success take time to develop. There's no shortcut around hands-on experience with tools, systems, and methodologies. You can't memorize your way through this one.
Best GPEN Study Materials and Resources
What is the GIAC GPEN certification (GIAC penetration tester)?
The GIAC GPEN certification is GIAC's mainstream pentest credential, and it maps pretty cleanly to what most employers actually want when they say "do a network and web app pentest, keep decent notes, don't break production systems, and write a report that doesn't read like you just vibed your way through the assessment."
Who GPEN is for (roles and experience level)
Pentesters early in their career. Security analysts moving into offensive work, which is a big jump. Blue team folks who want to understand attacker workflows without going full exploit-dev mode. Some consultants take it because clients recognize GIAC without pushback. Simple.
What skills GPEN validates (penetration testing focus)
Think practical penetration testing methodology: scoping, recon, enumeration, common exploitation patterns, password and auth issues, basic web testing, and then reporting that doesn't make directors cry. It's an ethical hacking certification GIAC shops will accept without an argument or weird HR friction.
GPEN exam overview
Exam format (proctored, question style, time)
The GIAC Penetration Tester exam is proctored and multiple choice. Open book. That "open book" part? It's the trap. If your notes and index are bad, you'll waste time flipping pages and panic scrolling PDFs while the clock keeps moving and your heart rate spikes.
GPEN passing score (what "passing" means)
GIAC publishes a passing threshold for each exam, and for GPEN you should plan around the official number shown on the GIAC exam page. Don't treat GPEN passing score as "I'll squeak by." Aim higher so a few weird questions don't sink you. Give yourself margin for the unexpected.
GPEN exam difficulty (what makes it challenging)
Not gonna lie. GPEN exam difficulty is less about "hardest hacking ever" and more about breadth plus speed under pressure. You get hit with lots of tools, lots of terms, and you need recall plus fast lookups. Indexing's the game.
GPEN exam cost (pricing breakdown)
GPEN exam cost (what's included)
GPEN exam cost varies depending on whether you buy exam-only or bundled with training, but GIAC exams are expensive relative to most certs out there. The fee typically includes an attempt, a practice test option depending on purchase path, and the proctoring setup. Check GIAC's current pricing before you budget, because sticker shock is real.
Training bundle vs exam-only options (SANS + GIAC)
If you do SANS GPEN training (the course commonly paired is SEC560), you're paying for structured content, labs, and the whole portal experience that works. Exam-only is cheaper but assumes you already know how to self-study and lab like an adult. Look, people pass both ways, but the SANS route is the smoothest if your employer's paying and you've got the time to absorb it properly.
Retake fees and budgeting tips
Retakes aren't free. Plan for them anyway. Set aside money or get pre-approval, because the worst feeling is failing by a few points and then waiting six months because finance said no to the retake budget.
GPEN exam objectives (domains)
GPEN exam objectives and scoping
Start by reading the official GPEN exam objectives and turning them into a checklist you can actually track. Scope, rules of engagement, and safe testing habits show up more than people expect. it's "run tools," it's "run tools without being reckless and getting walked out."
Reconnaissance and enumeration
This is where your process matters a lot. DNS, network mapping, service discovery, and then digging into what those services actually are beneath the surface. Notes. Commands. Expected outputs. Tiny details that add up.
Exploitation fundamentals and post-exploitation concepts
GPEN is not a pure hands-on exploit lab exam, but it expects you to understand what exploitation is doing, how shells happen, what post-exploitation goals look like, and why privilege matters in the kill chain. Short. Clear. Get the concepts cold.
Password attacks and authentication weaknesses
Hash types, spraying vs stuffing, MFA gotchas, Windows auth basics, and common misconfigurations. Don't overcomplicate it.
Web application testing fundamentals
You need the basics: input handling, auth/session issues, and common vulns that still plague production apps. If you've done even light web testing, you're fine. If you haven't, read a web chapter and do a few practice labs before moving on.
Reporting, remediation guidance, and communication
Reporting's part of being a pentester, not just a checkbox. Findings, risk rating, reproduction steps, and remediation that a sysadmin can actually do on a Tuesday. Fragments welcome in your notes. The report shouldn't be fragments.
GPEN prerequisites and recommended experience
GPEN prerequisites (official vs practical)
Officially, there aren't strict GPEN prerequisites in the way some certs gate you with hard requirements. You want comfort with TCP/IP, Windows and Linux basics, and common security tooling. Otherwise you'll spend your whole study window learning what a port is instead of methodology.
Recommended knowledge (networking, Windows/Linux, scripting)
Know subnets cold. Know what services usually run on which ports without Googling. Be able to read logs without panic. Basic bash and PowerShell helps a ton. Python's nice but not required for passing.
Who should take GPEN before/after other certs
Security+ before GPEN is common if you're new to the field. OSCP after GPEN makes sense if you want deeper hands-on exploitation skills and the community cred. And yes, people compare GPEN vs OSCP constantly, because that's how this industry copes with decision paralysis.
Best GPEN study materials (what to use)
Official GIAC/SANS materials (books, labs, portals)
If you took SANS, use the books like a reference system, not a novel you read cover to cover. Do the labs twice minimum. Build an index while you lab, not after. That's the secret sauce behind most "I passed first try" stories you see on LinkedIn.
Third-party books and references
Grab a solid pentesting methodology reference, a web basics book, and a Windows/Linux privilege concepts refresher. Nmap docs, OWASP Testing Guide, and vendor hardening guides fill gaps nicely. I spent a whole weekend once going through old OWASP examples when I should've been outside, but those SQLi patterns stuck better than any formal training video ever did.
Building a GPEN study plan (4,12 week paths)
A 4-week plan is intense: labs every day, index continuously, practice tests on weekends when you're already tired. A 12-week plan is calmer: one domain per week, labs twice a week, and a practice test every few weeks to check retention. The right plan is the one you can actually follow after work when your brain is fried and Netflix is calling. Consistency beats weekend cram sessions that collapse by week two when life happens and motivation tanks.
GPEN practice tests and exam strategy
Official practice tests (how they work and when to take them)
Use official GPEN practice tests as diagnostics, not confidence builders. Take the first one earlier than you want, like uncomfortably early. Then you'll stop guessing about readiness. Save the last one for the final stretch, when timing and index speed matter most and you're dialing everything in.
Indexing and open-book strategy
Index everything you can't recall in 10 seconds flat. Commands, flags, definitions, and "when you see X, think Y" mappings. Keep it searchable and organized. Page numbers if you use printed books, file names and headings if you use PDFs. The exam's open-book, but it rewards open-book discipline, not open-book chaos where you're hunting for stuff mid-question.
Common question themes and time management
Expect tool output interpretation, process ordering, and "best next step" logic traps. Don't camp on one question forever. Mark it. Move forward. Circle back.
How to pass the GPEN exam (step-by-step)
Map GPEN exam objectives to your notes, labs, and index entries. Then do timed drills on weak areas until they're not weak anymore. Final week: one practice test, index cleanup, sleep, and a boring night before the exam. Don't improvise index structure last-minute. Don't rush through questions. Don't spiral on doubts.
If you want extra reps, a cheap way to pressure-test recall is a question pack like GPEN Practice Exam Questions Pack at $36.99 for drilling. Use it to find gaps, not to "memorize answers," because that habit backfires hard when wording changes or questions twist. If you do buy something lightweight for practice, I'd rather see you do GPEN Practice Exam Questions Pack plus real labbing than spend weeks collecting random PDFs you never open.
GPEN renewal requirements (maintaining certification)
Renewal cycle and continuing education
GIAC certs renew on a cycle and typically require continuing education credits and a maintenance fee. GPEN renewal requirements are straightforward if you track CPEs as you go instead of scrambling at the deadline.
Renewal options (credits vs retake)
You can renew with credits or retake the exam entirely. Retake's the blunt instrument approach. Credits are smoother if you already do training, conferences, internal projects, or publish writeups as part of your normal workflow.
What activities typically count
SANS courses, other security training, conferences, relevant work contributions, and certain content creation like blog posts or talks. Keep proof. Save receipts. Boring admin stuff that matters later.
GPEN vs other penetration testing certifications
GPEN vs OSCP (difficulty, hands-on depth, employer preference)
GPEN is broader and more knowledge-and-process heavy, with open-book strategy baked in. OSCP is heavier hands-on exploitation under pressure without notes to lean on. Employer preference depends on the role and team culture: consulting firms and orgs that like SANS often prefer GPEN, while red-team-heavy hiring managers love OSCP for the hands-on proof. If your day job is more "assessments and reports" than "living in shells and chaining exploits," GPEN lines up with reality better than people admit. It's closer to what you'll actually do, and it can still pair nicely with OSCP later when you want to level up exploitation skills.
GPEN vs CEH / PNPT
CEH is more checkbox for some HR screens and government roles. PNPT is practical and report-oriented with lower cost. GPEN sits in the middle with strong brand recognition and structured content that enterprises trust.
Which certification to choose
Pick based on the work you want in six months, not the work you fantasize about at 2 a.m. when imposter syndrome hits.
GPEN faqs
How much does the GIAC GPEN exam cost?
GPEN exam cost depends on exam-only vs SANS bundle, and GIAC updates pricing periodically, so verify on the official GIAC page before purchasing to avoid surprises.
What is the passing score for GPEN?
The GPEN passing score is published by GIAC for the current version of the exam and posted clearly. Plan to clear it comfortably, not barely scrape by.
How hard is the GPEN exam compared to OSCP?
GPEN vs OSCP: GPEN is broader and open-book with methodology focus. OSCP is deeper hands-on exploitation with no notes allowed. Many find OSCP harder mechanically, but GPEN still punishes weak prep and poor indexing.
What are the GPEN exam objectives and domains?
Use the official GPEN exam objectives as your checklist and roadmap: scoping, recon, exploitation concepts, passwords, web basics, and reporting that doesn't embarrass you.
How do I renew my GPEN certification and maintain status?
Follow GPEN renewal requirements by earning CPEs during the renewal window or retaking the exam if credits don't fit your schedule. Track credits early so you're not scrambling later and panicking at the deadline. If you're also drilling questions for retention between study sessions, GPEN Practice Exam Questions Pack is a low-cost add-on that fits between lab sessions without overwhelming your schedule.
Conclusion
Pulling it all together
Look, the GIAC GPEN certification isn't one of those certs you just casually knock out on a Saturday afternoon. It's a serious exam that tests whether you actually understand penetration testing methodology, not just whether you can memorize exploit commands or regurgitate tool names. You're dealing with reconnaissance, exploitation fundamentals, password attacks, web application testing, and how to actually write a report that makes sense to someone who isn't a pentester. That's a massive amount of ground to cover, and the breadth of knowledge required catches people off guard way more often than they'd like to admit.
The GPEN exam cost is significant. Whether you go exam-only or bundle it with SANS GPEN training, you'll want to make sure you're ready before you sit for it. The GPEN passing score sits around 74%, which doesn't sound brutal until you realize the questions pull from six domains and expect you to apply concepts, not just recognize them. GPEN exam difficulty really comes down to how well you've indexed your materials and whether you can work through them quickly during the open-book portion. If your index is garbage? You're gonna struggle hard.
Clear enough, right? The GPEN exam objectives spell it out: you need to know penetration testing methodology from scoping through remediation guidance, plus the technical chops to handle enumeration, exploitation, post-exploitation concepts, and authentication weaknesses. GPEN prerequisites are minimal on paper but practically you need solid networking knowledge, comfort with Windows and Linux environments, and at least some scripting ability or you'll be lost. The thing is, if you're comparing GPEN vs OSCP, they're different animals. GPEN is knowledge-focused and open-book, OSCP is hands-on and you're alone in a lab for 24 hours trying not to lose your mind.
GPEN study materials matter. A lot. The official GIAC stuff is gold but you'll want to supplement with third-party references and build a realistic study plan. GPEN practice tests are critical for two reasons: they show you where you're weak and they teach you how to use your index under time pressure. Those practice tests saved me from bombing sections I thought I had nailed. Sections where I felt super confident until the practice exam completely humbled me and showed me I'd been skimming over key details. I once spent three hours reorganizing my index after a practice test revealed I couldn't find privilege escalation techniques fast enough, and that reorganization probably saved my score on exam day.
One last resource before you schedule
When you're in that final prep phase and want to validate you're actually ready, the GPEN Practice Exam Questions Pack can help you identify weak spots you didn't know existed. It's designed to mirror the question style and difficulty you'll face. Which means you're not walking in blind, right? Pair it with your indexed materials and you've got a solid game plan.
GPEN renewal requirements mean you'll need to stay engaged through CPEs or retake the exam every four years, but if you're working in pentesting that's usually not a problem. The ethical hacking certification GIAC offers here is respected, and employers recognize it as proof you've done the work. I've got mixed feelings about the CPE grind. Sometimes it feels like busywork, sometimes it actually keeps you sharp. Just make sure your fundamentals are strong and your index is organized. You got this.
Show less info
Comments
Hot Exams
Related Exams
GIAC Python Coder (GPYC)
GIAC Systems and Network Auditor
GIAC Secure Software Programmer – Java
GIACCertified Forensics Analyst
GIAC Certified Perimeter Protection Analyst
GIAC Information Security Fundamentals
GIAC Security Leadership Certification (GSLC)
GIAC Certified Incident Handler
GIAC Certified ISO-2700 Specialist Practice Test
GIAC Advanced Smartphone Forensics
GIAC Information Security Professional
GCIA – GIAC Certified Intrusion Analyst Practice Test
GIAC Certified Firewall Analyst
GIAC Penetration Tester
GIAC GIAC Secure Software Programmer - C#.NET
GIAC Certified Project Manager Certification Practice Test
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.