GISF Practice Exam - GIAC Information Security Fundamentals
Reliable Study Materials & Testing Engine for GISF Exam Success!
Exam Code: GISF
Exam Name: GIAC Information Security Fundamentals
Certification Provider: GIAC
Corresponding Certifications: GIAC Certification , GISF

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
GISF: GIAC Information Security Fundamentals Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 333 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena GIAC GIAC Information Security Fundamentals (GISF) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
GIAC GISF Exam FAQs
Introduction of GIAC GISF Exam!
The GIAC Information Security Fundamentals (GISF) certification exam is a comprehensive exam that tests a candidate's knowledge on the fundamentals of information security. It covers topics such as network security, cryptography, access control, malware, risk management, and more. Candidates must demonstrate their knowledge and proficiency in these areas in order to pass the exam and earn the GISF certification.
What is the Duration of GIAC GISF Exam?
The GIAC GISF exam is a two-hour exam consisting of 125 multiple-choice questions.
What are the Number of Questions Asked in GIAC GISF Exam?
There are a total of 125 questions on the GIAC GISF exam.
What is the Passing Score for GIAC GISF Exam?
The passing score required for the GIAC GISF exam is 76%.
What is the Competency Level required for GIAC GISF Exam?
The GIAC GISF exam requires a competency level of Advanced.
What is the Question Format of GIAC GISF Exam?
The GIAC GISF exam consists of multiple-choice and performance-based questions.
How Can You Take GIAC GISF Exam?
The GIAC GISF exam can be taken online or in a testing center. To take the exam online, you will need to register for the exam through the GIAC website and then purchase the exam voucher. You will then be able to access the exam through the GIAC Online Testing System. To take the exam in a testing center, you will need to contact a GIAC-certified testing center and register for the exam. You will then need to purchase the exam voucher and bring it with you to the testing center.
What Language GIAC GISF Exam is Offered?
The GIAC GISF exam is offered in English.
What is the Cost of GIAC GISF Exam?
The GIAC GISF exam is offered for a fee of $599.
What is the Target Audience of GIAC GISF Exam?
The GIAC GISF exam is targeted at individuals who have an understanding of security fundamentals and are looking to become an expert in the field of information security. It is ideal for professionals who have a background in IT security, such as security analysts, engineers, administrators, and auditors.
What is the Average Salary of GIAC GISF Certified in the Market?
The average salary for a GIAC GISF certified professional is around $90,000 per year. However, salaries can vary widely depending on experience, location, and employer.
Who are the Testing Providers of GIAC GISF Exam?
GIAC provides testing for GIAC GISF exam. Candidates can register for the exam online through the GIAC website. Candidates must also have a valid GIAC account to register for the exam.
What is the Recommended Experience for GIAC GISF Exam?
The recommended experience for taking the GIAC GISF exam is at least three years of experience in information security, including two years of experience in implementing and managing security controls. Additionally, it is recommended that candidates have a working knowledge of the GIAC GISF exam objectives, including network security, cryptography, access control, authentication, and security policy.
What are the Prerequisites of GIAC GISF Exam?
In order to take the GIAC GISF exam, you must have at least two years of professional experience in the field of information security or have completed a four-year degree in information security or a related field.
What is the Expected Retirement Date of GIAC GISF Exam?
The official website for GIAC GISF exam information is https://www.giac.org/certification/gisf-giac-information-security-fundamentals. There is no information on the expected retirement date of the exam.
What is the Difficulty Level of GIAC GISF Exam?
The GIAC GISF exam is considered to be of moderate difficulty. It requires a solid understanding of information security fundamentals and the ability to apply them to real-world scenarios.
What is the Roadmap / Track of GIAC GISF Exam?
The GIAC GISF certification roadmap includes the following steps:
1. Complete the GIAC GISF Training Course.
2. Pass the GIAC GISF Exam.
3. Receive your GIAC GISF Certification.
4. Maintain your GIAC GISF Certification by completing continuing education requirements.
What are the Topics GIAC GISF Exam Covers?
The GIAC GISF exam covers topics related to the implementation and management of information security frameworks and best practices. The topics covered are:
1. Risk Management: This topic covers the fundamentals of risk management, including risk identification, assessment, and mitigation. It also covers the different types of risk, such as financial, operational, legal, and compliance.
2. Security Policies and Procedures: This topic covers the development and implementation of security policies and procedures. It also covers the importance of compliance and auditing.
3. Security Architecture and Design: This topic covers the principles of security architecture and design, including the use of security controls and best practices. It also covers the importance of secure coding and application security.
4. Access Control: This topic covers the principles of access control, including authentication, authorization, and identity management. It also covers the importance of user access rights and privileges.
5. Network Security: This topic covers the fundamentals of
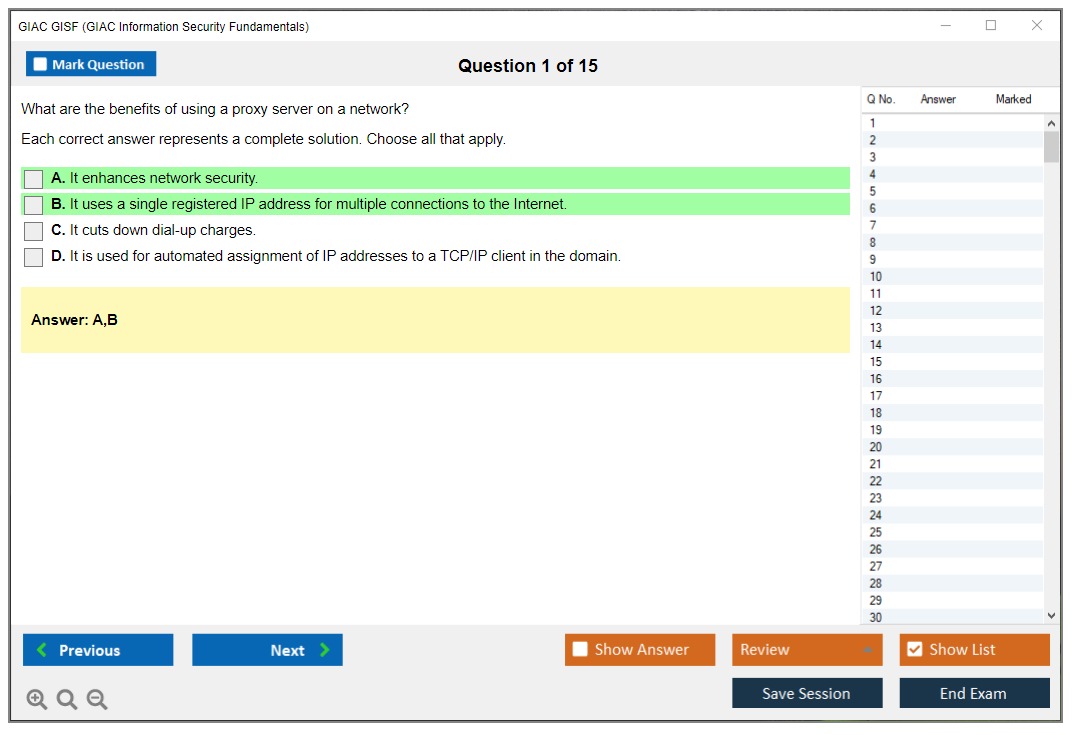
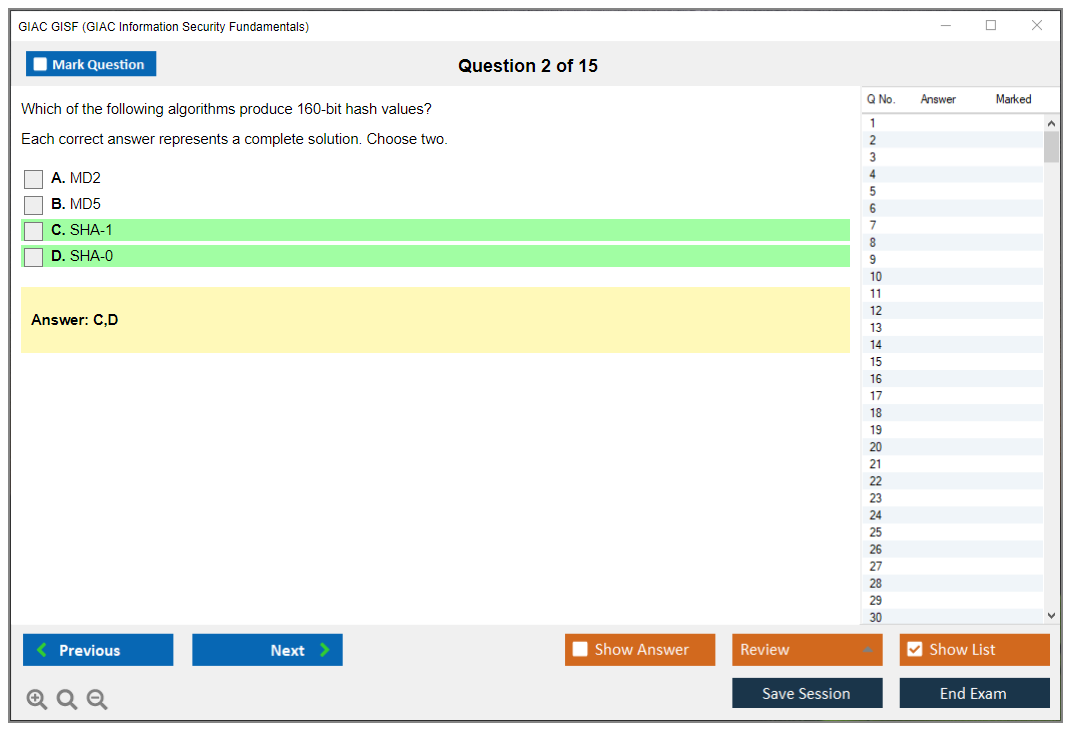
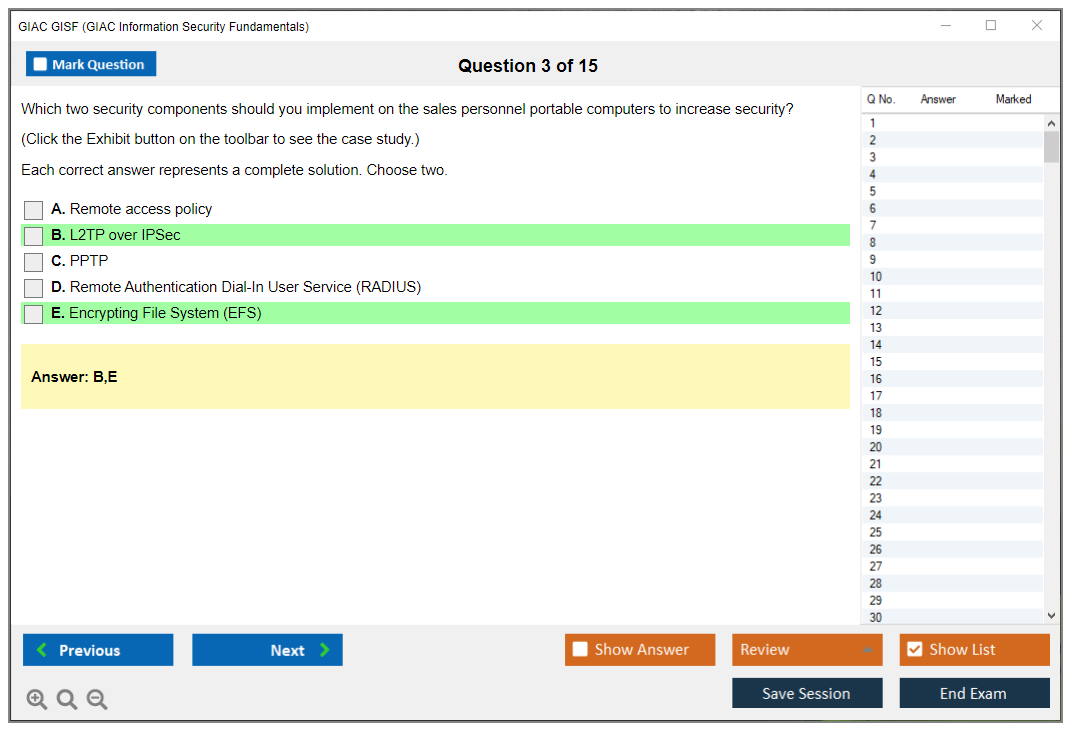
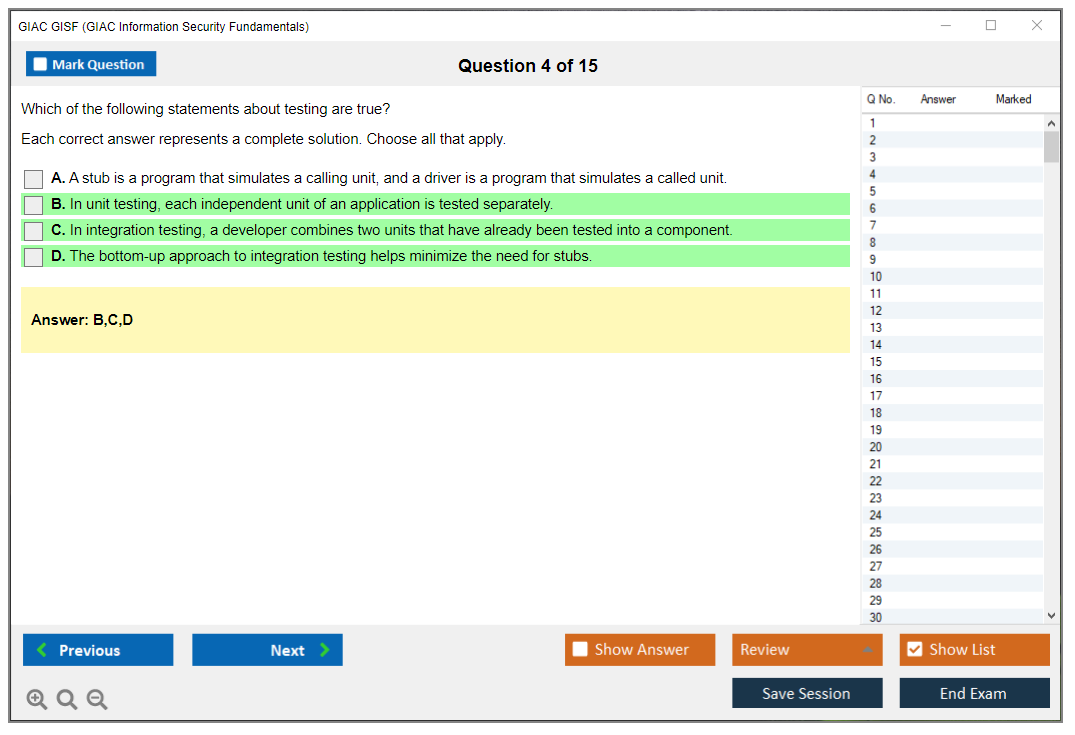
What are the Sample Questions of GIAC GISF Exam?
1. What is the purpose of the GIAC Global Information Security Fundamentals (GISF) certification?
2. What are the key components of the GIAC GISF certification?
3. What are the benefits of having a GIAC GISF certification?
4. What are the prerequisites for taking the GIAC GISF exam?
5. What topics are covered in the GIAC GISF exam?
6. How is the GIAC GISF exam scored?
7. What is the passing score for the GIAC GISF exam?
8. How long is the GIAC GISF exam?
9. What is the format of the GIAC GISF exam?
10. How often is the GIAC GISF exam updated?
GIAC GISF (GIAC Information Security Fundamentals) GIAC GISF Certification Overview What is GIAC GISF certification and why it matters GIAC's entry point. The GIAC GISF certification validates you understand fundamental security concepts without drowning you in advanced technical minutiae, and look, if you're trying to break into cybersecurity or you're an IT person who needs to prove baseline security knowledge, this is where GIAC wants you to start. Within the GIAC certification portfolio? GISF sits at the foundation. It's not flashy. Won't make you a penetration tester overnight, but honestly that's not the point. This thing proves you understand security principles, basic cryptography, network security fundamentals, and incident response concepts well enough to contribute in a security-conscious environment. Or at least well enough that nobody's going to blame you when something goes sideways. Government agencies recognize GISF for baseline requirements, which matters if you're... Read More
GIAC GISF (GIAC Information Security Fundamentals)
GIAC GISF Certification Overview
What is GIAC GISF certification and why it matters
GIAC's entry point.
The GIAC GISF certification validates you understand fundamental security concepts without drowning you in advanced technical minutiae, and look, if you're trying to break into cybersecurity or you're an IT person who needs to prove baseline security knowledge, this is where GIAC wants you to start.
Within the GIAC certification portfolio? GISF sits at the foundation. It's not flashy. Won't make you a penetration tester overnight, but honestly that's not the point. This thing proves you understand security principles, basic cryptography, network security fundamentals, and incident response concepts well enough to contribute in a security-conscious environment. Or at least well enough that nobody's going to blame you when something goes sideways.
Government agencies recognize GISF for baseline requirements, which matters if you're eyeing federal contracts or DoD positions. Helps satisfy DoD 8570/8140 requirements at lower tiers, making it practical for military folks transitioning to civilian cybersecurity careers. Employers see it as proof you're serious about security, not just someone who watched a few YouTube videos.
The value proposition's straightforward: you show foundational security knowledge that employers can trust. It's globally recognized, which means the credential travels if you do. Industry acceptance varies by sector. Government and defense contractors care more about GIAC credentials than some private sector companies, but the paper still carries weight when you're competing against candidates with no security certifications at all.
Who should pursue the information security fundamentals certification
IT professionals transitioning? Obvious candidates.
You're already comfortable with technology but need to formalize your security knowledge? GISF works. Help desk and technical support staff looking to advance beyond password resets find this useful as a stepping stone. I mean, you can only troubleshoot printer issues for so long before you want (honestly, before you need) something more challenging. Something that doesn't involve explaining why turning it off and on again actually matters.
System administrators expanding their security knowledge benefit because the cert covers practical concepts they encounter daily. Access controls, secure configurations, network defense basics. Recent graduates entering the cybersecurity field use GISF to differentiate themselves when they lack work experience. Career changers from non-technical backgrounds sometimes start here, though honestly they might struggle without basic IT fundamentals first.
Compliance and audit professionals needing to understand security fundamentals find GISF helpful. Government employees often pursue it to meet baseline security requirements mandated by their agencies. Military personnel preparing for civilian careers grab this because it translates military experience into a civilian-recognized credential that HR departments understand.
GISF vs other entry-level security certifications comparison
The thing is, the GIAC GISF versus CompTIA Security+ debate comes up constantly. Security+ has broader market recognition, especially in commercial sectors, but GISF dives deeper into specific security domains. Security+ covers more ground at a shallower depth. GISF focuses tighter but expects you to really understand what you're learning. Not gonna lie, the GISF exam cost runs higher than Security+, which matters when you're paying out of pocket.
Interesting comparison here.
GISF vs ISC2 CC (Certified in Cybersecurity) is interesting because CC's free for the exam itself. CC's newer, more accessible, and broader but less technical. GISF carries more weight with organizations familiar with GIAC's reputation, particularly government and defense contractors. The GSEC certification is where many GISF holders go next within the GIAC pathway.
When you compare GISF to CompTIA CySA+, you're really comparing apples and oranges. CySA+ targets analysts with existing experience, while GISF's really entry-level. Employer preference trends vary wildly by industry sector. Defense contractors often prefer GIAC certifications. Commercial tech companies lean toward CompTIA or vendor-specific credentials.
Technical depth differs significantly. GISF connects to SANS SEC275 GISF training, which is hands-on and scenario-based. Security+'s more conceptual. International recognition favors Security+ slightly due to CompTIA's longer market presence, but GISF holds strong globally among organizations that value SANS training.
Key benefits of earning GIAC GISF certification
Validation of core security competencies? That's the primary benefit.
Better resume credibility helps when you're competing for junior security analyst or SOC positions. Salary increase potential exists but temper your expectations. This is foundational, not specialized, so you might see a modest bump or qualify for positions you couldn't access before. Don't expect a massive jump.
Foundation for advanced GIAC certifications.
This provides a foundation for advanced GIAC certifications like GCIH or GPEN. Meeting DoD 8570/8140 baseline requirements opens government opportunities. You show commitment to professional development, which matters more than people think during interviews. Access to the GIAC holder community provides networking opportunities.
GISF certification validity and professional standing
Four-year certification validity.
The four-year validity period's standard across GIAC certifications. Your professional credibility remains solid throughout this period, though honestly technology moves fast enough that four years feels about right before requiring renewal. The relationship to SANS SEC275 GISF training course is tight. The exam objectives map directly to course content, though you can attempt the test without taking the course if you have equivalent knowledge.
GISF fits into cybersecurity career pathways as your starting point before specializing. Some people move toward GIAC Certified Incident Handler for incident response, others toward GSLC for leadership tracks. This proves current knowledge when you earn it, though maintaining relevance requires staying active in the field. Industry trends keep GISF relevant because fundamental security principles don't change as rapidly as specific tools and techniques.
GISF Exam Objectives and Domain Breakdown
GIAC GISF (GIAC Information Security Fundamentals) certification overview
The GIAC GISF certification is your "can you actually talk security without sounding clueless" badge. Not flashy. Incredibly practical. It's an entry-level GIAC certification aligned with what early-career security and IT professionals really encounter daily: user accounts, encryption fundamentals, network defenses, incident workflows, risk concepts, and web security chaos.
Honestly? GISF won't transform you into some elite pentester overnight or anything like that. It's an information security fundamentals certification validating you can interpret logs properly, adhere to established policies without constant hand-holding, and avoid catastrophically breaking production systems while "enhancing security measures."
GISF exam objectives (what you'll be tested on)
The GISF exam objectives come straight from GIAC as the official blueprint, grounded in job task analysis. These topics mirror what working practitioners actually report doing in their daily roles. Or at minimum supporting. That's exactly why the objectives feel like genuine operations work rather than disconnected academic theory. Content updates happen regularly as technology evolves and attacker tactics shift, honestly faster than most organizations bother updating their internal documentation. I once saw a company still referencing WEP encryption in their official 2019 wireless policy, which tells you everything about how slowly things move in large enterprises.
Total domains? Seven. Weighting fluctuates somewhat over time, but distribution typically spans access control, cryptography, networks, incident handling, risk, systems, and web communications. Always verify current weights in the official blueprint since GIAC refreshes exams to maintain relevance, and those "what matters most" percentages shift as the threat space and technology ecosystem transforms.
Blueprint availability? Straightforward. GIAC publishes official documentation for the GIAC Information Security Fundamentals exam, covering objectives, exam format specifics, and policy guidelines. Don't assume. Read it.
Domain 1: access control and password management
Who gets access. What they're allowed to touch. How accounts don't spiral into complete disasters. That's this domain.
Authentication factors appear constantly: something you know, possess, or are. MFA implementation matters significantly in practice because push fatigue is absolutely real and "we enabled MFA" doesn't equal "we configured it securely or intelligently."
Authorization models surface here: DAC, MAC, RBAC. RBAC dominates enterprise environments. Password policies and complexity mandates get attention, but also the emerging reality that lengthy passphrases combined with rate limiting often outperforms "P@ssw0rd rules" in numerous environments. SSO concepts appear too. Single sign-on is simultaneously convenient and absolutely terrifying when misconfigured.
Biometrics? Benefits and drawbacks. Excellent for user convenience, problematic for revocation scenarios. You can't exactly issue someone a new fingerprint after a breach. Account lifecycle management and privileged access management fundamentals also feature prominently because abandoned admin accounts are exactly how minor issues escalate into front-page security incidents. Common vulnerabilities include weak password resets, shared credentials, excessive permissions, flawed MFA recovery workflows.
Domain 2: cryptography fundamentals
Expect symmetric versus asymmetric encryption, plus when each approach fits best. Symmetric excels for bulk data operations. Asymmetric handles key exchange and identity verification. Hashing algorithms and integrity verification are foundational, alongside digital signatures and certificates so you can distinguish "encrypted" from "actually trusted."
PKI components matter here: CAs, intermediate authorities, certificate chains, revocation mechanisms. SSL/TLS and transport encryption appear because HTTPS represents the baseline expectation nowadays, and you absolutely need to grasp what TLS actually protects versus what it doesn't. You'll encounter standards like AES and RSA, key management best practices, and common crypto attacks including weak randomness, protocol downgrade vulnerabilities, and password-based key derivation failures.
Real scenario: encrypting data at rest becomes pointless when keys sit on that same server inside plaintext configuration files. People legitimately do this.
Domain 3: defense-in-depth and network security
Layered security architecture drives this domain. Firewall types and configurations. Network segmentation strategies. DMZ architectural design. IDS versus IPS distinctions. VPN technologies and remote access controls. Wireless security protocols like WPA2 and WPA3.
Network monitoring fundamentals surface too, which is where numerous entry-level roles actually exist: identifying suspicious outbound traffic patterns, DNS anomalies, or repeated authentication failures.
Perimeter defense remains relevant, though the exam reflects modern reality where identity verification and internal segmentation matter equally as much as defending the edge. Sometimes more than. Traditional network boundaries keep dissolving as cloud adoption accelerates and remote work becomes permanent for many organizations.
Domain 4: incident response and handling
The lifecycle. Preparation, detection, analysis, containment, eradication, recovery, and post-incident lessons learned. Short-term versus long-term containment differences really matter, because "just block the IP address" differs fundamentally from "eliminate attacker persistence mechanisms and remediate the underlying root cause." Confusing those distinctions under pressure wastes entire days or weeks.
Evidence preservation and chain of custody get included, plus incident classification approaches, prioritization frameworks, communications protocols, and documentation requirements. Quality notes. Clear chronological timelines. Who authorized which actions.
These fragments really save careers.
Domain 5: risk management and compliance
Risk assessment methodologies, qualitative versus quantitative analysis techniques, and treatment options: accept, mitigate, transfer, avoid. Compliance framework basics appear here. HIPAA, PCI-DSS, GDPR. Policy and procedure development, business impact analysis fundamentals, vendor risk concepts, and why mandatory security awareness training exists despite universal complaints about it.
Domain 6: system and application security
Secure configuration baselines, patch management workflows, malware categories and countermeasures. Application security principles and SSDLC basics. Input validation and prevalent vulnerabilities. Mobile device security, cloud fundamentals, virtualization security concepts.
Most organizations don't fail because they can't afford expensive tools or platforms. They fail because they don't patch consistently, don't harden configurations, and really don't know what's actually running in their environment.
Domain 7: web security and communication
OWASP Top 10 awareness, XSS and SQL injection fundamentals, secure protocols like HTTPS, SFTP, SSH. Email threats: phishing campaigns and spoofing techniques. Social engineering attack vectors. Browser security configurations. Secure communication best practices.
This domain maps cleanly to real help desk tickets: "is this email legitimate" and "why is this web form behaving strangely."
How GISF exam objectives map to job roles
For SOC analysts, GISF provides baseline vocabulary: security alerts, authentication logs, network control mechanisms, incident response workflows. For IT support teams, it fits with daily responsibilities like account provisioning, device hygiene enforcement, phishing email triage.
Junior security administrators encounter RBAC implementation, system hardening, VPN troubleshooting, patching schedules. Compliance analysts gain the risk assessment and framework grounding they'll reference constantly.
People frequently ask about the GISF exam cost, GISF passing score, GISF exam difficulty, GISF prerequisites, GISF study materials, GISF practice test, and GISF renewal requirements. The official GIAC pages and the SANS SEC275 GISF course outline represent the first resources I'd consult, and renewal connects back to GIAC certification maintenance (CPEs) regulations, which evolve less frequently than the technical content but still deserve careful review before you map out your certification cycle.
GISF Exam Cost and Registration Details
What you're actually paying for the GISF exam
The GIAC GISF certification exam runs $949 as of 2024 for a standalone attempt. Not cheap, honestly. That's the standard registration fee if you're buying just the exam without any SANS training attached to it. Compare that to CompTIA Security+ which hovers around $400 and you start to see why people hesitate on GIAC certs, even the entry-level ones like this information security fundamentals certification. The price gap alone makes folks rethink their entire certification roadmap before they've even cracked open a study guide.
Academic discounts exist though. Students can sometimes get 30-40% off through their institution if there's a SANS Academic Alliance partnership in place, which drops the price closer to $570-665. Worth checking if your school's got that relationship because those savings add up fast when you're already drowning in tuition costs. I remember when my cousin tried to get his school's IT department to confirm their partnership status and it took three weeks of emails bouncing between departments before anyone could give him a straight answer about whether they even had the discount available.
Government and military folks also get special pricing. Active duty military, DoD civilians, and federal employees can access reduced rates through specific programs, though the exact discount varies depending on which agency or branch you're working with and what training budget agreements exist.
The course bundle vs standalone exam math
Here's where it gets interesting. If you buy SANS SEC275 GISF course with the exam bundled in, you're looking at around $7,500-8,500 for live training or $5,700-6,200 for OnDemand. That price includes the exam attempt, course materials, textbooks, and four months of access to the online content. The standalone exam at $949 sounds cheaper until you realize you're studying completely blind without the official GISF study materials that most people need to pass this thing. Self-studying for GIAC exams without their materials is like trying to build IKEA furniture without the instructions. Technically possible but you'll probably end up with extra parts and a wobbly result.
Live training costs more but you get instructor interaction and networking opportunities. OnDemand is self-paced video content which works great if you've got solid discipline and don't need someone explaining the GISF exam objectives in real-time. I've seen people successfully self-study using third-party resources and then just buy the standalone exam, but it's the harder path for beginners.
What your registration actually includes
One exam attempt. You also get access to two GISF practice test attempts which expire 120 days after you activate them, so don't activate those the second you register unless you're ready to study immediately. The practice tests aren't perfect replicas but they give you a decent sense of question style and difficulty level.
You can take the exam either through online proctoring from home or at a Pearson VUE test center. Online proctoring's free but you need a webcam, stable internet, and a clean room that meets their requirements. Test centers charge an additional $50-100 depending on location.
Pass the exam and you get a digital badge immediately, plus a physical certificate mailed within 4-6 weeks. You also get lifetime access to the GIAC certification portal where you can download verification letters and track your GISF renewal requirements down the road.
Additional costs nobody warns you about
The GISF passing score is 74% but getting there might require more than just the exam fee. If you're self-studying without the SEC275 course, budget $100-300 for reference books, study guides, and maybe some Udemy courses that cover security fundamentals. Not all GISF exam difficulty can be conquered with free YouTube videos.
Retake fees? Brutal at $539 per attempt. You can fail twice and buy a third attempt, but there's no limit as long as you keep paying. That's where the real money drain happens if you're not prepared the first time.
Renewal hits every four years and costs $469 currently, plus you need 36 CPE credits earned through training, conferences, or other approved activities. Some CPE activities are free but quality training events usually cost money. I've got mixed feelings about the CPE system because while it does push ongoing learning, it also feels like paying rent on knowledge you've already proven you have. The GISF renewal requirements aren't as demanding as advanced GIAC certs but you can't just ignore them.
How to actually save money on this thing
Bundle with SANS training if your employer pays. The exam-only price seems attractive but the bundle's better value when someone else foots the bill. Work Study programs let you assist at SANS events in exchange for free course tuition, though spots are competitive and you've got to commit serious time.
Military and veteran educational benefits through GI Bill sometimes cover SANS training. Academic partnerships give students the best discount path for the standalone exam. Early bird registration for live training can save $500-800 if you plan months ahead.
International candidates need to factor in currency exchange rates and potential VAT charges depending on your country. The $949 USD might translate to a lot more in your local currency after conversion fees hit.
If you're considering other entry-level GIAC certification paths, compare the GSEC which is more thorough but costs the same for standalone exam access. Some people skip GISF entirely and jump straight to GCIH if they've got incident response experience already.
GISF Passing Score and Exam Format
GISF passing score requirements
The GIAC GISF certification uses a passing threshold that usually lands in the 73 to 74% range for the current form, and people obsess over that number. When you're paying GISF exam cost money and you've burned weekends on GISF study materials, you want a clean target.
Scaled scoring confuses everyone. GIAC exams use a scaled model so different versions stay comparable even if one form ends up tougher than another. The scaling uses psychometric analysis of how questions perform across a big sample of test takers, not on how you personally "felt" about the exam that day. Two people can walk out swearing they had wildly different difficulty and still both end up with scores that map fairly to the same standard.
How does GIAC set passing standards? They use statistical methods plus subject-matter review to decide what "minimally competent" looks like for the GIAC Information Security Fundamentals exam, then they keep tuning it as items get retired or refreshed. No mystery cabal. Just measurement nerd stuff.
Score reporting? Fast.
Most people see a preliminary pass/fail right after submission, then the official report follows in the GIAC portal shortly after, often the same day. Timing can vary if anything flags for review, but it's not like waiting weeks. You'll know pretty much immediately whether you passed.
Your score report typically includes your overall scaled score, pass/fail status, and a performance-by-domain breakdown aligned to the GISF exam objectives. That domain view matters because it tells you what to fix if you're retaking, or what to shore up before you roll into the next cert. Actually useful feedback compared to some other exams that just give you a number and send you home.
No partial credit, period. Multiple-select questions are all-or-nothing. Pick three correct and one wrong, you get zero. Brutal? Maybe. But that's the deal.
GISF exam format and structure
The GISF exam usually lands somewhere around 75 to 106 questions, depending on the current blueprint and form. Most candidates report a count in that window. Plan for the upper end so you don't get surprised. Better to budget for 106 and finish with time left than plan for 75 and panic.
Question types? Mostly multiple choice and multiple select. Multiple select is where people bleed points because they rush and assume it's "choose the best answer" when it's actually "choose all that apply" with zero partial credit. A GISF practice test or two can pay off by training your pacing and your attention to wording. Some folks grab extra drills like GISF Practice Exam Questions Pack when they want more reps without rereading the whole book again. Reps matter.
Time limit? Typically 2 to 3 hours. You can absolutely finish if you manage your open-book workflow, but if you treat it like a scavenger hunt and look up everything, you're going to run out of runway before you hit question seventy.
Delivery is either online proctored (commonly via ProctorU) or a test center. The interface usually supports basic navigation: you can move back and forth, mark questions for review, and track what you've answered. There's no negative marking. Wrong answers don't subtract points, so blank answers are almost always a bad idea. Just guess if you're stuck.
Calculator availability depends on the platform rules. Most GISF content isn't heavy math, but if a calculator is provided, it's usually an on-screen one and you should assume you can't bring your own. Not that you'll need it much anyway. I once spent fifteen minutes looking for the square root function before realizing the question didn't even need one.
Question difficulty and distribution
People ask about GISF exam difficulty like it's one universal experience. It's not. The exam is a mix of recall (terms, concepts), application (what control fits), and some analysis (read a scenario, decide the best action). Scenario-based questions show up often enough that you should expect them, but it's still an entry-level GIAC certification, not a forensics marathon or some insane red-team gauntlet.
Domain weighting shows up in question counts. If a domain is a bigger slice of the objectives, it gets more questions. Simple math. The practical angle is real: questions test whether you can think like a security-aware IT person, not whether you can recite a definition from memory while panicking under fluorescent lights at 9 a.m.
GIAC generally avoids "trick" questions. The challenge is precision, not gotchas. They want to know if you understand the concept, not if you can decode some riddle wrapped in technical jargon.
Open-book policy for GISF exam
Yes, it's open-book. GIAC's approach is basically: bring printed reference materials, but prove you understand them under time pressure. A fair test of real-world skills if you think about it. Allowed materials usually include printed books, printed notes, and a printed index. Digital files, extra monitors, and searching the internet are a hard no.
Indexing? Difference-maker.
Build an index that maps keywords to page numbers and tabs. Be consistent with your labeling. The best index is boring. It's fast. You're not writing a novel, you're building a lookup table that works under pressure when your brain is fried.
What's not allowed? Phones, PDFs, cloud notes, and anything that looks like you're trying to access outside info. Proctors will watch how you use references. Flipping pages is fine, but disappearing out of frame or constantly looking off-screen is how you get interrupted, or worse, flagged for misconduct.
Time management tip: answer what you know first, mark the rest, then use your index for targeted lookups only. If you want more timing practice, GISF Practice Exam Questions Pack can help you rehearse that "decide fast, search smarter" rhythm without burning through your actual study materials.
Online proctoring vs test center options
ProctorU remote proctoring usually starts with a system check, room scan, and ID verification. Can take anywhere from five minutes to, look, I've heard horror stories of thirty-minute tech troubleshooting sessions before the exam even starts. You'll need stable internet, a compatible browser, webcam, and a quiet space with decent lighting. They monitor camera, audio, and on-screen activity. They'll call you out for off-camera behavior, extra devices, or suspicious movements. Hands visible. No sudden moves.
Test centers are more controlled. Fewer tech surprises, more "airport security" vibes where you empty your pockets and get scanned. Scheduling depends on location availability, and some areas have limited slots, so don't wait until the week before to book.
Online is convenient. Test center is calmer. Pick your poison based on your setup and stress tolerance.
If tech issues happen online, you stop, work with the proctor, and document everything. Don't improvise. Follow instructions. Deviating from protocol can end your session and cost you a retake fee.
Exam day logistics and procedures
Plan to check in early. You'll do ID verification (usually government-issued photo ID), desk and pockets check, and a rules review that feels slightly redundant but just nod along. Prohibited items include phones, smartwatches, extra screens, and anything electronic that isn't explicitly allowed. They're serious about this. One candidate I know got booted for forgetting a fitness tracker.
Break policy is strict. Some formats allow breaks but the clock may keep running, and leaving camera view without permission can end your session. Terrifying if you really need to use the bathroom halfway through. Scratch paper rules vary: test centers often provide it, online sessions may allow a small whiteboard or nothing at all, depending on current policy and proctor mood.
After the exam you'll usually see preliminary results, then a short survey asking how you felt about the experience. Then you exhale.
Done. Finally.
If you're budgeting or planning next steps like GISF renewal requirements and GIAC certification maintenance (CPEs), treat the exam as step one, not the finish line. If you want more reps before test day, GISF Practice Exam Questions Pack is a cheap way to pressure-test your prep without guessing where you're weak or wasting money on a failed attempt.
GISF Exam Difficulty and Preparation Timeline
How hard is the GISF exam actually?
Not sugarcoating it. The GIAC Information Security Fundamentals exam sits in this weird spot difficulty-wise, honestly. It's marketed as entry-level, but GIAC doesn't really do "easy" certifications. Like, at all. Compared to something like GSEC or GCIH, yeah, GISF's lighter. But if you're coming in cold with zero IT background? This thing'll challenge you.
The exam focuses more on breadth than depth, which is actually kind of tricky when you think about it. You're covering networking basics, cryptography fundamentals, access control, incident response concepts, and compliance frameworks all in one sitting. Your brain's jumping around constantly. Nothing gets super technical like you'd see in GPEN, but the sheer range of topics trips people up. I mean, you need to understand OSI model layers one minute and then answer questions about GDPR compliance the next. Whiplash-inducing.
GIAC's exam development process? Actually pretty rigorous. They pull from real-world scenarios and update content regularly based on industry changes, which sounds great but also means you can't rely on outdated study materials. First-time test takers often underestimate this. They think "fundamentals" means surface-level memorization, but the scenario-based questions require you to actually apply concepts, not just regurgitate definitions you crammed the night before.
Who struggles most with GISF?
Complete beginners face the steepest climb. Honestly. If you've never configured a firewall rule or don't know the difference between symmetric and asymmetric encryption, you're looking at 6-12 months of serious preparation. And that's not just GISF study time, that's foundational IT knowledge you need first, which nobody really tells you upfront.
IT professionals with 1-2 years of helpdesk or sysadmin work? You've got a head start, no question. The networking stuff and basic security concepts probably make sense already. You're looking at 3-6 months of focused study, mostly filling gaps in areas like cryptography or compliance frameworks that don't come up in daily work. You know, the stuff that's boring but tested anyway.
Experienced IT folks transitioning to security can usually knock this out in 2-3 months, maybe less. You understand the technical foundation, you just need to reframe things through a security lens. And if you've already passed something like GISP or another security cert, GISF becomes a 1-2 month review exercise. Easy comparatively.
Academic background matters more than people admit, the thing is. Computer science grads have an easier time with the technical domains. Someone coming from a business or liberal arts background needs extra time on networking and cryptography fundamentals. Not a value judgment, just reality. I studied philosophy in college, so I get it. Took me way longer to wrap my head around subnetting than it did to understand Kant, which tells you something about how our brains get wired differently.
Why people actually fail GISF
Insufficient hands-on experience kills candidates constantly. Reading about encryption algorithms isn't the same as understanding when to use AES versus RSA in actual scenarios. Like, not even close. The exam tests application, not just theory.
Poor time management during the test itself? Another big one. GISF's open-book, which sounds great until you realize you're frantically searching through materials instead of actually knowing the content. People waste 5 minutes per question hunting through PDFs. Nightmare fuel.
Cryptography trips up tons of people, honestly. It's abstract, requires understanding mathematical concepts at least conceptually, and the questions get specific about key lengths, cipher types, and hashing algorithms. Wait, SHA-256 or SHA-3 for this scenario? This domain alone probably accounts for 30% of failures, maybe more.
Over-reliance on the open-book format is honestly the biggest trap I've seen. Yeah, you can reference materials, but if you haven't built a working index beforehand, you're toast. I've seen people spend 45 minutes creating their index during the exam. That's insane. That's failing before you've even started.
Real study timelines that actually work
For complete beginners, budget 6-12 months and about 200-300 total study hours. Sounds like forever, but it's necessary. Your first two months should focus on networking fundamentals and operating system basics. Don't even touch GISF materials yet. Months 3-4, start core security principles. Months 5-6, domain-specific deep dives into areas like cryptography and access control. The heavy stuff. Then hands-on labs for months 7-8, practice tests months 9-10, and final review the last two months.
IT professionals can compress this. 3-6 months and 100-150 hours total. Spend months 1-2 on SANS SEC275 or equivalent training materials (expensive but worth it if you can swing it), months 3-4 doing hands-on practice, month 5 on practice tests and identifying weak areas, month 6 for final prep and maybe some panicking.
Experienced security professionals? 1-2 months intensive review, 50-80 hours total. First two weeks reviewing all domains. Weeks 3-4 hammering practice tests. Weeks 5-6 focusing on whatever domains you scored lowest on. Final weeks doing full review and exam prep. You've got this.
What makes this exam harder than it should be
Limited practical experience with actual security tools makes the scenario questions brutal. I mean really difficult. You can memorize that IDS stands for intrusion detection system, but if you've never looked at IDS alerts or understood false positive rates, the questions won't make sense. They'll just look like word salad.
Weak foundational networking knowledge compounds everything else. If you don't instinctively understand how TCP/IP works or what ports common services use, you're constantly backtracking to figure out basic context before you can even address the actual security question being asked.
Test anxiety hits hard on timed exams with money on the line. The GISF exam cost isn't cheap, and that pressure makes people second-guess answers they actually know. Imposter syndrome's real.
Making GISF easier through smart prep
Hands-on lab practice makes the biggest difference, bar none. Spin up virtual machines, configure firewalls, practice with Wireshark, play with encryption tools. Even basic stuff helps tremendously because you're building muscle memory and intuition that reading alone never provides.
Build your exam index before test day. Seriously, I can't stress this enough. Organize your reference materials by domain, create a table of contents, bookmark key sections. This saves massive time during the actual exam when every second counts.
Practice tests from GIAC help you understand question patterns and time management in ways nothing else does. Take them under actual exam conditions: no phone, timed, the whole deal. If you're consistently scoring 80%+ on practice tests, you're probably ready for the real thing. The GISF passing score requirements mean you need solid mastery, not just barely scraping by with crossed fingers.
Regular study groups or peer discussion helps too, especially for abstract concepts like cryptography or compliance frameworks that feel disconnected from reality. Explaining concepts to someone else forces you to actually understand them, not just memorize them. That's the difference between passing and failing this exam. Understanding versus regurgitation.
GISF Prerequisites and Recommended Background
Official prerequisites (if any)
The GIAC GISF certification is one of the few security certs where the official stance is basically: no gatekeeping. GIAC lists no mandatory GISF prerequisites, and that means no required work history, no required class, no degree checkbox, nothing. Anyone can register for the GIAC Information Security Fundamentals exam if they're interested, and honestly that openness is part of why GISF keeps showing up as an entry-level GIAC certification on career switcher shortlists.
No experience needed. Zero college degrees. No "must have Security+" checkbox.
That said, look, "no prerequisites" doesn't mean "no preparation." The thing is, the GISF exam objectives cover a wide swath of fundamentals, and if you're coming in totally cold you'll feel it fast. Questions start mixing networking basics with security terms and real operational thinking. Even "fundamentals" can trip people up when they're layered together like that. So the real prerequisite? Self-assessment. I mean a brutally honest one. Read the GISF exam objectives line by line, compare them to what you can explain without Googling, then decide whether you need a runway month or two before you even start "studying for the test."
If you want a quick gut check, take a GISF practice test early. Not to "see if you pass," but to see what you don't even recognize yet, because that's the stuff that'll eat your time later when you're staring at a question and realizing you never learned the vocabulary.
Recommended knowledge (networking, OS basics, security concepts)
Networking's the first big bucket. You don't need to be a CCNA person, but you should be comfortable with TCP/IP and the OSI model at the level where you can explain what happens when you type a URL and it loads, and where things break when DNS is wrong or a firewall rule is blocking traffic. IP addressing and subnetting fundamentals matter too. Not advanced VLSM wizardry, just enough to understand ranges, masks, and why "this host can't reach that host" is sometimes a math problem.
Know the common protocols. HTTP, DNS, DHCP. Recognize what they do. Spot obvious abuse.
Also, have a mental picture of network devices. Routers vs switches, what a firewall actually does, and why "allow all outbound" is a policy choice with consequences. If that sounds like a lot, it is, but it's also the baseline for security work. Security questions are usually just networking questions plus "what could go wrong here?" I spent about three weeks once trying to explain to a finance director why we couldn't just "turn off all the security stuff to make the VPN faster," which tells you something about how little networking fundamentals get taught outside IT.
Operating systems are the next bucket, honestly. Windows administration basics are helpful. Things like local users and groups, services, event logs, and basic troubleshooting. On Linux or Unix, you should have at least some command line exposure: working through directories, viewing files, understanding permissions, and knowing that processes exist, consume resources, and can be inspected and stopped. File systems and permissions show up everywhere in security because misconfigurations are how real environments get popped, and "who can read or write or execute what" is the start of that conversation.
General IT literacy matters more than people admit, I mean really. Hardware components, software installation, patching, drivers, and basic troubleshooting habits. Security's still IT, just with sharper edges. Basic scripting awareness is nice, too. You don't need to write Python tools, but being able to read a simple script and not panic helps, especially when you're learning how attackers automate boring tasks.
On the security baseline side, you should understand the CIA triad, basic security terminology, and the common threats you hear about in the news. Malware, phishing, credential stuffing, ransomware, all that. You should also have at least some exposure to everyday tools like antivirus and host or network firewalls, plus a basic understanding of risk concepts, like likelihood vs impact, and a general awareness that compliance requirements exist (even if you're not memorizing any specific regulation yet).
Who should take GISF first (students, career changers, IT support)
The ideal candidates for the GIAC GISF certification are people who want a broad foundation and don't want to guess what "security fundamentals" really means. IT support technicians? Great fit. And 1 to 2 years of help desk experience is a sweet spot because you've probably seen password resets, malware scares, weird outbound traffic, maybe even a minor incident. Exposure to incidents helps. Not required, still helpful.
Recent CS or IT grads also do well, especially if you had academic security coursework or an internship where you touched real systems. Career changers can absolutely do GISF, but you need transferable skills that map to troubleshooting, process, documentation, and calm thinking under pressure. Military IT or cyber folks tend to ramp quickly. Same with law enforcement people who already have a technical background and want the vocabulary plus the fundamentals to move into private-sector security. Compliance professionals can benefit too, 'cause GISF gives you enough technical grounding to talk to admins without everything sounding like magic.
When should you do GISF versus something else first? Take GISF first if you're new to security and want the broad base. Consider CompTIA A+ or Network+ first if you have basically no IT background and terms like "subnet" and "DNS record" are still foggy. Pursue Security+ first if your employer requires it or you're optimizing for lower cost, because yes, GISF exam cost is usually higher than the mainstream entry certs. If you have 5+ years in security already, you might skip ahead to more advanced GIAC tracks, 'cause the GISF exam difficulty will feel like review.
Before you commit, do a skills gap assessment. Skim free online security fundamentals courses, review the GISF exam objectives honestly, take a practice test, and ask a mentor to sanity-check your readiness. And if you want targeted drilling, a paid question pack like GISF Practice Exam Questions Pack can help you find weak areas fast. I mean, it's not the only way, but it's a clean feedback loop, and GISF Practice Exam Questions Pack is priced like a small risk compared to scheduling an exam you're not ready for.
One more thing. The GISF passing score and the GISF renewal requirements matter later, but readiness matters now, 'cause the easiest way to waste money is to ignore your own gaps, pay the GISF exam cost, and hope confidence magically appears on test day. If you want extra reps right before you book, GISF Practice Exam Questions Pack is a decent final check.
Best GISF Study Materials and Resources
Official GIAC and SANS training options
Okay, so here's the deal. If you're actually serious about the GIAC GISF certification, SANS SEC275 is basically where you need to start. It's the gold standard, honestly. Not gonna sugarcoat it: the price tag is brutal, but you absolutely get what you pay for here. The six-day training covers everything from basic networking and cryptography to incident response fundamentals and security policy development. They don't mess around.
The course structure? Pretty intense, honestly. You're looking at six full days covering access control, network security, cryptography basics, defense in depth strategies, and practical security implementation. Like, all the foundational stuff you'd actually need in real-world scenarios where things can go sideways fast if you don't understand the fundamentals properly. SANS delivers this through multiple formats, which makes it accessible for different learning styles and schedules, depending on what works for you. The course books are thick. Really thick. And they become your reference material during the exam since GISF is open-book.
Instructor-led options include in-person bootcamps and Live Online sessions. The in-person format gives you that networking opportunity with other students and instructors, which is valuable if you're building a career in security. Live Online works similarly but you're attending remotely, still with real-time interaction and Q&A. Then there's OnDemand, which is self-paced video training that you can access for typically four months. The OnDemand lectures are high quality, broken into digestible segments, and you can rewatch anything that doesn't click immediately. I spent way too much time rewinding the cryptography sections because that stuff just wouldn't stick at first.
Cost wise? We're talking several thousand dollars for the full SANS package. OnDemand runs cheaper than in-person training, but it's still a significant investment either way. What you're paying for includes the course materials, practice exams, and access to SANS community forums where you can ask questions and connect with other students.
GIAC practice tests and how to use them
GIAC provides official practice exams when you register, and these are your best indicator of readiness. No question. The practice tests mirror the actual exam format pretty closely, giving you around 75-100 questions that cover the same domains. What's useful is the performance feedback you get afterward, showing which areas need more work.
When you take the GISF practice test, pay attention to the questions you're getting wrong and why. The explanations help you understand not just the correct answer but the reasoning behind it. I'd recommend taking a practice exam after your initial study, then using the results to focus your remaining prep time. Your practice test scores should consistently hit above 80% before you schedule the real thing. I mean, you could probably pass with lower scores, but why risk it?
GIAC CyberLive offers additional resources including webinars and technical content that supplements your core study materials. The advisory board resources provide whitepapers on specific security topics that can deepen your understanding beyond just exam prep.
Third-party books and supplementary materials
If you're not taking the SANS course or want additional references, there are solid third-party options. CompTIA Security+ study guides actually overlap quite a bit with GISF exam objectives since both cover security fundamentals. The Mike Meyers or Darril Gibson Security+ books work well as complementary reading.
For networking fundamentals, grab a TCP/IP guide like "TCP/IP Illustrated" by Stevens (ISBN 0201633469) or something more accessible like "Networking All-in-One For Dummies." Cryptography basics are covered well in "Cryptography and Network Security" by Stallings. You don't need deep mathematical knowledge for GISF, just understanding of how encryption works in practice.
Free and budget-friendly study resources
NIST publications? Completely free. And incredibly valuable, honestly. The NIST Cybersecurity Framework maps directly to many GISF concepts. Download SP 800-53 for security controls, SP 800-61 for incident handling, and SP 800-137 for continuous monitoring. These aren't light reading, but they're authoritative sources that the exam draws from.
YouTube has decent content on networking basics and security concepts. Channels covering CompTIA Security+ material often align with GISF objectives, which is convenient since you can find tons of that content. Professor Messer's free Security+ course covers fundamentals that apply directly to GISF. Cybrary offers some free introductory security courses too, though quality varies.
For practice questions beyond the official GIAC materials, our GISF Practice Exam Questions Pack at $36.99 gives you additional question exposure at a fraction of SANS pricing. More practice questions mean better pattern recognition when you hit the actual exam.
The r/AskNetsec and r/cybersecurity subreddits sometimes have GISF study threads with tips from recent test takers. GIAC's official study guides and reference materials available through their portal are worth reviewing as well.
If you're planning to continue with GIAC certifications, consider the GSEC or GCIH as logical next steps. Both build on GISF fundamentals with more technical depth. The GISP focuses more on management aspects if you're heading toward leadership roles.
Building a good index of your SANS books is critical since the exam is open-book. Tab important sections, create bookmarks, and practice finding information quickly during your practice tests.
Conclusion
Look, you made it this far. Probably serious then.
And honestly? That's exactly the mindset you need because this isn't one of those certs where you can just wing it on test day, roll in half-prepared, and somehow stumble your way to a passing score through sheer luck and multiple-choice odds.
The GISF exam cost isn't trivial, so treating this like a real investment makes sense. You're looking at significant money whether you go the SANS SEC275 route or self-study with other GISF study materials, and nobody wants to blow that budget on a failed attempt. The GISF passing score sits around 73-74% depending on the exam version, which sounds reasonable until you're actually sitting there second-guessing yourself on questions about access control models or (wait, was it discretionary or mandatory in that scenario?) incident response procedures.
Here's what I've seen work for people preparing for this entry-level GIAC certification: don't just read passively. The GISF exam objectives cover a ton of ground from cryptography basics to network security fundamentals to physical security controls, and you need to actually understand how these concepts connect to real scenarios. Build your index if you're doing the proctored version. Seriously, a good index is worth hours of study time. Practice with realistic questions that mirror the exam's scenario-based style. Give yourself enough runway because the GISF exam difficulty catches people off guard when they underestimate it.
Not gonna lie here. The GISF prerequisites are minimal on paper but you'll struggle hard if you don't have some baseline IT experience or at least strong familiarity with networking concepts and operating system basics. Career changers? Students sometimes? They find this out the hard way. The information security fundamentals certification assumes you can apply knowledge, not just memorize definitions. I had a coworker once who tried cramming everything the weekend before and he basically walked out halfway through, just done, said it felt like reading a foreign language. Anyway, point is you need actual foundation work here.
And once you pass? Don't forget about GIAC certification maintenance because those CPEs add up and the GISF renewal requirements kick in every four years. Mark it on your calendar now.
Before you schedule your exam, I'd seriously recommend working through a solid GISF practice test to gauge where you actually stand. The GISF Practice Exam Questions Pack gives you that reality check with questions that actually feel like the real exam, not just basic trivia. Use it a week or two before your test date to find your weak spots while you still have time to fix them.
This cert opens doors. Just make sure you're actually ready to walk through them.
Show less info
Hot Exams
Related Exams
GIAC GIAC Secure Software Programmer - C#.NET
GIACCertified Forensics Analyst
GIAC Penetration Tester
GIAC Systems and Network Auditor
GIAC Certified ISO-2700 Specialist Practice Test
GIAC Security Essentials
GIAC Information Security Fundamentals
GIAC Certified Enterprise Defender
GCIA – GIAC Certified Intrusion Analyst Practice Test
GIAC Advanced Smartphone Forensics
GIAC GIAC Secure Software Programmer - C#.NET
GIAC Secure Software Programmer – Java
GIAC Critical Controls Certification (GCCC)
GIAC Python Coder (GPYC)
GIAC Certified Perimeter Protection Analyst
GIAC Certified Firewall Analyst
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.