ECCouncil 712-50 (EC-Council Certified CISO (CCISO))
ECCouncil 712-50 CCISO Certification Overview
What is the EC-Council Certified CISO (CCISO)?
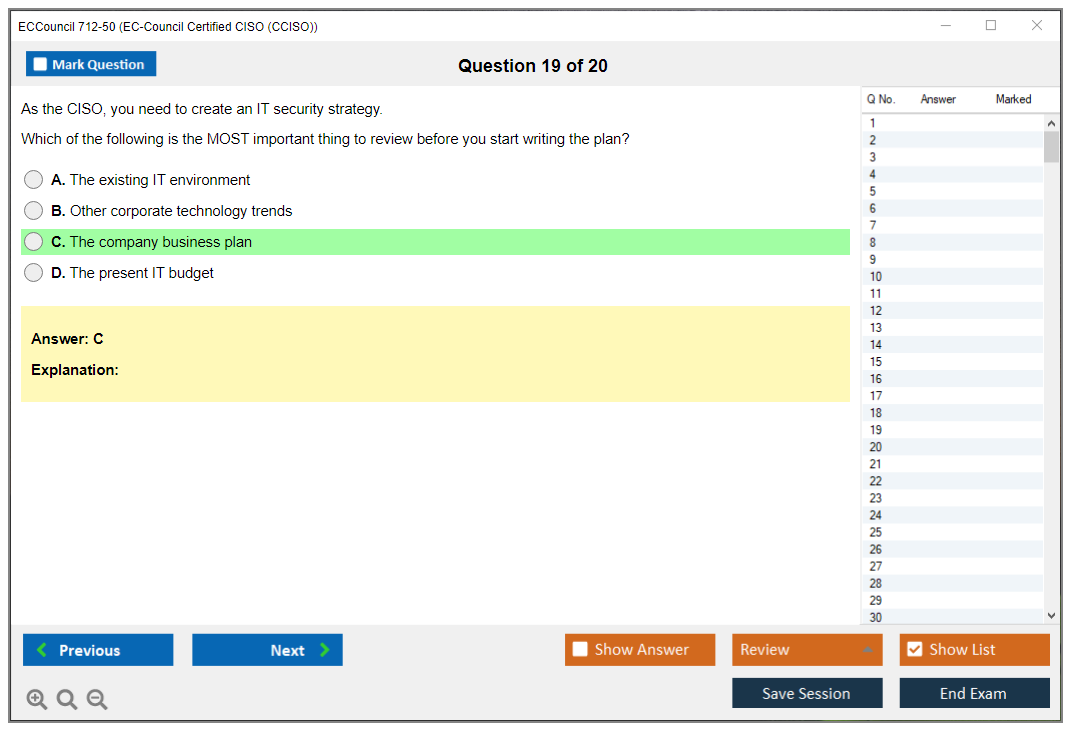
Okay, real talk here. If you're eyeing the corner office in cybersecurity, the ECCouncil 712-50 CCISO certification is probably already on your radar, or it should be. This is an executive-level cybersecurity leadership certification designed specifically for current and aspiring Chief Information Security Officers, and honestly, it's not your typical technical cert. I mean, this isn't about configuring firewalls or analyzing packet captures, you know? The EC-Council CCISO exam validates strategic, managerial, and technical knowledge required to build and manage enterprise security programs from 30,000 feet. Completely different animal than hands-on work.
What makes this thing different? Well, it focuses heavily on information security governance and risk management rather than hands-on technical skills, and I can't stress that enough. You won't be asked to demonstrate exploit techniques or write Python scripts during this exam. Instead, you're proving you can sit in a boardroom and explain why the company needs to allocate $2 million for zero trust architecture without making executives' eyes glaze over. The thing is, that's harder than cracking any hash.
The Certified Chief Information Security Officer credential is recognized globally as the premier certification for C-suite security professionals, no question. It demonstrates proficiency in security program management and strategy, budgeting, compliance, and board-level communication. Basically, the stuff that actually keeps you up at night when you're responsible for an entire organization's security posture and everything that comes with it. The CCISO differentiates itself from technical certifications by emphasizing business acumen, executive decision-making, and organizational leadership.
Five full domains here. The exam covers governance, controls, operations, core concepts, and strategic planning. We'll dig into those later, but just know they're designed to mirror what an actual CISO deals with daily, except condensed into exam scenarios. This credential is ideal for professionals transitioning from technical security roles to executive positions. That awkward leap from "the person who fixes things" to "the person who decides what needs fixing and convinces others to fund it."
Not gonna lie here. One of the most valuable aspects is how it validates your ability to align security initiatives with business objectives and communicate risk to non-technical stakeholders who'd rather talk about quarterly earnings. If you've ever tried explaining attack surface reduction to a CFO, you know why this matters. They're thinking ROI, you're thinking breach prevention. The disconnect is real. Wait, let me back up. I once sat through a budget meeting where the finance team spent forty minutes debating the coffee supplier contract but wanted to rush through our entire security infrastructure proposal in ten. Made me realize how differently these groups prioritize things. Anyway, the EC-Council CCISO exam 712-50 demonstrates commitment to professional development at the highest levels of information security management, which matters when you're competing for those six-figure leadership roles where everyone's resume looks identical.
Who should take the CCISO 712-50 exam?
Current Chief Information Security Officers seeking formal validation of their executive security expertise should absolutely consider this, period. Many CISOs have climbed the ranks through technical prowess and on-the-job learning, which is great, but formal certification adds weight to your resume and LinkedIn profile in ways experience alone sometimes can't. Security directors, managers, and senior architects preparing for CISO-level responsibilities will find this certification addresses the gap between technical knowledge and executive thinking that nobody really teaches you otherwise.
IT directors and CIOs with significant security oversight responsibilities benefit from the structured approach to security governance the CCISO provides. Same goes for risk management executives, compliance officers, and audit managers with security governance duties. If you're already dealing with frameworks, policies, and audit responses, this formalizes that expertise in a credential format that hiring managers recognize. Security consultants advising C-level executives on security program development and maturity can use the CCISO to establish credibility with clients who need executive-level guidance, not just technical recommendations.
Here's the thing though. You really need professionals with 5+ years of experience in information security management and leadership roles to make this worthwhile. The CCISO prerequisites are real, and we'll cover those specifically later, but jumping into this without meaningful leadership experience is setting yourself up for frustration and probably a failed exam. Individuals responsible for enterprise-wide security strategy, policy development, and incident response leadership and crisis management will find the curriculum directly applicable to their daily challenges in ways that feel immediately practical.
Security professionals seeking to differentiate themselves for executive-level career advancement use this cert as a signal. It tells recruiters and hiring managers you're serious about the C-suite track, not just collecting technical badges like Pokemon cards. Candidates who understand business operations, financial management, and organizational dynamics will get the most from this certification experience. If terms like CAPEX vs OPEX, vendor risk management, and board governance make sense to you already, you're in the right headspace to tackle this material.
Those comfortable with strategic thinking, vendor management, board presentations, and cross-functional leadership should take this exam, honestly. If presenting to executives makes you nervous or you've never managed a multi-million dollar budget, you might want to get some of that experience first before dropping money on this cert. The exam scenarios assume you've been in those rooms making those decisions under pressure.
CCISO vs CISSP vs CISM (executive focus comparison)
People ask me constantly. How do these three compare, and honestly they serve different purposes. Sometimes overlapping, sometimes not. The CCISO certification specifically targets C-level security executives, while CISSP covers broad technical security domains that span everything from crypto to physical security. If you want deep technical knowledge across cryptography, network security, and access control, CISSP is your jam, no doubt. But if you're trying to prove you can run an entire security program from a leadership perspective? CCISO all the way.
CISM (Certified Information Security Manager) focuses on management but lacks CCISO's executive strategic depth. It's good, don't get me wrong, but different. CISM sits in this middle ground between technical and executive, which makes it great for security managers who oversee teams and programs but aren't necessarily at the C-level yet or anytime soon. The CCISO exam objectives include procurement, vendor management, and financial planning that's just absent from CISSP entirely. Like completely missing. CISSP assumes you might touch those areas, but CCISO assumes you own them and report on them to the board.
CISM bridges technical and managerial roles adequately. CCISO exclusively addresses executive leadership challenges, though. The CCISO prerequisites require demonstrable executive experience, while CISSP accepts broader technical experience across different types of roles. You can get CISSP with mostly technical roles on your resume. Architect, engineer, analyst, whatever. For CCISO, EC-Council wants to see you've actually been making executive decisions that affect budgets and organizational direction.
Technical credibility matters. CISSP is valued for technical credibility. It tells people you understand how security actually works under the hood, the nuts and bolts. CCISO demonstrates boardroom-ready strategic thinking and political savvy. Many senior professionals hold multiple certifications: CISSP for technical foundation, CCISO for executive credibility, maybe CISM somewhere in the middle. I've met several CISOs who maintain both because they serve different audiences in their daily work. When you're hiring technical staff, they respect the CISSP because it speaks their language. When you're presenting to the board, they respect the CCISO because it proves you can think strategically.
CISM is managed by ISACA. Different domain structure there. CCISO follows EC-Council methodology, which has its own flavor and approach to cybersecurity education. CCISO uniquely addresses security program management and strategy from an organizational leadership perspective. How do you build a security culture that actually sticks, manage third-party risk at scale across hundreds of vendors, and balance security with business enablement without becoming the "department of no"?
Market recognition varies by region. It varies by industry too, but CCISO is increasingly preferred for actual CISO positions, especially in sectors where EC-Council certifications already have strong presence and brand recognition. The CCISO certification cost has higher initial investment but similar ongoing maintenance compared to CISSP or CISM when you factor everything in. We're talking exam fees, training costs, and renewal requirements that add up over three-year cycles.
Exam difficulty differs substantially here. The CCISO passing score requirements test strategic judgment and business acumen, not your ability to memorize port numbers or recall specific algorithm implementations like some technical exams. Training approaches vary too. CISSP emphasizes memorization of concepts across eight domains with thousands of facts to retain, while CCISO requires understanding real-world executive scenarios where there's rarely one "correct" answer and context matters enormously.
Career trajectory implications matter. CISSP supports technical advancement and proves you can architect secure systems that actually work. CCISO signals readiness for C-suite roles and proves you can lead security as a business function, not just a technical one. If you're trying to move from security architect to CISO, the CCISO directly addresses that transition in a way technical certs can't and won't.
The CCISO study guide materials assume you're already comfortable with information security governance and risk management concepts. They're not teaching you what risk is from scratch, they're teaching you how to communicate it to stakeholders who control budgets and don't care about technical details. That's a fundamentally different learning objective than technical certifications pursue. Look, many folks coming from technical backgrounds find they need multiple attempts at the CCISO because the executive mindset is really different from how engineers think. You're not troubleshooting technical problems with clear solutions, you're making business decisions with incomplete information while managing stakeholders who may not understand or value security the way you do. The Certified Ethical Hacker teaches you how systems get compromised through exploitation. The CCISO teaches you how to convince the CFO to fund the fixes without a guaranteed breach happening first.
CCISO 712-50 Exam Details
ECCouncil 712-50 (CCISO) certification overview
The ECCouncil 712-50 CCISO certification is EC-Council's executive cybersecurity leadership credential for folks who are expected to make actual grown-up calls. Not "configure the firewall" calls. "Explain to the board why we are dropping $600k on a program that prevents a disaster that has not even happened yet" calls.
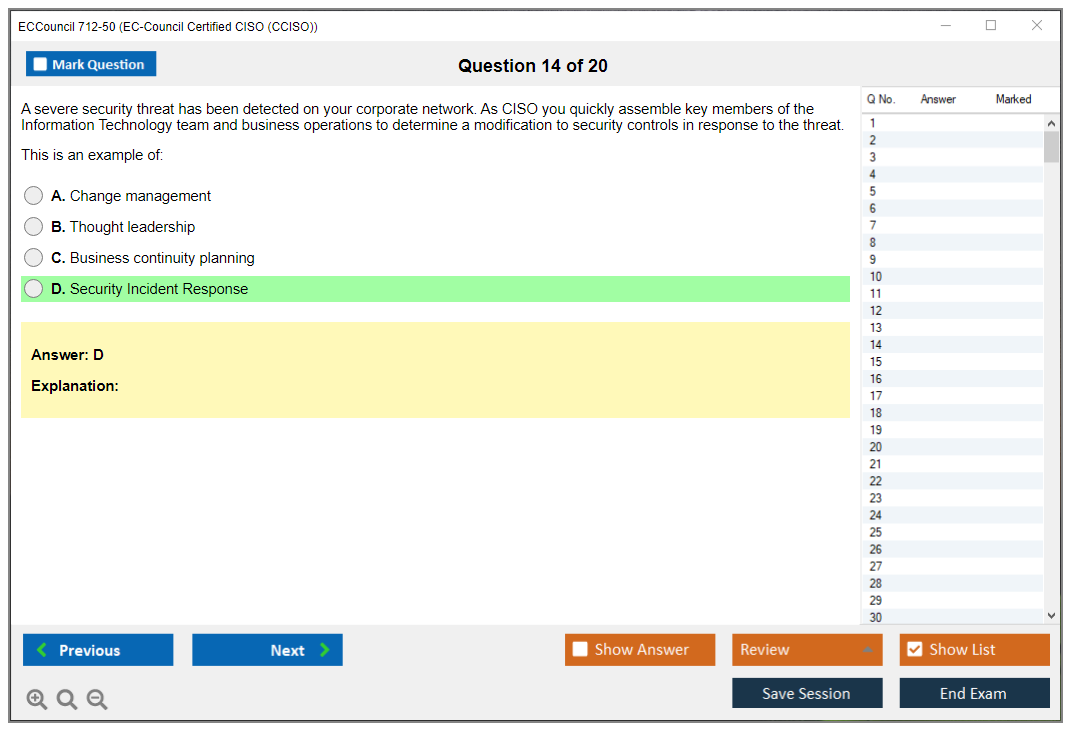
This one is closer to running a security program than being a security engineer, honestly. Policies. Risk acceptance. Metrics. Vendor drama. And yeah, incident response leadership and crisis management when everything is on fire and the CEO wants updates every 15 minutes. I mean, sometimes every five if things get really bad.
What is the EC-Council Certified CISO (CCISO)?
The Certified Chief Information Security Officer credential covers information security governance and risk management plus security program management and strategy. Less about commands. More about outcomes, tradeoffs, and accountability.
Short version: executive judgment, money problems, and people problems.
Who should take the CCISO 712-50 exam?
If you are already a security manager, director, deputy CISO, GRC lead, or you are the accidental CISO because the company is mid-sized and "you are the security person," the EC-Council CCISO exam 712-50 fits. If you have only got hands-on technical experience and you have never owned a budget, written an annual plan, or dealt with procurement, this exam is still doable. The thing is it can feel like you are reading a foreign language that just happens to use English words.
CCISO vs CISSP vs CISM (executive focus comparison)
CISSP is broad and can drift technical depending on your background and the question set. CISM lives in management land and governance. CCISO is the one that keeps pulling you back to C-suite behaviors like board presentations, budget justification, vendor selection, and how you prioritize when everyone is yelling and the clock is ticking. Different vibe. Less "what control is best," more "what decision is defensible and fundable."
CCISO 712-50 exam details
Exam format, number of questions, and time limit
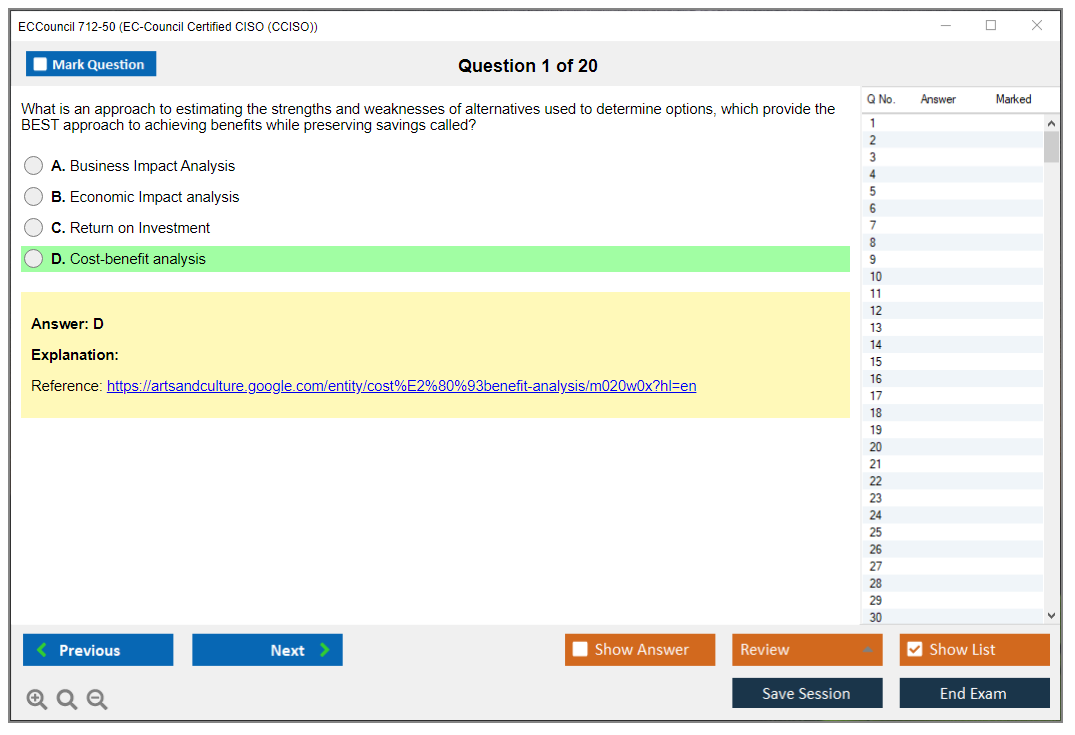
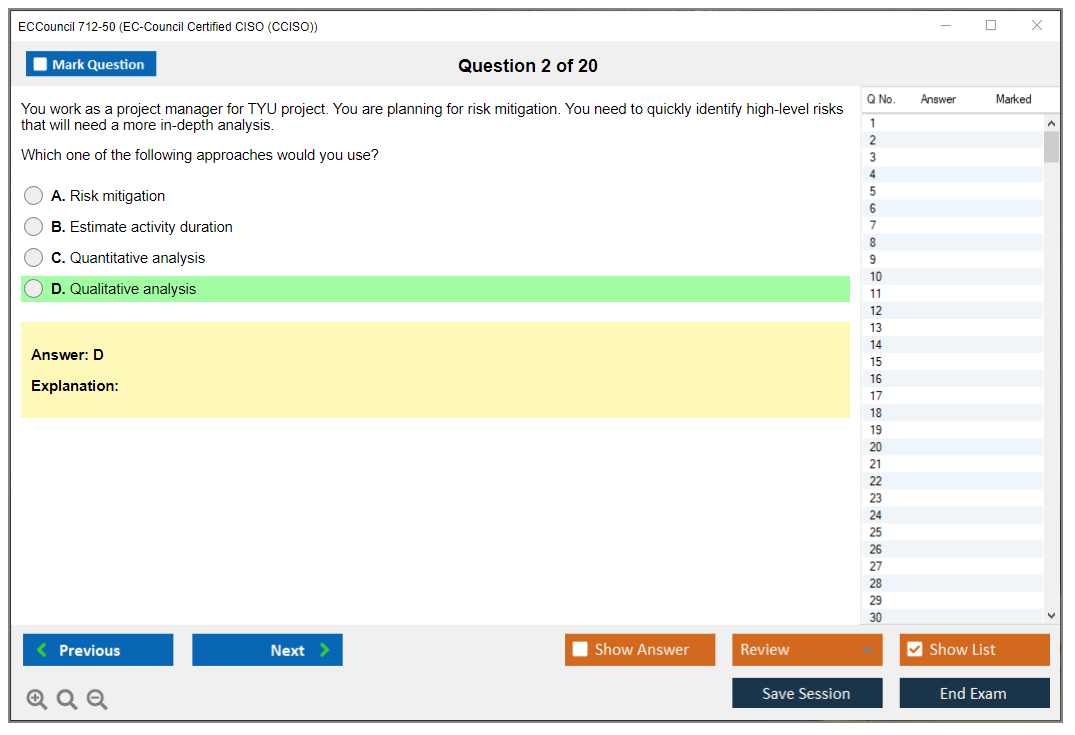
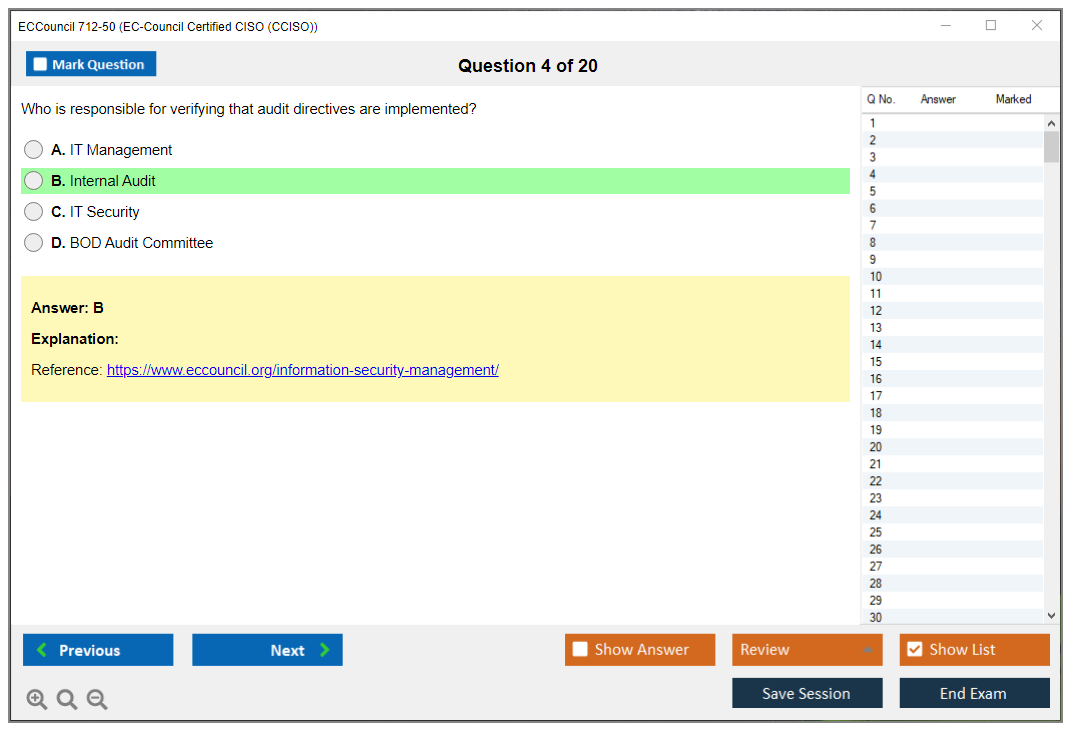
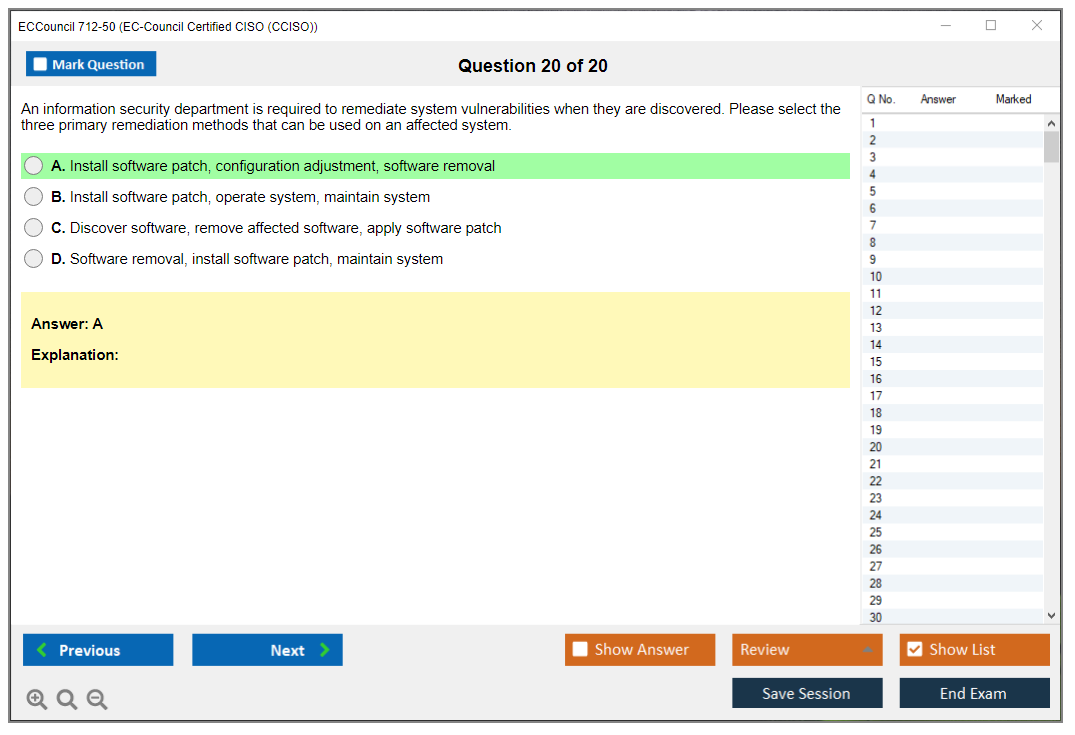
EC-Council CCISO exam 712-50 consists of 150 multiple-choice questions, and you get 3 hours (180 minutes). Four options per question, A through D.
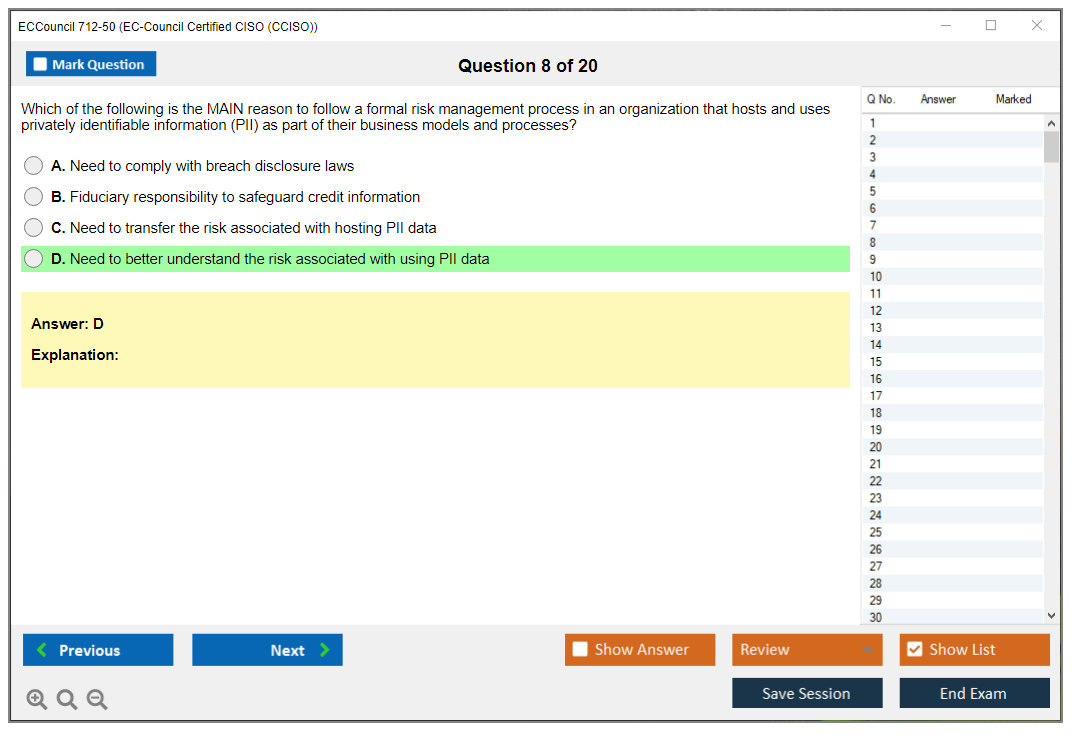
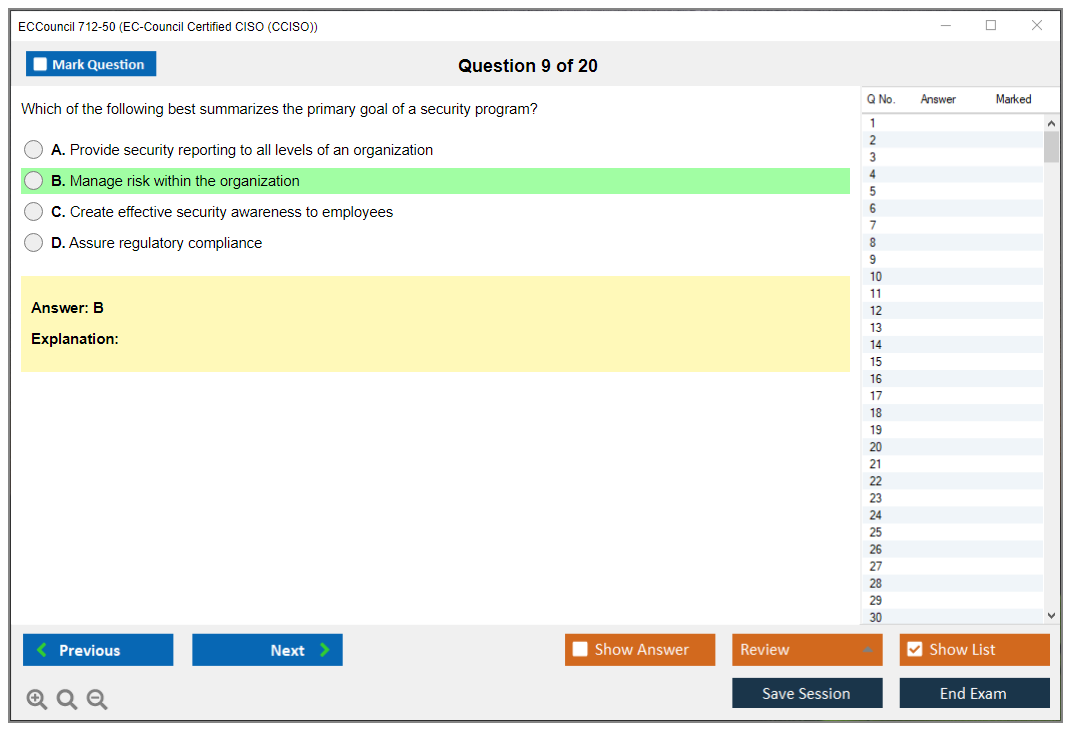
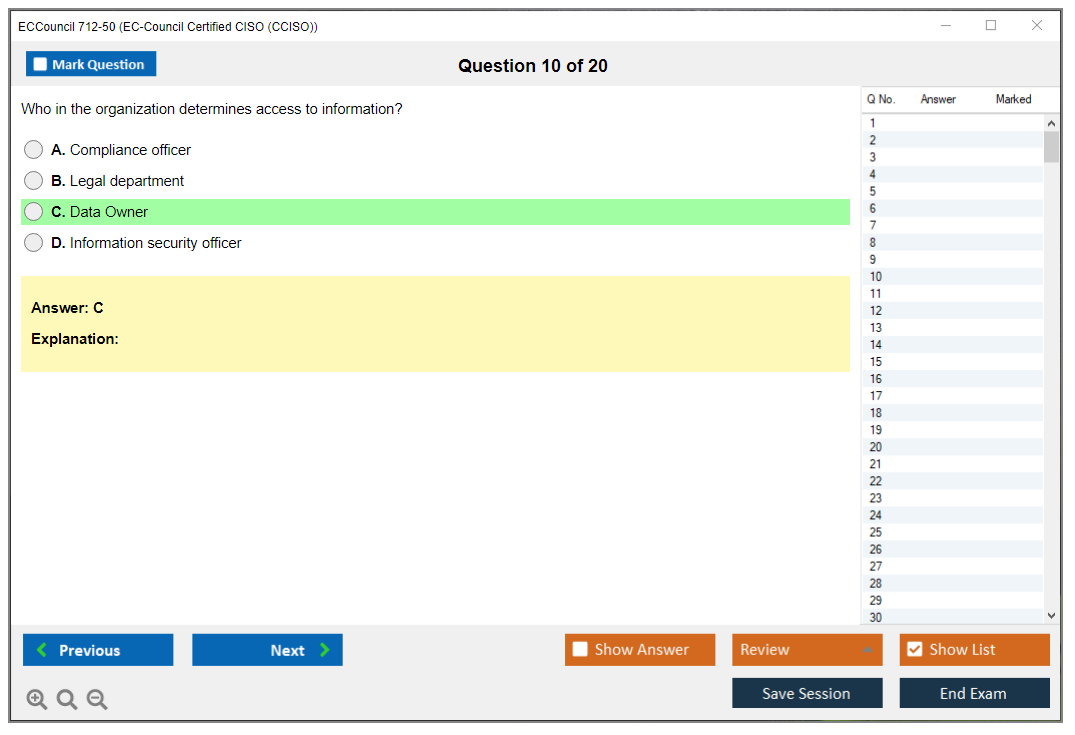
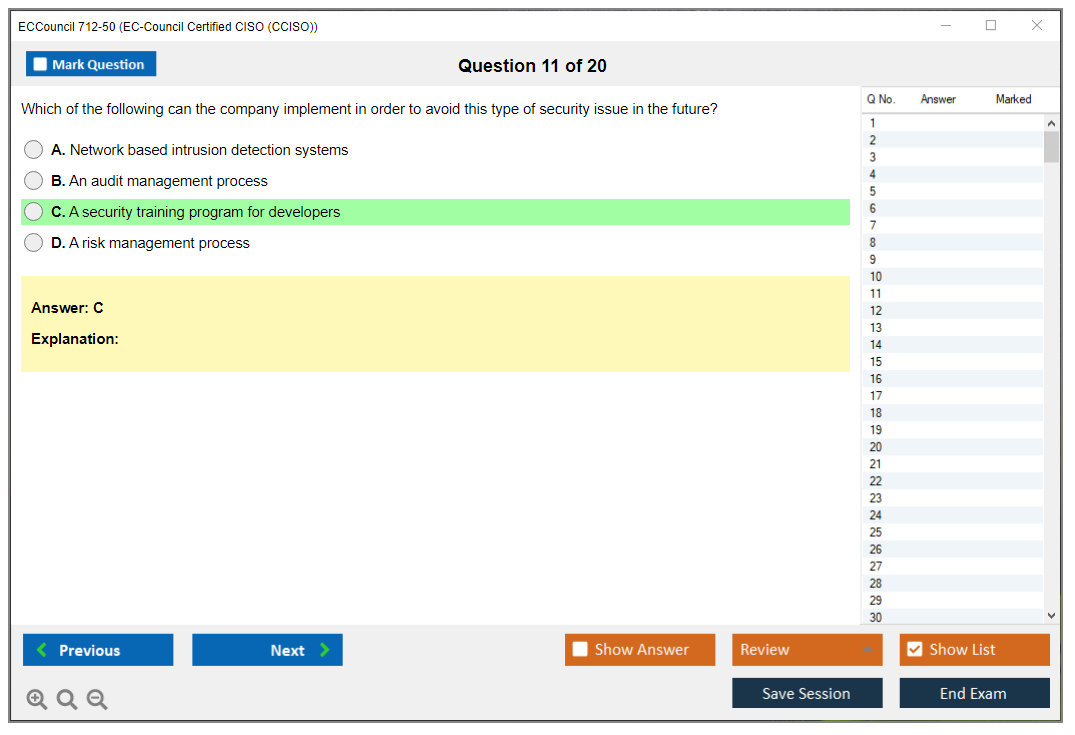
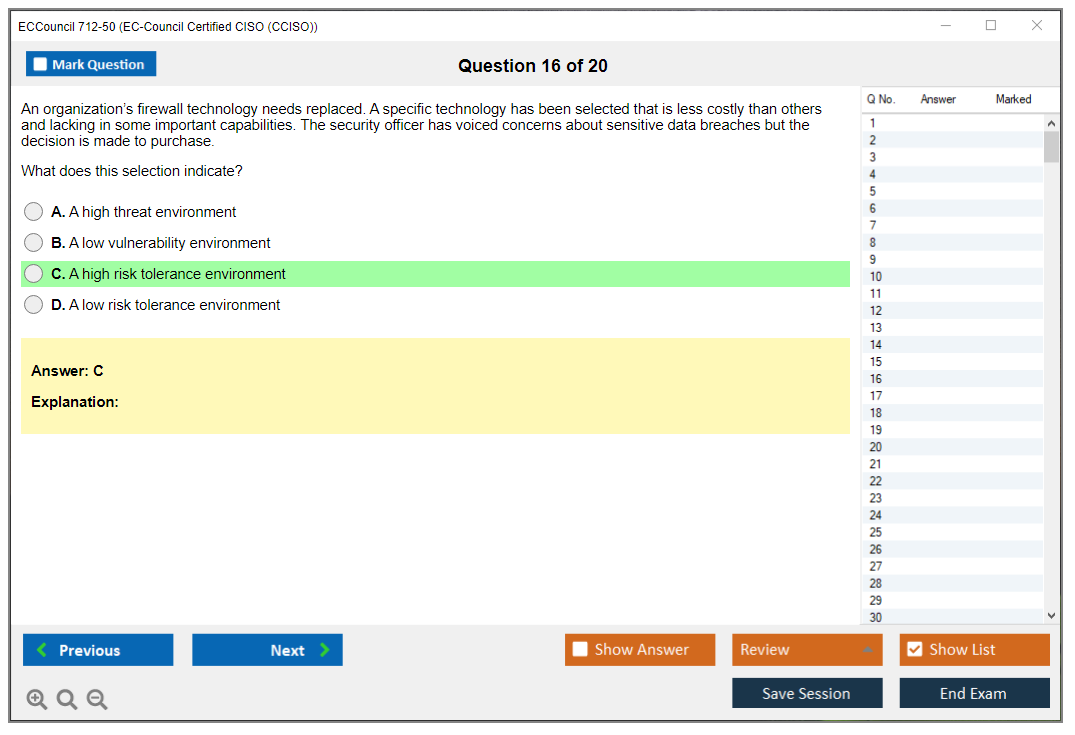
All questions are scenario-based, and that is the whole point. You are not being tested on recall like "what does this acronym mean." You are being tested on whether you can read a situation, see the constraints, and choose what a security executive would do next, even when every answer option sounds sort of reasonable if you squint hard enough.
The questions are distributed across five domains with different weights, because not everything is equally important at the CISO level. Delivery is through Pearson VUE testing centers or an online proctoring option, which is great if you test well at home, and terrible if your environment is noisy or your internet is sketchy.
No penalty for wrong answers. Answer everything. Always. Leaving blanks is basically donating points to the void.
The interface lets you flag questions for review, and you should use that, because some scenarios are long and you will want a second pass after you have seen the rest of the exam. No calculator required. No notes. No reference materials. This is not a math exam, it is a "do you think like leadership" exam.
Online proctoring needs a webcam, stable internet, and a secure room. Honestly the "secure room" part is harder than it sounds if you have got roommates or kids. In-person testing at Pearson VUE is controlled, with ID verification, which some folks prefer because it removes the "will my cat jump on the desk and invalidate my exam" risk. Results are typically immediate for computer-based testing.
CCISO passing score (what to expect and how scoring works)
The official CCISO passing score is 70%, which is 105 out of 150 correct. That is the number everyone remembers, and yeah, hitting exactly 70% is a pass.
Now the part people miss. EC-Council uses a scaled scoring methodology so different versions of the exam stay consistent, because difficulty varies by form. Your raw score is converted into a scaled score that accounts for question difficulty variations, and not all questions are weighted equally. Some harder questions can carry more value.
Experimental questions may show up. They do not count. You cannot identify them. Treat everything like it matters.
No partial credit. One question, one selected answer, correct or incorrect.
You get a pass/fail notification right away when you finish. Domain performance feedback is more useful when you fail, because it points to where you were weak. Passing candidates typically just see pass/fail, not a detailed score breakdown, which is annoying if you are the type who wants to measure everything, but that is the deal.
My recommendation is to aim for 80%+ on a CCISO practice test before you schedule, because 70% on the real thing can feel tight when scenarios get wordy and you start second-guessing yourself.
CCISO exam difficulty (experience level and common challenges)
This exam is challenging, but not because it is obscure. The difficulty is the scenario complexity and the fact that "best" is often "best given the business reality," not "best in a textbook."
Purely technical folks often struggle. Not because they are not smart. Because the exam expects you to think about budgets, stakeholder management, organizational politics, and competing priorities, and it assumes you know what a board wants to see and how a CISO frames risk without sounding like a doomsday blogger who just discovered ransomware exists. Which, sidebar, is half the vendor pitches I sat through last quarter. "The sky is falling, buy our box." Cool story. Where is the ROI model?
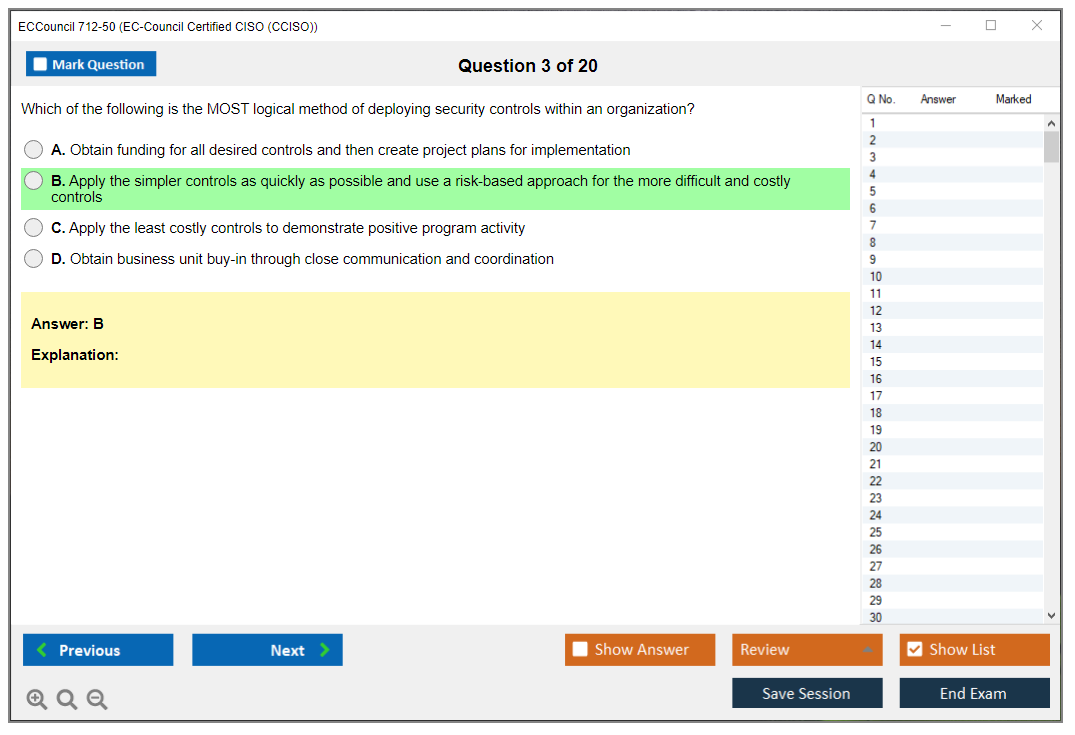
Time management is a real thing here. Scenarios can be long, and if you read every sentence three times, you will start rushing later and make dumb mistakes. Another common pitfall is overthinking, reading hidden meaning into a scenario that is not there, or picking the most technically perfect control even when the question is really about executive sequencing, like establishing governance first, defining ownership, and then rolling out controls.
Real-world leadership experience makes the exam feel much easier. Theoretical knowledge alone can get you close, but it is usually not enough to consistently pick the "executive practical" answer.
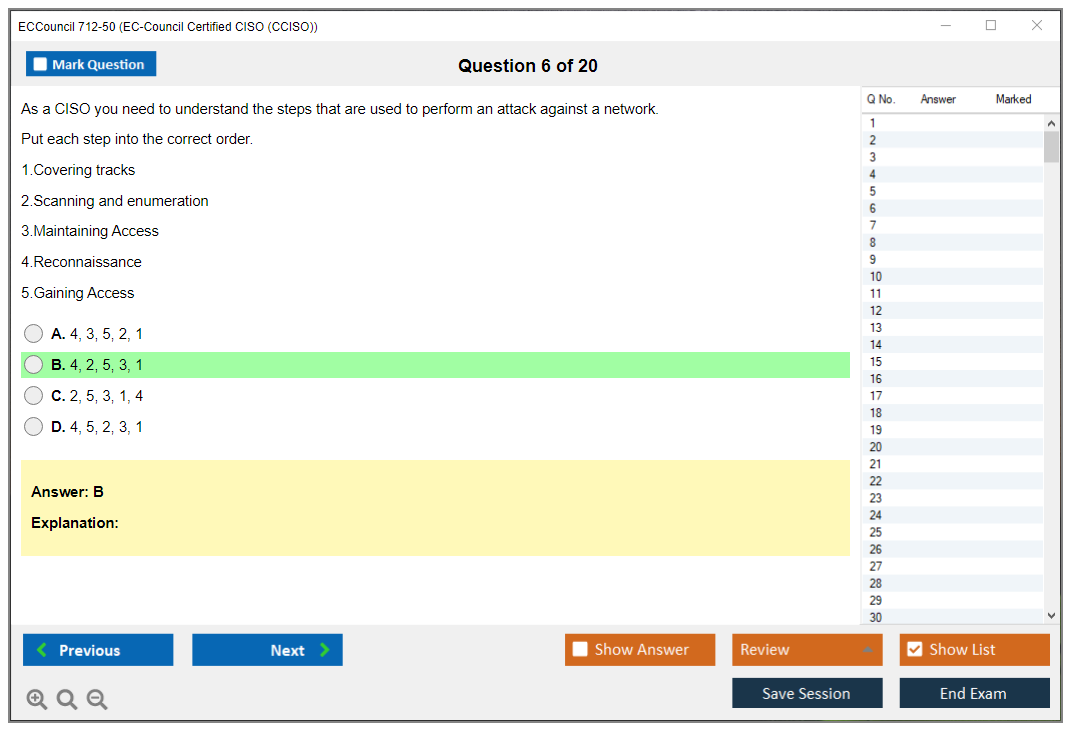
CCISO exam objectives (domains)
The CCISO exam objectives are split into five domains. You do not need to memorize the domain names like trivia, but you do need to recognize what kind of thinking each domain is pushing.
Domain 1 is governance and risk management. Domain 2 is controls, compliance, and audit management. Domain 3 covers program management and operations. Domain 4 addresses core concepts. Domain 5 digs into strategic planning, finance, procurement, and vendor management. That last one gets people, because procurement and finance questions feel weird if you have never owned a budget line.
CCISO prerequisites and eligibility
Work experience requirements (and what counts)
CCISO prerequisites are experience-heavy. EC-Council expects demonstrated work in multiple CCISO domains, and they care about leadership responsibilities, not just being adjacent to leadership. Managing a program. Owning risk decisions. Being accountable for outcomes.
Training vs exam-only eligibility (EC-Council pathways)
There is typically a training path and an exam-only path, and the exam-only route usually means more scrutiny on your experience documentation. Training does not magically replace experience, but it can make the application process smoother depending on your background.
Application/endorsement considerations (documentation and approval)
Expect paperwork. Proof of roles. Timelines. Maybe employer verification. Keep it clean. Titles alone do not convince anyone if the job duties do not match.
CCISO certification cost (full breakdown)
People ask about CCISO certification cost a lot, and the honest answer is this: it depends on whether you buy training, a voucher bundle, or you are doing an employer-paid package. Exam vouchers vary by region and promo timing, and training can dwarf the exam fee if you go official instructor-led.
Retakes cost money too, so budget like an adult. If you are paying out of pocket, plan for one attempt plus a retake cushion, because the cheapest exam is the one you only take once.
Best CCISO study materials (official + third-party)
A solid CCISO study guide should push you toward decision-making, not memorization. Official courseware is aligned to the domains, and it is useful for filling gaps, especially in finance, governance, and vendor management if you have lived mostly in technical delivery.
Third-party books and notes help, but pick materials that include scenario questions and explanations that talk about "why this option is best for an executive," not just "this is the right control."
CCISO practice tests and exam prep strategy
Good practice tests feel annoying. That is how you know they are realistic. They should be scenario-heavy, slightly ambiguous, and they should force you to choose the least-wrong answer based on priorities, budget, and risk tolerance.
Give yourself 2 to 6 weeks depending on experience. If you have been doing security leadership for years, you might just need to map your experience to the domains and tighten terminology. If you are coming from engineering, you will need more time to get comfortable with governance, metrics, and finance language. Honestly, the finance stuff trips up more technical people than anything else.
How to pass the CCISO 712-50 exam
Focus on board communication, risk framing, program planning, and vendor decisions. Practice reading questions fast without missing the actual ask. Use flags. Do a first pass, bank easy wins, then come back for the long scenarios.
Final week: sleep, review weak domains, stop cramming.
CCISO renewal and maintaining your certification
CCISO renewal requirements are the usual mix of continuing education and fees. Track your credits as you earn them, not at the deadline, because hunting for proof months later is miserable. If EC-Council audits, you want receipts, dates, and descriptions ready to go.
FAQs (CCISO 712-50)
How much does the EC-Council CCISO (712-50) exam cost?
Voucher pricing varies by region and whether you bundle training, retakes, or labs, so check EC-Council and Pearson VUE listings for current numbers. If your employer is paying, ask for a bundle that includes a retake.
What is the passing score for the CCISO 712-50 exam?
70%, or 105/150, with scaled scoring used to keep exam versions consistent.
How hard is the CCISO certification exam?
Hard if you are technical-only, because it is executive judgment under constraints. Easier if you have done security leadership, budgeting, governance, and crisis response for real.
What are the prerequisites for CCISO certification?
Documented experience across CCISO domains is the big one. Training can help, but experience is what the credential is really validating.
How do you renew the EC-Council CCISO certification?
Continuing education plus renewal fees, tracked over the renewal cycle. Do not wait until the last month. That is how people lose certs they worked hard to earn.
CCISO Exam Objectives (Domains)
Domain 1 -- Governance and risk management (weight: approximately 26%)
This domain's massive. Honestly it's the heaviest chunk of the CCISO exam and for good reason. If you can't govern a security program you're not ready to be a CISO.
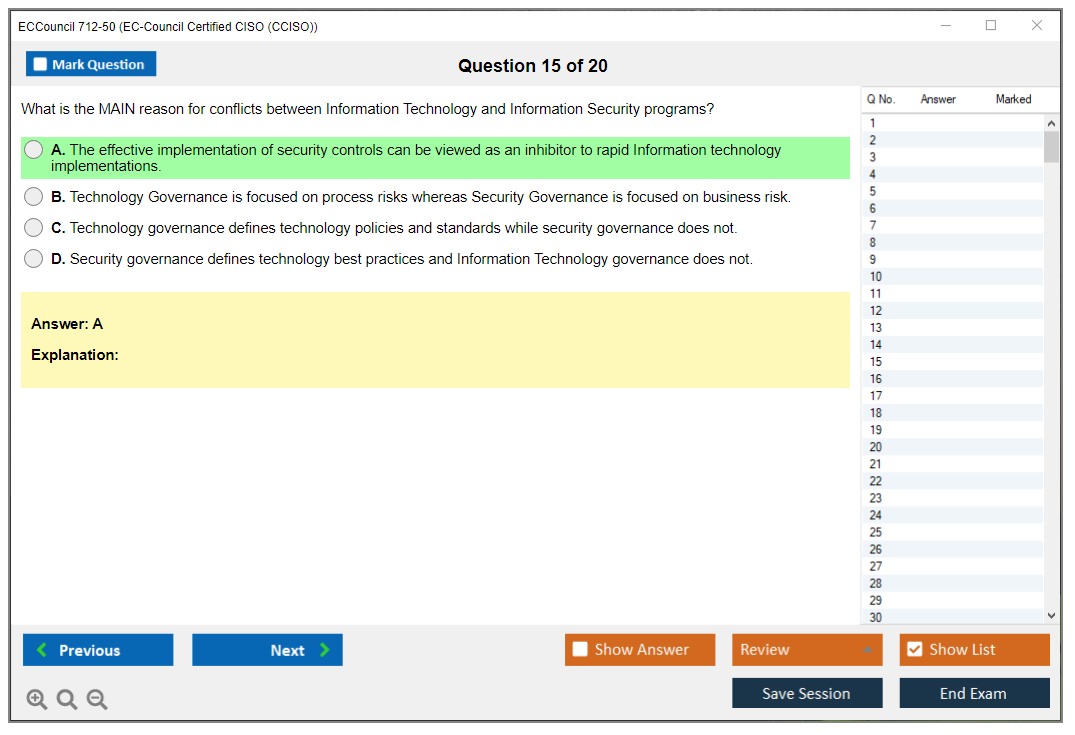
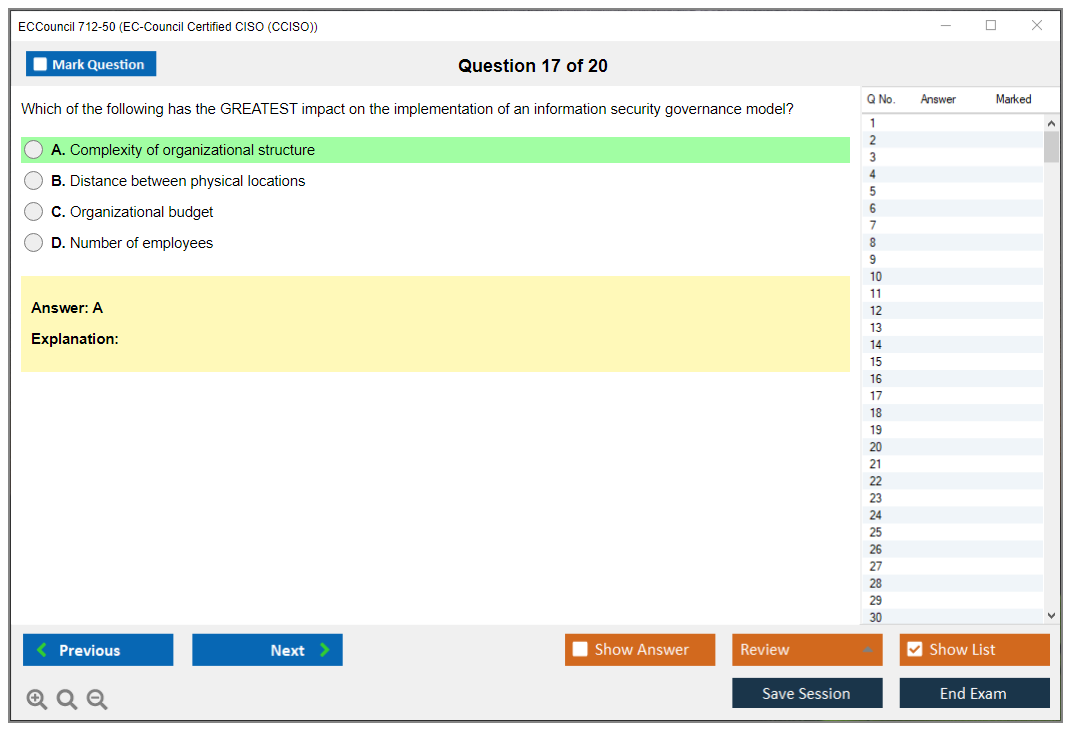
You'll need to understand how to establish enterprise information security governance frameworks from scratch, which means knowing how to align security structures with organizational objectives and culture. Not every company operates the same way. A startup needs different governance than a Fortune 500 bank, and you're expected to recognize that.
Creating policies, standards, procedures, and guidelines is table stakes. But the exam goes deeper into board-level governance, fiduciary responsibilities, and executive accountability. You've gotta speak the language of the boardroom, not just the SOC. I mean, if you can't explain why a security investment matters to someone who cares about shareholder value you're gonna struggle in this domain.
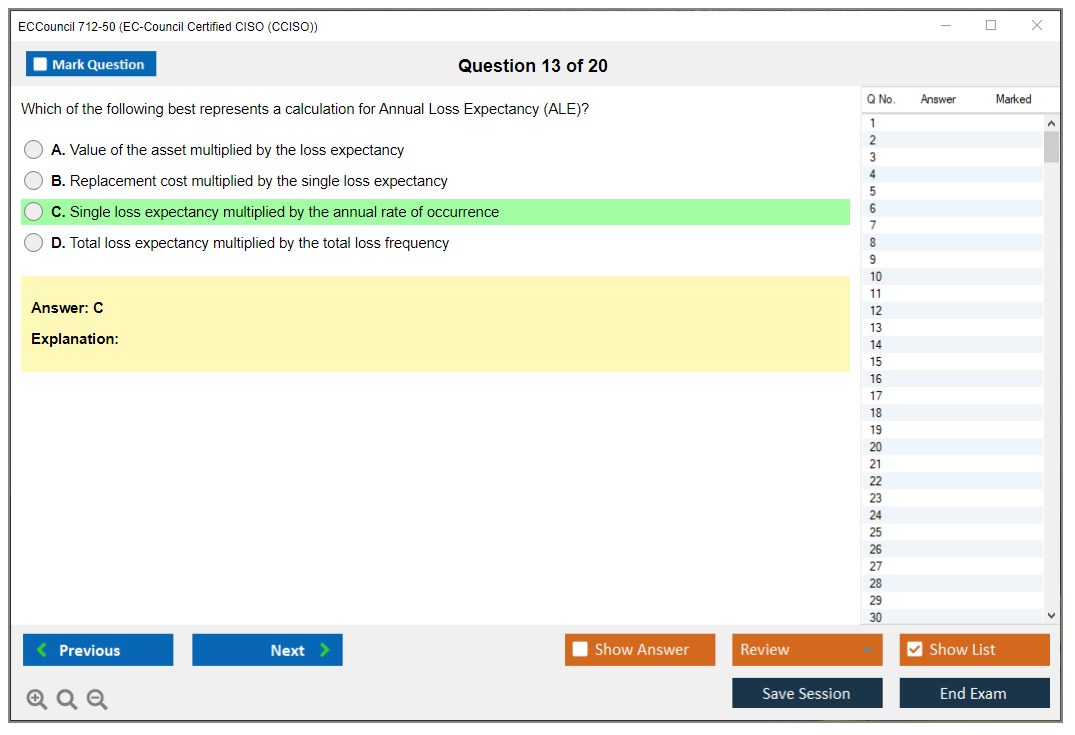
Risk management methodologies? Serious attention here. You'll see questions on qualitative versus quantitative risk assessment approaches, and you better know when to use each. Risk treatment strategies (accept, avoid, transfer, mitigate) come up constantly, and they want you to justify decisions with business context, not just technical reasoning.
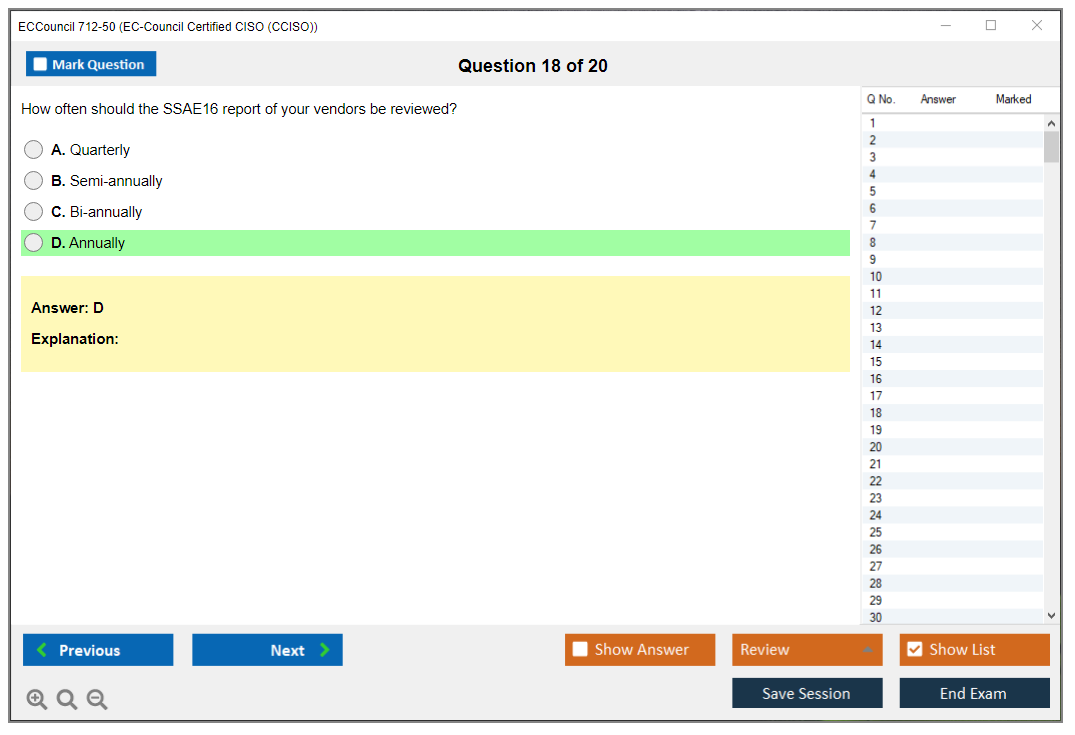
Regulatory compliance is another beast. GDPR, HIPAA, SOX, PCI-DSS, and industry-specific requirements all matter. Third-party risk management and vendor security assessment programs are huge too, especially since supply chain attacks keep making headlines. You'll need to know how to evaluate vendors, what questions to ask, and how to monitor them throughout the relationship lifecycle. This honestly becomes a full-time job in itself when you're juggling dozens of vendors who all claim they're "enterprise-ready" but half of them can't even complete a basic security questionnaire without three rounds of follow-up.
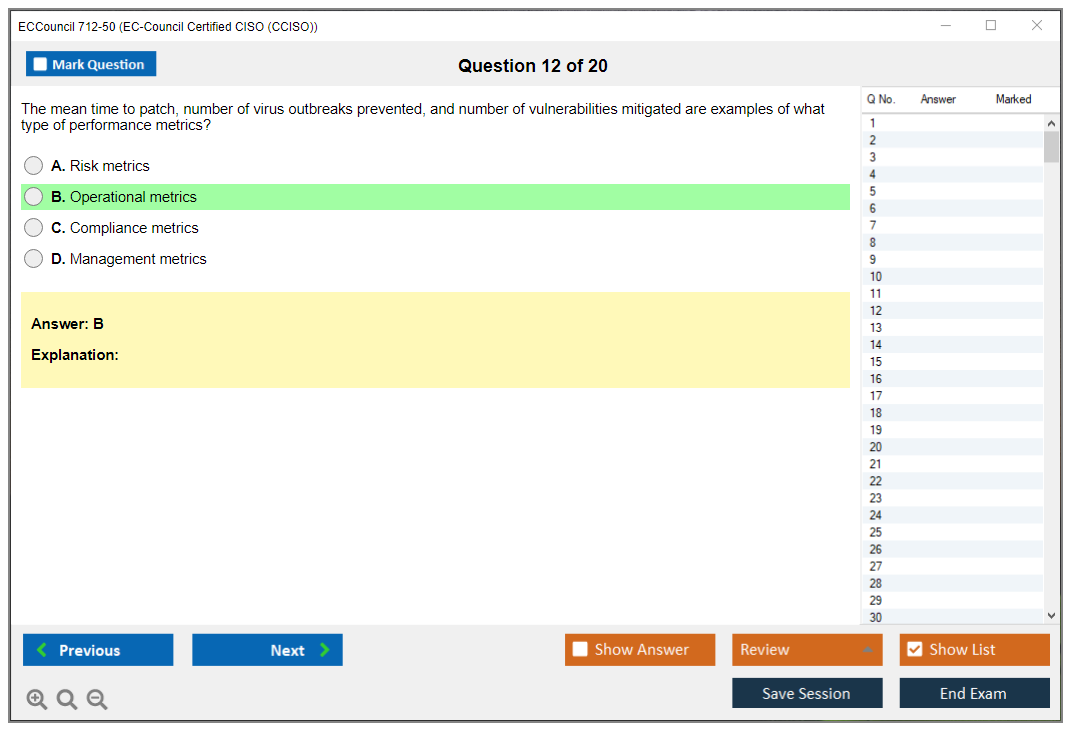
Security metrics, KPIs, and KRIs? Critical for measuring program effectiveness. They're also critical for communicating to executives who don't care about technical details but absolutely care about numbers. Business impact analysis and criticality assessment help you prioritize where to spend limited budgets. Something every CISO deals with constantly.
Enterprise risk management integration matters because security doesn't exist in a vacuum. You're part of a broader ERM program and need to play nice with other risk functions. Legal and regulatory considerations affect everything you design and implement, and privacy program development increasingly intersects with security governance thanks to regulations like GDPR and CCPA.
You'll need familiarity with security governance frameworks like ISO 27001, NIST CSF, COBIT, and framework selection criteria. Board reporting and risk communication are essential skills. Translating technical risks to business impacts is literally part of the job description for a CISO. Look, if you can't make the CFO understand why you need another $500K for security tooling you won't get the budget. I've watched talented technical people lose funding battles because they couldn't frame the ask properly, which is frustrating when you know the threat is real but can't articulate it in terms that resonate with finance people who think of security as pure cost with no upside.
Domain 2 -- Information security controls, compliance, and audit management (weight: approximately 24%)
Second heaviest domain. It's all about controls and proving they work.
Security control frameworks including NIST 800-53, CIS Controls, and ISO 27002 form the foundation here. Control selection, implementation, and validation based on risk assessment outcomes means you're not just throwing controls at the wall. You're being strategic and justifying every decision.
Compliance program management across multiple regulatory and contractual requirements gets complicated fast when you're dealing with HIPAA for healthcare data, PCI-DSS for payment cards, and SOX for financial reporting all at the same time. Internal audit coordination and external audit management require you to work with auditors who often don't understand security as well as they should. Which is frustrating but part of the role.
Evidence collection, documentation, and audit trail maintenance for compliance verification is tedious but absolutely necessary. Security control testing methodologies include vulnerability assessments, penetration testing, and control validation. You need to know the difference and when each applies.
Continuous monitoring programs help. Automated compliance validation tools help reduce manual work, but you still need to understand what they're doing under the hood. Gap analysis between current security posture and regulatory or framework requirements identifies where you're falling short. Remediation planning, tracking, and validation for identified control deficiencies shows you can actually fix problems instead of just identifying them.
Compliance reporting? Different audiences need different messages. Reporting to regulators, auditors, customers, and internal stakeholders requires tailoring your communication style. Managing audit findings, creating corrective action plans, and demonstrating remediation is something you'll do quarterly if not monthly. Security assessment and authorization processes for system accreditation matter particularly in government and defense sectors.
Control effectiveness measurement and maturity model assessment approaches help you understand whether you're getting better or just spinning your wheels. Integration of security controls with IT service management and change control processes ensures security doesn't become a bottleneck that slows down the business. Attestation, certification, and third-party validation programs like SOC 2, ISO certification, and FedRAMP provide external validation that your controls actually work, which customers and partners increasingly demand.
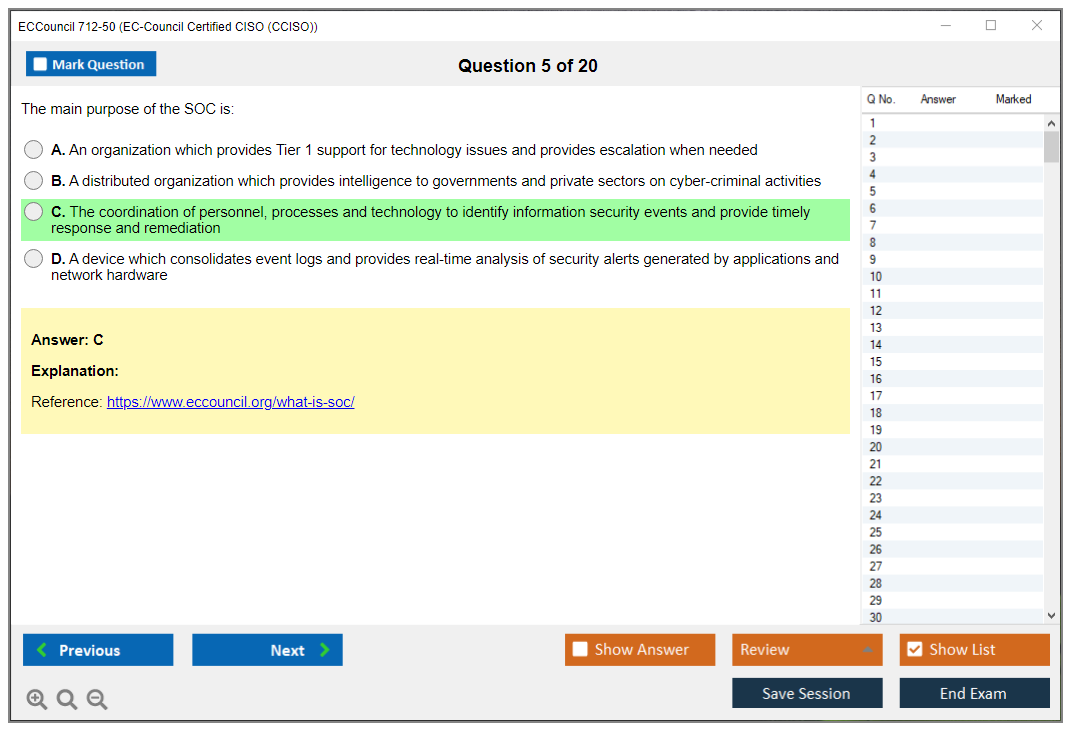
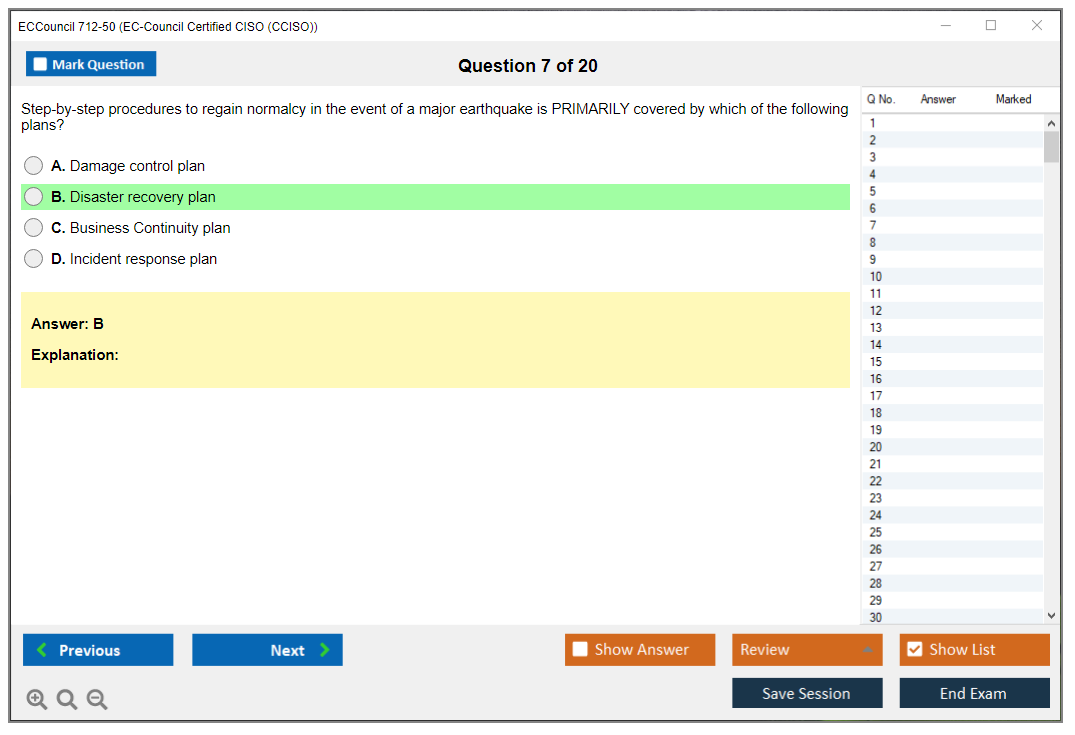
Domain 3 -- Security program management and operations (weight: approximately 23%)
This domain focuses on running the day-to-day security program and keeping everything operational.
Designing and implementing full enterprise security programs aligned with business strategy means understanding what the business is trying to accomplish and enabling it securely rather than just saying "no" to everything. SOC design, staffing, and operational management is critical. You need to know how to build a security operations center from scratch or optimize an existing one.
Incident response program development? Essential. Including incident response leadership and crisis management capabilities is something every CISO needs. Not gonna lie, incident response under pressure separates good CISOs from mediocre ones. Security incident classification, escalation procedures, and response playbooks ensure consistency when things go sideways at 2 AM.
Business continuity and disaster recovery planning with security considerations ensures you can recover from major incidents. Security architecture review and integration with enterprise architecture programs keeps security embedded in design decisions rather than bolted on afterward.
Identity and access management program governance and strategic direction matters because IAM is foundational to everything else. Data protection and classification programs including encryption strategy determine how you protect your most valuable assets. Security awareness and training programs for employees, contractors, and executives reduce human risk, which is usually your biggest vulnerability.
Physical security integration? Often overlooked but matters. Badge readers, cameras, and physical access controls all generate security data that needs to tie into your broader monitoring. Security tool selection, deployment, and lifecycle management requires balancing vendor relationships, budget constraints, and technical requirements.
MSSP evaluation and oversight comes up when you're considering outsourcing parts of your security operations. Security operations metrics, dashboards, and performance reporting keep executives informed without overwhelming them with details. Threat intelligence program development and integration with security operations helps you stay ahead of emerging threats.
Security program maturity assessment and continuous improvement initiatives ensure you're always getting better, which matters when you're competing for budget against other priorities. Priorities that frankly might seem more urgent to the business even though they're not addressing the real risks you're seeing in threat intelligence feeds.
Domain 4 -- Information security core concepts (weight: approximately 14%)
Lighter domain. Still important though. This covers fundamental technical knowledge that CISOs need even if they're not hands-on anymore.
Fundamental security principles like the CIA triad (confidentiality, integrity, availability) are baseline knowledge. Defense-in-depth strategy and layered security architecture approaches explain why you need multiple overlapping controls instead of relying on any single defense.
Security domains span network, application, endpoint, cloud, mobile, and IoT. Each has unique challenges. Cryptography principles and appropriate use cases for encryption technologies matter because encryption isn't always the answer despite what vendors claim. Authentication, authorization, and accounting concepts and implementation underpin most access control systems.
Security models like Bell-LaPadula, Biba, and Clark-Wilson have practical applications in designing secure systems, though honestly these feel a bit academic compared to the other domains that focus more on real-world scenarios. Threat space understanding including threat actors, attack vectors, and emerging threats keeps you current on what attackers are actually doing. Vulnerability management lifecycle from identification through remediation is straightforward but essential.
Security technologies overview covers firewalls, IDS/IPS, SIEM, DLP, and endpoint protection. You don't need to configure them but you need to understand what they do and their limitations. Cloud security considerations including shared responsibility models are increasingly important as everyone moves to AWS, Azure, or GCP.
Secure software development lifecycle? DevSecOps principles help you shift security left and catch vulnerabilities earlier. Network security architecture including segmentation, zero trust, and micro-segmentation represents modern approaches to network defense. MDM and BYOD security address the reality that everyone wants to use personal devices for work. Emerging technologies like AI/ML security, blockchain, and quantum computing implications prepare you for future challenges even if they're not immediate concerns today.
Domain 5 -- Strategic planning, finance, procurement, and vendor management (weight: approximately 13%)
Smallest domain. But arguably the most business-focused. This is where technical security people often struggle because it requires financial and strategic thinking.
Security strategy development aligned with organizational strategic objectives means your security roadmap supports what the business is trying to accomplish over the next 3-5 years. Multi-year security roadmap creation with prioritized initiatives and milestones gives you a plan instead of just reacting to incidents.
Security budget development, justification, and allocation across program areas is something you'll do annually and defend constantly. Return on security investment and cost-benefit analysis for security initiatives helps you prioritize where limited dollars go. CapEx versus OpEx decisions for security tools affect cash flow and accounting treatment differently.
Procurement processes for security products and services including RFP development ensures you're getting competitive pricing and appropriate terms. Vendor evaluation criteria (security capabilities, financial stability, support quality, roadmap alignment) help you pick vendors who'll be around in five years. Contract negotiation for security products, services, and managed security providers can save significant money if you know what to negotiate.
SLAs and OLAs for security services set expectations with vendors and internal teams. Vendor risk management throughout supplier lifecycle from onboarding to termination addresses the reality that vendors create risk exposure. Fourth-party risk considerations matter when your vendors use subcontractors or cloud services that you've never directly evaluated.
TCO analysis for security technology investments captures not just purchase price but ongoing maintenance, staffing, and integration costs. Build versus buy decisions for security capabilities require honest assessment of your team's capabilities and opportunity costs. M&A security due diligence and integration planning is essential when your company acquires others or gets acquired. Communicating security value proposition to CFO, board, and business unit leaders is how you get buy-in and budget for what you need to accomplish.
The thing is, the 712-50 practice exam questions can help you test your knowledge across all five domains before sitting for the actual CCISO exam. Similar to how the CEH v13 certification focuses on technical hacking skills, CCISO targets executive-level security leadership and program management.
CCISO Prerequisites and Eligibility
CCISO prerequisites and eligibility (what you actually need)
Look, if you're gunning for the ECCouncil 712-50 CCISO certification, the gatekeeping's real. Honestly? I kinda like that. This credential's supposed to represent executive cybersecurity leadership certification, not some "I configured a firewall once and skimmed a policy doc" situation. Paper titles don't matter nearly as much as what you actually did, who you led, what you owned, and (here's the kicker) whether you can prove it.
Read that again.
Prove it.
Work experience requirements (and what counts)
The baseline requirement seems simple enough on paper: minimum five years of paid, full-time work experience in information security management. Paid. Full-time. Management. If your background's mostly technical delivery with basically zero authority over people, money, or actual decisions, you're gonna have to work way harder to justify it.
Also, at least three of those five years must be in information security management at a senior level or CISO role. Senior means you weren't just "the most senior person on the night shift." It means you were doing executive-type work. Setting direction, making calls that really affect risk, being accountable when things go sideways. Presenting board updates. Steering committees. Signing off on exceptions and owning outcomes when everything hits the fan.
What counts as "qualifying roles"? EC-Council's pretty clear: CISO, CSO, security director, security manager, or equivalent leadership positions. The thing is, "equivalent" is doing a ton of heavy lifting there. If your title was "IT Manager" but you actually owned security program management and strategy, vendor risk, incident response leadership and crisis management, plus you had budget authority, you can probably make that case work. If your title was "Senior Security Engineer" but you were basically a project lead with no hiring input, no budget, and zero policy authority? That's a way tougher sell.
Now here's the big gotcha people constantly miss: your experience must show direct involvement in three or more of the five CCISO domains. Not "exposed to." Not "sat in meetings where it came up." Direct. Involvement. This is where you map your actual work to the CCISO exam objectives and show receipts.
Here's what that looks like in real life, the kind of evidence that usually passes a sniff test:
- Risk register ownership
- Governance committee minutes
- Audit responses and control exception workflows
- Program roadmaps
- Vendor security reviews, security metrics packs
- IR playbooks and post-incident reports
- Team leadership, budget line items
- Procurement decisions and strategic authority (not just executing someone else's plan)
Technical roles can count. Big condition, though. Analyst/engineer/administrator roles count only if they include significant management responsibility. Look, tons of companies blur lines, so you might've been an engineer who also ran a small team, owned the security budget for tooling, and wrote the security strategy for the next 12 months because nobody else would. That can qualify, but you need to document it like a manager, not like an engineer.
Part-time, contract, and consulting work may qualify too. I mean, EC-Council's focus is leadership scope, not whether you had a W-2. If you were a consultant acting as a virtual CISO, leading a security program, owning risk decisions, presenting to execs, covering multiple CCISO domains, that's real management experience. Same goes for military information security leadership experience, as long as it meets the management and domain requirements. Leadership is leadership, whether the org chart's civilian or military.
Some things don't count, and people get salty about this. Volunteer work and unpaid positions do not count toward experience requirements. And educational credentials do not substitute for the required work experience. Unlike some other certs, you don't "waive" years with a degree. Not gonna lie, that's frustrating if you're early-career. It's also consistent with what CCISO's trying to represent.
One more thing: experience must be verifiable. EC-Council can ask for employment records, references, or other professional documentation, and they reserve the right to audit experience claims. So keep artifacts. Keep role descriptions. Performance reviews mentioning security leadership. Keep the email where you were assigned budget responsibility. Boring admin stuff.
Do it anyway.
If you're applying, document specific projects like an exec would. Short bullets are fine, but they need substance. "Led ISO 27001 program, owned risk acceptance process, managed $450k security budget, built KRIs/KPIs for board reporting, ran incident tabletop and updated crisis comms plan." That kind of detail makes your experience legible.
Experience gained while holding other certifications like CISSP, CISM, or CISA can count, but only if the job itself meets CCISO criteria. Certs don't magically turn hands-on time into management time. They just help you describe it.
Side note: I once saw a guy try to submit his time as a solo pentester as "management experience" because he "managed client relationships." EC-Council laughed him out of the application portal. Don't be that guy.
Training vs exam-only eligibility (EC-Council pathways)
There are two pathways to earn the EC-Council CCISO exam 712-50 credential: training-then-exam, or exam-only based on experience.
The training pathway's the shortcut to eligibility. If you take the official EC-Council CCISO training (typically a 5-day course), you automatically get exam eligibility regardless of experience. That's the key line. This pathway's ideal if you're approaching the experience threshold, or you're moving from technical into leadership and want structure. Some people hate that it lets less-experienced folks sit the test, but the exam itself still filters people out.
At all.
Training completion doesn't guarantee exam success. Honestly, not even close.
Exam-only's the "prove you're already doing the job" route. If you meet all prerequisites, you submit your application and, once approved, you can schedule the exam. This is what lots of experienced CISOs choose because, honestly, paying for a week of training that rehashes things you've lived through feels like lighting money on fire.
Cost matters here. The training path usually costs significantly more because it bundles courseware, instructor time, and typically an exam voucher (pricing varies by provider and format). The exam-only route can be cheaper upfront, but you're responsible for building your own prep plan, finding a CCISO study guide, and getting realistic practice like a CCISO practice test. If you want a quick drill set, I've seen people pair their reading with a targeted pack like the 712-50 Practice Exam Questions Pack to find weak spots fast.
Training options come in a few flavors: online live, in-person, and self-paced through authorized training centers. Pick based on your learning style, not vibes. If you're transitioning from technical roles and you've never owned a security program, training's usually worth it because it forces you to think in governance, finance, and stakeholder language. Which is where technical folks often faceplant.
Voucher details matter too. The voucher included with training's often valid for about a year from course completion, and if you fail, you typically need to buy a retake voucher separately. Plan your timeline so you're not panic-studying at month 11.
Application/endorsement considerations (documentation and approval)
If you're going exam-only, you'll complete an online application detailing work experience and domain coverage. This isn't a one-paragraph "trust me bro" form. You'll provide job descriptions, dates of employment, and responsibilities that map cleanly to at least three domains. A resume or CV upload's usually required, and references may be contacted.
Processing time's often quoted around 5 to 10 business days, but it can stretch during peak periods. Incomplete applications get kicked back with guidance on what's missing.
Don't take it personally.
Just fix it.
Supervisor endorsement helps. A lot. Peer review or supervisor confirmation may be required to validate what you're claiming, and even when it's not strictly required, it can speed approval because it reduces ambiguity. If you're claiming budget responsibility, say who approved the budget with you. If you're claiming team leadership, mention headcount and what you owned: hiring, performance reviews, on-call rotations, security operations.
False info's a career self-own. Misleading application details can result in denial or even revocation later. EC-Council also reserves the right to audit, so keep your documentation organized. Offer letters, contracts, org charts. Project charters. Procurement approvals. Fragments help. Screenshots, PDFs, whatever you can legally keep.
If your application's denied, you can usually appeal with more supporting material. That's where a clearer mapping to the CCISO domains often fixes things. If you took training, you bypass the application entirely, which is another reason some borderline-eligible candidates pay for the course.
Quick practical tip: maintain career records as you go. I mean, nobody wants to do that. But when you're trying to prove executive-level work for a Certified Chief Information Security Officer credential, that habit saves you weeks of scrambling later.
And if you're building your prep plan while you wait on approval, do something concrete with it. Read the official objectives. Outline your domain gaps. Then pressure-test with scenario questions. A resource like the 712-50 Practice Exam Questions Pack can be handy for spotting whether you're thinking like a manager or still answering like an engineer. If it feels too easy, you're probably missing the governance angle. If it feels hard, good. That's where the growth is.
One last thing people always ask while they're checking eligibility: CCISO certification cost, CCISO passing score, and CCISO renewal requirements vary depending on vouchers, training bundle, and policy updates, so don't rely on a random forum post from 2021. Verify current numbers before you buy anything. Still, eligibility's the part you can control right now: document your leadership scope, map to domains, and make your application impossible to misunderstand.
That's the game.
CCISO Certification Cost (Full Breakdown)
Look, if you're eyeing the EC-Council Certified CISO (CCISO) certification, you're probably already deep into security leadership or trying to break into those executive-level roles. But let's talk money. This credential isn't exactly cheap. I mean, it's designed for CISOs and senior security leaders, so EC-Council prices it accordingly. Kind of makes sense when you think about who's actually sitting for this thing.
The 712-50 exam sits in that weird space where it's technical knowledge. You're being tested on governance, risk management, strategic planning, and how to talk to the C-suite about security budgets without making everyone's eyes glaze over. That executive focus? Comes with executive-level pricing.
Exam voucher price and what's included
The CCISO exam voucher costs somewhere between $999 and $1,199 USD when you buy it separately from EC-Council. Regional pricing exists, so you might see variations depending on where you're located. Not gonna lie, that's a significant chunk of change for a single exam attempt. Though I guess compared to an executive MBA program it's still reasonable?
What does that voucher actually get you? One exam attempt. That's it. You can take the test at a Pearson VUE testing center (the traditional route where you drive somewhere and sit in a beige room with a webcam pointed at you) or use the online proctored option if you prefer taking it from home or your office. The online option's become way more popular since 2020, though some people still swear by the testing center experience because fewer distractions.
Your voucher's typically valid for one year from the purchase date. Check the specific terms when you buy because EC-Council occasionally adjusts their policies. You don't want to accidentally let it expire if life gets crazy and you need to postpone your exam date. I've seen people lose vouchers because they thought they had more time. Frustrating and expensive mistake that'll make you want to kick yourself.
Here's what the voucher does NOT include: study materials, practice tests, official courseware, or any of the training resources. You're literally just buying the right to sit for the exam. If you want EC-Council's official training, that's a completely separate purchase, which we'll get into shortly.
The regional pricing thing's real. Someone in India might pay less than someone in the United States or Western Europe. EC-Council adjusts for purchasing power parity in some markets, so always check their website for your specific location's pricing before budgeting. Makes sense from a global perspective.
Official training costs (online/in-person) and optional add-ons
The official EC-Council CCISO training is where costs really escalate. Honestly, this is where your budget either survives or completely implodes depending on how you approach it and whether your employer's footing the bill.
We're talking anywhere from $3,000 to $8,000+ depending on format and provider. Big range, I know.
EC-Council's iClass (their online self-paced platform) typically runs around $3,000-$4,000. You get video lectures, official courseware, labs (though CCISO's way less hands-on than something like CEH), and access to their learning management system for a set period. It's convenient if you're busy and need to study on your own schedule, which most people targeting CCISO definitely are. I mean, you're probably already running a security team or managing multiple projects at the same time.
Live instructor-led training costs a lot more. Whether online or in-person doesn't matter much price-wise. In-person bootcamps can hit $6,000-$8,000 when you factor in the course fee, and that often includes the exam voucher bundled in. Some organizations send their security directors to these week-long intensive programs. If your employer's paying, the live training has value because you can ask questions specific to your organization's challenges. Plus you get to network with other security leaders who actually understand what you're dealing with daily. That part's harder to quantify but surprisingly useful when you're stuck on something six months later and can ping someone from your cohort.
Third-party training providers (authorized EC-Council partners) offer similar courses, sometimes at slightly lower prices. Quality varies wildly though. I've heard good things about certain providers and horror stories about others who basically just read the slides. The thing is, you won't know which you're getting until you're already committed.
Optional add-ons? Practice tests from EC-Council or third-party vendors run $100-$300. Study guides and books are another $50-$150. If you're self-studying without the official training, budget at least $500-$1,000 for quality prep materials unless you're cool with just the free resources floating around (which honestly aren't great for CCISO compared to more popular certs). This isn't like studying for CompTIA A+ where free materials are everywhere.
Retake fees and budget planning tips
Failed the exam? The retake fee's the same as the original exam voucher price. Another $999-$1,199. There's no discount for attempt number two. EC-Council doesn't have the "discounted retake" model that some other vendors offer, which honestly feels a bit punitive but whatever.
You need to wait a certain period before retaking (typically 7-14 days depending on their current policy), which gives you time to identify knowledge gaps but also extends your timeline if you're trying to get certified by a specific date for a job opportunity or promotion. Time pressure's real.
Budget planning tips from someone who's watched people work through this:
First, be realistic about whether you need the official training. If you've been a security director or senior manager for years and already understand governance frameworks, risk management methodologies, and security program operations, you might be able to self-study with books and practice tests. That saves you $3,000+ right there. No shame in self-study if you've got the background.
Second, check if your employer has a training budget or certification reimbursement program. Many organizations will pay for CCISO because it directly benefits them to have certified leadership. Let's be honest, if they're not investing in your professional development at this level, that's a red flag about the organization itself. Some will pay upfront, others reimburse after you pass.
Third, factor in the CCISO prerequisites and eligibility requirements. You need significant work experience (typically 5+ years in security with 3+ years in management), and if you don't meet those requirements, you might need to go through EC-Council's official training to become eligible. That changes your cost calculation completely because the training isn't optional anymore. It's required. The ECIH or ECSS certifications have different pathways if you're earlier in your career and want to build toward this.
Fourth, consider total cost of ownership including renewal. CCISO renewal happens every three years and costs around $500-$700, plus you need to earn continuing education credits. That's another $200-$300 per year when you factor in attending conferences, taking courses, or other CPE-eligible activities. The costs keep coming.
So realistically, if you're going the official training route, you're looking at:
Official training: $3,000-$8,000 Exam voucher (included or separate): $1,000-$1,200 Extra materials: $200-$500 First three years total: around $4,500-$10,000
Self-study route:
Exam voucher: $1,000-$1,200 Books and practice tests: $300-$600 First three years: around $2,000-$2,500
The CCISO passing score isn't publicly disclosed by EC-Council (they use scaled scoring), but most people estimate you need around 70-75% to pass. The exam difficulty's real. It's not a memorization test like some entry-level certs. You're analyzing scenarios, making executive decisions, and showing you understand how to build and manage enterprise security programs. Pattern recognition helps, but you need actual experience.
Is it worth the investment? Depends on your career path. If you're aiming for CISO roles or already in security leadership, the credential carries weight, especially in organizations that value certifications. Though I've met plenty of successful CISOs without it, so it's not like a magic bullet or anything. It's more focused on executive security leadership than CISSP or CISM, though those are often mentioned alongside CCISO in job descriptions.
The renewal requirements mean ongoing costs. But if you're active in the security field, you're probably already doing activities that count toward CPE credits anyway. Reading, attending conferences, taking additional training. Just document everything. Keep a spreadsheet or something.
If you're comparing EC-Council certifications, something like Certified Ethical Hacker is way cheaper but targets a completely different role. CCISO's specifically designed for the C-suite conversation, not penetration testing or technical security work. Totally different skill sets and career paths.
Bottom line: budget $1,000-$1,200 minimum if you're confident in self-study, $5,000-$10,000 if you want the full official training experience. Plan for retake costs just in case (most people pass on the first attempt if they prep properly, but executive-level exams are unpredictable). And don't forget renewal costs when calculating ROI over your career. This isn't a one-and-done investment.
Conclusion
So is the ECCouncil 712-50 CCISO certification actually worth your time?
Straight up? This one's weird. Different energy entirely. The EC-Council CCISO exam 712-50 isn't about memorizing port numbers or dissecting malware samples in a lab. None of that technical stuff you'd expect. It's executive-level territory, honestly, and if you're gunning for that CISO role or you're already in security leadership and need something that actually speaks the language of boards and C-suites, then yeah, the Certified Chief Information Security Officer credential makes sense for your career trajectory.
The investment isn't small though.
I mean, between the CCISO certification cost (exam fees, training materials, maybe a retake if things don't go your way the first time) and the hours you'll spend understanding information security governance and risk management at a strategic level, you're committing real resources here. But that's kinda the point? This isn't a cert you knock out in three weeks with brain dumps. The CCISO prerequisites alone ensure you've got legitimate experience, and the exam objectives push you to think like an actual executive, not just a technical expert who memorized frameworks.
The thing is, the stuff that trips people up isn't even the technical domains. It's security program management and strategy. The finance angles. Procurement decisions. Incident response leadership and crisis management when you're dealing with board members who want answers in business terms, not technical jargon. That's where a solid CCISO study guide and repeated exposure to scenario-based questions pays off big time, honestly more than most people realize going in.
My neighbor's kid asked me last week why security certs cost so much, and I didn't have a good answer beyond "because they can." Made me think about whether we're all just playing along with inflated pricing models, but that's probably a different conversation.
About that CCISO passing score: you'll need to clear the threshold, and the exam doesn't mess around with vague questions. Practice is non-negotiable. Not the kind where you skim questions once, but actual repeated testing under time pressure so you internalize how EC-Council frames governance scenarios (which, I'll be honest, caught me off guard initially). Right, the CCISO practice test route is how you figure out whether you're actually ready or just think you are because you read through the material twice and felt confident.
One more thing on CCISO renewal requirements: don't sleep on this part. The cert doesn't stay current automatically. You'll need to track CPEs and stay engaged with the community, which honestly keeps the credential from becoming one of those "got it and forgot it" situations that clutter your resume.
If you're serious about preparing properly and want questions that actually mirror what you'll face on test day, the 712-50 Practice Exam Questions Pack is worth checking out. It's structured around the real exam domains, gives you the repetition you need, and helps you spot weak areas before you're sitting in the testing center wondering why you didn't practice more scenario-based governance questions. Don't walk into this one unprepared.