312-85 Practice Exam - Certified Threat Intelligence Analyst (CTIA)
Reliable Study Materials & Testing Engine for 312-85 Exam Success!
Exam Code: 312-85
Exam Name: Certified Threat Intelligence Analyst (CTIA)
Certification Provider: ECCouncil
Corresponding Certifications: CTIA , ECCouncil Other Certification

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
312-85: Certified Threat Intelligence Analyst (CTIA) Study Material and Test Engine
Last Update Check: Mar 19, 2026
Latest 49 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena ECCouncil Certified Threat Intelligence Analyst (CTIA) (312-85) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
ECCouncil 312-85 Exam FAQs
Introduction of ECCouncil 312-85 Exam!
ECCouncil 312-85 is the Certified Ethical Hacker (CEH) exam. It is a comprehensive exam that tests a candidate's knowledge and skills in ethical hacking and countermeasures. The exam covers topics such as network scanning, system hacking, malware threats, cryptography, and more.
What is the Duration of ECCouncil 312-85 Exam?
The duration of the ECCouncil 312-85 exam is 4 hours.
What are the Number of Questions Asked in ECCouncil 312-85 Exam?
There are a total of 125 questions on the ECCouncil 312-85 exam.
What is the Passing Score for ECCouncil 312-85 Exam?
The passing score required for the ECCouncil 312-85 exam is 70%.
What is the Competency Level required for ECCouncil 312-85 Exam?
The ECCouncil 312-85 exam is designed to test the knowledge and skills of a Certified Ethical Hacker (CEH). To pass the exam, candidates must demonstrate a comprehensive understanding of the topics covered in the CEH curriculum, including network security, cryptography, and ethical hacking techniques. Candidates must also demonstrate the ability to apply these concepts to real-world scenarios. The exam is divided into five sections, each of which requires a different level of competency. The minimum competency level required to pass the exam is a CEH certification.
What is the Question Format of ECCouncil 312-85 Exam?
The ECCouncil 312-85 exam consists of multiple-choice questions.
How Can You Take ECCouncil 312-85 Exam?
The ECCouncil 312-85 exam can be taken online or in a testing center. The test can be taken online using the ECCouncil Exam Portal or through a secure remote proctoring solution. If you choose to take the exam in a testing center, you will need to register for the exam with the ECCouncil and then find a testing center that offers the exam.
What Language ECCouncil 312-85 Exam is Offered?
ECCouncil 312-85 exam is offered in English.
What is the Cost of ECCouncil 312-85 Exam?
The cost of the ECCouncil 312-85 exam is $250 USD.
What is the Target Audience of ECCouncil 312-85 Exam?
The target audience for the ECCouncil 312-85 Exam is IT professionals who have experience in systems security and auditing, as well as professionals who are looking to become certified in the Certified Chief Information Security Officer (CCISO) program.
What is the Average Salary of ECCouncil 312-85 Certified in the Market?
The average salary for a professional with EC-Council 312-85 certification is around $85,000 per year. However, salary can vary widely depending on the region and employer.
Who are the Testing Providers of ECCouncil 312-85 Exam?
ECCouncil provides the official exam testing for their 312-85 Certified Ethical Hacker (CEH) exam. You can register to take the exam at the ECCouncil website.
What is the Recommended Experience for ECCouncil 312-85 Exam?
The recommended experience for the ECCouncil 312-85 exam is three to four years of hands-on experience in the field of computer hacking and countermeasures. Candidates should have a good understanding of the principles and techniques of computer forensics, incident response, and security auditing. Experience with network and operating system security, as well as familiarity with programming languages and scripting, is also recommended.
What are the Prerequisites of ECCouncil 312-85 Exam?
The prerequisite for the ECCouncil 312-85 exam is to have at least two years of professional experience in the field of information security or hold a valid EC-Council certification. Additionally, applicants must agree to the EC-Council Code of Ethics and the CEH Candidate Agreement.
What is the Expected Retirement Date of ECCouncil 312-85 Exam?
The official website for ECCouncil 312-85 exam is https://www.eccouncil.org/programs/certified-ethical-hacker-ceh/. There is no information regarding the expected retirement date of the exam on this website.
What is the Difficulty Level of ECCouncil 312-85 Exam?
The difficulty level of the ECCouncil 312-85 exam is considered to be moderate. It is recommended that candidates prepare thoroughly and study all material related to the exam in order to ensure success.
What is the Roadmap / Track of ECCouncil 312-85 Exam?
The EC-Council 312-85 Exam is the certification track and roadmap for the Certified Ethical Hacker (CEH) v10 certification. This exam is designed to test an individual's knowledge and skills related to ethical hacking, computer forensics, and penetration testing. The 312-85 exam is a proctored, multiple-choice exam that consists of 125 questions and must be completed within four hours. Passing the exam will demonstrate a candidate's ability to identify vulnerabilities and threats in target systems, and to develop and implement appropriate countermeasures to protect them.
What are the Topics ECCouncil 312-85 Exam Covers?
The EC-Council 312-85 exam covers a range of topics related to Certified Network Defense Architect (CNDA). These topics include:
1. Network Security Fundamentals: This covers the basic concepts of network security, including security models, access control, authentication, cryptography, and risk management.
2. Network Attacks and Countermeasures: This covers the different types of network attacks, such as Denial of Service, Spoofing, and Man-in-the-Middle attacks, as well as countermeasures to protect against them.
3. Network Security Architecture: This covers the design and implementation of secure networks, including the use of firewalls, Intrusion Detection Systems, and Virtual Private Networks.
4. Network Security Policies: This covers the development of security policies and procedures to ensure the safety and integrity of a network.
5. Network Security Auditing: This covers the process of auditing networks to identify and address security vulnerabilities
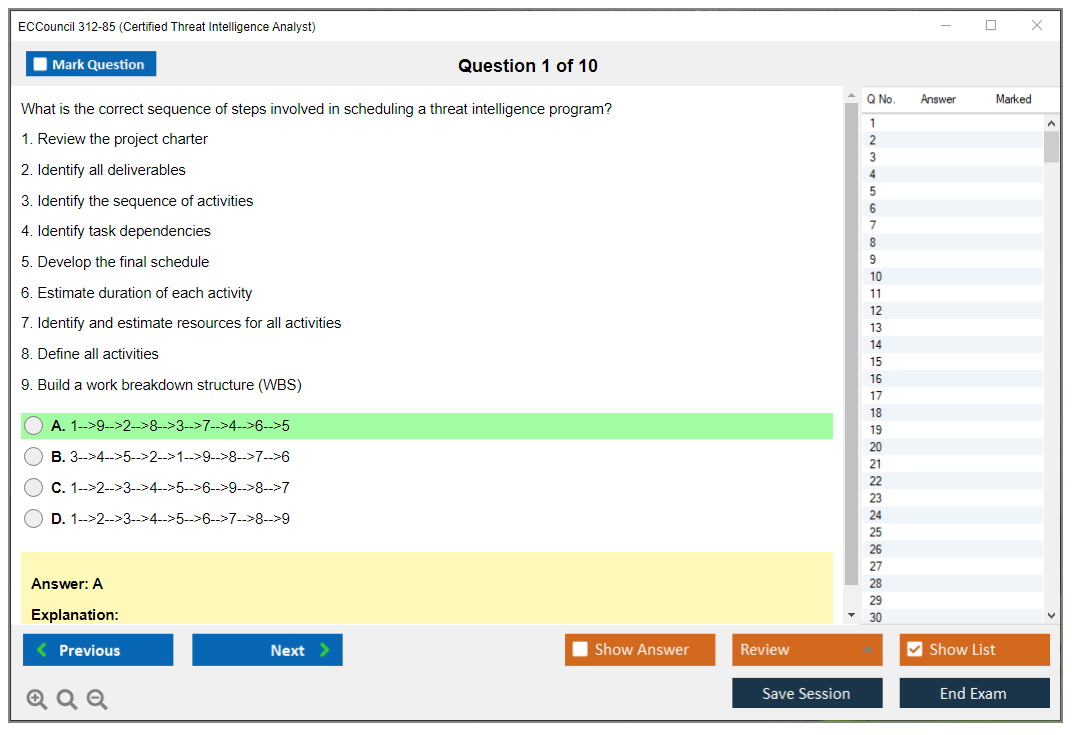
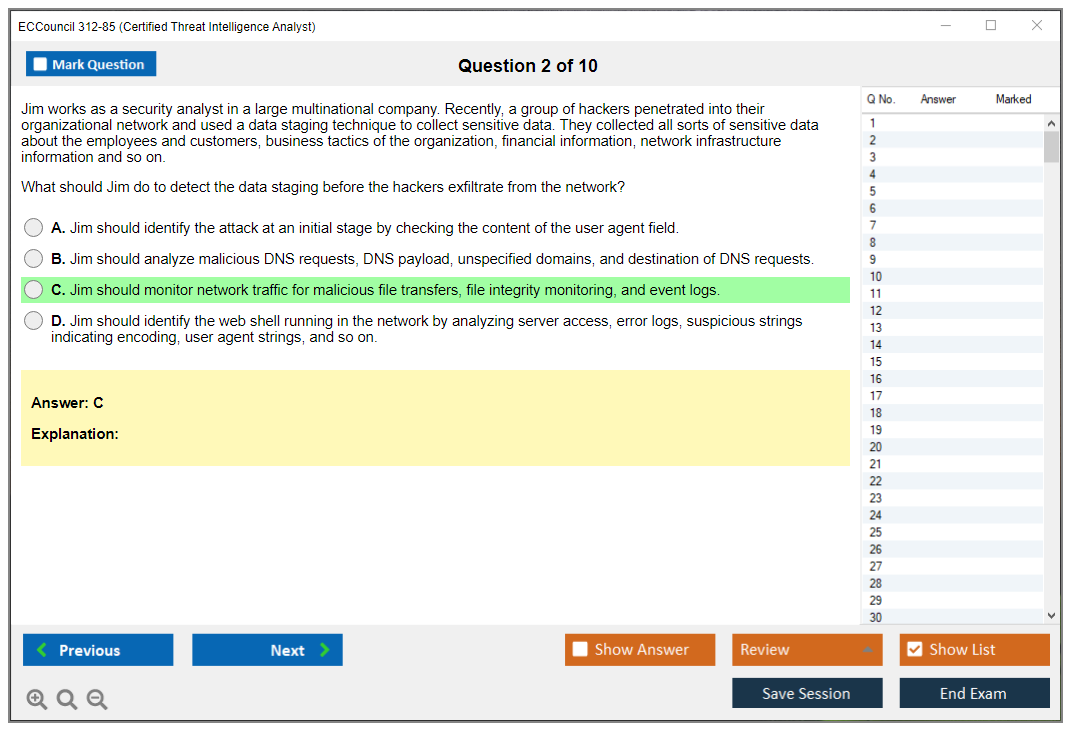
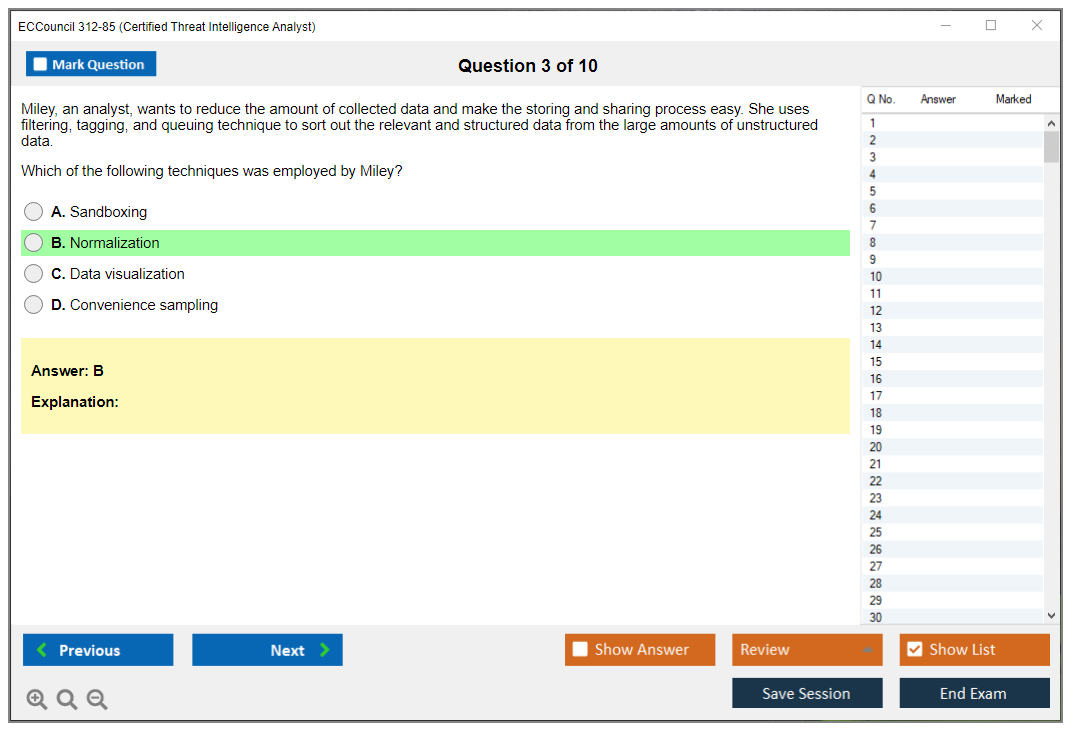
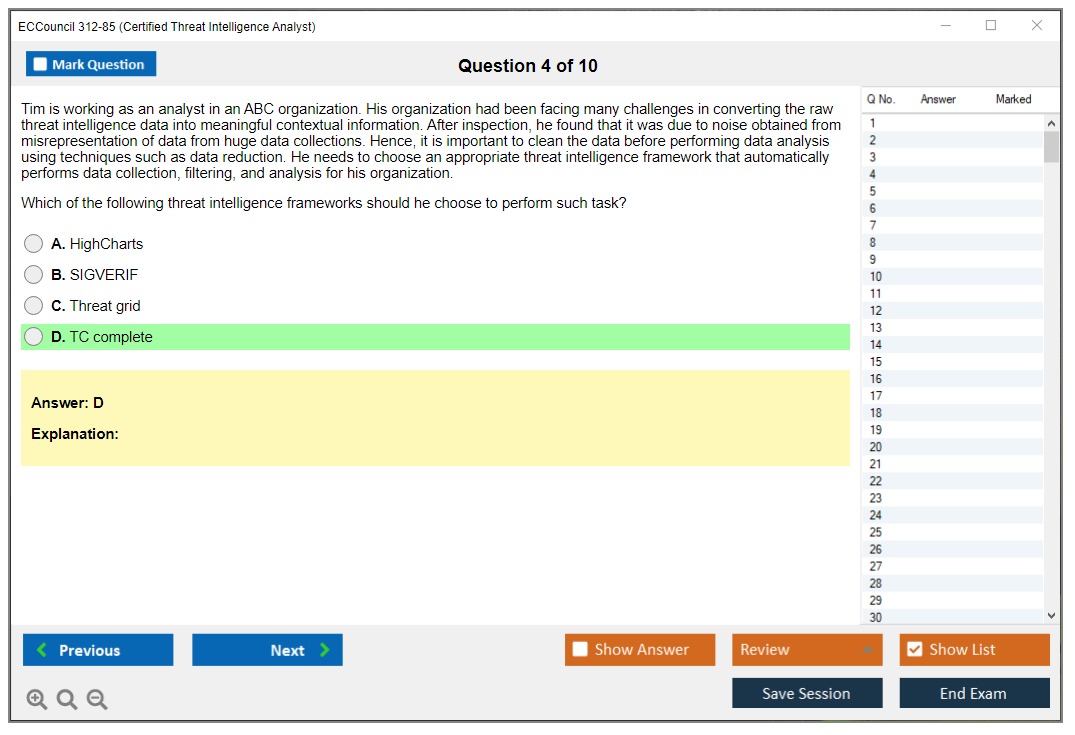
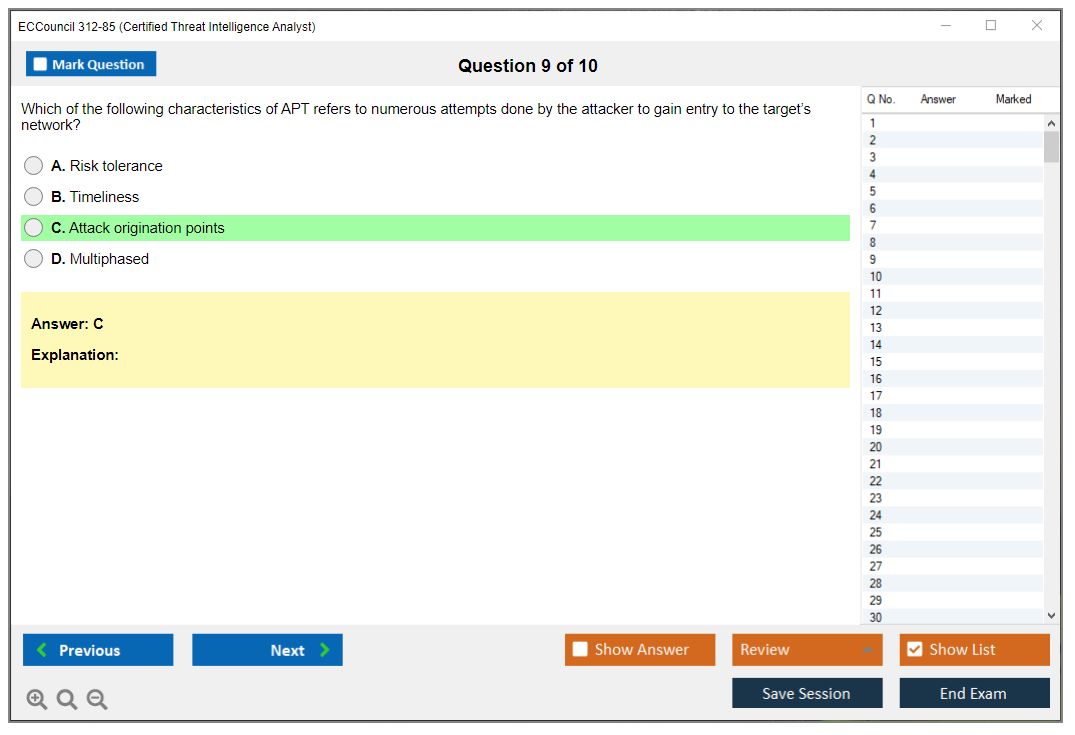
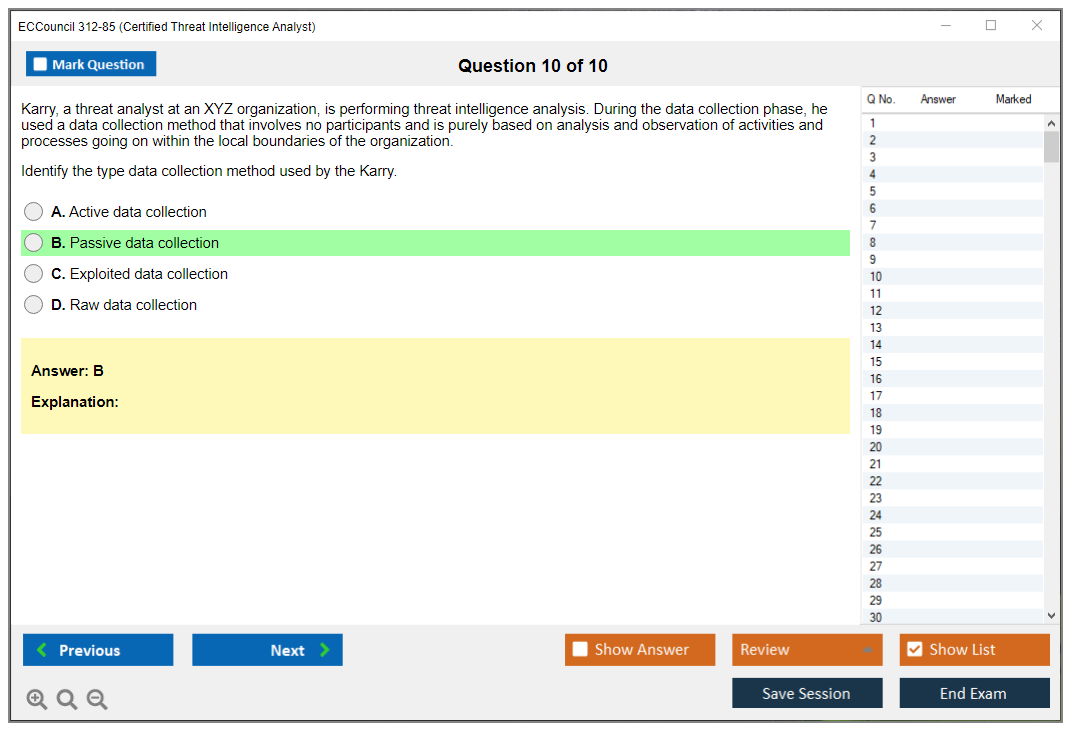
What are the Sample Questions of ECCouncil 312-85 Exam?
1. What is the purpose of the Network Access Control (NAC) framework?
2. What is the purpose of a honeypot in a security architecture?
3. What is the difference between a false positive and a false negative in intrusion detection systems?
4. What is the role of a penetration tester in a security audit?
5. What are the three primary components of a secure network architecture?
6. How does the use of encryption algorithms help protect sensitive data?
7. What is the purpose of a vulnerability assessment?
8. What is the difference between a vulnerability scan and a penetration test?
9. What are the benefits of using a firewall to protect a network?
10. What are the steps involved in the secure software development lifecycle?
ECCouncil 312-85 (Certified Threat Intelligence Analyst (CTIA)) EC-Council CTIA EC-Council CTIA What is the Certified Threat Intelligence Analyst (CTIA) certification Context matters more than raw alerts. If you're in a SOC or doing incident response, you already know this. The Certified Threat Intelligence Analyst (CTIA) certification from EC-Council is their premier credential for professionals who need to turn threat data into decisions that actually help organizations defend themselves. Not just collecting indicators of compromise and dumping them into a spreadsheet, because honestly, anyone can do that part. The CTIA validates your ability to collect, analyze, and disseminate threat intelligence across the entire lifecycle. Sounds fancy but really just means you understand how to go from raw data to strategic recommendations that executives and technical teams can both use. The cert focuses on strategic intelligence (long-term threat space analysis), operational intelligence... Read More
ECCouncil 312-85 (Certified Threat Intelligence Analyst (CTIA))
EC-Council CTIA
EC-Council CTIA
What is the Certified Threat Intelligence Analyst (CTIA) certification
Context matters more than raw alerts. If you're in a SOC or doing incident response, you already know this. The Certified Threat Intelligence Analyst (CTIA) certification from EC-Council is their premier credential for professionals who need to turn threat data into decisions that actually help organizations defend themselves. Not just collecting indicators of compromise and dumping them into a spreadsheet, because honestly, anyone can do that part.
The CTIA validates your ability to collect, analyze, and disseminate threat intelligence across the entire lifecycle. Sounds fancy but really just means you understand how to go from raw data to strategic recommendations that executives and technical teams can both use. The cert focuses on strategic intelligence (long-term threat space analysis), operational intelligence (understanding adversary campaigns and TTPs), and tactical intelligence (those IOCs and technical indicators your SIEM actually consumes).
This is designed for SOC analysts who want to specialize. Threat hunters building intelligence-driven methodologies. Incident responders who need to contextualize attacks, and security researchers who analyze emerging threats. What's cool is that the CTIA fits with NICE Framework roles like Cyber Defense Analyst and Threat/Warning Analyst, which matters if you're working in government or defense sectors or dealing with employers who map positions to that framework.
The industry recognition piece? Real. More employers are specifically requiring or preferring CTI credentials for mid-level and senior threat intelligence positions. Especially at MSSPs, financial services firms, healthcare organizations, and critical infrastructure providers. The cert distinguishes candidates who can translate raw threat feeds and OSINT into strategic security decisions rather than just forwarding alerts upstream without analysis.
EC-Council 312-85 CTIA exam structure and what it measures
The exam code is 312-85. Vendor is EC-Council (International Council of E-Commerce Consultants), and the official name is Certified Threat Intelligence Analyst (CTIA). Pretty straightforward naming there.
This exam measures your competency across threat intelligence fundamentals, collection methodologies, analysis techniques, and reporting formats that actually get read. Not just filed away in some forgotten SharePoint folder nobody checks. It assesses your knowledge of CTI frameworks like MITRE ATT&CK (which you absolutely need to know cold), the Diamond Model of Intrusion Analysis, and the Cyber Kill Chain. If you can't map adversary behavior to ATT&CK techniques, you're going to struggle with this cert.
The exam tests hands-on skills with OSINT collection, IOC enrichment (taking a single indicator and pulling context from multiple sources), basic malware analysis concepts, and working with threat intelligence platforms. It also evaluates your ability to produce intelligence products that different audiences can actually use. Reports, briefings, alerts. The thing is, writing for executives versus writing for detection engineers requires completely different approaches and vocabulary choices.
You'll see questions about threat actor profiling. Understanding adversary motivations and capabilities. How to make CTI actually work within SOC workflows, incident response procedures, and threat hunting operations.
Who should take the CTIA 312-85 exam
SOC analysts seeking to specialize? Definitely. You're tired of just triaging alerts and want to understand the "why" behind attacks? CTIA gives you that framework. Incident responders who need to contextualize attacks with CTI benefit hugely. Knowing whether you're dealing with ransomware-as-a-service or a targeted APT campaign changes your response priorities completely. The difference in how you allocate resources is night and day.
Security operations managers building or maturing threat intelligence programs need this knowledge to structure their teams and processes correctly. Threat hunters looking to formalize their intelligence-driven hunting methodology get a lot from the structured approach CTIA teaches. Hunting without intelligence is basically just guessing, hoping you stumble onto something suspicious.
Cybersecurity consultants advising clients? Valuable for credibility. Security engineers integrating threat feeds into SIEM, SOAR, and detection platforms need to understand what good intelligence looks like before they automate consumption of it. Government and defense sector analysts working in cyber defense roles will find this cert speaks their language and fits with position requirements.
If you're already holding the Certified Ethical Hacker Exam (CEHv12) or working as a Certified SOC Analyst (CSA), CTIA is a natural next step that adds defensive intelligence specialization to your offensive or detection skills.
Career benefits and salary impact of CTIA certification
Average salary boost sits around 10-20% for certified CTI analysts versus non-certified peers doing similar work, though that varies by market and organization size. The cert opens doors to dedicated Threat Intelligence Analyst roles, CTI Engineer positions, and Threat Research roles that often didn't exist or weren't available before.
It shows commitment to learning in a threat space that changes faster than most people can keep up with. Matters when hiring managers are choosing between candidates who look identical on paper until you spot that certification line. Your resume gets stronger for roles at MSSPs, financial services firms, healthcare organizations, and critical infrastructure providers. All sectors that take threat intelligence seriously because they're constantly targeted by sophisticated threat actors with actual budgets and patience.
The CTIA complements other EC-Council certs and builds out a more complete security skillset. If you've got CEH for offensive understanding, CHFI for forensics, or ECIH for incident handling, adding CTIA rounds out your defensive intelligence capabilities in a way that makes you significantly more valuable to employers building mature security programs instead of just checking compliance boxes.
I once worked with someone who had every possible cert except anything related to threat intelligence. Smart guy, could pentest circles around most people, but put him in front of a threat feed and ask him to prioritize what mattered for our environment? Lost. That's where credentials like CTIA actually prove their worth.
How CTIA fits into the EC-Council certification pathway
EC-Council structures their certs in a progression that actually makes sense, which is refreshing compared to some vendors. Entry-level starts with CEH (Certified Ethical Hacker) for foundational offensive security knowledge. Understanding how attackers think helps you analyze threats. Intermediate level includes CTIA for defensive intelligence specialization, which is where most SOC professionals want to go after getting their feet wet.
Advanced level has CCISO (Chief Information Security Officer) for leadership roles when you're ready to move into management. Lateral options include ECIH for incident handling specialization, LPT (Licensed Penetration Tester) for advanced offensive work, and CHFI for forensic investigation skills.
CTIA pairs really well with vendor-neutral certifications. CompTIA Security+, CySA+, and GIAC certifications like GCTI complement it nicely. I've seen professionals stack CTIA with SANS CTI courses or Recorded Future certifications to build threat intelligence expertise that employers actually want instead of just collecting alphabet soup credentials that don't translate to real capability.
CTIA exam cost and practical considerations
The EC-Council CTIA 312-85 exam cost typically runs around $650-$850 just for the exam voucher, though prices vary by region and whether you're buying through training bundles. Official EC-Council training adds another $2,000-$3,500 depending on format. iLearn self-paced versus instructor-led classroom options.
Retake fees hurt if you don't pass first attempt, so proper preparation matters financially. Some employers reimburse certification costs, especially if you're already working in a SOC or CTI role and the cert fits with position requirements. Definitely worth asking your manager before you drop your own cash.
The passing score for CTIA 312-85 isn't publicly disclosed by EC-Council, which is frustrating but typical for their exams. Most candidates report needing around 70-75% correct to pass based on their experience, but EC-Council uses scaled scoring that adjusts for question difficulty. Your mileage may vary depending on which question set you get.
Study materials and preparation strategy
Official EC-Council training provides courseware, labs, and exam prep, but you need hands-on experience beyond just their materials if you want to actually understand this stuff versus just memorizing answers. Study CTI frameworks and reference materials like the MITRE ATT&CK knowledge base, Diamond Model documentation, and Lockheed Martin's Kill Chain white papers alongside official content.
Hands-on practice matters. Work with OSINT collection tools (Maltego, Shodan, threat feeds), IOC enrichment platforms (VirusTotal, AlienVault OTX, Hybrid Analysis), and actual SIEM or threat intelligence platforms. Build your own mini CTI workflow. Collect indicators, enrich them, analyze patterns, write a brief report. That practical experience translates directly to exam scenarios in ways that reading slides never will.
If you're also studying for the Certified Network Defender (CND) or already passed the Certified Cybersecurity Technician (CCT), you'll find some foundational concepts overlap. But CTIA goes much deeper on intelligence-specific methodologies and frameworks that those other certs only touch on superficially.
CTIA 312-85 practice tests help identify weak areas. Use them strategically though. Take timed practice sets, review every question you miss, and understand why wrong answers are wrong. Not just memorizing the right answer. A sample weekly study plan might be 10-15 hours over 4-6 weeks if you're already working in security, longer if you're newer to threat intelligence concepts and frameworks.
CTIA certification renewal and maintaining credentials
CTIA certification renewal happens every three years through EC-Council's continuing education program. You need to earn 120 ECE credits during your three-year cycle and pay renewal fees (usually $80-$100 annually or $240 for the full three years upfront, which saves a bit if you're sure you'll stick with it).
You earn credits through training courses, webinars, conferences, publishing security content, or documenting work projects that advance your CTI skills. Which means if you're actually working in the field and attending occasional training, accumulating credits is pretty straightforward and doesn't require tons of extra effort beyond what you're already doing professionally.
What happens if your CTIA certification expires? You lose the credential and need to retest if you want it back. Expensive and annoying and honestly, just a waste of time when you could've just tracked your credits properly. Set calendar reminders for renewal deadlines and track your ECE credits throughout the cycle instead of scrambling at the end when you realize you're 40 credits short with two weeks to go.
CTIA 312-85 Exam Format and Key Details
EC-Council CTIA (312-85) exam overview
If you keep hearing people say "we need better intel" in a SOC, they're usually talking about cyber threat intelligence (CTI) that actually changes decisions, not a PDF nobody reads. The Certified Threat Intelligence Analyst (CTIA) certification is EC-Council's shot at validating that you can do the workflow end to end, from requirements and collection to IOC enrichment and analysis, and then writing something a human can act on.
This exam is more practical than people expect.
You're not coding. You are thinking. A lot.
CTIA makes the most sense for SOC analysts, junior threat intel folks, IR people who keep getting pulled into attribution discussions, and threat hunters who want to get better at turning raw sightings into intelligence reporting. If you're brand new, you can still study for it, but you'll feel the gap when questions assume you've seen a messy alert queue, a rushed incident call, or a stakeholder asking "so what do we do Monday morning?" I once watched a CISSP try this exam cold and the reporting questions absolutely wrecked him because he kept picking the technically complete answer instead of the one a VP could use.
CTIA 312-85 exam format and key details
This is the part everyone searches for, and the part that determines how you prep. The EC-Council 312-85 CTIA exam is pretty straightforward on paper, but the scenario wording can make it feel longer than it is if you don't manage time.
Exam code, name, and vendor (EC-Council)
Official exam code is 312-85. The full name is EC-Council Certified Threat Intelligence Analyst (CTIA), and it's administered by EC-Council through Pearson VUE test centers and the ECC EXAM portal (depending on what option you pick when scheduling).
It's available worldwide. Test center or online proctoring. That flexibility is nice, but online proctoring can be picky, so don't treat it like a casual "take it from the couch" situation. The primary language is English, and EC-Council is the source of truth for extra language availability, which changes over time and sometimes depends on region and delivery method.
One sentence opinion. Pearson VUE is usually smoother.
Question types and time limit (what to expect on test day)
You get 50 multiple-choice questions. Two hours. That's it.
Formats are mostly single-answer multiple choice plus scenario-based questions, where you're given a situation and you pick the best next step, the best explanation, or the best output. There are no performance-based tasks like some CompTIA exams, so you're not dragging and dropping logs into buckets or "configure this thing" inside a simulated environment.
Still, don't get complacent, because the exam leans on applied judgment. The scenarios often test whether you actually understand CTI workflows, the threat intelligence lifecycle, and where things like MITRE ATT&CK mapping or IOC enrichment and analysis fit when you're under time pressure and incomplete information. I mean, a lot of questions hit three layers at once: recall (do you know the term), analysis (can you interpret what's happening), and decision-making (what should a CTIA do next).
Two hours for 50 questions works out to about 2.4 minutes per question on average. My pacing advice is boring but works: do a first pass in 60 to 75 minutes, answer the easy and medium ones, and flag the ones that need careful rereads. Then use the remaining time for the second pass, because that's where you catch misreads like "most appropriate" vs "first step" vs "best source."
Answer everything. No penalty for guessing. Don't leave blanks.
Passing score for CTIA 312-85
The CTIA 312-85 passing score is 70%, which is 35 out of 50 correct.
Scoring isn't adaptive and each question is weighted the same, so you don't need to play mind games about "hard questions are worth more." You either picked the best answer or you didn't. Results are typically available immediately after completion as a pass/fail notification, and you'll get a score report with a domain-level performance breakdown so you can see where you were strong and where you got cooked.
No partial credit. One best answer. Move on quickly.
CTIA exam cost (exam voucher, training bundles, retake considerations)
Money talk. It matters.
The voucher-only price for the exam is commonly listed around $550 USD (as of 2026, and yes, prices change). The EC-Council CTIA 312-85 cost gets more painful if you want official training: an iLearn bundle with exam is often $1,399 to $1,799, and instructor-led training plus exam is usually $2,500 to $3,500 depending on location and partner.
Retakes exist and they're typically discounted, often in the $350 to $400 range for a retake voucher. Group or corporate pricing can be cheaper through partners if your company's buying multiple seats. Then you've got the "death by a thousand add-ons" category: optional CTIA 312-85 practice tests ($99 to $149), study guides, and sometimes paid lab access if you want a structured sandbox for OSINT, enrichment, or malware analysis basics.
One blunt take. Budget for a retake. Even if you pass.
CTIA 312-85 exam objectives (domains)
EC-Council updates objective wording occasionally, so always cross-check the latest CTIA exam objectives 312-85 on the official site before you lock your study plan. But the domains tend to cluster around the same skill blocks.
Threat intelligence fundamentals and the threat intelligence lifecycle show up everywhere, and the exam expects you to know what good requirements look like, how collection differs from processing, and why analysis is more than "paste indicators into a spreadsheet." Requirements, collection, processing, analysis. These usually show up as scenario choices like which source to use, what to enrich, what to prioritize, and how to validate reliability.
Intelligence production matters more than people think. Writing, briefing, dissemination. If you can't talk clearly to a SOC lead or an executive, the best intel in the world is just noise, and CTIA questions love testing whether you understand audience, confidence statements, and what belongs in an intelligence report versus an internal analyst note.
Tools and frameworks also show up, particularly cyber threat intelligence (CTI) tools, standards like STIX/TAXII, and MITRE ATT&CK mapping when you're trying to connect observed behavior to tactics and techniques in a way defenders can use. Operationalizing CTI is the "so what" domain, where intel feeds SOC detections, IR prioritization, threat hunting and intelligence reporting, and sometimes detection engineering decisions.
CTIA prerequisites and recommended experience
People ask about CTIA certification prerequisites a lot. EC-Council doesn't position CTIA like an entry-level cert, but it's also not a hyper-advanced research credential. Recommended background is usually some combination of SOC work, basic incident response exposure, comfort with networking and logs, plus enough OSINT literacy to evaluate sources without getting fooled by junk.
You can study your way through gaps, but if you've never done triage, never touched an intel feed, or never had to explain why an IOC is low-confidence, you'll spend extra time learning the "why" behind the process instead of memorizing terms.
CTIA 312-85 difficulty: how hard is the exam?
How hard is it? Depends who you are.
If you're already doing CTI, it's fair. If you're a pure pentester, you might find the reporting and lifecycle questions annoying because they're not about exploitation, they're about decisions and talking to humans. If you're a SOC analyst who lives in alerts but never writes anything longer than a ticket comment, the production side can feel weirdly hard.
The common pain points are analysis choices, picking the best next step in messy scenarios, and knowing when to use frameworks versus when to focus on stakeholder requirements. Also, the exam can punish overthinking, which is hilarious because threat intel people overthink for sport.
Best CTIA 312-85 study materials
For CTIA 312-85 study materials, the official EC-Council iLearn or ILT content is the cleanest match to the exam style. It's expensive, but it tracks the objective language closely, and that matters when questions are picky.
Alongside official content, I'd spend time with MITRE ATT&CK documentation, basic STIX/TAXII primers, and real-world writeups from reputable incident response teams so you get used to how intelligence reporting is structured and how confidence and sourcing are talked about. Hands-on practice helps too, even lightweight stuff: take a public report, extract a few IOCs, do enrichment, map behaviors to ATT&CK, and write a one-page summary that includes what defenders should do next.
Notes help. Flashcards help. Doing the workflow helps more.
CTIA 312-85 practice tests and exam prep strategy
Reputable CTIA 312-85 practice tests are useful for pacing and for spotting weak domains, but don't treat them like the exam's a trivia contest. Use timed sets, review every miss, and write down why the correct answer's correct, because CTIA questions often hinge on process order and audience fit.
A simple study pattern works: two to six weeks, depending on your background. Weeknights for reading and notes, weekends for scenario drills and writing short intel summaries. If you can explain, in plain language, how a requirement becomes a collection plan, becomes analysis, becomes a report that drives action, you're in good shape.
Exam registration process and scheduling
Registration is pretty procedural.
Step 1 is creating an EC-Council account at aspen.eccouncil.org. Step 2 is buying the voucher or bundle from the EC-Council store. Step 3 is waiting for the voucher code, usually emailed within 24 to 48 hours. Step 4 is scheduling through Pearson VUE or the ECC EXAM portal, then Step 5 is picking a test center or online proctoring.
Book early if you care about a specific slot. Two to four weeks ahead is safe. Rescheduling's usually allowed up to 24 to 48 hours before the exam, but fees can apply, and policies change, so read the current terms when you schedule.
What to expect on test day
Test center day is simple: arrive 15 to 30 minutes early, bring a government-issued photo ID like a passport or driver's license, and expect your stuff to go in a locker. No phone. No watch. No notes. They'll give you scratch paper or a whiteboard and something to write with.
Online proctoring's stricter: webcam, microphone, ID verification, and a room scan. Clear your desk. Kill extra monitors. Don't assume your Wi-Fi's fine, test it. There's usually a short tutorial around five minutes on the exam interface and it typically isn't counted in your exam time.
Results show immediately as pass/fail. The official certificate's usually emailed within 5 to 7 business days.
CTIA certification renewal and continuing education
People forget this part until year two. CTIA certification renewal requirements are handled through EC-Council's continuing education system, often based on ECE credits plus fees within the renewal cycle. The exact counts and windows can change, so check your Aspen portal for what applies to your cert version.
Credits can come from training, webinars, conferences, and sometimes work projects if they meet the rules. If you let it expire, you're usually dealing with reinstatement policies or retesting, and that's a dumb way to spend money.
CTIA 312-85 FAQ
How much does the EC-Council CTIA (312-85) exam cost? Voucher-only's commonly around $550, training bundles push it higher, and retakes cost extra.
What's the passing score for the CTIA 312-85 exam? 70%, or 35 out of 50.
How hard's the CTIA exam compared to other EC-Council certifications? Easier than deep technical exploit-focused exams, harder than you'd think if you hate writing and process questions, because it tests judgment.
What're the CTIA 312-85 exam objectives and domains? Expect lifecycle, requirements through analysis, production/reporting, tools and standards like ATT&CK and STIX/TAXII, and operationalizing intel into SOC and hunting.
How do I renew the CTIA certification and maintain it? Track ECE credits and fees in Aspen, log activities as you go, and don't wait until the deadline week.
CTIA 312-85 Exam Objectives and Domains
Overview of CTIA exam domains and weighting
The EC-Council 312-85 exam tests you across six distinct domains. The weighting matters way more than most realize. You're not getting an even split here. Data Analysis grabs the biggest chunk at 20 to 25%, which makes sense because that's where the actual intelligence work happens, the real meat of what separates amateurs from professionals who can actually connect dots under pressure. Intelligence Reporting and Dissemination follows close behind at 15 to 20%, then you've got Cyber Threats and Kill Chain Methodology also at 15 to 20%. Data Collection and Processing sits at 15 to 20% too.
The smaller domains? Introduction to Threat Intelligence (10 to 15%) and Requirements, Planning, Direction, and Review (10 to 15%). EC-Council clearly wants you spending most of your brain power on analysis and reporting. That's where CTI professionals actually earn their paycheck. Coming from a SOC background like many 312-39 (Certified SOC Analyst) holders, you'll recognize some concepts but the analytical depth here is different. The weighting tells you exactly where to focus your study time, though I've seen people waste months on the intro stuff.
Domain 1: Introduction to Threat Intelligence fundamentals
This domain covers the conceptual foundation. Threat intelligence isn't the same as threat data or threat information. Data is raw, information adds context, intelligence drives decisions. That distinction trips up experienced security folks more than you'd expect. The exam wants you to distinguish between strategic intelligence (executive risk forecasts), operational intelligence (campaign tracking and adversary behavior), tactical intelligence (TTPs and attack patterns), and technical intelligence (IOCs and malware signatures).
The threat intelligence lifecycle shows up repeatedly. You've got six phases: direction (defining requirements), collection (gathering data), processing (normalizing and enriching), analysis (finding patterns), dissemination (sharing finished intelligence), and feedback (measuring effectiveness). Each phase feeds the next. Understanding this cycle matters for probably half the exam questions in this domain.
Intelligence-driven security is about being proactive instead of reactive. Traditional security waits for alerts, but CTI helps you hunt threats before they trigger detections. It's a mindset shift that takes time to internalize. Sharing models include ISACs (Information Sharing and Analysis Centers), ISAOs (Information Sharing and Analysis Organizations), commercial feeds from vendors like Recorded Future or Crowdstrike, and open-source communities. Legal considerations come up too: privacy laws, attribution challenges, responsible disclosure when you find vulnerabilities.
Building a threat intelligence program means identifying stakeholders (CISO, SOC manager, IR team, executives), defining requirements based on business risk, and establishing success metrics. You can't just spin up a TIP and call it a day. You need organizational buy-in and continuous stakeholder engagement or your program dies within six months. The exam tests whether you understand the organizational aspects, not just the technical tools. I spent a year watching a well-funded program implode because they skipped stakeholder management, figured they could retrofit it later. Didn't work.
Domain 2: Cyber Threats and Kill Chain Methodology
Threat actors break down into types: nation-state APTs with massive resources, cybercriminals chasing financial gain, hacktivists pushing ideological agendas, insider threats with legitimate access, and terrorists aiming for disruption. Each has different motivations (financial, espionage, disruption, ideology, revenge) and different TTPs that create distinct behavioral signatures you'll learn to recognize over time.
The Cyber Kill Chain from Lockheed Martin walks through seven stages from reconnaissance through actions on objectives. You need to know this cold because exam questions will describe scenarios and ask which stage an adversary's in. Sometimes they'll combine it with ATT&CK mapping to make it trickier. MITRE ATT&CK is even more detailed, mapping specific tactics and techniques that adversaries use across the attack lifecycle. If you've worked with 212-89 (EC Council Certified Incident Handler) material, you've seen ATT&CK, but CTIA goes deeper into using it for threat profiling.
Really key here.
The Diamond Model connects four elements: adversary, capability, infrastructure, and victim. Understanding how these elements relate helps you pivot during investigations. Creates that "aha" moment when seemingly unrelated incidents suddenly connect through shared infrastructure. Attack vectors include phishing (still the most common), malware delivery, ransomware deployment, supply chain compromise, and zero-day exploitation. The exam loves scenario questions where you identify the vector and map it to a kill chain stage.
Domain 3: Requirements, Planning, Direction, and Review
Intelligence Requirements (IRs) and Priority Intelligence Requirements (PIRs) drive everything. You can't collect and analyze everything, so you focus on what matters to your organization. Sounds obvious but I've seen mature programs collapse under data overload. Stakeholder identification means understanding who needs intelligence and what decisions they're making. Your CISO needs strategic risk assessments, your SOC manager needs tactical IOCs, your IR team needs operational campaign analysis.
Aligning CTI with business objectives matters. A financial services company cares about banking trojans and fraud, while a defense contractor worries about nation-state espionage. The collection management framework handles tasking (assigning collection priorities), coordination (managing multiple sources), and evaluation (assessing source reliability).
The intelligence planning cycle sets objectives, allocates resources, and establishes timelines that actually work in the real world, not just on paper. Feedback loops measure whether your intelligence actually helped. Did it lead to better detections, faster response, reduced dwell time? Documenting requirements through RFIs (Requests for Information) and tracking intelligence gaps ensures continuous improvement. This domain's smaller but the concepts show up integrated into other domains too.
Domain 4: Data Collection and Processing
OSINT dominates most CTI programs. You're mining search engines, social media, paste sites like Pastebin, dark web forums, and public repositories where threat actors leak credentials and discuss vulnerabilities in surprisingly candid detail. HUMINT involves industry contacts, threat actor forums (where you're lurking not participating), and occasionally informants. Technical sources include network traffic captures, log data, endpoint telemetry, and honeypots that attract attackers.
Commercial threat feeds cost money. Significant money. But they provide curated intelligence with confidence ratings that save analysis time. ISACs offer sector-specific sharing for finance, healthcare, energy, and other industries. Data normalization takes disparate formats and standardizes them. Enrichment adds context, taking an IP address and adding geolocation, ASN, reputation scores, related domains.
IOC collection gathers IPs, domains, file hashes (MD5, SHA1, SHA256), URLs, registry keys, and other artifacts. Processing techniques include deduplication (removing duplicates), validation (checking if IOCs are still active), correlation (linking related indicators), and tagging (categorizing by campaign or threat actor).
STIX (Structured Threat Information Expression) and TAXII (Trusted Automated Exchange of Indicator Information) are standards for sharing CTI in machine-readable formats. Threat intelligence platforms like MISP, ThreatConnect, Anomali, and ThreatQuotient automate much of this. If you're studying for 312-85 (Certified Threat Intelligence Analyst), understanding TIP workflows matters because several exam questions will present scenarios about data ingestion and processing that test whether you understand automation versus manual analysis tradeoffs.
Domain 5: Data Analysis (largest exam focus)
This is where EC-Council really tests you. Analytical models include hypothesis testing and structured analytic techniques that reduce cognitive bias. The bias stuff feels touchy-feely until you've made a wrong attribution call that sent your team hunting ghosts for three weeks. Indicator analysis evaluates reliability (is the source trustworthy?), relevance (does this apply to our environment?), and fidelity (is this a true positive or false positive?).
IOC enrichment uses tools like VirusTotal for malware scanning, passive DNS for domain history, WHOIS for registration data, GeoIP for location, and malware sandboxes like Cuckoo or Joe Sandbox for behavioral analysis. Malware analysis basics cover static analysis (examining code without running it) versus dynamic analysis (executing in a sandbox to observe behavior).
Attribution's notoriously difficult. False flags, shared tools, proxy infrastructure, and VPN usage make it hard to definitively identify adversaries. Nation-states especially love planting false breadcrumbs. Adversary infrastructure analysis examines C2 servers, phishing infrastructure, domain registration patterns, and hosting providers. Campaign tracking links disparate incidents to a single threat actor or operation by identifying shared TTPs, infrastructure, or tooling.
Threat modeling identifies your critical assets, potential threats, existing vulnerabilities, and appropriate mitigations. MITRE ATT&CK mapping takes evidence from an incident and identifies which tactics and techniques the adversary used. Confidence levels matter. Using estimative language like "likely," "probable," or "highly confident" with probability scales prevents overconfidence.
Cognitive biases screw up analysis. Confirmation bias makes you see what you expect, mirror imaging assumes adversaries think like you, and groupthink suppresses dissenting opinions that might actually save your analysis. Structured Analytic Techniques like Analysis of Competing Hypotheses (ACH) and Key Assumptions Check force you to consider alternatives. This domain's dense and accounts for up to 25% of exam questions, so if you're using 312-85 practice exam questions to prep, focus heavily here. Disproportionately heavy.
Domain 6: Intelligence Reporting and Dissemination
Intelligence products vary by audience and purpose. Tactical reports include IOC lists, YARA rules for malware detection, and Sigma rules for SIEM correlation. These enable immediate defensive action. Operational reports provide campaign analysis, adversary profiles, and infrastructure maps for threat hunters and IR teams. Strategic reports offer threat space assessments, risk forecasts, and executive summaries for leadership who make budget and priority decisions.
Writing for different audiences is a critical skill. SOC analysts want technical details and actionable indicators, executives want business impact and risk quantification without jargon that makes their eyes glaze over. Effective intelligence writing requires clarity (no ambiguity), conciseness (respect their time), objectivity (facts not opinions), and actionability (what should they do with this?).
Dissemination methods include email reports, threat intelligence portals, SIEM integration for automated alerting, SOAR playbooks for orchestrated response, and threat feeds for continuous ingestion. The Traffic Light Protocol (TLP) controls information sharing: TLP:WHITE is public, GREEN is community-only, AMBER is limited distribution, RED is eyes-only. Violating TLP destroys trust. Completely destroys it. You'll get blacklisted from sharing communities permanently.
Feedback and evaluation measure intelligence impact. Did your IOC list lead to new detections? Did your campaign report change defensive priorities? Did your strategic assessment influence budget allocation? Continuous improvement means refining collection and analysis based on stakeholder feedback, similar to how folks pursuing 712-50 (EC-Council Certified CISO) think about program management.
The 312-85 exam heavily tests reporting scenarios where you choose the appropriate product type, audience, and dissemination method. You'll see questions about TLP usage and writing style that trip people up if they only studied technical collection and analysis. This domain separates people who can do CTI from people who understand the full intelligence cycle. That's probably intentional on EC-Council's part.
CTIA Certification Prerequisites and Recommended Experience
EC-Council CTIA (312-85) exam overview
The EC-Council 312-85 CTIA exam targets people wanting to do cyber threat intelligence work that actually ties into operations. Not just skimming reports. Not just dumping IOCs into tickets. Real collection, analysis, and reporting that a SOC can really act on.
CTI's a mindset. Also a workflow. And, look, mostly a writing job if we're being honest.
What is the Certified Threat Intelligence Analyst (CTIA)?
The Certified Threat Intelligence Analyst (CTIA) certification is EC-Council's CTI-focused credential built around the threat intelligence lifecycle, practical OSINT, and packaging intelligence so defenders can actually use it. You're expected to understand how intel transforms from "random indicator on Twitter" to "this matters to our org, maps to ATT&CK, and here's what we should monitor."
It's not a malware reversing cert. It's more about analysis discipline, collection tradecraft, and producing intelligence products that make sense to humans who're under time pressure.
Who should take the 312-85 CTIA exam?
SOC analysts who constantly get asked "is this real?" and want better answers. IR folks needing stronger attribution-lite context plus better IOC enrichment and analysis. Threat hunters wanting to formalize how they build hypotheses and turn findings into intelligence reporting.
Career changers can tackle it too. Expect extra work though. No shortcuts exist here.
CTIA 312-85 exam format and key details
Exam code, name, and vendor (EC-Council)
Exam code's 312-85, name's CTIA, vendor's EC-Council. You'll see it called the EC-Council 312-85 CTIA exam all over training portals and voucher pages, so don't overthink this part.
Question types and time limit (what to expect on test day)
It's a multiple-choice style exam, and the vibe's "scenario plus best answer," not "what port is DNS." You'll encounter questions testing whether you understand prioritization, what to collect next, how to handle source reliability, and how to turn findings into something operational like detections or hunting queries.
Some questions feel wordy. Others feel obvious. A few feel like two right answers exist, which is maddening until you learn to spot what they're really asking.
Passing score for CTIA 312-85
People constantly ask about CTIA 312-85 passing score, and the annoying truth? EC-Council exams often use a sliding scale that varies by form. So you might see ranges discussed rather than one fixed number. My take: prep as if you need a strong margin, because trying to "aim for the minimum" is how you wind up paying for a retake.
CTIA exam cost (exam voucher, training bundles, retake considerations)
If you're Googling EC-Council CTIA 312-85 cost, expect it'll depend on whether you buy an exam voucher alone, bundle it with official training, or get a discount through an employer or academic program. Retakes are where budgets get absolutely wrecked, so plan for practice and review up front instead of hoping you can brute-force your way through.
If you're the self-study type, a structured question pack can help you find weak spots fast. I've seen folks pair their notes with 312-85 Practice Exam Questions Pack and use it like a diagnostic, not like some magic answer key.
CTIA 312-85 exam objectives (domains)
EC-Council publishes CTIA exam objectives 312-85, and you should read them like a checklist for your brain. If an objective says "produce intelligence," you should be able to explain what goes in the product, who it's for, and how it gets disseminated and tracked.
Threat intelligence fundamentals and lifecycle
You need the threat intelligence lifecycle down cold. Requirements. Collection. Processing. Analysis. Production. Dissemination. Feedback. That loop shows up everywhere, and if you can't map a scenario to the lifecycle stage, you'll feel completely lost.
This is where opinions matter. The best analysts I've worked with treat requirements like a contract with the customer, because otherwise you collect everything, drown, and ship a report nobody wanted. I saw a team once spend six weeks building a competitor analysis brief when the CISO just needed to know if their VPN was getting hammered. Requirements matter.
Requirements, collection, processing, and analysis
Collection sources can be OSINT, internal telemetry, vendor feeds, ISACs, sandboxes, and good old log data. Processing's the unsexy part where you normalize, de-dup, and enrich. Analysis is where you make calls, connect dots, and assess confidence.
IOC enrichment and analysis is huge here. If you can take a hash or domain, pivot it through VirusTotal, passive DNS, and sandbox results, then summarize what matters and what doesn't, you're thinking like the exam wants.
Intelligence production (writing, briefing, and dissemination)
Writing's the skill nobody trains and everybody needs. You'll be expected to understand types of intel products, how to write clearly, how to label confidence, and how to share safely using TLP.
Short sentences win. Bullets too. Clarity above all.
CTI tools, frameworks, and standards (e.g., MITRE ATT&CK, STIX/TAXII)
You should be comfortable with MITRE ATT&CK mapping, the Cyber Kill Chain, and the Diamond Model. Not just definitions, but how you'd use them to structure analysis. And yeah, know what STIX/TAXII are for: describing and sharing threat intel in structured formats and moving it between systems.
Also, Traffic Light Protocol. People mess this up constantly. If you can't explain what TLP:AMBER means in practice, you're not ready yet.
Operationalizing CTI (SOC, IR, threat hunting, detection engineering)
This is the part I like. CTI that doesn't change a detection, a hunt, or a control is basically a blog post. Expect the exam to test whether you can connect intelligence to SOC workflows, incident response decisions, and hunting.
Threat hunting and intelligence reporting show up together for a reason: hunting finds patterns, intel explains them, and the output should feed detections and playbooks.
CTIA certification prerequisites and recommended experience
Official prerequisites (if any) vs recommended background
Here's the clean answer on CTIA certification prerequisites: there aren't any mandatory prerequisites. The exam's open to all candidates. No required training class. No approval process you've gotta pass.
That said, EC-Council recommends 1 to 2 years of experience in information security or a related field. Familiarity with security operations, incident response, or threat analysis is beneficial. And there's no requirement to hold other EC-Council certs like CEH before CTIA, which is refreshing because some cert paths get weirdly gatekeepy.
Skills checklist before you start (networking, SOC, IR, OSINT)
If you're coming in cold, this is what I'd want you to be comfortable with before you grind CTIA 312-85 study materials.
Networking fundamentals matter. TCP/IP basics, DNS behavior, HTTP/HTTPS flows, and common protocols. You don't need to be a packet wizard, but you should understand what "normal" looks like so "weird" stands out.
Security concepts should be familiar. Firewalls, IDS/IPS, endpoint protection, and especially SIEM basics. If you've never used a SIEM, at least understand what correlation rules are trying to do and why false positives happen.
Basic scripting helps a lot. Python or PowerShell for quick data collection, parsing, and enrichment. Not full apps. Simple stuff. Pulling data from an API. Cleaning a CSV. Extracting domains from logs.
Operating systems too. Windows and Linux command line, and log analysis habits. Windows Event Logs, Sysmon if you've seen it, auth logs on Linux. You should be comfortable reading "boring" artifacts and spotting what matters.
Web technologies are useful. HTML and JavaScript basics, and a working understanding of common web attacks like XSS and SQLi. Not exploitation. Just recognition and impact.
Log formats show up constantly. Syslog, Windows Event Logs, firewall logs, proxy logs. If you've never hunted through proxy logs for a domain, you'll feel slower during scenario questions.
Experience with security operations and incident response
SOC experience is a cheat code for CTIA. Alert triage, investigation, escalation workflows, and knowing what an analyst can realistically do at 2 a.m. makes intel more actionable.
Incident response fundamentals matter too: detection, containment, eradication, recovery. People love to memorize these words and forget the order under stress, so drill them until they're automatic.
Malware analysis basics help, even if you're not reversing. Being able to identify suspicious files, understand common behaviors like persistence and C2, and interpret sandbox output's enough.
Threat hunting concepts are worth having. Hypothesis-driven searches. Anomaly detection. Turning a hunch into a query. Then turning results into a short report that the next shift can use without calling you.
SIEM platforms are a plus. Splunk, QRadar, ArcSight, Elastic Stack. You don't need to be certified in them, but you should be comfortable with queries and correlation thinking.
OSINT and research skills checklist
OSINT's where a lot of CTI folks either shine or get wrecked by rabbit holes. You want controlled curiosity, not endless tabs.
Things to know: search engine operators and "Google dorking," plus Shodan and Censys for exposure checks. Social media research using Twitter, LinkedIn, and GitHub to track actors, tooling, and infrastructure patterns. Domain and IP investigation using WHOIS, passive DNS, and BGP lookups.
Dark web and underground forums come up too. Tor basics, paste sites, marketplaces. You're not buying anything, obviously. You're learning how information leaks and how actor chatter can signal targeting.
Malware repositories: VirusTotal, Hybrid Analysis, Any.Run, Joe Sandbox. Learn how to pivot, not just look at a single page.
Threat feed evaluation matters more than people admit. You need to assess quality, relevance, timeliness, and false positive rates for both commercial and open-source feeds, because stuffing junk IOCs into detections is how you burn analyst trust.
If you want practice questions to sanity-check your OSINT and analysis instincts, 312-85 Practice Exam Questions Pack can be a decent pressure test, especially when you review why you missed something instead of just moving on.
Familiarity with CTI frameworks and standards
Know the frameworks and what they're good at. MITRE ATT&CK for behavior and detections. Kill Chain for thinking in phases. Diamond Model for linking adversary, capability, infrastructure, and victim.
STIX/TAXII's where the exam can feel "standard-y." You don't need to write STIX by hand, but you should understand what structured intel looks like and why sharing protocols exist.
TLP's simple but important. Label your intel. Respect the label.
Educational background and alternative pathways
A degree in cybersecurity, computer science, or IT helps, but it's not required. I've met self-taught analysts with hands-on SOC time who run circles around degree holders because they've seen real alerts, real incidents, and real constraints.
Military or government cyber defense background's a strong foundation because the reporting discipline and intel mindset transfers well. Career changers can do fine too, but I'd recommend stacking fundamentals first: Security+ or CySA+ style knowledge, then CTIA-specific study. Optional prereq certs like Security+, CySA+, CEH, or equivalents can help, but again, CTIA doesn't require them.
CTIA 312-85 difficulty: how hard is the exam?
"How hard" depends on your background. If you've done SOC triage and written incident summaries, you'll find it reasonable. If you've only done theory or labs, the analysis and reporting questions can feel slippery because the best answer depends on context, confidence, and stakeholder needs.
Common pain points: frameworks used incorrectly, over-collecting OSINT, confusing indicators with TTPs, and writing-related concepts like audience and dissemination. Also, tool questions where they want the "why" not the "what."
Reduce risk with practice. Timed sets. Review misses. Re-read the objective you missed. Then do it again. If you're shopping for CTIA 312-85 practice tests, be picky and use them to learn patterns, not to memorize.
CTIA certification renewal requirements
People forget this until the last minute. CTIA certification renewal requirements generally involve EC-Council's continuing education program, with ECE credits, fees, and timelines depending on your certification cycle. Check your Aspen portal and the current EC-Council policy before you plan, because policies can change and your employer won't enjoy surprise renewal bills.
Earn credits through training, webinars, conferences, and sometimes work projects if they qualify. If it expires, you're dealing with reinstatement rules or retesting, and that's a pain you can avoid with a calendar reminder.
CTIA 312-85 FAQ
How much does the EC-Council CTIA (312-85) exam cost?
It varies by voucher vs bundle, region, and discounts, so treat any single number you see online as "maybe." If you're comparing options, include retake pricing and whether official training's bundled, because that's where EC-Council CTIA 312-85 cost can swing a lot.
What is the passing score for the CTIA 312-85 exam?
There isn't always one static published number for every form. Plan to exceed whatever minimum you hear quoted and focus on mastering the CTIA exam objectives 312-85, because that's what actually moves your score.
How hard is the CTIA exam compared to other EC-Council certifications?
It feels less "gotcha" than some offense-heavy tests, but more judgment-based. If you're strong in analysis and communication, it can feel easier than CEH. If you hate writing and ambiguity, it'll feel harder.
What are the CTIA 312-85 exam objectives and domains?
They cover the threat intelligence lifecycle, collection and analysis, production and dissemination, CTI tools and standards, and operationalizing intel across SOC/IR/hunting. Read the official outline, then map your weak areas to labs and reading.
How do I renew the CTIA certification and maintain it?
Track your ECE credits, pay attention to deadlines, and keep proof of activities. Also, keep your skills warm. CTI tools change, actor behavior changes, and your "old notes" get stale fast.
If you want one practical prep move, do a mixed routine: read the objectives, build small OSINT pivots daily, and use a question pack like 312-85 Practice Exam Questions Pack to expose gaps before exam day. That combo's boring. It works.
CTIA 312-85 Difficulty: How Hard Is the Exam?
Overall difficulty level: what you're actually getting into
Honestly? The EC-Council 312-85 CTIA exam occupies this strange territory where it's not quite the monster that CEH (312-50v12) represents in pure content volume, but it demands entirely different mental gymnastics. Most folks who've tackled both say CEH bombards you with topics..memorizing tools, attack vectors, scanning techniques, all that jazz. CTIA? Narrower focus, deeper dive. You're dissecting scenarios, threading connections between threat actor patterns and defensive countermeasures, reasoning through intelligence workflows from initial collection all the way to final dissemination.
First-attempt pass rates hover around 60-75% for properly prepared candidates. Not awful. Compare that to vendor exams dipping below 50% and you'll see EC-Council isn't playing total gatekeeper here. But here's the catch: those numbers assume relevant experience or really serious study investment. Winging it on general security knowledge? You're likely joining that 25-40% failure group.
The difficulty curve depends massively on your background. Someone running threat intelligence ops in a SOC for two years will cruise through sections that leave systems admins wondering why anyone gives a damn about cognitive biases in intelligence analysis. It's one of those certifications where your history matters way more than raw memorization skills.
Quick aside: I once watched a penetration tester with ten years' experience absolutely bomb a practice exam because he'd never actually produced intelligence reports or understood collection prioritization. Different ballgame entirely.
Who finds this exam easiest
SOC analysts handling actual threat intelligence responsibilities find this exam almost second nature. I mean, if you've spent the past year enriching IOCs, tracking adversary campaigns, writing intelligence reports..exam scenarios feel like Tuesday afternoon, honestly. You've lived the intelligence lifecycle. You understand why you'd pick one collection method over another because you've justified those exact decisions to your team lead.
Incident responders regularly digging into TTPs? Similar advantage.
When the exam asks you to map observed behaviors to MITRE ATT&CK techniques, you're not guessing from study materials. You're recalling that ransomware incident from three months back where you tracked lateral movement through specific techniques. Threat hunters using intelligence-driven methodologies already think in hypotheses, indicators, adversary patterns, which is precisely what CTIA evaluates.
Security researchers familiar with OSINT, malware analysis, IOC enrichment workflows walk in with half the battle already won. The exam loves asking about enrichment processes, validating indicators, distinguishing false positives from genuine threats. If you've actually performed this work, you're not memorizing procedures. You're just describing your job.
Candidates who've completed the official EC-Council CTIA training course definitely hold an edge. Not gonna lie, that course is expensive, but it maps directly to exam objectives and dissects the intelligence lifecycle in excruciating detail. If you've taken official training, you've already encountered the frameworks, practiced the analysis techniques, worked through comparable scenarios.
Who struggles with CTIA 312-85 the most
Entry-level security professionals without SOC or incident response experience? They hit a wall fast. The exam doesn't test whether you know what firewalls do or how DNS functions. It assumes foundational knowledge and jumps straight into "here's a threat actor campaign, what intelligence products would you generate for different stakeholders?" If you've never written an intelligence brief or tactical report, you're basically guessing.
Pure networking or systems administration backgrounds don't translate well here. I've talked to network engineers with solid CCNP credentials who found CTIA frustrating because..the thing is..it's just a completely different skill set. Knowing how to configure routing protocols doesn't help you understand structured analytic techniques or intelligence requirements.
People unfamiliar with CTI frameworks like MITRE ATT&CK, the Diamond Model, the Cyber Kill Chain? Uphill climb. The exam references these frameworks constantly. Questions might show you a scenario and ask which kill chain phase you're observing, or which ATT&CK tactic best describes adversary behavior. Without that framework knowledge deeply internalized, you're lost.
Test-takers relying purely on memorization without understanding workflows typically fail. This isn't Certified Cybersecurity Technician (212-82) where you can memorize security fundamentals and pass. CTIA wants you applying intelligence processes to novel scenarios. You need to understand why you'd use one analytical technique over another, not just know both exist.
Common challenge areas that trip people up
Scenario-based questions requiring multi-step analytical reasoning are the exam's bread and butter. You'll get a paragraph describing threat activity. Then you're identifying appropriate collection methods, analysis techniques, dissemination strategies. These questions don't have obvious answers. You're weighing trade-offs and selecting the best option among several plausible choices.
Distinguishing between strategic, operational, tactical, and technical intelligence confuses loads of candidates. The exam loves asking "what type of intelligence product would you create for this audience?" You need to know that C-suite executives want strategic intelligence focused on risk and business impact, while SOC analysts need tactical intelligence with specific IOCs and detection logic. Mix those up? You're missing points.
MITRE ATT&CK framework questions go deeper than "name some techniques." You're mapping observed behaviors to specific tactics, understanding sub-techniques, recognizing when an adversary's using multiple techniques to accomplish a single objective. The framework is massive, and the exam can pull from any corner. You don't need to memorize every technique, but you need solid understanding of how tactics relate to techniques and how techniques manifest in real attacks.
Intelligence writing and reporting trips up technical people who've never written for non-technical audiences. Questions ask about report structure. Appropriate detail levels for different stakeholders. When to use executive summaries versus detailed technical annexes. If you've only written technical documentation, this feels weird and subjective.
STIX/TAXII technical details and implementation get pretty specific.
The exam wants you knowing how STIX objects relate to each other, what TAXII servers do, how automated intelligence sharing works. Surface-level knowledge isn't enough. You need to understand the technical architecture.
Cognitive biases and structured analytic techniques like Analysis of Competing Hypotheses or Key Assumptions Check show up more than you'd expect. The exam tests whether you understand how biases affect intelligence analysis and which techniques help mitigate specific biases. It's the softer side of intelligence work that technical people sometimes dismiss, but EC-Council takes it seriously.
Attribution challenges and understanding limitations matter here too. The exam will present attribution scenarios and ask what you can reasonably conclude versus what's speculation. Overconfident attribution gets punished. You need to recognize when evidence supports low, medium, or high confidence assessments.
Threat actor profiling questions dig into motivations, capabilities, infrastructure patterns. You're not just identifying that an actor is APT29. You're analyzing behavior patterns to infer capabilities, recognizing infrastructure reuse, understanding how motivations shape targeting decisions.
IOC enrichment workflows require understanding the full process from raw indicator to actionable intelligence. How do you validate an IP address? What sources would you check? How do you distinguish malicious infrastructure from compromised legitimate infrastructure? It's practical stuff, but..I mean..the exam wants specific knowledge of tools and methodologies.
The Certified SOC Analyst (312-39) exam overlaps a bit with CTIA on detection and monitoring, but CTIA goes way deeper on the intelligence side. If you're deciding between them, CTIA's the move if you want to specialize in threat intelligence rather than general SOC operations.
Conclusion
Wrapping up your CTIA path
Look, the EC-Council 312-85 CTIA exam isn't something you just waltz into without a plan. I mean, you could, but that's probably not gonna end well. The Certified Threat Intelligence Analyst (CTIA) certification validates skills that organizations desperately need right now. Threat intelligence lifecycle management, IOC enrichment and analysis, MITRE ATT&CK mapping, the whole nine yards. That makes it worth the investment if you're serious about threat intel as a career path.
But here's the thing.
Understanding CTIA 312-85 exam objectives is one part of the equation. Memorizing frameworks? Sure, that's basic stuff. Knowing your cyber threat intelligence (CTI) tools? Absolutely necessary. But what really separates people who pass from those who don't is realistic practice under exam conditions. I've watched this happen more times than I can count. Especially when you're dealing with the CTIA 312-85 passing score requirements and time pressure breathing down your neck.
The EC-Council CTIA 312-85 cost isn't cheap either, so you don't wanna waste that voucher on a failed attempt because you skipped proper prep. I've seen too many people underestimate how specific this exam gets with threat hunting and intelligence reporting scenarios. CTIA 312-85 study materials help build your foundation. Official training, hands-on labs, reference docs for STIX/TAXII and MITRE frameworks. But practice tests are where you learn to think like the exam wants you to think. Not just what you know, but how fast you recall it and apply it under pressure.
Side note: I once knew someone who spent three months studying theory and then bombed the exam because they'd never timed themselves on practice questions. Frustrating to watch, honestly.
Don't forget about CTIA certification prerequisites. Does your background actually set you up for success here? If you're coming from a SOC or IR role you'll have context. Total beginners might struggle more. And once you pass, CTIA certification renewal requirements kick in, so factor that ongoing commitment into your decision.
If you're ready to lock in your prep and test your readiness with realistic questions, the 312-85 Practice Exam Questions Pack gives you that final confidence boost before test day. Walking into that exam knowing you've already seen similar question formats and scenarios makes a huge difference. You've already invested the time learning the material. Make sure you're actually ready to prove it when it counts.
Show less info
Hot Exams
Related Exams
Certified EC-Council Instructor (CEI)
Certified Network Defender (CND)
Ethical Hacking and Countermeasures V8
Certified Ethical Hacker Exam
Certified Ethical Hacker Exam (CEHv12)
Certified Ethical Hacker Exam (CEH v11)
EC Council Certified Incident Handler (ECIH v3)
EC-Council Certified Security Analyst (ECSA) V10
Linux Security
EC-Council Certified Security Analyst (ECSA)
Certified Ethical Hacker CEH v11
Certified Threat Intelligence Analyst (CTIA)
Computer Hacking Forensic Investigator
EC-Council Certified CISO (CCISO)
EC-Council Certified Encryption Specialist (ECES)
Computer Hacking Forensic Investigator (CHFI-v10)
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.