SEC504 Practice Exam - Hacker Tools, Techniques, Exploits and Incident Handling
Reliable Study Materials & Testing Engine for SEC504 Exam Success!
Exam Code: SEC504
Exam Name: Hacker Tools, Techniques, Exploits and Incident Handling
Certification Provider: SANS
Corresponding Certifications: Certified Incident Handler , Hacker Tools, Techniques, Exploits and Incident Handling

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
SEC504: Hacker Tools, Techniques, Exploits and Incident Handling Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 328 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena SANS Hacker Tools, Techniques, Exploits and Incident Handling (SEC504) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
SANS SEC504 Exam FAQs
Introduction of SANS SEC504 Exam!
SANS SEC504: Hacker Tools, Techniques, Exploits, and Incident Handling is a five-day security course which teaches students how to use hacking tools and techniques to assess, protect, and defend computer networks. The class is designed for security professionals and system administrators who need to understand the tactics and tools used by attackers and be able to respond quickly and effectively to incidents.
What is the Duration of SANS SEC504 Exam?
The SANS SEC504 exam is a 4-hour long exam.
What are the Number of Questions Asked in SANS SEC504 Exam?
The SANS SEC504 Exam consists of 175 multiple-choice questions.
What is the Passing Score for SANS SEC504 Exam?
The passing score for the SANS SEC504 exam is 70%.
What is the Competency Level required for SANS SEC504 Exam?
The SANS SEC504 exam requires a competency level of ICS410: ICS/SCADA Security Essentials.
What is the Question Format of SANS SEC504 Exam?
The SANS SEC504 exam consists of 150 multiple-choice questions.
How Can You Take SANS SEC504 Exam?
The SANS SEC504 exam is available in both online and in-person testing center formats. For the online format, students must register for the exam online and then take the exam remotely from their own computer. For the in-person format, students must register for the exam and then take the exam at a Pearson VUE testing center.
What Language SANS SEC504 Exam is Offered?
The SANS SEC504 exam is offered in English.
What is the Cost of SANS SEC504 Exam?
The cost of the SANS SEC504 exam is $1,599.
What is the Target Audience of SANS SEC504 Exam?
The SANS SEC504 exam is designed for IT professionals who are responsible for security operations, including security administrators, security engineers, system administrators, and network engineers. It is also suitable for those who are preparing for the GIAC Security Essentials Certification (GSEC).
What is the Average Salary of SANS SEC504 Certified in the Market?
The average salary for a person with SANS SEC504 certification can vary greatly depending on the individual's experience and the job market in their area. Generally, salaries for those with SANS SEC504 certification range from $60,000 to $125,000.
Who are the Testing Providers of SANS SEC504 Exam?
The SANS Institute provides the official testing for the SEC504 exam. The exam is administered at Pearson VUE testing centers.
What is the Recommended Experience for SANS SEC504 Exam?
The recommended experience for the SANS SEC504 exam is a minimum of two years of experience in information security, including hands-on experience with security administration, security analysis, and security engineering. It is also recommended to have taken the SANS SEC401: Security Essentials Bootcamp Style course or have equivalent knowledge.
What are the Prerequisites of SANS SEC504 Exam?
The Prerequisite for SANS SEC504 Exam is SANS SEC401: Security Essentials Bootcamp Style.
What is the Expected Retirement Date of SANS SEC504 Exam?
The expected retirement date of SANS SEC504 exam is not available online. You may contact SANS directly via their website (https://www.sans.org/contact-us) for more information.
What is the Difficulty Level of SANS SEC504 Exam?
The difficulty level of the SANS SEC504 exam is considered to be intermediate.
What is the Roadmap / Track of SANS SEC504 Exam?
The certification roadmap for the SANS SEC504 exam consists of the following steps:
1. Complete the SANS SEC504: Hacker Tools, Techniques, Exploits, and Incident Handling course.
2. Pass the SANS SEC504 exam.
3. Receive the GIAC Security Essentials Certification (GSEC).
4. Receive the GIAC Certified Incident Handler (GCIH) certification.
5. Receive the GIAC Certified Intrusion Analyst (GCIA) certification.
6. Receive the GIAC Certified Intrusion Analyst (GCFA) certification.
7. Receive the GIAC Certified Forensic Analyst (GCFE) certification.
What are the Topics SANS SEC504 Exam Covers?
1. Security Policies and Procedures: This topic covers the development, implementation, and maintenance of effective security policies and procedures to protect an organization's assets and information.
2. Network Security Architecture: This topic covers the design, implementation, and maintenance of secure network architectures, including firewalls, routers, switches, and other network components.
3. Host Security: This topic covers the design, implementation, and maintenance of secure host systems, including operating systems, applications, and user access controls.
4. Authentication and Access Control: This topic covers the implementation and management of authentication and access control systems, including user authentication, authorization, and access control lists.
5. Cryptography: This topic covers the fundamentals of cryptography, including encryption algorithms, digital signatures, and key management.
6. Malware Analysis: This topic covers the techniques used to detect, analyze, and respond to malicious software, including malware analysis tools and techniques.
7.
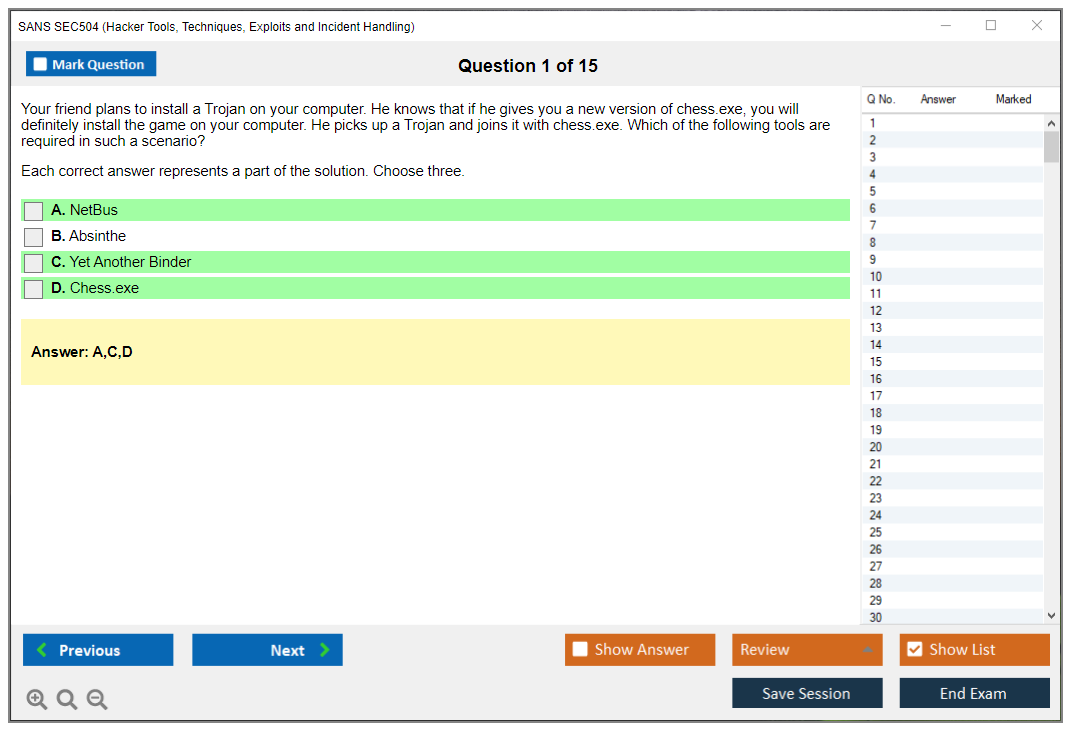
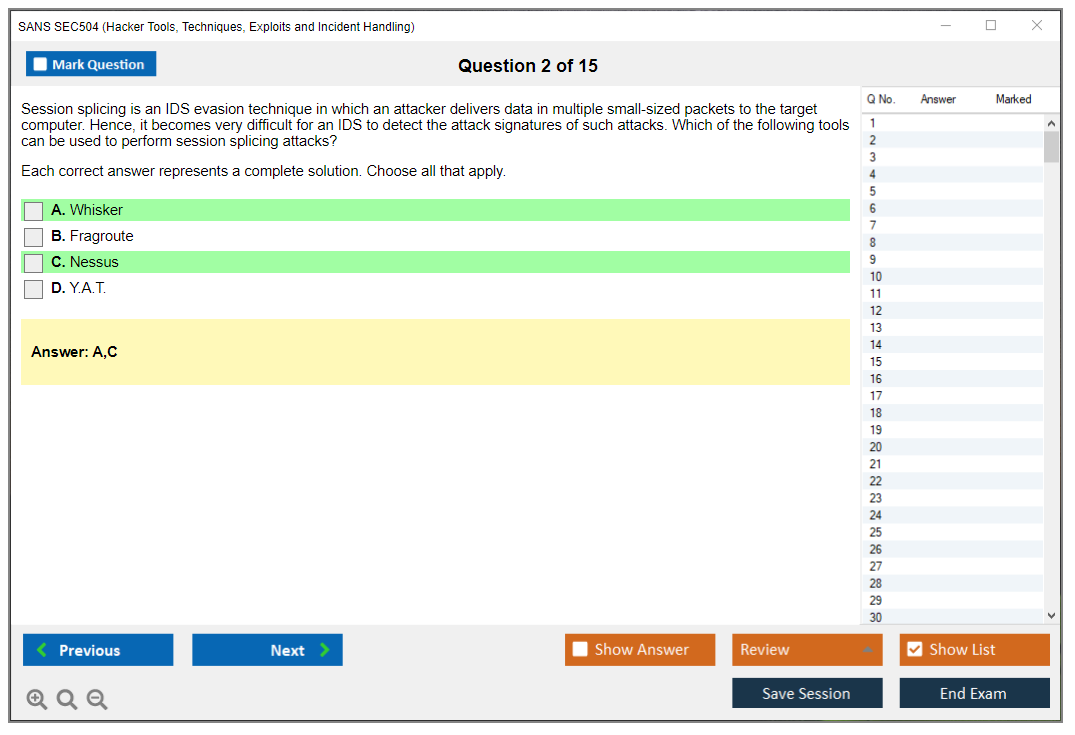
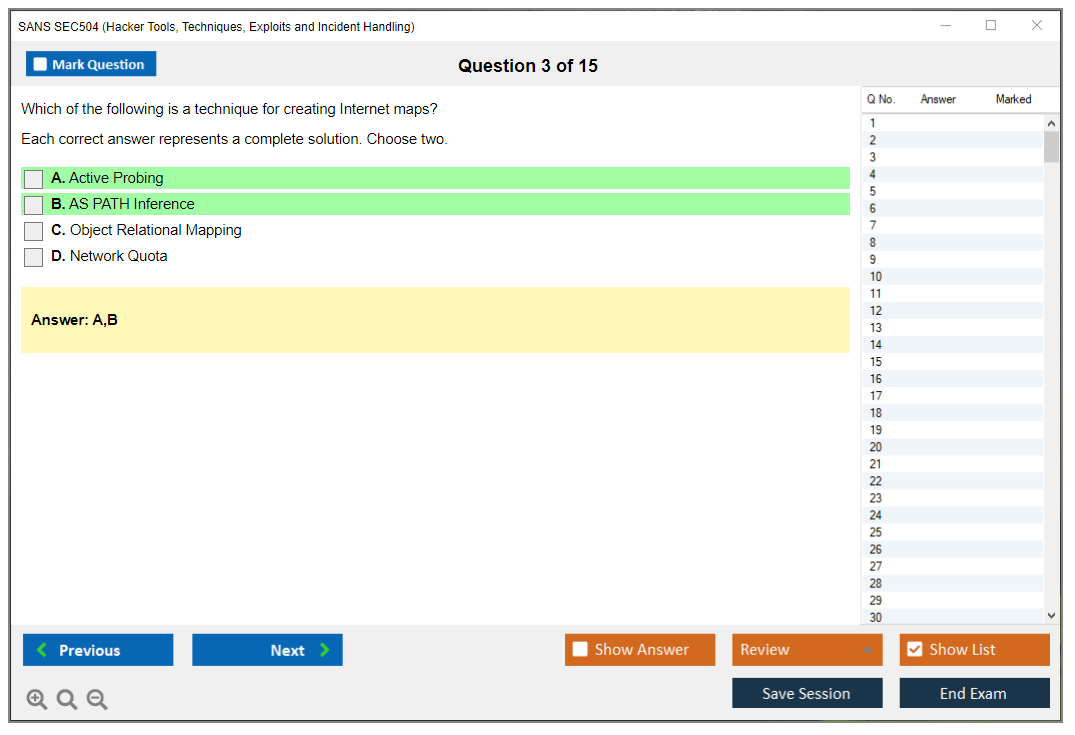
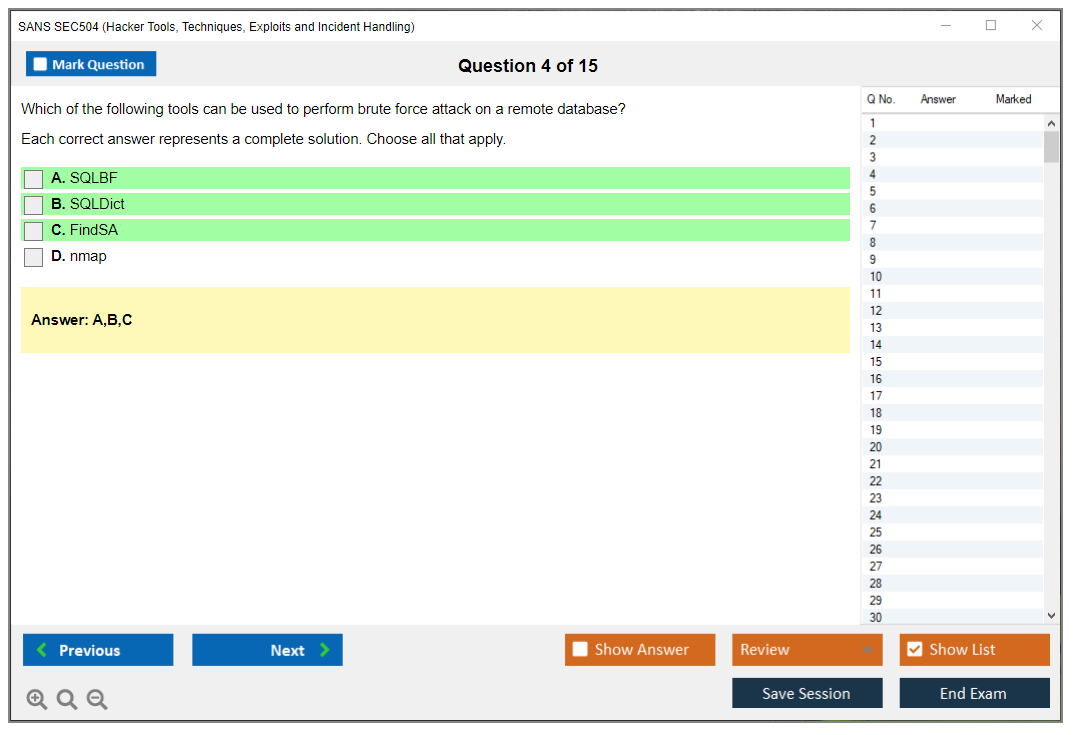
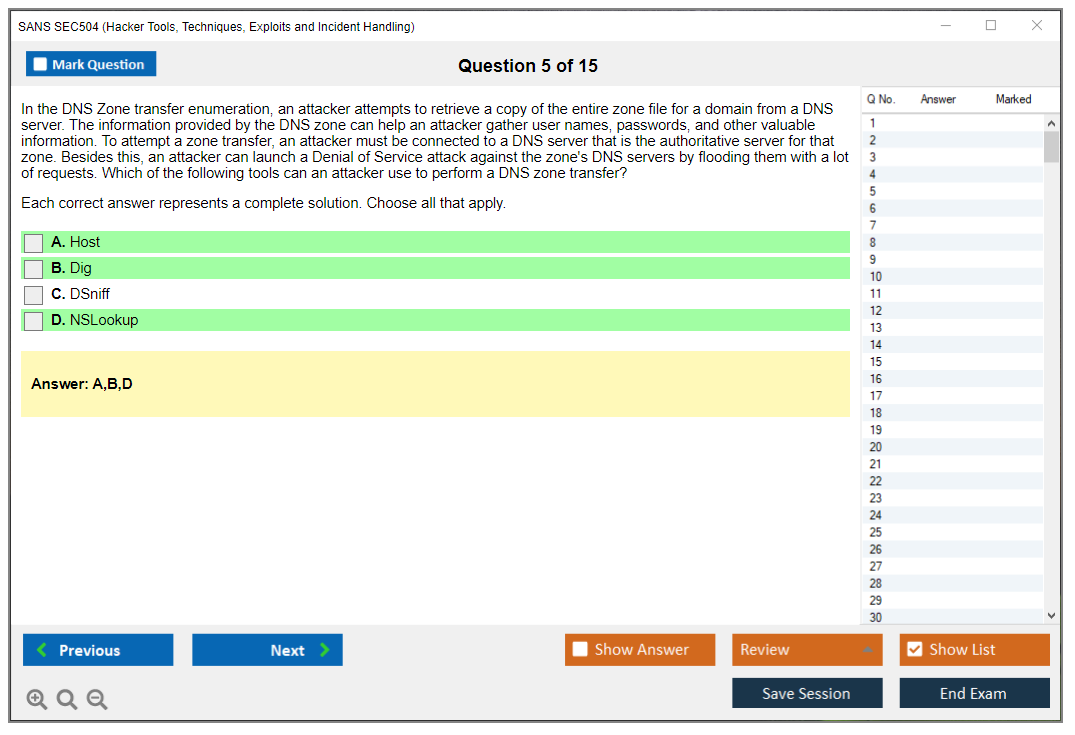
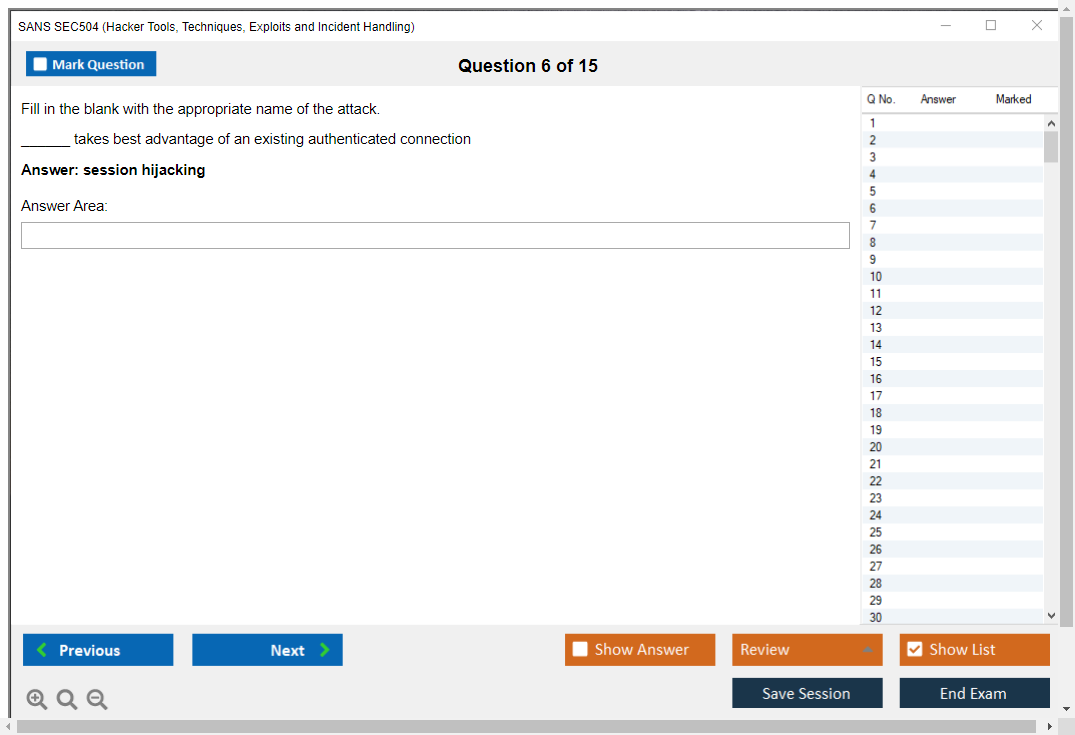
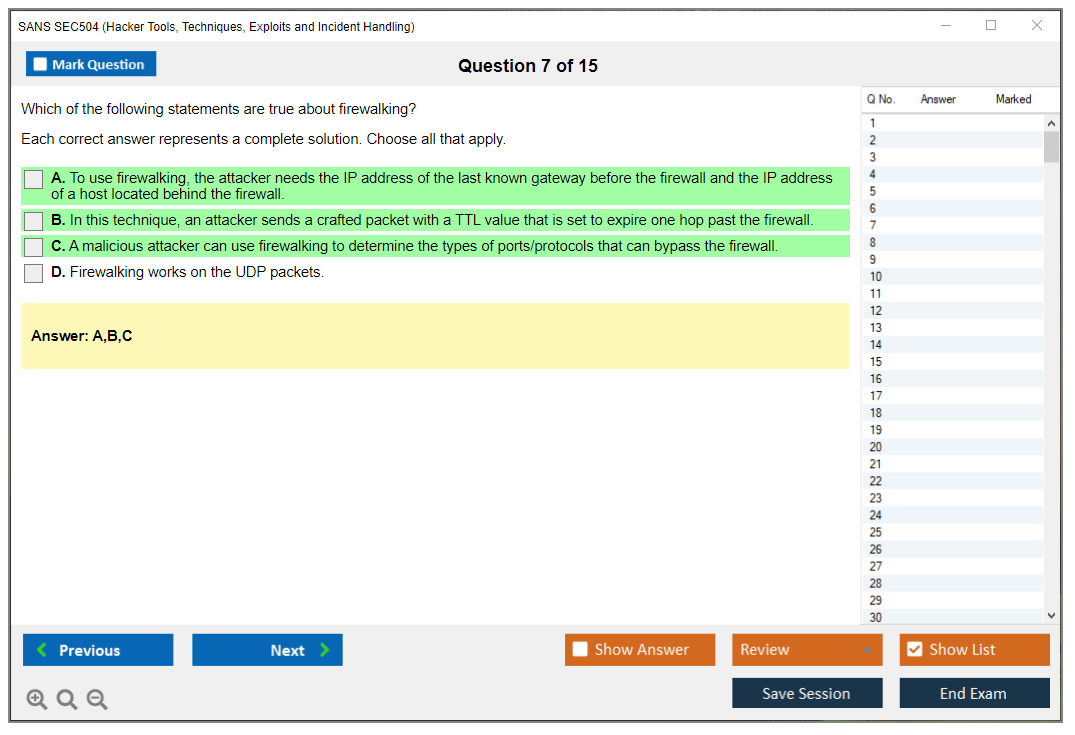
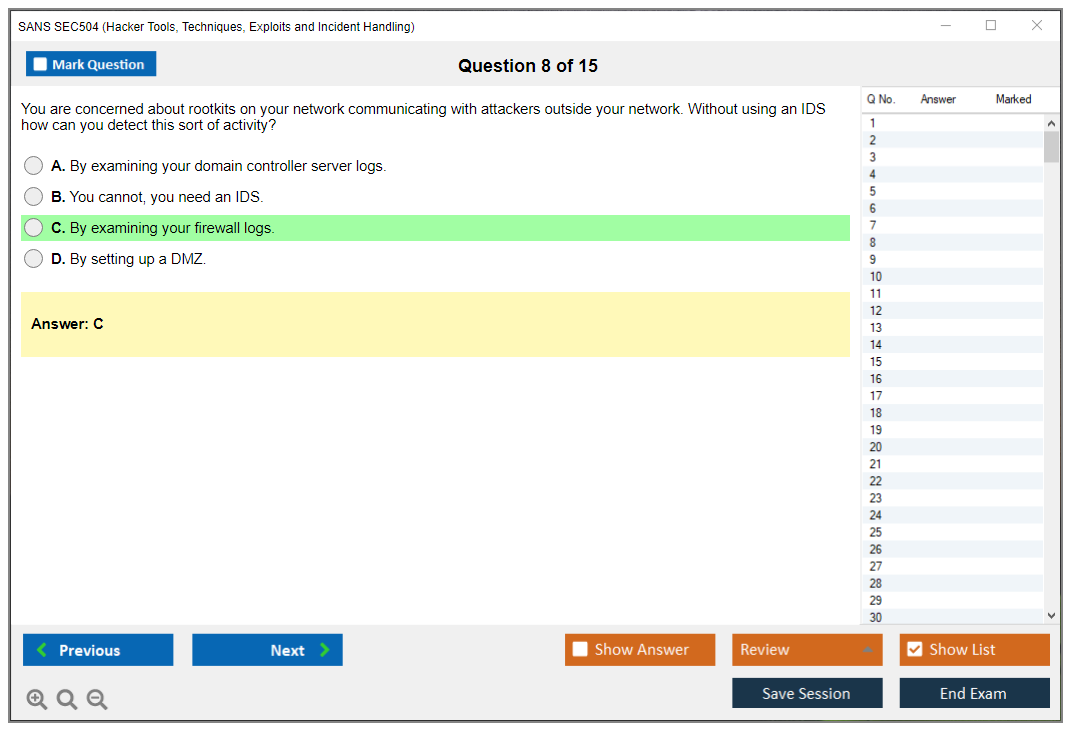
What are the Sample Questions of SANS SEC504 Exam?
1. What is the purpose of implementing an Incident Response Plan?
2. What are the best practices for securing a network against malicious attacks?
3. Describe the steps involved in performing a vulnerability assessment.
4. How do you identify potential threats and vulnerabilities on a network?
5. What is the difference between a security policy and a security procedure?
6. What techniques can be used to detect malicious activity on a network?
7. What measures can be taken to prevent data leakage?
8. How can a system administrator respond to a security incident?
9. What are the benefits of using a Security Information and Event Management (SIEM) system?
10. What is the purpose of a risk assessment and how is it conducted?
SANS SEC504 (Hacker Tools, Techniques, Exploits and Incident Handling) Overview What SEC504 actually teaches you Here's the deal. SANS SEC504 is where you learn to think like attackers so you can actually defend against them. It's industry-recognized training from SANS Institute that digs deep into hacker tools, techniques, exploits, and how to handle incidents when everything goes sideways. The foundation's pretty straightforward. You can't defend against attacks you don't understand, so the course walks you through attacker methodologies from reconnaissance all the way through post-exploitation. The primary learning outcomes revolve around detection, response, and mitigation. You're learning incident handling processes that actually work in the real world, not just theory that sounds good in a conference room but falls apart the second you're dealing with an actual breach. The hands-on component is huge. You're running through practical labs that simulate actual attack scenarios and... Read More
SANS SEC504 (Hacker Tools, Techniques, Exploits and Incident Handling) Overview
What SEC504 actually teaches you
Here's the deal. SANS SEC504 is where you learn to think like attackers so you can actually defend against them. It's industry-recognized training from SANS Institute that digs deep into hacker tools, techniques, exploits, and how to handle incidents when everything goes sideways. The foundation's pretty straightforward. You can't defend against attacks you don't understand, so the course walks you through attacker methodologies from reconnaissance all the way through post-exploitation.
The primary learning outcomes revolve around detection, response, and mitigation. You're learning incident handling processes that actually work in the real world, not just theory that sounds good in a conference room but falls apart the second you're dealing with an actual breach. The hands-on component is huge. You're running through practical labs that simulate actual attack scenarios and incident response workflows. That's where most people finally connect the dots between concepts and reality.
Who this training is designed for
Pretty broad audience but focused. Security analysts, incident responders, SOC personnel, network administrators trying to level up into security roles. Basically anyone who needs to deal with security incidents as part of their job. Not gonna lie, this isn't entry-level stuff. You need intermediate experience with foundational networking and operating system knowledge before you walk in the door.
If you don't know the difference between TCP and UDP or you've never looked at Windows Event Logs, you're gonna struggle. Hard. The course assumes you understand basic security concepts, common attack patterns, and can work through both Windows and Linux systems without getting lost. Helpful but not required: some scripting background and experience analyzing logs makes everything click faster.
I remember my first week in SOC work, before I had this training. Someone escalated what turned out to be a false positive lateral movement alert and I spent three hours chasing ghosts because I didn't understand how normal admin tools could mimic attacker behavior. Would've saved myself the embarrassment if I'd known what SEC504 covers about distinguishing malicious activity from legitimate sysadmin work.
How SEC504 maps to the GCIH certification
Here's where people get confused. SEC504 is the training course, GIAC Certified Incident Handler (GCIH) is the certification exam you take afterward. They're related but separate things. You can take SEC504 training through multiple delivery formats: live in-person training (the traditional boot camp style), OnDemand self-paced study if you learn better alone, vLive online instructor-led sessions, or private training for teams.
Time commitment is serious. Six-day intensive course with approximately 36 to 40 hours of instruction plus all the lab exercises. Plan to be mentally exhausted by day three because the information density is no joke.
The course materials you get are thorough. Multiple books, lab environments, reference materials, and documentation covering both attack and defense tools. Most bundles include an attempt at the GCIH exam, but confirm that at checkout because SANS pricing varies by delivery format, location, and timing.
Real-world value and career impact
The skills transfer directly to daily security operations, threat hunting, and incident response activities. I mean, you're learning the actual workflow (detect, contain, eradicate, recover) using the same tools and techniques professional incident responders use. You cover attacker tools and exploit methods, network and host-based detection concepts, evidence collection, triage, escalation, and how to communicate during incidents without causing panic.
Industry recognition is solid. Employers, government agencies, and security professionals globally respect GCIH because it demonstrates you can actually handle an incident, not just talk about handling incidents. There are way too many people who can talk a good game but freeze when alerts start firing. Career advancement potential is real. This opens doors to incident response positions, SOC analyst roles, security engineer jobs, and threat analyst positions.
SANS keeps the content current with regular updates reflecting the threat space, new attack techniques, and defensive technologies. That matters because last year's attack patterns don't help you defend against this year's campaigns.
Community resources and ongoing support
You get access to SANS community resources, alumni networks, and ongoing professional development opportunities. The SEC504 community is active and helpful when you're stuck on concepts or need real-world advice.
Cost-wise, SEC504 typically runs in the multi-thousand USD range, often around $7,000 to $9,000+ for the course bundle depending on format. That usually includes course tuition, official courseware, labs, and one GCIH exam attempt. Additional costs to budget for: retake fees if you don't pass first try, travel and lodging for in-person training, and proctoring requirements.
The GCIH exam itself is proctored, timed, and typically open-book (verify current rules on GIAC's site). Difficulty level sits at intermediate to advanced because you're covering breadth (attacks plus detection plus response) and time management becomes critical. Building an effective index during the course is necessary for open-book success.
SEC504 Course Objectives and Syllabus
What you actually get from the SANS SEC504 certification course
SANS SEC504 certification training (the "Hacker Tools, Techniques, Exploits and Incident Handling" class) is basically the course that teaches you how attacks really happen, then forces you to respond like you're on call at 2 a.m. It's a hacker tools and techniques course, but it's not cosplay. You learn the offensive moves so your incident handling and response training gets faster, calmer, and way more evidence-driven when things go sideways in production.
Look, the SEC504 course overview is wide on purpose, honestly. You touch recon, exploitation, post-exploitation, and then the defensive side that actually matters. Triage, logging, packet analysis, and containment choices that don't blow up the business while executives are breathing down your neck.
Who should take it (and who will hate it)
SOC analysts? Yeah. Incident responders. Security engineers. Some sysadmins moving into blue team.
Brand-new folks struggle. Honestly.
You'll be fine if you already speak TCP/IP, can read logs without panicking, and have basic Windows and Linux comfort. The SEC504 difficulty level comes from switching contexts constantly, not from one single "hard topic" you can brute force the night before with energy drinks and desperation.
How SEC504 maps to GIAC GCIH
People mix this up constantly. SEC504 is the training. GIAC GCIH exam details are about the certification test you take after, and the class is built to cover what GCIH expects. Recognize attacker behavior, confirm it with evidence, and respond with something better than "we rebooted it and hoped."
The SEC504 objectives and syllabus by day
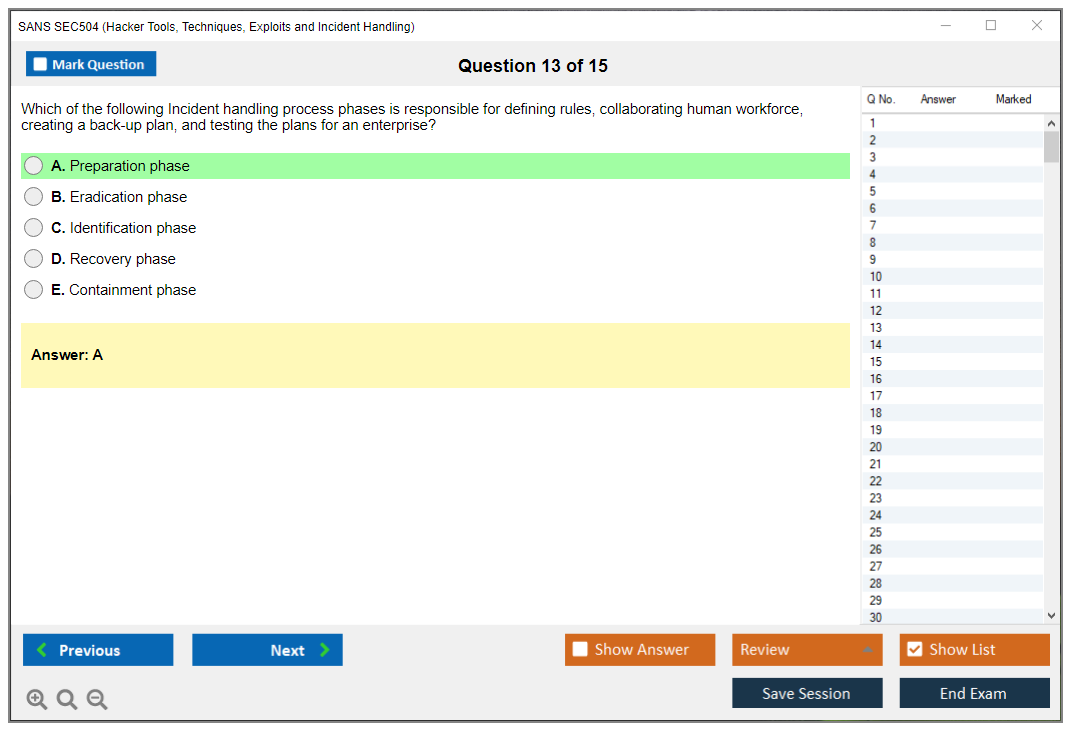
Day 1 is incident handling and computer crime investigation. You start with the incident response framework, the classic six-phase process: preparation, identification, containment, eradication, recovery, and lessons learned. Legal considerations show up early, which is good, because if you don't treat evidence correctly you can sabotage your own case before lawyers even get involved. You'll cover evidence collection methodology plus chain of custody requirements so your notes, hashes, timestamps, and storage decisions don't get shredded later by audit or legal teams who live for finding gaps.
Day 2 is recon, scanning, and enumeration. Attackers don't "hack" first. They look first, I mean that's the whole game. Reconnaissance techniques covered include OSINT gathering, social engineering, DNS enumeration, and other public info harvesting methods that'd surprise you how much is just sitting out there. Then you get into network scanning fundamentals like port scanning with Nmap, service fingerprinting, vulnerability identification, and basic network mapping, followed by enumeration strategies that pull users, shares, services, and system info from Windows and Linux targets without setting off every alarm. Defensive detection methods matter here too. You'll look for recon patterns through logs, network monitoring, and behavioral tells. A scan is often the earliest gift an attacker gives you if you're watching.
Day 3 is exploitation and gaining access. This is where exploit frameworks come in, usually Metasploit usage plus the concepts behind payload delivery and what "custom exploit development" really means at this level (more like understanding the moving parts than writing 0days in your spare time). Password attack techniques show up hard: credential harvesting, brute force, dictionary attacks, rainbow tables, hash cracking, the works. Web application exploitation is also on the table, including SQL injection, cross-site scripting (XSS), command injection, and the usual OWASP-type failures that still work shockingly well in 2025. Plus client-side attacks like phishing, malicious documents, browser exploits, and social engineering delivery methods that get you an initial foothold when perimeter defenses are actually decent.
Day 4? Post-exploitation and maintaining access. Persistence. Privilege escalation. Lateral movement. You'll cover Windows and Linux privilege escalation methods, then persistence mechanisms like registry modifications, scheduled tasks, service creation, and backdoor installation techniques that survive reboots and patching cycles. Lateral movement strategies include pass-the-hash, pass-the-ticket, remote execution, and credential reuse across the environment. The thing is, you also talk data exfiltration methods like covert channels, encrypted tunnels, DNS tunneling, and even steganography hiding payloads in cat pictures or whatever. Not gonna lie, this day is where people realize how fast "one box popped" becomes "domain problems" and executives asking why AD is toast.
Day 5 is detection and analysis, where network intrusion detection fundamentals come alive with packet capture using tcpdump/Wireshark, protocol analysis, and anomaly detection in flows that don't match baseline behavior. Log analysis fundamentals hit Windows Event Logs, Linux syslog, application logs, and centralized logging platforms you're supposed to have configured correctly (but let's be real, half the time aren't). Then intrusion detection systems work with signature versus anomaly thinking plus Snort/Suricata rule writing and alert triage so you're not drowning in false positives. You also get a memory forensics introduction: processes, malware in memory, artifacts in RAM that disappear when power cycles. Wait, did I mention IOC identification is threaded through this? Because indicators are only useful when you can connect them to behavior and scope across your environment, not just isolated events. My old manager used to say IOCs without context are just trivia night answers, which honestly stuck with me more than it probably should have.
Day 6 is containment, eradication, and recovery. The part where theory meets "the business is losing money every minute." Containment strategies include isolation, segmentation, quarantine, and damage limitation without nuking everything. Eradication procedures cover malware removal, patching, credential resets, and wiping attacker access from every corner they touched. Then recovery planning is about restoration, validation testing, resuming services, and monitoring for reinfection because attackers love coming back through doors you forgot to lock. Post-incident activities cover documentation, lessons learned, process improvement, and stakeholder communication that doesn't make you sound incompetent. Threat hunting concepts show up too, with hypothesis-driven searches and continuous monitoring. Waiting for alerts is a bad plan when advanced threats are patient.
Cost, score, practice tests, and renewal (quick reality check)
SEC504 cost and fees are usually in the multi-thousand USD range, often around $7,000 to $9,000+ depending on format and timing. The bundle commonly includes courseware, labs, and an attempt at the GIAC exam (confirm at checkout because SANS changes packages). SEC504 study materials are mostly the official books plus your labs. For open-book tests your index is everything. I mean it's the difference between "I know this" and "I can find this in 20 seconds" when the clock's ticking.
SEC504 practice tests from GIAC are the closest match to the real thing when your bundle includes them, so use 'em. For SEC504 passing score, check the official GIAC GCIH page because GIAC can change it without much warning. Same deal for renewal: GCIH validity and renewal requirements (CPEs, fees, timelines) should be verified on GIAC before you publish internal guidance or make promises to management.
Worth it?
If you want Windows and Linux attack techniques, plus real containment choices and threat hunting and containment skills that translate to on-call work at ungodly hours, SEC504 is a solid buy. If you hate logs, hate packets, and want only policy work where technical details are someone else's problem? You'll be miserable.
SEC504 Prerequisites and Recommended Background
Networking fundamentals you actually need
Okay, real talk here. SEC504 isn't messing around. It assumes you've already got decent networking chops under your belt. You'll need solid TCP/IP understanding, which means being comfortable with the OSI model layers and how data actually flows through them, not just regurgitating definitions you memorized the night before some certification exam. You've gotta understand how packets move from source to destination, what happens at each hop along the way, and why any of that matters when you're hunting for intrusions in a live environment.
Protocol knowledge? It's huge. HTTP and HTTPS behaviors, DNS lookups and zone transfers, SMTP mail flow, FTP data channels. You should know what normal looks like for these protocols before weird traffic shows up. SMB/CIFS for Windows file sharing, RDP for remote desktop, SSH for secure shell access. When you see traffic on port 445 or 3389, you need to immediately know what service that is and whether the volume or pattern seems off.
Subnetting can't be a mystery anymore. CIDR notation, subnet masks, how network segmentation works. The thing is, these are daily tools in incident response. If you're still counting on your fingers to figure out what /24 means, honestly, spend time on this before the course starts.
Operating system fundamentals across Windows and Linux
Windows experience? Non-negotiable. I mean really knowing Windows. Not just clicking around the desktop like you're browsing vacation photos. File system structure (NTFS permissions matter), user and group management, how the registry works at a basic level, common services like DNS Client or Server service. You'll be digging through compromised Windows boxes, so comfort with the OS is necessary.
Windows security features come up constantly in SEC504. UAC and how attackers bypass it, Windows Defender exclusions that malware loves to abuse, Group Policy basics for understanding enterprise controls, and authentication mechanisms like NTLM versus Kerberos. Honestly, if you don't know the difference, that's a problem. Windows Event Logs are your friend, or enemy if you don't understand them. Know the event types (Information, Warning, Error, Success Audit, Failure Audit), where logs live (Event Viewer, .evtx files), and recognize important event IDs like 4624 for logons or 7045 for new service installations.
Linux fundamentals matter too. The file system hierarchy (/etc, /var, /home, /tmp and why each matters), the permissions model with read/write/execute for owner/group/other, basic shell commands beyond just ls and cd. Process management with ps, top, and understanding parent-child process relationships when hunting persistence mechanisms. My old boss used to say you can tell how good someone is by watching them work through /var/log for thirty seconds, which sounds pretentious but turned out to be kind of true.
Linux logging through syslog? Different beast entirely. Understanding syslog architecture, knowing that /var/log is your hunting ground, and how log rotation with logrotate works. This stuff speeds up your analysis during labs.
Command-line comfort separates struggle from success
You need command-line proficiency. Both environments. PowerShell on Windows (not just CMD anymore), bash on Linux. If typing commands makes you nervous or you constantly need to Google basic syntax, that's gonna slow you down hard during the hands-on portions. And there are a lot of hands-on portions. Troubleshooting connectivity, analyzing processes, parsing logs. Much of this happens at the command line.
Security concepts and threat awareness
Foundation security concepts should already be in your head. CIA triad isn't just an acronym to memorize. You should understand confidentiality, integrity, and availability in practical terms, like how they apply to actual breaches you've read about. Threat modeling basics, common attack vectors like phishing or drive-by downloads, defense-in-depth principles and why single-layer security fails spectacularly.
Malware awareness means knowing the difference between viruses, worms, trojans, and ransomware. Not just definitions but behavioral patterns. How does ransomware typically spread? What persistence mechanisms do trojans use? This background context makes the course content click faster.
Authentication and authorization concepts include understanding how users authenticate (passwords, certificates, multi-factor), access control models like RBAC or DAC, and credential management. When you see pass-the-hash attacks in class, you'll need to understand why NTLM hashes matter. Wait, actually, you should probably already know that going in.
Helpful skills that accelerate learning
Scripting knowledge isn't required. But man, does it help. Python, PowerShell, or bash. Basic scripting with loops, conditionals, file I/O lets you automate repetitive analysis tasks during labs instead of doing everything manually like some kind of masochist. If you have zero scripting background, you'll survive. Expect more grunt work though.
Virtualization familiarity helps too. If you've worked with VMs, virtual switches, and virtual networking, the course lab architecture makes immediate sense. Not required, but nice to have.
How to prep and self-assess
Recommended preparation? Review TCP/IP fundamentals. Something like the SANS Cyber Aces tutorials works well. Practice basic packet analysis with Wireshark on your home network. Refresh your OS administration skills. Create users, modify permissions, read some logs.
Self-assessment is pretty straightforward: can you configure a home router and troubleshoot why devices can't reach the internet? Can you create users and manage permissions on Windows and Linux? Can you explain what's happening when you browse to a website, like actually explain the DNS resolution and TCP handshake? If yes, you're probably fine.
For gap-filling? SANS Cyber Aces has free tutorials, there are tons of free networking courses on YouTube (quality varies wildly, but that's another discussion), and OS vendor documentation is actually pretty good. Budget 10-20 hours for focused review if your skills are rusty but present. No programming requirement exists. Extensive coding or development experience isn't necessary for success here, despite what some people think.
SEC504 Cost and Fees Breakdown
What you're paying for (and what the course actually is)
The SANS SEC504 certification track is one of those courses people name-drop for a reason. SEC504 is the "Hacker Tools, Techniques, Exploits and Incident Handling" class, and the vibe is very practical: you learn what attackers do, how to spot it, and how to respond without turning your incident into a bigger incident.
It's also expensive. Like, seriously expensive.
SEC504 course overview? Incident handling and response training plus attacker tradecraft, with plenty of labs and "here's what this looks like on a real box" moments.
What you'll learn (high-level, but real)
The SEC504 objectives and syllabus are a mix of offense-informed defense and incident response muscle memory. Detect, contain, eradicate, recover, then document it so leadership doesn't freak out and your legal team can breathe.
You'll touch network intrusion detection fundamentals, triage patterns, and a bunch of Windows and Linux attack techniques that show up in real intrusions. There's also threat hunting and containment skills baked in, because the difference between "we're fine" and "we're compromised" is usually whether someone can connect weak signals fast enough to actually matter. I once watched a junior analyst miss three DNS tunneling indicators in a row because nobody taught them what normal recursion patterns look like, and that's exactly the kind of gap this course tries to close.
Who this is for (and who will hate it)
SOC analysts. Incident responders. Security engineers who get pulled into investigations, and sysadmins who keep inheriting security work. If you've never read logs or you don't know what DNS does, you can still survive, but you'll definitely feel the pain.
The SEC504 difficulty level sits somewhere around "intermediate-to-advanced" mostly because it's wide. The time pressure plus the breadth is what gets people, not one single impossible topic. You're constantly shifting contexts and that burns through mental energy faster than most people expect.
Course tuition range (the big number)
SEC504 cost and fees are usually in the $7,000 to $9,000+ USD range, depending on delivery format, location, and timing. That range is the reality for modern SANS pricing, and you should plan your budget like the high end's possible, because it often is.
Live in-person training? Highest price point. You get six days in a classroom with SANS-certified instructors, and that "ask a question in real time, get un-stuck fast" effect is legit, especially when labs go sideways.
vLive online training is usually comparable to in-person pricing. It's live instruction in a virtual classroom, with interaction, Q&A, and the same schedule pressure, just without flights and hotel coffee.
OnDemand self-paced pricing typically lands a bit lower than live, and you generally get around four months of access to the video lectures and labs. If you're working shift work or you can't disappear for a whole week, this is the format that keeps your life intact, though you do need self-discipline because nobody's watching you.
Private training options exist too, with custom pricing for orgs (usually 15+ students). If your company wants the hacker tools and techniques course delivered to your team with your internal context, this can be a better deal per head, but you'll be doing procurement paperwork for a while.
What's included in the base price (and what varies)
Most SEC504 bundles include the course books, usually 4 to 6 volumes, plus digital resources and reference material. Lab access is included, but the duration varies. OnDemand commonly gives you about four months. Live events can be more event-specific, so confirm the lab environment access window before you assume you'll have it all quarter.
Many formats include MP3 audio recordings of lectures. This sounds small, but it's huge when you're indexing, reviewing, or doing commute-time study.
The GIAC GCIH exam details matter here: most SEC504 packages include one GCIH exam attempt, but you should verify at purchase because SANS bundles change. Some packages include SEC504 practice tests (GIAC practice exams), some don't. Confirm the bundle contents during registration, not after.
If you want extra prep that's cheaper than a retake, you'll also see third-party options like the SEC504 Practice Exam Questions Pack at $36.99. It's not a replacement for the official SEC504 study materials and labs, but it can help you find weak spots fast when you're doing repetition the week before.
Extra costs people forget to plan for
Retakes. Miss the first try? An additional exam attempt typically runs $500 to $800. That number hurts, so plan for it even if you don't need it.
Proctoring fees can also show up, depending on testing provider and location, especially for remote proctoring. And if you're doing in-person training, travel and accommodation can easily add another chunk: flights, hotel, meals, local transport. All that stuff adds up faster than you'd think.
Discounts are real, though. Early registration discounts often land around $400 to $600 if you book weeks ahead. Government and military pricing can reduce cost with proper documentation. Multi-course discounts exist if you register for more than one class at once. Work-Study is the big one, often 50%+ off if you help with logistics during training, but you're trading time and energy for that discount. Academic pricing can apply for students and faculty via SANS Academic programs. Payment plans exist too, which is nice when you're fronting the cost personally.
GCIH exam expectations (passing score, format, difficulty)
GCIH's the certification tied to this course. What is the difference between SANS SEC504 and GIAC GCIH? SEC504 is the training. GCIH is the exam credential you earn after passing.
GIAC exams are commonly open-book and proctored, timed, and very index-friendly if you prepared right. What is the passing score for the GCIH exam? GIAC sets and can change the threshold, so check the official GCIH page for the current SEC504 passing score requirement.
How hard is SEC504 compared to other SANS courses? It's not the most math-y, but it is broad and speed-heavy, so if you're slow at reading packets or logs, that's where you'll feel it.
Budget planning and ROI (the real math)
If you're estimating total spend, I'd budget $7,000 to $9,000 for the course bundle, plus a "just in case" $500 to $800 retake line item, plus renewal planning. GCIH renewal requires fees every four years plus continuing professional education credits, so don't pretend it's a one-time cost.
Employer reimbursement's common. Most orgs that actually run a security team treat SEC504 as professional development, because the incident response readiness payoff is obvious when something breaks at 2 a.m. And ROI's usually there within 1 to 2 years if it helps you move into IR, detection engineering, or a higher-level SOC role, especially if you're pairing the class with focused practice like the SEC504 Practice Exam Questions Pack while you prep.
Tax deductibility can apply if you're paying out of pocket, but talk to a tax advisor. Seriously.
Quick take: is it worth it?
For the right person? Absolutely. You're paying for structured reps on real-world intrusion patterns, not motivational content, and that's why the SANS SEC504 certification path keeps showing up in job posts.
If you want to tighten your prep loop cheaply, the SEC504 Practice Exam Questions Pack is an easy add, but your main wins still come from the official labs, a solid index, and enough repetition that your brain stops freezing when the questions get wordy and you're racing the clock.
GIAC GCIH Exam Details and Requirements
What to expect when you register
The GIAC Certified Incident Handler (GCIH) exam is the certification test tied to SANS SEC504 training. This is not typical multiple-choice stuff where you wing it and pray for partial credit. The exam format is proctored, timed, and designed to validate that you actually understand incident handling, not just that you crammed a few flashcards the night before.
You are looking at somewhere between 106 and 150 questions. Different every time. GIAC adjusts the exact count based on psychometric analysis of each exam version. They constantly tweak things to maintain statistical validity, so the best move is checking the official GIAC website for the current number before you schedule. You will have 4 to 5 hours to work through everything, breaking down to roughly 2 to 3 minutes per question if you do the math.
Here is the thing that makes GIAC exams different: they are traditionally open-book, meaning you can bring your course materials, your notes, your lovingly crafted index, whatever you have prepared. But do not misunderstand what "open-book" means in this context.
Index prep is make or break
Creating a thorough, well-organized index is critical for open-book success. I have seen people spend dozens of hours building indexes with color-coded tabs, cross-references, and quick-lookup tables for command syntax. The kind of thing that would make a librarian weep with joy. Some folks go digital with searchable PDFs. The format matters less than the organizational logic. You need to find answers in seconds, not minutes.
If you show up thinking "it's open-book so I don't need to study," you are setting yourself up for a brutal time-management disaster. You will not have time to learn material during the exam. The index is there to jog your memory and confirm details, not to teach you incident response from scratch. I once watched a guy at a testing center flip through an unorganized three-inch binder for nearly ten minutes on a single question. He failed.
Passing thresholds and scoring
GIAC sets passing scores on a per-exam-version basis. No single magic number. Typically you are looking at needing 66% to 73% correct responses, but check the official GIAC GCIH page for the current threshold before you sit down. The scoring method is percentage-based, and some questions might carry different weights depending on difficulty, though GIAC does not publish the exact weighting formula.
The good news? Immediate provisional results. As soon as you click that final "submit" button, you will know whether you passed or failed. The official certification and digital badge typically show up within one to two weeks of passing, but you will walk out of that testing center (or close your browser if you are remote) knowing your fate right away.
Question styles you'll encounter
The difficulty sits somewhere between intermediate and advanced, mostly because of the sheer breadth of content combined with time constraints. You will face scenario-based questions that drop you into the middle of an active incident and ask what you would do next. Command syntax identification questions test whether you know the difference between nmap flags or PowerShell parameters. Log analysis interpretation is huge. You will see chunks of Windows Event Logs, Linux syslog entries, and network traffic captures that you need to parse quickly.
Questions focus on real-world application. Pure memorization will not cut it. For example, instead of "What port does HTTPS use?" you might get a pcap snippet showing TLS negotiation and be asked to identify the specific phase of the handshake or spot the anomaly. The exam balances both understanding attacker techniques and knowing the appropriate defensive responses. You need to think like both sides, which can mess with your head a bit.
Tool knowledge is required. Familiarity with Nmap, Metasploit, Wireshark, PowerShell, and the other tools covered in SEC504 will come up repeatedly. A significant portion is dedicated to log analysis across different platforms. Incident response workflow questions will test whether you understand proper procedures for each phase of the handling lifecycle: detection, containment, eradication, recovery, and lessons learned.
Proctoring logistics and policies
You have got two main proctoring options: Pearson VUE testing centers or remote online proctoring, though availability varies by region. Remote proctoring requires a webcam, microphone, quiet private space, and a system meeting specific technical specs. They are pretty strict about background noise and interruptions. Testing centers provide a professional environment with a provided computer, scratch paper, and strict security protocols. No phones. No smart watches. No bathroom breaks without ending your session.
Scheduling is usually pretty flexible. You can typically book within days to weeks of registration depending on availability. Rescheduling is allowed with advance notice (usually 48 to 72 hours), though you might incur fees for late changes. Your exam voucher is typically valid for four months from the issue date, but confirm the specific terms when you purchase.
Failed attempts? Retakable after buying another voucher. There is no mandatory waiting period. Special accommodations are available for candidates with documented disabilities, and the exam is primarily offered in English.
SEC504 Difficulty Level and Time Investment
What you're signing up for
The SANS SEC504 certification track? SANS basically took the gloves off. This is the hacker tools and techniques course that expects you to think like an attacker, then flip around and do incident handling and response training without losing the thread. Which, honestly, sounds cleaner than it actually feels when you're three days in.
Look, the SEC504 course overview is simple on paper: attacks, detection, and response. In practice, it feels like drinking from a firehose for six straight days, then realizing the GIAC exam cares whether you can find the exact command switch you used three labs ago. Short days? Not really. Long nights.
Difficulty level, honestly
My overall SEC504 difficulty level rating sits somewhere between intermediate and advanced. Newcomers can pass, but not by "reading the books and vibing" because the course pace is fast, the labs reward people who click around and break things, and the GIAC GCIH exam details include a time limit that punishes slow lookup habits even though it's open-book. The thing is, open-book doesn't mean easy when you're racing the clock.
Compared to other SANS classes? SEC504's more technical than SEC401 (Security Essentials) because you're doing real attacker workflows and then proving you can detect and contain them. It's also less specialized than FOR500 (Forensics), which goes deeper into forensics as a discipline, while SEC504 spreads the effort across a wider range of threat hunting and containment skills. Broad, sometimes annoyingly so. Useful anyway.
Deeper than Security+ and CEH, for sure. But it's broader than those "I only do malware reversing" type tracks. That breadth vs. depth challenge is the whole thing. You're not mastering one niche, you're building enough competence across Windows and Linux attack techniques, network intrusion detection fundamentals, triage, and communications that you can function during a real incident.
What makes it feel hard
The cognitive load doubles because you learn the offensive technique and the defensive response. I mean, one minute you're thinking about exploitation and persistence, the next you're parsing logs, scoping impact, and writing down what to tell leadership without sounding like you're guessing.
Command syntax trips people up. it's "know the tool," it's remembering the right switches across platforms, then being fast enough to retrieve it from your index when your brain blanks. Packet analysis? Similar deal. Reading pcaps fluently takes repetition, and if you haven't done much traffic work, you'll feel slow until you get more exposure.
Log analysis also bites. Interpreting logs quickly is pattern recognition, not magic, and SEC504 pushes you to build that muscle under time pressure. Which sounds reasonable until you're staring at your fifth consecutive Sysmon event trying to spot the anomaly.
Common struggle areas I keep hearing about: memory forensics, Windows registry analysis, and advanced PowerShell techniques. Not everyone hits all of those. But almost everyone hits at least one. Mixed bag, really. I spent an entire evening once just trying to understand why a particular registry hive was flagged as suspicious, only to realize I'd been looking at the wrong timestamp format the whole time. Stupid mistake, but that's how you learn.
The time investment (course week is intense)
SEC504 runs six consecutive days with 8+ hours of instruction, and yeah, you'll have evening lab work and reading assignments. Expect 10 to 12 hours daily during course week if you're serious about retention and not just attendance. Quick dinner. Back to labs. Repeat.
After the class, most candidates need 40 to 80 additional hours of review and practice. Some'll do it faster. Many won't. The reading volume's real too, over 1,500 pages of course books, so you need a systematic approach with notes and tabs, not random highlighting like you're studying for a history exam.
Index creation? Its own project. A thorough index usually takes 20 to 40 hours of focused organization, and it's the difference between "open-book comfort" and "open-book panic." I mean, you're not trying to build a novel. You're building a retrieval system.
Labs, practice, and the open-book reality
Hands-on skill focus isn't optional here. Passive reading's the fastest way to feel confident on Sunday and confused on exam day. Repeating the course labs 2 to 3 times helps a lot, because the second pass is where you stop following instructions and start understanding why the artifacts look the way they do.
If you want extra exam reps, SEC504 Practice Exam Questions Pack is a cheap way to pressure-test recall and index quality at $36.99. Not a replacement for the official stuff, but it can expose weak spots early. I'd rather find those gaps on a Tuesday night than during the real exam. Also, yes, SEC504 Practice Exam Questions Pack again if you're the type who needs structure to stay consistent.
Time management is the hidden boss
Course pace forces prioritization. The exam time limit forces efficient work habits. You need question triage, fast lookups, and the discipline to move on when you're stuck. Cramming the weekend before's a classic failure risk factor, along with a weak index and "I watched the labs" energy.
Success factors? Boring but true: do the labs, build a strong index, manage time, and keep a daily rhythm.
Background, support, and realistic timelines
Learning curve varies a lot. Security analysts with incident response experience find the material more intuitive than career changers. Strong networking and OS administration chops reduce the pain. If TCP/IP and Windows logging already feel familiar, you get to focus on higher-value thinking instead of basic translation.
Instructor support's usually solid during the course, and the SANS community forums, study groups, and alumni networks are helpful after. Study groups are underrated, honestly. You can swap index strategies, clarify weird points, and keep motivation up when you're sick of reading page 1,237.
Realistic timeline: most people can earn the SANS SEC504 certification within 2 to 4 months after the course with focused effort. Highly experienced practitioners sometimes do 2 to 4 weeks post-course with intense study, but that's not the median. That's the overachiever timeline.
Working pros usually manage 10 to 15 hours weekly for 8 to 12 weeks. Daily 1 to 2 hour sessions beat weekend marathons, honestly, because your brain stays warmed up and your index gets built steadily instead of in a stressful blur. If you're adding extra drills, SEC504 Practice Exam Questions Pack can slot into that routine pretty easily.
Best SEC504 Study Materials and Resources
The courseware is your foundation
The Official SANS SEC504 courseware? That's it. The single most critical resource you'll use. Everything you need to pass the GIAC GCIH exam lives in those books, and I'm not being dramatic here. SANS delivers typically 4-6 bound volumes organized by training day, each one absolutely stuffed with theory, real-world examples, and exercises that mirror what you'll actually face during incidents. The courseware covers all exam objectives comprehensively, from packet analysis to Windows registry artifacts to malware containment workflows.
These aren't light reading. Not gonna lie. Each volume corresponds to a training day and builds on the previous one, walking you through intrusion detection fundamentals, attacker methodologies, forensic triage steps, and response playbooks, all structured logically. The books become your open-book reference during the exam, so treat them like gold from day one.
How you mark up those books matters more than you think
Here's the thing people underestimate: your annotation strategy during the first read-through will make or break your exam experience. The GCIH's open-book, sure, but you've got limited time to find answers. Highlighting key definitions, tabbing major sections (protocols, attack signatures, tool outputs), and scribbling marginal notes creates a personalized index that's way faster than flipping randomly. You can't waste precious minutes hunting.
Start building your index early. Some folks use color-coded tabs. Blue for network concepts, red for Windows attacks, green for Linux, yellow for incident response phases. Others create a separate index document mapping topics to page numbers. Both work, honestly. The goal? Muscle memory. You should know instinctively that Metasploit payload encoding lives in Book 3, page 47, not waste three minutes hunting. I knew someone who got so obsessed with their indexing system they laminated custom reference cards and then couldn't use them because GIAC proctors flagged them as unauthorized materials. Learn from that mistake.
Lab practice is where concepts become skills
The lab workbook isn't optional supplemental material. It's where you actually learn this stuff. Step-by-step exercises walk you through using Wireshark to dissect malicious traffic, analyzing compromised hosts, and executing containment procedures with actual tools, not just theory. You'll work with virtual machines and simulated networks that recreate attack and defense scenarios realistically.
Complete each lab minimum 2-3 times. First pass you're just following instructions. Second time you start understanding why each command matters. Third time builds muscle memory and you'll recognize attack patterns faster, troubleshoot issues without constantly referencing notes. This repetition? Critical for exam speed and real-world incident handling readiness.
MP3 lectures let you absorb while multitasking
SANS includes MP3 audio recordings of the instructor lectures with most course packages, which are perfect for commutes or gym sessions when you can't actively read. Hearing the material explained verbally reinforces concepts differently than reading alone. The instructor anecdotes about real breaches stuck in my memory better than dry textbook descriptions, weirdly enough.
You won't learn everything from audio alone. But it's solid for review cycles and keeping material fresh between study sessions.
Practice exams tell you where you actually stand
The SEC504 Practice Exam Questions Pack at $36.99 gives you realistic question formats and time pressure simulation. GIAC practice tests (if included in your bundle) are the gold standard since they match the actual exam style most closely, though honestly, any timed practice helps. Work through these under timed conditions. Don't just casually browse answers.
Practice tests expose knowledge gaps you didn't know existed. Maybe you're solid on Linux log analysis but shaky on Windows Event IDs, or you understand attacks conceptually but can't identify them quickly in packet captures. Use practice results to target your lab repetitions and book reviews strategically.
Supplemental resources fill specific gaps
The official courseware's full, but sometimes you need different explanations for tricky concepts. Free resources like TCP/IP protocol references, Windows Event Log documentation from Microsoft, and Linux logging guides (rsyslog, auditd) can clarify confusion. The SEC504 course itself teaches these but outside references sometimes just click better.
Don't go overboard chasing third-party materials though. I've seen people waste weeks on random blog posts instead of drilling the official content, which is counterproductive. Stick with SEC504 (Hacker Tools, Techniques, Exploits and Incident Handling) courseware as your primary source and only branch out for targeted clarification.
Your study strategy determines exam performance
Build your index during the course week itself. Not during frantic pre-exam cramming. Run through labs repeatedly until commands feel automatic, use the practice exam pack to simulate test conditions and refine your lookup speed. The exam tests both knowledge and time management. You need both to hit the passing score.
Most failures? They aren't from lack of knowledge. They're from poor index organization or skipping hands-on practice. The materials are excellent, but you've gotta use them strategically.
Conclusion
Wrapping this up
Look, SEC504's legit. It actually delivers. The material's dense, labs are challenging, and honestly you'll probably feel overwhelmed around day three when you're juggling packet captures, Windows event logs, and trying to remember which Linux persistence mechanism maps to which MITRE ATT&CK technique. All while questioning if you've retained literally anything from the previous sessions. But that's kind of the point.
The GIAC GCIH exam that follows? Not a walk in the park either. You're managing a timed, open-book test where speed matters just as much as accuracy. If your index isn't dialed in you'll burn precious minutes flipping through six books trying to find that one PowerShell obfuscation technique you know you highlighted somewhere. Time management during the exam is brutal. I've seen people who knew the material cold still struggle because they couldn't triage questions fast enough or got stuck second-guessing themselves on scenario-based problems that pull from multiple domains at once. Network traffic analysis, host forensics, incident response workflow. All happening simultaneously.
Here's the thing, though.
If you're working in a SOC, on an incident response team, or trying to move into blue team work, the skills you pick up are immediately applicable. Not gonna lie, this cert has weight in the industry because employers know SANS doesn't hand these out for memorizing definitions. You're expected to actually understand attacker tradecraft, recognize indicators of compromise in real traffic, and coordinate response activities under pressure. That combination of offensive awareness and defensive execution? Rare and valuable.
The cost's significant, sure. You need to factor in the time commitment for both the course and exam prep. But the ROI shows up when you're the person in the room who can confidently walk through a breach timeline, explain what the attacker did and why, and recommend concrete containment steps that actually make sense for your environment.
I knew someone who passed GCIH on their second attempt. First time they walked in overconfident, figured the open-book format meant they could just reference everything on the fly. Tanked hard. Second round they treated it like a closed-book exam during prep, only using the books to verify answers, not hunt for them. Made all the difference.
Before you sit for the GCIH, give yourself every advantage. Official practice tests help, lab repetition's non-negotiable, and your index needs to be tested under exam conditions. You'll also want to drill with realistic question sets that mirror the exam's style and difficulty. The SEC504 Practice Exam Questions Pack is worth checking out as part of your final prep. It's designed to surface gaps and build the pattern recognition you need when the clock's ticking and you're staring at question 87 of 150.
Get after it. The certification's tough, but if you're serious about incident handling and response, SEC504 and GCIH belong on your roadmap.
Show less info
Hot Exams
Related Exams
ITIL 4 Foundation Exam
Ethical Hacking and Countermeasures V8
Certified Treasury Professional
Oracle EBS R12.1 Inventory Essentials
EC-Council Certified Secure Programmer (ECSP)
HDS CERTIFIED IMPLEMENTER - ENTRY LEVEL ENTERPRISE
Nuage Networks Virtualized Network Services (VNS) Fundamentals
Huawei Certified Pre-sales Specialist - Service Solution
Junos, Associate (JNCIA-Junos) Exam
Automating and Programming Cisco Security Solutions (300-735 SAUTO)
SAP Certified Associate - SAP Mobile Platform Native and Hybrid Application Administration (SMP 3.0)
Certified Associate in Project Management (CAPM) Certification
SAP Certified Application AssociateSAP IBP for Supply Chain (2302)
Oracle Database Administration II
IBM Watson IoT Maximo Solution Architect V1
Hacker Tools, Techniques, Exploits and Incident Handling
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.