ISC2 ISSEP Certification Overview
What you're actually getting with this credential
Look, the ISC2 ISSEP certification isn't for everyone, and honestly that's kind of the point. This is the ISSEP Information Systems Security Engineering Professional credential, and it's one of those concentration certifications that ISC2 offers after you've already earned your CISSP. You can't just walk in off the street and take this exam. You need that CISSP foundation first, which already tells you this is specialized territory.
The ISSEP focuses specifically on systems security engineering. We're talking about the folks who architect, design, and implement secure information systems from the ground up. Not the people managing security operations day-to-day, but the engineers who're building the actual security architecture that everything else runs on. It validates that you understand how to apply engineering principles throughout the entire system lifecycle, from initial requirements gathering all the way through decommissioning.
What makes this different from just being a security person who knows some engineering? The ISSEP proves you can integrate security requirements into complex system architectures using actual engineering methodology. You're expected to know NIST standards inside and out, understand the Risk Management Framework (RMF), and apply security engineering lifecycle (SDLC) principles in real-world scenarios. The certification recognizes you as someone who can handle the technical depth required for enterprise-level security engineering work.
I knew a guy who spent two years doing security operations before deciding he wanted to move into architecture. Smart guy, knew his stuff operationally. But when he started studying for the ISSEP, he realized how different the engineering mindset was from the operational one. He had to basically rewire how he thought about problems. Took him three attempts to pass, but he said it changed how he approached every project afterward.
Who actually needs this thing
Security architects are the obvious candidates. If you're designing enterprise-level security solutions and need to justify your architectural decisions to stakeholders who actually understand the technical details, the ISSEP gives you that credibility. I've seen architects use this credential to differentiate themselves when competing for high-level positions where generic security knowledge isn't enough.
Systems engineers working on secure system development and integration benefit too. Government contractors especially. If you're working on classified systems or sensitive government projects, the ISSEP's often listed as a preferred or required credential. The defense and intelligence communities recognize this certification because it fits with their frameworks and standards.
Security consultants advising on architecture and engineering best practices use it as proof they're not just theoretical. Chief Information Security Officers overseeing engineering teams sometimes pursue it to maintain technical credibility. Not gonna lie though, the exam's technical enough that some CISOs who've been in management roles for years find it challenging to pass without serious study time.
Then there's IT professionals transitioning from operational security into engineering roles. If you've been doing security operations work and want to move into architecture and design, the ISSEP can help make that career pivot more legitimate in the eyes of hiring managers.
How this differs from your CISSP
Here's the thing about the relationship between CISSP and ISSEP. They're not competing certifications, they're complementary. You literally can't get the ISSEP without holding an active CISSP first. The thing is, ISSEP's a concentration certification, not a standalone credential.
The CISSP covers broad security management topics across eight domains. It's a mile wide and an inch deep in many areas, which is fine because it's meant to cover the entire security field. The ISSEP goes deep on engineering specifically. Where CISSP might ask you general questions about secure system design principles, the ISSEP expects you to understand the detailed methodology for integrating security controls into system architectures based on NIST SP 800-160 and similar engineering standards.
Exam difficulty? Generally considered higher for ISSEP. The questions assume you've got that CISSP foundation and then build on it with much more technical engineering scenarios. Both certifications share CPE requirements and renewal cycles, which is convenient. You're maintaining both with the same continuing education activities.
Target audience size is way different too. CISSP has hundreds of thousands of holders worldwide. ISSEP? Much smaller, more specialized group. That specialization can work in your favor in certain job markets, particularly government and defense contracting where they specifically want security engineering expertise.
How ISSEP stacks up against other ISC2 concentrations
ISC2 offers three main concentration certifications beyond the base CISSP. There's ISSAP (Architecture Professional), ISSMP (Management Professional), and ISSEP. Each targets different career paths within security.
The ISSAP focuses on solution design and security architecture frameworks. ISSMP emphasizes leadership, governance, and security program management. ISSEP's the most technical of the three, addressing engineering methodology and technical implementation details. If you're more interested in the management side, ISSMP makes sense. If architecture frameworks are your thing, ISSAP. But if you want to prove deep technical engineering competency, ISSEP's where it's at.
I've talked to people who hold multiple concentration certifications, and they'll tell you the ISSEP requires the most hands-on technical understanding. The ISSMP can be passed by strong managers who understand security programs even if they're not deeply technical. ISSEP? I mean, you need to understand the actual engineering work. There's no getting around that technical depth requirement.
Where this certification actually matters
DoD 8570/8140 compliance is a big deal for ISSEP holders. Certain Information Assurance positions within the Department of Defense recognize this credential, which opens doors in military and defense contractor roles. Federal government agencies beyond DoD also recognize ISSEP for security engineering positions, especially those involving system accreditation and authorization work.
Defense contractors value the ISSEP heavily for proposal teams and technical lead positions. When you're bidding on government contracts, having ISSEP-certified engineers on your team can strengthen your proposal. It shows you're not just throwing generic security people at the problem. You've got actual certified systems security engineers.
Private sector acceptance is growing. As more commercial organizations adopt NIST frameworks and RMF processes, they're realizing that people with ISSEP credentials understand these frameworks at an implementation level. Enterprise architecture roles increasingly recognize the value, particularly in regulated industries like finance and healthcare where formal security engineering processes are becoming standard.
International acceptance varies but is growing. Organizations outside the US that adopt NIST frameworks or work with US government systems find value in ISSEP-certified professionals who can bridge the engineering methodology gap.
Career perks you actually get
Salary potential's better. Specialized certifications like ISSEP command higher compensation compared to general security certifications like Security+ or even CISSP alone. I've seen salary surveys showing ISSEP holders earning 15-20% more than CISSP-only holders in comparable roles, though obviously that varies by location and industry.
Differentiation in competitive job markets? Huge. When you're competing for a senior security architect or principal engineer role against other qualified candidates, having ISSEP can be the tiebreaker. It proves you've invested in specialized expertise beyond the baseline.
Credibility when proposing security architectures to stakeholders gets boosted considerably. When you're presenting a complex security architecture to a technical review board or government authorization officials, having ISSEP after your name signals that you know the formal engineering methodology they expect.
Professional networking through the ISC2 member community connects you with other specialized engineers. The ISSEP holder community's small enough that you can actually make meaningful connections with peers facing similar engineering challenges.
Some high-level security engineering positions list ISSEP as a prerequisite or strongly preferred qualification. Government and defense contractor positions especially. Without it, you might not even get past the initial resume screening for certain roles.
How this certification evolved
ISC2 launched the ISSEP to address a specific gap in the certification space. There were plenty of general security certifications and even some architecture-focused ones, but nothing that really validated systems security engineering expertise using formal engineering methodology. The certification aligned with NIST Special Publications and established systems engineering standards from day one.
The exam content gets updated periodically to reflect changing threats and engineering practices. Early versions focused heavily on traditional system development lifecycles. Modern versions incorporate cloud architecture, DevSecOps practices, and emerging technology considerations while maintaining that core systems engineering foundation.
Integration with frameworks like NIST RMF and the Cybersecurity Framework has become more prominent in recent years. The certification's adapted to address how security engineering applies to cloud environments, containerized applications, and continuous integration/continuous deployment pipelines. But that fundamental engineering discipline approach remains at the core, just applied to modern technology stacks instead of only traditional enterprise systems.
ISSEP Exam Details and Logistics
What this exam actually looks like
The ISC2 ISSEP certification exam is computer-based. Standard Pearson VUE setup, honestly. You register through ISC2, get authorized, then sit at a testing center like everyone else who's ever tackled a high-stakes IT cert. Quiet room. Proctor watching. Camera. You know the vibe.
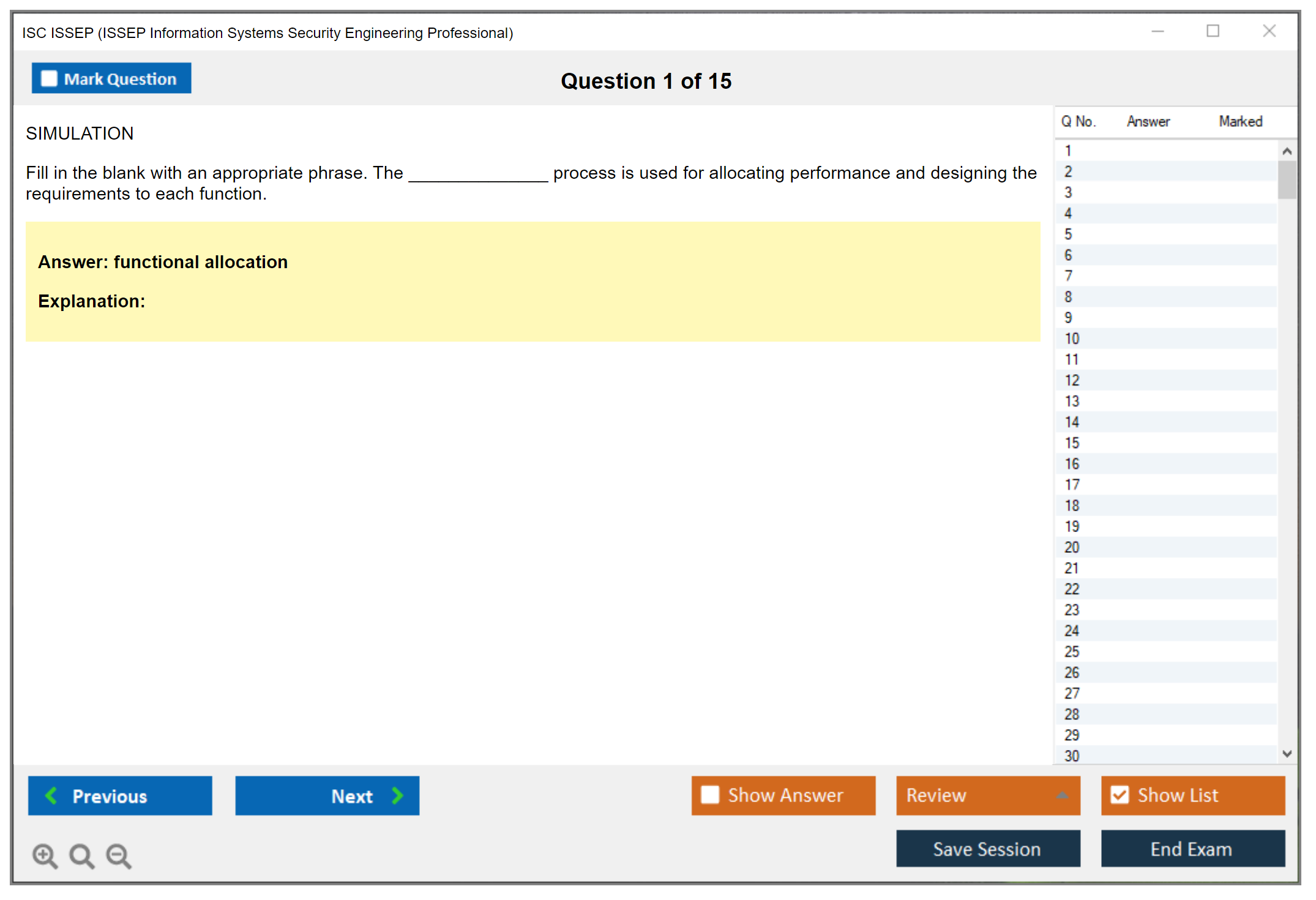
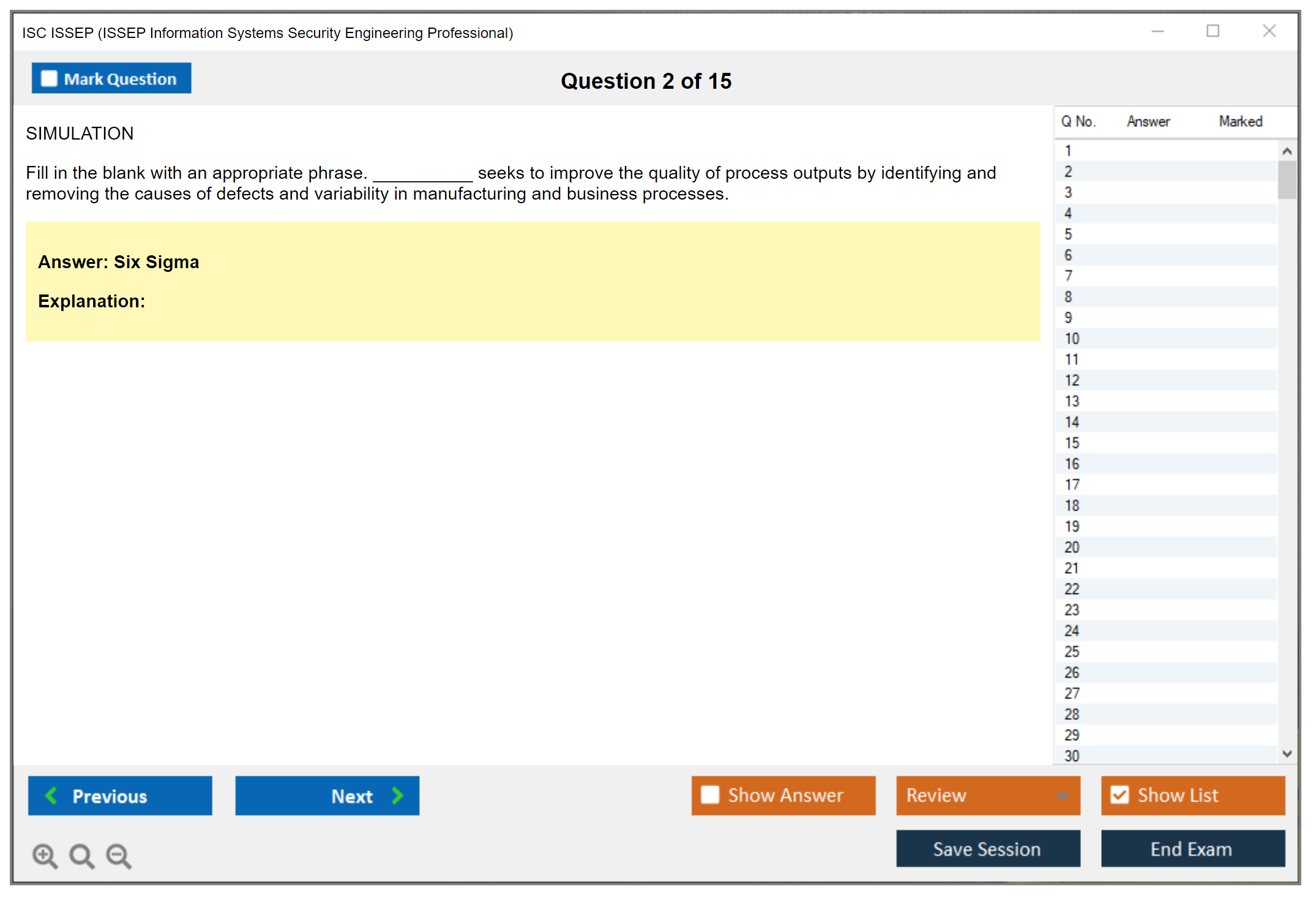
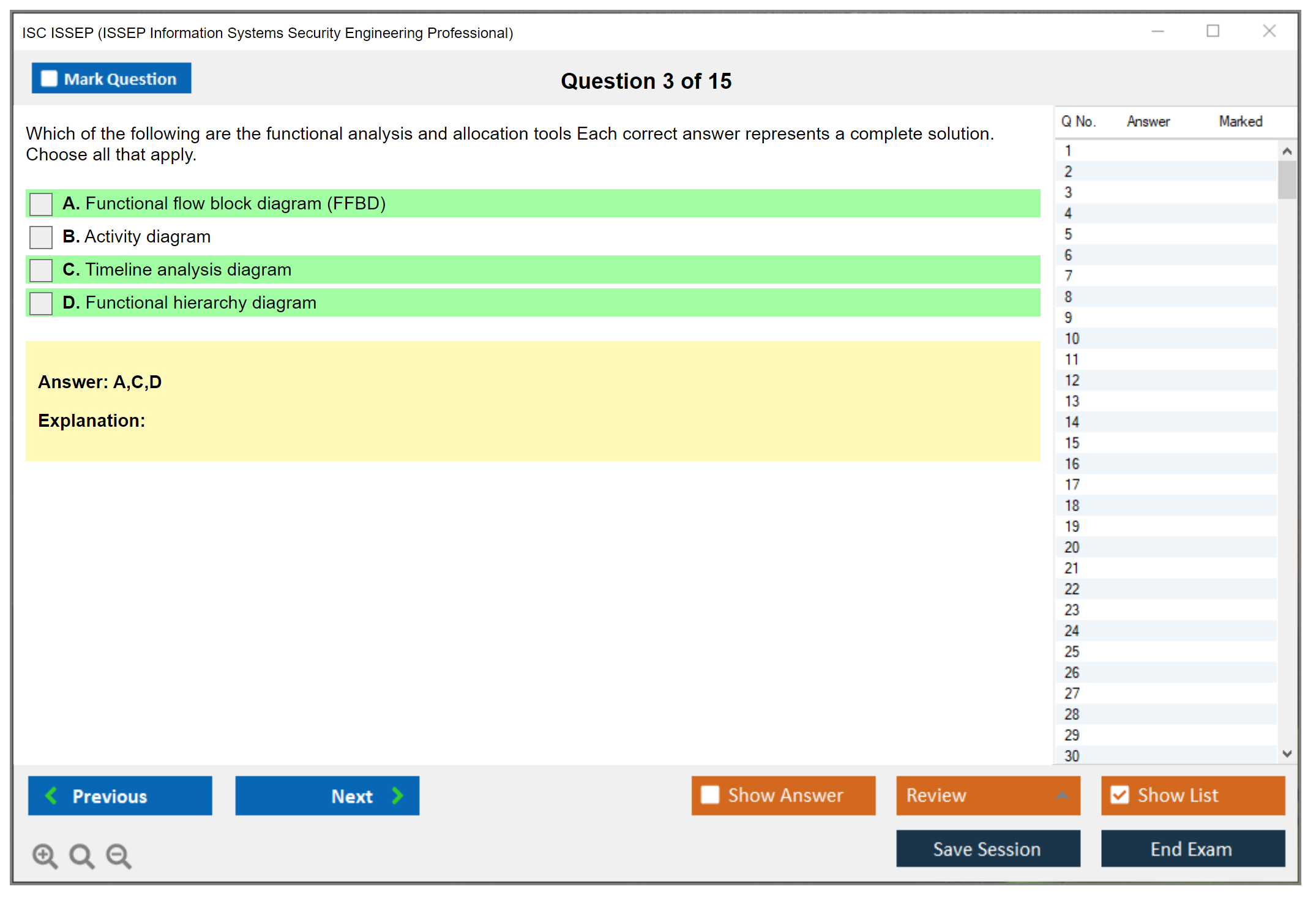
Format-wise it's straightforward on paper: 125 multiple-choice questions, four domains, three-hour time limit (180 minutes). That sounds generous until you realize the questions are scenario-heavy and you're constantly context-switching between engineering lifecycle thinking, governance constraints, and "best answer" judgment calls that'll make your head spin. Also, you have to sign a non-disclosure agreement before starting. No skipping that. No "I'll just click later" nonsense. It's part of the deal.
English is the default exam language. There can be translations in select languages, but don't assume it. Check what ISC2 and Pearson VUE list for your region because showing up expecting your preferred language and getting English instead? That's a bad day.
No penalty for guessing. Answer everything. Seriously. Leaving blanks is just donating points.
How the questions mess with your brain
Most questions are scenario-based, and they're written to force analysis and application, not recall. If you're hoping for "what port does X use" style trivia, look, wrong exam. You're being tested like a systems security engineering certification candidate, not some security trivia champion.
A common pattern? Multi-concept integration inside one question. You'll see a system described, a lifecycle phase implied, some constraints like mission needs or compliance requirements, and then you're asked what you should do next or which approach is best. Distractors aren't dumb. They're often things that are technically true but wrong for the scenario, wrong timing, wrong authority, or wrong tradeoff.
Some items basically ask you to prioritize. Not "what's correct" but "what's most appropriate right now". That's where people melt down, because multiple answers can feel defensible. The exam wants the option matching engineering discipline and governance reality.
Expect references in spirit, and sometimes in wording, to NIST publications, frameworks, methodologies. The NIST RMF and security controls mindset shows up constantly, and if you don't have comfort with the way NIST talks about categorization, selection, implementation, assessment, authorization, monitoring, you'll feel behind the whole time. You don't need to memorize publication numbers like some robot, but you do need to think in those structures. I once watched a colleague fail because he kept treating NIST documents like suggestions instead of the actual framework the exam expects you to work within. That's not a minor gap.
Short version? Higher-order thinking. Lots of "best answer" scenarios. Minimal freebies.
Exam cost and what people forget to budget
The standard exam fee is commonly listed as $699 USD for ISSEP, but it's subject to change, so verify current pricing on the ISC2 site before you expense it or pitch it to your boss. There may be an ISC2 member discount depending on your membership status and whatever promotions are running, but don't build your plan on a discount you haven't confirmed yet.
Retakes cost the same as the initial exam fee if you fail. That's not a scare tactic, that's just math. So your "ISC2 ISSEP exam cost" isn't just the fee. It's also the risk of paying it twice.
Then there's the hidden pile:
- ISSEP study materials, which can be cheap or weirdly expensive depending on what you buy
- training courses if you're the type who needs structure
- ISSEP practice tests, which are limited compared to CISSP and can be hit or miss
- time off work if you're doing deep prep
ISC2 official training often lands in the $2,000 to $3,500 range. Not gonna lie, that price makes sense for corporate budgets and feels wild for self-pay. If you want complete preparation including paid content, a realistic total budget is often $1,500 to $4,000 all-in, depending on how much you already know and whether your employer is covering it.
Employer sponsorship is common. Especially for folks already in security engineering, federal contracting, or roles tied to system authorization work. ROI can be very real, too. A passed ISSEP can translate into better roles, better billing rates, better salary bands. It's not magic, but it's a strong signal if your work actually matches the concentration.
Passing score and how scoring really works
ISC2 uses scaled scoring. Passing is 700 out of 1000. That number is real, but it's not a percentage and it's not "70% correct" in a clean way.
Scaled scoring exists because different exam forms have different difficulty mixes, and the scoring model normalizes that. So you can't calculate a raw-score equivalency from the scaled score. People try. People fail. Don't waste the energy.
Unofficially, you'll hear estimates like "around 70% correct" as a rough feel, but ISC2 doesn't disclose the exact raw score requirement. Treat any hard number you see online as speculation.
You get preliminary results at the test center right after finishing. If you fail, your score report includes domain-level performance diagnostics showing where you were weak. It won't tell you what you got right or wrong, and it won't tell you how close you were. It's more like "here's where to fix your gaps".
Why ISSEP feels harder than CISSP
The ISSEP exam difficulty is a real talking point because many people coming from CISSP expect a similar vibe. Honestly? It's usually tougher. Not because the interface is harder or because it's trickier English, but because the focus is narrower and deeper, and the exam expects you to think like a systems security engineer inside an engineering organization.
CISSP is broad. ISSEP is opinionated. It lives in the security engineering lifecycle (SDLC) space and expects discipline around requirements, architecture, design tradeoffs, verification, validation, lifecycle governance.
A few things crank up the difficulty. Breadth of NIST Special Publications implied by the exam objectives. Integration of risk management framework thinking with engineering lifecycle decisions. Complex scenarios requiring synthesis across domains. Government and DoD-flavored standards and expectations showing up as assumptions. Limited availability of official practice questions, which makes calibration harder. Ambiguity, where multiple answers feel "fine" but only one is best.
Also, the candidate pool is smaller. So there are fewer shared war stories, fewer high-quality third-party question banks, fewer "here's exactly what I saw" hints floating around. That's good for exam integrity. It's annoying for candidates though.
Time pressure is sneaky. Three hours sounds like a lot, but long scenario questions can eat minutes fast, and you still have to stay sharp enough to catch the distractor that's wrong because it violates process order or engineering accountability.
Scheduling, registration, and exam-day reality
You register through ISC2, and you typically need to confirm your CISSP status is active since ISSEP is a CISSP concentration. After registration, you'll receive an eligibility or authorization email that lets you schedule with Pearson VUE.
Book at least two weeks out if you want your preferred testing center and time slot. Some locations fill up, especially around common deadlines and end-of-quarter training pushes.
Rescheduling and cancellation follow ISC2 and Pearson VUE policies, and yeah, fees can apply. Read the policy before you click purchase. Past-you won't rescue future-you.
Exam day is standard Pearson VUE procedure. Bring a valid government-issued photo ID. Arrive 30 minutes early because check-in can take time.
Inside the testing room, personal items aren't allowed. Bags, phones, watches, random paper. All of it goes in a locker. They provide scratch paper and a pencil. Optional breaks exist, but the clock keeps running, so don't treat breaks like free time.
There's usually a computer-based tutorial before the timed portion begins. Use it if you've never taken a Pearson VUE CBT, otherwise skip and bank the mental energy.
Finish the exam, submit, and you'll see the preliminary result right there. Then you'll get the official notification afterward through ISC2.
That's the logistics. The rest is preparation and mindset. And yeah, for ISSEP, mindset is half the fight.
ISSEP Exam Objectives and Domain Breakdown
How the exam blueprint actually works
Look, the ISSEP exam's chopped into four major domains covering the entire systems security engineering lifecycle. ISC2 publishes exact percentages for each domain, and honestly, this is one of those certs where you can't just cram the heavy-weighted sections and hope for the best. The domains bleed into each other constantly.
Domain 3 (Security Planning, Design, and Implementation) is the heavyweight at 35% of the exam, which makes sense because that's where the rubber meets the road. Domain 4 (Secure Operations, Maintenance, and Disposal) comes in at 30%, Domain 2 (Risk Management and Frameworks) sits at 20%, and Domain 1 (Systems Security Engineering Foundations) rounds it out at 15%. But here's the thing: a single question might touch on risk management principles while also testing your knowledge of secure design patterns and operational monitoring. These domains aren't neat little boxes you can study separately and call it done.
I've seen people fail this exam because they studied each domain in isolation. I mean, that's not how systems security engineering works in the real world, and it's definitely not how ISC2 writes these questions. You need to understand how requirements flow from stakeholder analysis through design, implementation, and into operations. If you're also prepping for something like the CISSP or CISSP-ISSAP, you'll notice the ISSEP goes way deeper on the engineering process itself.
Systems security engineering foundations (15%)
Small domain. Big consequences.
This domain feels small at 15%, but it sets the foundation for everything else. You need to know systems engineering fundamentals cold. Lifecycle models, stakeholder requirements definition, that whole mess. The exam expects you to understand systems thinking, not just security thinking. What's the difference? Systems thinking means you're considering the entire system context, all the interfaces, all the trade-offs between security, functionality, cost, and schedule.
ISO/IEC 15288 is the systems engineering lifecycle standard that underpins a lot of this domain, while NIST SP 800-160 Vol 1 and Vol 2 are basically required reading because they translate systems engineering concepts into security engineering guidance. I mean, you could probably pass without memorizing every page, but you need to understand how security gets woven throughout the lifecycle, not bolted on at the end.
The exam'll test you on security design principles. Least privilege, defense in depth, fail secure, separation of duties, all that foundational stuff. But it's "what is least privilege?" It's more like "given this system architecture with these constraints, which design principle should take priority and why?" You'll see questions about secure design patterns and anti-patterns. You need to recognize when a design's fundamentally broken from a security perspective.
Component integration and interface security are huge here. Systems don't exist in isolation. Every interface is a potential security boundary, and the exam wants to know if you understand how to identify, document, and secure those interfaces. CMMI for security might come up too, though it's less emphasized than the NIST guidance. I once watched a colleague completely miss the interface security angle on a project, and by the time we caught it during the assessment phase, the rework cost was brutal.
Risk management and frameworks (20%)
This domain's where a lot of ISSEP candidates already have experience, especially if they've worked on federal systems or defense contracts. The NIST Risk Management Framework's central to this section. You need to know all six steps: Categorize, Select, Implement, Assess, Authorize, and Monitor. But knowing the steps isn't enough. You need to understand the artifacts, the decision points, the feedback loops that make the whole thing actually work in practice.
FIPS 199 security categorization is where it all starts. You're determining the impact levels (low, moderate, high) for confidentiality, integrity, and availability. Then FIPS 200 gives you the minimum security requirements. Then you're selecting controls from NIST SP 800-53, starting with the baseline for your impact level and tailoring from there. The thing is, the exam loves questions about tailoring. When to add controls, when to compensate, when to accept residual risk.
NIST SP 800-53A covers security control assessment procedures, and you need to understand how assessments feed into the authorization decision. The Authorization to Operate (ATO) process's all about documenting risk, getting the authorizing official to accept that risk, and then maintaining that authorization through ongoing monitoring. Look, continuous monitoring isn't just a buzzword here. It's an entire operational philosophy that connects back to Domain 4.
Threat modeling's another big piece. You should be familiar with multiple approaches. STRIDE, PASTA, attack trees, whatever works for the context. The exam isn't usually asking you to perform a detailed threat model, but you need to know when and how threat modeling fits into the risk management process. Same with vulnerability assessments. How do they slot into risk assessments? How do you translate vulnerability scan results into risk decisions that executives can actually act on?
Supply chain risk management has gotten way more attention in recent revisions, probably because of all the high-profile supply chain attacks we've seen. You need to understand third-party risk, vendor assessments, and how supply chain considerations flow through the entire lifecycle. If you're studying for CSSLP or CAP alongside ISSEP, there's definitely some overlap in this area.
Security planning, design, and implementation (35%)
This is the big one.
More than a third of your exam score comes from this domain, and it covers an enormous amount of material. Security requirements engineering's where it starts. You're eliciting requirements from stakeholders, documenting functional and non-functional security requirements, and maintaining traceability throughout the lifecycle. Requirements traceability's a big deal. If a requirement changes, you need to track that impact through design, implementation, testing, and operations.
Security architecture design's probably the deepest topic in this domain. You need to understand reference architectures, design patterns, Zero Trust concepts, defense-in-depth strategies, network segmentation, secure enclave design. All of it. The exam'll give you scenarios and ask you to make architectural decisions. Should you segment this network? How should you implement authentication? What's the right cryptographic approach for this use case?
Cryptographic architecture and key management are tested in detail. Not just "what algorithm should you use" but "how do you architect a key management system that scales across multiple security domains?" Identity and access management architecture's similar. it's about the controls, it's about how you design IAM services that integrate with the broader system.
DevSecOps and secure development lifecycle integration are increasingly important these days. The exam expects you to understand how security gets automated and woven into CI/CD pipelines. Security testing throughout the development lifecycle. Static analysis, dynamic analysis, penetration testing. When does each type of testing make sense? That's what they're really asking.
Configuration management and change control from a security perspective are huge. Every change has security implications, and you need to understand how to assess those implications, document them, and manage security baselines. The System Security Plan (SSP) is the primary security documentation artifact, and you should understand what goes into an SSP and how it relates to other system documentation.
Cloud security architecture has become more prominent, which honestly makes sense given where the industry's going. You need to understand shared responsibility models, how security controls map to cloud environments, virtualization security, container security, orchestration platforms like Kubernetes. Mobile and endpoint security architecture round out this domain. If you've got experience with CCSP, some of these cloud concepts'll feel familiar, though ISSEP approaches them from more of an engineering perspective.
Secure operations, maintenance, and disposal (30%)
Operations is where your beautiful security architecture meets reality, and reality's always messier than the design docs suggest. This domain covers how security gets operationalized, monitored, maintained, and eventually decommissioned. Security operations center (SOC) integration's a big topic. How does your system architecture support SOC operations? What telemetry do you need to provide? How do you design logging and monitoring that actually enables effective security operations?
SIEM integration, vulnerability management, patch management, configuration drift detection. These're all operational concerns that need to be considered during design and implementation. The exam'll test whether you understand how operational security requirements influence architectural decisions. Continuous monitoring comes up again here, but now it's about the actual implementation. What tools, what processes, what metrics?
Security metrics and key performance indicators are tricky because they bridge technical and management concerns in ways that make both groups uncomfortable. You need to understand what makes a good security metric, how to measure security posture, how to report security status to different stakeholder audiences. Compliance monitoring and reporting tie back to Domain 2. You're demonstrating that controls are operating as intended and that risk remains acceptable.
Change management and security impact assessment are constant operational activities. Every patch, every configuration change, every system update needs a security lens. Regression testing after security updates's something people often overlook, but it's on the exam. You can't just apply a patch and walk away. You need to verify that security functionality still works.
Disaster recovery and business continuity integration are about resilience. Can your system actually survive the bad day you designed it to survive? How do you design systems that can recover from security incidents? What're the backup and recovery security requirements? High availability architecture has security implications. Redundancy can improve security or create new attack surface depending on how it's implemented.
System decommissioning and disposal are the end of the lifecycle, but they can't be an afterthought. Data sanitization standards, media destruction requirements, asset disposal procedures. These all need to be planned from the beginning. End-of-life planning for security systems's particularly tricky because you might have security dependencies that outlive the system itself.
For anyone serious about passing this exam, quality practice materials matter. The ISSEP Practice Exam Questions Pack is worth checking out because it helps you understand how ISC2 actually asks these questions. The domains're interconnected, and practice questions that span multiple domains are the most valuable for prep.
ISSEP Prerequisites and Eligibility Requirements
Quick take on what this cert is
The ISC2 ISSEP certification is ISC2's concentration for folks who already speak CISSP and now live in engineering land. Think security requirements, architecture tradeoffs, system lifecycle decisions, and proving you did the work, not just talking about it.
Look, if your day job involves shaping systems before they ship, writing security specs, reviewing designs, mapping controls to real implementations, and arguing with engineers about constraints, this is your lane. If your whole week's tickets, alerts, and "please reset the VPN," you can still grow into ISSEP, but you're not there yet.
Who it fits (and who it doesn't)
Some roles line up naturally with ISSEP Information Systems Security Engineering Professional. Security architects. Systems engineers with security ownership. Cloud folks doing real design work.
Others.. not so much.
SOC analyst work alone usually won't cut it. Same for pure compliance checklists where you never touch design choices or implementation detail. Different skills. Different proof.
CISSP is non-negotiable
Here's the part that trips people up: the mandatory CISSP prerequisite requirement is real, and it's strict.
Active CISSP certification required before applying for ISSEP. Period. Not "I passed the CISSP exam and I'm waiting." Not "I'm basically doing CISSP stuff." You need the credential in hand, active, and in good standing.
Good standing means your CISSP must be current with CPE requirements. CPEs filed. AMF paid. No weird suspension situation. Honestly, ISC2 isn't trying to be mean here. They're trying to ensure a baseline security management competency before specialization, because ISSEP assumes you already understand governance, risk, and the security program view of the world.
Associate of ISC2 status doesn't qualify for ISSEP pursuit. That one stings for some people. Associate's great for getting started, but ISSEP is an advanced add-on, and ISC2 treats it like "prove you're already CISSP, then prove you're an engineer."
CISSP provides foundational knowledge for the concentration. You'll feel that in the exam too, because the ISSEP exam expects you to translate CISSP-ish concepts into engineering artifacts, lifecycle decisions, and security architecture and design engineering that holds up under scrutiny.
The ISSEP work experience requirement (the real eligibility gate)
Minimum two years cumulative work experience in systems security engineering. Not "security work" broadly. Not "IT work." Systems security engineering.
Experience must be within last 10 years of application. So if you did amazing engineering work 15 years ago and spent the last decade in management only, you may have a gap to close.
Full-time or part-time employment acceptable, with hours calculated proportionally. So yes, contracting counts. Part-time counts. Mixed roles count. But you need enough real engineering time to add up.
What matters is security architecture, design, implementation. That means actual system design inputs, requirements, engineering reviews, security control selection tied to a system, threat modeling that changes the design, and implementation guidance that engineers follow. Not a slide deck that vanishes after the meeting. Evidence matters.
Systems engineering roles with security responsibilities qualify, and this is where a lot of candidates come from. If you were doing systems engineering and you owned security requirements, security control integration, or verification steps, that's often strong ISSEP experience.
Security consulting focused on engineering principles counts too, as long as you can describe what you produced and how it impacted the system. Government or defense contractor security engineering positions work well, mostly because those environments tend to produce documentation trails and clear mappings to NIST RMF and security controls.
Experience must show direct application of security engineering principles. That phrase is your north star when you write your application. If you can't describe the engineering decision you made, the constraint you handled, and the output you delivered, you're probably describing operations or management instead.
What qualifies (examples that usually map well)
Here are qualifying work experience examples and acceptable roles. Not all are equal. A couple are "slam dunk" if you can document them well.
Security architect designing enterprise security solutions works great when you can tie architecture to requirements, reference architectures, control selection, and implementation patterns across systems. Add how you validated designs in the security engineering lifecycle (SDLC).
Systems engineer integrating security into system development. Also strong. Especially if you did security requirements decomposition, secure interface definitions, verification planning, or design reviews with engineering teams.
Security consultant performing architecture reviews and design. Works when it's more than opinions. Like you produced findings mapped to controls, proposed designs, and followed through to implementation decisions.
Technical lead implementing security controls in complex systems. Mention it, but be ready to show the engineering part, not just "I deployed tool X."
Risk management professional applying RMF to system authorization. This can qualify if you're doing real RMF work that influences system design, control implementation detail, and ongoing authorization evidence, not just pushing paperwork. I once worked with someone who got hung up on this distinction for weeks, actually. He kept saying his RMF work should count until someone finally asked him to name one design decision that came out of his assessment process. Couldn't do it. That's when it clicked for him.
Others that work:
- Security engineer developing secure system specifications
- Solutions architect incorporating security requirements
- DevSecOps engineer automating security in development pipeline
- Cloud security architect designing secure cloud environments
- Network security engineer designing secure network architectures
The theme's consistent. Design, architecture, engineering outputs, and SDLC touchpoints.
What does not qualify (common misunderstandings)
Pure security operations or SOC analyst work insufficient. It's valuable work, and it builds instincts, but ISSEP's looking for engineering.
General IT administration without engineering focus. Same deal. If you were patching servers and managing accounts, that's not systems security engineering certification territory.
Security awareness training delivery alone. Compliance auditing without technical implementation. Security management without hands-on engineering. Help desk or technical support roles. All respectable, all real, just not aligned with the "design and build secure systems" requirement.
Experience must involve design, architecture, or engineering aspects. If you're trying to pivot from ops to engineering, start volunteering for design reviews, threat modeling, requirements writing, reference architecture work, and RMF control implementation planning. That's the kind of work you can later describe cleanly.
Endorsement: how ISC2 validates you
Submit application through ISC2 online portal. Then you provide detailed work experience descriptions. Not vague. Dates, scope, what you did, what artifacts existed, how it mapped to ISSEP expectations.
Next, identify ISC2 member in good standing as endorser. Endorser reviews application and validates experience claims. The endorser doesn't need ISSEP, just CISSP or other ISC2 certification.
Alternative: ISC2 staff endorsement if no member endorser available. It's slower sometimes, and you should expect more scrutiny because you're basically asking ISC2 to do the validation work an endorser usually does.
Endorsement typically completed within 4-6 weeks. May request additional documentation or clarification during review. That's normal. Don't panic. Answer clearly, keep it engineering-focused, and don't fluff your role.
What documentation you should have ready
Application documentation requirements are pretty standard, but candidates get sloppy here.
You need detailed employment history with dates and responsibilities. Specific examples of security engineering work performed. Supervisor contact information for verification if needed. Educational background and degrees if you have them. Other professional certifications held. Agreement to ISC2 Code of Ethics. Consent to audit of credentials and experience.
Fragments help here.
Projects. Deliverables. Review boards. Control matrices. Architecture diagrams. Change records.
Background checks, audits, and why lying is career suicide
ISC2 reserves right to verify employment claims. Random audits of applications conducted regularly. False information grounds for application denial or revocation.
Professional references may be contacted. Educational credentials may be verified with institutions. Maintain documentation proving experience for potential audit. Honestly, keep a personal folder with offer letters, role descriptions, project summaries you wrote, and sanitized artifacts that prove what you did, because six months later you'll forget details and your old manager might be unreachable.
Timeline: from application to certified
Application submission to endorsement: 4-6 weeks typically. Schedule exam after endorsement approval received.
Pass exam and receive provisional certification immediately, then official certification awarded after endorsement wraps. Total timeline: 2-4 months from application to full certification. Expedited processing not typically available, so plan around work travel and busy quarters.
Costs you should plan for (not just the exam)
People fixate on the exam fee, then get surprised later.
Annual Maintenance Fee (AMF) for ISC2 membership matters. AMF covers all ISC2 certifications held (CISSP + ISSEP). Current AMF approximately $125 annually (verify current rate). Also, CPE submission fees if using non-ISC2 activities can pop up depending on how you report, and renewal audit documentation costs if selected can be annoying, even if it's just time and admin overhead.
If you're budgeting for prep, a practice product can be a sane line item. I've seen people pair official references with ISSEP Practice Exam Questions Pack because they want repetition and feedback, not just reading. The thing is, if you're the "learn by doing questions" type, ISSEP Practice Exam Questions Pack at $36.99 is cheaper than burning another month second-guessing yourself.
Special circumstances: accommodations and sponsored paths
Testing accommodations available for disabilities, but you must request accommodations through ISC2 before scheduling. Documentation of disability may be required, and it can take time, so don't wait until the week you want to book the exam.
Language translation services limited, so verify availability. Military and government personnel may have sponsored programs. Ask your training office. Ask your contract PM. Stuff exists, but it's not always advertised.
A few exam-adjacent notes people ask anyway
ISC2 ISSEP exam cost: ISC2 changes pricing, so verify on the official site, but don't ignore the AMF because that's the recurring cost that follows you. ISSEP passing score: ISC2 typically doesn't publish a simple numeric passing score for every exam format the way people want, so treat it like "meet the standard," not "hit 700." ISSEP exam difficulty: it feels harder than CISSP if you never did engineering lifecycle work, and it feels fair if you live in SDLC, NIST RMF and security controls, and architecture tradeoffs daily.
ISSEP study materials and ISSEP practice tests matter because this exam punishes hand-wavy knowledge. Read the ISSEP exam objectives, map them to what you've actually done, then close gaps with references and targeted practice like ISSEP Practice Exam Questions Pack if you need more reps under time pressure.
FAQs people always ask
How much does the ISC2 ISSEP exam cost?
ISC2 updates exam pricing, so check the official ISC2 listing, then add AMF (around $125 yearly, verify current rate) because you'll pay that to keep CISSP + ISSEP active.
What is the passing score for the ISSEP exam?
ISC2 doesn't always give a single public "passing score" number you can game, so focus on mastering the ISSEP exam objectives and being consistent across domains.
How hard is the ISSEP compared to CISSP?
Harder if your background's ops or management only. More straightforward if you've done security architecture and design engineering work across the security engineering lifecycle (SDLC) and can explain why a control or requirement exists.
What are the ISSEP prerequisites?
Active CISSP in good standing, with CPE compliance, plus at least two years of systems security engineering experience in the last 10 years, then endorsement through an ISC2 member or ISC2 staff.
How do you renew ISSEP and how many CPEs are required?
ISSEP prerequisites and renewal tie back to ISC2's certification CPE renewal requirements, AMF payments, and audit readiness. Since ISSEP's a CISSP concentration, plan your CPEs like a professional habit, track proof, and submit on time so "good standing" never becomes a problem.
Best ISSEP Study Materials and Resources
Look, if you're chasing the ISSEP certification, you already know this isn't like studying for entry-level certs. The ISC2 ISSEP exam tests deep engineering knowledge, and honestly, the study materials space is sparse compared to what you get with CISSP or even CCSP. This makes prep harder but also means you need to be strategic about what you use.
What ISC2 actually gives you
The official ISC2 ISSEP Common Body of Knowledge is your starting point. Period. This document outlines all four domains and tells you exactly what ISC2 expects you to know. Download the exam outline from the ISC2 website. It's free and breaks down the percentage weighting for each domain. You'd be surprised how many people skip this step and then wonder why they're studying the wrong stuff.
ISC2 member resources include webinars on security engineering topics, though they're not always ISSEP-specific. If you're already a member through another cert like SSCP, dig through their recorded sessions. Some of them cover systems security engineering concepts that directly map to ISSEP domains.
The big limitation? ISC2 doesn't pump out tons of official ISSEP materials because the market's smaller. They've got official practice questions available through their platform, but the pool isn't huge. Compare that to CISSP where you can find official practice exams everywhere. For ISSEP, you're working with maybe 50-100 official questions if you're lucky.
Training courses that actually matter
ISC2's five-day instructor-led training is the gold standard here. Costs what, $2,500-$3,500? Depends on format and location. Not cheap but it covers all four domains in a systematic way. You get official courseware, some practice questions bundled in, and access to ISC2-authorized instructors who've actually passed the ISSEP themselves.
They offer self-paced online training modules too. Video lectures you can watch at 2x speed when the instructor's dragging through basic concepts. Virtual instructor-led training is the middle ground. Remote participation with live interaction, useful if you learn better with real-time Q&A.
Here's the thing: the training isn't mandatory. But I'd recommend it if you don't have a strong engineering background or if you're coming from pure admin or analyst roles. The structured learning helps. Plus networking with other candidates gives you study partners who understand the pain. One guy I know from a training session ended up being my study buddy for three months, and we both passed. Actually reminds me of when I was studying for my driver's license years ago and this random person at the DMV became my practice parallel parking coach, which has nothing to do with ISSEP but sometimes the most useful connections come from weird places.
NIST publications you can't ignore
NIST SP 800-160 Volumes 1 and 2 are essential. Volume 1 covers systems security engineering fundamentals. This is the framework ISSEP questions pull from. Volume 2 goes into cyber resiliency engineering, which shows up in Domain 3 and 4 questions more than you'd expect.
You also need NIST SP 800-37 (Risk Management Framework), SP 800-53 (Security and Privacy Controls), and SP 800-30 (Risk Assessment). These aren't light reading. SP 800-53 alone is hundreds of pages of control families and implementation guidance. But here's what I did: I didn't read them cover to cover. I focused on understanding the RMF lifecycle phases and how controls map to engineering requirements. That's what the exam tests. Application, not memorization.
NIST SP 800-64 on security considerations in the system development lifecycle is another one. Shorter, more digestible, directly relevant to Domain 3. If you're working in federal contracting or government systems, you've probably already used these. Even if you have, budget serious time to get comfortable with NIST's language and frameworks because the exam's gonna test how well you apply this stuff, not just whether you've skimmed it once.
Books and third-party resources
This is where it gets frustrating.
No "ISSEP Official Study Guide."
There's nothing like other certs have. You're cobbling together materials from systems engineering books, security architecture references, and engineering lifecycle documentation.
The INCOSE Systems Engineering Handbook is worth grabbing if you can afford it. It's not security-focused but covers systems engineering principles that underpin Domain 1. Same with "Systems Security Engineering" by Schaeffer. Dense, academic, but maps well to what ISSEP expects.
For practice questions beyond the official ISC2 offerings, the ISSEP Practice Exam Questions Pack at $36.99 gives you additional exposure to question formats and domain coverage. I used it to identify weak areas in Domain 2 (Risk Management) where I kept confusing quantitative versus qualitative analysis approaches. The explanations helped more than the questions themselves sometimes. They'd walk through why wrong answers were tempting but technically incorrect.
Study strategy that worked for me
I built a 10-week plan. Weeks 1-2 were just reading the CBK and NIST SP 800-160 Vol 1. Weeks 3-6 covered one domain per week with deep dives into relevant NIST pubs. Week 7 was pure practice questions. Official ISC2 ones first, then the practice pack I mentioned. Weeks 8-9 were review cycles where I went back to weak domains. Week 10 was light review and mental prep.
The hardest part is that ISSEP questions aren't just "what is X?" They're scenario-based. "Given this system architecture and these requirements, what's the most fitting engineering approach?" You need to think like an engineer, not just recall definitions.
If you're also considering other ISC2 concentrations, know that CISSP-ISSAP focuses more on architecture while ISSEP is pure engineering. CISSP-ISSMP is management-heavy. Different animals entirely.
Practice tests and question quality
Quality practice tests for ISSEP are rare. What you want: questions that mirror the scenario-based, application-focused style of the real exam. Not just "define this term" garbage.
The official ISC2 practice questions nail the style but limited quantity means you'll exhaust them fast. Third-party sources vary wildly. Some are clearly written by people who've never seen the actual exam. Look for explanations that reference NIST publications and engineering frameworks, not just answer keys.
Common mistake? Treating ISSEP like a memorization exam. It's not CC where you can brain-dump definitions. You need to understand engineering tradeoffs, risk-based decision making, and lifecycle integration. Another mistake: ignoring Domain 4 (Secure Operations, Maintenance, and Disposal) because it's only 15% of the exam. That 15% can make or break your passing score.
Where people actually struggle
Domain 2 (Risk Management) trips up a lot of technical people who aren't used to quantitative risk analysis. You need to understand ALE, SLE, ARO calculations and when qualitative approaches make more sense. Domain 3 (Security Planning, Design, Implementation) is massive. About 40% of the exam. Weak performance here kills you.
The exam costs $699 for members, $749 for non-members. No official passing score published, but ISC2 uses scaled scoring. You're aiming for whatever their statistical model decides is "passing" based on question difficulty weighting. Yeah, it's frustrating not knowing the exact number you need.
Getting the right study materials means combining official ISC2 resources, NIST publications, engineering references, and quality practice questions. It's more work than other certs because there's no single guide that covers everything. But if you're methodical about it, totally doable.
Conclusion
Getting started with ISSEP prep
Okay, here's the deal. The ISC2 ISSEP certification? It's not something you casually tackle on a random Tuesday because you're bored. This thing's specialized, technical, and honestly rewards folks who've actually gotten their hands dirty doing systems security engineering work in the real world, not people who've just skimmed whitepapers about it. If you're eyeing this path, you've probably already figured out whether your background matches what ISC2's looking for, and look, those prerequisites aren't some arbitrary gatekeeping nonsense. They exist because the exam straight-up assumes you've lived and breathed this material.
The exam cost? Not cheap at all. And that ISSEP passing score threshold means you've gotta truly understand security architecture and design engineering at a deep level, not just memorize brain dumps or frantically cram study materials five days before test day. I mean, the difficulty level here reflects that this is a concentration cert designed for practitioners who wrestle with NIST RMF, security controls, and the entire security engineering lifecycle constantly in their actual jobs.
Don't underestimate practice
Real talk now. Here's what trips people up constantly: they'll study the ISSEP exam objectives thoroughly, read every recommended book, maybe even shell out for official ISC2 training, but then they don't actually test themselves enough under realistic exam-like conditions.
ISSEP practice tests aren't just knowledge checks. They teach you how ISC2 phrases their questions, where tricky answer choices love to hide, what "best" really means in their specific context. Pattern recognition matters here.
The systems security engineering certification demands you think like an engineer solving messy real-world problems, not a student hunting for the "correct answer" from multiple choices. That's a different mental model. Takes dedicated practice. I've seen plenty of sharp people stumble here because they figured their job experience alone would carry them through.
Make your prep count
If you're serious about passing (and you've already worked through foundational study materials and wrapped your head around the CPE renewal requirements you'll eventually face) the next logical step's validation. You need to identify where your gaps are before sitting for the actual exam, because the ISSEP Practice Exam Questions Pack gives you that realistic checkpoint with questions mirroring the exam's style, difficulty level, and domain coverage so you're not blindly guessing about readiness.
Won't sugarcoat it. This cert takes effort.
But if security engineering's your career path? ISSEP proves you can do way more than just talk about security. You can architect it, implement it, defend your decisions under scrutiny. That's worth the work.