What Is the ISC2 HCISPP Certification?
Healthcare data breaches? Different animal entirely. You're not just protecting credit card numbers or email addresses. You're protecting someone's cancer diagnosis, mental health records, HIV status. The HCISPP certification addresses this reality in ways most credentials just don't, making it one of the more underrated credentials in cybersecurity right now.
HCISPP stands for HealthCare Information Security and Privacy Practitioner. It's a globally recognized credential from ISC2 that's built for professionals who implement, manage, and assess security and privacy controls in healthcare environments. Not hospitals alone. We're talking insurance companies, pharmaceutical firms, medical device manufacturers, health IT vendors, and anyone else touching protected health information (PHI).
This healthcare cybersecurity certification validates expertise in protecting PHI across clinical, administrative, and technical domains. You could be a CISSP with fifteen years under your belt, but walk into a hospital IT environment without understanding HIPAA Security Rule requirements or how breach notification timelines work? You're gonna struggle.
Why healthcare security is its own specialty
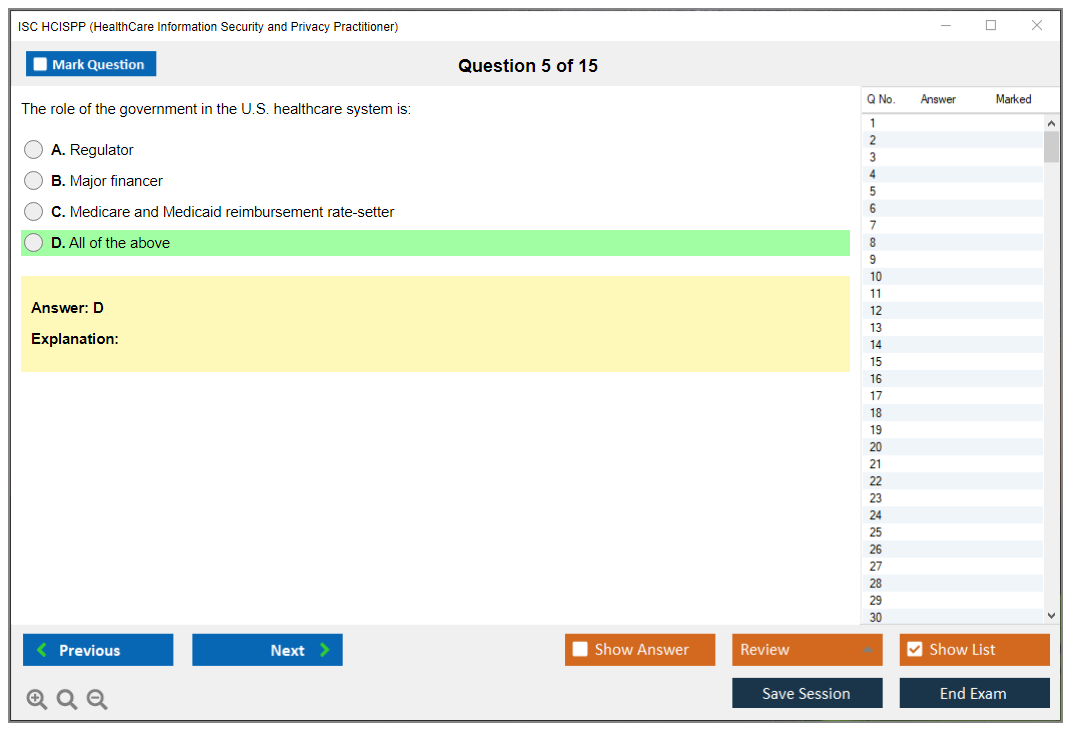
The thing is, healthcare differs from every other industry because the regulatory environment is absolutely insane. You've got HIPAA. HITECH Act. 42 CFR Part 2 for substance abuse records. State privacy laws that sometimes contradict federal ones. GDPR if you're dealing with European patients.
Unlike PCI-DSS where you can just not accept credit cards, healthcare organizations can't opt out of regulatory compliance. Period.
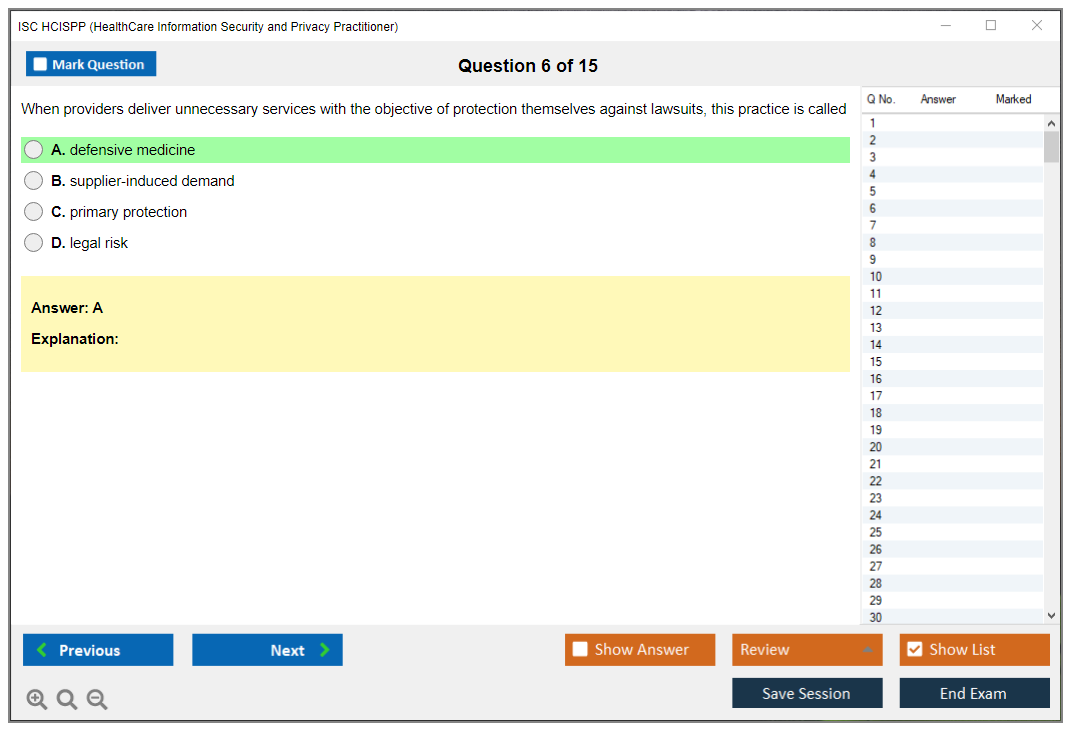
The HCISPP certification addresses the unique intersection of information security, patient privacy, and regulatory compliance in healthcare settings. That intersection is messy as hell. You're balancing security controls against clinician workflow. Lock things down too tight and doctors literally can't access patient records during emergencies. Too loose and you're looking at breach fines that can run into millions.
Unlike general security certifications, HCISPP focuses only on healthcare-specific threats, vulnerabilities, and regulatory frameworks. Break-glass access procedures. Clinical system authentication that doesn't require fifteen-character passwords when someone's coding a patient. Medical device security when half your environment is running Windows XP because the manufacturer won't certify the MRI machine on anything newer.
I once watched a security team lock down a radiology department so tight that technicians couldn't pull up images during an active stroke case. Patient waited 23 minutes while IT scrambled to restore access. That's the kind of mess you avoid when you understand both sides of this equation.
What makes someone a medical data privacy practitioner
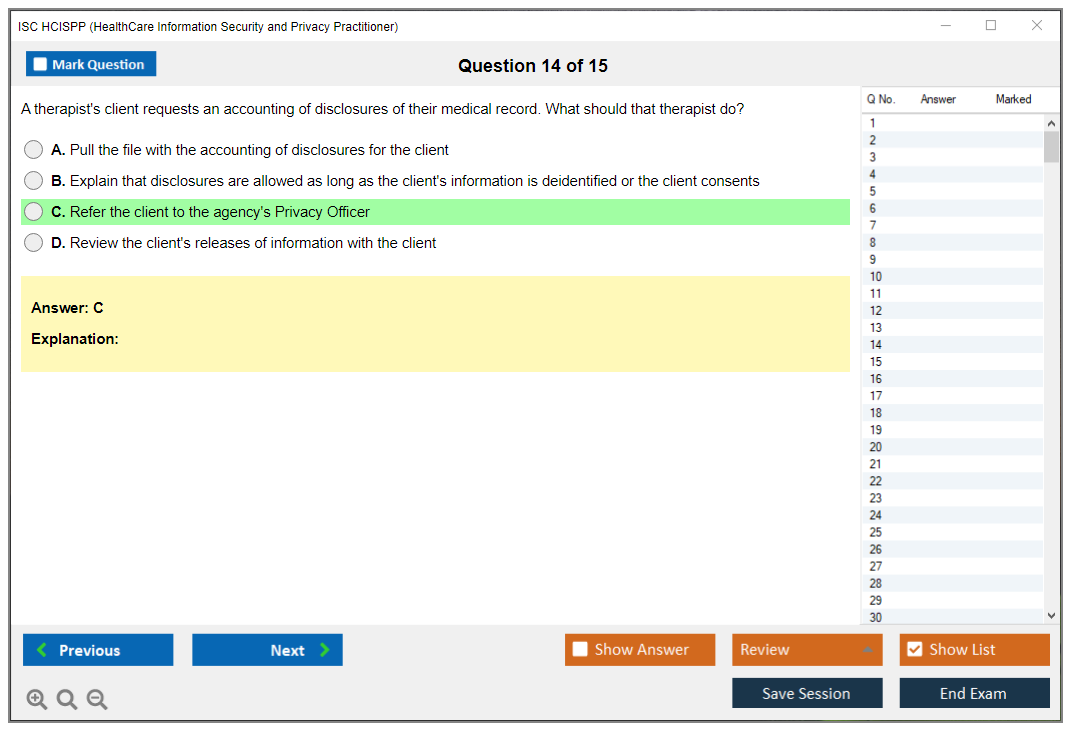
Medical data privacy practitioner skills include risk assessment, incident response, privacy impact analysis, and compliance auditing within healthcare organizations. You're looking at stuff like determining whether a nurse accessing her neighbor's chart constitutes a breach, figuring out data minimization strategies for research datasets, managing consent across treatment, payment, and operations. It's nuanced work.
The credential is vendor-neutral. Applies across hospitals, health systems, insurance companies, pharmaceutical firms, medical device manufacturers, and health IT vendors.
I've seen HCISPP-certified folks working in telehealth startups, clinical research organizations, and even health departments managing public health surveillance systems. The skills transfer anywhere PHI lives.
HCISPP complements other ISC2 certifications like CISSP but provides specialized knowledge needed for healthcare environments. Organizations pursuing HITRUST certification, HIPAA compliance, or healthcare risk management and compliance initiatives value HCISPP-certified professionals because they can actually speak both languages. Security and healthcare.
The certification covers both technical security controls and privacy governance, making it ideal for bridging IT security and healthcare compliance teams. Those two groups rarely understand each other. Having someone who gets both sides is worth its weight in gold.
Who actually needs HCISPP
Healthcare information security officers? Analysts responsible for protecting electronic health records (EHR) and health information exchanges? Obvious candidates. Privacy officers and compliance managers who handle HIPAA security and privacy certification requirements, Security Rule, and Breach Notification Rule are right there too.
IT security professionals transitioning into healthcare or expanding their expertise in regulated industries should seriously consider this. Risk managers and auditors who assess healthcare information systems against regulatory frameworks and industry standards absolutely benefit. Health Information Management (HIM) professionals seeking to strengthen technical security knowledge beyond just documentation and coding.
Clinical informaticists? Health IT specialists who design, implement, or manage healthcare technology systems? You're making architectural decisions that have privacy implications. Consultants and advisors who provide security assessments, gap analysis, or compliance services to healthcare clients basically need this to be taken seriously.
Security architects and engineers who build infrastructure for telehealth, remote patient monitoring, or cloud-based health applications need it. Third-party vendors and business associates who handle PHI and must demonstrate security competency are increasingly being asked to show credentials. Government and military healthcare IT personnel responsible for Veterans Affairs, Department of Defense, or public health systems.
What you actually learn
The exam covers the healthcare regulatory environment including HIPAA, HITECH, 42 CFR Part 2, state privacy laws, and international regulations like GDPR as applied to health data. Privacy and security frameworks specific to protected health information (PHI) security including administrative, physical, and technical safeguards. That's the three-pillar structure of HIPAA Security Rule.
Risk analysis? Risk management methods adjusted to healthcare organizations and their unique threat space. Third-party risk management for business associates, cloud service providers, medical device vendors, and health information exchanges gets deep coverage because that's where most breaches actually happen, not gonna lie.
Incident response and breach management specific to PHI, including notification requirements, forensic investigation, and remediation. You've got 60 days to notify affected individuals after discovery. The clock starts ticking whether you're ready or not.
Access controls, authentication mechanisms, and authorization models for clinical systems, patient portals, and mobile health applications. Encryption, data loss prevention, and secure transmission protocols for health information at rest, in transit, and in use.
Security architecture for healthcare IT infrastructure including network segmentation, medical device security, and telehealth platforms. Privacy impact assessments, data minimization principles, and consent management across treatment, payment, and operations. This stuff is more nuanced than most security people realize. Audit logging, monitoring, and compliance reporting to demonstrate adherence to regulatory requirements and organizational policies.
Exam format and what to expect
The HCISPP exam has 125 questions and you get three hours to complete it. Questions are multiple choice. Like other ISC2 exams, you're looking at scenario-based questions that test application of knowledge, not just memorization. Computer-based. Administered at Pearson VUE testing centers or through online proctoring.
The HCISPP exam objectives are divided into six domains: Healthcare Industry, Regulatory and Standards Environment, Privacy and Security in Healthcare, Information Governance and Risk Management, Third Party Risk Management, and Information and Asset Management.
Each domain has specific weight. You need to understand all of them because questions pull from across domains.
The HCISPP passing score isn't publicly disclosed by ISC2. They use scaled scoring like most professional certifications. You need 700 out of 1000 points on the scaled score, but that doesn't mean 70% correct answers. The scaling accounts for question difficulty, so don't try to reverse-engineer it.
Cost breakdown
The ISC2 HCISPP exam cost is $425 USD for members and $525 for non-members. ISC2 membership is $50 annually, so if you're planning to take the exam it makes sense to join first and save money.
Training costs vary wildly. Official ISC2 training runs around $2,495 for instructor-led courses, but self-study using books and HCISPP study materials can be done for under $200.
Retake fees? Same as the initial exam cost, so you want to pass the first time. Budget for HCISPP practice tests separately. Good question banks run $50-150 depending on the vendor.
Prerequisites you need to know
HCISPP prerequisites require two years of cumulative paid work experience in one or more of the six domains. The experience must be within the last ten years, and it needs to be paid full-time work (part-time and internships count at reduced rates).
Acceptable experience types include security analyst roles in healthcare, privacy officer positions, compliance auditing, health IT implementation, or risk management.
If you don't have the experience, you can sit the exam and become an Associate of ISC2, then have five years to gain the required experience. The endorsement process requires an ISC2 member in good standing to vouch for your experience and professional conduct.
How hard is this thing really
The HCISPP exam difficulty sits somewhere between SSCP and CISSP in my experience. If you're already working in healthcare security, it's very doable with 6-8 weeks of focused study.
Coming from general IT security with no healthcare background? Expect 10-12 weeks because you're learning an entirely new regulatory framework.
Factors that make HCISPP challenging include the depth of healthcare regulations, the nuanced difference between privacy and security (they're not the same thing), and risk management scenarios that require understanding clinical workflows.
Compared to CISSP, HCISPP is narrower in scope but deeper in healthcare-specific content. There's less overlap than you'd think. CISSP covers security broadly, HCISPP dives deep into healthcare contexts.
Study time varies by background. Healthcare professionals with compliance experience but weak technical skills need more time on encryption and access controls. Security professionals need more time on HIPAA Privacy Rule and consent management details.
Best ways to study
Official ISC2 resources include the exam outline (download it first, it's your roadmap) and official training courses. Books and study guides should cover all six domains in detail, include practice questions, and ideally be written by healthcare security practitioners, not just general security authors.
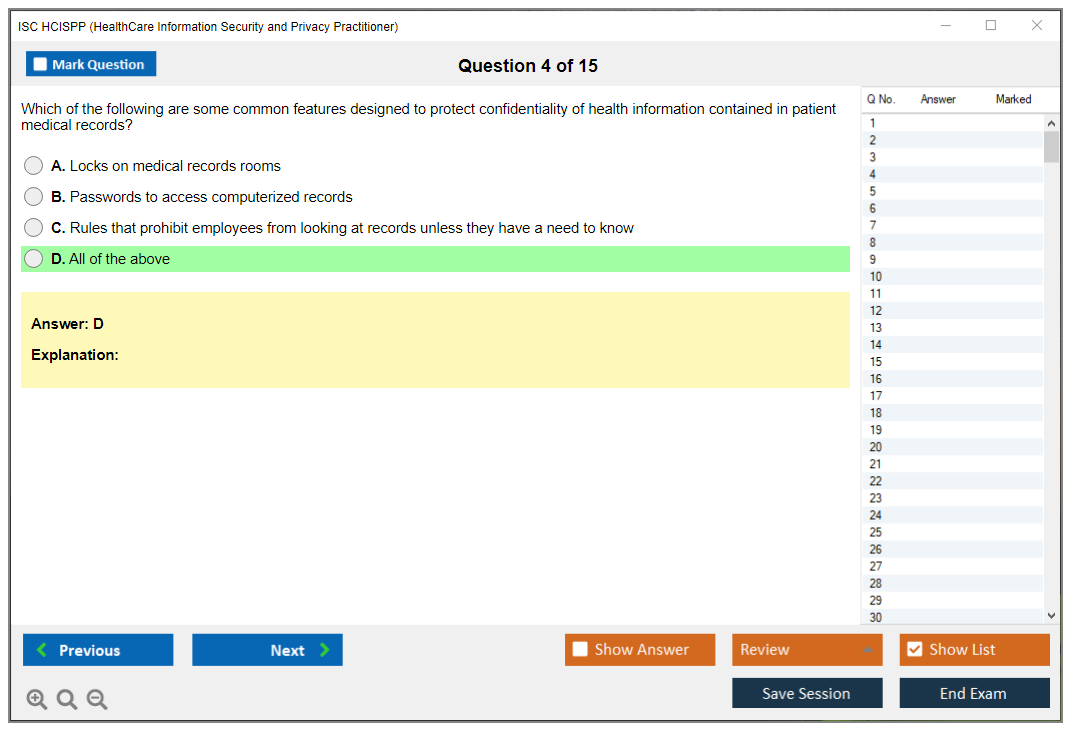
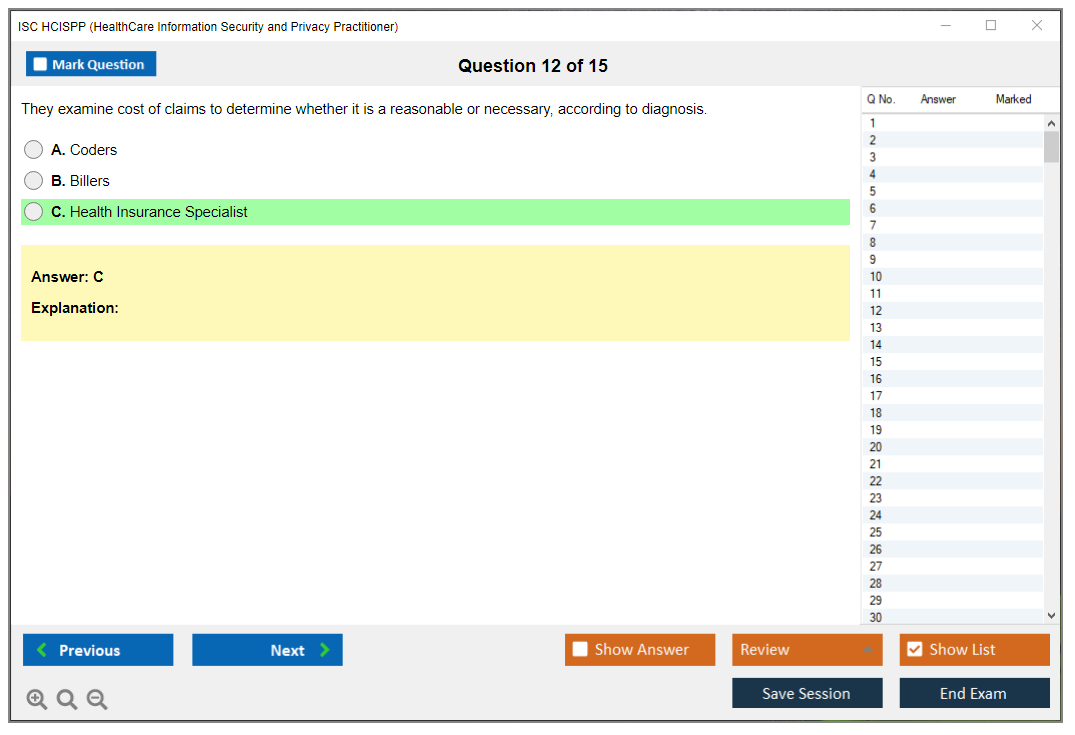
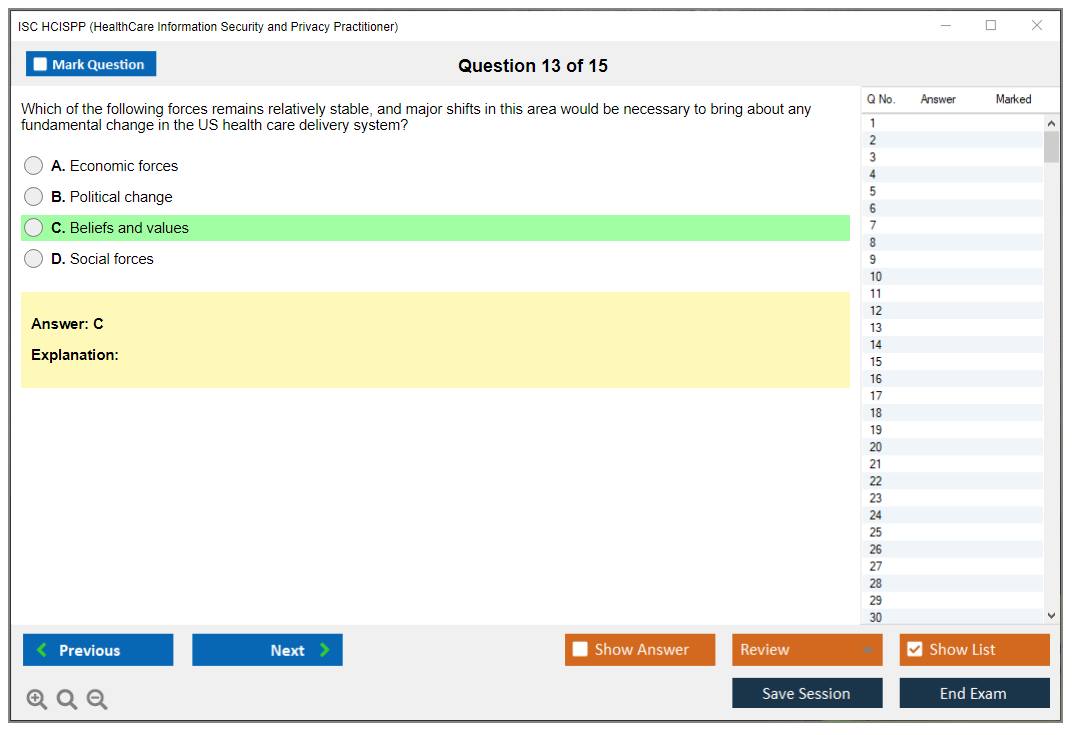
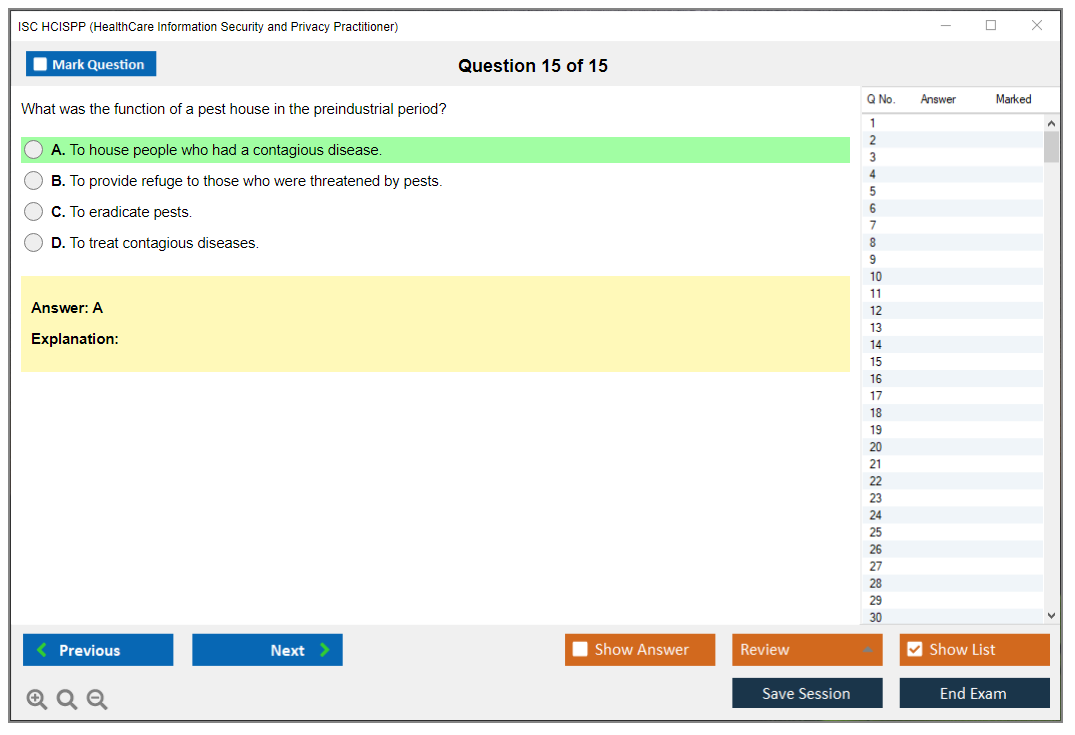
HCISPP practice tests are absolutely needed. Use them to identify weak domains, get comfortable with ISC2 question style, and build stamina for a three-hour exam.
Good practice tests should include domain coverage that matches the exam outline, detailed explanations for both correct and incorrect answers, and questions that test application rather than memorization.
Common pitfalls? Practice tests reveal these: confusing privacy requirements with security requirements, misunderstanding minimum necessary standard application, and getting tripped up on business associate agreement requirements versus covered entity responsibilities.
Renewal requirements
HCISPP renewal requirements mandate 40 CPE credits every three years. You also pay an annual maintenance fee (AMF) of $65.
CPE credits can be earned through webinars, online courses, conferences, teaching and training others, publishing articles, or even work activities if they involve professional development.
ISC2 is pretty flexible about CPE sources. Attending healthcare security conferences like HIMSS, completing online HIPAA training, reading relevant whitepapers and writing summaries. Just document everything.
Is it worth it
For HIPAA-focused roles and healthcare security positions? Absolutely. The credential shows specialized knowledge that general certifications don't cover. You can definitely work in healthcare security without HCISPP, but having it opens doors and often justifies higher compensation.
No healthcare background but want to break into the field? HCISPP gives you credibility faster than years of on-the-job learning.
The jobs that benefit most are privacy officer positions, healthcare security analyst roles, compliance auditor positions, and consulting roles focused on healthcare clients.
Download the exam objectives from ISC2's website. Build a domain checklist and assess your current knowledge honestly. Choose study materials based on your learning style and budget. Schedule your exam date 8-12 weeks out to create accountability. Then actually study consistently rather than cramming the week before.
HCISPP Exam Overview
The HCISPP certification is ISC2's healthcare-focused credential for people who touch security, privacy, and compliance around patient data. It's not some niche "HIPAA only" badge, honestly. More like a healthcare cybersecurity certification that expects you to understand how hospitals and payers actually work, then apply security and privacy controls without breaking clinical care.
Healthcare is weird. The priorities are different. Patient safety beats perfect security, downtime costs are brutal, and protected health information (PHI) security has to coexist with clinicians who need fast access, third parties everywhere, and devices that were never designed to be hardened.
Who HCISPP is for (roles and industries)
Security analysts in hospital IT. Privacy officers who keep getting pulled into incident calls. GRC folks stuck translating HIPAA into controls. Vendor risk people reviewing BAAs at 10 pm.
Also? Consultants. Auditors. Managed security teams. Even app owners in EHR ecosystems who keep getting asked, "Are we HIPAA compliant yet?" and need a HIPAA security and privacy certification that maps to real operational decisions.
What you'll learn (security + privacy in healthcare)
You're learning how regulations, technical safeguards, and organizational policy collide in real life. Like when a clinical workflow needs access "right now" but the minimum necessary standard still applies. Or when a cloud migration improves resilience but makes your business associate agreement language suddenly matter a lot more than anyone wanted to admit.
It's privacy and security together. Consent. De-identification. Access control. Risk assessments. Incident response. Vendor management. Medical data privacy practitioner stuff, but with teeth.
How the test is put together
The HCISPP exam is a thorough assessment of the knowledge and skills required to implement and manage security and privacy programs in healthcare settings. ISC2 designs it to test practical application, not trivia night memorization, so you're gonna read scenarios, weigh tradeoffs, and pick the "best" answer even when two options feel decent.
The exam's available in English at Pearson VUE test centers worldwide and through online proctoring. No notes. No reference materials. No "quick check" on a regulation detail. Just you, the clock, and a testing interface with highlighting, strike-through, a timer, and the ability to mark questions for review.
Exam format, length, and question types
You get 125 questions. Three hours. That's about 1.4 minutes per question if you want review time, and honestly time management is make-or-break because scenario prompts can be chunky. You'll burn minutes re-reading if you don't stay disciplined.
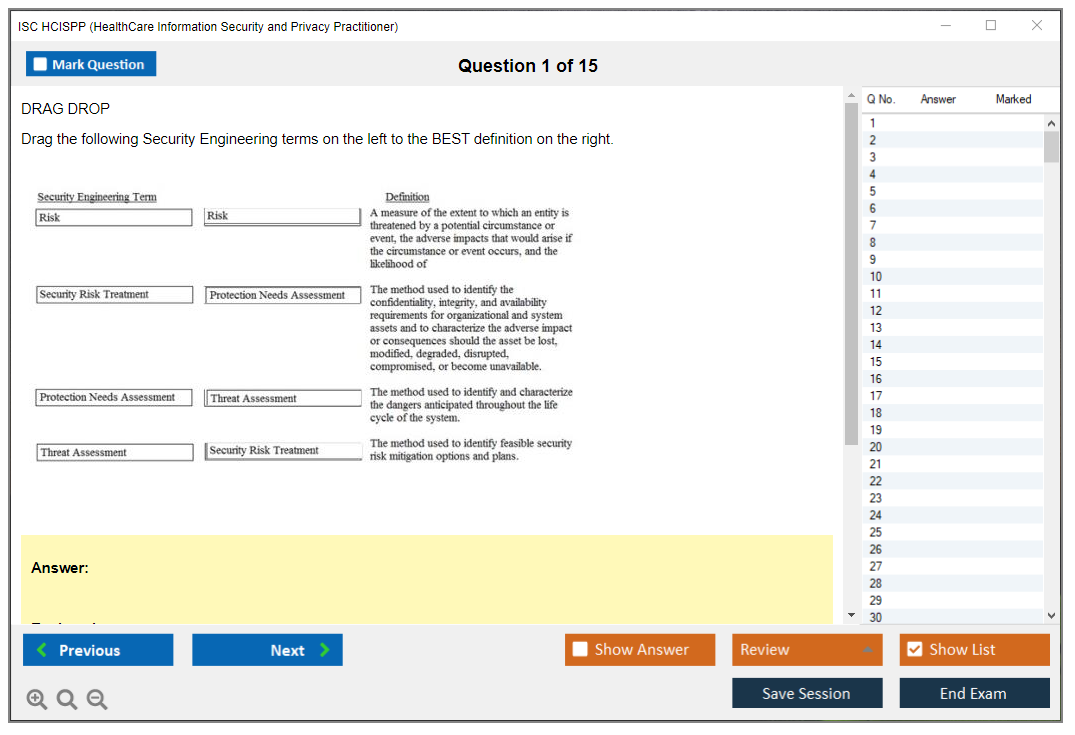
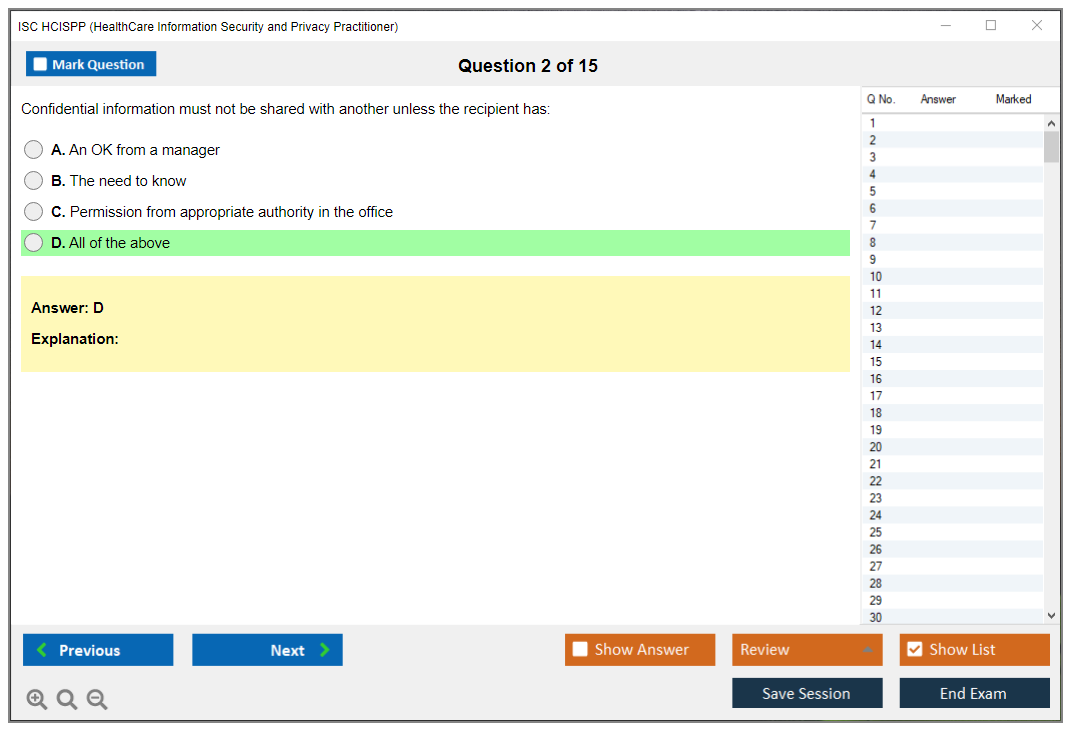
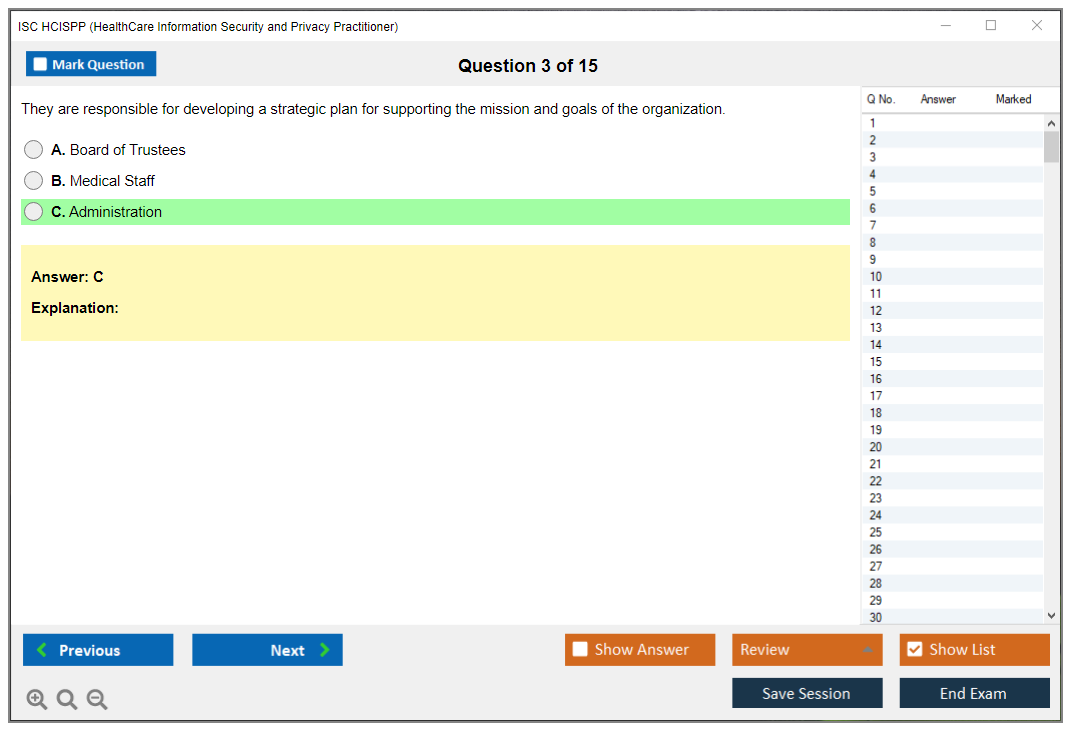
The question set includes multiple-choice plus "advanced innovative questions" like drag-and-drop, hotspot selection, and scenario-based sets. Four options is typical for multiple-choice, and the trap is that the wrong answers are often "not insane." They're just less correct based on context, priority, or regulatory expectation.
One detail people miss? All 125 questions are scored on HCISPP, unlike some ISC2 exams that mix in unscored pretest items. Every question counts. No freebies.
HCISPP exam objectives (domains)
ISC2 updates HCISPP exam objectives periodically, which matters because healthcare threat trends shift fast. So do interpretations and enforcement patterns. Candidates should review the current exam outline from ISC2 before trusting any HCISPP study materials. Domain weightings change and some books lag behind.
The certification demonstrates competency across all six domains without separate tests per domain, which is great because it mirrors the job. But it also means you can't "skip" privacy or vendor management and hope to coast.
Here's the domain breakdown, with the stuff that actually shows up in scenario thinking:
domain 1: healthcare industry (11%) This is the "how does healthcare function?" section. Delivery models, payment systems, clinical workflows, stakeholders, basic medical terminology. Short percent, but it sets the context for everything else. Security in a radiology workflow doesn't look like security in a call center workflow, and the exam will expect you to respect clinical priorities without ignoring controls.
domain 2: regulatory and standards environment (22%) Big weight. HIPAA Privacy Rule and Security Rule, HITECH, state privacy laws, sometimes international considerations, and frameworks like HITRUST and NIST. You need to know requirements, penalties, enforcement, and how to build a compliant program that doesn't collapse the first time a third party touches PHI. Mentioning "HIPAA says.." won't cut it if you can't connect it to safeguards, documentation, and operational policy.
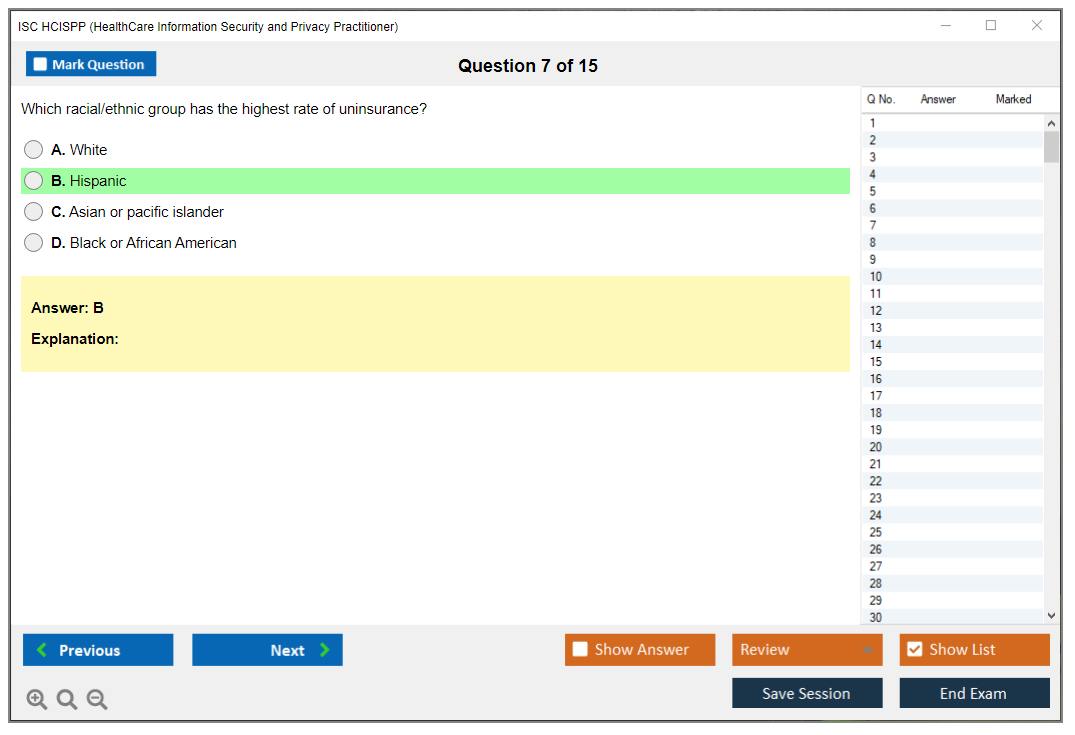
domain 3: privacy and security in healthcare (22%) Another heavy hitter. Consent management. Minimum necessary. De-identification. Access controls. Training and awareness. This domain lives in the tension between treatment, payment, operations, and research. The exam loves asking how to share data safely while still letting the business function, which is basically healthcare risk management and compliance in sentence form.
domain 4: information governance and risk management (15%) Information lifecycle. Classification. Retention schedules. Risk assessment methods and treatment options. This is where a lot of candidates get tripped up because they know technical controls but haven't had to formalize risk acceptance, compensating controls, or retention schedules that align with legal, clinical, and operational needs. I've seen people nail the tech questions and then completely blank when the question asks about policy documentation or lifecycle management.
domain 5: third-party risk management (11%) BAAs. Vendor assessments. Supply chain risk. Cloud service providers. Outsourcing. Not gonna lie, this domain feels "paperwork-y" until you've lived through a breach where the weak link was a billing vendor, a transcription service, or a cloud misconfiguration and suddenly everyone wants to know who signed what and whether your contract language even required security controls.
domain 6: information security and privacy incident management (19%) Detection. Response. Breach analysis. Notification. Forensics. Lessons learned. HIPAA breach notification rules plus state breach laws, and the practical reality of handling ransomware, insider threats, and medical device vulnerabilities under pressure. This domain fits with current healthcare security challenges (including ransomware and cloud adoption) and it expects you to know what to do first, what to document, and who must be notified and when.
Questions are pulled from a large item bank and weighted by those domain percentages, so your experience might "feel" heavier in some areas. But the blueprint is the blueprint.
Passing score (what ISC2 discloses vs. what to expect)
ISC2 uses a scaled score. Passing is 700 out of 1000, and no, that doesn't mean 70% correct. The scaled score accounts for question difficulty so standards stay consistent across different exam versions. ISC2 doesn't publish the exact percent correct required because it varies by the set of questions you get.
You'll hear industry estimates like 70 to 75% correct being "typical" for the HCISPP passing score, but that's not official. What is real is the psychometric analysis behind scoring and the fact that you only get pass/fail at the end, with immediate results on computer-based testing. If you fail, you'll get a diagnostic per domain like above/near/below target, not a numeric breakdown.
Aim for mastery. Seriously. "Barely passing" study habits show up as time pressure, second-guessing, and missed detail in scenario questions.
HCISPP cost (exam fees and total cost to get certified)
People ask about the ISC2 HCISPP exam cost like it's one number. It's really exam fee plus prep plus time plus whatever you spend fixing gaps.
Exam registration cost
ISC2 sets the exam price and it can change, so check the current fee on the official site before budgeting. Pearson VUE is the delivery channel, but pricing's controlled by ISC2. Add taxes where applicable. Also add travel if you pick a test center.
Training costs (self-study vs. instructor-led)
Self-study can be cheap-ish if you already know HIPAA operations, incident response, and governance. Instructor-led can be worth it if you're coming from pure IT security and you've never had to think about consent, minimum necessary, or BAAs beyond "legal handles that." That assumption gets people wrecked on exam day.
Other options exist. Bootcamps. Subscription platforms. Internal hospital training. Mentioning them's easy. Picking one that matches the current HCISPP exam objectives is the hard part.
Retake fees and budgeting tips
Retakes cost money. Plan for the possibility, even if you don't need it, because it lowers pressure and keeps you from rushing scheduling. A practical tip? Delay booking until you've done timed HCISPP practice tests and you can finish with 20 to 30 minutes to review flagged questions without panicking.
HCISPP prerequisites and eligibility
Required work experience (and acceptable experience types)
ISC2 requires relevant work experience for full certification status, tied to HCISPP domains. Healthcare IT security counts. Privacy and compliance work can count. Risk management work can count. Confirm specifics on the current ISC2 policy page because experience rules change more often than people expect.
Endorsement process (ISC2 endorsement basics)
After you pass, you go through endorsement. Another ISC2-certified professional can endorse you, or ISC2 can do it. It's paperwork. It's normal. Don't procrastinate it.
Associate of ISC2 option (if experience is missing)
No experience yet? You can still pass the exam and become an Associate of ISC2 while you earn the required time. This is a decent move if you're pivoting into healthcare security from general IT.
HCISPP difficulty: how hard is the exam?
The HCISPP exam difficulty is less about "hard math" and more about mixed context. You're juggling clinical workflow, legal constraints, and security controls. The question's often, "What's the best next step given patient care, compliance, and risk?"
Factors that make HCISPP challenging (healthcare regs, privacy, risk)
Regulatory detail. Vocabulary. Who's a covered entity versus a business associate in a given scenario. What triggers breach notification. How "minimum necessary" applies in treatment versus operations. And then you add ransomware pressure and cloud service shared responsibility, and candidates start picking technically correct answers that are operationally wrong.
HCISPP vs. CISSP / CCSP (difficulty and overlap)
Compared to CISSP, HCISPP's narrower but more regulation-heavy and workflow-heavy. Compared to CCSP, it's less cloud architecture and more healthcare governance and privacy decision-making, though cloud adoption shows up a lot in third-party and risk scenarios. If you're earlier in your career, something like SSCP or CC can be a better ramp before you dive into healthcare-specific governance.
How long to study (time estimates by background)
If you already work HIPAA incidents and vendor reviews, 4 to 6 weeks can be enough. If you're coming from general security with no healthcare exposure, plan 8 to 12 weeks. More if you hate policy work.
Best HCISPP study materials (official and third-party)
Official ISC2 resources (exam outline, official training)
Start with the official exam outline. Print it. Build a checklist. If a resource doesn't map cleanly to the outline, it's suspect, even if it has good reviews.
Official training's structured and usually aligned, but it's not magic. You still need reps on scenarios.
Books and study guides (what to look for)
Look for recent publication dates and explicit mapping to the latest HCISPP exam objectives. Look for scenario explanations, not just definitions. If the book treats HIPAA like a glossary, skip it.
Flashcards, notes, and domain summaries
Flashcards help for terminology and regulation hooks. Notes help for decision trees like "breach?" versus "incident?" Domain summaries help you review fast in the final week. None of these replace practice questions with explanations.
HCISPP practice tests and question banks
How to use practice tests effectively (timing, review, error log)
Timed runs matter. Do at least a couple full-length simulations. Track misses in an error log with the "why," not just the right letter. The exam's about reasoning under constraints, and you need to see your patterns, like picking technical fixes when the scenario demanded policy, notification, or governance first.
What a good practice test should include (domain coverage, explanations)
Coverage across all six domains. Explanations that cite principles like minimum necessary, risk treatment choices, or BAA obligations. A mix of straightforward and messy scenarios. If it's all definition questions, it's not preparing you for the real thing.
Common pitfalls practice tests reveal (privacy vs. security details)
People over-focus on access control and under-focus on disclosure rules. Or they assume "encrypt it" is always the answer when the question's really about incident handling, documentation, and notification timelines. Practice tests make those blind spots obvious fast.
HCISPP study plan (step-by-step)
4-week plan (accelerated)
Week 1: domains 1 and 2, because healthcare context and regulations drive everything. Week 2: domains 3 and 4, with emphasis on minimum necessary, de-identification, and risk assessment outputs. Week 3: domains 5 and 6, plus one full timed exam. Week 4: two more timed sets, heavy review of wrong answers, and memorize your "first action" instincts for incidents.
Fast. Intense. Doable if you already live this work.
8 to 12 week plan (standard)
Go domain by domain. One per week early. Two weeks for domains 2 and 3 because they're heavy and nuanced. Add practice question blocks every weekend and keep an error log from day one. Waiting until the end to see your gaps is how you waste time and panic-schedule a retake.
Final week checklist (readiness criteria)
Finish a timed 125-question set in under 2 hours and 40 minutes. Review flagged questions without changing answers blindly. Confirm you can explain, in plain language, how HIPAA, policy, and technical controls interact in ransomware and insider scenarios. Sleep.
Renewal: how to maintain HCISPP (CPEs and fees)
Renewal cycle and CPE requirements (what to confirm on ISC2)
ISC2 certifications run on a renewal cycle with CPE requirements, and yes, you should confirm the current HCISPP renewal requirements on ISC2 because numbers and rules can change. Don't rely on old forum posts.
Annual maintenance fee (AMF) and payment
There's an annual maintenance fee. Budget for it. Missing payment can create reinstatement headaches you don't want.
Ways to earn CPEs (webinars, courses, conferences, work activities)
Webinars are the easy mode. Courses count. Conferences count. Some work activities can count if documented properly. The trick's logging as you go, not trying to recreate a year of learning from memory.
FAQs about HCISPP
Is HCISPP worth it for HIPAA/security roles?
If your job touches PHI decisions, vendor risk, audits, or incident response, yes. It signals you can think across privacy and security without treating compliance like an afterthought.
Can I take HCISPP with no healthcare background?
You can. But expect extra study time on how care delivery works and how regulations apply in context. The exam assumes you can interpret scenarios like a functioning healthcare org, not a generic enterprise.
What jobs benefit most from HCISPP?
Security and privacy leads in hospitals and clinics. GRC analysts in healthcare. Vendor risk managers. Incident responders dealing with PHI exposure. Consultants doing HIPAA risk analyses. Anyone who wants to be the person in the room who can translate "what happened" into "what we must do next."
Next steps
Download the exam objectives and build a domain checklist
Start with the current HCISPP exam objectives and weightings, then map your notes and practice questions to them. If your materials don't line up, you're studying vibes, not content.
Choose study materials + schedule your exam date
Pick your core book or course, add HCISPP practice tests with explanations, and set a date once you can hit timed runs confidently. If you're also comparing paths, it's worth glancing at HCISPP resources alongside CISSP and CCSP so you're not accidentally training for the wrong style of question.
The first question? "What's this gonna cost me?" And honestly, it's way more than just the exam fee. You've got study materials, maybe training, membership decisions, and then there's also ongoing costs after you pass that people completely forget about. Let me break down what you're actually looking at financially.
What you'll pay just to sit for the test
Standard HCISPP exam registration fee is $425 USD for non-members and $375 USD for ISC2 members as of 2025. That's your baseline. The price to walk into the testing center (or log into your computer for online proctoring) and take your shot at the 125 questions.
Here's where it gets interesting, though. That $50 discount for members? ISC2 associate membership costs $50 annually. So if you're just going for HCISPP and nothing else, the member discount basically pays for your membership. You're not saving money, but you get the member benefits for free, which includes access to forums, some study resources, webinars, that kind of thing.
Full membership runs $125 annually. Requires you to already hold an ISC2 certification. Since you don't have that yet, you'd go with associate membership first, but if you're eyeing other certs like CISSP or CCSP down the road, that membership starts making more financial sense in the long run.
Payment happens at registration through the ISC2 or Pearson VUE portal. Credit card, basically. Some regions might see different pricing because of currency conversion or local taxes, and I mean, I've seen people get surprised by that, so check the actual checkout price for your location before you assume anything.
Training options and what they actually cost
Self-study is your cheapest route. You can get away with $100-$300 total if you're disciplined about it and have a decent baseline of knowledge already. A good HCISPP study guide runs $50-$80. Practice tests are another $50-$100. Maybe you grab some flashcards or supplementary materials for another $50. That's it.
Official ISC2 training courses? Different beast entirely. $2,000-$3,000 for instructor-led bootcamps. These are delivered in-person or virtually over several days, and yeah, they're expensive as hell. You get structured content, expert instructors, official materials, but not gonna lie, it's hard to justify that cost unless your employer is paying or you've got money to burn.
Self-paced online training through ISC2 or authorized partners sits in the middle at $800-$1,500. You get video lectures, practice questions, maybe some labs, but you're learning on your own schedule without someone holding you accountable.
The thing is, most people with a decent background in either healthcare IT or security can pass with self-study alone. Career changers or folks completely new to healthcare compliance? They usually benefit from structured training. It's about knowing yourself and being honest about your learning style and how much hand-holding you need.
Free resources exist too. The official ISC2 exam outline is free and tells you exactly what's on the test. Literally the blueprint. Their candidate information bulletin explains the format. Webinars pop up occasionally. Community forums can be helpful, though quality varies wildly depending on who's posting. LinkedIn Learning and similar platforms have healthcare security courses that supplement your prep, though they're not HCISPP-specific.
For what it's worth, I've seen plenty of people succeed by combining a good study guide with solid practice tests and free resources, and that's maybe $150 total if you're smart about it. Our HCISPP Practice Exam Questions Pack at $36.99 gives you realistic questions across all domains, and when you pair that with a good book, you're covering all the bases without dropping thousands on a bootcamp you might not even need.
By the way, I knew someone who spent nearly four grand on a bootcamp because they panicked about prep time, then barely studied the materials because work got crazy and they were too burned out after the intensive week. Failed anyway. Wasted all that money. Sometimes more expensive isn't better, it's just more expensive.
When things don't go according to plan
Didn't pass? You're looking at the full exam fee again. $375-$425 depending on your membership status. There's a 30-day wait before you can retake, which honestly gives you time to figure out what went wrong. Fail twice? Now it's a 90-day wait before attempt three, and at that point you really need to rethink your prep strategy.
Retake fees are identical to the initial registration cost. This is where poor preparation gets expensive fast. Two failed attempts add $750-$850 to your total cost, not counting the time and stress and the hit to your confidence. I always tell people: invest in proper prep materials upfront. Spending an extra $100 on quality practice tests beats paying $425 for a retake every single time.
The exam fee includes one attempt only. ISC2 doesn't give you a do-over or a discount on retakes like some other certification programs. You pay full price each time you sit for that exam.
Adding it all up (and how to keep costs reasonable)
Total first-year cost typically ranges from $600-$3,500 depending on your approach and how much money you want to throw at the problem. Here's the breakdown:
Budget route: $425 exam fee plus $150 study materials equals $575. Add the $125 annual maintenance fee after you pass (we'll get to that in a second), and you're at $700 for year one.
Middle ground: $375 exam fee (member price) plus $50 membership, $800 self-paced training, and $125 AMF. That's $1,350.
Premium route: $375 exam fee, $50 membership, $2,500 bootcamp, $125 AMF totaling $3,050, which is a lot but some people have that kind of budget.
Most people land somewhere between budget and middle ground in my experience. Starting with free resources to assess your baseline knowledge makes sense. Download that exam outline, watch some free webinars, see what you already know versus what you need to learn, then invest in targeted materials for your weak areas rather than buying everything under the sun.
Bundled study packages (book plus practice tests plus flashcards) often cost less than buying components separately, so look for those. Setting aside 3-6 months for study lets you spread costs over time instead of panic-buying expensive last-minute training when you realize the exam is next week and you're not ready.
What happens after you pass
Annual maintenance fee is $125 for full members or $80 for the AMF-only option. You need to earn CPE credits to maintain your certification. The exact number varies, so confirm current requirements on the ISC2 website because they change these things periodically. These are similar to what's required for SSCP or other ISC2 certs if you're familiar with those.
Ways to earn CPEs? Attending webinars. Taking courses. Going to conferences. Publishing articles. Teaching. Even documenting certain work activities. Many are free or low-cost, which is nice. Your employer might send you to conferences anyway, and those hours count toward your CPE requirements.
This ongoing cost is something people forget when budgeting. You're not just paying once and done. It's an annual investment in maintaining the credential, and if you don't pay or earn your CPEs, you lose the certification entirely.
Making the math work in your favor
Many employers offer tuition reimbursement. Professional development budgets. Healthcare organizations especially value HCISPP because it directly applies to HIPAA compliance and protected health information security, which they absolutely need people who understand. Ask about certification bonuses too. Some places pay a one-time bonus when you achieve certification or give you a raise, which can offset the entire cost.
If your employer won't pay upfront, ask about reimbursement after passing. Some will reimburse exam fees and study materials if you provide receipts and proof of certification, which at least means you're not out the money permanently.
Military discounts exist. Government discounts. Academic discounts occasionally appear through special programs. ISC2 sometimes offers promotional pricing during cybersecurity awareness events or at conferences, though you can't count on these. Group discounts may be available if your organization is sponsoring multiple employees. These aren't always advertised prominently, so ask directly.
Tax deductions might apply for professional certification expenses depending on your jurisdiction and tax situation. I'm not a tax advisor, obviously, but it's worth asking your accountant whether exam fees, study materials, and travel to training count as deductible business expenses in your specific case.
Viewing this as an investment, not just an expense
HCISPP is specialized. The field desperately needs qualified people who understand this stuff. Healthcare data breaches are expensive and frequent. Organizations need practitioners who understand both the security and privacy sides, who know HIPAA inside and out, who can work through healthcare-specific risk management without screwing things up.
That specialization translates to better job prospects. Higher earning potential. Whether you're in healthcare IT security, compliance, risk management, privacy, or consulting, HCISPP sets you apart from people who just have general knowledge. The certification signals to employers that you've invested in understanding this specific domain, not just general security principles like you'd get from CC.
Compared to what you might spend on a college course or other professional certifications, HCISPP's total cost is actually reasonable when you think about it. You're looking at roughly $600-$1,500 for most people when they're smart about resource selection, and that's less than a single college credit in many programs these days.
The key? Planning ahead and being strategic. Don't wait until two weeks before you want to test and then panic-buy a $2,500 bootcamp because you're desperate. Don't skip practice tests to save $50 and then fail the $425 exam because you weren't properly prepared. Don't ignore the annual maintenance fee and get surprised by it later when ISC2 sends you an invoice.
Budget appropriately, choose study resources that match your learning style without breaking the bank, and view the whole thing as a professional investment that pays dividends over your career. That mindset shift makes the expense easier to justify and helps you make smarter spending decisions throughout the process instead of just throwing money at whatever seems convenient in the moment.
HCISPP certification? It's ISC2's healthcare-focused credential for people who live at the intersection of security, privacy, and compliance. Not theory, not vibes, but the day-to-day reality of protecting patient data while a hospital's literally on fire operationally, a clinic's running on fumes staff-wise, and everyone still expects the EHR to stay up like it's some kind of magic.
I mean, it's a healthcare cybersecurity certification, sure, but it's also a HIPAA security and privacy certification in the sense that you're actually expected to understand how healthcare works in practice. Covered entities. Business associates. Protected health information (PHI) security. Breach response. Risk decisions that aren't purely technical. The thing is, you're making judgment calls that affect real patients.
HCISPP fits people in hospitals, clinics, health systems, payers, EHR vendors, telehealth companies, and business associates handling PHI. Security analysts. Privacy and compliance staff. Internal audit folks. Risk managers. Consultants. Even IT people supporting EHRs and medical devices who suddenly got yanked into "why is this data exposed" conversations they didn't sign up for.
Not everyone has "security" in their title, honestly. That's totally fine.
You're learning how healthcare risk management and compliance actually works when real regulations and real patient harm are on the line. Plus the controls and governance that keep medical data privacy practitioner work from turning into a paper exercise that nobody reads. Policies. Training sessions. Incident response. Third-party risk assessments. Technical safeguards. Administrative safeguards. And the messy, frustrating overlap between them that makes your job interesting or infuriating depending on the day.
The exam's the gate. But the credential's the point. If you don't understand the eligibility rules early, you can pass the test and still get stuck at the finish line waiting on experience or paperwork. Honestly that's just a dumb way to lose momentum when you're this close.
ISC2 exams are typically multiple-choice style questions with scenario wording that tries to see if you can actually apply concepts, not just recite definitions you memorized on the train. Expect governance questions. "Best next step" questions where context matters. And plenty of situations where more than one answer sounds decent, but one matches healthcare privacy expectations better, and you need to know why.
ISC2 defines six HCISPP exam objectives (domains). You don't need to memorize the domain names for eligibility, but you absolutely do need to map your work to one or more of them later during endorsement. And the thing is, that mapping part trips people up constantly because they underestimate how specific ISC2 wants you to be.
People always ask about the HCISPP passing score, and ISC2 generally doesn't make this a simple "get X percent" situation you can game with formulas. Plan like you need to be solid across the domains, because weak spots get exposed fast when the questions are scenario-heavy and you can't just pattern-match your way through.
Money matters. Budgeting matters even more when your employer's only half-supportive and you're trying to justify this investment without sounding desperate.
If you're pricing this out, you're probably also searching ISC2 HCISPP exam cost like everyone else. The exam fee can change, and region pricing happens, so check ISC2's current fee page before you commit to a date and block your calendar. Also remember: passing the exam's not the only cost. Annual maintenance fees show up later, and they add up over time.
HCISPP study materials range from "I found a used book and made my own notes in the margins" to official instructor-led training that costs as much as a decent laptop. Self-study's cheaper, but slower if you're new to healthcare workflows or privacy language. Instructor-led can be worth it if you need structure and accountability, but not if you're expecting it to magically do the learning for you while you zone out.
Retakes cost money. Timeline costs money too, because you lose momentum if you're waiting months to try again while your knowledge gets stale. Schedule when you can actually study consistently, not when the calendar looks pretty or your boss suggests it.
ISC2 sets HCISPP prerequisites because the credential only means something if certified people have real experience, not just exam stamina and good test-taking skills. That gatekeeping's annoying when you're eager to move forward, but it also keeps the certification from becoming another badge anyone can buy after a weekend cramming session. I mean, that's the whole point of professional standards, right?
The structure's also more flexible than people assume when they first read the requirements. You don't need a perfect job title. You don't need to have worked at a massive hospital system with thousands of beds. You need the right kind of work, done for long enough, recently enough, and you need to be able to explain it clearly without HR buzzwords.
I spent six months once trying to map my vendor work to these domains while also helping my employer work through their first OCR audit. Talk about timing. The audit taught me more about what ISC2 actually cared about than any study guide did, though I wouldn't recommend that learning method unless you enjoy stress-testing your documentation skills under federal scrutiny.
Baseline requirement? A minimum of two years of cumulative paid work experience in one or more of the six HCISPP domains. Two years. Paid work. Cumulative, so it can be spread across roles and employers. And the experience has to be within the last five years immediately preceding your application date, which actually matters if you did healthcare privacy work a decade ago and then moved into something totally different.
Part-time's acceptable. But it has to add up to roughly two full-time equivalent years, about 4,000 hours. This is where people get sloppy with their math. If you worked 20 hours a week doing privacy and compliance tasks, you can't just call it "two years" unless the hours really stack up properly when you do the calculation.
What counts? A lot, actually, as long as it's hands-on work and tied to healthcare security or privacy outcomes.
Information security roles in healthcare organizations qualify when your responsibilities include protecting PHI. Like securing EHR access, logging, monitoring, incident response, encryption standards, vendor risk reviews, and identity management that directly affects patient data. Privacy officer, compliance officer, or HIPAA coordinator work counts when you're doing policy development, workforce training, investigations, and regulatory adherence, because that's domain work, not "soft" work. Health information management can count too, but only when you're doing security or privacy responsibilities beyond routine records management. Think release-of-information rules, minimum necessary enforcement, audit logging review, or coordinating breach response rather than just processing charts all day.
Other examples you can usually map cleanly: IT security supporting healthcare applications and medical devices, risk management or audit focused on healthcare controls, consulting that includes security assessments or privacy impact assessments, and business associate work where you directly protect or manage PHI. Mentioning "I worked at a vendor" isn't enough. You need the PHI thread running through your responsibilities.
Quick gotchas. Volunteer work doesn't count. Academic study doesn't count. "I sat in meetings" doesn't count unless you were actually responsible for domain activities and deliverables, not just nodding along. Supervisory or management experience can qualify, but only if you were directly involved in the work, not just approving someone else's plan in a quarterly review while thinking about lunch. Document what you did. Dates. Scope. Systems. Regulations. Outcomes. Later-you will thank now-you for being this organized.
After you pass the exam, you've got nine months to complete the endorsement application to actually earn the HCISPP certification. This is the part people don't take seriously until they're staring at the clock and realizing how fast nine months disappears.
Endorsement's ISC2 verifying you meet the experience requirement and that you agree to uphold the ISC2 Code of Ethics without crossing your fingers behind your back. You submit detailed work history: employers, dates, job responsibilities, and which HCISPP domains each role maps to. Then an ISC2 member in good standing endorses you, basically vouching that your experience claims are real and that you're not a dumpster fire ethically.
If you don't personally know an ISC2 member, ISC2 can endorse you through an internal review process. That's normal. It can take longer, honestly, but it works.
The review typically takes 4 to 6 weeks, but complex cases run longer, especially when your experience is spread across roles or your domain mapping's vague and they need clarification. ISC2 may contact employers or ask for supporting documentation like job descriptions, performance reviews, or reference letters. So yeah, keep receipts. Save PDFs. Capture role descriptions before HR "updates" them into generic fluff that says nothing useful.
Also, don't get cute with your application. False or misleading info can get your certification denied, or revoked later if it's discovered after you've been using the credential. Not worth it. Once you're endorsed, you get official notification, you can use HCISPP after your name on email signatures and LinkedIn, and your certification date becomes the anchor for your annual maintenance fee timing and your CPE cycle, which ties directly into HCISPP renewal requirements later.
If you pass the exam but don't have the two years yet, you can become an Associate of ISC2. This is the pressure release valve for recent grads, career changers, and folks in adjacent roles trying to break into healthcare privacy or security without waiting forever to even attempt the test.
Associates can't use the HCISPP designation. You can say you're an "Associate of ISC2." You pay an annual $50 fee to maintain that status. And you have six years from your exam pass date to earn the required experience and then submit the endorsement to upgrade to full certification. Honestly, that's generous. Experience gained after passing counts, so you can pass first, then go build the work history while you're employed and learning on the job.
The thing is, some employers do respect the Associate status. Not all of them. But it signals you cleared the exam and you're serious about this career path, which can help when you're trying to pivot into PHI-facing work from general IT or compliance.
FAQs about HCISPP prerequisites and planning
People always want the quick answers, so here are the common ones, with the career-planning angle that actually matters beyond just passing a test.
How much does the HCISPP exam cost? Check the current ISC2 fee page for your region, then add training, retake risk, and the ongoing annual maintenance fee to get a real number that won't surprise you later.
What is the passing score for the HCISPP exam? ISC2 doesn't make it a simple target you can reverse-engineer with practice test percentages, so plan for broad competency across all domains, then use HCISPP practice tests to find weak domains early while you still have time to fix them.
How hard is the HCISPP certification compared to CISSP? HCISPP exam difficulty's usually less "wide" than CISSP, but it's sharper on healthcare privacy and compliance details, and that can be brutal if you've never lived through HIPAA investigations, BAAs, or clinical workflow constraints that make perfect security impossible.
What are the HCISPP exam objectives and what do they cover? Six domains that blend governance, risk, compliance, privacy, and security operations in healthcare settings. Download the official outline and map your job tasks to it now, not later when you're trying to remember what you did three years ago for endorsement. Wait, I'm getting ahead of myself here.
How do I renew HCISPP and how many CPEs are required? Renewal's tied to CPEs and annual fees, and the exact numbers and cycles should be confirmed on ISC2's current policy pages because they can change. Build a habit of logging CPEs monthly so you're not scrambling at the end of your cycle like most people do.
Download the exam objectives and make a simple domain checklist tied to your real work tasks today. Then start an "endorsement folder" with job descriptions, role dates, and a running list of PHI-related responsibilities, because passing the exam's great, but getting endorsed is what actually turns your score report into HCISPP certification.
Conclusion
Pulling it all together
Okay, so here's the thing: HCISPP certification? It's definitely not your run-of-the-mill cybersecurity cert. Specialized as hell, honestly, but that specificity is precisely what gives it serious clout in healthcare IT and compliance circles where people actually know what they're looking at. If you're working anywhere adjacent to protected health information (PHI) security or actively trying to break into healthcare risk management and compliance roles, this credential signals to hiring managers that you really understand the intersection of HIPAA security and privacy certification requirements meshed with real-world technical controls. Not just theory you memorized last week. Won't sugarcoat it: it's niche. But niche pays dividends when you're literally the only candidate in the room who speaks both HIPAA regulations and InfoSec protocols fluently without needing a translator.
Real talk? The ISC2 HCISPP exam cost won't bankrupt you compared to some of those enterprise-level certs that charge obscene amounts, and the HCISPP renewal requirements aren't remotely unreasonable once you're embedded in the ecosystem naturally earning CPEs through your regular day job anyway. What actually trips candidates up (I mean consistently) is underestimating HCISPP exam difficulty just because it's not as globally famous as CISSP or CISM.
Privacy details alone? They'll wreck you completely if you just skim HCISPP study materials casually on your lunch break. Understanding the operational difference between "minimum necessary" under HIPAA and "least privilege" in traditional security contexts sounds almost trivial in conversation until you're sitting there staring at a scenario question at the testing center and your brain just.. freezes. Those distinctions matter intensely. I once watched a colleague with ten years of network security experience completely bomb this section because he kept defaulting to IT logic instead of healthcare compliance thinking. Different worlds.
Your study plan matters way more than simply how many months you allocate to prep. Some people absolutely crush it in four focused weeks with the right HCISPP practice tests and domain-focused review sessions. Others really need twelve weeks because they're coming from pure IT backgrounds without any healthcare exposure, and that's completely fine and valid. Just be brutally honest about your baseline knowledge and the HCISPP prerequisites knowledge gaps you actually need to fill before sitting for the exam. The HCISPP exam objectives are publicly posted, so there's literally zero excuse for walking in blind to what ISC2 specifically expects you to know about medical data privacy practitioner responsibilities, breach notification timelines, or healthcare cybersecurity certification standards across various regulatory frameworks.
One thing? Made a massive difference for me personally and pretty much everyone I've talked to who passed on their first attempt: quality practice questions that actually explain in detail why wrong answers are wrong, especially around those tricky privacy vs. security edge cases that appear simple but aren't. If you're really serious about passing on your first attempt and confidently hitting that HCISPP passing score threshold, I'd recommend checking out the HCISPP Practice Exam Questions Pack. It's built specifically for the current exam domains and gives you that realistic question exposure you absolutely need before test day arrives.
Schedule your exam. Build your checklist.
You've got this.