Isaca CDPSE (Certified Data Privacy Solutions Engineer)
Understanding the ISACA CDPSE Certification and Its Value in Privacy Engineering
What is the ISACA CDPSE certification?
The ISACA CDPSE exam represents the industry's premier credential for privacy engineering professionals who design, build, and implement privacy-by-design solutions within organizational technology ecosystems. I've watched this certification emerge over the past few years, and honestly it's filling a gap that desperately needed filling. There were plenty of compliance-focused privacy certs out there, but nothing that really spoke to the technical folks actually building the systems, you know?
Real technical validation here. The Certified Data Privacy Solutions Engineer designation validates technical competency in translating privacy requirements into engineered controls, distinguishing it from compliance-focused privacy certifications. This isn't about reading GDPR articles and writing policies (though you've gotta understand that stuff). It's about taking those requirements and actually implementing them in code, infrastructure, and system architecture. The ISACA privacy certification emerged in response to growing demand for professionals who can operationalize privacy principles through technical architecture, not just policy documentation that sits in a SharePoint folder somewhere gathering digital dust.
CDPSE bridges the gap between privacy governance frameworks like GDPR, CCPA, and other privacy regulations with actual system implementation, making it essential for privacy engineers, security architects, and technical privacy practitioners. I mean, how many times've you seen a DPO write a beautiful privacy policy only to have the dev team stare blankly when asked to implement it? That's exactly the problem CDPSE solves.
Who CDPSE is for (privacy, security, risk, engineering, GRC)
The CDPSE certification targets professionals who work at the intersection of privacy, security, and engineering. Those responsible for embedding privacy controls into applications, infrastructure, and data processing systems. Ideal candidates include privacy engineers (obviously), security architects supporting privacy initiatives, data protection officers with technical responsibilities, application security engineers, cloud architects, and GRC professionals transitioning to technical privacy roles.
Privacy engineers benefit most since CDPSE directly validates their core competency in designing privacy-enhancing technologies, implementing data minimization, and building privacy controls into system architecture. Security architects gain recognition for privacy-specific expertise, demonstrating capability to incorporate privacy by design principles into security architecture and threat modeling processes. Not gonna lie, if you're already doing threat modeling, adding privacy considerations isn't a huge leap, but having the formal knowledge and credential makes a massive difference in how organizations perceive your expertise and whether they'll actually listen when you raise concerns in architecture reviews.
Data protection officers and privacy managers with technical backgrounds use CDPSE to strengthen implementation oversight capabilities and communicate more effectively with engineering teams. Compliance and GRC professionals use the certification to transition from policy-writing roles into technical privacy implementation, significantly expanding career opportunities. I've seen several GRC folks make this transition. Their salaries jumped considerably. Honestly, we're talking 30-40% increases in some cases.
DevOps engineers find value too. Platform engineers working with sensitive data use CDPSE to formalize privacy knowledge and take ownership of privacy requirements in CI/CD pipelines and infrastructure-as-code. Cloud architects and solutions architects benefit by demonstrating competency in implementing privacy controls across multi-cloud environments, particularly for data residency, encryption, and access controls.
What roles benefit (privacy engineer, security architect, DPO support, compliance lead)
The privacy engineering certification distinguishes technical practitioners from compliance-focused privacy professionals, commanding higher salaries and opening specialized roles in technology companies. Organizations increasingly require CDPSE-certified professionals to lead privacy-by-design initiatives, conduct privacy impact assessments with technical depth, and implement data protection controls across complex technology stacks.
Career advancement opportunities expand dramatically. You're looking at senior privacy engineer roles, privacy architecture positions, technical privacy leadership, and consulting roles requiring both privacy expertise and technical implementation skills. Salary premium for CDPSE-certified professionals ranges from 15-25% compared to non-certified peers in similar technical privacy roles, with higher premiums in regulated industries. That's real money we're talking about.
CDPSE exam overview
The certification demonstrates mastery of privacy governance frameworks, privacy architecture principles, and data lifecycle management. The three core domains essential for engineering privacy solutions. CDPSE holders understand how to assess privacy risks from a technical perspective, select appropriate privacy-enhancing technologies, and validate that implemented controls meet privacy requirements.
Exam format (questions, timing, delivery)
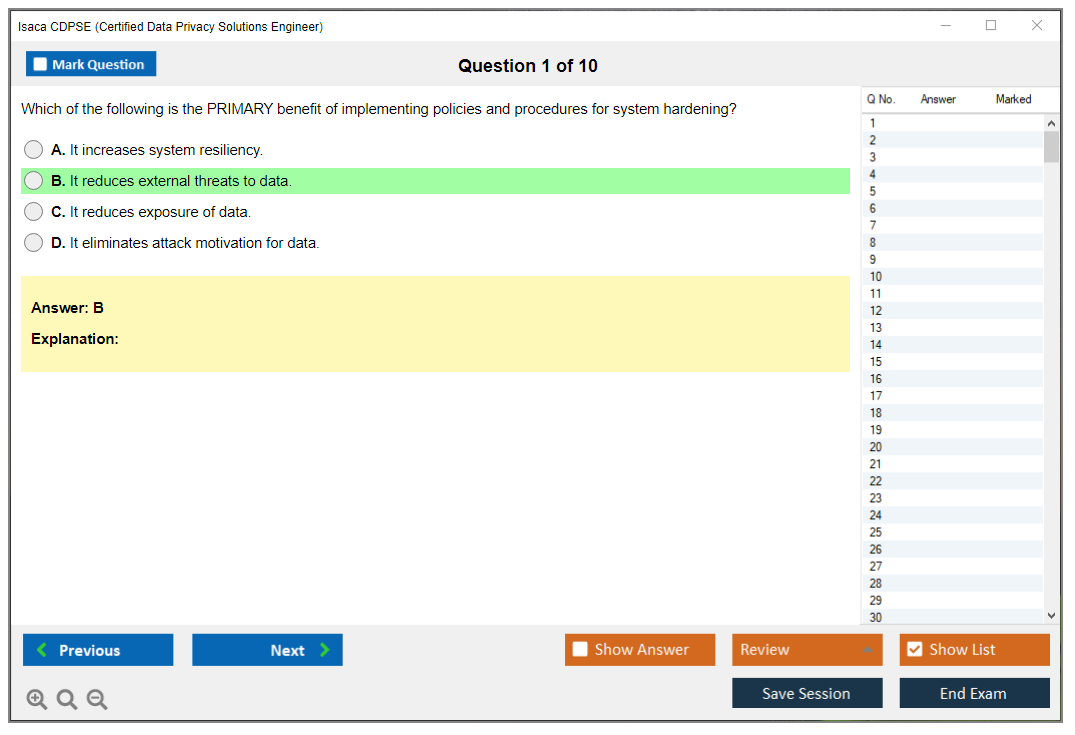
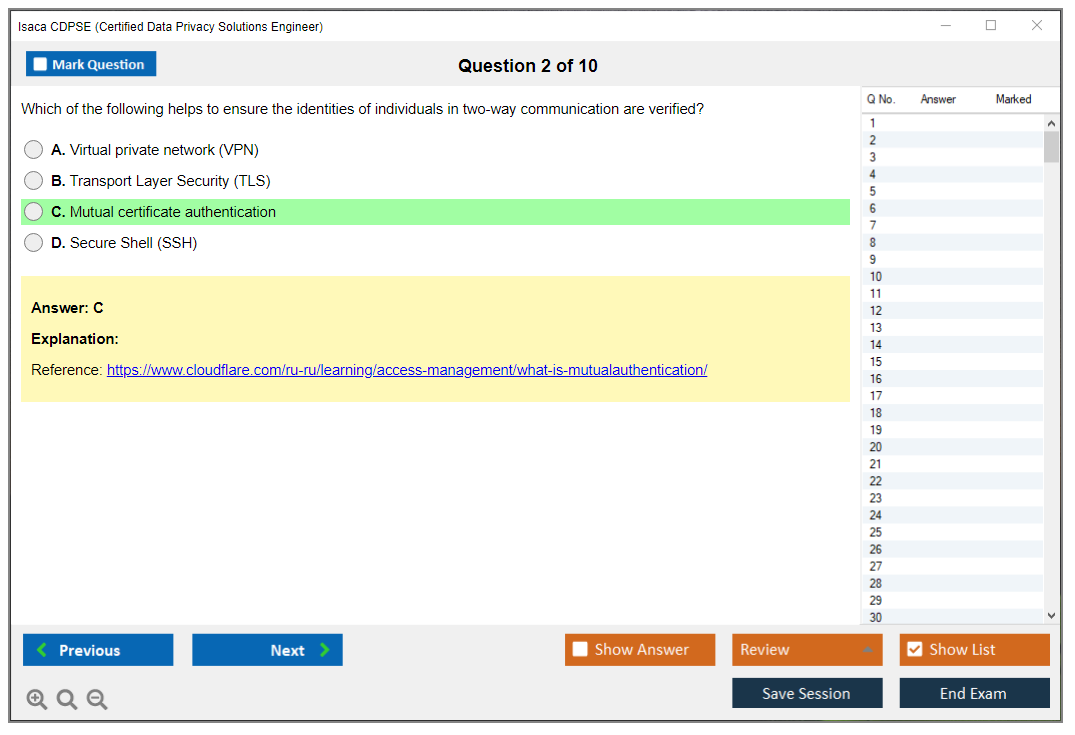
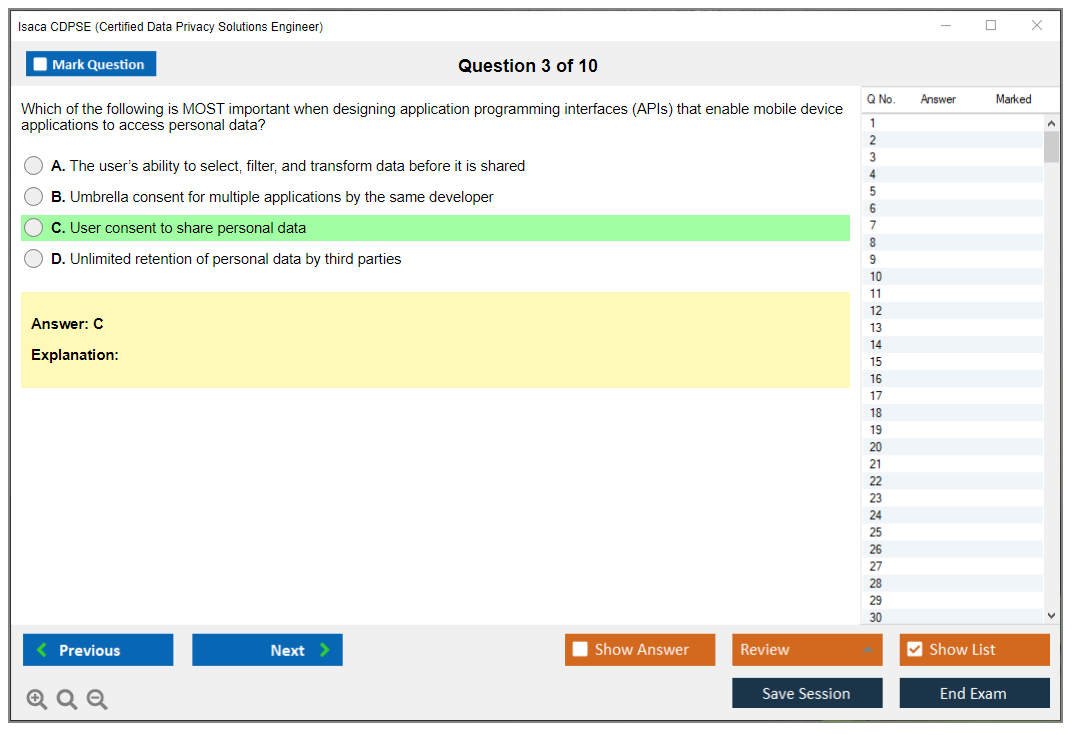
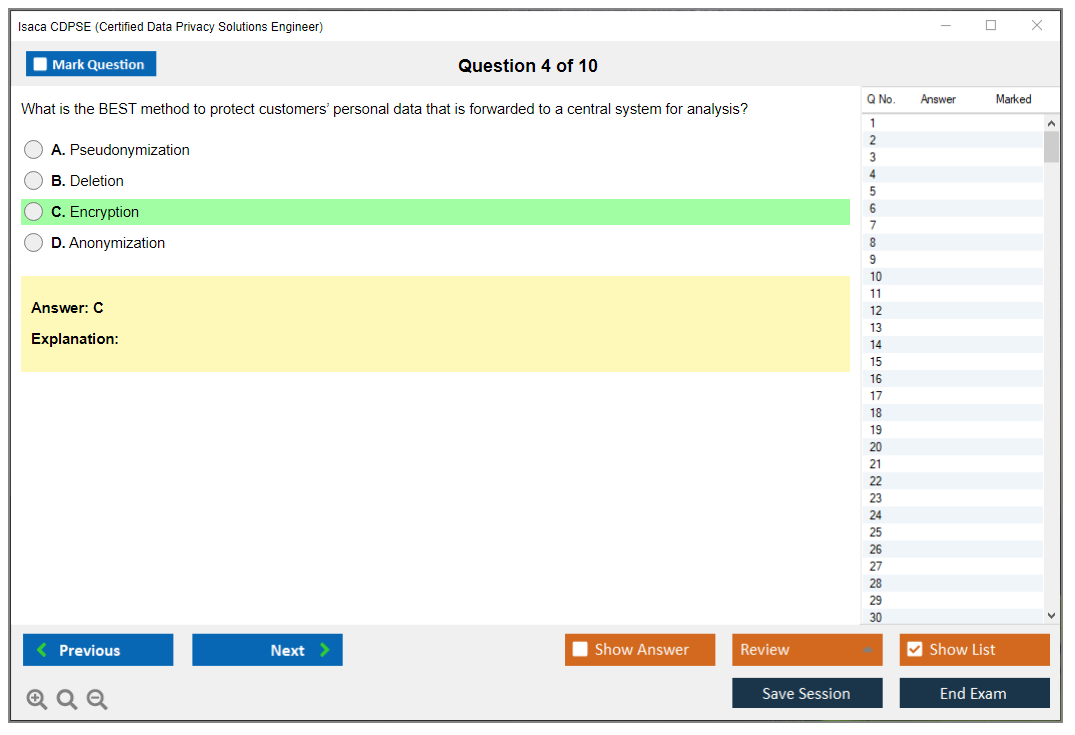
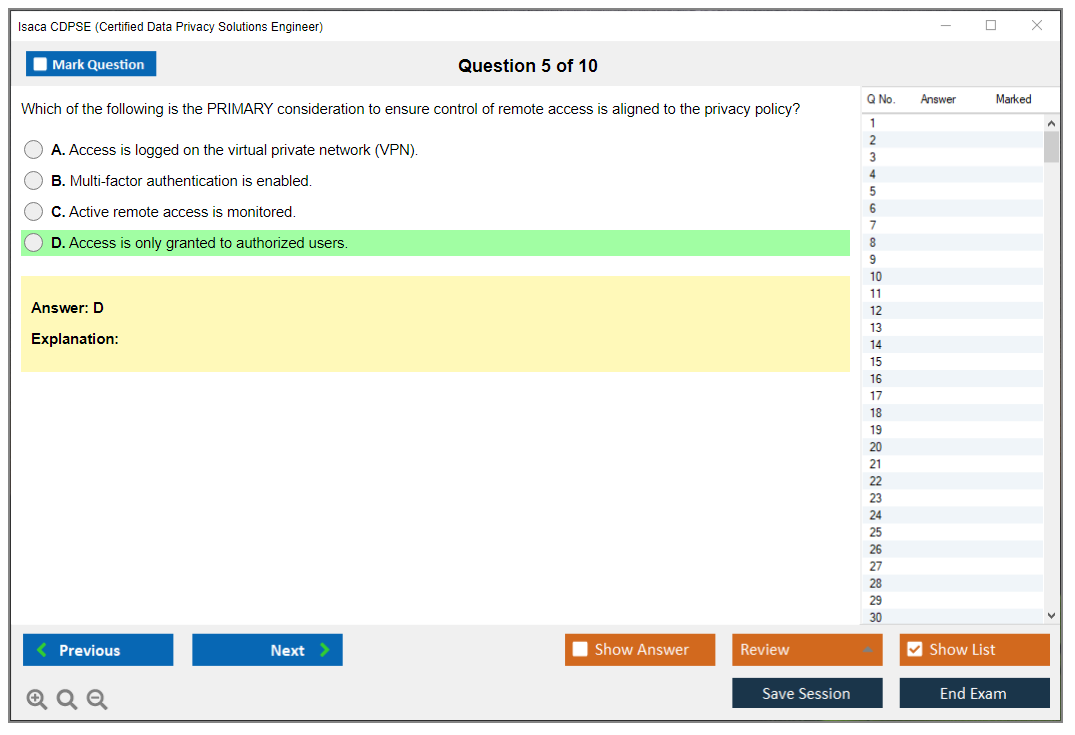
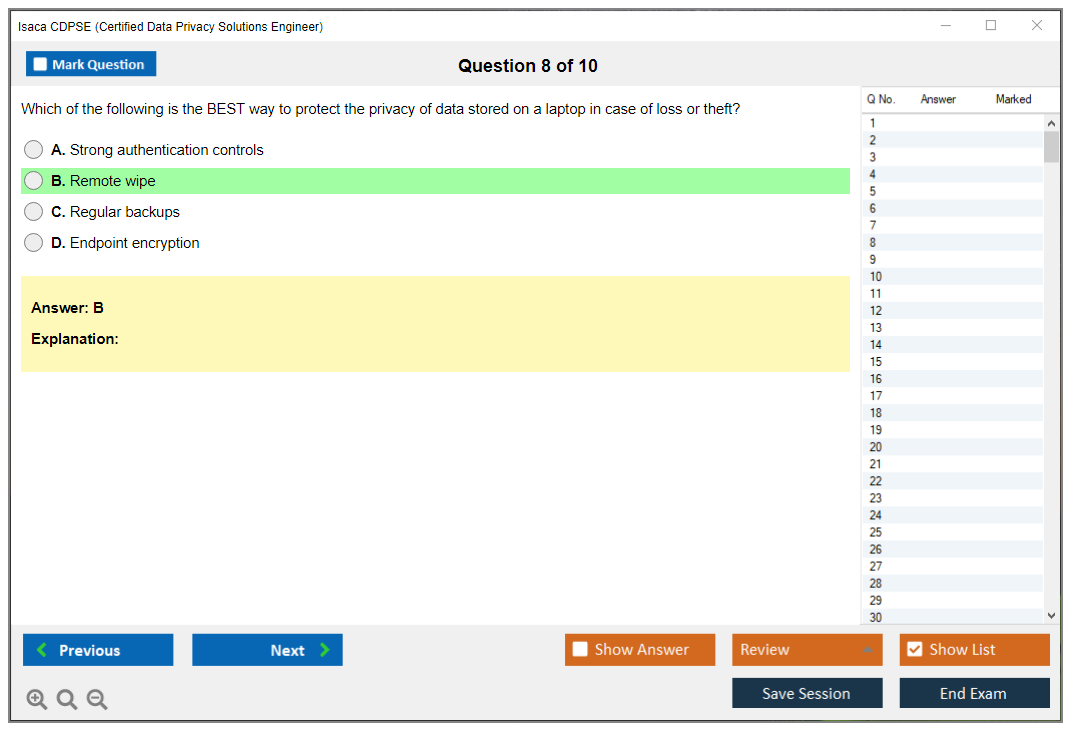
The exam consists of 150 questions delivered over four hours through Pearson VUE testing centers or online proctoring. It's all multiple-choice, but these aren't your typical cert exam questions. They're scenario-based and require you to actually think through privacy engineering problems, considering context, constraints, and competing requirements. You can't just memorize definitions and pass.
CDPSE exam objectives (domains)
Three domains total. Privacy Governance (25%) tests your understanding of governance frameworks, regulatory requirements, and organizational privacy program structures. Privacy Architecture (40%) is the meat of the exam. This covers designing privacy controls, implementing privacy-enhancing technologies, and integrating privacy into system architecture. Data Lifecycle (35%) focuses on privacy considerations throughout data collection, processing, storage, sharing, and disposal.
Look, the Architecture domain's weighted heaviest for a reason. That's where the rubber meets the road in privacy engineering.
CDPSE cost (exam fees and total certification cost)
The certification's vendor-neutral approach ensures relevance across technology platforms, programming languages, and cloud providers, unlike vendor-specific privacy credentials. CDPSE complements security certifications like CISM and CISA by adding specialized privacy engineering depth, and complements IAPP certifications by adding technical implementation expertise.
CDPSE exam registration cost (member vs non-member)
Honestly, the pricing structure matters here. ISACA members pay $575 for the exam, while non-members pay $760. The membership itself costs $135 annually, so if you're not already a member, you still save money by joining first. Plus you get access to member-only study resources. Total first-year cost runs around $710 for members including membership fees.
Other costs to plan for (training, books, practice tests, retake fees)
Budget beyond exam registration because study materials add up fast. The official CDPSE Review Manual costs $110 for members, $150 for non-members. The Question and Answer Database runs about $60. If you want formal training, ISACA's official course costs $1,395 for members, $1,695 for non-members. Though honestly, many people pass without it if they've got strong technical privacy experience already.
Retake fees match initial costs, so you really wanna pass first attempt. Factor in maybe $200-400 for supplementary books on privacy engineering, GDPR technical requirements, and privacy-enhancing technologies. I once spent an entire weekend reading about differential privacy algorithms just to understand one exam domain better. Total rabbit hole, but it paid off.
CDPSE passing score and scoring
Organizations pursuing privacy maturity models, zero-trust architectures, or privacy-by-design initiatives specifically seek CDPSE-certified professionals to lead technical implementation efforts. The credential validates understanding of privacy regulations from an engineering perspective. Knowing not just what regulations require, but how to technically implement compliant solutions.
What the CDPSE passing score is (scaled scoring)
ISACA uses scaled scoring with a range of 200-800, and 450 is the passing score. You're not scored on raw percentage correct because the scaling adjusts for exam difficulty. This means you don't necessarily need to answer 75% of questions correctly. The actual percentage varies by exam form.
How scoring works and what to aim for by domain
Each domain contributes based on weighting, and you'll receive domain-level feedback showing whether you performed above, at, or below proficiency in each area. Aim to score well above proficiency in Privacy Architecture since it's 40% of your score. You need strong performance there to offset any weaker areas, plain and simple.
CDPSE difficulty: how hard is the exam?
CDPSE certification demonstrates commitment to the emerging privacy engineering discipline, positioning professionals at the forefront of this rapidly growing field. As privacy regulations expand globally and privacy becomes a competitive differentiator, demand for CDPSE-certified professionals continues accelerating across industries.
What makes CDPSE challenging (scenario-based privacy engineering)
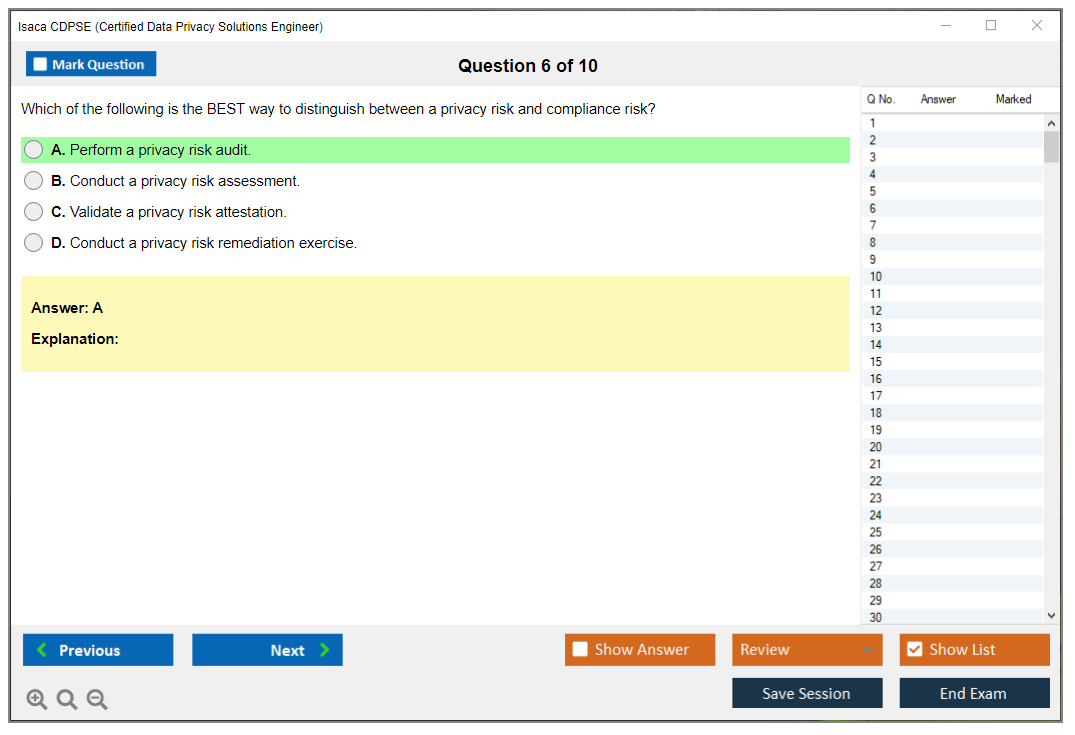
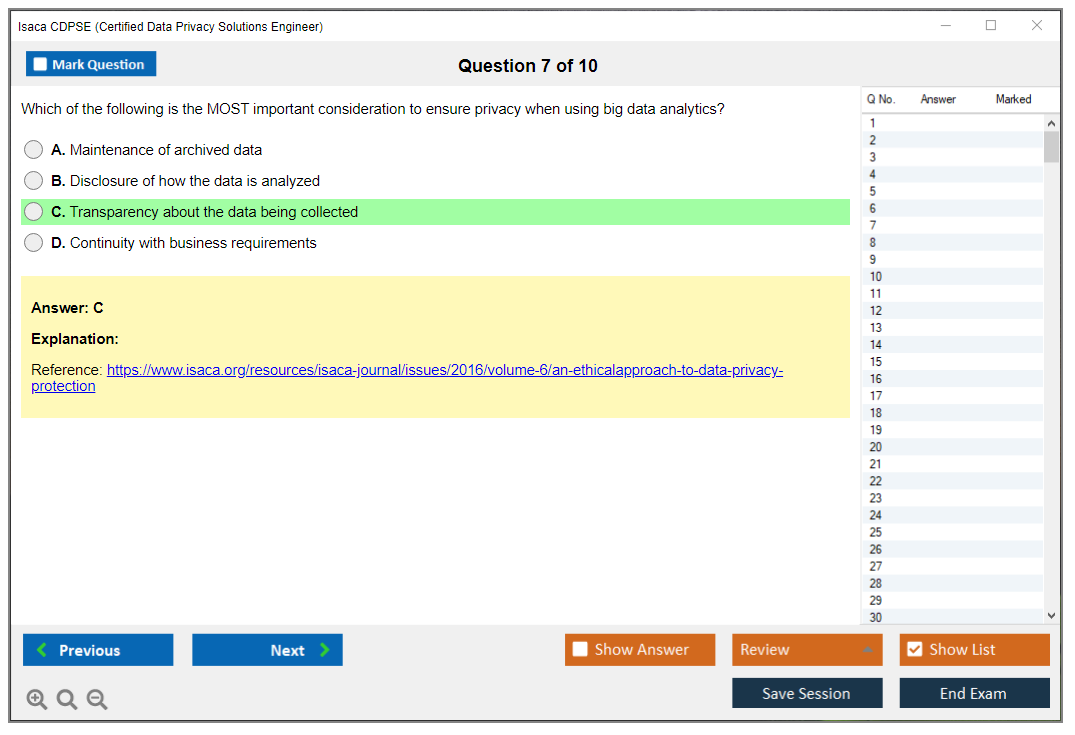
Real difficulty here. The exam's challenge stems from its scenario-based questions requiring application of privacy engineering principles to real-world situations. You're not just identifying what a privacy control is. You're selecting the appropriate control for a specific technical context, understanding implementation tradeoffs, and recognizing when controls conflict with other requirements like performance or user experience.
Many questions present complex scenarios involving multiple privacy principles, regulatory requirements, and technical constraints. You've gotta synthesize all that information and pick the best answer, not just a correct answer.
Difficulty by background (privacy/GRC vs security/engineering)
Your background significantly impacts difficulty. Security engineers and architects typically find the technical implementation aspects straightforward but struggle with privacy governance details and regulatory requirements. GRC professionals and privacy managers face the opposite challenge. They know the regulations cold but struggle with technical implementation details like encryption selection or anonymization techniques.
Privacy engineers with balanced backgrounds have the easiest path, though the exam still requires dedicated study. I'd say it's comparable in difficulty to CRISC if you're coming from security, maybe slightly easier than CGEIT if you're coming from governance.
How long to study (typical timelines)
Most candidates need 8-12 weeks of study at 10-15 hours weekly. Those with strong privacy engineering experience can compress this to 6-8 weeks. Career-changers from pure compliance or pure security roles should plan 12-16 weeks. Don't rush it. The exam's scenario-based nature requires deep understanding, not surface memorization.
CDPSE prerequisites and eligibility requirements
The certification provides framework-agnostic privacy engineering knowledge applicable to NIST Privacy Framework, ISO 27701, GDPR Article 25, and other privacy-by-design mandates. The credential's value extends beyond any single regulation or framework, making it relevant globally.
Required work experience (how many years and what counts)
ISACA requires three years of experience. Experience must include privacy, security, or IT with at least two years specifically in privacy engineering or related technical privacy work. Experience must involve designing, implementing, or supporting privacy controls in technology systems. Project management, compliance auditing, or pure policy work generally doesn't count.
Substitutions/waivers (if applicable) and documentation
You can substitute experience though. Up to two years swap with relevant education or other certifications. A four-year degree in information technology, computer science, or related field substitutes for two years. IAPP CIPT certification substitutes for one year. CISSP or similar security certifications substitute for one year.
How to apply for certification after passing
After passing, submit your certification application through ISACA's website. You'll document work experience, providing employer verification, job descriptions, and specific details about your privacy engineering responsibilities. ISACA reviews applications and may request additional documentation. Plan 4-6 weeks for application processing.
Best CDPSE study materials (official and third-party)
Look, the official ISACA materials should form your foundation, but you'll probably need supplementary resources depending on your background gaps.
Official ISACA resources (review manual, QAE, training)
The CDPSE Review Manual's essential because it covers all exam objectives and provides domain-specific guidance. The Questions, Answers and Explanations database gives you 400+ practice questions with detailed explanations. These explanations often teach as much as the manual itself, honestly. The official training course is full but expensive. Consider it only if you need structured learning or your employer's paying.
Recommended books and references (privacy engineering, governance, controls)
"Privacy Engineering" by Michelle Finneran Dennedy, Jonathan Fox, and Thomas Finneran is practically required reading. It covers privacy-by-design implementation in depth with real-world examples that'll help you understand how these principles apply in actual system development. NIST's Privacy Framework documentation is free and excellent for understanding privacy governance from a technical perspective. The GDPR text itself, particularly Article 25 on data protection by design and by default, should be studied carefully with focus on technical requirements.
Dive into NIST documentation. For data lifecycle management, look into NIST SP 800-122 on protecting confidentiality of personally identifiable information. For privacy-enhancing technologies, research papers and vendor documentation on differential privacy, homomorphic encryption, secure multi-party computation, and anonymization techniques provide depth beyond what the review manual covers.
Study plan by domain (privacy governance, architecture, lifecycle)
Start with Privacy Governance even though it's only 25%. You need this foundation to understand why privacy engineering matters. Spend about 2-3 weeks here understanding regulatory requirements, governance frameworks, and organizational privacy program structures.
Privacy Architecture deserves serious time, so allocate 5-6 weeks since it's 40% of the exam. Focus on designing privacy controls, selecting appropriate privacy-enhancing technologies, and integrating privacy into system architecture and SDLC. Work through scenarios involving different architectural patterns like microservices, cloud-native, legacy systems.
Data Lifecycle takes 3-4 weeks to cover properly. You'll need to understand privacy considerations for collection, processing, storage, sharing, retention, and disposal. Understand technical controls at each stage and how to implement data minimization, purpose limitation, and storage limitation principles.
CDPSE practice tests and exam prep strategy
Honestly, practice tests make or break your preparation. They reveal knowledge gaps and train you for the exam's question format.
Where to find CDPSE practice questions (QAE, banks, labs if used)
The official QAE database's your primary source since you're getting 400+ questions reflecting actual exam difficulty and format. Third-party practice tests exist but verify they're updated for current exam objectives. Some privacy engineering training platforms offer scenario-based labs. These help with practical understanding but aren't direct exam prep.
How to use practice tests effectively (timed sets, error log, weak domains)
Don't just grind questions mindlessly. Take timed 50-question sets simulating exam conditions. Review every question, even ones you got right, to understand why wrong answers are wrong. Keep an error log categorizing mistakes by domain and topic. If you're consistently missing questions about specific privacy-enhancing technologies or particular regulatory requirements, that's your signal to review those areas.
Common mistakes and how to avoid them
Common mistakes include overthinking questions, choosing "ideal" answers instead of "best" answers given constraints, and mixing up similar privacy controls. Many candidates struggle with questions involving tradeoffs between privacy and other requirements like functionality, performance, or security. The exam expects you to balance these realistically, not choose absolute privacy every time like you're some sort of privacy absolutist.
CDPSE renewal requirements (maintenance and CPE)
Certification doesn't end at passing, so you've gotta maintain it through continuing education and annual fees.
CPE requirements and reporting cycle
CDPSE requires 120 CPE hours spread over a three-year certification period, with a minimum of 20 hours annually. You report CPE hours through ISACA's certification portal. CPE activities must relate to privacy, security, governance, or technical domains covered by CDPSE.
Annual maintenance fees (member vs non-member)
Annual maintenance fees run $45 for ISACA members, $85 for non-members, and this's separate from membership fees. Miss the payment and your certification becomes inactive, requiring reinstatement fees and potentially retaking the exam if you wait too long.
What activities count for CPE (training, webinars, work activities)
Qualifying activities include formal training courses, conferences, webinars, self-study, professional presentations, published articles, and certain work activities. Teaching privacy engineering topics earns CPE. Attending privacy-focused conferences like IAPP summits counts. Even reading privacy engineering books and articles counts if documented properly. Volunteer work for ISACA or privacy organizations qualifies.
Similar ISACA certifications like COBIT-2019 or IT Risk Fundamentals might share CPE activities if they overlap in content areas, which's a nice efficiency gain for multi-cert holders.
CDPSE Exam Structure, Format, and Core Domain Objectives
What is the ISACA CDPSE certification?
The CDPSE certification (Certified Data Privacy Solutions Engineer) is ISACA's privacy engineering certification for folks who exist between policy and systems. Not lawyers. Not pure compliance. More like the person who reads a DPIA, then goes and rewires the architecture, the logging, the access model, and the retention jobs so the thing actually works the way it's supposed to.
ISACA built this as an ISACA privacy certification that expects you to think like an engineer with governance awareness, which honestly makes sense when you consider how many orgs have compliance frameworks that look great on paper but fall apart when you look at the actual infrastructure. Nobody enforces retention. The consent records are stored in three different places with no single source of truth. You're expected to understand why a requirement exists, then implement it with data protection controls that hold up in production.
Who CDPSE is for (privacy, security, risk, engineering, GRC)
Security architects. Privacy engineers. GRC folks who got tired of writing policies nobody implements.
Also product and platform engineers. The ones who keep getting pulled into "quick privacy review" meetings.
What roles benefit (privacy engineer, security architect, DPO support, compliance lead)
Privacy engineer? Obvious choice.
Security architect comes in close second.
DPO support roles benefit too, because you'll finally be able to translate "data minimization" into specific technical decisions. Event payload trimming. Short-lived identifiers. Retention enforcement that isn't just a spreadsheet someone updates quarterly and then ignores.
CDPSE exam overview
The ISACA CDPSE exam is 150 multiple-choice questions, computer-based, delivered at Pearson VUE testing centers or via online proctored exam. Four hours (240 minutes). That's about 1.6 minutes per question, and the thing is, that's the first gotcha because long scenarios will tempt you to reread the same paragraph three times.
All questions are scenario-based. No flashcard vibes. You're applying privacy engineering principles to realistic org situations, where requirements conflict, stakeholders disagree, and the "best" answer is the one that manages risk while staying implementable.
Most items test analysis and decision-making: interpret privacy requirements, evaluate solution options, recommend controls, and assess whether the implementation's effective. Effectiveness means evidence, monitoring, metrics, and feedback loops. Not "we turned on encryption."
Exam format (questions, timing, delivery)
150 questions. Four hours. Computer-based.
A few short sentences. Time disappears fast. Don't drift.
The practical move is to do a first pass with momentum, mark the slow ones, then circle back. If you spend five minutes on question 7, you'll pay for it at question 120 when your brain's cooked and you still have 40 items left.
CDPSE exam objectives (domains)
The CDPSE exam objectives are split into three domains with different weights. Privacy Governance is the base layer, then Privacy Architecture and Data Lifecycle build on that with implementation details and operational control thinking. People with only policy backgrounds sometimes feel punched in the face by the technical depth.
- Privacy Governance (26%, about 39 questions)
- Privacy Architecture (34%, about 51 questions)
- Data Lifecycle Management (40%, about 60 questions)
Privacy Governance
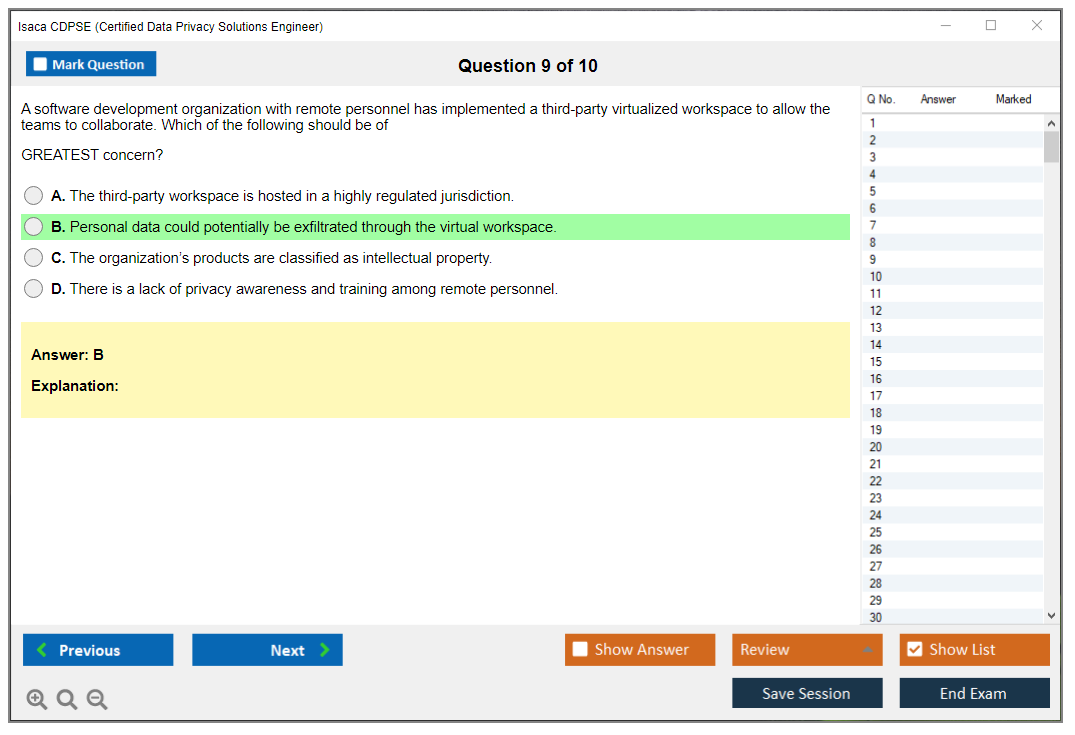
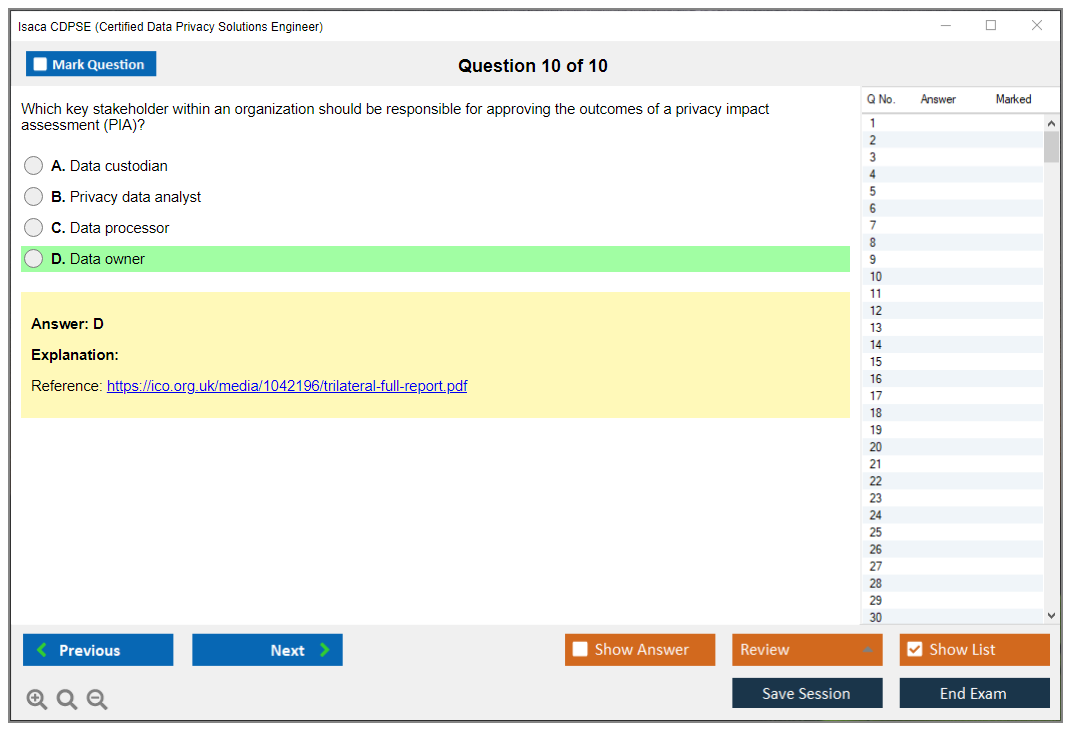
Domain 1 is about establishing and maintaining governance that makes privacy by design real across the org. That includes privacy strategy, the regulatory environment, risk assessment methods, PIAs/DPIAs, and the structures that make accountability possible.
You need familiarity with frameworks like the NIST Privacy Framework, ISO 27701, and GDPR principles, plus privacy maturity models and how privacy goals align with business objectives. Not in a fluffy way either. More like, "What governance artifacts force engineering teams to build consent capture correctly, document lawful basis, and set retention defaults that match policy?"
Expect questions where you translate policy into technical requirements. Define roles and responsibilities. Set accountability mechanisms. You'll see privacy risk assessment from business and technical angles, including risks in system design, data flows, and third-party relationships.
PIA/DPIA content is heavily tested. Triggers. Methodology. Technical elements. Where in the SDLC it should happen and what you do when the assessment finds high risk. "We'll accept the risk" isn't always a valid answer depending on the scenario constraints.
Metrics matter here too. KPIs. Monitoring. Control effectiveness. Look, things like DPIA completion rates are nice, but coverage of high-risk processing, DSAR fulfillment time, and exception rates on retention enforcement are the kinds of measures that show whether controls work.
Privacy Architecture
Domain 2 is the biggest technical design chunk. It tests your ability to translate privacy requirements into specs, pick privacy-enhancing technologies (PETs), and design architectures that preserve privacy without breaking the business.
Privacy by design principles show up constantly: proactive protection, default privacy, embedded privacy, lifecycle protection, and user-centric approaches. The exam likes to put you in a messy scenario, like a microservices platform with shared logging and a data lake downstream, then ask what you change first to reduce risk while maintaining functionality. This is exactly the kind of decision you'll make in real work anyway, just without the timer.
You're expected to know controls across the application layer, data layer, infrastructure layer, and network layer. PETs include encryption (at-rest, in-transit, and in-use), tokenization, anonymization, pseudonymization, differential privacy, homomorphic encryption, and secure multi-party computation. Some of those are "know what it's for" more than "derive the math," but you should be able to pick the right tool for the requirement. Choose tokenization for operational reversibility versus anonymization when you truly don't need re-identification.
Access control shows up constantly: RBAC, ABAC, just-in-time access, privileged access management, least privilege. Data minimization is also big, and it's "collect less." You'll see purpose limitation, storage limitation, and technical methods like schema design choices, logging redaction, field-level encryption, and retention automation.
Other topics get mentioned and can pop up: API privacy controls, cloud architecture privacy, and design patterns versus anti-patterns (like over-sharing via internal APIs because "it's trusted network" which is, not gonna lie, a classic failure mode). Consent management systems, preference centers, privacy notices, and technical controls for data subject rights (access, rectification, erasure, portability) are fair game.
Secure data sharing is increasingly tested too: data clean rooms, privacy-preserving record linkage, federated learning. You don't need to be a research scientist, but you do need to recognize when centralizing raw data is the wrong move.
Speaking of wrong moves, I once watched a vendor pitch a "privacy solution" that was literally just S3 buckets with better folder names. Not even encryption. Just folders. The exec team nodded along like it made sense. That's the level of theater you're avoiding by actually understanding this stuff.
Data Lifecycle Management
Domain 3 is 40% of the exam, around 60 questions, and it's about controls across collection, processing, storage, sharing, retention, and disposal. This is where lots of people lose points because they know the principles, but they haven't actually implemented them end-to-end, so the scenario questions feel slippery.
Collection phase: consent mechanisms, notice requirements, collection limitation, purpose specification, lawful basis determination. Processing phase: enforcing purpose limitation, data quality, transparency, safeguards for automated decision-making, and maintaining processing records.
Sharing and disclosure: third-party risk management, DPAs, cross-border transfer mechanisms, and enforcing sharing limits. Retention: retention schedules, automated enforcement, legal holds, defensible disposition. Disposal: secure deletion, sanitization standards, destruction verification, documentation.
You'll also get DSAR implementation questions, which are more technical than people expect: automated discovery, extraction, rectification, and erasure across systems, plus how you prove you did it. Data mapping and inventory management are foundational here. This includes automated discovery tools, data classification, and metadata management, because you can't protect what you can't find.
Emerging tech shows up in lifecycle context: AI/ML, IoT, blockchain, biometrics. Usually the question is, "What privacy risk does this introduce and what control actually fits," not "explain blockchain."
CDPSE cost (exam fees and total certification cost)
People ask: How much does the ISACA CDPSE exam cost? The CDPSE exam cost depends on whether you're an ISACA member, and ISACA updates pricing, so check the official fee page before you budget.
Other costs to plan for (training, books, practice tests, retake fees)
Plan for CDPSE study materials, maybe a course if you need structure, and a retake cushion if your employer won't cover it. Add the certification application and annual maintenance fees too. Honestly? It adds up fast.
CDPSE passing score and scoring
What is the passing score for the CDPSE exam? ISACA uses scaled scoring, and the CDPSE passing score is 450 (on a 200 to 800 scale). That doesn't mean "get 56% right" or any clean number. It's scaled.
How scoring works and what to aim for by domain
Aim to be comfortable in all three domains, because bombing one big domain like Data Lifecycle is hard to recover from given the weighting. I mean, you can't "make it up" with Governance if Lifecycle is where 40% of the questions live.
CDPSE difficulty: how hard is the exam?
How hard is the CDPSE certification exam? Harder than people expect if they've only done policy work, and also tricky for pure engineers who haven't lived through DPIAs, third-party reviews, or cross-border transfer constraints.
What makes it challenging is the scenario style. You're often picking the best next step, or the most appropriate control, under constraints like budget, legacy systems, regulatory requirements, and business timelines. The distractor answers are usually things that are "true" but not the best choice for that specific situation.
CDPSE prerequisites and eligibility requirements
CDPSE prerequisites include professional experience requirements set by ISACA, and you'll need to document your work history when you apply after passing. Check ISACA's current policy for the exact number of years and what counts, because that's one of those details that can change and you don't want to get surprised at application time.
Best CDPSE study materials (official and third-party)
For CDPSE study materials, start with ISACA's official review manual and the QAE database. Add references that cover privacy engineering and architecture, like materials on PETs, identity and access management, cloud security architecture, and DPIA practice.
One more thing. Read real DPIA templates. Seriously.
CDPSE practice tests and exam prep strategy
A CDPSE practice test is only useful if you use it like a feedback tool. Timed sets. Error log. Rework missed questions and write down why the right answer is right, and why your pick was tempting.
Common mistakes: over-focusing on encryption, ignoring data minimization, and treating consent like a UI checkbox instead of a system of record with auditability and downstream enforcement.
CDPSE renewal requirements (maintenance and CPE)
People also ask: How do I renew my CDPSE certification and maintain CPEs? CDPSE renewal requirements follow ISACA's CPE model with reporting cycles and annual maintenance fees (member versus non-member). Activities that count include training, webinars, conferences, and sometimes relevant work outputs, depending on ISACA's rules, so keep receipts and a simple tracking spreadsheet from day one.
CDPSE FAQ
What are the CDPSE exam domains and objectives? Three domains: Privacy Governance (26%), Privacy Architecture (34%), Data Lifecycle Management (40%).
Retake policy and scheduling tips. Book early for Pearson VUE. Online proctoring is convenient, but your desk, room, and network need to be boring and stable. Interruptions are the fastest way to waste a testing day.
CDPSE Exam Cost Breakdown and Total Investment Planning
The real cost of getting CDPSE certified
Okay, real talk here. The CDPSE exam cost isn't just the registration fee you hand over to ISACA. I mean, yeah, that's the number that'll make you wince initially, but if you're actually serious about passing this beast on your first attempt (and honestly, you really want to because retakes aren't cheap), you've gotta think way beyond that single line item.
Actual exam registration? $760 USD for non-members. That's your starting point, the baseline you can't avoid. But here's where things get kinda interesting, and this is something a lot of people miss when they're first researching this: ISACA members only pay $575 USD. We're talking about a $185 difference sitting right there. Now, membership itself runs $135 annually for standard tier, so you're already $50 ahead just by joining for this one exam alone.
The real value? It kicks in when you're maintaining certification long-term or eyeing other credentials like CISM or CRISC down the line. I've personally watched colleagues grab membership thinking they'd do one cert and bail, then they ended up chasing the entire privacy and security track because, well, career momentum's a thing. One guy I know got CDPSE, then six months later he's texting me about whether CISA or CRISC should come next. That's how it goes.
Breaking down what membership actually gets you
Look. Not perfect.
I'm not gonna sit here and tell you ISACA membership is some magical solution to everything, but for CDPSE certification candidates it usually makes financial sense. Beyond just the exam discount, you're getting reduced pricing on literally every single thing they sell. The official CDPSE Review Manual? $95 for members versus $125 if you're paying full freight. The Questions, Answers & Explanations database (which, the thing is, you really should get this one) runs $99 member pricing versus $129 non-member. These differences pile up shockingly fast when you're actually budgeting out the whole preparation package.
Plus there's access to member-only webinars and networking opportunities that don't completely suck. Not gonna lie here, some webinars are dry as dust, but you'll occasionally stumble onto one that actually covers real-world implementation scenarios that really help with those scenario-based exam questions.
Study materials are where costs spiral
This is where budget planning gets very real, very fast. The CDPSE exam registration cost stays fixed no matter what, but study materials? That's a total choose-your-own-adventure financial situation.
On the lean end, you could grab just the official Review Manual and the QAE database. That's roughly $194 for members ($254 non-members) stacked on top of your exam fee. Totally doable. I know people who passed with exactly those two resources, especially folks who already had solid privacy engineering experience under their belts.
But here's the thing, and I feel like I should interrupt myself here because, okay, most people actually need more than that. Official ISACA training courses range from $1,095 all the way up to $1,795 depending on whether you do on-demand or instructor-led formats. The instructor-led sessions are honestly better if you can swing both the cost and the schedule coordination, because you can actually ask questions about those tricky privacy by design implementation scenarios that trip people up. The on-demand stuff? Fine, I guess, but you're basically watching recorded sessions without interaction.
Third-party options exist too. Video courses and practice platforms from various providers run anywhere from $50 to $400. Some are really great, some are absolute garbage. The CDPSE Practice Exam Questions Pack at $36.99 gives you solid practice scenarios without obliterating your budget. When you're drilling practice questions repeatedly, you want variety and different question formats, not just the official QAE questions memorized word-for-word like some kind of robot.
Then there's supplementary reading materials. If you're coming from a security background but don't have deep privacy engineering experience, you'll probably want some reference books covering privacy architecture and data protection controls implementation. Budget another $100-200 for technical privacy resources. I grabbed three books when I was studying and honestly only seriously used two of them, but that's just how this process goes sometimes.
The retake reality nobody wants to discuss
Here's something uncomfortable we need to address: the retake fee matches your initial registration exactly. $760 for non-members, $575 for members.
This is precisely why skimping on preparation is a false economy that bites you later. I've watched colleagues try saving money by doing minimal prep, fail the exam, then have to pay the whole exam fee again PLUS spend more time studying when they're already demoralized. The CDPSE passing score uses scaled scoring (typically around 800 on a 200-800 scale based on what I've seen reported in study groups) and those scenario-based questions are absolutely brutal if you haven't practiced enough beforehand.
Exam delivery? Pearson VUE handles it. Good news here: testing center fees are included in your ISACA registration, so no surprise charges there. If you do the online proctored version instead, make sure you've got a decent webcam and stable internet connection. I did mine at a testing center because I didn't want to risk technical issues at home derailing everything, but that's totally personal preference.
Total investment scenarios
Let's run actual numbers.
Budget-conscious approach for a non-member: $760 exam + $125 review manual + $129 QAE = $1,014 baseline. Add maybe $50 for a practice exam pack and you're sitting at $1,064. That's your absolute minimum viable budget.
For members doing that same minimal approach: $135 membership + $575 exam + $95 review manual + $99 QAE = $904 total. Already cheaper than the non-member minimal route, which is kinda wild when you think about it.
Full preparation (what I'd actually recommend if you want solid chances) for non-members: $760 exam + $125 manual + $129 QAE + $1,095 on-demand training + $200 supplementary materials = $2,309. Could push $2,800 with instructor-led training instead.
For members going full: $135 membership + $575 exam + $95 manual + $99 QAE + $1,095 training + $200 supplements = $2,199 total. The member full approach is actually cheaper than the non-member budget approach plus training, which really highlights the value.
Employer sponsorship changes everything
Not gonna lie here, most CDPSE candidates I personally know got at least partial employer support. Like 60-70% had some coverage, whether full or partial. Many companies will cover exam registration and official materials if you make a solid business case that privacy engineering capabilities directly benefit the organization's compliance and security posture. Some have training budgets specifically earmarked for professional development that cover exactly these costs.
If your employer has a professional development fund sitting there, use it without guilt. The ROI for them is pretty clear when you spell it out: Certified Data Privacy Solutions Engineer credentials are increasingly required for technical privacy roles across industries, and certified employees can implement privacy by design properly instead of bolting privacy controls on after the fact like an afterthought.
The ongoing cost nobody tells you about upfront
So you pass the exam. Congrats, honestly.
Now you've got annual maintenance fees: $45 for members, $85 for non-members. Required to keep your certification active and in good standing. Plus you need to earn CPE credits over each three-year cycle, and while some CPE activities are free (reading privacy articles, attending certain webinars, participating in study groups), others definitely cost money. Conferences, paid training courses, specialized workshops, stuff like that.
Over a three-year certification cycle, you're looking at $135-255 in maintenance fees alone. Add CPE acquisition costs (budget $300-600 depending on how you choose to earn them) and your three-year total beyond the initial certification runs somewhere between $500-1,000. Not huge in the grand scheme, but it's definitely there in your budget.
ROI makes the investment make sense
Here's why people actually pay all this: salary premium is real.
Technical privacy roles with privacy engineering certification command 15-25% higher salaries than equivalent roles without certification, based on what I'm seeing in the market. I've personally seen privacy engineers jump from $95K to $115K after getting certified with no other major changes. Security architects who add CDPSE to their existing CISM or CISA credentials can push into significantly higher compensation brackets.
The market for people who can actually implement privacy architecture (not just write policies or check compliance boxes) is really tight right now. Companies building serious privacy programs need technical expertise, and CDPSE demonstrates you can do the actual implementation work, not just the compliance paperwork that anyone can copy-paste.
Comparison with other privacy certifications
IAPP certifications are the other major player in privacy credentials. Their pricing is generally comparable when you break it down, but CDPSE focuses specifically on the engineering and implementation side rather than policy. If you're coming from a technical background (security, engineering, architecture), CDPSE tends to be the better fit for your skillset. If you're more on the legal/compliance side, IAPP's CIPP tracks might make more sense for your career path.
Cost-wise? CDPSE sits in the middle range. It's more expensive than entry-level certs but less than some of the specialized technical certifications out there. Given the growing demand for data protection controls implementation expertise across industries, the investment pencils out pretty well for most people's career trajectories.
Smart budgeting approach
If I were planning this today from scratch, here's exactly what I'd do: get the ISACA membership first ($135), grab the review manual and QAE database ($194 total), add a good practice exam resource like the CDPSE Practice Exam Questions Pack for additional question variety beyond the official stuff, then decide if you need formal training based on how comfortable you feel with the material after a couple weeks of study. That keeps initial outlay under $400 beyond the exam fee itself.
Set aside the exam fee ($575 as a member) once you're really confident in your preparation level. And yeah, budget for a potential retake even though you're not planning to need it, because life happens and these exams are legitimately challenging even for experienced professionals.
Total realistic budget for most people? $1,200-1,800 for first attempt including study materials. Higher if you want formal training, lower if your employer covers some costs. The certification pays for itself pretty quickly once you factor in salary increases and career advancement opportunities that open up.
CDPSE Passing Score, Scaled Scoring System, and Performance Standards
What is the ISACA CDPSE certification?
The CDPSE certification is ISACA's privacy engineering credential, and it hits different from the usual privacy certs because it expects you to think like someone building systems, not just writing policies. Less "quote the regulation." More "design the control so the product team can ship without setting the company on fire."
Who's it for. Privacy folks, security engineers, architects, risk people, and GRC leads who keep getting pulled into data protection controls conversations. Also the folks who sit next to the DPO and translate legal requirements into technical requirements. That translator role? Big deal.
Roles that benefit: Privacy engineer, security architect with privacy by design responsibilities, compliance lead who owns DPIAs but needs real implementation knowledge, and anyone supporting a DPO who's tired of hand waving and wants to talk data flows, identity, logging, minimization, and retention like an adult. This is an ISACA privacy certification that leans hard into "how do you actually build it."
CDPSE exam overview
Exam format (questions, timing, delivery)
The ISACA CDPSE exam is computer based, 2 hours and 30 minutes, and it's 120 multiple choice questions. No labs. No simulations. Just scenarios, lots of them. Some questions feel like a design review meeting where everyone's slightly annoyed and you're trying to pick the least bad answer under constraints, which is pretty accurate to real privacy engineering work.
Results show up immediately at the testing center for computer based delivery. You'll know if you passed right then. If you pass, the official certification processing starts after ISACA confirms the score and you complete the certification application steps.
CDPSE exam objectives (domains)
The CDPSE exam objectives map to three domains:
- Privacy Governance (26%). Still a chunk. Roughly 39 questions.
- Privacy Architecture (34%). Technical and easy to underestimate.
- Data Lifecycle (40%). The biggest slice, and it touches everything from collection to deletion.
Look, that weighting matters when you plan study time, because getting cute and ignoring one domain is how people end up retaking. I've seen someone bomb the exam because they figured Governance was "just common sense" and spent all their time on Architecture. Common sense doesn't score points when you're staring at a question about accountability frameworks and you never learned the actual definitions ISACA uses.
CDPSE cost (exam fees and total certification cost)
CDPSE exam registration cost (member vs non-member)
People always ask: How much does the ISACA CDPSE exam cost? It depends on ISACA membership status, and pricing can change, so I'm not gonna pretend a number I type today will be accurate forever. Expect the member price to be meaningfully lower than non member, and factor in taxes or regional pricing if that applies to your testing location.
Also remember the exam fee isn't the whole story. There's the certification application fee after passing, plus ongoing annual maintenance fees later. More on that below.
Other costs to plan for (training, books, practice tests, retake fees)
Training adds up fast. Official manuals, QAE database access, and instructor led classes can run high, and retake fees are a real thing if you miss the mark. The thing is, if you want a cheaper practice option, I've seen people pair official resources with a question pack like CDPSE Practice Exam Questions Pack to get more repetitions in before exam day. Not magic. Just reps.
Budget like a grownup. Exam fee, study materials, and maybe a retake. It's annoying, but it's better than being surprised.
CDPSE passing score and scoring
What the CDPSE passing score is (scaled scoring)
The CDPSE passing score is 450, on a scaled score range of 200 to 800. That 450 is the minimum competency threshold ISACA sets using psychometric analysis and standard setting procedures, which is a fancy way of saying they do stats work to decide what "minimally competent" looks like for this specific exam and this specific job role.
Here's the part that trips people up: The passing score isn't a raw percentage correct. It's scaled. So you can't say "450 equals X%" and be right across forms, because the whole point of scaled scoring is to adjust for difficulty differences between versions of the exam.
How scoring works and what to aim for by domain
Scaled scoring exists to keep things fair across exam versions. One test form might have slightly harder questions in Privacy Architecture, another might be slightly easier overall, and ISACA uses equating to statistically adjust results so the passing standard stays consistent over time. That's why two candidates can answer different sets of questions and still be judged against the same competency bar.
The raw score to scaled score conversion? Proprietary and non linear. Meaning 450 doesn't map to a fixed percent correct. ISACA doesn't publish conversion tables or exact percentage requirements, and I get why, because once you publish that stuff you invite people to game the exam and you weaken exam integrity.
So what's the practical takeaway. Most candidates who pass are probably landing somewhere around 65 to 70% correct as a rough estimate, but it varies by form and the difficulty distribution of the questions you got. Don't cling to that number. Use it as a gut check only.
Also, unanswered questions get no credit. No "partial." No sympathy. And there's no penalty for wrong answers, so you should answer every question even if you're guessing on the last few because the clock is bullying you. Each attempt is scored independently too, with no carry over between attempts. You either clear 450 that day or you don't.
Score reports. Passing candidates typically see pass status, and failing candidates see the scaled score plus domain level performance indicators. Those domain indicators are qualitative, not numeric: below expectations, near expectations, meets expectations. That's actually useful for retakes because it tells you where you're weak without giving away the whole scoring model.
What to aim for while studying? I tell people to target 75 to 80% mastery across all domains, because exam day is messy and your practice set might be easier than the real thing. Data Lifecycle is 40%, so you need solid understanding of data protection controls across collection, use, sharing, storage, retention, deletion, and the messy middle where "temporary" data becomes permanent by accident. Privacy Architecture is 34% and it's where people panic when privacy enhancing technology shows up, plus design patterns, threat modeling-ish thinking, and system constraints. Governance is 26% but still about 39 questions, and weak governance answers can sink you because scenario questions often include risk assessment and decision rights.
If you're drilling questions, something like CDPSE Practice Exam Questions Pack can help you spot patterns in your mistakes, but only if you keep an error log and actually read why you missed it. Mindless clicking? Waste of time.
CDPSE difficulty: how hard is the exam?
What makes CDPSE challenging (scenario-based privacy engineering)
People also ask: How hard is the CDPSE certification exam? It's hard in a specific way. The questions are scenario based, and the "best" answer is often the one that best fits with privacy by design while still being feasible in an enterprise environment with legacy systems, stakeholders, and competing risks.
Tiny detail. Big consequences. A question will mention a data processor relationship, or an analytics pipeline, or a retention requirement, and if you miss that, you pick the answer that sounds nice but is wrong.
Difficulty by background (privacy/GRC vs security/engineering)
If you come from privacy or GRC, Governance will feel comfortable, but Architecture can feel like someone swapped your keyboard for a legal pad. If you come from security engineering, Architecture and controls might feel fine, but you can get wrecked by governance concepts like accountability, DPIA triggers, and how to operationalize privacy requirements without turning into the Department of No.
How long to study (typical timelines)
Timelines vary. If you already do privacy engineering work, 6 to 10 weeks of steady study can be enough. If you're coming in cold, plan longer, because you're not just memorizing terms, you're learning how ISACA wants you to reason in ambiguous scenarios.
CDPSE prerequisites and eligibility requirements
Required work experience (how many years and what counts)
The CDPSE prerequisites include relevant work experience requirements set by ISACA, and you should check the current policy because they can update what counts. Generally, they want hands on experience across privacy governance, architecture, or lifecycle activities, not just "I attended a privacy meeting once."
Substitutions/waivers (if applicable) and documentation
If ISACA offers substitutions or waivers for certain credentials or experience types, it'll be documented in the certification requirements. Keep evidence. Job descriptions, project summaries, attestations. Paperwork's part of the game.
How to apply for certification after passing
After you pass, you submit the application and verify experience. Passing the exam alone isn't the final step. Annoying? Normal.
Best CDPSE study materials (official and third-party)
Official ISACA resources (review manual, QAE, training)
Official materials are the core. The review manual helps align you to ISACA's wording, and the QAE helps you practice the style of questions. Add third party references if you need clarity on data protection controls or privacy engineering patterns.
Recommended books and references (privacy engineering, governance, controls)
Pick a privacy engineering book that explains design choices, and pair it with governance references that cover risk assessment and operational privacy programs. Keep it practical. If you can't map it to a system diagram or a data flow, you're studying the wrong thing.
Study plan by domain (privacy governance, architecture, lifecycle)
Spend extra time where the weight is. Data Lifecycle first, then Architecture, then Governance, but don't ignore Governance because it's the glue in scenario questions. I mean, if you want more question volume, mix official QAE with CDPSE Practice Exam Questions Pack as supplemental reps, and focus hard on why an answer's best, not just why it's not wrong.
CDPSE practice tests and exam prep strategy
Where to find CDPSE practice questions (QAE, banks, labs if used)
QAE's the obvious one. Other banks exist. Some are decent, some are trash. No labs are required for the exam, but diagramming data flows on your own is basically a lab anyway.
How to use practice tests effectively (timed sets, error log, weak domains)
Do timed sets. Review every miss. Write down the concept and the trigger phrase you missed in the scenario. Then go back to the domain content and patch the hole. If your score's "fine" but you're guessing, that's not fine.
Common mistakes and how to avoid them
Biggest mistake's treating practice tests like entertainment. Another is over trusting a raw percent score and assuming you're safe, when scaled scoring and form difficulty can make your exam feel tougher than your practice set.
CDPSE renewal requirements (maintenance and CPE)
CPE requirements and reporting cycle
The CDPSE renewal requirements include earning and reporting CPEs within ISACA's reporting cycle. Track them as you go. Don't wait until the deadline week and start begging webinars for certificates.
Annual maintenance fees (member vs non-member)
There's an annual maintenance fee, and member pricing's usually lower. Plan for it. This credential isn't a one and done purchase.
What activities count for CPE (training, webinars, work activities)
Training counts. Many webinars count. Some work activities can count if they meet ISACA rules and you document them. Read the policy so you don't waste time logging stuff that won't be accepted.
CDPSE FAQ
Cost, passing score, difficulty, prerequisites, renewal (quick answers)
What is the passing score for the CDPSE exam? 450 on a 200 to 800 scaled score range. How much does the ISACA CDPSE exam cost? Member vs non member pricing, plus application and maintenance fees. Check current ISACA pricing. How hard is it? Scenario heavy, especially in Privacy Architecture and Data Lifecycle. What are the domains? Governance, Architecture, Data Lifecycle. How do I renew? Earn CPEs and pay annual maintenance fees per ISACA rules.
Retake policy and scheduling tips
No partial credit. No score carry over. Each attempt's a fresh shot at clearing 450. If you fail, use the domain indicators, hammer anything marked below expectations, do more scenario practice, and tighten your technical understanding of privacy by design and data protection controls before you schedule the retake.
CDPSE Difficulty Level, Challenge Factors, and Study Timeline Recommendations
How hard is the CDPSE certification exam
Not gonna sugarcoat this. The CDPSE certification sits firmly in the "moderately difficult to difficult" range. Most candidates rate the difficulty around 7.5 out of 10, which feels about right from what I've seen, but here's the thing: your mileage will vary dramatically based on your background.
Privacy pros? Years working with GDPR compliance and privacy frameworks mean they'll breeze through governance sections. Security engineers and architects who understand encryption and access controls inside-out will find the technical architecture domain much more approachable. Nobody gets a completely free pass here, but your starting point matters a ton.
The exam doesn't care if you can recite definitions. It wants to know if you can actually solve privacy problems in real organizational contexts, which is a completely different skill set altogether.
What makes CDPSE challenging
Scenario-based questions are the real killer.
You're not getting straightforward "what is tokenization?" questions. Instead, you're looking at a three-paragraph scenario about a multinational company implementing a new customer data platform, and you need to evaluate four plausible approaches to data minimization where each answer sounds reasonable. Three of them are partially correct or work in specific contexts.
The ISACA CDPSE exam deliberately includes distractors based on common misconceptions. I've seen questions where the "obvious" answer reflects what many organizations actually do in practice, but it's wrong because it doesn't align with privacy-by-design principles or misapplies a privacy-enhancing technology. You need nuanced understanding, not just surface-level familiarity.
Technical depth in the Privacy Architecture domain challenges a lot of candidates. You need to understand encryption methods (symmetric vs asymmetric, when to use each), tokenization versus anonymization (and the differences matter), pseudonymization techniques, differential privacy concepts, and how various access control mechanisms protect data at different processing stages. If you're coming from a pure privacy or GRC background without hands-on technical experience, this stuff requires serious study.
Privacy-enhancing technologies questions don't just ask "what is homomorphic encryption?" They ask when you'd implement it versus other PETs. They ask what the performance trade-offs are, and what limitations you need to communicate to stakeholders. That's applied engineering knowledge.
The integration piece really trips people up too. You're translating legal requirements from GDPR Article 25 or CCPA Section 1798.100 into specific technical controls and architectural decisions. It's not enough to know what "privacy by design" means conceptually. You need to implement it across data collection, processing, storage, and deletion stages.
Speaking of GDPR, I spent about two weeks just on Article 25 alone during my prep because the concept kept showing up in weird ways across different question types. Probably overkill, but it ended up helping with at least five exam questions that I could identify.
Difficulty by background
Privacy and GRC professionals typically find the governance domain accessible. They've dealt with privacy frameworks, data protection impact assessments, and regulatory compliance before. But throw them into technical architecture questions about implementing encryption key management or designing anonymization pipelines? That's where struggle happens. I've mentored folks from compliance backgrounds who needed an extra 20-30% study time just to build baseline engineering competency.
Security professionals and engineers have the opposite problem.
They grasp the technical privacy controls immediately. Encryption, tokenization, secure deletion, access controls are familiar territory. But privacy frameworks, governance structures, and the details of various privacy regulations? That requires dedicated study. You can't just wing the governance domain based on security knowledge alone.
Software developers and architects transitioning into privacy engineering find the technical content familiar but still need foundational privacy knowledge. Understanding how to implement a consent management system is different from understanding why certain consent patterns comply with GDPR while others don't.
Even candidates with both privacy knowledge and technical background (the ideal CDPSE target audience) still need 80-120 hours of study. The exam's breadth across three domains plus the depth within each domain means there's just a lot of ground to cover, similar to how CISM requires both technical and management knowledge. CDPSE demands integration of privacy expertise with engineering skills.
How long to study for CDPSE
For experienced privacy engineers with 5+ years in relevant roles, plan on 8-12 weeks of focused study. That's folks who've already been implementing privacy controls, working with PETs, and designing privacy-preserving architectures. You're mostly consolidating knowledge and filling gaps.
Privacy professionals with limited technical background should plan 12-16 weeks. You'll need extra time for the Privacy Architecture domain and hands-on technical learning. The thing is, you should consider setting up lab environments to actually work with encryption tools, tokenization systems, or data masking techniques. Reading about them isn't enough.
Security professionals moving into privacy? 10-14 weeks makes sense, with additional time focused on privacy frameworks and regulations. If you've got CISA or similar certifications, you understand governance concepts, but privacy governance has its own specific frameworks and requirements.
Entry-level candidates or career changers should allocate 16-20 weeks. You're building both privacy and technical foundations at the same time, which just takes time. Not gonna lie, this is a tough certification to pursue as your first major credential, but it's doable with dedicated effort.
Study hour recommendations range from 80-150 hours total. Experienced privacy engineers can get away with 80-100 hours. Those building foundational knowledge need 120-150 hours. Weekly study commitment of 8-12 hours works for most people. Enough to maintain momentum without burning out.
I recommend domain-focused study blocks. Spend 3-4 weeks on Privacy Governance, then 4-5 weeks on Privacy Architecture (it's the meatiest domain), then 2-3 weeks on Data Lifecycle Management. Use the final 2-3 weeks for integrated review and practice exams.
Study timeline by domain allocation
Privacy Governance deserves about 30-35% of your study time. You're covering privacy frameworks, regulatory requirements, privacy program management, and governance structures. This domain connects to certifications like CRISC in terms of risk management thinking, but with privacy-specific focus.
Privacy Architecture needs 40-45% of your time.
It's the largest domain and the most technically demanding. You're learning about privacy-preserving architectures, PETs implementation, secure data handling, and privacy controls across system design. Budget extra time here if you're from a non-technical background.
Data Lifecycle Management gets 20-25% of study time. It covers privacy controls across collection, processing, storage, sharing, and disposal stages. Scenario questions here often integrate concepts from both other domains.
Using CDPSE study materials well matters as much as total study time. The official ISACA review manual is essential. Don't skip it. Supplement with privacy engineering books, PETs whitepapers, and regulatory guidance documents. The CDPSE Practice Exam Questions Pack at $36.99 is one of the better investments you can make. Scenario-based practice questions that mirror actual exam format help tremendously.
Plan for multiple practice test rounds. First round identifies weak areas. Second round after targeted study confirms improvement. Final round right before exam builds confidence and timing skills. Track your performance by domain to guide additional study where needed.
The CDPSE passing score uses scaled scoring (typically 450 out of 800), so you don't need perfection. But aim for 70%+ across all domains in practice tests before scheduling your exam. Weak performance in any single domain can sink you even if other areas are strong.
Conclusion
Wrapping up your CDPSE path
Real talk here. The CDPSE certification isn't just another acronym to slap on your LinkedIn profile. It's honestly one of the few credentials that bridges the gap between privacy compliance and actual engineering implementation. If you've read this far, you probably already know that privacy by design isn't some theoretical concept anymore, right? Organizations desperately need people who can translate regulatory requirements into technical controls, and the Certified Data Privacy Solutions Engineer credential proves you're that person.
The CDPSE exam cost runs about $575 for ISACA members and $760 for non-members. Not cheap, honestly. But when you factor in the skyrocketing demand for privacy engineering skills and the absolute scarcity of professionals who understand both the governance side and the technical architecture side, it's a solid investment in your career trajectory. The CDPSE passing score sits at 450 out of 800 on that scaled scoring system. Most people find the scenario-based questions way more challenging than they expected because you're not just reciting definitions. You're applying privacy architecture principles to messy real-world situations that don't fit neatly into textbook categories.
The thing is, you can memorize frameworks all day, but the exam throws curveballs. Like, they'll describe some legacy system integration nightmare and ask you how to retrofit privacy controls without breaking everything. That's the stuff that trips people up.
Prerequisites matter here. The CDPSE prerequisites require five years of experience in information privacy or related work, though you can start the exam before you've hit that mark. Not gonna lie, if you're coming from a pure security background without much privacy governance exposure, plan on spending 2-3 months minimum with the CDPSE study materials. Maybe more. The exam objectives across those three domains (Privacy Governance, Privacy Architecture, and Data Lifecycle) cover a ton of ground. Don't forget about CDPSE renewal requirements. You'll need 20 CPE hours annually and 120 over three years, plus those annual maintenance fees that add up.
Here's the thing about CDPSE practice tests: they're absolutely critical. You can read the official ISACA review manual cover to cover, but until you're working through scenario questions under timed conditions, you won't really know where your weak spots are. The official Question, Answer and Explanation database helps, but honestly you need more volume than that to feel confident walking into the testing center.
If you're serious about passing the ISACA CDPSE exam on your first attempt, I'd strongly recommend checking out a thorough CDPSE Practice Exam Questions Pack at /isaca-dumps/cdpse/. Getting exposure to hundreds of practice questions that mirror the actual exam format makes a huge difference in your ability to recognize question patterns and manage that four-hour time crunch. This ISACA privacy certification is totally achievable with the right prep strategy. Mixed feelings about some study resources out there, but solid practice questions? Those'll get you across the finish line.