PT0-002 Practice Exam - CompTIA PenTest+ Certification Exam
Reliable Study Materials & Testing Engine for PT0-002 Exam Success!
Exam Code: PT0-002
Exam Name: CompTIA PenTest+ Certification Exam
Certification Provider: CompTIA
Corresponding Certifications: CompTIA PenTest+ , PenTest+ , CompTIA Certification

Free Updates PDF & Test Engine
Verified By IT Certified Experts
Guaranteed To Have Actual Exam Questions
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
100% Money Back Guarantee
Instant Downloads
Free Fast Exam Updates
Exam Questions And Answers PDF
Best Value Available in Market
Try Demo Before You Buy
Secure Shopping Experience
PT0-002: CompTIA PenTest+ Certification Exam Study Material and Test Engine
Last Update Check: Mar 18, 2026
Latest 278 Questions & Answers
45-75% OFF
Hurry up! offer ends in 00 Days 00h 00m 00s
*Download the Test Player for FREE
Dumpsarena CompTIA CompTIA PenTest+ Certification Exam (PT0-002) Free Practice Exam Simulator Test Engine Exam preparation with its cutting-edge combination of authentic test simulation, dynamic adaptability, and intuitive design. Recognized as the industry-leading practice platform, it empowers candidates to master their certification journey through these standout features.
What is in the Premium File?
Satisfaction Policy – Dumpsarena.co
At DumpsArena.co, your success is our top priority. Our dedicated technical team works tirelessly day and night to deliver high-quality, up-to-date Practice Exam and study resources. We carefully craft our content to ensure it’s accurate, relevant, and aligned with the latest exam guidelines. Your satisfaction matters to us, and we are always working to provide you with the best possible learning experience. If you’re ever unsatisfied with our material, don’t hesitate to reach out—we’re here to support you. With DumpsArena.co, you can study with confidence, backed by a team you can trust.
CompTIA PT0-002 Exam FAQs
Introduction of CompTIA PT0-002 Exam!
CompTIA PT0-002 is a performance-based exam that focuses on the CompTIA PenTest+ certification. It is designed to assess a candidate's ability to use various penetration testing techniques and tools to identify, analyze, and document security vulnerabilities in an organization’s network, system and application environments. The exam covers topics such as information gathering, vulnerability analysis, threat modeling, attack methods, and penetration testing tools.
What is the Duration of CompTIA PT0-002 Exam?
The CompTIA PT0-002 exam is 90 minutes long.
What are the Number of Questions Asked in CompTIA PT0-002 Exam?
There are 90 questions on the CompTIA PT0-002 exam.
What is the Passing Score for CompTIA PT0-002 Exam?
The passing score required for the CompTIA PT0-002 exam is 750 out of 900.
What is the Competency Level required for CompTIA PT0-002 Exam?
The CompTIA PT0-002 exam requires a competency level of intermediate. This exam is designed to test a candidate’s knowledge and skills related to setting up, configuring, and maintaining physical and virtual networks. Candidates should have a good understanding of networking concepts, including IP addressing, subnetting, routing, switching, and security.
What is the Question Format of CompTIA PT0-002 Exam?
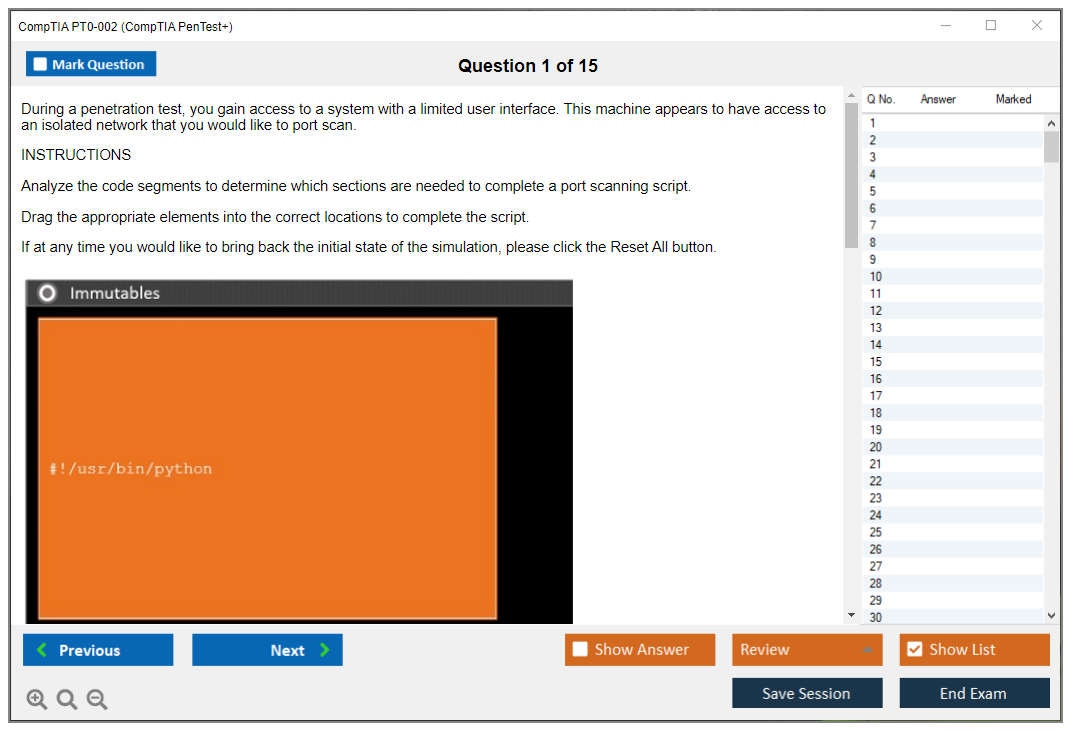
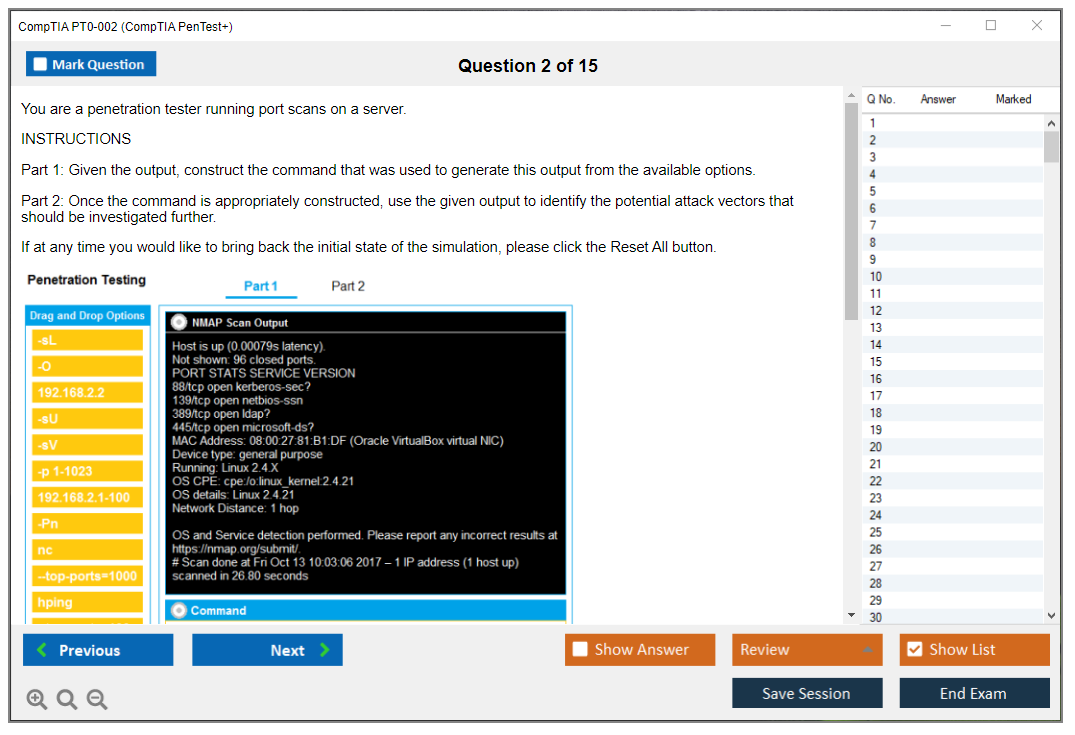
The CompTIA PT0-002 exam has multiple-choice questions, performance-based questions, drag-and-drop questions, and fill-in-the-blank questions.
How Can You Take CompTIA PT0-002 Exam?
CompTIA PT0-002 exam can be taken either online or in a testing center. To take the exam online, you will need to register for the exam on the CompTIA website and then follow the instructions to complete the exam. To take the exam in a testing center, you will need to register for the exam at a Pearson VUE testing center and then follow the instructions to complete the exam.
What Language CompTIA PT0-002 Exam is Offered?
CompTIA PT0-002 exam is offered in English.
What is the Cost of CompTIA PT0-002 Exam?
The cost of the CompTIA PT0-002 exam is $219 USD.
What is the Target Audience of CompTIA PT0-002 Exam?
The target audience for the CompTIA PT0-002 exam is IT professionals who want to demonstrate their knowledge and understanding of the fundamentals of IT service management. This includes IT professionals who are responsible for managing IT services, such as IT technicians, IT managers, system administrators, and IT consultants.
What is the Average Salary of CompTIA PT0-002 Certified in the Market?
The average salary for someone with a CompTIA PT0-002 certification is around $60,000 per year. This figure can vary depending on the individual's experience and location.
Who are the Testing Providers of CompTIA PT0-002 Exam?
CompTIA provides official practice tests for their certification exams, including the PT0-002 exam. These practice tests are available for purchase through the CompTIA Marketplace. Additionally, there are a number of third-party providers that offer practice tests for the PT0-002 exam.
What is the Recommended Experience for CompTIA PT0-002 Exam?
The recommended experience for the CompTIA PT0-002 exam is three to five years of experience in the IT industry, including two years of experience in IT security. Additionally, it is recommended that candidates have a basic understanding of network security, security operations, and risk management.
What are the Prerequisites of CompTIA PT0-002 Exam?
The Prerequisite for CompTIA PT0-002 Exam is that candidates must have at least two years of experience in the field of IT security and/or system administration.
What is the Expected Retirement Date of CompTIA PT0-002 Exam?
The official website for checking the expected retirement date of CompTIA PT0-002 exam is the CompTIA website. The link to the page is https://certification.comptia.org/certifications/a/pt0-002.
What is the Difficulty Level of CompTIA PT0-002 Exam?
The CompTIA PT0-002 exam is considered a medium difficulty level exam.
What is the Roadmap / Track of CompTIA PT0-002 Exam?
The CompTIA PT0-002 Exam is a certification exam that is designed to assess a candidate's knowledge and skills in the areas of IT security, risk management, and compliance. The exam is part of the CompTIA PenTest+ certification program and is intended for IT professionals who want to demonstrate their ability to identify, analyze, and respond to security risks.
The certification roadmap for the CompTIA PT0-002 Exam includes the following steps:
1. Complete the CompTIA PenTest+ Certification Exam: This exam is designed to test a candidate's knowledge and skills in the areas of IT security, risk management, and compliance. Candidates must pass this exam in order to become certified.
2. Complete the CompTIA PenTest+ Certification Course: This course is designed to help candidates prepare for the exam by providing them with the necessary skills and knowledge to pass the exam.
3. Obtain the CompTIA PenTest
What are the Topics CompTIA PT0-002 Exam Covers?
CompTIA PT0-002 exam covers the following topics:
1. Troubleshooting: This covers the ability to diagnose and troubleshoot common problems in a physical computing environment.
2. Networking: This covers the ability to install, configure, and maintain network hardware and services.
3. Security: This covers the ability to identify and mitigate security threats and vulnerabilities.
4. System Administration: This covers the ability to manage and maintain physical computing systems.
5. Virtualization: This covers the ability to deploy and manage virtualized computing environments.
6. Cloud Computing: This covers the ability to implement and manage cloud computing solutions.
7. Data Storage: This covers the ability to manage and maintain data storage solutions.
8. Professionalism: This covers the ability to demonstrate professional demeanor and communication skills.
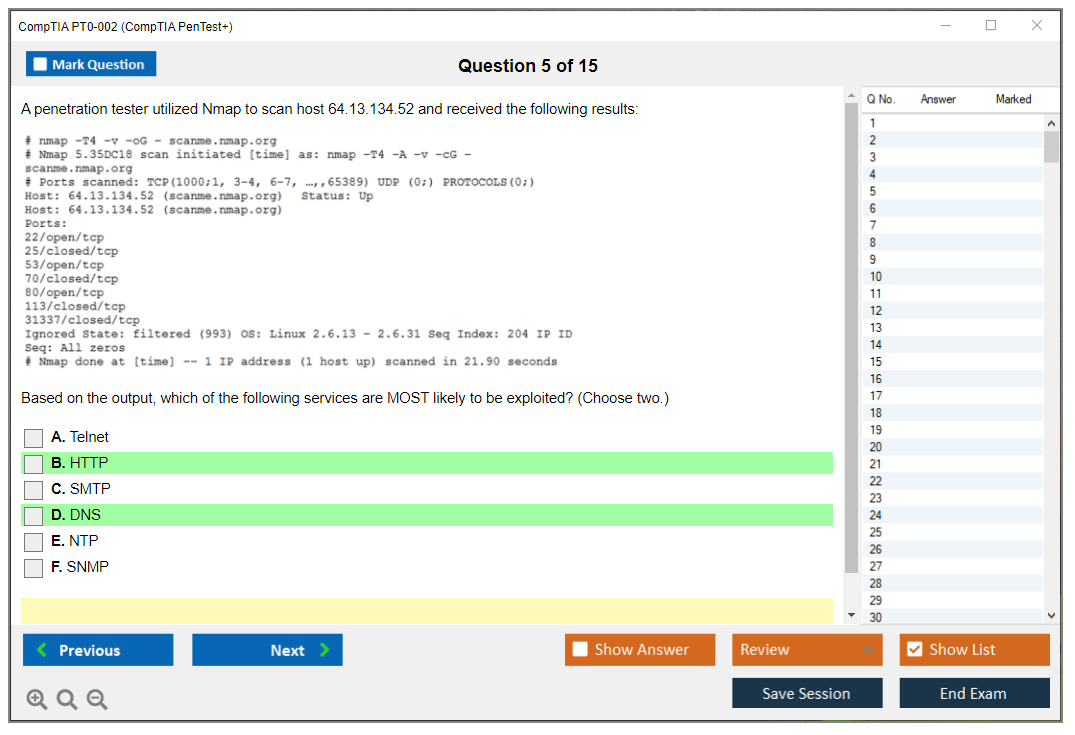
What are the Sample Questions of CompTIA PT0-002 Exam?
1. What is the purpose of a vulnerability scan?
2. What is the best way to protect against a Denial of Service (DoS) attack?
3. What is the difference between a firewall and an intrusion detection system?
4. What is the purpose of the Risk Management Framework (RMF)?
5. How can an organization ensure the security of its data?
6. What is the difference between authentication and authorization?
7. What is the purpose of a patch management system?
8. What is the difference between a vulnerability assessment and a penetration test?
9. What is the importance of data classification in an organization?
10. What are the different types of malware and how can they be prevented?
CompTIA PT0-002 (CompTIA PenTest+ Certification Exam) CompTIA PenTest+ PT0-002 Certification Overview and Exam Introduction What makes CompTIA PenTest+ PT0-002 different from other security certs Look, I've watched tons of people chase certifications in cybersecurity, and CompTIA PenTest+ PT0-002 stands out for one massive reason. It actually makes you do stuff. This isn't one of those exams where you memorize definitions and call it a day. The CompTIA PenTest+ certification throws performance-based questions at you that simulate real scenarios, meaning you've gotta know how to use tools, analyze results, and make decisions under pressure just like you would during an actual penetration test. Released October 2021. PT0-002 replaced the older PT0-001 version with content that reflects what's happening right now in offensive security. We're talking cloud environments, modern attack vectors, and the kind of defensive tech you'll actually encounter when testing client networks. The thing... Read More
CompTIA PT0-002 (CompTIA PenTest+ Certification Exam)
CompTIA PenTest+ PT0-002 Certification Overview and Exam Introduction
What makes CompTIA PenTest+ PT0-002 different from other security certs
Look, I've watched tons of people chase certifications in cybersecurity, and CompTIA PenTest+ PT0-002 stands out for one massive reason. It actually makes you do stuff. This isn't one of those exams where you memorize definitions and call it a day. The CompTIA PenTest+ certification throws performance-based questions at you that simulate real scenarios, meaning you've gotta know how to use tools, analyze results, and make decisions under pressure just like you would during an actual penetration test.
Released October 2021.
PT0-002 replaced the older PT0-001 version with content that reflects what's happening right now in offensive security. We're talking cloud environments, modern attack vectors, and the kind of defensive tech you'll actually encounter when testing client networks. The thing is, none of this stuff is theoretical anymore. The penetration testing certification exam covers everything from initial planning conversations with clients through the final report delivery, which honestly is how real engagements work.
What really matters here? The validation of ethical hacking and pentesting skills that employers actually care about. When you pass PT0-002, you're telling potential employers that you can perform vulnerability assessments, exploit weaknesses responsibly, and communicate findings to people who might not understand technical jargon. That last part trips up loads of technical people, but it's key.
The practical side nobody warns you about
The exam includes these performance-based questions that feel more like mini-labs than traditional test questions. You might need to analyze packet captures. Or identify the right tool for a specific scenario. Maybe interpret vulnerability scan output and prioritize findings. I mean, this is where a lot of candidates struggle because knowing what Nmap does theoretically is way different from understanding when to use specific scan types during different phases of a penetration test.
CompTIA positions this cert as intermediate-level.
That means they expect you've got some baseline knowledge before attempting it. Not gonna lie, jumping straight into PT0-002 without understanding networking fundamentals or basic security concepts is a recipe for frustration. Most successful candidates have backgrounds similar to what you'd get from CompTIA Security+ or equivalent real-world experience, though some self-taught folks with strong home labs manage it too. Actually the hands-on penetration testing labs component demands you've actually spent time in Kali Linux, configured vulnerable machines, and gotten your hands dirty with exploitation frameworks, so there's really no shortcut here.
Random thought: I once watched someone spend three hours troubleshooting why their Metasploit payload wouldn't execute, only to realize they'd fat-fingered the IP address. Sometimes the simplest mistakes eat up the most time.
Who actually needs this certification
The PT0-002 exam cost runs around $392 for the voucher, though prices vary depending on where you buy it and whether you bundle it with training materials. That's not pocket change, honestly. But here's the thing. This cert fits with DoD 8570.01-M and the newer 8140 requirements, making it valuable for government contracting work and military cybersecurity positions. If you're aiming for roles as a penetration tester, vulnerability assessment analyst, or security analyst with an offensive focus, PT0-002 gives you credible validation.
Scores are scaled.
I've seen people ask about the PenTest+ PT0-002 passing score, and CompTIA uses a scaled scoring system where you need 750 out of 900 points. The scaling accounts for question difficulty, so two people getting the same number of questions right might score differently depending on which questions they answered correctly. You get 165 minutes for up to 85 questions. Those questions split between multiple-choice and the performance-based scenarios I mentioned earlier.
Breaking down what you actually need to know
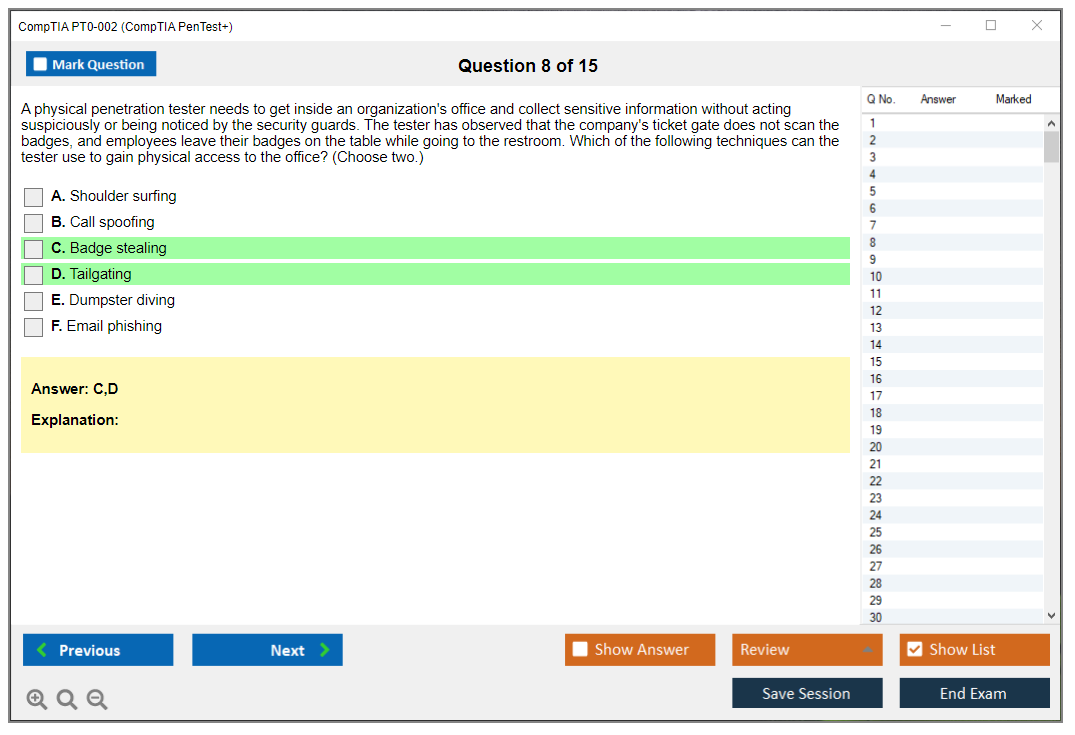
The PenTest+ PT0-002 exam objectives divide into five domains with different weightings. Planning and Scoping makes up 14% of the exam. This covers understanding client requirements, defining rules of engagement, and ensuring you've got proper authorization before touching anything. People underestimate this domain constantly, but getting scoping wrong in real life can land you in legal trouble or cause business disruption. Nobody wants that on their resume.
Information Gathering and Vulnerability Scanning accounts for 22% of the exam. You've gotta know passive reconnaissance techniques. OSINT gathering. How to run and interpret various scanning tools. Most importantly, how to distinguish between false positives and actual vulnerabilities. I've reviewed scan results where inexperienced testers flagged hundreds of issues that weren't actually exploitable, wasting everyone's time and making the client question whether they hired the right team.
Attacks and Exploits? Biggest chunk.
This represents 30% of exam weight. This domain covers password attacks, social engineering, application attacks, network attacks, wireless attacks, and working around security controls like firewalls and IDS/IPS systems. You'll need hands-on experience with tools including Metasploit, Burp Suite, SQLmap, and various password cracking utilities. The exam tests whether you understand when to use each tool and technique, not just that they exist or what their help files say.
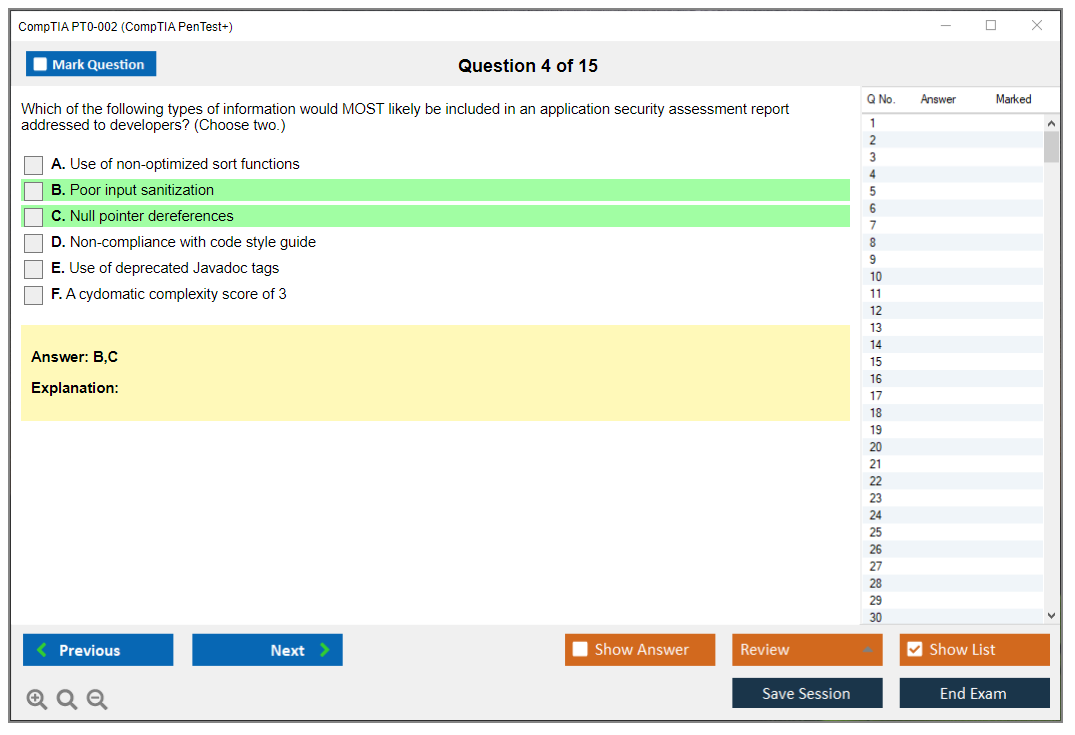
Reporting and Communication is 18% of the exam. Honestly this is where many technical people struggle the most. You need to show you can write clear findings, prioritize vulnerabilities based on business impact, communicate with both technical staff and executives, and provide actionable remediation recommendations. The best penetration testers I know are the ones who can translate technical findings into business risk that makes CFOs and CIOs actually care enough to allocate budget for fixes.
Tools and Code Analysis rounds out the remaining 16%. This covers scripting basics. Analyzing code to identify vulnerabilities. Understanding how exploits work at a code level. Customizing existing exploits for specific scenarios. You don't need to be a developer necessarily, but you should be comfortable reading Python, PowerShell, and Bash scripts without your eyes glazing over.
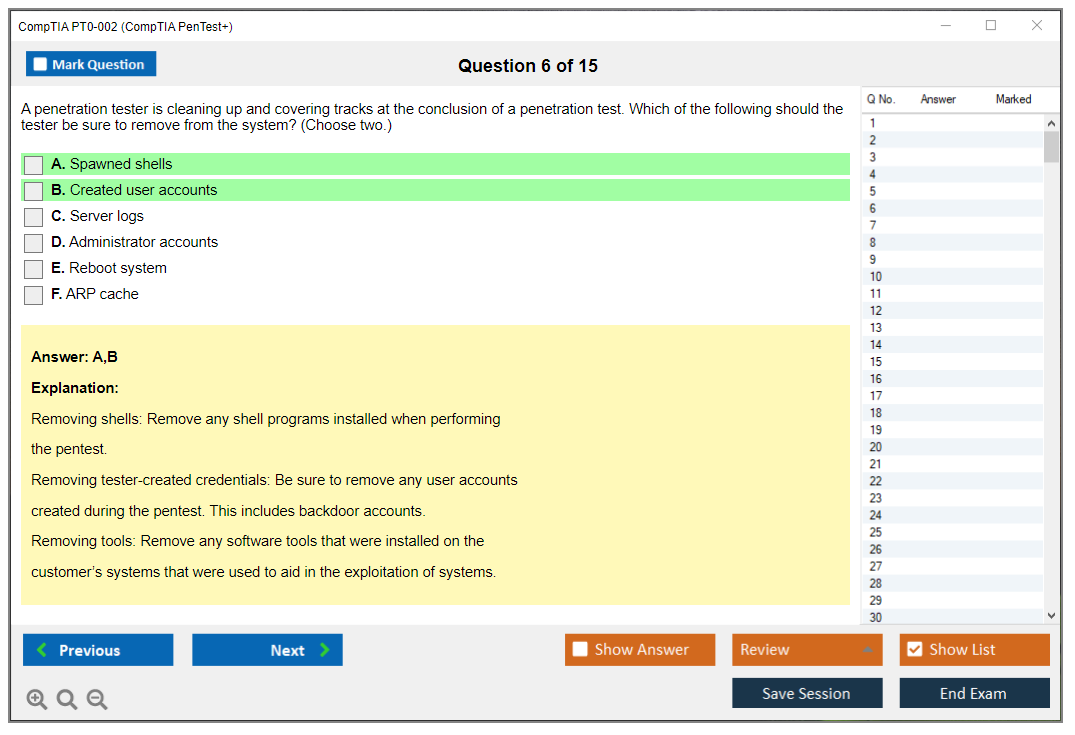
What actually changed in PT0-002
Compared to PT0-001, the updated exam includes way more content around cloud environments and hybrid infrastructure. Traditional perimeter-based thinking doesn't work anymore when applications run in AWS, Azure, or Google Cloud. PT0-002 also expanded coverage of post-exploitation activities. Privilege escalation. Lateral movement. Persistence mechanisms. Data exfiltration techniques that advanced persistent threats actually use.
Defensive tech matters now.
The exam added more weight on understanding defensive technologies and how to test them properly. You've gotta know how modern endpoint protection works, what SIEM systems look for, and how to conduct testing that provides value without triggering every alert and disrupting business operations. It's a delicate balance that separates amateurs from professionals.
Prerequisites and what you should know first
CompTIA officially recommends Network+ or equivalent knowledge plus 3-4 years of hands-on information security or related experience. That's their recommendation, not a hard requirement though. I've seen people with strong home lab experience and self-study pass without the formal prerequisites. But they put in serious work. I'm talking 12-hour weekend lab sessions and reading exploit documentation for fun.
The skills checklist before attempting PT0-002 should include comfortable command-line usage in Linux. Understanding TCP/IP networking at a deep level. Familiarity with common vulnerabilities (OWASP Top 10, CVE databases). Basic scripting ability. Experience with at least some penetration testing tools. If you're struggling with subnetting or don't understand how three-way handshakes work, you're going to have a bad time with this exam. Honestly you should probably step back and shore up those fundamentals first.
The difficulty factor everyone asks about
The PenTest+ PT0-002 difficulty really depends on your background and preparation approach, which I know sounds like a cop-out answer but it's true. Candidates with strong networking fundamentals and some security experience typically find it challenging but manageable. Complete beginners often struggle hard, especially with the performance-based questions that require actual tool knowledge and decision-making under time pressure.
Common weak areas? Several.
Proper scoping and planning (people want to jump straight to exploitation because that's the fun part). Understanding when findings are actually exploitable versus just interesting from an academic perspective. Writing clear reports that non-technical stakeholders can understand without dumbing things down too much. Choosing the right tool for specific scenarios. The exam also tests your ability to work methodically through the entire penetration testing lifecycle rather than just focusing on the exciting exploitation phase that gets glamorized in movies.
Study time varies wildly based on experience. Someone with solid Security+ knowledge and some practical experience might need 6-8 weeks of focused study. Complete beginners should plan for 12-16 weeks minimum, including significant hands-on lab time that can't be replaced with passive reading or video watching.
Keeping your cert current
The PenTest+ PT0-002 renewal requirements follow CompTIA's continuing education model. Your certification's valid for three years from your pass date. To renew, you've gotta earn 60 continuing education units (CEUs) during that three-year period. You can earn CEUs through training, publishing articles, attending conferences, completing higher-level certifications, or various professional development activities.
Renewal fee? Pretty reasonable.
It runs around $50-75 depending on your membership status. Miss the renewal window and your cert expires, requiring you to retake the full exam. That means another $392 and all that study time again. Not fun at all.
PT0-002 Exam Cost, Registration Process, and Voucher Information
CompTIA PenTest+ PT0-002 exam overview
Okay, so PT0-002. It sits right between "I opened Metasploit once" and "I'm leading APT simulations for Fortune 500s." This penetration testing certification exam demands you know ethical hacking and pentesting skills, but here's the thing: you've also gotta explain vulnerabilities like you're briefing executives who think a firewall is actual fire protection. Which honestly tests a different muscle entirely.
The validation's legit practical. Scoping engagements. Reconnaissance work. Exploitation fundamentals, post-exploitation strategy, and reporting that doesn't look like you copy-pasted from ExploitDB at 3am. Performance-based questions show up too, so memorizing switches for tools won't save you when you're staring at a simulated network that's actually fighting back.
Who should take PenTest+ (roles and experience level)
If you're in security already and want vendor-neutral credibility, this fits. Junior pentesters, SOC analysts wanting to pivot offensive, sysadmins exhausted from patching the same Apache vulnerability monthly, GRC folks who need to understand what they're actually approving in those scoping documents.
Complete beginners? Sure, they pass sometimes. But PT0-002 difficulty isn't insurmountable. It just demands reps, the kind you get from real engagements or at least a home lab where you've broken authentication schemes deliberately and documented the carnage afterward.
PT0-002 exam cost and registration
Exam voucher price (and what impacts cost)
Standard voucher pricing hits $392 USD for US candidates. That's the number everyone quotes, and yeah, it's accurate domestically, but international folks see different totals based on currency conversion rates and regional pricing structures that CompTIA adjusts periodically. Your actual checkout amount might surprise you.
Discounts exist as a side mission. CompTIA drops promotional discounts occasionally, usually 10-20% during major holidays or cybersecurity awareness months. Not constant. Not predictable. Worth monitoring though.
Then there's the legitimately cheaper path. Academic institutions provide discounted vouchers to students in CompTIA-approved training programs, sometimes 50% off or more through Academic Partner programs. Military personnel, veterans, and their spouses qualify for roughly 50% reductions via CompTIA's military and veterans discount program. Government employees and non-profit staff sometimes access special pricing, but you'll need employment verification. Paperwork. Tedious, honestly. Still saves cash.
Bundles cost more initially, which obviously they do, but they're smarter financially if you really need PenTest+ PT0-002 study materials like CertMaster Learn, CertMaster Practice, or CertMaster Labs bundled in. If building your own lab sounds terrible, bundles keep you accountable.
Corporate volume purchasing is another angle when your employer's training multiple people. CompTIA's volume purchasing programs slash per-voucher costs. This becomes a "talk to your manager, not your credit card" scenario.
Where to buy vouchers and schedule the exam
You can purchase vouchers directly from the CompTIA Store at store.comptia.org, through authorized CompTIA partners, or via training providers packaging vouchers inside course bundles. The exam voucher covers one attempt and expires 12 months after purchase. Set a calendar reminder. Seriously, do it now.
Pearson VUE handles testing delivery. After securing your voucher code, you schedule through the Pearson VUE website or call center. Registration demands two accounts: a CompTIA account tracking certification status and history, plus a Pearson VUE account managing scheduling and delivery. Two logins. Two separate profiles. It's.. fine, I guess.
When scheduling, enter that voucher code exactly as provided. No extra spaces, no transposed characters. Verify it applied successfully before confirming appointment details, because troubleshooting voucher issues post-confirmation is really miserable.
Also, register at least 24-48 hours ahead. Last-minute availability sometimes exists depending on test center capacity, but gambling your entire week on finding an open seat is a weird flex.
Retake policy and retake costs (what to expect)
If you fail, the retake policy's straightforward: no waiting period for your first retake, then 14-day waits after the second attempt and subsequent attempts. The painful part? Cost. Retakes match full exam price, meaning you're buying another voucher (or a dedicated retake voucher) each time.
You can sometimes purchase a retake voucher during initial checkout for slight discounts versus buying post-failure. Exam voucher bundles including one retake attempt typically run $470-$500, basically "insurance" if you're not confident about passing attempt one.
One detail people overlook: some promotional or discounted vouchers carry restrictions, so verify voucher compatibility with your intended testing method (online versus test center) before purchasing.
PT0-002 passing score and exam format
Passing score (scaled scoring) and how scoring works
The PenTest+ PT0-002 passing score is 750 on a 100-900 scale. It's scaled scoring, so don't waste energy reverse-engineering it into "I need exactly 73 correct." Focus on domain mastery and performance-based questions, because those can dramatically swing your result if you're weak on practical workflow execution.
I spent way too much time trying to calculate my exact score once during a different CompTIA exam. Kept tallying questions I thought I got right, adjusting confidence percentages, building spreadsheets. Completely pointless. The scaled scoring makes that math worthless, and honestly, you're better off just learning the material cold instead of gaming probability.
Number of questions, time limit, and question types (MCQ + PBQs)
Expect a mixture of multiple-choice and PBQs. The PBQs are where candidates burn time, not because they're impossible, but because you'll second-guess tool output or get trapped trying to achieve perfection instead of correctness.
Time management matters. A lot. Flag and keep moving.
Testing options (online vs test center)
Test centers exist globally, thousands of locations searchable by postal code or city in Pearson VUE's scheduler. Online proctored testing is the alternative, convenient but picky. You need reliable high-speed internet, webcam, microphone, and a private quiet room with zero interruptions. No second monitor allowed. No random sticky notes visible on walls. They're strict about this stuff.
If you've got roommates, barking dogs, or unstable Wi-Fi, take it at a test center and eliminate that stress variable entirely.
PenTest+ PT0-002 difficulty: what to expect
Why candidates find PT0-002 challenging
PT0-002 difficulty stems from constant context switching. One minute you're evaluating scoping and rules of engagement, next you're interpreting scan results, then suddenly you're writing what the client should actually do about discovered vulnerabilities. The exam punishes candidates who only studied tools while ignoring process, and it equally punishes those who only consumed theory without ever touching a terminal.
Common weak areas (tools, reporting, scoping, analysis)
Common failure points include tool output interpretation, professional reporting language, scoping constraints, and analysis connecting "finding" to "business risk" to "remediation steps." Another trap is code and scripting basics, not full developer-level stuff, more like "can you read this Bash script and understand what it's attempting."
How long to study for PT0-002 (by experience level)
If you've done security work previously, 4-8 weeks is realistic with consistent labs and PenTest+ PT0-002 practice tests. If you're newer to the field, 8-12 weeks is normal. Some people cram in two weeks. Some pass. Many crash spectacularly. Your choice.
PT0-002 exam objectives (domains) breakdown
Domain 1: Planning and scoping
This is where the exam gets uncomfortably adult, uncomfortably fast. Rules of engagement, legal constraints, scoping boundaries, and activities you absolutely cannot do. Clients care about this significantly more than your exploit chains.
Domain 2: Information gathering and vulnerability scanning
Reconnaissance, enumeration, scanning, and determining what actually matters. You need to read results without panicking when false positives appear, because they will.
Domain 3: Attacks and exploits
Exploitation concepts, common attack paths, and post-initial-access decisions. Not Hollywood hacking. More "what's the next logical step that won't crash production systems."
Domain 4: Reporting and communication
This is the domain candidates skip during prep. Then they fail because of it. Reporting isn't optional. You need to write findings, prioritize by severity, and communicate risk in language non-technical stakeholders actually understand.
Domain 5: Tools and code analysis
You should recognize common tools and their purposes, plus basic scripting and code review thinking. Not writing massive programs from scratch. Reading existing code and spotting security issues.
What changed in PT0-002 (vs previous versions)
Version updates typically tighten focus on real-world workflows and reporting expectations, and they update tool and technique coverage. Always download current PenTest+ PT0-002 exam objectives directly from CompTIA, because "my friend took this last year" isn't a valid study strategy.
Prerequisites and recommended experience
Official prerequisites (and what CompTIA recommends)
CompTIA doesn't enforce hard prerequisites, but it recommends prior knowledge and hands-on exposure. Their polite way of saying "don't make this your first certification ever."
Recommended prior certs/knowledge (Network+/Security+ equivalents)
Network+ and Security+ level knowledge helps tremendously. Routing fundamentals, port functions, protocol behaviors, authentication mechanisms, common defensive controls. If you're shaky there, you'll waste precious exam time on foundational concepts instead of the actual assessment.
Skills checklist before attempting PT0-002
Know how to read scan output confidently, explain common web and network vulnerabilities, understand basic Linux and Windows command-line operations, and write short remediation notes that a sysadmin won't immediately hate. That's your baseline.
Best study materials for PT0-002
Official CompTIA study resources (study guide, CertMaster, labs)
If you prefer structured learning paths, CompTIA's official resources are solid, and the labs prove useful when you don't want to DIY everything. CertMaster can be expensive though, so compare pricing against your current skill level and learning style.
Books and video courses (how to choose)
Pick one primary resource. Add a second only if the first isn't clicking for you. Accumulating too many resources transforms into procrastination with extra steps and guilt.
Hands-on labs and home lab setup (VMs, Kali, practice targets)
A basic home lab suffices: one Kali VM, a couple target VMs, and intentionally vulnerable applications. Practice the complete workflow from reconnaissance to exploitation to documentation. That loop builds muscle memory.
Study plan (2-week / 4-week / 8-week options)
Two-week plans are for experienced professionals with abundant free time. Four weeks is aggressive but achievable. Eight weeks is comfortable and provides room for hands-on penetration testing labs, review cycles, and repetition until concepts stick.
PT0-002 practice tests and exam prep strategy
Best practice test types (timed, domain-based, PBQ-focused)
Timed tests develop pacing skills. Domain-based quizzes identify weak areas requiring attention. PBQ-focused practice is the closest simulation to real exam stress you'll experience beforehand.
How many practice questions you should do
Enough that question phrasing stops surprising you. Hundreds of questions, not dozens.
How to review missed questions effectively
Review why you missed each question. Knowledge gap, misread the question, or tricky wording. Fix the underlying cause, not just the symptom. Write notes. Retest that topic later to confirm improvement.
Final week checklist and exam-day tips
Sleep properly. Check ID requirements carefully. For online exams, test your system and room setup days ahead. For test centers, arrive early and don't bring unnecessary stress.
Renewal and continuing education (CE) for PenTest+
Renewal cycle length and CE requirements
PenTest+ has renewal requirements under CompTIA's CE program, operating on a three-year cycle. You renew by earning CEUs or completing qualifying activities within that window.
Ways to renew (CEUs, higher-level certs, training)
Common options include training courses, earning higher-level certifications, and submitting CE activities. Read CompTIA's current policy pages because rules occasionally change without much fanfare.
Fees and deadlines to avoid expiration
There are renewal fees and deadlines. Miss them and you risk certification expiration, which is an expensive way to learn calendar management skills.
PT0-002 FAQs
How much does the CompTIA PenTest+ PT0-002 exam cost?
In the US, standard PT0-002 exam cost is $392 USD, with regional pricing variations elsewhere and multiple discount paths depending on eligibility status.
What is the passing score for PenTest+ PT0-002?
The PenTest+ PT0-002 passing score is 750 on a 100-900 scale.
How hard is the PT0-002 PenTest+ exam?
Hard if you avoid labs and rely exclusively on memorization. Manageable if you practice complete workflows, study the PenTest+ PT0-002 exam objectives thoroughly, and drill extensively with PenTest+ PT0-002 practice tests.
What are the PT0-002 exam objectives and domains?
Five domains: planning and scoping, information gathering and vulnerability scanning, attacks and exploits, reporting and communication, and tools and code analysis.
How do I renew my CompTIA PenTest+ certification?
Through CompTIA CE: earn sufficient CEUs or complete qualifying activities within the renewal cycle and pay required fees on time.
Next steps
Download the objectives and build your study roadmap
Grab the PenTest+ PT0-002 exam objectives and map your weak areas specifically. Make it visible somewhere. Put actual dates next to goals.
Recommended sequence: objectives, labs, practice tests, review
Start with objectives, then hands-on penetration testing labs, then practice tests, then targeted review of weak areas. Repeat this cycle until the exam feels boring, because boring usually signals "ready."
PenTest+ PT0-002 Passing Score, Exam Format, and Testing Logistics
Understanding the PenTest+ PT0-002 passing score
The PenTest+ PT0-002 passing score sits at 750 on CompTIA's scaled scoring system, which ranges from 100 to 900. Not a simple percentage.
Look, CompTIA doesn't just tally up how many questions you got right and call it a day. They use this whole scaled scoring methodology that normalizes results across different exam versions. Makes sense when you think about it because not everyone gets the exact same questions, and that would be unfair if one version was way harder than another.
The scaled score accounts for varying difficulty levels among questions. Some questions are harder than others, and CompTIA's algorithm weighs them differently. A really tough question about exploit development might count more toward your final score than a basic recall question about scanning tools. This can be frustrating because you never really know which questions matter most while you're taking the exam.
When people ask me what 750 actually means in terms of percentage, I usually say roughly 75% correct responses. That's a ballpark estimate because the scaling adjusts based on which specific question set you receive. You could theoretically answer 75% correctly and still fail if those questions happened to be easier ones. Or you might answer 70% correctly and pass if you nailed the harder questions. Weird system? Yeah, kinda.
Getting your results and understanding the score report
Immediate pass/fail notification.
Candidates receive it upon completing the exam. The moment you click that final submit button, the system calculates everything and displays your scaled score right there on the screen. I mean, talk about instant gratification or instant heartbreak, right?
The score report doesn't indicate exactly how many questions were answered correctly or incorrectly. You won't see "you got 63 out of 85 correct" or anything like that, which honestly bugs some people. Instead, you get that scaled score and a performance breakdown by domain showing whether you performed "above target," "near target," or "below target" in each of the five exam areas.
Domain-level performance indicators actually become super useful if you don't pass on your first attempt. They help failed candidates identify weak areas for focused re-study instead of just reviewing everything blindly. If you see "below target" in Domain 3 (Attacks and Exploits) but "above target" in Domain 1 (Planning and Scoping), you know exactly where to focus your retake prep. Saves time and, honestly, sanity.
PT0-002 exam format and time constraints
The PT0-002 exam contains maximum of 85 questions that must be completed within 165 minutes. That's 2 hours and 45 minutes, which gives you approximately 2 minutes per question on average. Sounds generous until you factor in those performance-based questions that can eat up 10 to 15 minutes each. Then suddenly you're scrambling.
Question types include traditional multiple-choice questions with single or multiple correct answers and performance-based questions that simulate real-world penetration testing scenarios. The PBQs are what separate this exam from something like CompTIA Security+ SY0-701 where the scenarios are more theoretical.
Performance-based questions typically appear at the beginning of the exam. You'll sit down, get through the tutorial, and boom. First thing you see is probably a simulated environment where you need to actually do something, which can be jarring if you're not expecting it. PBQs may involve interacting with command-line interfaces, analyzing log files, interpreting network diagrams, selecting appropriate tools for specific scenarios, or completing penetration testing workflows. I've heard of scenarios where you're given a Metasploit interface and need to configure the right payload. Or you're analyzing Nmap scan results to identify vulnerable services.
Multiple-choice questions range from straightforward recall questions to complex scenario-based questions requiring analysis of penetration testing situations. Some will ask you straight-up "what tool would you use for this" while others present a whole paragraph describing a client engagement and ask you to select the best approach from four options. Not gonna lie, those scenario ones can be tricky because multiple answers seem plausible.
Some multiple-choice questions include exhibits like images, code snippets, log files, or network diagrams that candidates must analyze to determine correct answers. You might see Python code and need to identify what it does, or examine a network topology and determine where to position your attack box.
I remember when I was prepping for my first penetration testing cert years back, way before CompTIA even had PenTest+, and we basically just had CEH or OSCP as options. The whole certification space has shifted dramatically. Now you've got entry points like PenTest+ that give you structured paths into offensive security without requiring you to root 30 machines in 24 hours. Different world.
Test-taking logistics and interface features
Candidates can mark questions for review and return to them before submitting the exam. This feature is clutch for time management. I always recommend answering easier questions first, marking the tough ones, then circling back because it keeps momentum going and prevents you from burning time on one brutal question while easier points sit there unanswered.
The exam interface includes basic calculator functionality and the ability to adjust text size, though no external reference materials, notes, or devices are permitted during testing.
If you're testing at a center, you need to arrive 15 to 30 minutes before scheduled appointment time for check-in procedures. This includes identity verification and secure locker storage of personal belongings. Acceptable identification includes government-issued photo ID like a driver's license, passport, or national ID card with name matching the exam registration exactly. Middle names matter here. If your voucher says "John Michael Smith" but your ID says "John M. Smith," you might have problems, which seems petty but it's their policy.
Test center rules prohibit watches, jewelry, wallets, phones, bags, study materials, and any electronic devices in the testing room. Violations result in exam dismissal without refund, which is harsh but necessary to maintain exam integrity. Can't have people cheating and devaluing everyone else's hard-earned certs. Testing centers provide scratch paper or dry-erase boards for notes and calculations. Must be returned before leaving and cannot be removed from the testing facility.
Scheduled breaks aren't included.
Bathroom breaks or other interruptions consume testing time and should be minimized. Plan accordingly. Hydrate before but don't chug a liter of water right before the exam starts.
Online proctored testing requirements
Online proctored exams require candidates to complete system checks and environmental scans before beginning. You'll show the proctor your testing area via webcam to verify no unauthorized materials are present. They'll make you pan around the room, check under your desk, show them your workspace from multiple angles. It's thorough, borderline invasive, but I get why they do it.
Online testing prohibits additional monitors, requires closing all applications except the exam software, and mandates remaining visible to the webcam throughout the entire testing session. Proctors monitor online exams via webcam and may intervene if they observe suspicious behavior, unauthorized materials, or violations of testing policies. I've heard stories of people getting flagged for looking away from the screen too much or having someone walk into the room behind them. Even a cat jumping on your desk can cause issues, which sounds ridiculous but it's real.
Technical issues during online proctored exams should be reported immediately through the proctor chat function. Significant disruptions potentially qualify for exam rescheduling without additional fees, but you need to document everything as it happens.
After the exam: getting your certification
Candidates completing the exam receive a printed score report at test centers or a digital score report for online exams. This is temporary proof of certification until the official certificate is issued. Passing candidates receive digital badges and certificates through the CompTIA certification portal within 3 to 5 business days, which can be shared on professional networking platforms and resumes.
Preparing for success with practice materials
Honestly, the best way to ensure you hit that 750 passing score is practicing with realistic questions that mirror the exam format. You can't just read theory and expect to crush performance-based questions that require actual hands-on skills. The PT0-002 Practice Exam Questions Pack for $36.99 gives you exposure to both multiple-choice and performance-based question styles so you're not surprised on exam day. You need to practice under timed conditions too. Knowing the material is one thing, but executing under that 165-minute time pressure is different, way different.
If you're coming from foundational certs like CompTIA A+ 220-1101 or CompTIA Network+ N10-008, you'll notice PT0-002 demands much more hands-on technical skill. The performance-based questions don't care if you memorized facts. You need to actually demonstrate competency with penetration testing tools and methodologies, which means lab time, not just flashcards.
Building a home lab with Kali Linux, intentionally vulnerable VMs like Metasploitable or DVWA, and practicing common attack workflows will prepare you way better than just reading study guides. Run Nmap scans, exploit vulnerabilities with Metasploit, capture traffic with Wireshark, crack passwords with John the Ripper. The practical experience translates directly to those PBQs in ways that reading about tools never will.
Time management becomes critical.
With 85 questions in 165 minutes, every second counts. Skip the PBQs initially if they're eating too much time, knock out the MCQs you're confident about, then return to the harder stuff. This strategy saved me when I took it. Every question you leave blank is guaranteed wrong, but every question you answer gives you a chance at points, so educated guessing on flagged questions beats leaving them empty.
PenTest+ PT0-002 Difficulty Level, Preparation Timeline, and Common Challenges
CompTIA PenTest+ PT0-002 exam overview
CompTIA PenTest+ PT0-002 is an intermediate step in the CompTIA pathway. It sits between Security+ (you know the basics, mostly defensive) and CASP+ (you're expected to think like a senior security person and justify decisions). Short version: not easy, not impossible.
What PT0-002 validates is practical, job-ish pentest capability. Planning and scoping, recon and scanning, exploitation, post-exploitation thinking, and then the part everyone forgets: writing it up like a professional doing vulnerability assessment and reporting for a real client who's got budgets and politics and deadlines.
Who should take it? People in SOC, sysadmin, network admin, vuln management, appsec, or junior pentest roles who want to prove they can cross the line from defensive to offensive without turning into a chaos gremlin. If you're a complete beginner to cybersecurity, honestly, don't make CompTIA PenTest+ certification your first stop. Get Network+ and Security+ level skills first, then come back.
PT0-002 exam cost and registration
The PT0-002 exam cost is basically "CompTIA pricing plus reality." Voucher price changes depending on region, promos, academic status, and whether you buy a bundle with retakes or training. Most people pay somewhere around the typical CompTIA pro-level range, and then they get mad because failing once is expensive.
Where to buy and schedule: you buy a voucher from CompTIA or an authorized partner, then schedule through Pearson VUE. Don't wait until the last week. Seats disappear.
Retakes follow CompTIA's usual policy, which means you can retake, but you pay again unless you bought a bundle that includes a retake. Not gonna lie, that bundle can be worth it if test anxiety is your thing. PBQs can make calm people spiral when a simulated terminal doesn't behave like their lab. I once watched someone spend twenty minutes trying to figure out why a command worked fine at home but threw errors in the testing environment. Turns out the exam version had slightly different syntax requirements, which is the kind of thing that'll haunt you if you're not ready for curveballs.
PT0-002 passing score and exam format
The PenTest+ PT0-002 passing score is a scaled score, and CompTIA doesn't grade like your college professor. You'll see a number, not a "you got 73 out of 90." PBQs can carry significant weight, and CompTIA's famously quiet about exact scoring.
Format breakdown: expect multiple-choice plus performance-based questions (PBQs), with a time limit that feels generous until you're 40 minutes deep into a PBQ trying to remember the exact flag for a tool you haven't touched in two weeks. Online testing is convenient, test center testing is calmer for some people. Different stress, same exam.
PenTest+ PT0-002 difficulty: what to expect
PenTest+ PT0-002 difficulty is usually rated moderately difficult to difficult by working pros. The pass rate people throw around for first-time test-takers with structured prep is roughly 60 to 70%. That tracks with what I see: people who actually do hands-on labs tend to pass, people who only memorize Q&A dumps tend to get humbled hard by scenario questions.
The real difficulty? The exam's bias toward hands-on practical application over trivia. You need ethical hacking and pentesting skills, yes, but you also need to read outputs, choose the right next step, and explain why you're doing it without breaking scope, law, or the client's production environment. That's a weird mix if you've lived your whole career in "patch it, harden it, close the ticket" mode.
PBQs are the big pain point. Candidates with limited real-world pentesting experience get hit twice: they're learning the offensive mindset and the tool workflow at the same time, and then time management goes out the window because they spend too long early, panic later, and rush the multiple-choice questions that they actually could've nailed.
Tool breadth is its own tax. PT0-002 expects functional familiarity with lots of recon, scanning, exploitation, and post-exploitation utilities. Not just "I heard of Nmap," but "I can interpret output, pick flags, and know what it can't tell me." Add Linux command-line expectations on top, and Windows-only folks feel it fast. Fragments everywhere. Terminal fear. Totally normal.
Common weak areas I see from failed attempts: command line skills on Linux, because Kali feels like a foreign country when you only speak Windows GUI. Wireless testing basics, because people skip it and then the exam doesn't skip them back. Scripting and light code analysis, because reading a snippet and spotting what it does is different from watching a video about it.
PT0-002 exam objectives (domains) breakdown
The PenTest+ PT0-002 exam objectives are where you should start, even if you hate official docs. Print them. Make them your checklist. The domains map to how real engagements run.
Domain 1 is planning and scoping. This is where technical people get tripped up by legal and business constraints like authorization, rules of engagement, data handling, and compliance. You're being tested on whether you can operate like a consultant who doesn't accidentally commit a crime.
Domain 2 covers information gathering and vulnerability scanning. Recon, enumeration, interpreting scan results, and knowing when scans lie. Network protocol analysis shows up here too, so if TCP handshakes and common ports feel fuzzy, fix that before you go hard on exploit practice.
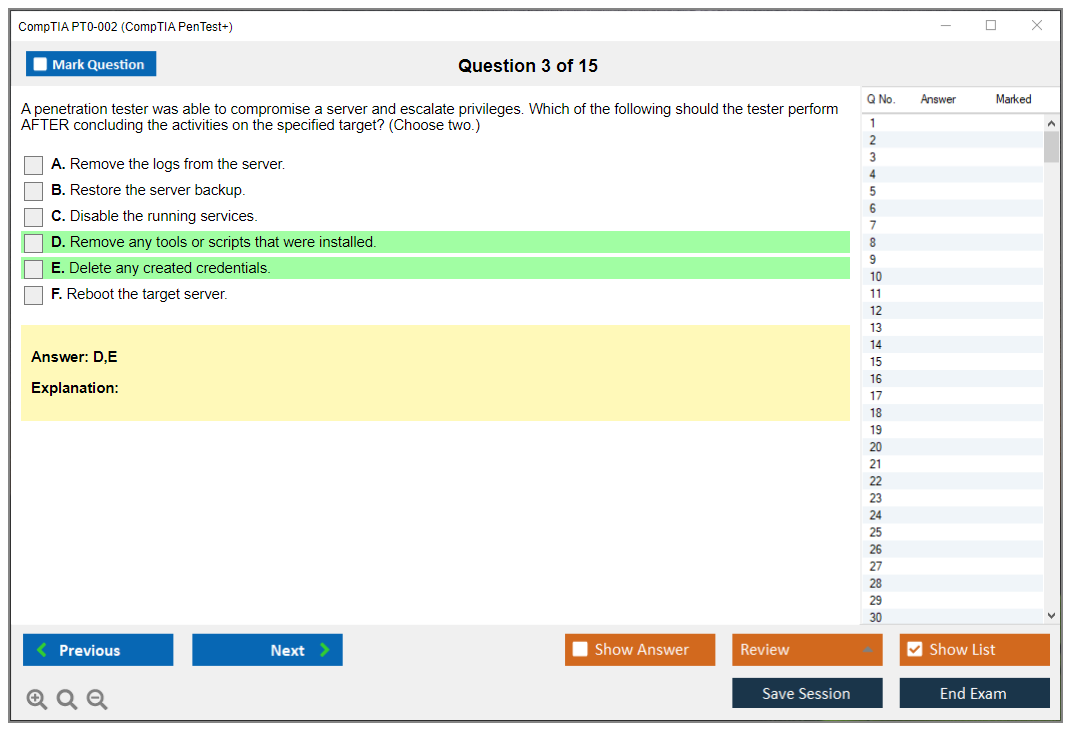
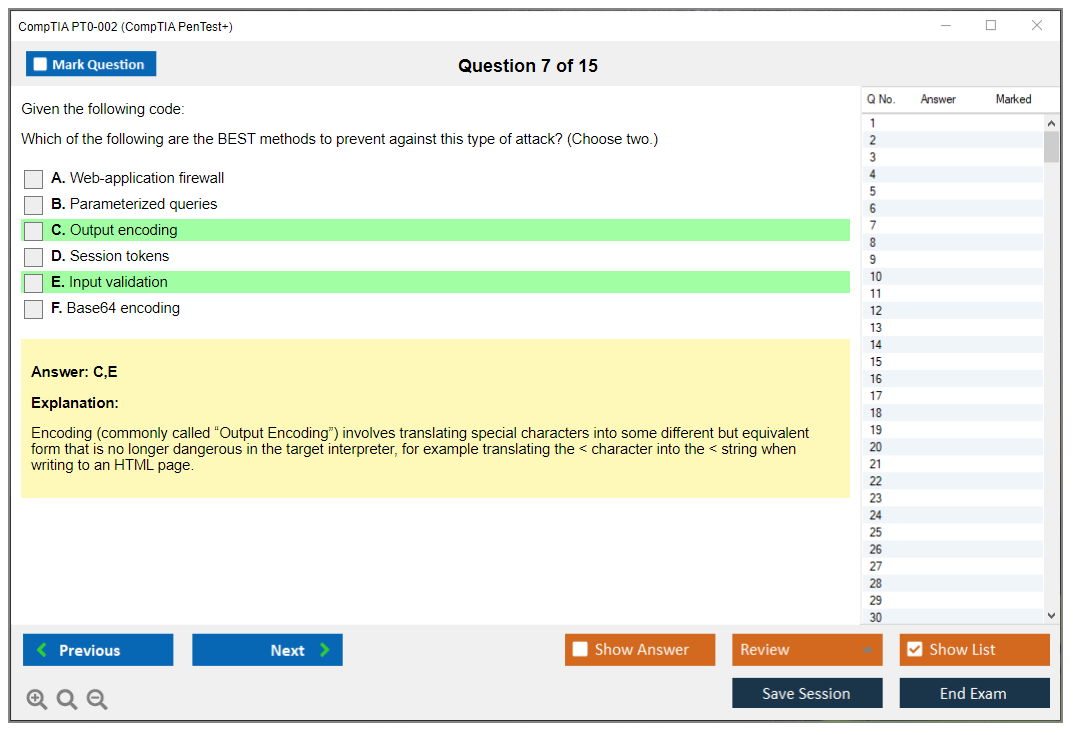
Domain 3 is attacks and exploits. Web app testing (OWASP Top 10, SQL injection variations, XSS) is a frequent offender because you need both theory and that "I've actually seen this break" muscle memory. Post-exploitation matters too: privilege escalation, lateral movement, persistence, and cleanup thinking. This is where people realize the exam isn't only about initial compromise. Wait, it's also testing if you can avoid leaving forensic breadcrumbs everywhere.
Domain 4 handles reporting and communication. Honestly, this domain is sneaky hard. You've gotta translate technical findings into business language, rate risk, and propose remediation that isn't fantasy. That's unfamiliar if you've never written for executives who don't care about your screenshot of a shell.
Domain 5 focuses on tools and code analysis. This domain punishes surface-level familiarity. You need to know when a tool's appropriate, what its limitations are, and how to interpret output, plus basic scripting and code reading. Emerging tech shows up more now: cloud and container security testing concepts that on-prem folks sometimes haven't touched.
What changed in PT0-002: more modern environments, more emphasis on applying knowledge in scenarios, and more expectation that you can reason across tools instead of memorizing one vendor workflow. Vendor-neutral is great, but it also means you can't hide inside one favorite toolkit.
Prerequisites and recommended experience
The PenTest+ PT0-002 prerequisites aren't hard gates, but CompTIA's recommendations exist for a reason. If you don't understand networking, authentication, web basics, and common defensive controls, you'll spend your study time learning foundational security instead of pentesting.
Skills checklist before you attempt it: Linux basics (files, permissions, pipes), TCP/IP fundamentals, reading logs and packet captures, web request/response understanding, and enough scripting literacy to look at a snippet and not freeze. Be honest. Fill gaps early.
Best study materials for PT0-002
PenTest+ PT0-002 study materials that work usually combine one structured "cover the objectives" resource and a lot of hands-on. Official stuff like CompTIA study guides and CertMaster can help keep you aligned to objectives, but hands-on penetration testing labs are what make the exam feel fair instead of random.
Home lab setup can be simple: a laptop or desktop with enough RAM for a couple VMs, Kali, and legal practice targets like intentionally vulnerable boxes. Spend real time here. Candidates with limited hands-on experience should plan at least 60 to 80 hours of lab work. Reading about a tool isn't the same as troubleshooting it when output looks weird.
Timelines vary. If you actively do pentesting, 4 to 6 weeks of focused study can work. If you're coming from SOC or sysadmin, plan 8 to 12 weeks. Accelerated timelines usually mean 15 to 20 hours per week, and that includes labs and review, not just watching videos at 1.5x speed while you scroll.
PT0-002 practice tests and exam prep strategy
PenTest+ PT0-002 practice tests matter, but only if you use them correctly. Timed tests help with pacing. Domain-based sets help you find holes. PBQ-focused drills help you stop panicking when the question looks like a tiny lab.
How many questions? Enough that you stop being surprised by CompTIA wording, but not so many that you memorize letter patterns. Review missed questions by tracing back to the objective, then doing a mini-lab that proves the concept. The exam loves novel scenarios that punish pure memorization.
If you want something quick to slot into your prep, I'd add a targeted question pack like PT0-002 Practice Exam Questions Pack to your routine, then treat every wrong answer like a lab assignment. Use it again later as a timed set. Then once more right before the exam. That's three different uses, not just "grind until I recognize it." Also yes, it's $36.99, which is nothing compared to a retake.
Exam-day tips: don't get trapped by PBQs at the start. Skim them, flag the monsters, knock out easy points first, then come back with a clearer head. Time pressure's real, and lots of people feel rushed on the real thing even if untimed practice felt comfy.
Renewal and continuing education (CE) for PenTest+
PenTest+ PT0-002 renewal requirements follow CompTIA CE rules: a renewal cycle, CEUs, and deadlines that'll sneak up if you ignore email. Ways to renew include earning CEUs through training and activities, or getting a higher-level cert that renews it. There's a fee, and missing the window's annoying, so track it like you track cert expirations at work.
PT0-002 faqs
How much does the CompTIA PenTest+ PT0-002 exam cost? Voucher pricing varies by region and discounts, so check current CompTIA pricing, but assume it's expensive enough that you should prep like you mean it.
What's the passing score for PenTest+ PT0-002? It's a scaled score, and CompTIA doesn't publish the exact scoring recipe.
How hard is the PT0-002 PenTest+ exam? Intermediate, often rated moderately difficult to difficult, mainly because of PBQs, tool breadth, and scenario questions.
What're the PT0-002 exam objectives and domains? Planning and scoping, recon and scanning, attacks and exploits, reporting, and tools and code analysis. Download the objectives and map your study plan to them.
How do I renew my CompTIA PenTest+ certification? Through CompTIA CE: CEUs, eligible training, higher certs, and paying the renewal fees on time.
Next steps
Download the objectives today, then build your roadmap. Objectives first, then labs, then timed practice, then review. Add a question resource like the PT0-002 Practice Exam Questions Pack when you're ready to pressure-test weak domains, especially if PBQs and scenario wording keep throwing you off.
PT0-002 Exam Objectives and Domain Breakdown with Detailed Coverage
Understanding the PenTest+ PT0-002 exam objectives structure
The PenTest+ PT0-002 exam objectives break down into five major domains with specific percentage weightings that determine how many questions come from each knowledge area. This weighting system tells you exactly where to focus your study time.
Look, if you're coming from foundational certs like SY0-601 Security+ or even N10-008 Network+, you'll notice PT0-002 demands way more hands-on technical depth. The domain breakdown matters because failing one heavily-weighted section can completely torpedo your entire exam attempt, even if you nail the others.
Domain 1: Planning and Scoping (14% coverage)
Domain 1: Planning and Scoping represents 14% of the exam (approximately 12 questions) and covers the pre-engagement phase of penetration testing projects. A lot of candidates skip over this domain thinking it's just paperwork and client conversations.
That's a mistake.
Planning and Scoping includes comparing governance, risk, and compliance concepts as they relate to penetration testing engagements and legal authorization requirements. You need to know the difference between a vulnerability assessment and a full pentest. They're not interchangeable terms, though people use them that way constantly. You need to understand when you're doing a compliance-driven test versus a red team engagement. The exam throws scenarios at you where you have to determine what's in scope, what's off-limits, and how to document it properly because one wrong move could land you in legal hot water.
This domain tests your understanding of scoping considerations including target identification, testing type determination (black box, white box, gray box), and defining rules of engagement. You can't just start hammering away at systems without understanding what methodology you're using. Black box testing means you know nothing about the target. You're simulating an external attacker with zero insider knowledge. White box gives you full documentation, credentials, source code access, the whole nine yards. Gray box sits somewhere in the middle, maybe you've got user-level credentials but not admin access.
Candidates must demonstrate knowledge of resource requirements, timeline estimation, and communication protocols established before penetration testing begins. The exam might ask you how long a typical web application test should take, or what happens when you discover something critical mid-engagement. Do you stop everything? Keep going? Wait until the report's finished? These aren't theoretical questions. They're based on real-world scenarios where the wrong answer could land you in legal trouble or get systems taken offline at the worst possible moment.
Actually, I remember one engagement where we found active malware during routine testing and the whole communication protocol question became very real very fast. You can't just put that in your final report three weeks later. But that's a whole different discussion about incident response versus pentesting scope.
Domain 1 covers target audience identification for penetration testing reports and understanding different stakeholder information needs from technical teams to executive leadership. Your report for the CISO looks completely different from what you give the sysadmin team. Like, fundamentally different documents. Executives want risk quantification and business impact in plain English. Technical folks want CVE numbers, proof-of-concept code, and specific remediation steps they can implement tomorrow.
Compliance-based assessments including PCI DSS, HIPAA, and other regulatory frameworks require understanding how penetration testing supports compliance validation. Compliance testing can be boring as hell, but it pays the bills for most pentesting firms. You need to know which frameworks require annual testing, what specific controls get tested, and how to map findings back to compliance requirements without just copy-pasting from the standard.
Domain 2: Information Gathering and Vulnerability Scanning (22% coverage)
Domain 2: Information Gathering and Vulnerability Scanning comprises 22% of the exam (approximately 19 questions) and focuses on reconnaissance and vulnerability identification phases. This is the heaviest-weighted domain, which makes sense because reconnaissance is where most pentests actually start. You can't attack what you don't know exists.
Information gathering includes both passive reconnaissance techniques that avoid direct target interaction and active scanning methods that directly probe target systems. Passive recon is like researching a company before applying for a job. You're gathering intel without them knowing you exist. Active scanning is more like calling their IT department and asking questions directly, which leaves traces everywhere.
Candidates must understand OSINT (Open Source Intelligence) gathering from public sources including social media, DNS records, WHOIS databases, and search engine reconnaissance. The exam loves OSINT questions. I've seen them on every practice test and heard about them from everyone who's taken this thing. You might get a scenario where you need to identify which tool to use for subdomain enumeration, or how to use Google dorks to find exposed configuration files sitting on public servers. Tools like theHarvester, Maltego, Shodan, and Recon-ng all fall under this domain. Some you'll use constantly in real work, others you'll mention once in your report and forget about until the next cert renewal.
This domain covers network scanning using tools like Nmap, including scan type selection and interpretation of results. Nmap isn't just "run a scan and see what happens." You need to know the difference between TCP SYN scans, TCP connect scans, UDP scans, and when each makes sense based on your situation. The exam will give you Nmap output and ask you to interpret it, or present a scenario where stealth matters and you need to choose the right scan flags to avoid detection.
Vulnerability scanning with tools like Nessus, OpenVAS, and Qualys gets tested heavily here. You need to understand credentialed versus non-credentialed scans, how to reduce false positives (because there'll be tons), and what vulnerability severity ratings actually mean in practice. A "critical" finding in an automated scan might be completely unexploitable in the real environment, while a "medium" rating could turn out to be your way into the entire network. Automated tools don't understand context.
Similar to how CS0-003 CySA+ focuses on defensive analysis, PT0-002 flips that perspective to offensive reconnaissance. You're not just identifying vulnerabilities for someone else to fix. You're figuring out which ones are actually exploitable and worth your limited time during the engagement.
Domain 3: Attacks and Exploits gets technical
Domain 3 covers 30% of the exam. Heaviest section by far. This domain tests your ability to actually exploit systems, not just find vulnerabilities and write them down. You need hands-on experience with exploitation frameworks like Metasploit, manual exploitation techniques, password attacks, and post-exploitation activities.
Performance-based questions appear here.
The exam includes scenarios where you might need to demonstrate exploiting a specific vulnerability or escalating privileges on a compromised system within their simulation environment. Wireless attacks, web application exploitation (SQLi, XSS, CSRF), and network-based attacks all fall here. You can't just memorize theory from books. You need lab time with actual tools, breaking actual systems (legally, in your home lab or platforms like HackTheBox).
Domain 4: Reporting and Communication explains your findings
Domain 4 represents 18% of exam content and focuses on documenting your penetration test results in ways that actually get read and acted upon. You need to know how to write executive summaries that don't put people to sleep, technical findings sections that developers can actually use, and remediation recommendations that are implementable rather than theoretical.
The exam tests your ability to prioritize findings based on business impact, not just technical severity scores from your scanner. Report writing might sound easy until you realize the exam expects you to understand the difference between a vulnerability, a finding, and a risk. They're related but not identical concepts. You need to know what goes in an appendix versus the main body, how to handle sensitive data in reports (you can't just include plaintext passwords, even if you found them), and what metrics actually matter to different audiences depending on their role.
Domain 5: Tools and Code Analysis rounds out coverage
Domain 5 accounts for 16% of the exam and covers tool selection, script modification, and basic code analysis. You don't need to be a software developer with ten years of experience, but you should be able to read Python or Bash scripts and understand what they're doing at a functional level. The exam might present a script and ask you to identify what it's scanning for or how to modify it for a specific purpose. Like changing target ports or adjusting timing parameters.
This domain also covers tool troubleshooting, which comes up more in real work than people expect. What do you do when your exploit keeps failing despite following every tutorial? How do you adjust your approach when defenses block your initial attack vector? These practical considerations separate people who've actually done pentesting in production environments from those who've only watched YouTube videos and read blog posts.
The CompTIA PenTest+ PT0-002 exam structure forces you to demonstrate both breadth and depth across all five domains rather than letting you specialize in just exploitation or just reporting. Similar to how PT0-001 tested earlier concepts, the updated objectives reflect current penetration testing methodologies and tools used in 2024 and beyond.
Conclusion
Wrapping it all up
Look, the CompTIA PenTest+ PT0-002 isn't some walk-in-the-park certification you can knock out over a weekend. It's really one of those exams where you've got to prove you can actually do the work, not just memorize definitions. The PBQs alone? They'll expose you if you haven't spent real time in Kali or actually ran vulnerability scans beyond clicking "Start" in some tutorial video.
But here's the thing. If you've got the ethical hacking and pentesting skills down and you're comfortable with vulnerability assessment and reporting, you're already halfway there. The hard part's behind you, honestly. The PenTest+ PT0-002 exam objectives are thorough but fair. They mirror what actual penetration testing certification exam content should look like, which is why employers actually respect this cert.
Don't overthink the PT0-002 exam cost or obsess over the PenTest+ PT0-002 passing score too much. Yes, you need 750 out of 900. Yes, you're dropping around $392 for the voucher, more if you fail and need a retake. That's real money. But compared to spending months in a job you hate because you can't prove your skills? Worth it. The PT0-002 difficulty is manageable if you put in the work with proper PenTest+ PT0-002 study materials and actually build a home lab instead of just reading about one. I mean, reading only gets you so far, right? My buddy spent six weeks just watching videos and got wrecked by the first PBQ. Actual keyboard time matters.
The PenTest+ PT0-002 prerequisites are basically "know your stuff before you show up." CompTIA recommends Network+ or Security+ level knowledge plus some hands-on experience, and that's not just corporate speak. You'll struggle without it. Period. And once you pass, remember the PenTest+ PT0-002 renewal requirements kick in after three years, so plan for those CEUs or higher-level certs to keep it active.
Here's what I'd do right now: nail down your weak domains with hands-on penetration testing labs. Set up actual VMs, break some stuff, write reports like you're billing a client. Pretend money's on the line. Then hammer through PenTest+ PT0-002 practice tests until you're consistently hitting 85%+. Not 70%, not "close enough." You want buffer room because exam day nerves are real, and they mess with even experienced folks.
If you need solid practice material that actually mirrors the exam format, check out the PT0-002 Practice Exam Questions Pack at /comptia-dumps/pt0-002/. I'm not gonna sugarcoat it: quality practice questions that actually challenge you instead of just rehashing the same easy scenarios make a massive difference when you're gauging readiness and figuring out if you're truly prepared.
You've got this. Just don't skip the labs.
Show less info
Comments
Hot Exams
Related Exams
CompTIA Server+ Certification Exam
CompTIA Data+ Certification Exam
CompTIA A+ Certification Exam: Core 1
CompTIA Cloud+
CompTIA Network+ Exam
CompTIA PenTest+ Certification Exam
CompTIA CySA+ Certification Exam (CS0-002)
CompTIA A+ Certification Exam: Core 1
CompTIA A+ Certification Exam: Core 2
CompTIA A+ Certification Core 2 Exam
CTT+ Exam (Certified Technical)
CompTIA Network+ Certification Exam
CompTIA SecurityX Certification Exam
CompTIA Cloud Essentials+
CompTIA Project +
CompTIA Advanced Security Practitioner (CASP+) Exam
How to Open Test Engine .dumpsarena Files
Use FREE DumpsArena Test Engine player to open .dumpsarena files


DumpsArena.co has a remarkable success record. We're confident of our products and provide a no hassle refund policy.

Your purchase with DumpsArena.co is safe and fast.
The DumpsArena.co website is protected by 256-bit SSL from Cloudflare, the leader in online security.