Cisco 300-215 (Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR))
Cisco 300-215 CBRFIR Exam Overview and Introduction
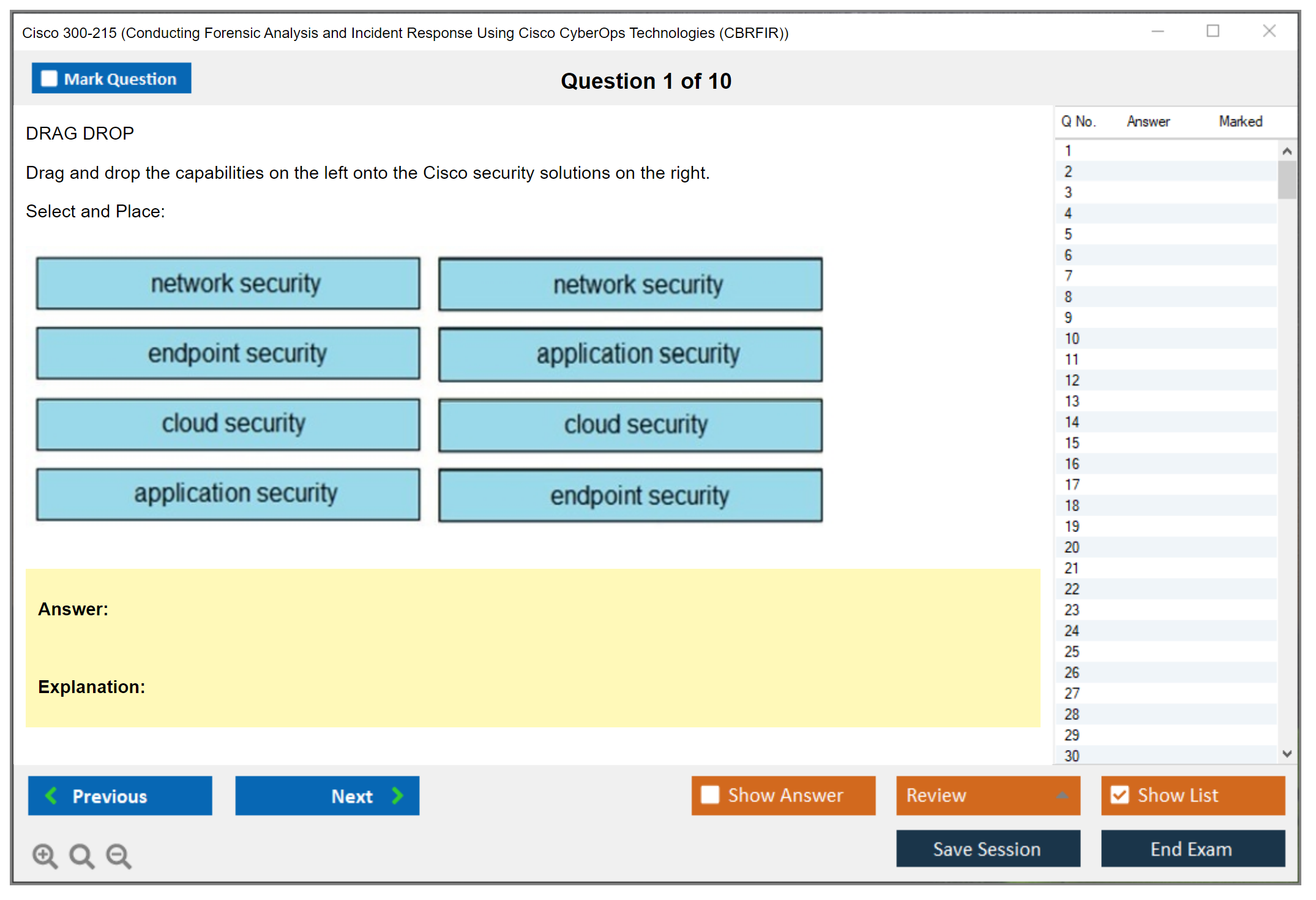
What is the Cisco 300-215 CBRFIR exam?
The Cisco 300-215 CBRFIR exam (officially titled "Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies") is a professional-level concentration test that validates your ability to perform hands-on digital forensics and incident response work. This is not rote memorization.
It's built to prove you can actually dig through malware artifacts, reconstruct attack timelines, and coordinate a multi-phase incident response workflow using both Cisco platforms and third-party forensic tools that real SOC teams rely on daily. Not just bubble in answers about abstract concepts you'll forget next week.
Within Cisco's security certification portfolio, the 300-215 CBRFIR exam is one of several concentration options for earning the CyberOps Professional certification. You can't just walk in and take it though. You need to pass the 350-201 CBRCOR core exam first, which covers foundational security operations and threat analysis concepts. Once you've cleared that hurdle, you pick a concentration. CBRFIR focuses specifically on forensics and incident response, while alternatives like 200-201 CBROPS target entry-level operations. The professional-level track separates people who've moved past basic monitoring into roles where you're investigating breaches, collecting evidence, and building cases.
This exam aligns tightly with what modern SOC analysts and DFIR specialists do every day. Real-world scenarios dominate the test: analyzing memory dumps, triaging alerts from Cisco Secure Endpoint (formerly AMP for Endpoints), correlating network flow data from Cisco Secure Network Analytics (Stealthwatch), and using Cisco SecureX to orchestrate investigations across multiple security tools. It covers third-party forensic platforms and open-source tools too. No real shop runs purely on one vendor's stack, right? You'll need familiarity with the broader ecosystem that fills gaps in any security operation.
Who should take this exam
Security operations center analysts looking to level up their forensic chops? Prime candidates.
If you're currently in a SOC and find yourself wanting deeper technical skills to investigate incidents instead of just escalating tickets, CBRFIR gives you that credential. Incident response team members already doing DFIR work will find the exam validates what they're doing while filling knowledge gaps around Cisco-specific tooling.
Security engineers who handle post-incident investigations should consider it too. Network security administrators expanding into threat hunting? Yeah, this applies. You need a solid foundation before attempting this though. Cisco recommends three to five years of security operations experience, and that's not arbitrary. You should be comfortable with network protocols, understand basic malware analysis concepts, and have touched incident response workflows even if you weren't leading them.
Cybersecurity professionals transitioning from pure network or systems work into forensic roles will benefit, but expect a learning curve if you haven't worked security operations before. The exam assumes you know what indicators of compromise look like and can differentiate normal network behavior from malicious activity without someone holding your hand. I spent about six months in a junior SOC role before I felt ready to even think about professional-level material, and that timeline felt rushed.
Where 300-215 fits in the certification path
The CyberOps Professional certification requires two exams: the 350-201 CBRCOR core exam plus one concentration. CBRFIR is that concentration option when your career leans toward forensics and incident response rather than general security operations. Other concentration options exist, like implementing security solutions with exams such as 300-710 SNCF or 300-715 SISE, but those stress deployment and configuration over investigation and analysis.
Already earned the CyberOps Associate?
If you've passed 200-201 CBROPS, the professional track is your logical next step. The associate level proves you understand security monitoring fundamentals. The professional level proves you can respond to and investigate actual incidents. This distinction matters when employers review resumes. Associate says "I can watch dashboards," professional says "I can lead investigations."
The certification opens pathways to expert-level credentials too, though Cisco's security expert track focuses more on architecture and design. For pure technical depth in operations and forensics, CyberOps Professional represents the ceiling unless you branch into specialized areas like 350-701 SCOR for broader security infrastructure.
Key technologies you'll encounter
Cisco SecureX ties everything together as the orchestration layer. You'll need to understand how it aggregates data from multiple security products and how to build investigation workflows within the platform. Cisco Secure Endpoint forensics capabilities get heavy coverage: file trajectory analysis, device isolation, prevalence checking, all the features that let you determine what a piece of malware did across your environment.
Cisco Secure Malware Analytics (Threat Grid) integration comes up frequently for automated malware sandboxing and behavioral analysis. Cisco Secure Network Analytics (Stealthwatch) teaches you how to analyze NetFlow data to identify lateral movement, data exfiltration, and command-and-control communications. The exam also tests third-party forensic tools and open-source platforms because no real SOC runs purely on one vendor's stack. You'll work with memory forensics frameworks, disk imaging tools, and log analysis platforms that security teams actually use.
Exam format and what happens after you pass
You'll take the Cisco 300-215 CBRFIR exam through Pearson VUE test centers or via online proctoring if that's your preference. Expect multiple question types including multiple choice, drag-and-drop exercises, and possibly simulations where you perform actual tasks in a simulated environment. Cisco doesn't publish exact question counts or duration anymore for professional exams, so verify current details on their official exam page before booking.
You sign an NDA before starting, which means you can't discuss specific questions afterward. You'll get preliminary results immediately after finishing, with official scores appearing in your Cisco CertMetrics account shortly after. The certification stays valid for three years from your pass date, and that three-year clock matters because technology and threats evolve fast. Renewal options include retaking an exam or earning continuing education credits through Cisco's program.
Career-wise, the CyberOps Professional credential carries weight. Employers actively seek candidates with forensics and incident response skills, and having Cisco's backing on your resume demonstrates you can work with enterprise-grade security platforms. Salary implications vary by region and role, but professional-level security certifications consistently correlate with higher compensation compared to associate-level credentials. The certification also maps to frameworks like NICE and NIST that government and enterprise organizations use to define cybersecurity job roles, which helps when you're applying for positions with specific certification requirements.
Cisco 300-215 CBRFIR Exam Cost, Registration, and Logistics
Cisco 300-215 CBRFIR exam overview
The Cisco 300-215 CBRFIR exam is the concentration test called Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR), and it's built for folks doing SOC work, incident response, and that practical "what the hell happened here?" side of security. Not theory. Not vibes. The thing is, it's closer to real forensic analysis workflows CyberOps teams actually run when they're staring at logs at 2 a.m. and somebody swears nothing changed, but you know something absolutely did.
Who should take it? Incident responders, SOC analysts, security engineers who get pulled into investigations, and anyone trying to prove they can follow incident response and digital forensics Cisco style with Cisco tooling in the mix. Some experience helps. A lot, actually.
Where it fits: it's a Cisco CyberOps Professional concentration exam, so you need to budget and plan for the full path, meaning a core exam plus one concentration like this. That "core plus concentration" structure matters because cost and scheduling become a whole different thing when you're doing two exams, not one. Two appointments. Two chances to reschedule. Two separate fees.
Cisco 300-215 CBRFIR exam cost and registration
Let's talk 300-215 CBRFIR cost. Standard exam fee? $400 USD, but you should verify current pricing on Cisco's site right before you pay because Cisco has changed pricing before and Pearson VUE checkout screens aren't the place you want surprises lurking. Regional pricing variations are real too. Sometimes you'll see the fee in local currency, sometimes converted at a rate that doesn't match what your bank thinks today's rate is. Currency conversion fees. Card issuer "international" fees. Annoying little extras that add up.
Taxes depend on where you sit the exam. VAT, GST, sales tax, whatever your jurisdiction adds, can land on top of the base price, and that's why two people can book the same test and pay different totals. Some corporate payment methods trigger extra processing rules. Fun times.
No separate cost for the exam blueprint or basic study info, thankfully. The 300-215 CBRFIR exam objectives are published, and the CBRFIR blueprint domains are available without paying Cisco a separate fee. Same deal for a lot of Cisco documentation. Your spend is usually training, labs, and time, not "unlocking" the blueprint like some pay-to-play nonsense.
Compared with other Cisco pro-level concentration exams, $400 is pretty typical. Some exams are cheaper, some are the same, and a few tracks feel like death by a thousand receipts once you add official training. If you're budgeting the complete path, do the math as "core exam fee, concentration exam fee, retake buffer, training." I mean, even if you're confident, you want a contingency fund because retake policies exist for a reason. People fail. It happens. I've watched someone walk out of a test center, call their boss, and have to explain why they need another week and another $400. Not a fun conversation.
Where and how to register for the 300-215 CBRFIR exam
Registration is basically Cisco account plus Pearson VUE scheduling. First, create or sign in to your Cisco certification profile (CertMetrics is usually where your identity and history end up). Then you click through to Pearson VUE from the Cisco certification pages and pick the exam. Simple enough.
Next decision: test center vs online proctored delivery. Pick carefully. Switching later? Total hassle.
Scheduling is straightforward. Choose a date, see time slots, confirm details, pay, and then you'll get confirmation emails from Pearson VUE. Save them. Screenshot the appointment info too because I've learned this the hard way. Appointment management is done in Pearson VUE, not in some random Cisco portal you bookmarked three years ago and forgot about.
ID requirements matter on exam day. Like, really matter. Usually it's one or two forms of identification depending on country and test center rules, and the name must match exactly. Not mostly. Not "close enough." Exactly. If your Cisco profile says "Mike" and your ID says "Michael," fix it early because nobody wants that argument at the check-in desk while stressed before an exam.
Reschedule and retake policies for 300-215
Rescheduling typically has a 24 to 48 hour cutoff before your appointment. That window can vary by program and region, so confirm the policy shown during checkout, but don't plan on "I'll move it the night before" unless you enjoy throwing money away. Late reschedules can trigger fees, and no-shows often mean you lose the whole exam fee. Brutal? Absolutely. Common, though.
Retakes have waiting periods. The first retake is typically a 5-day wait, and later attempts can require longer waits, depending on Cisco's current rules for that track. There can also be limits on maximum attempts within a certification period. Read the policy now, not after a failed attempt when you're stressed and trying to rebook for next weekend because your manager's asking questions.
Refunds are limited. Exceptional circumstances exist, but they're not a strategy. If you think there's any chance your week explodes, reschedule early and keep your options open instead of gambling.
Test center vs online proctored exam
Test centers are boring. That's the point. Controlled environment, fewer technical surprises, and you're not gambling that your neighbor won't start mowing the lawn during check-in or your cat won't walk across the keyboard. If you have flaky internet or you share a living space, a test center is usually the safer call, period.
Online proctored is convenient, I'll give it that. No commute. More time slots. Home testing. But you must meet technical requirements: webcam, stable internet, a supported OS and browser, and a workspace that passes the room scan. Environmental requirements get strict. Quiet room, clear desk, no extra monitors, decent lighting. Even innocent stuff like sticky notes or a smartwatch can cause drama with proctors.
Check-in is different too. At a test center you show up early and they handle the process, pretty straightforward. Online you do the system test, upload photos, scan the room, and wait for the proctor, and the most common issues are audio permissions, corporate VPNs, locked-down work laptops, and Wi-Fi that looks fine until it isn't, right when you need it most. Troubleshooting tip: use a personal computer you control, run the Pearson VUE system test days before, and don't change anything last minute. Seriously, don't update your OS the night before.
Preparation timeline and scheduling strategy
How long should you study? Depends on background, but most people need a real block of time because 300-215 CBRFIR difficulty is not beginner-friendly if you haven't done investigations before. If you already live in IR tickets and know forensic analysis workflows CyberOps teams follow, you might be fine with 4 to 6 weeks. If you're new to DFIR concepts, plan longer, and build hands-on time around logs, alerts, and casework, not just reading slides or watching videos passively.
Booking early has one big advantage: it forces a deadline and keeps you accountable. Booking late avoids wasting money if you're not ready. Look, I've done both approaches. The sweet spot is booking when you're 70% through your plan, then leaving buffer time for unexpected delays, extra review, or a week where work eats your brain and you accomplish nothing study-wise.
Avoid holiday periods and end-of-quarter chaos if you can because time slots disappear and corporate training schedules get weird around fiscal year planning. Also, if your employer reimburses, align your exam date with their approval cycle so you're not floating $400 plus tax for months waiting for reimbursement to hit your account.
Quick answers people ask anyway
How much does the Cisco 300-215 CBRFIR exam cost? Usually $400 USD plus local taxes and possible currency conversion fees. Verify on Cisco before paying, always.
What is the 300-215 CBRFIR passing score? Cisco doesn't always publish a fixed number publicly, and it can vary by exam form, so check the official exam page for what they disclose currently.
Is Cisco 300-215 CBRFIR hard? If you haven't done IR or forensics work, yes, absolutely. If you have, it's still serious but fair enough.
What are the objectives for CBRFIR? The published 300-215 CBRFIR exam objectives map to incident response process, investigative steps, and tooling that match the blueprint domains Cisco outlines.
How do I renew after passing Cisco 300-215? Track your 300-215 CBRFIR renewal status in CertMetrics and use Cisco security certification recertification options like continuing education credits or passing eligible exams, depending on the current policy. Also, no, you don't need to pay for the blueprint, but you probably will pay for 300-215 CBRFIR study materials and maybe 300-215 CBRFIR practice tests if you want realistic timing and question pressure before the real thing.
300-215 CBRFIR Passing Score, Exam Format, and Scoring
Understanding the official passing score for 300-215 CBRFIR
Cisco doesn't mess around here. Their 300-215 CBRFIR exam uses scaled scoring from 300 to 1000 points. Passing usually sits somewhere between 750 and 850 points, but you need to check the official exam page before registering because Cisco adjusts these thresholds periodically based on actual performance data and content updates.
Why adjust scores? It keeps things consistent across different exam versions. When Cisco updates questions or tweaks difficulty levels, they recalibrate the passing threshold so earning this certification means roughly the same thing whether you took it last month or next week. Otherwise you'd have people getting certified under completely different standards, which would be a mess.
How scaled scoring actually works
Scaled scoring isn't your raw percentage multiplied by some magic number. Way more complex than that. Cisco uses psychometric analysis to weight questions by difficulty and importance. A super hard forensic analysis simulation question? Worth more than basic multiple-choice about IR terminology.
You might answer 60% correctly and fail. Or answer 55% and pass. Depends entirely on which questions you got right. The system accounts for question difficulty, so don't try calculating your score during the exam. Just focus on answering what's in front of you.
Partial credit and complex question types
Most people don't realize this. Those drag-and-drop sequencing exercises and multi-select questions on the 300-215 CBRFIR exam format award partial credit. If a question asks you to select three correct incident response phases and you pick two right plus one wrong, you get some points but not full credit.
This matters because you should always attempt every question. No exceptions. There's no penalty for guessing on the Cisco 300-215 CBRFIR exam. Even if you're completely stumped on a packet capture analysis question, take your best shot. Blank answers definitely get you zero points.
Score reporting breakdown
When you finish you get immediate pass/fail notification on screen. No waiting around wondering. The detailed score report shows up in your Cisco CertMetrics account within 48 hours, and it's actually useful. You'll see performance breakdowns by exam domain. Maybe you crushed forensic analysis workflows but struggled with containment strategies.
What you won't get is question-level feedback. Cisco doesn't tell you which specific questions you missed or show correct answers. That would compromise exam security, and they guard those test questions like nuclear codes.
What the exam format looks like
The 300-215 typically includes 55 to 65 questions. Verify current count on the official blueprint. You get 120 minutes to work through everything. Two full hours. The tutorial time at the start doesn't count against your exam duration, so use those few minutes to get comfortable with the interface and testing controls.
There's usually a survey at the end asking about your experience. Optional and not scored. I always skip it because my brain is fried by that point.
Question distribution follows exam domains. Heavier weighting on core forensic analysis and incident response process steps. Lighter coverage of tool-specific features.
Different question types you'll encounter
Multiple-choice single answer questions are your bread and butter. Most of the exam uses this format. Then you've got multiple-choice multiple answer questions where you need to "select all that apply," which are trickier because you don't know if the right answer is two options or four.
Drag-and-drop exercises might ask you to sequence IR phases or match forensic artifacts to analysis techniques. Simulation questions use Cisco interfaces where you actually configure something or run commands. Exhibit-based questions show you log files, packet captures, or screenshots and ask you to interpret what you're seeing. Scenario-based questions present a multi-step incident and test your reasoning through the whole thing.
The simulations are the most time-consuming. Budget extra time for those.
If you don't pass the first time
Your score report becomes your study guide. If you scored poorly in the "forensic analysis workflows" domain but did well everywhere else, you know exactly where to focus. The waiting period before retaking is typically five days minimum, though you should confirm current retake policies when scheduling.
Failing sucks. And costs money. The 300-215 CBRFIR cost for each attempt adds up, so develop a targeted restudy plan before booking your retake. Maybe you need hands-on lab practice with packet captures instead of just reading about them. Maybe you need official Cisco training instead of whatever random YouTube videos you watched the first time.
How this fits into your certification path
The 300-215 is a concentration exam for Cisco CyberOps Professional. You need to pass a core exam first, typically 350-201 CBRCOR, before your concentration exam counts toward the full certification. Order matters here. If you pass 300-215 first, that result stays valid for three years while you work on the core, but you won't get the full certification until both are complete.
Once you pass both your digital badge typically issues within a week. The certification itself is valid for three years, and the clock starts when you complete your final exam. For context, this works similarly to other professional-level paths like passing 350-401 ENCOR for enterprise networking or 350-701 SCOR for security core.
Your CertMetrics account tracks everything. Keep that login handy for checking status and planning your Cisco security certification recertification when the time comes.
300-215 CBRFIR Difficulty Level and What Makes It Challenging
Cisco 300-215 CBRFIR exam overview
The Cisco 300-215 CBRFIR exam is Cisco's CyberOps Professional concentration test for incident response and digital forensics work, with a heavy tilt toward doing investigations inside Cisco's security stack, not just talking about them. It's aimed at SOC analysts, DFIR folks, IR leads, and security engineers who already live in logs and tickets. Not beginners. At all.
Where it fits matters. This is a Cisco CyberOps Professional concentration exam, so you're expected to show you can operate, triage, and explain decisions under pressure while bouncing between tooling and DFIR concepts that map to real casework.
Cisco 300-215 CBRFIR exam cost and registration
300-215 CBRFIR cost is typically in the Cisco professional exam range (think a few hundred USD), and then you get local taxes, currency conversion, and whatever Pearson VUE adds in your region. The price is annoying, so confirm the current number on Cisco's exam page before you schedule, because it changes and people love quoting last year's pricing like it's gospel.
Registration is standard Cisco-to-Pearson VUE flow. Book early if you want a weekend slot. If you're the type who reschedules twice, double-check the retake and reschedule rules before you click pay.
300-215 CBRFIR passing score and exam format
300-215 CBRFIR passing score is the classic Cisco situation: they don't always publish a fixed score the way some vendors do, and it can vary by exam form. You can't "aim for 820" with confidence. You aim for mastery.
Expect scenario-heavy questions. Some feel like "what would you do next" and some feel like "what does this artifact mean." Time goes fast. Complex prompts. Lots of reading. And if you're slow at interpreting logs or packet snippets, you'll feel it.
300-215 CBRFIR difficulty: what to expect
300-215 CBRFIR difficulty is intermediate to advanced, and honestly it's closer to advanced if you don't have hands-on time with the Cisco tools. Compared with other Cisco professional exams, it's less about memorizing commands and more about reasoning through messy evidence, which sounds nicer until you're on question 43 and you're still decoding what the alert timeline is trying to say.
Associate-level exams reward breadth. This one? Depth wins. That's the big shift. You're expected to understand forensic analysis workflows CyberOps style, which means methodology, evidence handling, investigative order, and when to pivot from host to network to malware clues. And you have to do it while translating vendor terminology back to industry-standard concepts, which is a sneaky time sink.
Pass rate estimates are always unofficial, but candidate feedback trends usually cluster around "harder than expected" and "labs would've helped." A lot of people fail because they studied like it was a vocabulary test. Fragments. Flashcards. Then boom, a scenario question that asks you to choose the best next action in an incident response process phase, and the "right" answer depends on priorities and containment trade-offs. I once watched a colleague with three certs and five years of SOC time walk out shaking his head because he'd prepped for definitions instead of decisions.
Common challenges candidates face with 300-215
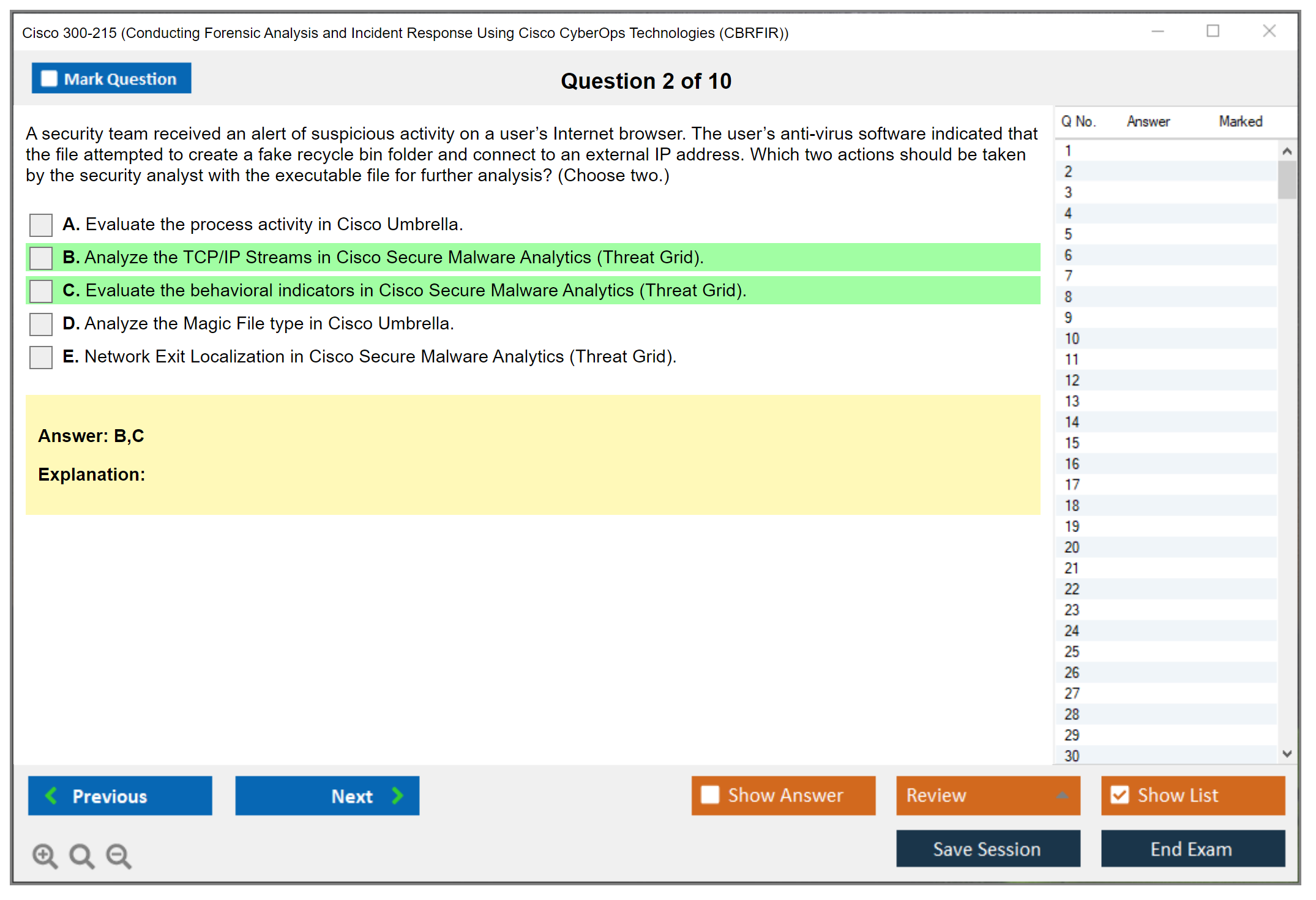
The most common pain? Workflow thinking. Deep forensic analysis workflows and methodology understanding isn't optional, because the exam leans on order-of-operations logic: what you collect first, what you preserve, what you can safely change, and how you document decisions when the business wants the system back yesterday.
Another big one is tool hopping. Familiarity with multiple Cisco security product interfaces is a real factor, because you might conceptually know what "EDR isolation" means, but the question's framed through Cisco Secure Endpoint screens, telemetry terms, and investigation features. You have to recognize what's being described without a screenshot.
Also, interpreting complex log files and network traffic captures. You don't need to be Wireshark-famous, but you need to read enough packet and flow context to spot beaconing, lateral movement hints, odd DNS, and "this isn't normal" authentication patterns.
Time management is its own monster. Complex scenarios take longer, and if you get stuck trying to be 100% certain on every artifact, you'll run out of minutes and start guessing late. Balancing Cisco-specific knowledge with general DFIR principles is a constant tension, because the exam wants both and it punishes people who only have one side.
Technical complexity areas in the exam
Memory forensics and volatile data analysis concepts show up as "what can you get from RAM" thinking. You should know why volatility matters, what you lose after reboot, and what volatile artifacts can prove, even if you're not running plugins in the exam.
Disk forensics includes file system artifacts, recovery ideas, and the kind of reasoning you use when timelines don't match user stories. Network forensics hits packet analysis and flow data. You need to connect indicators to behavior, not just name protocols.
Malware analysis is more behavioral than reverse-engineering. Think execution chains, persistence clues, and sandbox outputs. EDR investigation workflows matter too, because modern IR is often "follow the telemetry," contain, scope, then eradicate.
Security orchestration and automated response scenarios can appear as "what should be automated" and "what could backfire," because automation's great until it blocks a business-critical subnet. Context matters.
Cisco-specific technology learning curve
Mastering Cisco SecureX navigation and features can be a learning curve if you've never pivoted through incidents, observables, and casebooks inside it. Cisco Secure Endpoint forensic capabilities matter for endpoint isolation, trajectory views, and how you validate whether an alert's real or noisy.
Threat Grid is another one. You should be comfortable with what a sandbox report's telling you, what indicators are strong, what's weak, and what "looks scary but is common." Secure Network Analytics (Stealthwatch) is flow-focused, so you need to interpret conversations, anomalies, host groups, and "why's this host suddenly talking like that."
Integration between products is part of the story too. Cisco likes connected workflows, and the exam likes asking about pivots. Vendor-specific terminology versus industry-standard concepts is where people get tripped, because you know the concept but you don't recognize Cisco's label for it.
Hands-on vs theoretical knowledge balance
Book knowledge alone? Insufficient for the Cisco 300-215 CBRFIR exam. You can read about investigations forever, but the exam wants you to move like an analyst: collect, pivot, confirm, decide, document. That muscle memory only comes from labs, even simulated ones, because you need to practice the boring stuff like filtering noise, validating timestamps, and choosing the next data source when your first lead dies.
Simulated practice is good. Production experience is better. Troubleshooting skills come from real alerts that don't line up neatly, where you learn to stop chasing one shiny indicator and instead scope the incident properly.
How long to study for 300-215 based on background
Strong DFIR background: 4 to 6 weeks of focused study, mostly Cisco tooling and mapping to the CBRFIR blueprint domains. SOC analysts with limited forensics: 8 to 12 weeks, because you'll be learning methodology while learning tools.
Network security pros transitioning: 10 to 14 weeks. You'll know traffic, but host forensics and IR decision-making will slow you down. Complete beginners to incident response: 16 weeks or more, and honestly you should get real practice first. Daily hours available matters. Prior certs help. Accelerated paths save time but increase risk.
Strategies to overcome difficulty and succeed
Build a structured plan tied to the 300-215 CBRFIR exam objectives, with milestones you can measure weekly. Prioritize hands-on lab time over passive reading, because the exam rewards operational confidence. Reading alone doesn't teach you how to pivot when the first hypothesis is wrong.
Use spaced repetition for memorization-heavy topics like artifacts and IR phases. Regular 300-215 CBRFIR practice tests help you find weak spots, not "learn the questions." Schedule the exam when you're consistently scoring 85% or higher on good practice sets, because exam-day stress will shave points off.
If you want targeted practice, the 300-215 Practice Exam Questions Pack is $36.99 and can help you pressure-test your timing and scenario reading. Treat it like a diagnostic tool, not a magic key. Same link again for later when you're ready to simulate exam pacing: 300-215 Practice Exam Questions Pack.
Comparison with other security certifications and renewal
Compared with GCIH, CBRFIR feels more vendor-anchored and workflow-driven inside Cisco products. Compared with GCFA, it's usually less deep on pure forensic internals, but it's harder on tool context switching and "what do you do next" operational judgment.
For 300-215 CBRFIR prerequisites, Cisco doesn't require formal prereqs, but you'll want solid networking, security operations basics, and comfort with endpoint and network telemetry. For 300-215 CBRFIR renewal, it rolls into Cisco security certification recertification rules for CyberOps Pro, so track your timeline in CertMetrics and choose retake versus CE credits based on how you prefer to maintain momentum. If you're practicing for a retake window or just want more reps, the 300-215 Practice Exam Questions Pack is a straightforward way to keep yourself honest.
FAQ (People Also Ask)
How much does the Cisco 300-215 CBRFIR exam cost? It's typically a few hundred USD plus local fees, so confirm the current 300-215 CBRFIR cost on Cisco's exam page before booking.
What is the passing score for the 300-215 CBRFIR exam? Cisco may vary it by form, so treat the 300-215 CBRFIR passing score as "aim for mastery," not a fixed target.
Is Cisco 300-215 CBRFIR hard? Yes. Overall difficulty: intermediate to advanced, and it feels advanced without hands-on time.
What are the objectives for Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)? They map to CBRFIR blueprint domains around endpoint, network, malware, orchestration, and incident response decision-making with Cisco tools.
How do I renew Cisco CyberOps Professional after passing 300-215? Use Cisco's recert rules: either earn CE credits or pass qualifying exams before expiration, and track it in CertMetrics for clean 300-215 CBRFIR renewal planning.
300-215 CBRFIR Exam Objectives and Blueprint Domains
Official exam blueprint overview and structure
Here's the thing. The Cisco 300-215 CBRFIR exam isn't just random questions thrown at you. There's actually a blueprint. Your roadmap, basically. Honestly, if you haven't downloaded it from Cisco's official certification website before studying, you're already playing catch-up, and that's not where you wanna be.
The blueprint breaks down exactly what you need to know. Everything. You'll find it on the Cisco Learning Network under the CyberOps Professional certification track, where the document lists every objective, every domain, and the percentage weighting for each section. This maps directly to how many questions you'll encounter from that particular area. Not gonna lie, version tracking matters here because Cisco updates these blueprints periodically when technologies evolve or exam focus shifts. Always verify you're studying the current version, usually marked with a version number and effective date.
When the blueprint says "describe," it's testing conceptual understanding. "Implement" means you need hands-on knowledge of actually configuring or executing something. "Troubleshoot" is the deep end. You're expected to diagnose problems and know how to fix them under pressure, which honestly can be tricky. Wait, let me back up. The 300-215 Practice Exam Questions Pack at $36.99 can help you test which action verbs you're actually ready for versus which ones still trip you up.
Domain 1: Endpoint Threat Analysis and Computer Forensics (weight around 30%)
This domain's the heaviest hitter. Thirty percent of your exam.
You're diving into endpoint compromise indicators and forensic artifacts across multiple operating systems, and it gets detailed fast. Windows forensics dominates here. Registry analysis like HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run for persistence checks, event logs (Security, System, Application logs with Event ID patterns), and prefetch files that show program execution history. Then there's Linux and Unix forensics with /var/log/ directories, bash history files that reveal attacker commands, cron jobs for scheduled malicious tasks.
macOS forensics gets tested too. Less heavily, sure, but it's there. You need to know where artifacts live, like in ~/Library/Preferences/ and system logs in /var/log/system.log. Memory forensics is huge. Analyzing running processes, active network connections, detecting malware signatures in RAM dumps. File system forensics covers MFT (Master File Table) analysis on NTFS, recovering deleted files with carving techniques, and creating forensic timelines that show the sequence of attacker actions.
Cisco Secure Endpoint (formerly AMP for Endpoints) features prominently here. You need to know its investigation workflows, trajectory views, and how to pull forensic data from the console. If you're coming from the 200-201 CBROPS foundation exam, this builds directly on those concepts but goes way deeper into actual forensic methodology.
Quick tangent. A lot of people skip the memory forensics piece because it feels abstract compared to file system work. That's a mistake. Some of the trickiest exam scenarios involve malware that exists only in RAM, stuff that never touches disk. You can't autopsy what you can't see, so knowing how to capture and analyze volatile memory becomes critical when dealing with fileless attacks.
Network forensics and packet-level investigation
Domain 2 sits at roughly 25% of the exam.
Packet capture analysis using Wireshark? Non-negotiable knowledge. You'll need to filter traffic, follow TCP streams, identify protocol weirdness, and spot malicious payloads in packet contents. Network flow data analysis means understanding NetFlow records like source and destination IPs, ports, byte counts, timing data. Cisco Secure Network Analytics (the product formerly known as Stealthwatch) is your primary tool here for flow-based investigation.
Identifying command and control communication patterns is critical, and honestly, this is where things get interesting. C2 traffic often uses regular beaconing intervals, specific user agents, or unusual destination ports. Lateral movement shows up in network traffic as RDP connections, SMB traffic between workstations, or admin tool usage across multiple systems. DNS analysis reveals exfiltration through DNS tunneling and connections to known malicious domains.
Proxy log analysis and web traffic forensics round this out. You're looking at HTTP headers, POST data that might contain stolen information, and URL patterns that indicate compromise. The 350-701 SCOR exam covers some security concepts that overlap here, but CBRFIR goes deeper into the investigative analysis side rather than just configuration.
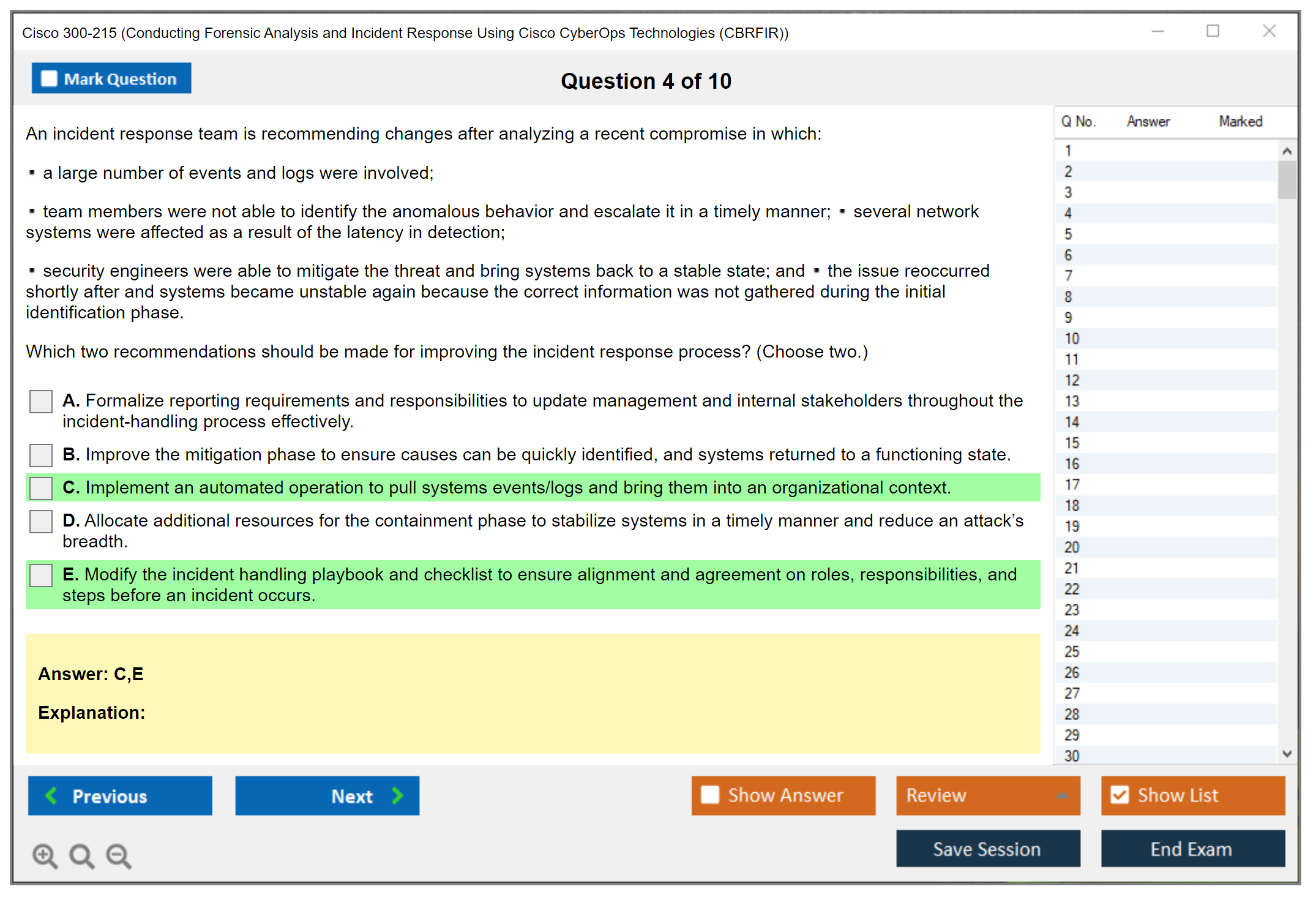
Incident response process and procedures
Domain 3 weighs in at about 20%.
The NIST incident response lifecycle is your framework. Preparation, detection and analysis, containment/eradication/recovery, and post-incident activity. SANS has a similar six-phase process that often shows up in exam scenarios. You need to know triage procedures, how to quickly assess severity and scope when an alert fires.
Containment strategies vary. Network isolation might mean VLAN changes or firewall rules. Account disabling stops lateral movement. System quarantine prevents further compromise spread. Eradication techniques include removing malware, closing vulnerabilities, and patching systems. Recovery procedures bring systems back online safely while monitoring for re-infection.
Chain of custody is legally important. Really important, I mean it. You document who handled evidence, when, and how it was stored. Any break in the chain can invalidate forensic findings in legal proceedings. Post-incident reporting and lessons learned sessions help organizations improve their security posture for next time.
Data and event analysis across security tools
Domain 4 represents roughly 15% of exam content.
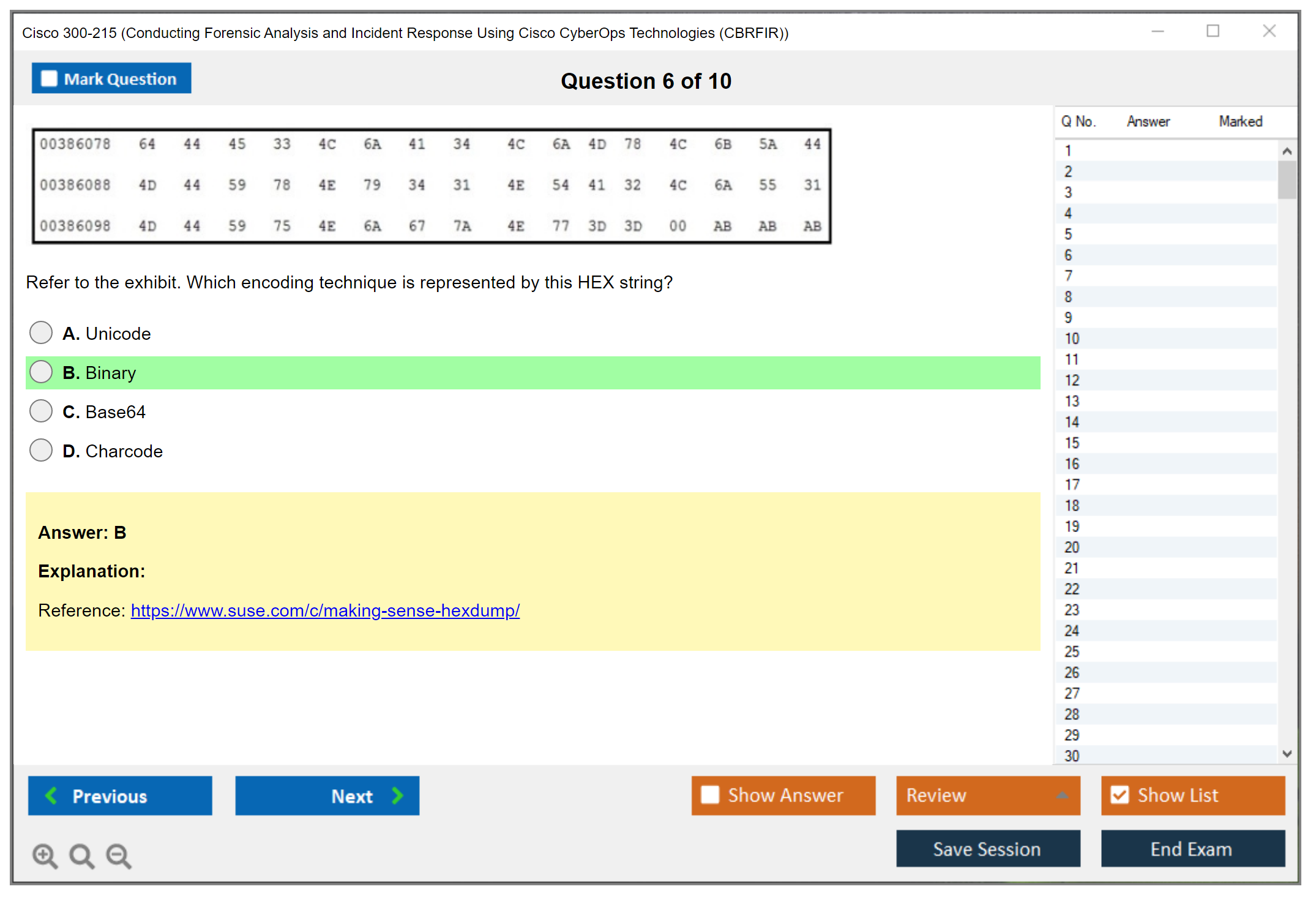
SIEM data correlation is foundational. You're pivoting from one indicator to related events across multiple log sources. Log aggregation brings data from firewalls, endpoints, web proxies, and authentication systems into one place. Normalization converts different log formats into a consistent schema so you can correlate things properly.
Threat intelligence integration means enriching your indicators with context from external feeds. Is this IP address a known C2 server? Does this file hash match known malware families? That sort of thing. Timeline analysis synthesizes data from multiple sources to build a complete picture of the attack sequence. You'll also distinguish false positives from true incidents because not every alert represents actual compromise.
Cisco SecureX provides threat response and investigation workflows that automate much of this correlation work. Knowing how to work through SecureX and use its orchestration capabilities is exam-relevant. The 350-201 CBRCOR core exam also covers some SecureX concepts, making it a natural companion certification.
Intrusion analysis and malware behavior
Domain 5 is the smallest at around 10% but still critical.
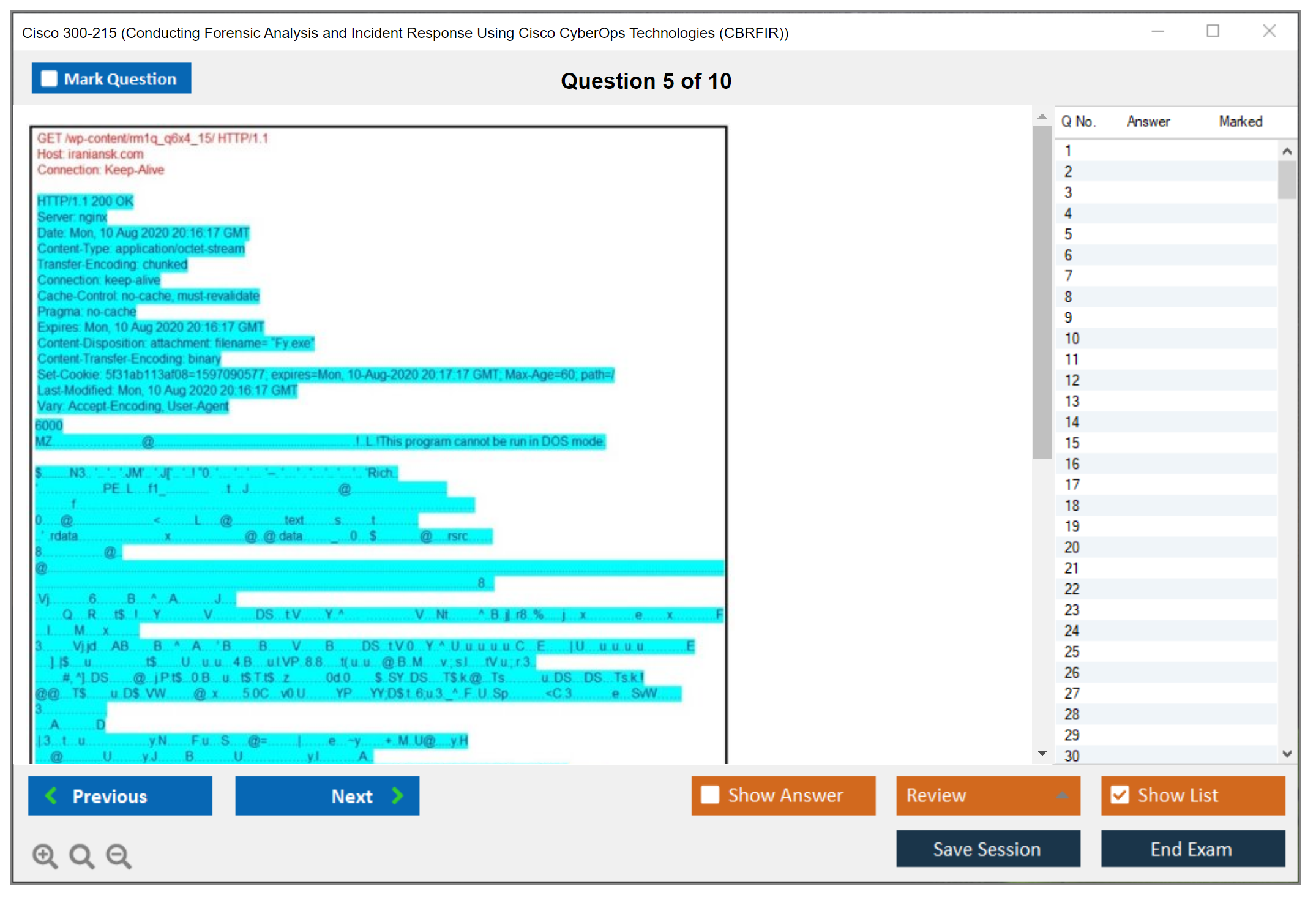
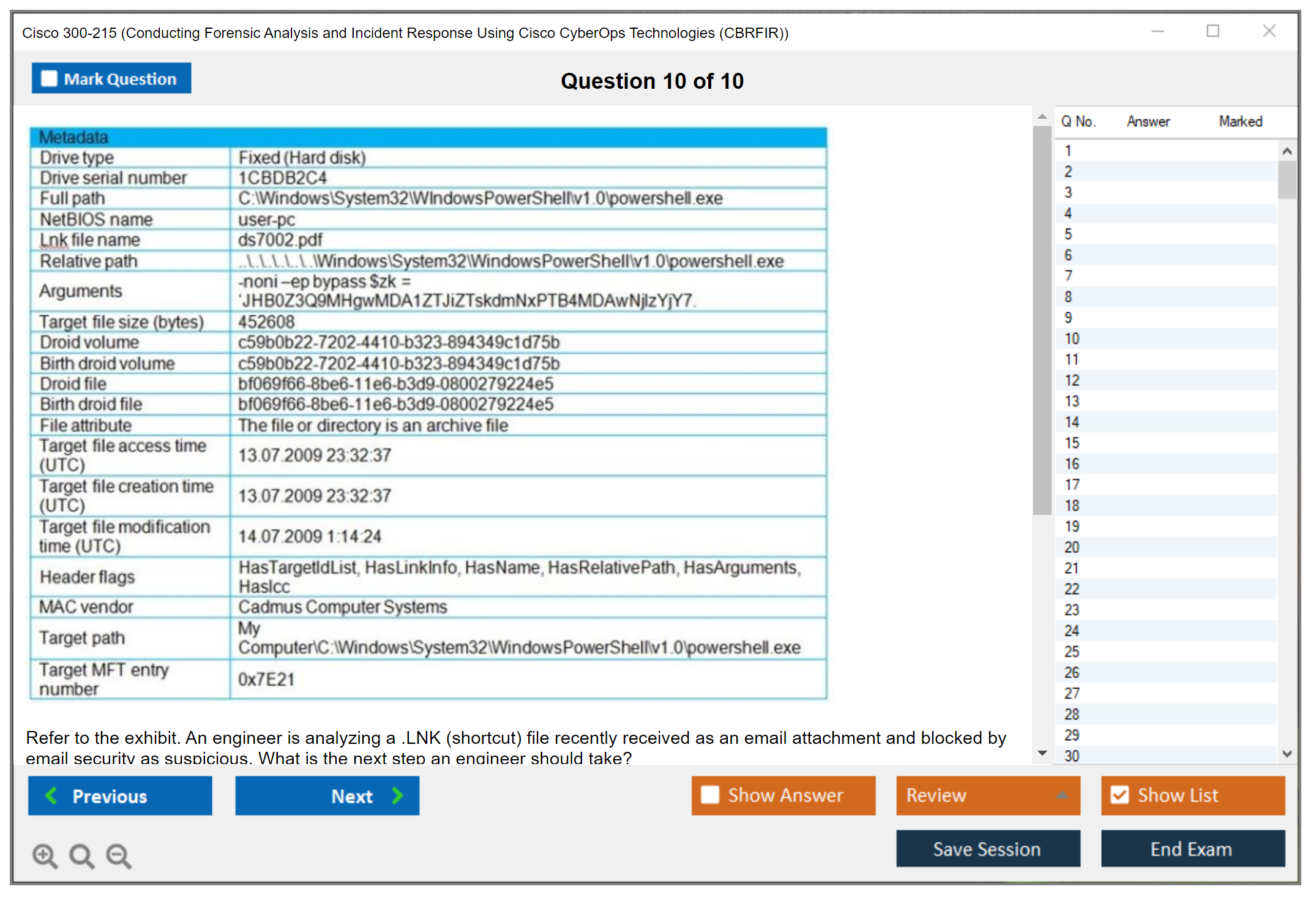
Static malware analysis includes examining strings in executables, parsing PE headers for suspicious imports, and checking file signatures. Dynamic analysis means detonating samples in sandboxes and observing behavior. What files get created? What registry keys change? What network connections occur?
Cisco Threat Grid (Secure Malware Analytics) is your go-to sandbox platform here. You submit samples, review behavioral reports, and extract IOCs from the analysis results. Behavioral indicators include persistence tricks (Registry Run keys, scheduled tasks), privilege escalation attempts, data staging in temporary directories before exfiltration.
Fileless malware and living-off-the-land techniques use legitimate system tools like PowerShell, WMI, or PsExec, making detection harder. Ransomware forensics involves identifying patient zero, tracking encryption spread, and supporting recovery decisions. Attribution indicators might point to specific threat actor groups based on TTPs and infrastructure patterns.
Using the blueprint as your study roadmap
Honestly, the blueprint should guide every study decision. If a domain's 30% of the exam, it should get 30% of your study time. Focus on the tools Cisco pushes: Secure Endpoint, Secure Network Analytics, Threat Grid, SecureX. They'll show up in scenario questions.
The 300-215 Practice Exam Questions Pack for $36.99 mirrors blueprint structure, so you can assess readiness by domain. When practice questions reveal weak areas, go back to that blueprint section and hit it harder with hands-on labs and documentation review.
Mapping objectives to real-world SOC and DFIR tasks
The exam scenarios mirror actual incident investigations you'd handle in a security operations center. A typical DFIR professional day involves triaging alerts, pulling endpoint forensics, analyzing network traffic, correlating events across tools, and documenting findings.
Enterprise environments differ from MSSP contexts in scale and tool access, but the methodology stays consistent. Regulatory compliance considerations like GDPR breach notification timelines, HIPAA evidence handling, PCI-DSS forensic investigation requirements influence how you conduct and document investigations.
Integration with SOC workflows means understanding how tier 1 analysts escalate to tier 2 investigators, and when DFIR specialists get pulled in for deep forensic work. Career progression often starts with foundational certs like 200-301 CCNA for networking basics, then moves through security operations fundamentals before specializing in forensics and incident response at the professional level.
The blueprint version matters because as Cisco releases new security products or updates existing platforms, exam objectives shift to reflect current technology. Check the effective date on your blueprint copy and compare it against what's currently published. You don't want to study deprecated content that won't appear on your actual exam.
Prerequisites and Recommended Experience for 300-215 CBRFIR
Are there formal prerequisites for 300-215?
The Cisco 300-215 CBRFIR exam is a concentration exam under the Cisco CyberOps Professional track, and the only hard gate you can't wiggle around is this: you must pass 350-201 CBRCOR first. That core exam's the mandatory requirement. Period. No CBRCOR, no CyberOps Professional, and you'll feel it in the CBRFIR blueprint domains because the concentration assumes you already speak "core SOC" without stopping to explain the basics.
No other Cisco cert's required beyond CBRCOR. Not CyberOps Associate, not CCNA, not any specialist badge. You can stack them if you want, but Cisco doesn't demand them as part of the 300-215 CBRFIR prerequisites. There's no formal work experience requirement either, and Cisco doesn't force you to complete a training class before you sit. That said, reality check here: CBRFIR's about incident response and digital forensics Cisco style, and if your only exposure is a weekend lab, you're probably going to find the 300-215 CBRFIR difficulty pretty spicy.
Age and education requirements? They get weird because they depend on your testing region and the policies of the delivery partner. Cisco's program rules plus Pearson VUE rules can vary, especially for minors or candidates who need accommodations, so you've gotta confirm on the official exam page and your local Pearson VUE site. Don't guess. Booking day isn't the time to learn you need a parent consent form.
If you're coming up through Cisco Networking Academy or a partner program, that's a valid option too. Not mandatory. But those ecosystems can get you discounted learning, structured labs, and access to instructors who've run forensic analysis workflows CyberOps style, not just read slides. Sometimes the instructor connections matter more than the courseware itself, especially when you're stuck on a weird artifact correlation problem at 2 AM.
What knowledge should you have before attempting CBRFIR
Look, CBRFIR isn't a "memorize terms" exam. It's closer to "here's messy evidence, now reason like an analyst" and that means your fundamentals have to be automatic so your brain's free for the investigative parts, especially across the CBRFIR blueprint domains where you pivot between telemetry, endpoint artifacts, and response steps.
Start with TCP/IP.
Strong comfort with routing basics, ports and protocols, DNS weirdness, TLS basics, NAT, and what normal traffic looks like versus compromised host behavior. Then operating system internals. Windows event logs and process trees, Linux auth logs, cron, systemd, file permissions, macOS artifacts and the general architecture. Not kernel dev level, but you should know where the bodies are buried on each OS and why attackers pick persistence methods that survive reboots.
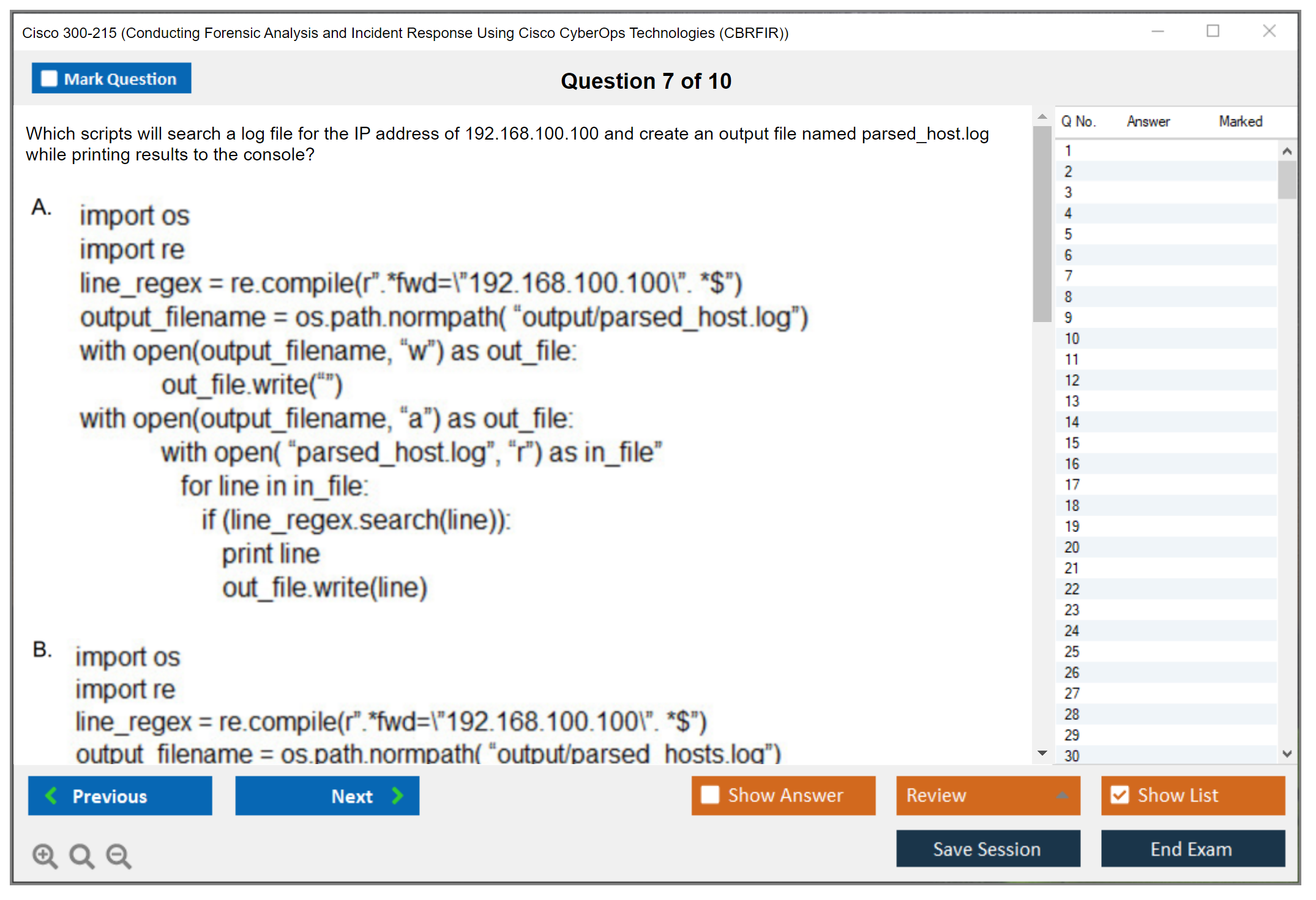
Scripting matters more than people admit. Basic Python for parsing, PowerShell for Windows triage, Bash for quick automation. You don't need to write a full toolchain, but you should be able to read scripts, tweak a regex, and automate repetitive checks because that's how you survive a real incident without losing hours to copy-paste. I mean, it's just how the job works.
You also want SOC processes and workflows down cold: ticketing, escalation, triage versus containment, evidence handling, and what "chain of custody" means when legal or HR gets involved. Add common attack vectors and threat actor tactics using MITRE ATT&CK, because mapping observed behavior to tactics is how you go from "random alert spam" to "this looks like credential access followed by lateral movement." Knowing SIEM platforms helps too, not because the exam's a SIEM product test, but because correlation, normalization, and searching across sources is the job.
Malware types and infection chains? Another must. You should understand how phishing leads to initial access, how droppers and loaders behave, how C2 traffic can hide, and what execution artifacts tend to show up on endpoints. The exam objectives won't reward vague vibes. They reward knowing what evidence you'd expect and where you'd confirm it.
How much hands-on experience do you really need
Cisco doesn't require years on the job. But if you want my opinion, minimum 1 to 2 years in security operations or incident response makes the content feel normal instead of terrifying. You need scar tissue. Real alerts. Real false positives. Real "why is this log missing" moments.
Experience investigating actual incidents matters more than building perfect lab scenarios. Labs are great for repetition and tool comfort, but real environments teach you constraints like incomplete telemetry, time pressure, stakeholders, and systems you're absolutely not allowed to reboot just because it would be convenient.
You should be familiar with at least one major forensic tool suite. Pick one. Get comfortable. The rest you can name-drop. Practical exposure to Cisco security products in production helps a lot, especially things in the SecureX and Secure Endpoint orbit, plus Threat Grid style malware analysis workflows. Log analysis across multiple platforms is non-negotiable, and yes that includes endpoints, network devices, DNS, proxy, identity, and cloud sources when you can get them.
Also worth doing: incident response exercises and tabletop scenarios. Not because they're fun, but because they teach you communication and decision points. Compliance and regulatory exposure helps too, even if it's just learning what gets documented, what gets preserved, and how timelines get written when an audit team's watching.
Helpful related certifications and why they matter
If you want extra prep structure, Cisco CyberOps Associate (200-201 CBROPS) is a solid foundation before you go professional-level. CompTIA Security+ is fine for baseline terminology and controls. CompTIA CySA+ fits the analyst mindset and can make the 300-215 CBRFIR exam objectives feel less foreign.
For deeper incident response methodology, GIAC GCIH is strong. For forensics depth, GIAC GCFA is the heavyweight, though expensive and intense. CISSP gives breadth and context, useful for policy and risk conversations, but it won't teach you hands-on DFIR by itself. The thing is, CISSP's more about governance than getting your hands dirty. ECIH can be an alternative if you want a structured IR overview without going full GIAC.
Training resources and checking for skills gaps
Official Cisco instructor-led training for CBRFIR's the cleanest mapping to the exam, and Cisco Digital Learning Library subscriptions can be a good deal if you're studying multiple Cisco tracks. Cisco Learning Network community threads and study groups help when you hit a weird topic and need practical explanation, not marketing copy.
For Cisco tooling? Vendor training on SecureX, Secure Endpoint, and Threat Grid is worth your time. Third-party providers like Pluralsight, CBT Nuggets, and INE can fill gaps, especially when you need a different teaching style. University programs in cybersecurity or digital forensics can help if you want structured fundamentals. Conferences like SANS, Black Hat, and RSA are great for workshops that feel like real casework.
Before you commit, do a skills gap assessment. Take the published exam topics, turn them into a self-assessment questionnaire, and be brutally honest about what you can explain and what you only recognize. Then run a practice exam baseline. Not to predict your 300-215 CBRFIR passing score because Cisco doesn't publish a fixed one that never changes, but to find weak areas fast. Same with 300-215 CBRFIR study materials and 300-215 CBRFIR practice tests: use them to diagnose, not to memorize.
Also, plan ahead for admin stuff. Confirm 300-215 CBRFIR cost in your region with taxes and fees, and keep an eye on 300-215 CBRFIR renewal options through Cisco security certification recertification rules, because you don't want to pass and then ignore CertMetrics until your clock runs out.
Conclusion
Getting ready to tackle the Cisco 300-215 CBRFIR exam
Let's be real here.
Passing the Cisco 300-215 CBRFIR exam isn't something you just walk into. This is a Cisco CyberOps Professional concentration exam that digs deep into incident response and digital forensics, and the 300-215 CBRFIR difficulty is legit if you're coming in without hands-on SOC experience. But here's the thing: it's absolutely doable if you approach it the right way.
You've already seen what the 300-215 CBRFIR cost runs (usually around $300 USD, though that varies by region). The 300-215 CBRFIR passing score? Hovers somewhere in that 750-850 range out of 1000.
The exam objectives cover everything from forensic analysis workflows CyberOps teams actually use to building IR playbooks that work under pressure. I've got mixed feelings about how Cisco structures some of these modules because the weighting feels uneven, but whatever. What matters now is how you prepare.
The 300-215 CBRFIR study materials space is crowded as hell. You've got Cisco's official training, documentation deep-dives, random YouTube walkthroughs, and a ton of blogs promising shortcuts that sound too good to be true. Because they usually are. Some of that stuff is gold. Some is outdated or just flat wrong.
The CBRFIR blueprint domains don't change often. But the tooling and best practices? Absolutely do. So you need current resources that reflect how real incident response teams operate today, not what worked three years ago when threat landscapes looked completely different. I remember when everyone swore by a particular SIEM setup that's basically irrelevant now.
And yeah, 300-215 CBRFIR practice tests matter more than people think. Not just for memorizing answers (that's useless) but for understanding question patterns and identifying gaps in your knowledge before exam day. You want practice exams that mirror the actual difficulty and cover all the objectives, especially the forensic evidence handling and containment strategy sections that trip people up.
Honestly?
Before you register through Pearson VUE, make sure you've actually worked through labs, analyzed packet captures, traced attack chains, and documented findings the way you would in a real investigation. The 300-215 CBRFIR prerequisites aren't formally strict but you absolutely need baseline security operations knowledge or you'll struggle hard. If you're planning your Cisco security certification recertification timeline, remember this exam counts toward continuing education once you pass.
For practice materials that actually prepare you for the real thing, check out the 300-215 Practice Exam Questions Pack. It's built around current exam objectives and gives you the kind of scenario-based questions you'll face, not just brain dumps that teach you nothing. Pair that with hands-on lab work and you're in solid shape.