Introduction to Mile2 Certification Exams
Okay, so cybersecurity certifications. If you've spent any time in this field, CEH and OSCP probably ring a bell. But Mile2? They're way less visible compared to those heavyweights, and honestly that's kinda their superpower. Mile2's been operating since the early 2000s (not exactly newcomers), but they've built this really interesting niche by emphasizing actual, hands-on security testing instead of just cramming theory into your brain.
Their approach differs significantly. CompTIA delivers foundational concepts, EC-Council owns the brand recognition game, and Offensive Security? They'll absolutely wreck you with exams so brutal you'll question your life choices. Mile2 occupies this middle ground. Certifications that demand real skill demonstration without, you know, completely pulverizing your mental health. Take their MK0-201 (Certified Penetration Testing Specialist) exam. You're not just bubbling in answers about port scanning techniques, you've gotta actually perform it.
Why these certifications actually matter right now
Here's what's happening in 2026: literally every organization thinks they need penetration testers. Ransomware keeps dominating news cycles. Compliance frameworks? Getting more demanding by the quarter. The hunger for people capable of ethically compromising systems has gone absolutely bonkers, and there's zero indication it'll cool down.
Mile2 certifications have grabbed serious momentum because they match what hiring managers actually want. When someone spots CPTS on your application, they're not wondering whether you memorized the OSI model. They know you've proven hands-on penetration testing abilities. The certifications align with NIST frameworks and industry benchmarks, which becomes key when organizations need compliance checkbox validation.
Entry-level professionals find Mile2 accessible without already being security wizards. Experienced practitioners? The certifications confirm specialized capabilities that directly translate to daily work. I mean, I've watched network admins use these to jump into offensive security positions, and it succeeds because the material immediately applies to real scenarios.
Who should care about Mile2 exams
Security analysts wanting red team transitions? Huge portion of Mile2's audience. You've got fundamentals down, defensive security makes sense, but now you're ready to adopt an attacker mindset. Mile2 builds that bridge without demanding five years of pentesting background just for exam eligibility.
Network administrators seeking specialization frequently gravitate here too. Infrastructure already makes sense to you. Mile2 shows you exploitation methods. Career changers entering cybersecurity appreciate the hands-on emphasis since it develops genuine skills beyond theoretical memorization. Students and fresh graduates use foundation-level Mile2 credentials for building credibility when work history doesn't exist yet.
Speaking of credentials, my cousin actually tried getting into cybersecurity through a bootcamp last year. Spent like twelve grand and six months on this program that barely touched practical skills. Total waste. He ended up grabbing a Mile2 cert instead for a fraction of the cost and got hired within three months. Sometimes the flashier path isn't the smarter one.
How they stack up against the competition
Real talk about comparisons. EC-Council's CEH costs significantly more and carries superior name recognition, but Mile2's practical orientation often delivers better preparation for actual pentesting responsibilities. That price gap isn't insignificant either. We're discussing hundreds saved with Mile2 while still obtaining industry-recognized validation.
CompTIA's Security+ covers broader territory and stays more foundational. PenTest+ goes deeper than Security+ but still doesn't achieve the specialized intensity you'll find with Mile2's penetration testing track. Want general security knowledge? Choose CompTIA. Want offensive security specialization specifically? Mile2 makes way more sense.
Offensive Security certifications like OSCP are punishingly difficult and massively respected, but they're also substantially harder and pricier. OSCP demands 24 straight hours of hands-on hacking under proctored conditions. Mile2's tough yet reachable. You can pass without hibernating in isolation for half a year. GIAC certifications provide incredible depth but the thing is pricing excludes tons of people. Mile2 hits this perfect balance of affordability and tangible value.
The certification ecosystem structure
Mile2 organizes certifications across tiers. Foundation-level credentials for absolute beginners just starting out. Intermediate certifications for working professionals wanting skill validation and expansion. Advanced certifications targeting specialized roles like digital forensics or complicated exploitation methodologies.
They mandate continuing education and recertification, which honestly benefits everyone. Technology moves ridiculously fast. A certification earned back in 2020 shouldn't hold identical weight in 2026 without demonstrating you've maintained currency with emerging techniques and toolsets.
What you actually get from earning these
Demonstrable competency proof matters enormously. Anybody can claim SQL injection knowledge or buffer overflow exploitation capabilities. Mile2 certification? That's verification. I've watched people use these credentials for salary negotiations. We're seeing 15-20% bumps in certain situations depending on your geographic market and experience depth.
Career mobility improves dramatically. You transform from "IT person with some security awareness" into "certified penetration testing professional." Doors open. The professional community access gets underestimated too. Connections to fellow practitioners, resource libraries, membership perks extending beyond just credential acquisition.
What this guide covers
We're diving deep into certification pathways and strategic progression through Mile2's ecosystem. You'll receive thorough coverage of popular exams, particularly the MK0-201 CPTS certification which has become their flagship penetration testing credential. Study strategies that really work, not just "consume the textbook and hammer practice questions." Actual career impact breakdowns with salary figures. How these certifications convert to real job functions and opportunities.
This isn't promotional nonsense. We're providing practical guidance for making smart decisions about your certification path.
Mile2 Certification Paths and Levels
How Mile2 lines things up
Mile2's built like a ladder. You start low, prove you've got fundamentals, then stack specialties on top. Pretty straightforward.
The tiered approach? It's basically skills validation with guardrails, and honestly, I mean that in a good way. It stops people from sprinting headfirst into advanced exploitation certs when they don't even know how DNS works or, like, why patch cycles exist in the first place. You'll see logical progression from awareness and vulnerability discovery, moving into hands-on offensive and defensive work, and then branching into expert tracks like cloud architecture and auditing where you're expected to think in systems, not just memorize tools. Specialization tracks exist inside the ecosystem too, so you can lean into pentesting, defense, cloud, audit, or forensics depending on what you actually do at work. Or want to do.
Prereqs aren't always "hard" requirements. But recommended experience levels? Those matter. Foundation's fine for newcomers and adjacent roles. Intermediate assumes you can live in a terminal and read scan results without guessing wildly. Advanced expects you to plan engagements, write findings that'll survive a grumpy security manager's redline session, and operate with way less hand-holding.
The entry certs that get you moving
Foundation Level's where you pick up credibility fast. Also where you avoid overwhelm.
C)SA, the Certified Security Awareness Practitioner, is the "make humans less risky" cert. Target audience? Non-technical professionals, managers, help desk folks, HR, compliance teams, and honestly anyone who keeps getting pulled into security training conversations and wants to stop sounding completely lost. Exam objectives tend to circle security fundamentals and best practices: password hygiene, phishing, social engineering basics, data handling, physical security, and what policies actually exist for. It's an ideal starting point if you're trying to pivot into security from operations or admin work and you need a clean on-ramp that doesn't require scripting skills.
C)VA (Certified Vulnerability Assessor) is where things start feeling technical without going full hacker-movie. Focuses on identifying and analyzing vulnerabilities, reading scan outputs, prioritizing remediation, understanding exposure. Important distinction here: vulnerability assessment isn't penetration testing. VA is "find and report, validate where reasonable." Pentesting's "prove impact with exploitation in scope." Career-wise, C)VA lines up well with compliance and risk management roles, SOC support, and internal security teams that need someone who can run assessments and speak remediation without stumbling.
The middle tier where you pick a lane
Intermediate Level's where Mile2 starts separating "I know terms" from "I can actually do the work."
MK0-201, the Certified Penetration Testing Specialist (CPTS), is the premier intermediate option for offensive security. Covers penetration testing methodologies end to end, and it's a bridge between foundational knowledge and the more advanced exploitation-heavy certs. If you're specifically researching the MK0-201 (Certified Penetration Testing Specialist (CPTS)), remember it's not meant to be your first security exam unless you already have hands-on experience and you're comfortable troubleshooting on the fly when labs go sideways.
C)PTE, Certified Penetration Testing Engineer, pushes into more advanced pentesting techniques and enterprise-level assessment thinking. Look, C)PTE's where scoping, reporting quality, and repeatable methodology start to matter as much as popping a box does. The thing is, recommended prep path usually means: have C)VA-level scanning and analysis down solid, do MK0-201-level methodology work, then add deeper exploitation and real engagement practice before attempting this.
C)NDA (Certified Network Defense Architect) is the defensive complement. It's for people who want balanced security skill sets, not just offense. You'll deal with network security architecture, segmentation, monitoring strategy, and defense approaches that actually hold up in production environments where everything's on fire half the time.
The expert tier where you're expected to lead
Advanced Level's where you're proving you can operate like a senior. Not just pass a test.
C)PEH, Certified Professional Ethical Hacker, is positioned as expert-level ethical hacking. Expect advanced exploitation techniques and more custom tool development mindset. Industry recognition varies by market, but the career advancement angle's real if your current job needs a "senior offensive" signal and you can back it up with projects and writeups, not just the paper.
C)CSA, Certified Cloud Security Architect, is the cloud specialization everyone's suddenly asking about. Multi-cloud coverage shows up across AWS, Azure, and GCP. The demand's obvious because so many orgs are half-migrated and confused about shared responsibility models and identity federation nightmares. Cloud penetration testing skills are growing in value, but the cert's more than just "scan cloud stuff." Architecture decisions, identity, logging, and understanding shared responsibility are the core, and frankly, that's where most breaches actually happen anyway, not some zero-day exploit. I spent three months last year helping a company figure out why their S3 buckets kept leaking data, and it was never the tech that was broken. It was always the humans configuring it wrong or the policies nobody bothered reading.
C)ISSA, Certified Information Systems Security Auditor, is the audit and compliance heavy hitter. It fits with regulatory frameworks like PCI-DSS, HIPAA, and SOX, and it maps nicely to security auditing, GRC, and internal controls roles that pay well but require patience with spreadsheets.
Specialty options that don't fit neatly in tiers
Specialized tracks exist outside the "one ladder" idea, which is honestly refreshing. Digital forensics and incident response certifications are there if you like timelines, evidence handling, and messy reality where nothing's documented. Web application security specializations matter if you live in Burp and threat models. Mobile security and IoT pentesting tracks are also a thing, but they're niche and often employer-driven rather than something you pursue independently.
The Mile2 CPTS certification path, specifically
If you're eyeing the MK0-201 CPTS exam, don't treat it like a trivia quiz you can cram for. Recommended prerequisites are boring but real: foundational networking and security knowledge (TCP/IP, DNS, HTTP/S, common ports, auth basics), basic Linux and Windows administration skills (users, services, logs, permissions), and familiarity with common tools and frameworks like Nmap, Wireshark, Metasploit concepts, and basic OWASP thinking. You should also understand the MK0-201 exam objectives well enough to map each topic to a lab you can actually do, because reading-only prep's how people fail and then blame the vendor on Reddit.
After CPTS, the next logical steps are usually C)PTE for deeper enterprise pentesting or C)PEH if you want the "expert offensive" flag on your resume. Complementary certs from other providers can round out your penetration tester career roadmap too, and yes, CPTS vs CEH vs PenTest+ comparisons come up constantly because hiring managers recognize different brands in different regions. Sometimes annoyingly so. Build a portfolio alongside the Mile2 penetration testing certification, because employers still want proof beyond "I passed a multiple-choice exam."
Picking the right cert without wasting money
Do a self-assessment first. Be brutally honest. If you can't explain the difference between a vulnerability and an exploit without Googling, start at C)SA or C)VA.
Align the cert to your job role requirements, not your ego or what sounds coolest. Market value depends on region, employer, and what else you bring to the table, so Mile2 CPTS career impact's strongest when it matches your day-to-day work. Mile2 CPTS salary outcomes usually follow experience, not the paper alone. I've seen people with zero certs making more than cert-stacked juniors because they ship results. Also consider time and financial investment, plus your own MK0-201 exam difficulty ranking based on hands-on comfort, because "hard" is often just "I didn't lab it enough."
Keeping it current after you pass
Most cert paths don't end at pass day, which catches people off guard. Recertification timelines and continuing education matter, and Mile2 tracks CPE credits depending on the credential.
Staying current's the whole game in security. Threats change, tools change, and your muscle memory fades fast if you stop practicing. Mile2 resources, labs, and your own habit of reading advisories and doing hands-on work are what keep Mile2 Certification Exams from becoming a one-time checkbox gathering dust, and that's also the real answer to how to pass MK0-201 long-term: keep doing the work, even when nobody's grading you or watching over your shoulder.
Popular Mile2 Exams: Deep Dive
What you're actually getting with CPTS
The Mile2 CPTS (MK0-201) certification? It's one of those practical pentesting certs that doesn't waste your time with endless theory. Built for security professionals who need to prove they can actually break into systems, not just talk about it. Sure, there's definitely some theory involved (you can't escape that entirely), but the focus is on hands-on skills that translate directly to real-world pentesting work. Makes all the difference when you're job hunting.
Industry acceptance has grown quite a bit heading into 2026. You'll find CPTS listed as a preferred or accepted qualification in more job postings now, especially from companies that want penetration testers with practical exploitation skills rather than just vulnerability scanning experience. It validates real-world competencies in ways that some of the more theory-heavy certifications don't quite manage.
Breaking down the exam format
The MK0-201 exam contains 60 questions. You need to complete in 90 minutes. That's not a ton of time when you consider the scenario-based questions that require actual thinking rather than simple recall. The thing is, you're constantly watching that clock tick down while analyzing complex attack vectors.
Question types include multiple-choice, but honestly the scenario-based and performance-based questions are where people struggle most. You're not just picking answers from a list. You're analyzing attack scenarios and determining proper exploitation techniques while mentally juggling a dozen variables. Passing score sits at 70%, which sounds reasonable until you're staring at a complex web application attack scenario with the clock ticking and your palms getting sweaty.
You can take it online with proctoring or head to a testing center. Both have pros and cons if I'm being honest. The online option uses standard remote proctoring software, which means stable internet connection is non-negotiable unless you enjoy the panic of mid-exam disconnections. Testing center option removes that technical risk if your home setup isn't reliable.
Skills they're actually testing
Information gathering and reconnaissance techniques form the foundation here. Network scanning and enumeration methodologies build on that, then you move into vulnerability identification and analysis, which gets progressively more nuanced as you dig deeper into exploitation techniques section covering common security weaknesses you'll encounter in real pentests.
Post-exploitation activities and privilege escalation get deep. Really deep. This is where you demonstrate understanding of what happens after initial compromise. Not just breaking in, but what you do once you're inside the network. Social engineering tactics appear throughout because, let's face it, human-based attacks remain incredibly effective no matter how much we invest in technical controls.
Web application penetration testing fundamentals cover OWASP Top 10 and beyond. Wireless network security assessment tests your ability to attack WiFi networks and wireless infrastructure in ways that'd make your neighbors nervous. Had a buddy who practiced wireless attacks from his apartment and accidentally knocked out half his building's internet. Learned real quick about proper lab isolation and why you don't test certain techniques in multi-tenant buildings.
Report writing matters more than people expect, honestly. Professional communication of findings separates actual pentesters from script kiddies who can't articulate what they found or why it matters to business stakeholders. Ethical and legal considerations remind everyone that we're the good guys here. Wait, I should clarify that proper authorization and scope definition separate legitimate security testing from criminal hacking.
Where CPTS fits in your certification path
This sits at intermediate level. You don't absolutely need prerequisites, but recommended foundational knowledge includes networking basics and Linux command line comfort. Without those, you're gonna have a rough time working through exploitation scenarios. Natural progression leads to advanced Mile2 credentials like C)PTE or specialized tracks depending on your career direction and whether you lean more toward web apps, infrastructure, or cloud environments.
It complements other certifications well, which I think is its strongest selling point. Someone with CompTIA Security+ or CEH can add CPTS for hands-on credibility that demonstrates they've moved beyond theoretical understanding into practical application.
Who should actually take this thing
Security analysts seeking offensive security skills are prime candidates here. IT professionals transitioning to penetration testing roles find it accessible enough to break into the field without being completely overwhelming or requiring years of prior exploitation experience. Network administrators expanding security expertise appreciate the practical approach that builds on existing infrastructure knowledge they've already developed troubleshooting production systems.
Career changers entering cybersecurity field use it as proof they can do the work, not just study it. Students preparing for penetration testing careers benefit from structured objectives that map to actual job requirements instead of abstract academic concepts that don't translate to employer needs.
How hard is this really
Not gonna lie here. Difficulty ranking compared to other pentest certifications is tricky because everyone's background differs wildly based on whether you came up through networking, development, or pure security tracks. Compared to EC-Council CEH, the CPTS goes deeper on exploitation techniques but covers slightly less breadth overall. You're getting more focused technical depth rather than mile-wide, inch-deep coverage.
Complexity comparison with CompTIA PenTest+ shows CPTS requires more hands-on technical skills while PenTest+ emphasizes methodology and process. Both valuable, just different approaches to validating competency. Technical depth versus Offensive Security OSCP? Look, OSCP is still the gold standard for difficulty and industry respect. CPTS doesn't require 24 hours of practical exploitation in an exam environment, making it more accessible for people who can't take days off work or handle that intensity level.
Hands-on requirements compared to eLearnSecurity certifications put it somewhere in the middle tier. Overall difficulty rating sits at moderate to moderately-difficult on industry scale, assuming you've got foundational knowledge already established.
What trips people up
Technical depth catches people. Specifically, exploitation techniques trip up folks who've only done vulnerability scanning without ever actually weaponizing findings into working exploits.
Breadth of topics covered in single examination means you can't just focus on web apps and ignore wireless. Honestly frustrates specialists who want to focus on their preferred attack surface.
Time management during exam completion becomes critical when scenario questions eat minutes fast. I mean, you're sitting there analyzing a multi-stage attack chain while the timer keeps counting down relentlessly. Practical application versus theoretical knowledge creates problems for people who memorized without lab practice, then freeze when faced with actual exploitation decisions.
Keeping current with evolving attack methodologies matters because pentesting techniques change constantly as defenses improve and new vulnerabilities emerge.
Actually passing this exam
Recommended study timeline runs 8-12 weeks. Balance between theoretical study and hands-on practice should lean heavily toward labs. Maybe 70% hands-on, 30% reading if you want my opinion. Focus areas based on exam objective weighting means spend extra time on exploitation and post-exploitation since those carry significant weight in scoring calculations.
Test-taking strategies for scenario-based questions include reading all answer options before selecting and eliminating obviously wrong answers first. Sounds basic but gets forgotten under pressure. Managing exam anxiety and time pressure means practice exams under timed conditions before the real thing. Simulate that stress in your home lab so it's familiar when stakes are high.
Other Mile2 certifications worth knowing
The C)PTE (Certified Penetration Testing Engineer) goes beyond CPTS. It dives into advanced penetration testing methodologies and more complex exploitation scenarios that require chaining multiple vulnerabilities together for initial access or privilege escalation. Target audience includes experienced pentesters seeking advanced credentials after they've already proven foundational competency.
C)PEH (Certified Professional Ethical Hacker) represents expert-level credential. Full exploitation and attack techniques spanning multiple domains and attack surfaces. Industry recognition has grown as Mile2's reputation improves and more employers recognize their practical focus over purely theoretical certifications.
C)NDA focuses defensive security. Network architecture security principles, valuable for balanced security professionals who want both offensive and defensive skills rather than pure red team or blue team specialization. Honestly, that versatility helps with career longevity as priorities shift.
C)CSA addresses cloud security specialization, increasingly relevant in 2026 as more infrastructure moves to AWS, Azure, and GCP whether security teams are ready or not. Growing market demand for cloud penetration testers makes this certification practical for career growth since traditional network pentesting skills don't directly translate to cloud environments.
C)VA is entry-level credential. Distinct from penetration testing certifications but useful for compliance and risk management applications where full exploitation isn't authorized or necessary.
C)IHE covers incident response and forensics focus. The thing is, these are complementary skills for penetration testers who want to understand the defensive side and how their attack techniques appear from blue team perspective. Career opportunities in SOC and IR teams open up with this credential beyond pure offensive security roles.
Study Resources for Mile2 Certification Exams
start with the official stuff first
When people ask me about Mile2 Certification Exams, I always say the same thing: start with Mile2's own material, then branch out. Vendor exams tend to reward vendor phrasing, vendor scope, and vendor priorities. Annoying, but real.
Mile2 official courseware and curriculum is usually the cleanest map of what the test expects, especially when you're aligning your notes to MK0-201 exam objectives. The instructor-led training programs and boot camps can be great if you need a deadline and someone to keep you honest, but honestly, they're also where your budget goes to die if you don't already have the time blocked off. Official practice exams and assessment tools are the part I'd pay attention to most because they show you how Mile2 asks questions, not how a random author thinks pentesting "should" be asked.
Also check what's inside the Mile2 learning management system resources. Sometimes there are extra quizzes, PDFs, and lab prompts that never show up in the public course description. Some gaps exist. Some sections feel thin. Overall though, the quality and depth of official materials is usually enough to pass if you actually do the labs and don't just read slides like bedtime stories.
mk0-201 resources that actually map to the test
For MK0-201 CPTS exam prep, you want resources that match the "Certified Penetration Testing Specialist (CPTS)" vibe: practical workflow, common tools, and a report-minded approach, not just exploit trivia.
The best starting point is Mile2's official training and any recommended books they list for CPTS. That's the closest thing you'll get to "how to pass MK0-201" without guessing what the exam writer was thinking at 2 a.m. Third-party study guides and reference materials can help, but look, some are basically SEO fluff with screenshots. Pick references that teach fundamentals you can apply during scenario questions, stuff you can cross-check against the MK0-201 exam objectives.
Video training courses can fill gaps fast. Yeah, Udemy, Pluralsight, and Cybrary all have options, but the quality swings wildly based on the instructor, the upload date, and whether they treat pentesting like a checklist instead of a method. Online tutorials and blog resources are great for quick "how do I do X in Kali" moments.
Community forums and study groups? That's where you go when you're stuck on a tool output, a scan result, or (the thing is) a weird privilege escalation rabbit hole that your courseware doesn't explain. I spent two hours once trying to figure out why my reverse shell kept dying. Turns out my VM's network adapter was set to NAT instead of bridged. Forums saved me.
If you're building out the bigger Mile2 CPTS certification path, start tracking what you learn as reusable skills. That's where the Mile2 CPTS career impact comes from, not the badge.
labs and practice that won't waste your time
Reading about exploitation is cute. Doing it is different.
For hands-on prep, virtual lab environments for penetration testing practice are non-negotiable. Hack The Box and TryHackMe integration is basically the default these days, and I mean that in a good way. They force repetition and pattern recognition, especially around recon, enumeration, and "why did my exploit fail" troubleshooting. VulnHub and practice vulnerable machines are still awesome when you want downloadable boxes you can run offline, break, reset, then break again.
Add Mile2 CPTS practice questions and mock exams once you've got momentum. Practice questions are where you learn the exam's pacing and where you discover your blind spots fast. Building home lab environments for hands-on learning is also worth it if you're serious: one Kali VM, one Windows VM, one Linux VM, plus a vulnerable target VM, and suddenly you can rehearse the same steps until they're muscle memory.
And yes, take notes. Short notes. Real notes.
books worth your attention
Recommended books and reading materials matter most when they teach method, not magic.
Penetration testing methodology books help you think like a tester. Network security and exploitation references help when you keep seeing the same services and don't really understand what "normal" looks like. Web application security resources are huge because web issues show up everywhere, even when the exam isn't "a web exam." Scripting and automation guides for security are the quiet multiplier. Being able to throw together a quick Python or Bash helper can save you hours in a lab.
Industry-standard references like PTES and OWASP are also solid. Not because Mile2 is copying them word for word, but because they anchor your process, and process is what keeps you from spiraling when a scan gives you ten leads and only one is real.
training platforms, money, and what to pick
Mile2 official e-learning platform is the obvious paid option. It's the closest match to Mile2 wording. Third-party training providers vary a lot, so sample lessons first if you can.
Self-paced versus instructor-led options comes down to discipline: if you won't study without structure, pay for structure, but if you can grind solo, save the cash for labs and exam attempts.
Cost comparison is messy. Free versus paid resource evaluation is basically this: pay for alignment and accountability, use free stuff for enrichment and troubleshooting. Budget-conscious strategy? Official outline plus labs plus selective videos. That's it.
hands-on environments and tool setup
Setting up Kali Linux for penetration testing practice is table stakes.
Do it in a VM. Snapshot it. Break it. Restore it. Vulnerable-by-design applications and networks are where you learn safely, and cloud-based lab environments are great when your laptop is tired. CTF competitions help with speed and creativity, but don't confuse CTF tricks with real engagement flow.
Real-world practice scenarios and simulations matter because Mile2 penetration testing certification exams tend to reward the boring steps done well: recon, validate, document, repeat.
study plans that match your timeline
2-week intensive plan for experienced pros: daily blocks, heavy on practice tests and labs, light on reading. Focus areas are recon and enumeration, common services, web basics, reporting mindset. Prereqs assumed: networking, Linux, Windows basics, and you've touched tools before.
4-week balanced plan for intermediate learners: weekly topic breakdown, two lab days per week minimum, one checkpoint at the end of each week with a timed quiz, and one full mock exam at the end. Mix theory with hands-on every day, even if it's just 30 minutes of running scans and interpreting results.
8-week plan for beginners: slow ramp, fundamentals first, then tools, then exploitation patterns, then mock exams. Weekly milestones. Time management matters here. If you skip labs early, you pay for it later with panic.
community support and staying current
Mile2 certification community forums exist.
Reddit communities for Mile2 and pentesting exist too, and Discord study groups are where you'll get fast feedback when you're stuck. LinkedIn groups are more career-focused, which helps when you're thinking about penetration tester career roadmap, Mile2 CPTS salary, and how to explain your skills after you pass MK0-201 (Certified Penetration Testing Specialist (CPTS)).
Also, watch for Mile2 exam updates. Content revisions happen. Security changes weekly. Ongoing learning is part of the deal, not extra credit.
practice exam strategy that works
Use practice tests to find gaps, not to farm scores.
Simulate exam conditions sometimes, review every wrong answer, and write down why you missed it. Schedule the real exam when your practice scores are stable, not when you get one lucky high run. If you're wondering about MK0-201 exam difficulty ranking or CPTS vs CEH vs PenTest+, the truth is your difficulty is mostly your lab time, not the logo on the cert.
Career Impact of Mile2 Certifications
Okay, real talk. The Mile2 CPTS career impact isn't exactly headline news in infosec, but here's the thing. The MK0-201 (Certified Penetration Testing Specialist (CPTS)) credential actually opens doors you wouldn't necessarily expect, especially if you're combining it with genuine lab experience and can hold your own when technical conversations happen during interviews, not just recite memorized definitions.
What roles actually want this certification
Penetration Tester positions? Obviously. Companies needing someone to break into their systems (legally, duh) want proof you're not just guessing, and CPTS delivers that. Ethical Hacker roles overlap but sometimes lean toward ongoing red team operations instead of those one-and-done assessments. Wait, I should clarify what I mean there.
Security Analyst positions focusing on offensive work are where it gets kinda interesting because honestly these roles pay decently and you're not grinding through identical testing routines every single day. Variety matters. Vulnerability Assessment Specialist roles show up at larger organizations needing dedicated folks who run scans and actually comprehend what all that scanner output means. Not just regurgitate auto-generated reports. Security Consultant opportunities exist, but they'll want client-facing skills too, which the cert definitely doesn't teach. Red Team member positions are tougher to snag straight from certification. Most teams want battle-tested professionals who've done actual engagements. CPTS at least gets your resume past that initial filter though.
The practical skills companies actually care about
After passing MK0-201, employers look for hands-on penetration testing ability. Can you actually follow structured approaches or do you just randomly throw exploits at targets until something sticks? I mean, process matters way more than people realize. Vulnerability identification and exploitation capabilities are baseline expectations, but you'd be really surprised how many cert holders can find vulnerabilities but absolutely struggle with the exploitation phase.
Professional reporting skills? Critical. Nobody wants pentest reports reading like CTF writeups. Clients need actionable remediation guidance. Understanding ethical and legal compliance keeps you outta jail, which seems important. Tool proficiency and technical adaptability matter because the security space evolves faster than certification bodies update exams, so you've gotta prove you can learn new tools without constant handholding.
Where the job market actually stands
Industry trends favoring hands-on security certifications work in Mile2's favor since CPTS focuses on doing rather than memorizing. But not gonna lie, where you live makes a huge difference. Some markets barely know it exists while others have consulting firms specifically listing it in postings.
How do employers rank Mile2 versus competing certifications? Usually below OSCP and maybe tied with CEH depending on who's hiring. HR teams recognize CEH more because EC-Council's marketing is everywhere. Technical hiring managers sometimes prefer Mile2 'cause it's more hands-on than CEH's multiple-choice format. Job posting analysis requiring Mile2 credentials shows it appearing most frequently in government contractor positions and defense industry roles, way less in startup environments or big tech.
Growth projections for penetration testing roles through 2026 look solid regardless of which cert you're holding. The field's expanding. Companies need people who can actually test their security, not just theorize about it. Actually, I've noticed more mid-sized firms spinning up internal red teams lately instead of just contracting everything out, which changes the hiring space a bit.
Moving up the ladder
Entry-level to mid-level progression with CPTS typically takes 2-3 years if you're actively working in security. You start as junior pentester or security analyst, build your engagement portfolio, then transition into full pentester roles. Senior penetration tester and lead security positions open up once you've got 5+ years and can demonstrate you've led assessments end-to-end, handling client communications and everything. Management positions in security operations sometimes want pentest backgrounds because you understand the attacker mindset, which really helps when building defenses.
Consulting and independent contractor opportunities are where the money gets interesting. But you need reputation first. Nobody's hiring a fresh CPTS as independent consultant. After you've got foundational certification, specialization paths include wireless security, web app pentesting, cloud security assessments, or IoT/embedded systems testing.
Building your certification stack
Next-step certifications after CPTS for career growth should probably include OSCP if you want credibility in the pentest community. I'm serious, OSCP carries weight that Mile2 just doesn't match yet, though that's slowly changing in some markets. Complementary credentials from other providers might include Security+ for DoD jobs, CEH if your employer's paying, or CySA+ for defensive security knowledge.
Should you specialize or stay general? Depends entirely on your career goals. Early career? Go broad. Mid career, pick a lane and own it. Vendor-specific certifications from AWS, Microsoft, or Cisco security programs help if you're regularly testing those environments. Advanced offensive security certifications like OSCP or OSCE are where you go when you're ready to prove you can pop boxes without someone walking you through every single step.
Where Mile2 actually gets respect
Financial services and banking security requirements sometimes specifically list Mile2 because of regulatory compliance needs. Healthcare and medical device security teams need pentesters understanding HIPAA implications. Government and defense contractor positions frequently list Mile2 certifications in job postings, probably because of existing contracts or approved training lists.
Technology companies? Sometimes. Software development firms hiring security engineers occasionally want offensive security backgrounds. Consulting firms and managed security service providers need people who can bill hours on client engagements, and CPTS proves baseline competency even if it's not the most prestigious cert on the market.
Mile2 Certification Salary Insights
what the CPTS pay picture looks like in 2026
When people ask about Mile2 Certification Exams, they usually want the same thing. Money. Specifically, what the MK0-201 (Certified Penetration Testing Specialist (CPTS)) does to your salary once you can credibly say "yes, I can test systems and write it up like a professional" and not just run tools.
For 2026, I'd set realistic Mile2 CPTS salary expectations like this. Entry-level pentest or junior offensive roles often land around $70k to $95k in the US if you've already got some hands-on labs, basic scripting, and you can speak to the MK0-201 exam objectives without sounding like you memorized a PDF the night before. Mid-level security pros who actually ship work (meaning scoping, executing, reporting, and retesting) tend to sit around $100k to $135k. Senior penetration tester and lead roles go $140k to $185k, and yeah, some people clear $200k+ when they're in high-cost cities, consulting, or they own client relationships.
Quick reality check. CPTS isn't magic. It's a signal.
entry, mid, senior: compensation by career stage
Entry-level (0 to 2 years) is where CPTS can help you get past the "no pentest experience" wall, honestly. A junior role with CPTS commonly pays $70k to $95k, but I mean the spread's wide because "entry-level" could mean a former help desk tech with home labs, or a security intern who already wrote internal tooling. Some teams'll title you "security analyst" and still have you do vuln validation and light testing, and that can come in lower, like $65k to $85k, while still being a decent stepping stone.
Mid-level (3 to 5 years) is where the money starts acting normal, you know? You're expected to run engagements with less hand-holding, communicate with engineering without making enemies, and produce reports that don't read like scanner output. Benchmarks I see people target are $100k to $135k for in-house roles, higher if you're billable in consulting. Look, the jump from junior to mid's less about the cert and more about whether your work product actually reduces risk, because leadership pays for outcomes, not for your tool list.
Senior-level (6+ years) earning potential's where titles and client trust matter. Senior testers and leads often hit $140k to $185k, and if you're a lead who mentors, handles scoping, and can defend findings in tense meetings, you can push past that. Fragments. Politics. Documentation. I once watched a lead pentester spend 40 minutes explaining why a "medium" finding was actually critical to a CTO who kept insisting it was theoretical. She got the retest budget approved. That's the job at this level.
why your location changes everything
Geographic location's still the biggest salary factor affecting Mile2 certified professionals. The thing is, high cost-of-living metros pay more, but you also burn more. United States regional salary variations are predictable: Bay Area and NYC trend high, the Midwest tends to trend lower, and DC-area roles can spike because of government and defense contractor demand.
International market compensation differences? Even more dramatic. A US-based CPTS holder might see six figures as normal for mid-level pentest work, while comparable roles in parts of Europe, LATAM, or South Asia may price differently due to local labor markets and benefits structures, even when the skill's the same. That's not "fair." It's how budgets work.
Remote work complicates it. Some companies pay "national" bands now, others adjust based on your ZIP code, and a few try to split the difference with a base plus stipend approach. Honestly, remote can raise your ceiling if you're in a low-cost area applying to high-paying companies, but it can also cap you if the employer insists on cost-of-living adjustments downward.
experience, titles, and what you actually do all day
Years in cybersecurity matter. But the kind of years matters more. If your first two years were ticket triage, your CPTS might help you pivot, yet you're still building offensive credibility. If your first two years were vuln management plus occasional internal testing, you can pitch yourself as closer to a true junior pentester.
Job title and role responsibilities create huge differences, I mean really huge. Penetration Tester versus Security Analyst compensation often comes down to whether you're expected to perform adversary-style testing and produce executive-ready reporting, or whether you're monitoring, tuning detections, and responding to incidents. Both are hard. They pay differently.
Consultant versus full-time employee's another split. Consulting roles can pay more, especially when you're billable and you can travel, but you'll feel it in workload and utilization pressure. Sometimes in unpredictable schedules that'll wreck your weekends. Management roles and leadership premium are real too, but you earn it by owning delivery, coaching others, and dealing with risk conversations that're messy and non-technical.
industry and company size: the quiet multiplier
Enterprise versus small business compensation's usually higher at enterprise, but small shops can give you wider exposure fast, which (look, that's valuable when you're still figuring out what you actually like doing). Financial services and healthcare often pay a premium because compliance, third-party risk, and audit pressure create consistent demand for testing and remediation evidence, and they'll spend to avoid bad headlines.
Government and defense contractor pay scales can be strong, especially with clearances, but they may come with tighter rules, slower tooling changes, and more paperwork than you'd expect. Startup versus established company differences are real: startups might offer higher upside or equity, but they can also underpay cash while asking for "do everything" security generalists.
CPTS ROI: where the cert actually pays off
Salary increase percentages after earning CPTS are usually modest if you stay in the same role. Think 5% to 12% when it's tied to a formal skills matrix, or when it helps you justify a role change internally. The bigger jump happens when CPTS helps you switch to a pentest track, because the title change moves the band.
Time to recoup certification investment costs can be quick. Real quick. If you spend a few hundred to a couple thousand on training and exam fees, a single raise or a better offer can pay it back in months, not years, assuming you can interview well and show skills beyond the certificate. This's where MK0-201 study resources and hands-on labs matter more than people admit, because the cert gets you the interview and your portfolio gets you the offer.
Certified versus non-certified salary ranges are messy, but in general, two candidates with similar experience'll often see the certified one win the higher offer, especially when the hiring manager needs a clean justification. That's the Mile2 CPTS career impact in a sentence.
2026 CPTS (MK0-201) salary table by experience
Here's a practical snapshot for Certified Penetration Testing Specialist (CPTS) holders tied to MK0-201 CPTS exam expectations:
- 0 to 2 years: $70k to $95k (junior pentest, associate consultant, security analyst with testing duties)
- 3 to 5 years: $100k to $135k (pentester, security consultant, roles with purple-team overlap)
- 6+ years: $140k to $185k (senior tester, lead, principal consultant, team lead)
Other factors matter too. Tooling familiarity, report quality, client communication, and whether you can answer "how to pass MK0-201" questions with real examples instead of theory. Also, yeah, recruiters'll ask about CPTS vs CEH vs PenTest+. Have an opinion. Back it up.
Conclusion
Getting ready for your Mile2 exam
Look, I'm not gonna lie. Mile2 certifications like the MK0-201 CPTS aren't a walk in the park. But they're also not some impossible mountain to climb either, you know? You just need the right approach and, honestly, some decent practice materials that don't make you want to throw your laptop out the window.
Real skills matter here.
The CPTS exam tests actual penetration testing abilities. Not just theory you'll forget in a week or, I mean, that stuff you crammed the night before and can barely remember by breakfast. You're dealing with actual methodologies, tools, and scenarios that really matter when you're out there in the field trying to identify vulnerabilities before the bad guys do. That's valuable stuff for your career, honestly.
Here's what I've learned works: study the official materials first, get your hands dirty with labs (seriously, don't skip this part, I know it's tempting when you're tired), and then test yourself repeatedly with practice exams. This part is key. Like absolutely critical. You need to know where your weak spots are before exam day, not during it when you're sweating bullets and the clock's ticking down.
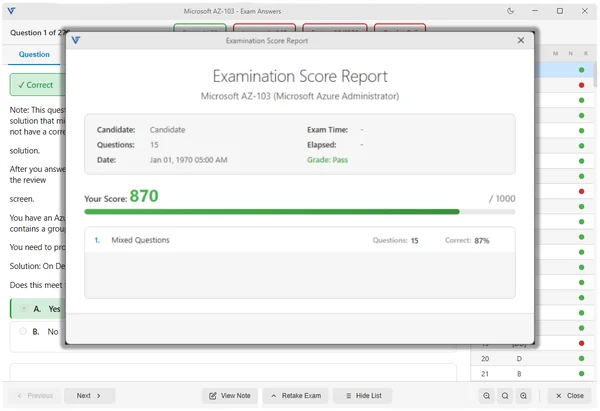
We've put together practice exam resources at https://www.dumpsarena.com/vendor/mile2/ for people prepping for these certifications. The MK0-201 practice materials at https://www.dumpsarena.com/mile2-dumps/mk0-201/ mirror the actual exam format, which helps kill that anxiety when you sit down for the real thing. No surprises. You know what to expect. Question types, time pressure, all that stuff that normally freaks people out.
Practice exams do something else too. They force you to recall information under pressure, which is completely different from passively reading a textbook while half-watching Netflix in the background. That active retrieval? That's what actually makes knowledge stick in your brain instead of just floating around temporarily. Kind of like how I can still remember my high school locker combination from muscle memory but forget my current Wi-Fi password every other week.
Don't just take one practice test and call it done though. That's like going to the gym once and expecting abs. Take multiple attempts, review every single question you miss (even the ones you guessed correctly, because let's be real, lucky guesses don't count), and understand WHY the right answer is right. That's where the actual learning happens, the thing is.
Your Mile2 certification can really open doors. Companies want proof you can do the work, and CPTS shows exactly that. Not just that you can memorize stuff, but that you can actually apply it when things get messy. Put in the prep time now, use quality practice resources, and you'll walk into that exam confident instead of stressed. You've got this. Just don't shortcut the preparation phase or you'll regret it later. Future you will thank present you for doing it right.