Trend Micro Deep Security Professional Exam Overview
Look, I've been watching the security certification space for years, and the Trend Micro Certified Professional for Deep Security credential is one of those certifications that doesn't get enough hype outside the circles where it actually matters. If you're working in enterprise security, especially in environments with complex hybrid cloud setups, this certification proves you can actually do the work, not just talk about it.
Why this credential matters in today's security space
Here's the thing. The Deep Security Professional certification validates that you know how to deploy, configure, manage, and troubleshoot Trend Micro's Deep Security platform across Windows, Linux, and cloud environments. I mean, it's about installing agents and calling it a day. You're demonstrating expertise in the entire architecture: Deep Security Manager, Agents, Relays, Virtual Appliances, the whole ecosystem really. With organizations running workloads across VMware, AWS, Azure, GCP, and on-premises data centers simultaneously, someone who can manage security consistently across all those platforms is worth their weight in gold. Maybe platinum these days given how rare that skillset actually is.
This certification sits within Trend Micro's professional certification track. Above entry-level credentials. But it's accessible to practitioners with solid hands-on experience, which I appreciate. It aligns directly with enterprise security operations roles and cloud security engineering positions where workload protection is a primary concern.
What you're actually proving you can do
The exam validates advanced knowledge across all Deep Security architecture components. You need to understand how the Manager coordinates with Agents, how Relays optimize communication in distributed environments, and when Virtual Appliances make sense versus agent-based protection. Not gonna lie, the architecture questions can trip people up if they've only worked in small deployments where everything's basically plug-and-play.
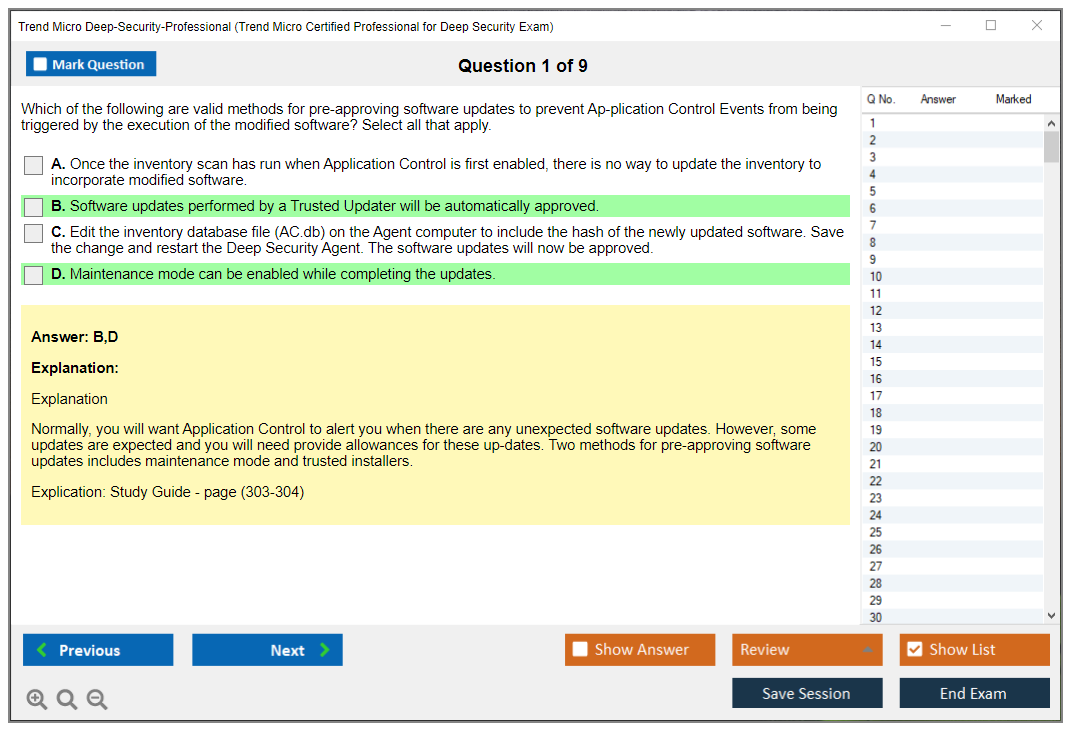
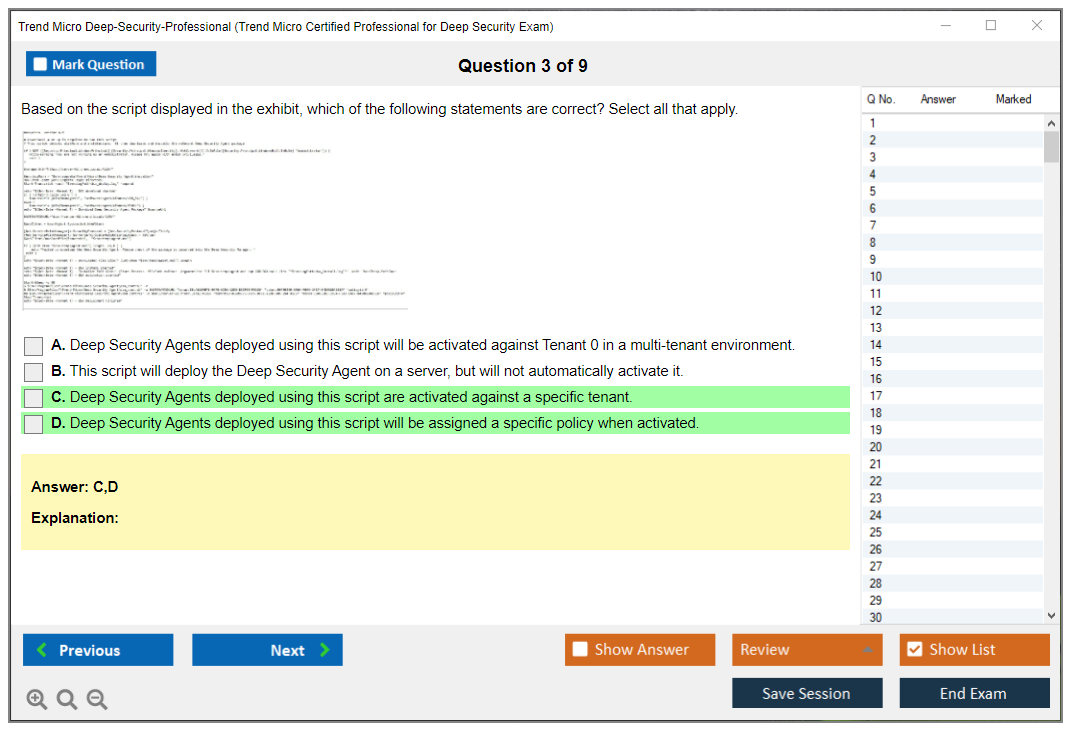
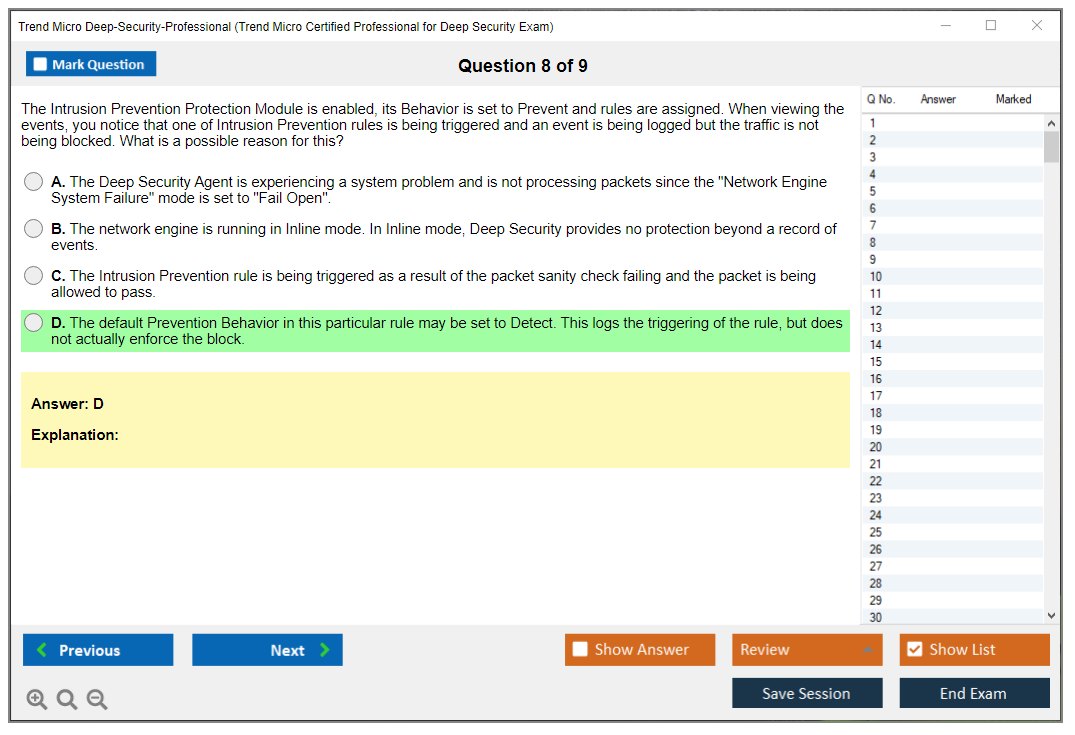
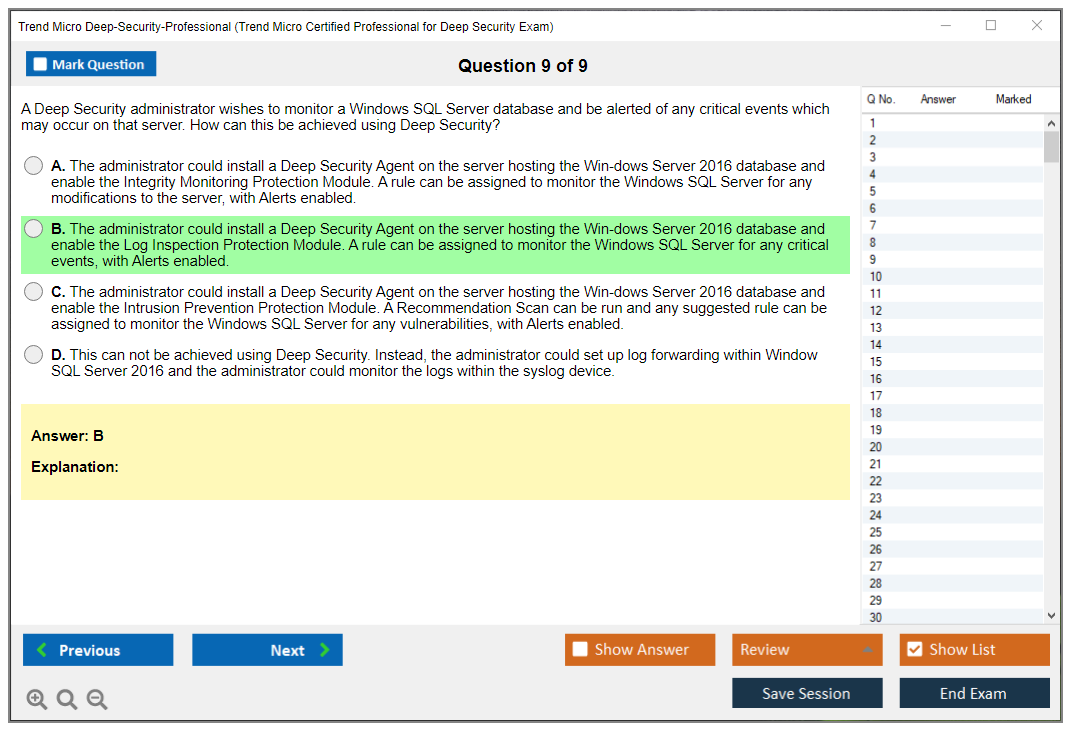
You'll need to demonstrate proficiency across all the protection modules. Anti-Malware, sure. But also Firewall configuration, Intrusion Prevention System tuning, Integrity Monitoring for compliance, Log Inspection for threat detection, Web Reputation filtering, and Application Control whitelisting. Each module has its own configuration details. Performance considerations too. I've seen plenty of admins who know Anti-Malware inside and out but struggle with IPS rule tuning or Application Control policy design. It's a different mindset entirely.
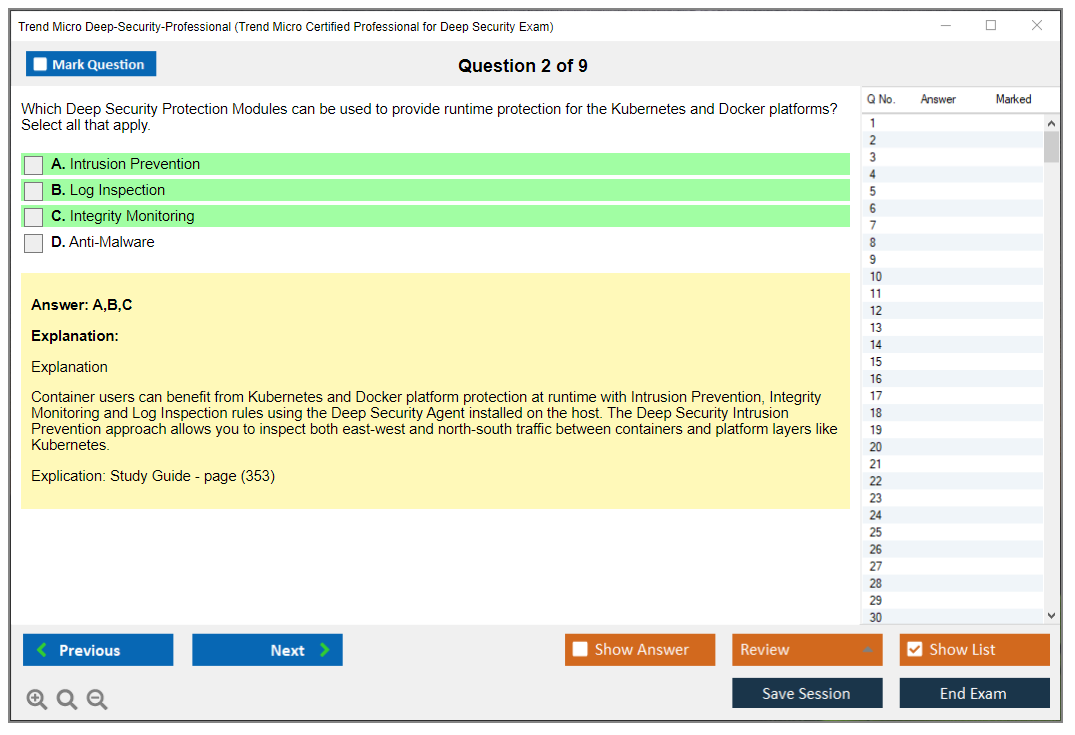
Agent deployment matters. Lifecycle management across different platforms is huge. Windows Server deployment looks different from Linux, and cloud-native deployment through automation tools adds another layer that some people underestimate. Skills in security event analysis and incident response workflows matter too. You're not just blocking threats, you're investigating what happened and why, which separates decent security folks from great ones.
The integration piece is critical. Deep Security doesn't exist in a vacuum, right? You need to understand how it integrates with VMware vCenter, Hyper-V Manager, AWS Systems Manager, Azure Security Center, and GCP security tools. Multi-tenancy and role-based access control come up when you're managing security for different business units or, if you're an MSSP, for multiple clients from a single console.
Who should actually pursue this certification
Security operations center analysts? Prime candidates. Engineers too. If you're triaging alerts from Deep Security or tuning policies to reduce false positives, this certification formalizes that expertise you've been building. Cloud security architects and engineers managing workload protection across hybrid environments are the other obvious audience, though I'd argue you already know that.
System administrators responsible for server security often end up managing Deep Security whether they planned to or not. Getting certified makes that responsibility official. Security consultants implementing Trend Micro solutions for clients benefit enormously. The certification gives clients confidence you know what you're doing, which matters more than people think when you're trying to win contracts. DevSecOps engineers integrating security into CI/CD pipelines find value here too, especially when automating Deep Security policy deployment through APIs and infrastructure-as-code tools, which is becoming standard practice now. IT managers overseeing enterprise security infrastructure and compliance officers ensuring regulatory adherence through security controls round out the typical audience.
I've also seen professionals transitioning from competing platforms like Symantex, McAfee, Carbon Black use this certification to validate their pivot into the Trend Micro ecosystem. Smart move.
The career impact you can expect
Let's talk job roles. Real numbers. Deep Security Administrator positions specifically call out this certification in job descriptions. Average salary ranges from $75K to $110K depending on region and experience, with higher ranges in major metro areas and for senior-level roles where you're expected to mentor others. Cloud Security Engineers specializing in workload protection command similar ranges, often higher when they bring multi-cloud expertise to the table.
Security Solutions Architects for hybrid environments? They can push $120K-$150K+, especially with this certification stacked alongside cloud certifications like AWS Solutions Architect or Azure Security Engineer. Managed Security Service Provider analysts with Deep Security expertise are in constant demand as MSSPs expand their Trend Micro service offerings. It's a growth area. Virtualization Security Specialists, Incident Response Analysts with Deep Security skills, and Technical Account Managers at Trend Micro partners all benefit from this credential in tangible ways.
The certification differentiates you. In competitive job markets. When two candidates have similar experience but one has the certification, guess who gets the callback? There's typically a salary premium of 10-15% associated with vendor certifications in security roles, which adds up over time. Plus, it opens pathways to advanced Trend Micro certifications like Cloud One specializations and gives you recognition within the Trend Micro partner ecosystem. The thing is, that matters more if you're consulting or thinking about going independent eventually.
Actually, I knew someone who used this cert to break into consulting work after years of being stuck in internal IT. Changed his whole trajectory. Just saying, sometimes one credential is the difference between staying put and making a real move.
What the exam actually looks like
The exam is computer-based. Administered through Pearson VUE testing centers. You can also take it online proctored if you prefer testing from home, just make sure your workspace meets their requirements because online proctoring can be finicky. I've heard horror stories about people getting disconnected mid-exam. The format includes multiple-choice questions and scenario-based questions where you're given a situation and asked how to configure or troubleshoot.
Expect around 60-80 questions. Though the exact count varies by exam version. Duration is typically 90-120 minutes, which sounds like plenty until you hit those complex scenarios that require working through multiple configuration steps mentally. Suddenly you're watching the clock. It's closed-book, no reference materials, and you'll sign an NDA before starting. The exam is available in English and select other languages depending on your region.
Prerequisites and what you should know first
There are no mandatory prerequisites. Technically. Which technically means anyone can register and take the exam. But practically? You want 6-12 months of hands-on experience with Deep Security before attempting this. I've talked to people who tried it after just reading documentation, and they got destroyed by the practical scenario questions that require you to actually understand the implications of different configurations.
Basic understanding of operating system security is necessary. Windows Server administration, Linux distributions, user permissions, file system security, all that foundational stuff. You need fundamental networking concepts: TCP/IP, how firewalls work, VLANs, routing basics. Familiarity with virtualization technologies and cloud computing models helps enormously since so much of Deep Security's value proposition is cloud workload protection in environments where you're managing security across multiple hypervisors and cloud providers simultaneously.
General cybersecurity knowledge matters. About the threat space. Common attack vectors, defense-in-depth strategies. This provides context for why certain configurations matter beyond just 'that's what the manual says.' If you're new to Deep Security, start with the official training course and spend serious time in a lab environment before scheduling your exam, because there's no substitute for breaking things and fixing them yourself.
How this fits into the broader certification picture
The Deep Security Professional certification sits within Trend Micro's broader certification framework, which has gotten more full over the years. There are related certifications for other Trend Micro products. Apex One for endpoint protection, Vision One for extended detection and response, Cloud One for cloud-native security. Some professionals collect multiple Trend Micro certifications to demonstrate full platform knowledge, which makes sense if you're working in a multi-product environment.
The progression path typically goes from associate-level to professional to expert levels, though Trend Micro's certification structure has evolved over the years and continues to adapt to market needs. This Deep Security Professional credential is solidly at the professional tier. Meaning it assumes real-world experience. Technical depth matters here.
The Deep Security Professional exam requires serious preparation, but for security professionals working in enterprise or cloud environments, it's one of those certifications that directly translates to daily job responsibilities. That's the best kind of certification. The kind that makes you better at your actual job, not just better at taking tests, which I think we can all agree is what really matters in the long run.
Exam Cost, Registration, and Scheduling Details
What you're paying for (and why the number varies)
The Trend Micro Deep Security Professional exam usually lands in the $300 to $400 USD range. That's the standard fee you'll see quoted, but the exact number depends on where you live and which testing partner setup Pearson VUE is using in that country.
Not cheap. Not outrageous either. Costs still sting though.
Here's how the regional pricing variations tend to shake out, in real-world terms:
- North America: commonly near the upper end, roughly $350 to $400 USD depending on state or province taxes and how Pearson VUE lists it that week.
- EMEA: you'll often see pricing listed in EUR or GBP, and the converted amount can look higher than $400 if your local VAT is baked in, which catches people off guard.
- APAC: some countries price closer to $300 USD equivalent, others don't, and exchange rates can swing hard month to month.
- Latin America: sometimes lower on paper, but bank fees and currency conversion spreads can erase the deal fast.
Currency conversion's the sneaky part. You might see the exam priced in your local currency, pay with a card that bills in USD, then get hit with your bank's conversion fee on top, plus whatever rate they decide to use that day. If you're trying to budget tightly for the Trend Micro Deep Security exam cost, assume a little padding.
Discounts that exist (and the ones people assume exist)
If you're paying out of pocket, you should at least check whether you qualify for any discount channels before clicking 'Pay.'
A few that matter:
- Corporate/volume discounts: If your company's training multiple admins, security engineers, or SOC folks, you can sometimes get a better per-exam rate through Trend Micro sales or an authorized training partner. This is one of those 'ask your account rep' situations, and yeah, it's a bit of a black box, but it can be real money if you're booking several seats.
- Trend Micro partner program vouchers: Partners sometimes get exam vouchers or discounted codes as part of their benefits. If your employer's a Trend Micro partner and nobody's checked the partner portal, look, that's on them. Ask.
- Academic discounts: These are less consistent. Some regions support student pricing through certain programs, some don't. If you're a student, try anyway, but don't assume it's like the big cloud vendors where academic pricing is everywhere.
Other discounts you'll hear about casually include seasonal promos and training bundles, but they come and go, and they're not always advertised loudly.
Cost compared to AWS and Azure security certs
People like comparing everything to AWS and Microsoft, so let's do that quickly. Most AWS associate exams are around $150 USD and professional level exams are around $300 USD, while Microsoft role-based exams are often around $165 USD (varies by country). So the Deep Security Professional certification cost can feel a bit high if you're used to Microsoft pricing, but it's closer to what you'd pay for an upper-tier vendor exam.
Also, not gonna lie, the market value math is different. AWS and Azure certs are broad and stackable. The Trend Micro Certified Professional for Deep Security credential is narrower, but if your job revolves around Deep Security manager administration, policy tuning, and platform operations, it's relevant in a way cloud certs sometimes aren't.
Where registration happens
Registration's done through the Pearson VUE platform. That's the main route for the Trend Micro Certified Professional for Deep Security exam scheduling and payment, and it's what most candidates will use whether they test at a center or online.
One portal. One account. So many clicks.
Step-by-step: registering without making it weird
Here's the walkthrough that saves you from bouncing around pages.
1) Create a Pearson VUE account Use your legal name. Exactly. If your ID says 'Michael A. Smith' and you register as 'Mike Smith,' you can get turned away. Yes, it happens.
2) Find the Trend Micro program Once logged in, search for Trend Micro in the exam catalog or use Trend Micro's certification page link that forwards you into Pearson VUE with the right program preselected.
3) Link to your Trend Micro certification profile Depending on how Trend Micro's set up in your region, Pearson VUE may prompt you to confirm program details. If you already have a Trend Micro certification history, make sure you're not accidentally creating a duplicate identity. Two profiles is a mess later when you're trying to prove you passed.
4) Pick delivery: test center or online proctored You'll choose your exam, then choose delivery method, then you'll see appointment times.
5) Pay and confirm After payment, you'll get a confirmation email. Keep it. Screenshot it. Calendar it.
ID requirements you should not mess up
Pearson VUE's baseline requirement is a government-issued photo ID. Usually that means a passport, driver's license, or national ID card, and the name must match your registration profile. Some countries or test centers ask for a second ID, so read the exact rules in your confirmation, because 'I didn't know' doesn't work at the check-in desk.
Scheduling lead times and time zone gotchas
Availability ranges from 'tomorrow morning' to 'two weeks out,' and it depends on your city, your time of year, and whether you're going online. Booking windows can be as short as 24 hours, or several weeks if you're in a smaller market with limited test centers.
Online proctoring adds a time zone twist. The slots are shown in your local time, but if you travel, change time zones, or book while your laptop's set to a different region, you can end up showing up an hour late without realizing it. Pearson VUE will treat that like a no-show, which is a brutal way to burn $300 to $400.
Test center vs online proctored: what I'd pick and why
Test centers are boring, and that's the point. You get a controlled environment, fewer weird variables, and if the workstation crashes or the login fails, there's on-site staff who can fix it or at least document it. If you're the type who gets thrown off by distractions, a test center's usually the safer bet.
Online proctoring's convenient. Also picky. Sometimes stressful.
For online proctored delivery, you need to be ready for technical requirements that sound simple but fail in dumb ways: a supported OS, a webcam and microphone that work well, stable internet that won't drop for a minute, and the ability to install Pearson VUE's secure browser. Corporate laptops can be a problem because endpoint controls block the proctoring app. The worst time to learn that's 10 minutes before check-in when you're already caffeinated and anxious.
Workspace rules are strict too. Quiet room, clean desk, no papers, no second monitor, no phone within reach, and no 'my roommate will be quiet' promises. Proctors can make you pan your webcam around the room, and if they see something they don't like, they can end the session. Fragments. Random cables. Sticky notes. They care.
Check-in looks different for each method. Test center check-in's ID, pockets out, locker, then you sit down. Online check-in's photos of your ID, photos of your room, face scan, waiting for a proctor, then more instructions, and it can take longer than you think, so build in time.
Rescheduling and cancellation: don't assume you can move it last minute
Pearson VUE rescheduling windows are usually 24 to 48 hours before the appointment. The exact cutoff depends on the exam program and region, so verify in your candidate portal, but the practical advice's simple: if you might need to move it, do it early.
Late reschedules can mean a fee, and no-shows often mean you lose the whole exam fee. That includes 'my internet died' for online testing, unless you can prove an outage and Pearson VUE agrees to an exception, which's possible but not something you should count on.
Rescheduling's done through your Pearson VUE candidate portal. Find your appointment, choose reschedule or cancel, pick a new slot, confirm. Weather delays and test center closures happen too, and in those cases Pearson VUE usually contacts you with next steps, but keep an eye on email the day before if a storm's coming.
Emergency exceptions exist, but they're case-by-case. Medical events, family emergencies, that kind of thing. Documentation can be required. It's not fun.
Retakes and waiting periods (budget for this)
Trend Micro retake rules can vary by program version, so check the current policy on the official certification page, but the patterns you'll see are familiar: first failure might allow a quick retake, while later failures can trigger a waiting period, often around 14 days after a second failure. There's usually also a cap on attempts within a certain timeframe.
Full payment's required for each attempt. So if you're planning your budget, assume worst case that you pay again for a retake, because that's how most vendors handle it.
This is where vendors differ. Microsoft's pretty standardized. AWS is pretty standardized. Trend Micro programs can be a bit more 'depends on the exam,' so don't rely on what your friend experienced on a different Trend Micro track.
Funny thing is, I've seen people obsess over study materials for weeks, buy three different practice exams, then completely forget to budget for a retake. Then they fail by like two questions and have to scramble to find another $400 while the knowledge is still fresh. Don't be that person.
Vouchers, bundles, and getting your employer to pay
Exam vouchers can be purchased through Trend Micro authorized training partners, and sometimes you'll see bundles where a Trend Micro Deep Security training course comes with a voucher. If you were going to take the course anyway, bundles can be worth it, but don't buy training you won't finish just to save $50 on an exam.
Promotional periods happen. Sometimes around conferences, partner events, end-of-quarter pushes. The thing is: employee education benefits, internal L&D budgets, and occasional partner promos all pop up casually.
If you're employed, push for reimbursement. Bring documentation. Keep the receipt, the Pearson VUE confirmation, and your score report. Also, depending on your country, professional certification expenses may be tax-deductible, but that's one to confirm with a tax pro because rules vary a lot.
Accommodations for disabilities: plan ahead
Pearson VUE handles accommodations requests, and you need to request them before scheduling, or at least well before your appointment. Documentation's required, and approvals often take 2 to 4 weeks, so don't book an exam for next Friday and then ask for extended time on Monday.
Accommodations can include extended time, separate rooms at test centers, and assistive tech like screen readers depending on what's supported. The key's lead time. That's it.
After you register: confirmation details and prep logistics
After payment, you'll get a confirmation email. Verify the exam name, delivery method, appointment time, and your name spelling. Add it to your calendar with two reminders, because life happens.
Do the system test early for online proctoring. Not the night before. Drivers update, webcams fail, corporate VPNs interfere, and you don't want to troubleshoot while a proctor watches you struggle through driver updates at the last second.
For test centers, arrive 15 to 30 minutes early. Traffic exists. Check-in lines exist. And if you're already studying things like Deep Security agent and policy configuration and intrusion prevention and anti-malware Deep Security, don't let something dumb like parking be the reason you start flustered.
One last thing. This section's about logistics, but people always ask about the Deep Security exam passing score, the Deep Security exam objectives, and which Deep Security Professional practice test or Deep Security Professional study guide is best. Passing score details are sometimes not publicly disclosed, renewal rules for Deep Security certification renewal can change by version, and prerequisites for Trend Micro certification prerequisites can be lighter than you expect, but the scheduling part's the easy win. Get registered cleanly, pick the right delivery method, and remove the chaos.
Deep Security Exam Passing Score and Scoring Methodology
What you're actually scored on
Okay, so here's the deal. Trend Micro doesn't publish the exact passing score for the Deep Security Professional exam publicly. I've dug through their documentation and talked to people who've taken it, and honestly, here's what I know: the exam uses a scaled scoring system, typically ranging from 300 to 900 points. Most Trend Micro certifications require something around 750 to pass on that scale, but the thing is, they don't confirm this number outright. You won't see "you need 70% correct" anywhere official because it's not that simple.
The scoring isn't just counting right and wrong answers.
Trend Micro uses psychometric scaling, which sounds fancy but basically means they're adjusting for exam difficulty. If you take version A of the exam and your friend takes version B three months later, the questions might differ slightly. Maybe your version had harder scenario questions about IPS tuning or policy inheritance. The scaling process accounts for this so passing the exam in January is roughly equivalent to passing it in July, even though the actual questions aren't identical.
Here's the thing that trips people up: raw score versus scaled score. You might answer 65 questions correctly out of 90, but that raw percentage doesn't directly translate to your final score. The psychometric model weights questions differently based on their difficulty and how well they discriminate between candidates who truly understand Deep Security versus those who don't. A really tough question about agent-relay communication troubleshooting might be worth more than a straightforward question about what anti-malware protection does.
I remember reading somewhere that other certification programs like Cisco use similar models, though they're more transparent about their cut scores. Trend Micro keeps it closer to the vest, which honestly just adds to the anxiety when you're sitting there clicking through questions wondering if you're even close to passing.
Why some questions don't even count
Not gonna lie, this annoyed me when I first learned it.
Some questions on your exam are experimental. They're being tested for future exam versions and don't affect your score at all. You've got no way of knowing which ones these are during the test, so you still need to answer everything seriously. Trend Micro uses these unscored items to gather statistical data: how many people get them right, how long they take, whether the question correlates with overall performance.
This ties into item response theory (IRT), which is the mathematical framework behind modern certification exams. IRT analyzes each question's characteristics. Difficulty, discrimination ability, and whether low-performing candidates can guess it correctly. Questions that everyone gets right or everyone gets wrong aren't useful for determining competency. The exam needs questions that separate candidates who've actually deployed Deep Security policies in production from those who just skimmed the admin guide.
Standard-setting procedures at Trend Micro involve subject matter experts (people who actually work with Deep Security daily) reviewing the exam blueprint and determining what constitutes minimally competent performance. They decide which topics are critical, which scenarios represent real-world challenges, and where the cut score should fall, then statisticians validate that the exam actually measures what it's supposed to measure. It's more rigorous than you'd think.
Getting your results back
The moment you finish the exam, you'll get a preliminary pass/fail notification. If you're testing at a Pearson VUE center, it shows up on screen immediately.
Online proctored exams work the same way. I mean, it's both a relief and terrifying when that screen loads. The preliminary result is almost always accurate, but the official score report comes later.
Within 24 to 48 hours, you'll receive your official score report through the Trend Micro certification portal. You log in with the same credentials you used to register, and the report breaks down your performance by domain. You'll see your overall scaled score (that 300-900 number), whether you passed, and then percentage ranges for each exam objective area. It might say you scored 80-100% on "Deep Security architecture and components" but only 40-60% on "troubleshooting agent communication issues."
The score report doesn't give you question-by-question feedback. You won't know which specific questions you missed. But the domain-level breakdown is actually pretty useful for understanding where you're weak. If you barely passed or failed, those performance indicators tell you exactly what to study harder. Some people get frustrated that it's not more granular, but honestly, knowing you bombed the IPS configuration section is enough to direct your review.
Digital badges and proving you passed
Your Deep-Security-Professional certification comes with a digital badge through Credly (formerly Acclaim). This usually arrives within 5 to 7 business days after you pass.
You get an email from Credly asking you to claim your badge. Once claimed, you can share it on LinkedIn, embed it in email signatures, or link it from your website, and employers and recruiters can click the badge to verify it's legitimate and see when you earned it.
The PDF certificate downloads from the Trend Micro portal pretty quickly, sometimes within 24 hours. It includes your name, certification ID number, and issue date. That ID number is important because third parties can use it to verify your credential through Trend Micro's verification system. I've had recruiters actually check this, so make sure you keep that number handy on your resume or LinkedIn.
When you don't pass the first time
Let's talk about failing because it happens. A lot.
You get your score report showing maybe a 710 when you needed 750, and it stings, but look at those domain breakdowns carefully. Most failed attempts show a pattern: candidates do fine on theoretical knowledge (architecture, components, basic features) but struggle with hands-on scenarios. Questions about policy inheritance across computer groups, configuring recommendation scans, or troubleshooting why agents aren't checking in. That's where people crash.
The diagnostic information in your score report is gold for creating a targeted study plan. If you scored 30-50% on "configuring and tuning Intrusion Prevention," you don't need to re-study everything. Focus there. Spin up a lab environment, actually configure IPS rules, test them against traffic, see what happens when you enable detect mode versus prevent mode. The Deep-Security-Professional practice test materials can help you identify these gaps before test day, honestly.
Common patterns I've seen: people rush through the exam and make careless mistakes on easy questions, or they spend 10 minutes on one really hard scenario and run out of time at the end. Time management is brutal on this exam. You've got roughly 90 minutes for around 65-75 questions (Trend Micro doesn't publish exact numbers, but that's the ballpark). That's just over a minute per question, and some scenario questions require reading a paragraph of context. Practice pacing yourself.
Why people miss the passing score
Insufficient hands-on experience is the number one killer. You can memorize that Deep Security uses agents for protection and a manager for central control, but when a question asks how to troubleshoot an agent that's installed but showing as "not activated" in the manager console, you need to have actually seen that error.
Study guides help, but they're not enough alone. You need to install agents on Windows and Linux, configure policies, see what happens when things break.
Over-reliance on memorization versus understanding kills people on scenario questions. The exam doesn't just ask "what does Integrity Monitoring do?" It presents a situation where file changes aren't being detected and asks you to identify the misconfiguration. Maybe the policy isn't assigned, or the baseline hasn't been created, or the rule doesn't cover that directory. Understanding the workflow matters more than memorizing definitions.
Misinterpreting scenario questions happens constantly. People read the first sentence, think they know the answer, and miss critical details in the second paragraph. I've done this myself on other exams. Slow down. If a question describes a multi-tier application with web servers, app servers, and databases, and asks about policy recommendations, you need to consider that each tier probably needs different protection modules enabled.
Gaps in specific technical domains hurt. Advanced IPS tuning is a common weak spot. So is complex policy inheritance when you've got nested computer groups with conflicting rules. The exam tests edge cases and real-world complexity, not just happy-path scenarios. If you've only worked with Deep Security in a small environment with one simple policy, you're not ready for the certification-level questions.
How hard is it really
Industry estimates suggest first-attempt pass rates for the Trend Micro Certified Professional for Deep Security exam are probably around 60-70%, though Trend Micro doesn't publish official statistics. That's actually pretty reasonable compared to some vendor exams that have sub-50% pass rates.
The Deep Security Professional certification isn't entry-level, but it's not the absolute hardest cert out there either.
Higher pass rates correlate strongly with completing official Trend Micro training courses and having at least 6-12 months of hands-on experience with the platform. People who've deployed Deep Security in production, managed policies across multiple environments, and troubleshot real issues pass at much higher rates than those studying purely from books. That practical experience gives you intuition about how the product behaves, which is invaluable when facing tricky scenario questions.
Compared to other Trend Micro exams, the Deep Security Professional sits in the middle difficulty range. It's harder than foundational-level certifications but easier than architect or specialist tracks. You need depth in Deep Security specifically, but you don't need to be a virtualization expert or a deep networking specialist. Basic understanding of operating systems, networks, and security concepts is enough background knowledge. The exam focuses on Deep Security product knowledge and operational skills, not broad IT theory.
Exam Difficulty: How Hard Is the Deep Security Professional Exam?
What this certification actually proves
The Trend Micro Deep Security Professional exam isn't a "did you read the admin guide" quiz. It's a working-admin exam. You're tested on whether you can run Deep Security in production without breaking things, leaving gaps, or honestly, melting a host with an overzealous IPS policy.
This one's for people doing endpoint and workload security day to day. Deep Security Manager administration. Deep Security agent and policy configuration. And yeah, the stuff that only surfaces at 2 a.m. when agents stop heartbeating and your change window's already toast.
Who this exam is for (and who'll hate it)
Security engineers and ops folks who actually own workload protection? They'll feel at home. SOC analysts who only see alerts might struggle. Same for people who "touched it once" during a pilot.
Look, if your experience is mostly checkbox compliance and you've never tuned intrusion prevention and anti-malware Deep Security policies across mixed Windows and Linux fleets, I mean, this exam'll feel mean.
Format and delivery expectations
Trend Micro exams are typically proctored through an exam provider, and the questions skew scenario-based. Lots of "here's the environment, here's the constraint, what do you change first" type prompts. Some questions are short. Some are long and annoying. Time pressure's real because the scenarios can be wordy and you've still gotta pick between options that sound almost identical.
Exam cost, registration, and scheduling
Trend Micro certification pricing changes by region and currency, and discounts happen through training bundles or vouchers. So the honest answer on Trend Micro Deep Security exam cost is: check the current listing in your region before you book, because what your coworker paid last year might not match today.
Where to register. Trend Micro's certification portal'll bounce you to the test delivery vendor. Booking's normal. Pick a slot, verify ID rules, don't wing the system check.
Reschedule and retake policies vary. Read 'em before paying. Especially retakes. Nothing stings like failing by a hair and realizing the cooldown plus cost means you're waiting weeks.
Passing score and how scoring works
If Trend Micro publishes the Deep Security exam passing score for your specific exam code, great, use it. In many cases, vendors don't publicly disclose the passing score, and candidates only see pass/fail plus a domain breakdown.
The scoring's usually weighted by domain and question type, so bombing one major area can sink you even if you're decent everywhere else. Common miss reasons. People underestimate policy inheritance, they guess on HA architecture, and they assume "recommendations" behave the way they wish they did instead of how they actually work.
Difficulty classification and where it sits on the scale
I'd rate the Trend Micro Deep Security Professional exam as intermediate to advanced. Not expert-level like "design a global program from scratch" but also not entry-level "define IPS" stuff.
Overall difficulty rating, my take:
- 7.5/10 for someone without daily admin time
- 5.5/10 if you've been living in Deep Security for a year
Compared to industry-standard scales, it lands above CompTIA Security+ for sure, because Security+ is broad and conceptual and this is product-accurate and operational. Compared with the old CCNA Security vibe (vendor config plus troubleshooting), it's similar in intensity but narrower in scope. Vendor-neutral benchmarks like Security+ and Network+ help with foundations, but they won't teach you Deep Security's opinionated way of doing policies, agents, relays, and updates. Actually, I once watched someone with three vendor-neutral certs absolutely bomb the policy inheritance section because they kept trying to apply generic firewall logic instead of just learning how Deep Security actually handles it.
Within the Trend Micro certification portfolio, this one's harder than the "intro admin" style certs and closer to the ones where you're expected to know real deployment tradeoffs. Deep Security Professional certification is where Trend Micro starts assuming you can run the platform, not just click around it.
Depth vs breadth in the exam objectives
The Deep Security exam objectives usually cover all protection modules. Anti-Malware, Web Reputation, Firewall, IPS, Integrity Monitoring, Log Inspection. Updates and component management. Alerts and reporting. RBAC. Architecture.
Breadth's wide. But the depth spikes hard in a few places. Policy inheritance. IPS tuning. Manager architecture. Troubleshooting. That's where people burn time and lose points because the "right" answer depends on a detail buried in the scenario.
Skills and experience that make it manageable
Daily experience matters more than book study. Honestly, 6 to 12 months of daily Deep Security administration experience is the cheat code. You've seen the weird cases. You've clicked every tab. You've made mistakes and fixed 'em.
A few things that make the exam feel easier. Hands-on practice with all modules, not just anti-malware and IPS. Log Inspection and Integrity Monitoring show up, and people who never touched 'em get wrecked. Real troubleshooting beyond basic config. Agent activation loops. Relay mis-sizing. Update failures. Certificate issues. That muscle memory helps when the question's basically "what broke" disguised as multiple choice. Understanding underlying tech matters too. Virtualization, cloud platforms, OS internals. If you know how Windows filtering platform behaves or how Linux kernel versions can affect drivers, you can reason through scenarios instead of guessing.
Competitive product experience (Symantec, McAfee, CrowdStrike) helps. Not because the tools match, but because you already think in policies, exclusions, performance tradeoffs, and deployment blast radius. Strong networking and sysadmin foundations. DNS, proxies, TLS, routing, ports. Boring stuff. Exam-winning stuff. Scripting and automation. PowerShell, Python, REST APIs. Even if the test isn't "write code," it expects you to understand what automation touches and what permissions it needs, especially in multi-tenancy. Compliance exposure (PCI DSS, HIPAA, SOC 2). Those frameworks shape why Deep Security gets deployed a certain way, and the exam likes questions that assume you know why Integrity Monitoring's enabled or why logs must be retained.
The topics candidates call "brutal"
Some parts are just harder. Not because they're impossible, but because they're specific and the distractor answers are believable.
Advanced policy architecture and inheritance models are the big one. Complex parent-child policy relationships. Override behaviors and conflict resolution. Computer-specific overrides versus policy-level settings. If you can't picture the inheritance chain in your head, you'll waste minutes rereading the scenario, and you'll still pick the wrong "where do I set it" option.
Intrusion Prevention System fine-tuning's another pain point. Rule recommendations and assignment logic. Performance impact analysis. Custom IPS rule creation and testing. CVE mappings and vulnerability coverage. This is where people who only ever clicked "Assign Recommended" get humbled, because the exam wants you to think about why a rule's recommended, what traffic it inspects, and what it does to CPU on a busy box.
Deep Security Manager architecture and high availability gets technical fast. Multi-node manager deployments. Database sizing and performance tuning. Load balancer config for manager access. Disaster recovery and backup strategies. This is one of those areas where the "almost right" answer's wrong because it ignores a dependency or a single point of failure.
Agent communication troubleshooting shows up constantly. Heartbeat failures. Proxy and relay configs across segmented networks. Certificate and SSL/TLS problems. Activation and reactivation scenarios. The thing is, these questions often have multiple plausible causes, so you need to know the quickest validation step, not just the theoretical list of causes.
Cloud and orchestration integrations are increasingly common. AWS Systems Manager integration, Azure Security Center connectivity, Google Cloud deployment manager integration, Kubernetes and container protection details. If you've only done on-prem, you'll feel the gap.
Log Inspection and custom rule creation can get sneaky. Regex patterns for log parsing. Decoder and parser behavior. Performance implications when someone turns on extensive log inspection across everything because "more logs equals more security." It doesn't. It equals more pain.
Multi-tenancy and delegated administration also trips people. Tenant isolation boundaries. RBAC granularity. API key management. Easy to get wrong if you've only worked in single-tenant setups.
Time-to-prepare estimates that don't lie
For experienced Deep Security admins (1+ years daily use), 2 to 4 weeks of focused review's usually enough. You're filling gaps in advanced features and cleaning up terminology. Practice tests help you spot weak domains fast.
For IT pros with a security background but new to Deep Security, plan 8 to 12 weeks with a structured plan and real lab time. Not optional. A Trend Micro Deep Security training course is honestly worth it here because it forces you through modules you might ignore on the job.
For entry-level IT folks or career changers, 3 to 6 months is more realistic, because you're building foundations while learning the product. Consider Trend Micro certification prerequisites indirectly by grabbing Network+ or Security+ first if networking and security basics are shaky.
Why the exam feels harder than expected
Scenario-based questions require multi-step reasoning. Edge cases show up. Time pressure's real because the scenarios are long. You must distinguish between similar configuration options that differ by scope, inheritance, or where the setting lives.
Version differences can also bite you. Some questions assume knowledge of how a feature behaves in a specific release family. Troubleshooting prompts often include three plausible causes, and the "best next step" is what they're really grading.
Strategies that reduce difficulty fast
Build a home lab. A manager, a few agents, mixed OS, and at least one "problem child" host you can break and fix. Document what you do. Screenshots, notes, and little "if X then check Y" runbooks.
Teach it to someone else. Study groups, mentoring a junior admin, whatever. If you can explain policy inheritance without hand-waving, you're ready.
Mind maps and architecture diagrams help a lot for HA, relays, ports, update flows. Also do timed exam simulations regularly, because knowing the answer and finding the answer under time pressure are different skills.
If you want extra reps, a Deep Security Professional practice test can help, as long as you treat it like diagnostics, not memorization. The Deep-Security-Professional Practice Exam Questions Pack ($36.99) is one option people use to pressure-test weak domains, and it's also useful for pacing because it forces you to commit under a clock. I mean, use it to find gaps, then go back to docs and labs. Same tool, right approach. If you're the type who needs structure, pairing your lab plan with the Deep-Security-Professional Practice Exam Questions Pack makes the prep feel less random. Actually, it also surfaces those edge cases you'd never think to lab on your own.
What to study and how to aim it
A Deep Security Professional study guide should map directly to real tasks. Manager architecture. Agent deployment and activation. Policies, rules, and recommendations. Updates. RBAC. Troubleshooting flows. Reporting. And every protection module, even the ones your org barely uses.
Pick two areas to go deep. Policy inheritance and IPS tuning are the best ROI. Then cover the rest at a working level. Don't ignore Log Inspection. People do. Then they fail.
Renewal and staying current
Deep Security certification renewal rules depend on Trend Micro's program at the time. Some certs require recertification exams, others have validity periods tied to product versions. Check the current policy for Deep Security certification renewal before you assume it's lifetime.
Stuff changes. Product UI changes. Cloud integration changes. Your brain forgets. Keep a small lab around if Deep Security's part of your career path.
FAQ style answers people ask anyway
How much does the Trend Micro Deep Security Professional exam cost? It varies by region and voucher availability, so confirm on the official registration page before booking.
What's the passing score for the Trend Micro Deep Security Professional exam? Often not publicly disclosed, and you'll get pass/fail plus domain feedback.
How hard is the Trend Micro Deep Security Professional certification? Intermediate to advanced, hardest for people without hands-on admin time.
What study materials are best? Official docs, a Trend Micro Deep Security training course if you're new, your own lab notes, and a targeted practice test like the Deep-Security-Professional Practice Exam Questions Pack when you're ready to measure readiness.
How do I renew the Trend Micro Deep Security Professional certification? Follow Trend Micro's current policy for validity and recertification, because it can change with program updates.
Deep Security Exam Objectives and Study Domains
Where to actually get the blueprint
Okay, first things first. Before you dive into anything else with the Trend Micro Deep Security Professional exam, you need to download the official exam objectives document. This sounds stupidly obvious, but you'd be shocked at how many people just study random blog posts instead of going straight to the actual source material. The current objectives live on Trend Micro's certification portal under the Deep Security Professional certification page. You'll find a PDF that breaks down exactly what topics appear on the exam and roughly how much weight each domain carries.
Here's the thing though, and this bit's important. Trend Micro updates this document whenever major product versions drop or when they decide to restructure the exam content. I've watched the blueprint shift between Deep Security 11 and Deep Security 20, mostly adding cloud-native deployment scenarios and NSX Service Composer details that weren't there before. So grab the latest version, check the date stamp carefully, and make absolutely sure it matches the exam version you're registering for. Nothing's worse than grinding through outdated material.
The blueprint isn't just some topic list either. It includes specific task statements like "configure anti-malware scanning options" or "troubleshoot agent communication failures." Those task statements? That's what the exam tests. Don't gloss over them.
How Trend Micro organizes exam content
Trend Micro structures the Deep Security Professional exam into weighted domains. Usually five or six major areas that cover architecture, deployment, configuration, protection modules, and operations. Each domain gets a percentage allocation where you'll see something like "Domain 1: Architecture and Components, 15-20%" which tells you roughly 10-13 questions out of 65 total will come from that bucket.
The percentages matter. They guide your study priorities in ways most candidates miss. If policy configuration is 25% of the exam and relay deployment is 5%, you know where to spend your precious study time. Not gonna lie, most candidates obsess over relay architecture because it feels advanced and impressive, but then they bomb policy inheritance questions that make up a quarter of the test. I've watched this happen repeatedly.
Typical distribution usually puts policy management and protection module configuration at the top (combined maybe 40-45% of exam content). Installation and deployment sit at 15-20%, followed by architecture fundamentals also around 15-20%. Operations and troubleshooting take up another 15-20%, and then smaller chunks for reporting, integration, and advanced scenarios that don't get tested as heavily. But check your specific blueprint because Trend Micro does adjust these numbers between exam versions.
Mapping objectives to product docs
Once you've got the blueprint, your next move is mapping each objective to the official product documentation. Trend Micro publishes detailed admin guides, installation guides, and best practice documents for Deep Security. For every exam objective like "configure intrusion prevention rules," you need to find the corresponding section in the Deep Security Administrator's Guide.
I usually open the PDF blueprint in one window and the online documentation in another, then create a checklist that feels borderline obsessive. Each objective gets a checkmark only after I've read the relevant doc section, tested it in a lab environment, and can explain it without looking at my notes. This sounds tedious. It is tedious as hell. But it works better than scattered studying where you bounce between topics randomly.
Real talk here. The documentation portal also includes knowledge base articles that explain specific configurations or troubleshooting steps. Some of these KB articles directly address exam-relevant scenarios like "Agent shows 'Managed (Online)' but protection modules are inactive" or "Manager database connection pool exhaustion." Those real-world scenarios appear on the exam as multi-part questions that test whether you can troubleshoot under pressure.
Speaking of real-world stuff, I once spent three hours troubleshooting why agents wouldn't activate in my home lab, only to discover I'd fat-fingered the activation URL in my deployment script. Stupid mistake, but it taught me more about agent-to-manager communication than reading documentation ever could. Sometimes the tangents matter more than the main path.
Deep Security Manager is the control plane
Deep Security Manager (DSM) is the centralized management console and policy engine for the entire Deep Security deployment. The manager runs as a web application with a backend database, and you access it through a browser-based console that feels pretty intuitive once you've used it a few times. Understanding the manager architecture is probably 15-20% of the exam content, so let's break down what matters.
The manager handles policy creation, agent activation, security updates distribution, event aggregation, and reporting. It's the brain. The web-based console is where administrators configure policies, computer groups, intrusion prevention rules, anti-malware scanning schedules, firewall rules, you name it. The exam will test whether you understand the manager's role versus agent responsibilities because they're distinct. For example, the manager doesn't perform actual malware scanning. It just pushes policies that tell agents what to scan and when.
Database backend options include PostgreSQL, Microsoft SQL Server, and Oracle. The exam asks about database sizing and performance considerations that matter in production. A manager protecting 500 computers needs way less database horsepower than one managing 10,000 endpoints. This isn't rocket science, but you need to understand the scaling implications. Trend Micro publishes sizing guidelines that correlate protected computer count with CPU, RAM, and database IOPS requirements. You should know these rough numbers like a manager handling 5,000 computers typically needs 8 CPU cores and 16GB RAM minimum. Not exact memorization, but ballpark understanding.
Multi-node manager deployments come up for high availability scenarios. You can run multiple managers in a cluster sharing a single database, or configure primary/secondary manager pairs with database replication for failover. The exam might present a scenario where a company needs zero-downtime management and ask which deployment model fits their requirements best.
Agents do the actual protection work
Deep Security Agents install directly on protected computers and perform the actual security functions. Scanning files, blocking network attacks, monitoring system integrity, all the stuff that matters. The agent architecture integrates at the kernel level on both Windows and Linux, which gives it visibility into file operations, network traffic, and system calls before they execute.
Agent platforms supported include Windows Server and desktop versions, various Linux distributions (RHEL, CentOS, Ubuntu, SUSE), AIX, and Solaris. The exam expects you to know which OS versions are supported and any platform-specific limitations that might bite you. For instance, certain advanced features like Application Control might only work on specific Windows versions, which is annoying but important to remember.
Resource consumption is a big deal in production environments where every CPU cycle matters. Agents typically use 1-3% CPU during idle periods and spike during full system scans or pattern updates. Memory footprint runs around 150-300MB depending on active modules, which isn't terrible but adds up across thousands of endpoints. The exam loves scenario questions like "customer complains about agent performance impact on database servers, what tuning options exist?" You need to know about scheduled scans, real-time scan exclusions, and cache sizing options.
Agentless protection is an alternative for VMware environments where you don't install agents on individual VMs. Instead, a Deep Security Virtual Appliance (DSVA) protects multiple VMs from outside the guest OS, which sounds weird but works surprisingly well in the right situations. The exam will test when to use agentless versus agent-based protection because agentless has limitations like no application control and reduced visibility into encrypted traffic within VMs.
Agent self-protection prevents malware from disabling or tampering with the agent itself. Once activated, the agent locks its own processes and files so even local administrators can't easily stop it without proper authorization. You need the manager console or specific uninstall credentials to remove an activated agent.
Virtual appliances and agentless scenarios
The Deep Security Virtual Appliance provides agentless protection for VMware vSphere environments. You deploy the appliance as a virtual machine on each ESXi host, and it uses VMware vShield/NSX APIs to inspect traffic and file operations for other VMs on that host without installing agents inside guest VMs.
NSX integration and service insertion are exam topics that trip people up constantly. With VMware NSX, you can automatically deploy appliances and apply security policies based on NSX security groups and tags. The service insertion framework redirects VM traffic through the appliance for inspection transparently. You should understand how this works because exam questions test your grasp of the traffic flow. VMs get transparent protection without knowing the appliance exists.
Appliance deployment models include standalone (one appliance per host) and NSX Service Composer integration. Performance-wise, appliances share the host's CPU and memory resources, so there's overhead you can't ignore. A single appliance can protect maybe 100-200 VMs depending on workload characteristics, versus agent-based protection that scales per-VM with more predictable resource consumption.
When to use agentless? Temporary VMs, VDI environments with thousands of identical desktops, or situations where you can't install agents for technical or political reasons. When not to? Workloads that need application control, log inspection, or maximum performance. The exam presents scenarios and you pick the right approach.
Relays extend the architecture
Deep Security Relay functionality helps scale deployments across distributed environments by caching security updates and agent software locally. Relays sit between agents and the manager, reducing WAN traffic and improving update performance for remote offices that might have limited bandwidth.
When to deploy relays: branch offices connected via slow WAN links, segmented networks where agents can't directly reach the manager due to firewall restrictions, cloud regions with hundreds of instances that would overwhelm your manager with simultaneous update requests. A relay downloads updates once from the manager, then serves them to local agents. This cuts WAN bandwidth by 90% in typical deployments, which makes finance departments happy.
Relay configuration involves installing the relay software (which is actually just an agent with relay mode enabled, kinda clever when you think about it), then assigning agents to use that relay for updates and communication. Agents can automatically discover nearby relays or you manually configure relay groups depending on your network topology. The exam asks about relay assignment strategies and troubleshooting agent-to-relay communication when things break.
Relay redundancy matters for availability. You can deploy multiple relays in a location and agents fail over automatically if their primary relay goes offline. Understanding failover behavior and relay priority settings shows up on the exam.
Installation and getting everything deployed
Manager installation starts with meeting system requirements. Supported OS versions, database prerequisites, network ports, SSL certificates, all the boring stuff that causes problems if you skip it. The exam tests whether you know the preparation steps like creating the database schema before running the manager installer, configuring firewall rules for agent communication (port 4120 is the big one), and setting up the initial administrator account with proper credentials.
Installation methods include the graphical installer for Windows/Linux, silent installation using command-line parameters for automation scenarios, and cloud marketplace deployments (AWS, Azure) where you launch pre-configured manager instances that skip most setup steps. You should know the basic command-line syntax for silent installs because the exam might present an automation scenario.
License activation happens after installation. You enter the license key in the manager console, which validates against Trend Micro's licensing servers. The exam might ask about license types (term, perpetual, subscription) or what happens when licenses expire.
Agent deployment at scale
Manual agent installation works for small deployments. Download the installer, run it, activate using an activation code from the manager. But production environments need automated deployment methods that don't require touching every single server individually.
Deployment scripts and silent installation parameters let you push agents via login scripts, startup scripts, or configuration management tools that handle the heavy lifting. The Windows agent installer supports MSI properties for silent install, activation URL, and policy assignment. Linux agents use RPM or DEB packages with command-line options.
Software distribution tools integration is huge for enterprises. SCCM deployments might create a package with the agent MSI and deployment script, then target computer collections based on AD groups. Ansible playbooks can download agents, install them, and activate in one workflow that runs across hundreds of servers. Puppet and Chef modules exist for agent lifecycle management.
Cloud platform integrations include AWS Systems Manager Run Command to deploy agents across EC2 fleets, Azure VM extensions that automatically install and activate agents when VMs launch, and GCP deployment manager templates. The exam loves cloud scenarios, so understand these native integration points.
Our Deep-Security-Professional practice questions pack covers agent deployment scenarios heavily because they're about 15-20% of the real exam. You'll see questions about troubleshooting failed deployments, choosing the right activation method, and configuring proxy settings for agent communication. Getting comfortable with these deployment methods through practice questions helps way more than just reading documentation passively.
Policy architecture is where it gets interesting
Policy architecture in Deep Security follows a hierarchical model with base policies and computer-specific overrides. You create a base policy with common settings, assign it to a group of computers, then override specific settings on individual machines if needed. Understanding inheritance and precedence is critical. The exam will test this concept multiple times.
Parent-child relationships mean changes to a base policy flow down to all assigned computers unless you've created an override. If you enable Firewall in the base policy, all computers get it. But you can override the Firewall state on specific computers without affecting other settings inherited from the base.
Recommendation scans are automated analysis runs where the manager examines a computer's configuration, running processes, open ports, and installed software, then recommends which protection modules to enable and which intrusion prevention rules to apply based on what it finds. The exam asks when to run recommendation scans (after OS updates, application installations, before moving to production) and how to interpret recommendations that might seem contradictory.
Policy templates provide baseline configurations for common workloads. Web server policies, database server policies, domain controller policies that address typical threats. You can create custom templates or use Trend Micro's built-ins as starting points. Best practices include consistent naming conventions, documenting policy purposes, and testing changes in development before production rollout.
Creating and assigning policies involves defining the policy in the manager console, configuring each protection module's settings, then assigning the policy to individual computers or computer groups. Assignment precedence rules determine what happens when a computer belongs to multiple groups with different policies. Usually the most specific assignment wins.
The Trend Micro Certified Professional for Deep Security exam dedicates probably 20-25% of questions to policy configuration scenarios that test your understanding deeply. You'll get questions like "a computer inherits Firewall rules from its base policy but needs custom rules for a specific application, what's the best approach?" Understanding when to use overrides versus creating separate policies separates passing scores from failing ones.
Conclusion
Wrapping up your certification path
Okay, so here's the deal. Passing the Trend Micro Deep Security Professional exam? It's not some memorization game with product features. It's really about proving you can deploy, configure, and troubleshoot Deep Security in actual production environments where downtime costs serious money and security gaps create legitimate risk that keeps executives up at night.
The Trend Micro Certified Professional for Deep Security credential opens doors.
I'm talking roles managing hybrid cloud security, where grasping intrusion prevention and anti-malware Deep Security configurations isn't optional. It's the baseline expectation. Companies running Deep Security manager administration at scale need folks who've demonstrated real competency, not people who just watched some YouTube videos and skimmed through the admin guide pretending they absorbed it all.
The Deep Security exam passing score requirements push you to master the full platform in ways that feel uncomfortable at first. You can't just know agent deployment and conveniently ignore policy inheritance, or understand firewall rules but then completely fumble through integrity monitoring when it comes up. The exam objectives cover everything from Deep Security agent and policy configuration to troubleshooting communication failures between agents and the manager. Actually, that troubleshooting piece trips up so many people because they never practiced it. That's intentional though. Trend Micro wants certified professionals who won't panic when something breaks at 2 AM and everyone's freaking out.
Most people mess up their prep strategy right here. They read documentation front-to-back like it's some thriller novel, never actually touch a live system, then act surprised when scenario-based questions trip them up. Build that lab environment. Break things on purpose. Deploy agents in different modes, test policy conflicts, simulate update failures. The Deep Security Professional study guide hands you theory, but hands-on work gives you the pattern recognition you need when exam questions throw curveballs you didn't see coming.
I once spent three hours troubleshooting why agents wouldn't activate in a test lab, only to realize I'd fat-fingered the manager hostname in the deployment script. Felt stupid at the time. But that mistake? Saved me during the exam when a similar scenario appeared and I knew exactly what to check first.
Before you schedule that exam, test yourself under real conditions. Not gonna lie, a solid Deep Security Professional practice test shows you exactly where your knowledge gaps are hiding. That's why I recommend checking out the Deep-Security-Professional Practice Exam Questions Pack because it mirrors the question styles and domains you'll face, so you're walking in prepared instead of just guessing and hoping for the best.
The Deep Security Professional certification renewal keeps you current as the product evolves, which honestly matters because cloud workload protection changes ridiculously fast. Get certified now, stay sharp, and you'll have skills that actually translate to paychecks and career momentum.
Start prepping today.