
312-50: CEH Certified Ethical Hacker (312-50v9)
Prepare for your ECCouncil examination with our training course. The 312-50 course contains a complete batch of videos that will provide you with profound and thorough knowledge related to ECCouncil certification exam. Pass the ECCouncil 312-50 test with flying colors.
Curriculum For This Course
-
1. Create A VeraCrypt Container to Protect Your Laptop or Desktop10m 48s
-
2. Build a Manual Lab 013m 48s
-
3. Lab Legalities2m 44s
-
4. Getting to Know Your Win2k VM5m 25s
-
5. Getting to Know Your XPAttacker VM3m 4s
-
6. Getting to Know You Win7 VM3m 57s
-
7. Getting to Know Your Win2k3-AD1m 27s
-
8. Getting to Know Your WebApp1m 31s
-
9. Putting Our Lab Together Step By Step12m 30s
-
10. Tying everying together in our Lab5m 44s
-
1. Introduction to Pentesting and Ethical Hacking31s
-
2. Teaser-How Hackers Obtain Serial Numbers Even VMware Workstation Pro4m 58s
-
3. Defintion of a Penetration Test1m 46s
-
4. The Evolving Threat1m 49s
-
5. The Vulnerabilty Lifecycle2m 16s
-
6. Map.Norsecorp.com1m 56s
-
7. Botnet Definition5m 12s
-
8. Defense in Depth4m 47s
-
9. MetaData3m 30s
-
10. Types of PenTests4m 47s
-
11. Types of Hackers1m 32s
-
12. Common Definitions1m 43s
-
13. Hacker vs5m 27s
-
14. Penetration Testing Terminology3m 10s
-
15. Essential Terminology3m 51s
-
16. OSSTMM Methodology8m 43s
-
17. Tools vs Technique4m 45s
-
18. Things are not always as they seem1m 13s
-
19. Calculating Risk & Formulas2m 48s
-
20. Analyzing Findings45s
-
21. Calculating SLE, ARO, ALE1m 6s
-
22. Other Penetration Testing Methodologies3m 15s
-
1. Introduction to Footprinting43s
-
2. What Information is Gathered by the Hacker5m 37s
-
3. Methods of Obtaining Information And Physical Access1m 24s
-
4. Social Access4m 27s
-
5. Digital Access3m 2s
-
6. Passive vs Active Reconnaissance2m 14s
-
7. Footprinting Defined1m 32s
-
8. Exercise: Footprinting Tool: Maltego2m 3s
-
9. Most Powerful Hacking Tool on the Internet Today4m 16s
-
10. Instructor Demonstration - The Power of Google -A5m 44s
-
11. Instructor Demonstration - The Power of Google -B10m 16s
-
12. Instructor Demo: GoogleAlerts4m 24s
-
13. Removing Searchable Content4m 55s
-
14. Internet Archive: The WayBack Machine6m 44s
-
15. Domain Name Registration-WhoIs Information1m 20s
-
16. Instructor Demonstation - CentralOps6m 14s
-
17. DNS Databases3m 21s
-
18. Traceroute Operation5m 30s
-
19. InstructorDemonstration: Online Tools4m 19s
-
20. Spokeo - No Refuge for the Wealthy4m 59s
-
21. Netcraft, DoaminsbyProxy, Countermeasures8m 43s
-
1. Introduction to Linux24s
-
2. Linux History - Linus + Minux = Linux2m 29s
-
3. Linux GUI Desktops2m 9s
-
4. Linux Shell Linux Bash Shell2m 31s
-
5. Passwd & Shadow File Formats1m 52s
-
6. InstructorDemo:User Account Management6m 20s
-
7. Tarballs & Zips & Installing VMware Tools5m 30s
-
8. Compiling Programs in Linux, Shell Shock, Poodle Vulnerability2m 44s
-
9. Most Popular Linux Security Distribution1m 58s
-
1. Introduction to Port Scanning15s
-
3. TCP/IP Stack6m 22s
-
4. TCP 3-Way HandShake7m
-
5. NMap ServiceVersion Detection And Demo1m 44s
-
6. Instructor Demonstration-Engage, NmapScans1m 24s
-
7. Hping3, NMap -O1m 32s
-
8. Fuzzy Logic1m 30s
-
9. Countermeasures: Scanning2m 21s
-
1. Intro to Enumeration17s
-
2. Grabbing Banners4m 25s
-
3. Shodan5m 20s
-
4. ZoneTransfers5m 1s
-
5. DNS Enumeration4m 26s
-
6. SNMP Countermeasures, AD and AD Countermeasures4m 13s
-
7. Null Sessions8m 40s
-
1. Intro Into Cryptography31s
-
2. Beginings of Cryptography4m 36s
-
3. Implementation, Stream Cipher, Block Cipher and the Enigima8m 54s
-
4. Asymetric Encryption, Hybrid Encryption, Comparison of Algorithims, Key Exchange5m 7s
-
5. Hashing, Hashing Collisions, Common Hash Algorithms9m 38s
-
6. Ransomware3m 7s
-
7. IPSec and SSH3m 46s
-
8. PKI Applications, Quantum Crypto and VeraCrypt3m 27s
-
1. Introduction to Malware and How The Internet Makes Money23s
-
2. Things that make the World Go Around - Well as far as the Internet is concerned9m 10s
-
3. Trojans and Back Doors6m 17s
-
4. Defining Malware: Viruses and Worms7m 14s
-
5. Defining Malware: Spyware5m 35s
-
6. Data Loss Prevention (DLP) and other Creepy things10m 31s
-
7. Distributing Malware6m 19s
-
8. Malware Capabilities5m 27s
-
9. Auto Starting Malware1m 44s
-
10. Tool: Netcat3m 41s
-
11. Demo: NetCat Procedure10m 28s
-
12. Executable Wrappers4m 22s
-
13. Instructor Demo: Executeable Wrappers 18m 51s
-
14. Instructor Demo: Executeable Wrappers 21m 53s
-
15. Malware Avoiding Detection4m 33s
-
16. Malware Countermeasures 18m 10s
-
17. Malware Countermeasures 26m 39s
-
1. Introduction to System Hacking Introduction1m
-
2. Types of Password Attacks, Keystroke Loggers5m 44s
-
3. Password Guessing Online7m 44s
-
4. Cracking Windows Passwords - A3m 25s
-
5. Cracking Windows Passwords - B8m 32s
-
6. Cracking Windows Passwords - C7m
-
7. Cracking Windows Passwords - D8m
-
8. Cracking Windows Passwords - E8m 25s
-
9. Countermeasures: Stealing the Passwords, Syskey, Salting8m 41s
-
10. Cloud Cracking Techniques1m 55s
-
11. Generating Rainbow Tables, Free Rainbow Tables3m 17s
-
12. Password Hash Insertion Attack9m 21s
-
13. Demonstration MimiKatz10m 59s
-
14. Privilege Escalation, Countermeasures5m 37s
-
15. Covering Tracks, Disable Auditing, Clearing the Event Log3m 4s
-
16. Alternate Data Streams Demonstration - A8m 7s
-
17. Alternate Data Streams Demonstration - B11m 55s
-
18. Alternate Data Streams Demonstration - C10m 39s
-
19. Anonymizers - JAP3m 42s
-
20. Steganography11m 41s
-
21. Virtually Complete Secrecy, TOR11m 2s
-
22. RootKits - Overview8m 39s
-
23. RootKits - Frightening Demo13m 22s
-
24. Root Kit Countermeasures, Tokens and Smart Cards11m 19s
-
1. Introduction to Advanced System Explotation1m
-
2. How do Exploits Work?5m 8s
-
3. Buffer Over Flows Introduction I do when Speaking at a Conference5m 59s
-
4. Processors and Stacks10m 23s
-
5. Basic Types of Buffer Overflows And Demo 0111m 12s
-
6. Basic Types of Buffer Overflows And Demo 029m 27s
-
7. Basic Types of Buffer Overflows And Demo 031m 37s
-
8. Stages of Exploit Development7m 54s
-
9. Buffer Overflow Prevention5m 8s
-
10. The Metasploit Project5m 10s
-
11. Core Impact Overview12m 54s
-
1. Introduction to Database Management Systems23s
-
2. Overview of Databases, Types of Databases, Relations of Databases7m 16s
-
3. View of DBMS, Injecting a DBMS, Why SQL Injection, SQL Connection Properties6m 40s
-
4. SQL Injection Types, Stored Procedures, Shutdown, Locating SQL, Sensitive Info9m 21s
-
5. Hardening SQL Server9m 21s
-
6. SQL Injection Demo 19m 54s
-
7. SQL Injection Demo 26m 10s
-
8. SQL Injection Demo 34m 3s
-
1. Introduction to WiFi and Mobile Hacking26s
-
2. WiFiNetwork Types, Widely Deployed Standards, A, B, G, 802.11n - MIMO, 802.11ac,4m 9s
-
3. 802.11n - MIMO, 802.11ac, SSID, MAC Filtering, WEP, Weak IV Packets5m 44s
-
4. XOR Basics, WEP Weaknesses3m 26s
-
5. TKIP, WPA vs WEP, WPA MIC Vulnerabilty, WPA-PSK Encryption3m 26s
-
6. Kismet, Aircrack-ng, Aireplay2m 54s
-
7. EAP Types, EAP Advantages/DisAdvantages, Typical Wired/Wireless Network2m 47s
-
8. Exercise/Assignment; Cracking WPA/WPA2 Password Preparation12m 45s
-
9. Exercise/Assignment; Cracking WPA/WPA2 Password - Solution5m 19s
-
1. Introduction to Sniffing17s
-
2. Packet Sniffers, PCap & WinPcap, Wireshark, TCP Reassembly, Packetyzer7m 34s
-
3. TCP Dump & WinDump, Network Miner Wildpackets, Cain and Able, Passive Sniffing4m 16s
-
4. Active Sniffing & Methods, Switch Table Flooding4m 22s
-
5. Arp Cache Posioning6m
-
6. Arp Cache Posioning Tools and Countermeasures5m 35s
-
7. Breaking SSL Traffic, Intercepting VoIP, Routing Protocols, RDP, Passwords and M6m 18s
-
8. Exercise/Assignment Breaking SSL - Preparation9m 3s
-
9. Exercise/Assignment Breaking SSL - Solution5m 19s
-
1. Introduction tp Firewalls, IDS and IPS WAF8s
-
2. Firewall - Your First Line of Defense6m 35s
-
3. IDS Your Second Line of Defense4m 55s
-
4. Web Application Firewall and Evasion Techniques'7m 45s
-
5. Behavioural Firewalls and IPS Systems3m 35s
-
1. Introduction to Web Application42s
-
2. Common Security Threats, Need for Monitoring, SANS Seven MGT Errors6m 35s
-
3. Anatomy of a Web Attack, Web Attack Techniques, Typical Web App Componets5m 12s
-
4. Logs Cancanolization and Other Attacks3m 36s
-
5. Web App Scanner, HTTrack,HTTPrint, Proxies7m 7s
-
6. Directory Traversal & Other Common Vulnerabilties9m 44s
-
7. XSS Demo and Countermeasures8m 50s
-
8. Common Ways to Attack Web Technologies, Cross Site Scripting (XSS)8m 50s
-
9. Cross Site Request Forgery6m 3s
-
10. Cookies and Session Management5m 19s
-
11. OWASP Top 107m 5s
-
1. So your Ready To Take Your Test 1?7m 16s
-
1. Backing Up our Veracrypt Storage Enclosure for Saftey5m 14s
Hot Exams
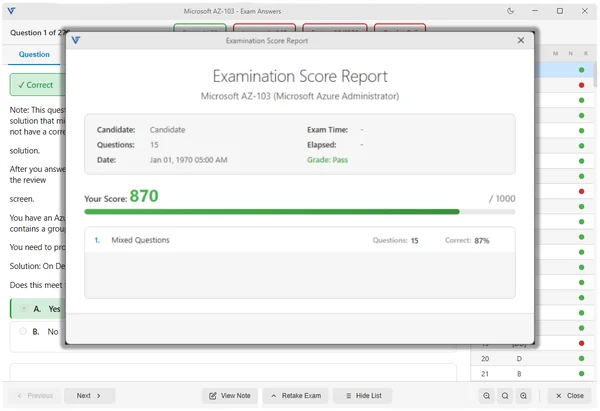
VTSimu Exam Simulator
How to open .dumpsarena files
Use Free VTSimu Exam Simulator to open .dumpsarena files
Satisfaction Guaranteed
98.4% DumpsArena users pass
Our team is dedicated to delivering top-quality exam practice questions. We proudly offer a hassle-free satisfaction guarantee.
Why choose DumpsArena?
23,812+
Satisfied Customers Since 2018
- Always Up-to-Date
- Accurate and Verified
- Free Regular Updates
- 24/7 Customer Support
- Instant Access to Downloads
Secure Experience
Guaranteed safe checkout.
At DumpsArena, your shopping security is our priority. We utilize high-security SSL encryption, ensuring that every purchase is 100% secure.