
SY0-501: CompTIA Security+
Prepare for your CompTIA examination with our training course. The SY0-501 course contains a complete batch of videos that will provide you with profound and thorough knowledge related to CompTIA certification exam. Pass the CompTIA SY0-501 test with flying colors.
Curriculum For This Course
-
1. Overview of Security2m 55s
-
2. CIA Triad3m 54s
-
3. AAA of Security3m 5s
-
4. Security Threats2m 57s
-
5. Mitigating Threats2m 28s
-
6. Hackers4m 53s
-
7. Threat Actors3m 12s
-
1. Malware39s
-
2. Viruses6m 21s
-
3. Worms2m 9s
-
4. Trojans2m 48s
-
5. Demo: Viruses and Trojans6m 16s
-
6. Ransomware2m 30s
-
7. Spyware2m 39s
-
8. Rootkits3m 29s
-
9. Spam2m 56s
-
10. Summary of Malware2m 2s
-
1. Malware Infections4m 12s
-
2. Common Delivery Methods3m 23s
-
3. Botnets and Zombies3m 30s
-
4. Active Interception and Privilege Escalation2m 28s
-
5. Demo: Privilege Escalation5m 41s
-
6. Backdoors and Logic Bombs3m 48s
-
7. Symptoms of Infection4m 10s
-
8. Removing Malware5m 1s
-
9. Preventing Malware5m 56s
-
1. Security Applications and Devices33s
-
2. Software Firewalls4m 16s
-
3. Demo: Software Firewalls6m 44s
-
4. IDS5m 3s
-
5. Pop-up Blockers3m 9s
-
6. Data Loss Prevention (DLP)3m 43s
-
7. Securing the BIOS3m 56s
-
8. Securing Storage Devices3m 26s
-
9. Disk Encryption4m 51s
-
1. Mobile Device Security1m 14s
-
2. Securing Wireless Devices1m 30s
-
3. Mobile Malware6m 19s
-
4. SIM Cloning & ID Theft4m
-
5. Bluetooth Attacks2m 8s
-
6. Mobile Device Theft3m 10s
-
7. Security of Apps5m 6s
-
8. BYOD4m 56s
-
9. Hardening Mobile Devices3m 51s
-
1. Hardening1m 47s
-
2. Unnecessary Applications3m 10s
-
3. Restricting Applications2m 56s
-
4. Demo: Unnecessary Services5m 35s
-
5. Trusted Operating System1m 57s
-
6. Updates and Patches3m 26s
-
7. Patch Management3m 49s
-
8. Group Policies2m 33s
-
9. Demo: Group Policies4m 6s
-
10. File Systems and Hard Drives3m 18s
-
1. Virtualization2m 7s
-
2. Hypervisors2m 37s
-
3. Demo: How to create a VM4m 39s
-
4. Threats to VMs3m 43s
-
5. Securing VMs3m 47s
-
6. Demo: Securing VMs4m 41s
-
1. Application Security1m 43s
-
2. Web Browser Security6m 39s
-
3. Web Browser Concerns3m 19s
-
4. Demo: Web Browser Configuration5m 20s
-
5. Securing Applications4m 49s
-
1. Software Development8m 34s
-
2. SDLC Principles6m 22s
-
3. Testing Methods6m 59s
-
4. Software Vulnerabilities and Exploits2m 28s
-
5. Buffer Overflows6m 15s
-
6. Demo: Buffer Overflow Attack6m 25s
-
7. XSS and XSRF3m 7s
-
8. SQL Injection6m 25s
-
9. Demo: SQL Injection7m 13s
-
1. Network Security44s
-
2. The OSI Model6m
-
3. Switches3m 32s
-
4. Routers2m 27s
-
5. Network Zones3m 26s
-
6. Network Access Control2m 40s
-
7. VLANs1m 30s
-
8. Subnetting1m 51s
-
9. Network Address Translation2m 26s
-
10. Telephony5m 58s
-
1. Perimeter Security46s
-
2. Firewalls8m 1s
-
3. Demo: SOHO Firewall4m 4s
-
4. Proxy Servers4m 12s
-
5. Honeypots and Honeynets1m 22s
-
6. Data Loss Prevention1m 35s
-
7. NIDS and NIPS4m 11s
-
8. Unified Threat Management1m 52s
-
1. Cloud Computing3m 29s
-
2. Cloud Types2m 51s
-
3. As a Service7m 4s
-
4. Cloud Security2m 25s
-
5. Defending Servers4m 32s
-
1. Network Attacks38s
-
2. Ports and Protocols54s
-
3. Memorization of Ports11m 30s
-
4. Unnecessary Ports3m 21s
-
5. Denial of Service7m 56s
-
6. DDoS1m 36s
-
7. Stopping a DDoS2m 27s
-
8. Spoofing1m 16s
-
9. Hijacking3m 45s
-
10. Replay Attack1m 27s
-
11. Demo: Null Sessions2m 24s
-
12. Transitive Attacks1m 24s
-
13. DNS Attacks4m 33s
-
14. ARP Poisoning1m 30s
-
1. Securing Networks49s
-
2. Securing Network Devices6m 43s
-
3. Securing Network Media8m 48s
-
4. Securing WiFi Devices4m 22s
-
5. Wireless Encryption5m 30s
-
6. Wireless Access Points6m 11s
-
7. Wireless Attacks4m 15s
-
8. Demo: Wireless Attack6m 58s
-
9. Other Wireless Technologies6m 2s
-
1. Physical Security1m 30s
-
2. Surveillance2m 51s
-
3. Door Locks3m 47s
-
4. Demo: Lock Picking1m 36s
-
5. Biometric Readers4m 15s
-
1. Facilities Security36s
-
2. Fire Suppression6m 21s
-
3. HVAC2m 23s
-
4. Shielding2m 34s
-
5. Vehicles2m 3s
-
1. Authentication5m 53s
-
2. Authentication Models5m 17s
-
3. 802.1x3m 44s
-
4. LDAP and Kerberos2m 26s
-
5. Remote Desktop Services1m 51s
-
6. Remote Access Service2m 3s
-
7. VPN3m 2s
-
8. RADIUS vs TACACS+2m 18s
-
9. Authentication Summary2m 4s
-
1. Access Control50s
-
2. Access Control Models8m 14s
-
3. Best Practices5m 44s
-
4. Users and Groups9m 12s
-
5. Permissions3m 41s
-
6. Usernames and Passwords2m 36s
-
7. Demo: Policies4m 34s
-
8. User Account Control1m 53s
-
1. Risk Assessments8m 33s
-
2. Qualitative Risk4m 6s
-
3. Quantitative Risk5m 27s
-
4. Methodologies2m 49s
-
5. Security Controls6m 49s
-
6. Vulnerability Management7m 50s
-
7. Penetration Testing4m 26s
-
8. OVAL1m 34s
-
9. Vulnerability Assessments6m 52s
-
10. Demo: Nmap Scanning8m 50s
-
11. Demo: Vulnerability Scanning9m 33s
-
12. Password Analysis5m 54s
-
13. Demo: Password Cracking2m 36s
-
1. Monitoring Types2m 54s
-
2. Performance Baselining4m 35s
-
3. Protocol Analyzers2m 58s
-
4. SNMP3m 40s
-
5. Demo: Analytical Tools4m 27s
-
6. Auditing1m 54s
-
7. Demo: Auditing Files3m 53s
-
8. Logging3m 39s
-
9. Log Files5m 14s
-
10. SIEM2m 54s
-
1. Cryptography4m 56s
-
2. Symmetric vs Asymmetric6m 12s
-
3. Symmetric Algorithms4m 56s
-
4. Public Key Cryptography3m 9s
-
5. Asymmetric Algorithms3m 44s
-
6. Pretty Good Privacy1m 46s
-
7. Key Management2m 11s
-
8. One-Time Pad4m 18s
-
9. Hashing8m 27s
-
10. Demo: Hashing3m 4s
-
11. Hashing Attacks3m 15s
-
12. Increasing Hash Security1m 26s
-
1. Public Key Infrastructure3m 53s
-
2. Digital Certificates6m 42s
-
3. Demo: Certificates3m 31s
-
4. Certificate Authorities4m 12s
-
5. Web of Trust2m 35s
-
1. Security Protocols21s
-
2. S/MIME1m 29s
-
3. SSL and TLS5m 48s
-
4. SSH2m 28s
-
5. VPN Protocols6m 37s
-
6. Demo: Setting up a VPN1m 37s
-
1. Planning for the Worst2m 9s
-
2. Redundant Power3m 8s
-
3. Backup Power3m 6s
-
4. Data Redundancy4m 39s
-
5. Demo: RAIDs3m 35s
-
6. Network Redundancy2m 4s
-
7. Server Redundancy1m 42s
-
8. Redundant Sites2m 20s
-
9. Data Backup2m 54s
-
10. Tape Rotation3m 52s
-
11. Disaster Recovery Plan5m 38s
-
1. Social Engineering52s
-
2. Demo: Pretexting4m 14s
-
3. Insider Threat2m 10s
-
4. Phishing1m 13s
-
5. More Social Engineering4m
-
6. User Education4m 44s
-
1. Policies and Procedures5m 53s
-
2. Data Classifications6m 42s
-
3. PII and PHI6m 19s
-
4. Security Policies10m 19s
-
5. User Education4m 2s
-
6. Vendor Relationships7m 52s
-
7. Disposal Policies5m 4s
-
8. Incident Response Procedures4m 36s
-
9. Data Collection Procedures3m 11s
-
10. Demo: Disk Imaging6m 56s
-
11. IT Security Frameworks3m 18s
-
1. Exam Tricks4m 9s
Hot Exams
VTSimu Exam Simulator
How to open .dumpsarena files
Use Free VTSimu Exam Simulator to open .dumpsarena files
Satisfaction Guaranteed
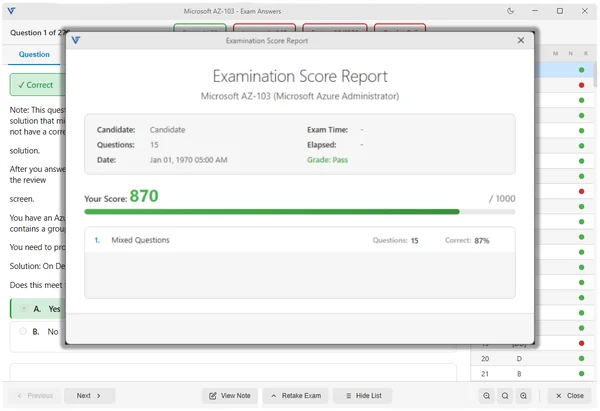
98.4% DumpsArena users pass
Our team is dedicated to delivering top-quality exam practice questions. We proudly offer a hassle-free satisfaction guarantee.
Why choose DumpsArena?
23,812+
Satisfied Customers Since 2018
- Always Up-to-Date
- Accurate and Verified
- Free Regular Updates
- 24/7 Customer Support
- Instant Access to Downloads
Secure Experience
Guaranteed safe checkout.
At DumpsArena, your shopping security is our priority. We utilize high-security SSL encryption, ensuring that every purchase is 100% secure.