Understanding the Fortinet NSE7_EFW-6.2 Certification
Look, if you're working with FortiGate firewalls day in and day out and you've already got your NSE 4 under your belt, you've probably wondered what's next. The Fortinet NSE7_EFW-6.2 exam is that next step, and honestly, it's another cert to toss on your resume. This thing actually tests whether you can troubleshoot real problems in production environments, not just regurgitate configuration commands you memorized the night before.
What this certification actually proves you know
The Fortinet NSE 7 Enterprise Firewall 6.2 certification validates that you can deploy, manage, and (most importantly) troubleshoot enterprise-level FortiGate firewall solutions running FortiOS 6.2. We're talking advanced stuff here. Complex NAT scenarios where you're dealing with central NAT, virtual IPs, and policy-based NAT all at once. VPN troubleshooting that goes way beyond "did you check if phase 1 is up?" You'll need to understand deep packet inspection flows, how traffic moves through security profiles, and why your IPS might be blocking legitimate traffic while letting something sketchy through.
The certification demonstrates you can design firewall policies that actually make sense at scale. You'll tune security profiles without tanking performance, configure high availability clusters that don't fall apart during a failover, and diagnose why traffic isn't flowing the way it should. It's the difference between knowing how to configure something and knowing why it's broken.
Where NSE 7 fits in the Fortinet certification ladder
NSE7_EFW-6.2 sits at the expert level (Level 7) of Fortinet's Network Security Expert program. You've got NSE 4 at the professional level, which covers the fundamentals of FortiGate security and infrastructure. Most people tackle NSE4_FGT-7.2 or whatever version is current first. Then there's NSE 7, where you prove you can handle enterprise deployments and complex troubleshooting. Above that? NSE 8, the architect level, where you're designing entire security infrastructures.
Not gonna lie, jumping from NSE 4 to NSE 7 is a big leap. NSE 4 tests whether you understand the concepts. NSE 7 tests whether you can fix things when they break at 2 AM and everyone's breathing down your neck.
Who should actually take this exam
Senior network security engineers are the obvious candidates here. If you're the person people call when a FortiGate cluster isn't failing over correctly, this is your cert. Firewall administrators who manage complex enterprise deployments with hundreds of policies and multiple VPN tunnels? Yeah, this validates what you already do. Security architects designing zero-trust segmentation strategies need to understand how FortiGate actually processes traffic at this level.
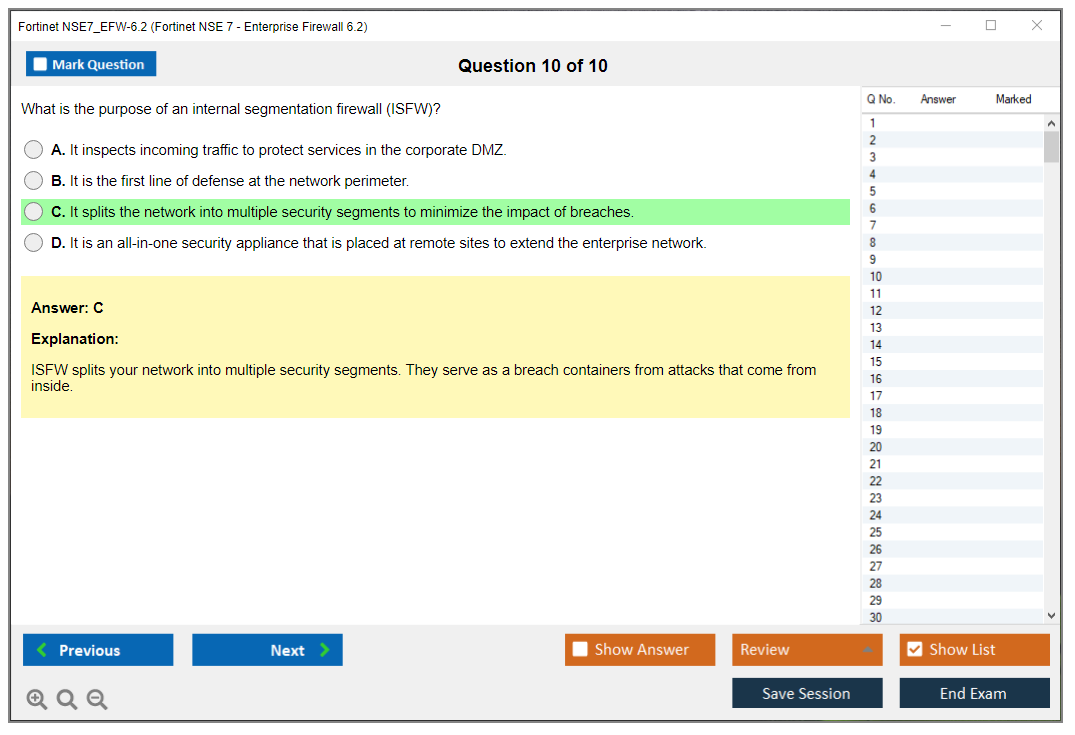
Consultants who implement FortiGate solutions for different clients benefit big time because you're constantly dealing with new environments and weird edge cases. Pre-sales engineers at Fortinet partners or resellers use this to demonstrate technical credibility when you're in front of customers. And if you work for a managed security service provider, having NSE 7 on your profile shows you can handle enterprise-class firewall management, not just basic monitoring.
The real-world skills you'll actually use
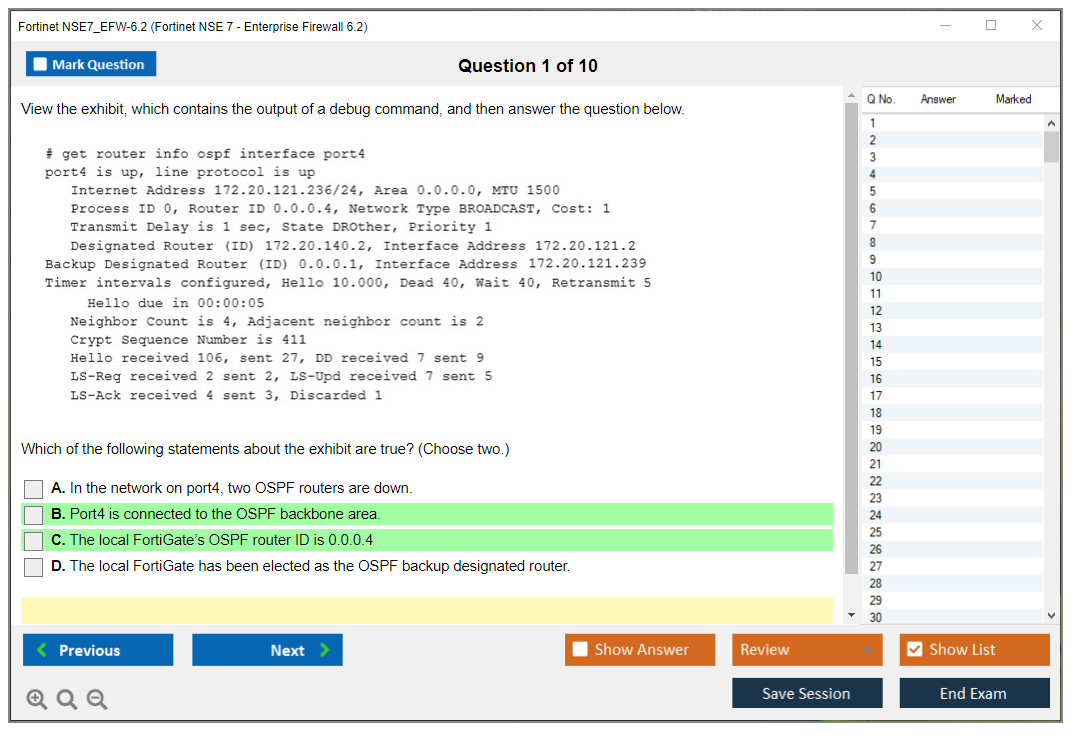
Here's what makes NSE7_EFW-6.2 different from lower-level certs: scenario-based troubleshooting. You learn to diagnose traffic flow issues using CLI commands like 'diagnose debug flow', 'diagnose sniffer packet', and various 'get' commands to pull routing tables, session tables, and policy hit counts. You'll optimize security inspection performance because you understand the order of operations. When does the firewall check policies versus when does it apply security profiles versus when does NAT happen?
Designing resilient HA clusters? Goes beyond just enabling FGCP. You need to understand session synchronization, when to use active-active versus active-passive, how to handle asymmetric routing, and what happens during a failover. Implementing zero-trust segmentation requires deep knowledge of how identity-based policies work, how to integrate with authentication sources, and how to segment traffic without breaking legitimate business flows.
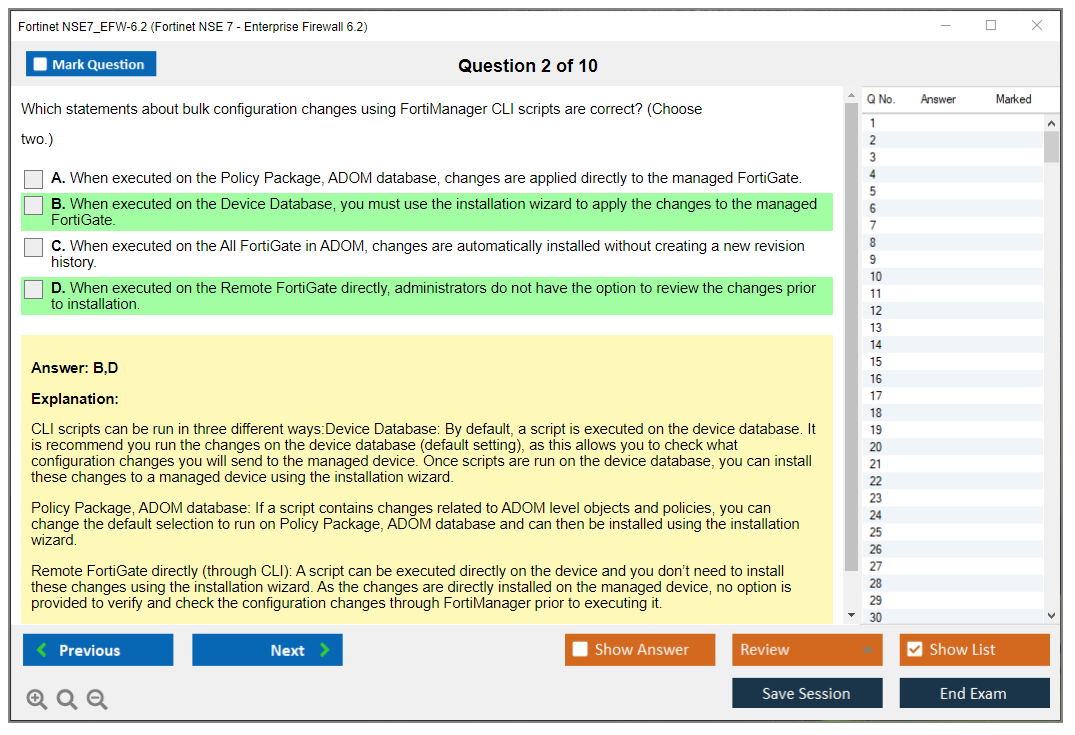
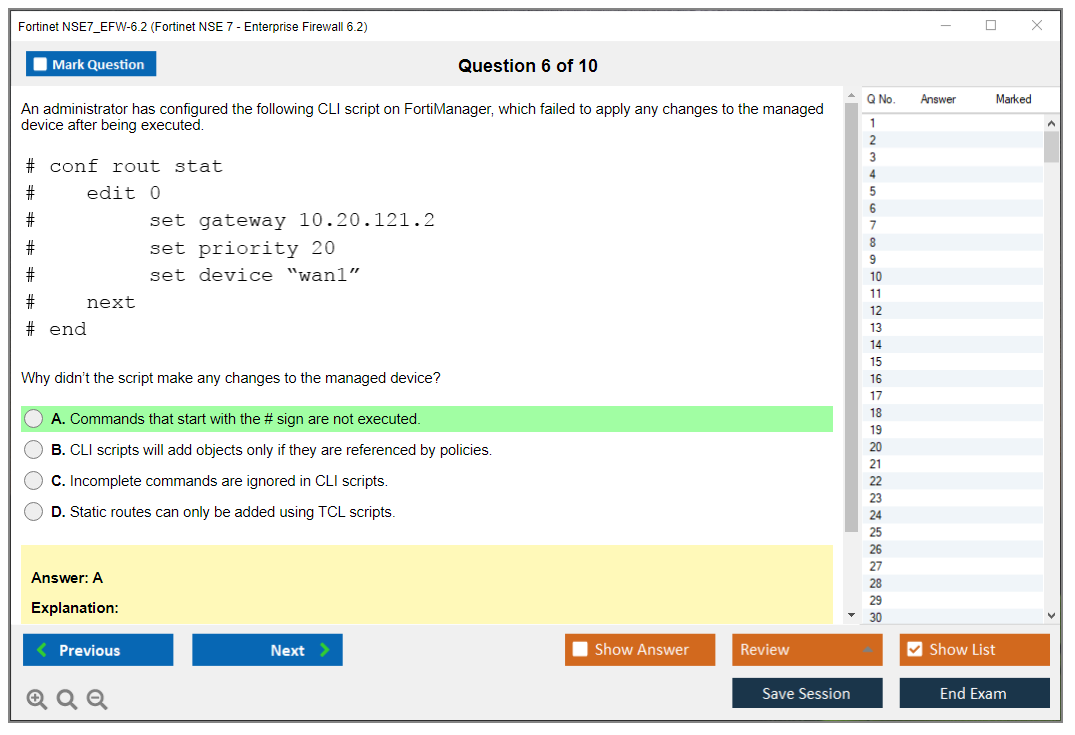
Integration with FortiAnalyzer and FortiManager becomes critical at this level too. You're not just collecting logs. You're using log analysis to troubleshoot incidents, identify policy gaps, and prove compliance. You're pushing policy changes through FortiManager to dozens of devices while maintaining consistency.
The FortiOS 6.2 version question everyone asks
Yeah, FortiOS 6.2 isn't the latest version anymore. We've got 6.4, 7.0, 7.2, and beyond now. But honestly, a ton of enterprises are still running 6.2.x in production because they're conservative about upgrades or they're waiting for certain features to mature in newer releases. I've walked into Fortune 500 companies in 2024 that were still on 6.2 for stability reasons.
The core troubleshooting approach you learn for NSE7_EFW-6.2 applies across versions. Traffic flow logic hasn't fundamentally changed. The diagnostic commands? Mostly the same. Security profile concepts carry over. Where you'll see differences is in specific CLI syntax for newer features, GUI workflows that got redesigned, and new capabilities that didn't exist in 6.2.
If you're studying for NSE7_EFW-7.0 instead, you'll cover SD-WAN integration more heavily and newer security fabric features. But the 6.2 exam is still relevant for many production environments, and the troubleshooting skills translate directly. I actually knew a guy who passed NSE 7 for 6.2 and then walked into an environment running 7.0. He was fine. The principles don't change that much.
Career impact and what doors this opens
NSE 7 Enterprise Firewall 6.2 certification opens senior-level positions that require proven troubleshooting expertise. Job postings for senior security engineers and firewall architects often list NSE 7 as a preferred or required qualification. It shows you're not just configuring firewalls but designing solutions and fixing complex problems.
Salary-wise? Having NSE 7 can bump you into higher compensation brackets because it validates skills that fewer people have compared to NSE 4. Employers and clients recognize that someone with NSE 7 can handle escalations and complex deployments without hand-holding.
It also demonstrates commitment to Fortinet technology mastery. If you're working for a Fortinet partner, having multiple NSE 7 certified engineers can affect your partner tier and the discounts you get. For your career, it signals you're serious about specializing in Fortinet rather than being a generalist who knows a little bit about everything.
How NSE 7 EFW differs from other NSE 7 tracks
Fortinet offers multiple NSE 7 tracks, and they're not interchangeable. The Enterprise Firewall track focuses specifically on FortiGate firewall technologies: policies, NAT, routing, VPNs, security profiles, HA, logging, and troubleshooting. Meanwhile, NSE7_SAC-6.2 covers Secure Access, which deals with FortiAuthenticator and FortiToken for authentication and access control.
There used to be separate NSE 7 tracks for SD-WAN before it got rolled into the newer FortiOS 7.0 Enterprise Firewall exam. Other NSE 7 certifications cover LAN Edge, which focuses on FortiSwitch and secure network access. Each track validates expertise in a different product family or solution area within the Fortinet ecosystem.
If you're a firewall person who spends your days writing policies and troubleshooting traffic flows, Enterprise Firewall is your track. If you're more focused on network access control and authentication, you'd look at different NSE 7 options.
Building your foundation before attempting NSE 7
Most people complete NSE 4 FortiGate Security and Infrastructure before attempting NSE 7, and honestly, that's the smart move. NSE 4 covers the fundamentals: how FortiGate processes traffic, basic policy configuration, common VPN setups, security profiles, and basic HA. You need that foundation solid before you tackle advanced troubleshooting scenarios.
Real-world hands-on experience matters more for NSE 7 than for lower-level certs. If you've never configured a FortiGate in production, never troubleshot a VPN that won't come up, never diagnosed why certain traffic is getting blocked when it shouldn't be, you're gonna struggle with NSE 7. The exam assumes you've been in the trenches dealing with actual problems, not just lab scenarios.
Look, I've seen people try to jump straight to NSE 7 after cramming NSE 4 material for two weeks. Doesn't work. The scenario-based questions require pattern recognition that only comes from experience. You need to have seen enough weird issues that when the exam throws a troubleshooting scenario at you, you recognize the symptoms and know which diagnostic commands to run.
What makes this exam harder than NSE 4
Unlike associate-level certifications that test theoretical knowledge, NSE7_EFW-6.2 emphasizes scenario-based troubleshooting and real-world problem-solving skills. You'll get questions that present symptoms (traffic not flowing, VPN tunnel flapping, HA cluster not syncing sessions) and you need to identify the root cause and the correct diagnostic approach.
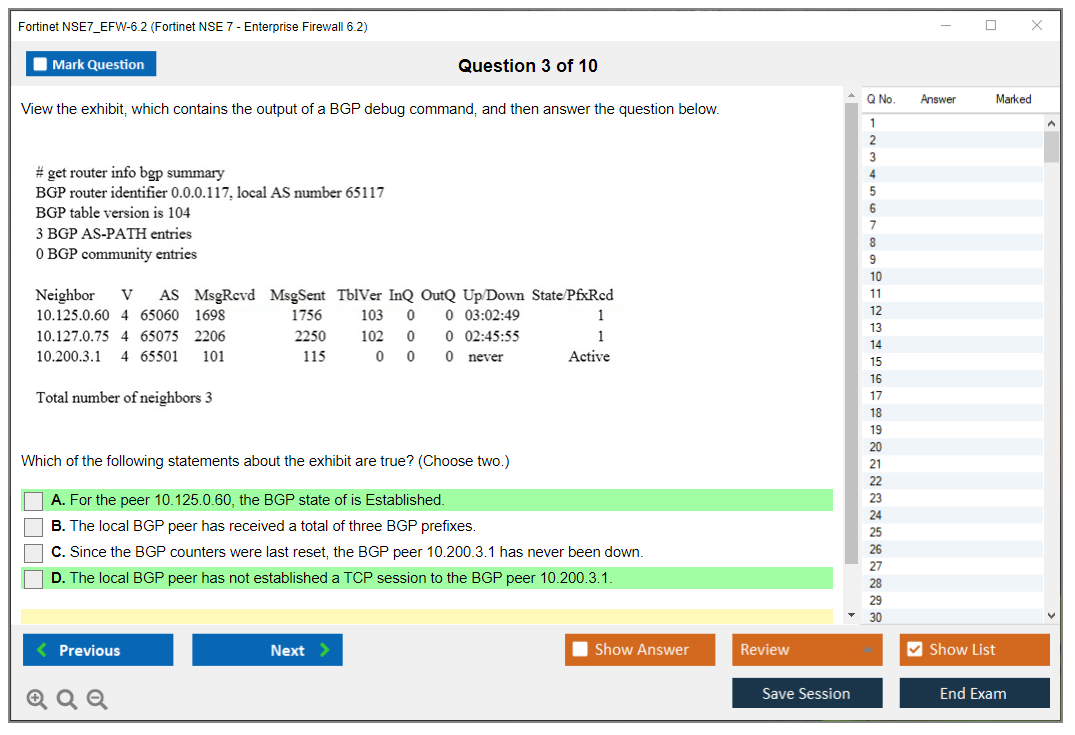
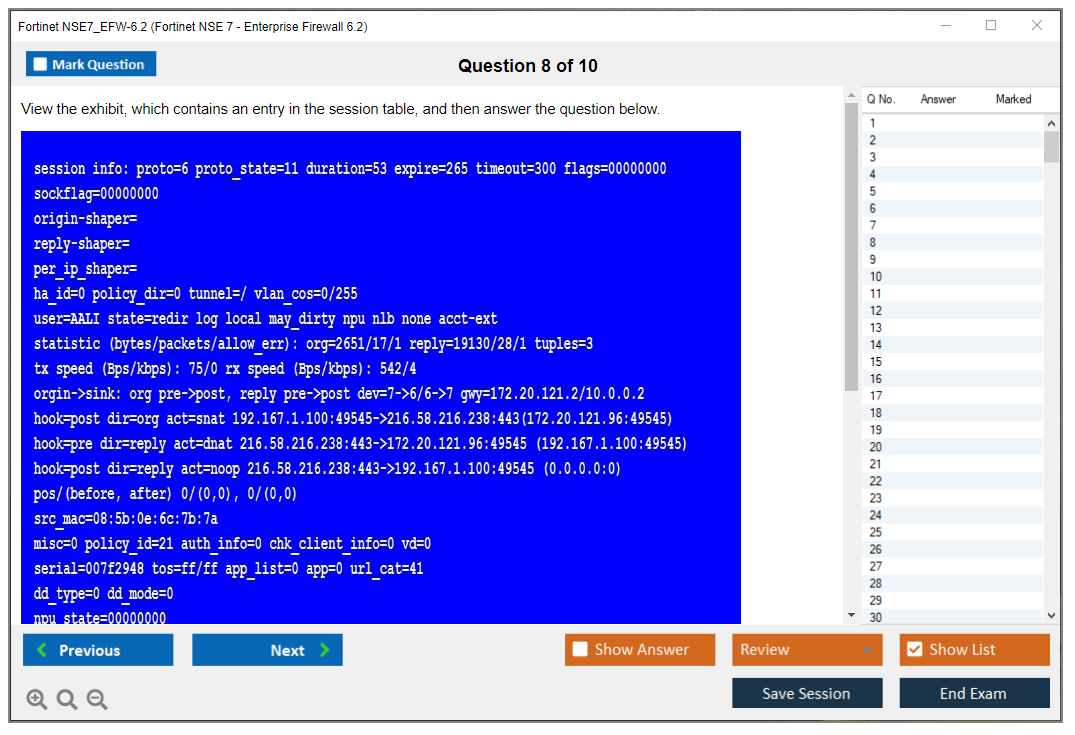
The CLI diagnostics are critical. You need to know commands like 'diagnose debug flow filter' to trace specific traffic, 'diagnose sniffer packet' to capture packets at different points in the traffic flow, and various 'diagnose sys' commands to check system status. You'll need to interpret routing tables, session tables, and policy lookup results.
The exam also tests your understanding of the order of operations. When does the FortiGate perform routing lookups versus policy checks versus NAT versus security profile inspection? Getting this sequence wrong means you'll misdiagnose problems. Understanding packet flow through the FortiGate is absolutely necessary.
Global recognition and industry standing
Fortinet NSE 7 Enterprise Firewall 6.2 certification is recognized worldwide by employers, partners, and customers as proof of advanced FortiGate expertise. Fortinet is one of the top firewall vendors globally, so having deep expertise in their platform matters. Government agencies, financial institutions, healthcare organizations, and enterprises across industries deploy FortiGate, creating demand for certified professionals.
For partners and MSSPs, having NSE 7 certified staff affects your ability to win enterprise deals. Customers often require certified engineers for implementations and ongoing support. The certification gives you credibility in technical discussions and proves you can handle their complex requirements.
Compared to other vendor certifications at similar levels (like Palo Alto Networks PCNSE or Cisco CCNP Security), NSE 7 focuses specifically on advanced Fortinet technologies. If your organization is heavily invested in the Fortinet security fabric, NSE 7 is more directly applicable than a competitor's cert.
NSE7_EFW-6.2 Exam Format and Requirements
What this certification actually proves
The Fortinet NSE7_EFW-6.2 exam (officially titled Fortinet NSE 7 - Enterprise Firewall 6.2) is the one that proves to employers you can actually operate a FortiGate like a professional in an enterprise environment. Not just clicking through the GUI anymore. More like you've gotta explain why traffic suddenly disappeared after some routing change, back it up with packet captures, then fix everything without accidentally destroying the HA setup.
This is about operations. Real networks. Real outages.
What it validates is your capability to implement and troubleshoot FortiOS 6.2 features that actually appear in production environments: FortiOS 6.2 firewall policies and NAT, identity-based access, VPN behavior across multiple hops, plus all the messy stuff like security profiles inspection flow (IPS/AV/Web Filter) where performance and policy logic basically collide head-on. The thing is, it also expects you to be comfortable proving your theory using logs and debugs. Including FortiAnalyzer/FortiManager log analysis for troubleshooting.
Who should take it (and who shouldn't)
This exam targets firewall engineers, senior network/security admins, and consultants who regularly touch FortiGate deployments beyond just a single site. If you're that person who gets the panicked call when "the VPN shows up but absolutely nothing works," you're exactly the target audience.
New to FortiGate? Don't even think about it.
If your day job mostly involves ticket routing and you haven't actually had to chase down asymmetric routing, session pickup weirdness, or VIP hairpin NAT under pressure, honestly, you'll feel this exam pushing back hard. That's the point. I've seen people with solid networking backgrounds still struggle here because FortiGate has its own way of handling traffic flow that doesn't always match what you'd expect from other vendors.
The format, timing, and delivery
Basics first. The exam code is NSE7_EFW-6.2, and Pearson VUE delivers it either as an online proctored exam or at a physical test center.
Here's what you'll encounter: typically 30 to 35 questions. Mostly multiple-choice and multiple-select. Exact count varies by version, so don't get obsessed over whether it's 32 or 34. Get obsessed over whether you can read a scenario and pick the one fix that actually matches FortiOS behavior.
Time? 120 minutes. That works out to roughly 3 to 4 minutes per question, which sounds comfortable until you hit some dense troubleshooting prompt with CLI output, a topology diagram, and four answers that all sound reasonable if you haven't done enough labs.
Closed-book. No notes. No vendor docs. No second monitor with some cookbook pulled up. Test centers usually give you scratch paper or a wipeable board. Online proctoring gives you a digital whiteboard, which is.. fine. Clunky, but fine.
Question styles you'll get
Expect scenario-heavy prompts. Not trivia. You'll see:
- Scenario-based multiple choice where you diagnose traffic flow issues
- Multiple select "choose all that apply" questions, and yeah they're absolutely unforgiving
- Troubleshooting questions that include CLI output (think routing tables, debug flow snippets, IPsec status) or a simple topology diagram
The "gotcha" rarely feels like a cheap trick. It's usually one missing detail. Like policy order, route preference, or inspection mode. That completely changes the entire answer.
Exam cost and regional pricing reality
The NSE7_EFW-6.2 exam cost runs about $400 USD. That's the number most people quote, and it's a decent planning estimate.
Now for the annoying part. Pricing varies significantly by region and test center, and some places tack on VAT or local taxes. EMEA often looks higher on the receipt because of tax handling. APAC can swing wildly depending on country. Latin America can be all over the place because of local pricing rules and currency conversions. So yeah, definitely check the Fortinet Training Institute portal and Pearson VUE checkout in your currency before you expense it and get surprised.
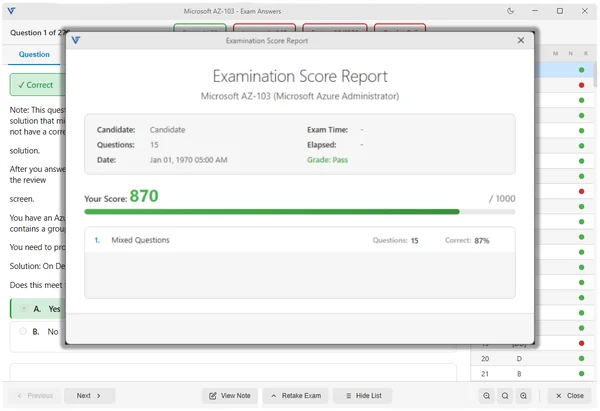
Passing score and how scoring works
Everyone asks about the NSE 7 EFW 6.2 passing score. Fortinet doesn't publicly disclose exact passing scores for NSE 7 exams, and they won't give you a detailed score report. You get pass or fail. That's it.
Scoring-wise, treat every question as equal weight. Also, no partial credit on multiple-select. If it says choose two and you pick one correct and one wrong, that's a miss. Brutal, but it matches how these questions are written. They're testing whether you can be precise under pressure.
Immediate results show on screen right when you finish. Certificate delivery is digital, and it typically shows up in the Fortinet Training Institute portal within 24 to 48 hours after you pass.
Retakes, waiting period, and the pain factor
Fail it? You wait 15 days before retaking. And yes, you pay the full fee again. No discounted second attempt.
Not gonna lie, that waiting period is actually a gift if you use it correctly. It forces you to fix the weak areas instead of rage-booking the next slot and repeating the same mistakes.
Language availability and scheduling
Most people take it in English. It's also offered in Japanese, plus select other languages depending on region and demand.
Scheduling? Pretty flexible. Pearson VUE test centers often offer appointments seven days a week, and online proctoring is available 24/7 in many regions. If you work weird hours, online delivery is definitely the move, assuming your home setup won't get you flagged.
What you'll be tested on (the real objectives)
If you're using an NSE7_EFW-6.2 study guide or reviewing the NSE7_EFW-6.2 exam objectives, these are the buckets that matter.
Policies and NAT behavior
You need comfort with policy order, implicit denies, and NAT logic without just "trying stuff until something works." Central NAT vs policy NAT shows up constantly in real life. The exam loves scenarios where a VIP exists but traffic still fails because the matching policy or interface pair is wrong.
Spend time on VIPs, VIP groups, policy matching, and how UTM profiles attach to policies. Also, understand what changes when you flip between flow-based and proxy-based features in the inspection path.
Identity, auth, and access control
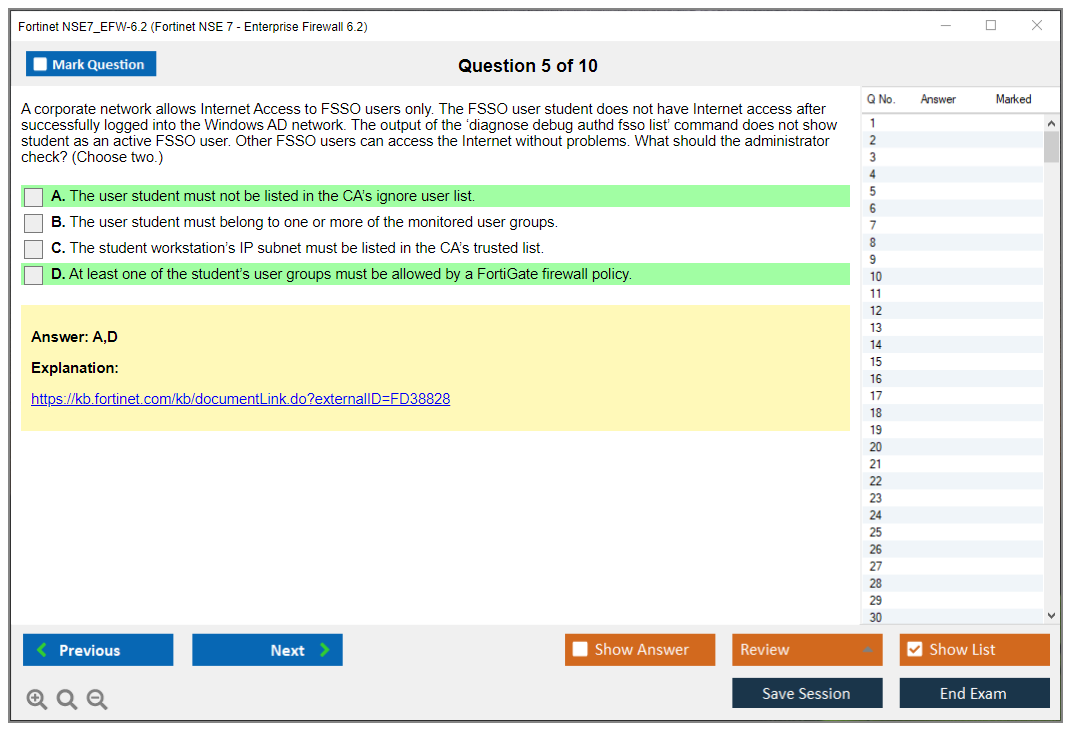
Identity-based policies. FSSO concepts. Local users vs remote auth. What happens when authentication is required but the traffic isn't browser-friendly. Captive portal behavior. Group matching. Edge cases.
You don't need to memorize every single knob. You do need to know what to check first when a user "can't get out" but the policy looks correct.
Routing and advanced networking
Static routes, policy routes, dynamic routing basics, and what happens when you introduce a second path and forget how FortiGate chooses routes.
This is where FortiGate routing and VPN troubleshooting overlaps hard with firewall policy logic. The firewall can have the perfect rule and still drop traffic due to return path issues, SD-WAN decisions, or route distance.
VPNs and troubleshooting
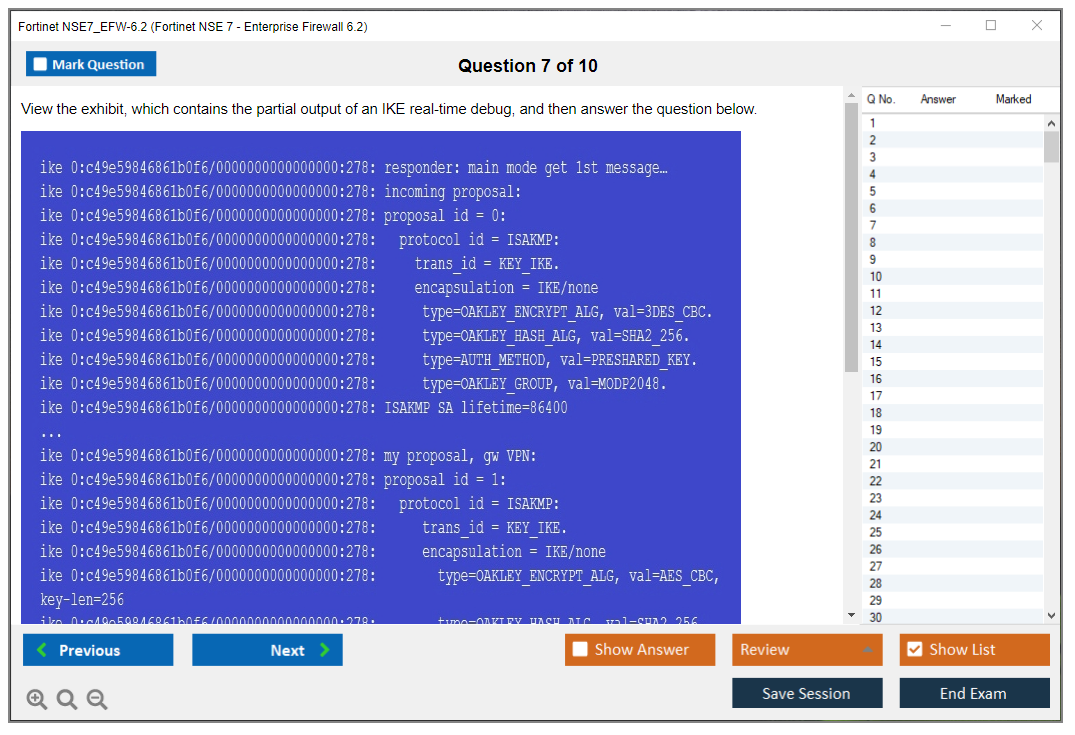
IPsec? Core theme. Phase 1/2 mismatches, selectors, NAT traversal, DPD behavior, and multi-hop scenarios where the tunnel is up but the subnets don't actually pass.
SSL VPN can appear too, but the heavier lift is usually IPsec plus routing plus policy. The exam loves "tunnel is established" screenshots followed by "users still can't reach app." That's exactly what happens in production, by the way.
Security profiles and inspection flow
This is where people burn serious time. You need to understand how security profiles inspection flow (IPS/AV/Web Filter) impacts sessions, what logs you expect to see, and what changes when you add SSL inspection.
Performance tuning under inspection load is part of the difficulty too. You'll see questions that basically ask "what's the least bad option" when you need security controls but throughput matters.
HA and resiliency
Know HA clustering and session synchronization at a practical level. A-P vs A-A, what gets synced, what breaks failover expectations, and why a failover can look clean but still drop certain sessions.
HA questions often hide the answer in one detail. Like mismatched interface monitoring, link failure detection, or session pickup settings.
Logging, monitoring, and CLI diagnostics
CLI? Not optional here. You should be able to interpret debug flow output, sniffers, routing tables, and IPsec status commands.
Also, logs. Especially if you're using centralized tools. FortiAnalyzer/FortiManager log analysis for troubleshooting matters because the exam expects you to know where to confirm your hypothesis, not just guess.
Prereqs (official vs what you really need)
Officially, there are no hard prerequisites. Realistically, Fortinet recommends NSE 4 knowledge and about 2 to 3 years of hands-on FortiGate admin experience.
If you've never built policies from scratch, tuned UTM profiles, or troubleshot VPNs with CLI output, this isn't the exam to "see how it goes."
Quick skills checklist before you book
Be comfortable reading CLI output fast. Know the traffic flow. Have a repeatable troubleshooting method. Understand enterprise change side-effects.
That's your baseline.
Best study materials that don't waste your time
Official training that maps to the exam
Start with the official NSE7_EFW-6.2 training course material from the Fortinet Training Institute. It fits with how Fortinet phrases features and scenarios. That phrasing matters on test day, even if you disagree with it.
Docs worth prioritizing
If you're gonna read docs, focus on FortiOS 6.2 admin guides, cookbooks, and release notes for the features you actually touch. Release notes sound boring, but they explain behavior changes. Behavior changes are where troubleshooting questions come from.
Labs and hands-on practice
A FortiGate VM lab is the best ROI. Build a few topologies. Break them on purpose. Capture the debug flow and sniffer outputs so you stop treating CLI as some magic incantation and start treating it like evidence.
Practice tests and how to use them without fooling yourself
An NSE7_EFW-6.2 practice test is useful only if you review wrong answers by objective and recreate the scenario in a lab when possible. Memorizing question patterns is how people feel confident and then fail anyway.
Spend extra time on the topics that create "almost right" answers. NAT+VIP matching, route selection, and IPsec traffic selectors.
Exam day expectations (online and test center)
Online proctoring requires stable internet connection, webcam, mic, and a quiet private room. You do a system check before the exam. Clear your desk. No extra screens. Don't mumble to yourself while reading because proctors can interpret that as "talking."
Time management matters. If you hit a long scenario, decide fast whether you can solve it now. Flag it and move if you're stuck. Missing easy questions because you got lost in one IPsec rabbit hole is the classic fail pattern.
Certification validity and renewal
NSE 7 certifications are valid for two years from the date you pass. After that, you recertify to keep it active, and the exact rules can change, so always confirm on the official Fortinet certification policy page before you plan your renewal.
Version drift? Real. FortiOS moves fast. Studying 6.2 while your job runs 7.x means you've gotta be extra careful about using the right docs and not answering based on newer behavior you've gotten used to.
FAQ
How much does the NSE7_EFW-6.2 exam cost?
About $400 USD, but regional pricing varies, and some countries add VAT or local taxes. Check Pearson VUE checkout for your exact total.
What is the passing score for NSE7_EFW-6.2?
Fortinet doesn't publish a fixed passing score for NSE 7 exams. You receive an immediate pass/fail result after finishing.
Is NSE 7 Enterprise Firewall 6.2 difficult?
Yes. It's considered one of the tougher Fortinet exams because it leans heavily on troubleshooting, CLI diagnostics, HA behavior, and complex traffic flow analysis.
What are the best study materials for NSE7_EFW-6.2?
Start with official Fortinet Training Institute materials, then back it up with FortiOS 6.2 docs, and labs using FortiGate VM. A good NSE7_EFW-6.2 study guide helps, but hands-on practice is what makes the questions feel "fair."
How do I renew the Fortinet NSE 7 certification?
NSE 7 is valid for two years, and renewal is done by recertifying under Fortinet's current program rules. Confirm the current policy on the Fortinet Training Institute site before your certification expires.
Detailed NSE7_EFW-6.2 Exam Objectives
Understanding what you're actually signing up for
The Fortinet NSE7_EFW-6.2 exam isn't your typical "memorize some commands and pass" certification. This is advanced-level stuff that validates you can actually troubleshoot enterprise FortiGate deployments running FortiOS 6.2, design complex firewall policies, and handle the kind of problems that wake you up at 3 AM. Honestly, the scenarios they throw at you are pulled straight from real network emergencies where everything's on fire and management's breathing down your neck.
The exam assumes you already know the basics. Still figuring out how interfaces work? You should probably step back and get comfortable with NSE4_FGT-7.2 material first.
The certification targets network security engineers, firewall administrators, and security architects who work with FortiGate devices daily. Not the people who just monitor dashboards. I'm talking about folks who get called when VPN tunnels won't establish, when traffic isn't flowing as expected, or when someone needs to implement identity-based policies across a multi-site deployment and everything has to work perfectly by Monday morning. (I once watched a colleague spend an entire weekend tracing a routing asymmetry issue that turned out to be a stale ARP entry on a switch nobody knew existed, but that's another story.)
What the test format looks like
The NSE7_EFW-6.2 exam consists of 30 scenario-based questions. You get 90 minutes to complete it. That's three minutes per question, which sounds like plenty until you're reading through a five-paragraph scenario describing a broken VPN setup and you need to identify the exact configuration issue from four plausible answers. Multiple choice questions, sure. But they're the kind that require you to actually understand the technology rather than just recognize keywords.
Fortinet delivers the exam through Pearson VUE testing centers or online proctoring. The online option's convenient, but make sure your testing environment meets their requirements because getting kicked out mid-exam for a background noise violation? Not fun.
How much this'll cost you
The exam cost for NSE7_EFW-6.2 typically runs around $400 USD, though pricing varies by region and gets adjusted periodically. Pearson VUE handles the payment. Yeah, that's not cheap. Some employers will cover the cost if you're pursuing it for work, which is worth asking about before you drop your own money on something that might not even benefit your current role. The price includes one attempt. If you fail, you're paying again for a retake, so make sure you're actually ready before scheduling.
What score you need to pass
Here's where Fortinet gets a bit opaque. They don't publicly announce a specific passing score for most NSE exams, including this one. The score report you get after the exam shows your performance by domain rather than giving you a straightforward percentage. From what I've seen in the community, you're looking at needing around 70-75% to pass, but Fortinet reserves the right to adjust the cut score based on exam difficulty and psychometric analysis. Not the most transparent approach.
Why this exam's really difficult
The NSE 7 Enterprise Firewall 6.2 is challenging for a few specific reasons. First, the scenarios are realistic and messy. You'll get questions where multiple things could be wrong, and you need to identify the most likely culprit based on limited diagnostic output. Second, FortiOS 6.2 has specific behaviors and command syntax that differ from newer versions, so if you've been working primarily with FortiOS 7.x, you'll need to consciously study the 6.2 documentation.
Third, and this is critical, troubleshooting methodology matters more than rote memorization because you need to understand the flow of traffic through the firewall, the order of operations, how each component interacts, and why certain configurations produce unexpected results in edge cases that you've probably never encountered in production environments.
Firewall policies and NAT configurations that actually matter
Policy evaluation order's fundamental, and it trips people up constantly. FortiGate processes policies top-down, first-match wins. Seems simple until you have 200 policies and traffic's matching policy 47 when you expected it to match policy 180. The implicit deny rule at the bottom catches everything else, but you'll also encounter implicit rules for certain traffic types that don't show up in the policy list.
Central NAT (CGNAT) changed the game for how NAT's configured in FortiOS 6.2 and later. Instead of embedding NAT configuration directly in firewall policies, you can configure separate central SNAT and DNAT rules that apply after policy matching. Makes policy management cleaner. Lets you change NAT behavior without touching firewall policies. The exam'll definitely test your understanding of when central NAT rules are processed versus policy-based NAT, and how to troubleshoot when traffic isn't getting translated as expected.
Virtual IPs and IP pools? Another area where theory meets painful reality. Port forwarding with VIPs, one-to-one NAT, server load balancing VIPs.. each has specific use cases and configuration requirements. Debugging VIP translation issues typically involves diag debug flow and checking whether the VIP's even matching the incoming traffic. Hairpin NAT scenarios, where internal users try to reach internal servers using the external IP, require specific policy configurations that many people get wrong.
Policy consolidation using address objects, service objects, and wildcard FQDN addresses helps keep policy counts manageable. Dynamic address objects that pull from threat feeds are powerful but need to be understood in terms of update frequency and how they affect existing sessions.
Identity-based policies and authentication integration
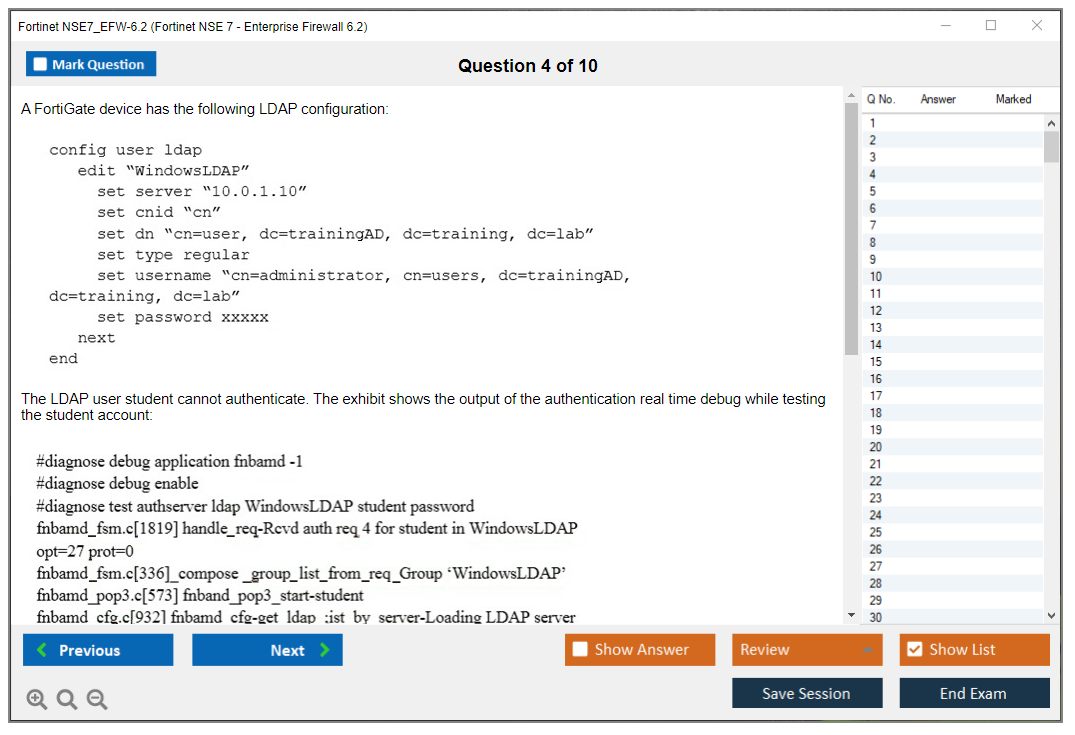
Integrating FortiGate with authentication sources is where security gets personalized. LDAP, RADIUS, TACACS+, SAML SSO, and FSSO each have different architectural requirements and use cases. FSSO's particularly important for Windows environments. The DC Agent or Collector Agent polls Active Directory or uses WMI to discover which users are logged into which workstations, then pushes that identity information to FortiGate. When FSSO isn't working? Usually DNS resolution problems. Or firewall rules blocking the collector. Sometimes permissions issues on the DC Agent.
Creating identity-based firewall policies means your rules match authenticated users or groups rather than just source IP addresses. This is huge for environments where IP addresses are dynamic or shared. The thing is, you can't just rely on static IP assignments anymore when everyone's working remotely or moving between conference rooms with their laptops. The exam'll test your knowledge of how authentication happens, how user identity's maintained, and what happens when a user's session expires.
Guest portals and captive portal configurations come up often in enterprise scenarios. You need to understand the workflow: unauthenticated user hits the firewall, gets redirected to a captive portal, authenticates or accepts terms, then gets access based on which user group they're in. Customizing portal appearance's less important for the exam than understanding the underlying authentication flow and troubleshooting why users can't get past the portal.
Certificate-based authentication and MFA? Increasingly common requirements. PKI integration, client certificate validation, OCSP/CRL checking for certificate revocation.. these're all testable topics. Multi-factor authentication with FortiToken or RADIUS-based MFA adds another layer, and you need to know how to configure it for both admin access and VPN users.
Routing and networking complexity
Static routing on FortiGate includes administrative distance, route priority, and redundant path configurations. Blackhole routes for preventing routing loops or null-routing malicious destinations are useful in specific scenarios. The exam assumes you understand how route selection works when multiple routes to the same destination exist.
Dynamic routing protocols like OSPF and BGP on FortiGate behave mostly like you'd expect if you have routing experience, but there're FortiGate-specific considerations around how routes are injected into the routing table and how route redistribution works between protocols. Policy-based routing lets you override the routing table based on source, destination, service, or incoming interface. Critical for multi-ISP environments where you want certain traffic to use specific WAN links.
SD-WAN in FortiOS 6.2 was still relatively early in its evolution compared to 7.x, but the basics're there: defining SD-WAN interface members, setting up performance SLAs to monitor link health, and creating traffic steering rules to intelligently route traffic based on application, performance requirements, or link availability. Won't go deep into advanced SD-WAN features, but you need the fundamentals.
VRF (virtual routing and forwarding) and VDOMs both let you create multiple routing tables on a single FortiGate, but they work differently and have different use cases. Route leaking between VRFs? Common requirement when you need limited connectivity between isolated routing domains.
VPN technologies and the art of troubleshooting tunnels
IPsec VPN troubleshooting's a massive portion of what you'll face. Phase 1 negotiation establishes the IKE SA, Phase 2 establishes the IPsec SA. When a tunnel won't come up, you need to systematically check: Phase 1 proposals (encryption, hashing, DH group, authentication method), Phase 2 proposals, pre-shared keys or certificate validation, NAT-T if there's NAT in the path, routing on both ends, and firewall policies that allow tunnel traffic. The commands diag debug application ike -1 and diag vpn tunnel list become your best friends.
Site-to-site IPsec VPN in hub-and-spoke topologies? Standard stuff. Redundant tunnels, dynamic routing over IPsec. These're standard enterprise deployments. ADVPN (Auto Discovery VPN) allows spoke-to-spoke tunnels to establish dynamically without requiring full-mesh configurations, which is elegant when it works and a nightmare when it doesn't.
SSL VPN in web mode and tunnel mode offers clientless or full tunnel access respectively. Portal customization, bookmarks for web mode, and deploying the FortiClient SSL VPN client for tunnel mode're all fair game. Per-user and per-group access control using portal assignments is how you give different user populations different levels of access.
VPN performance optimization involves choosing appropriate encryption algorithms. AES-GCM's faster than AES-CBC with separate HMAC. Enabling hardware acceleration when available, and adjusting MTU/fragmentation settings to prevent performance-killing fragmentation.
Security profiles and inspection that slows everything down
Security profiles're where FortiGate does deep packet inspection. Antivirus, IPS, Web Filtering, Application Control, DNS Filter, and DLP each scan traffic for different threats. The inspection mode (proxy-based versus flow-based) dramatically affects what features're available and how much performance impact you'll see. Proxy-based inspection terminates the connection, fully reassembles content, and inspects it, which is thorough but slower. Flow-based inspection examines traffic as it passes through without full reassembly. Faster but less thorough.
SSL/TLS inspection's critical for catching threats in encrypted traffic, which is most traffic these days. Certificate inspection mode just looks at the certificate metadata, while full SSL inspection decrypts, inspects, and re-encrypts the traffic. This requires uploading a CA certificate to client devices so they trust the FortiGate's re-signed certificates, which raises privacy and legal considerations in some organizations.
The inspection sequence matters. Traffic flows through profiles in a specific order, and understanding this helps diagnose why traffic's being blocked. Generally it goes AV, Web Filter, Application Control, IPS, DLP, though the exact flow depends on inspection mode and which profiles're enabled.
Tuning IPS profiles to reduce false positives while maintaining security's an ongoing challenge. Signature selection, custom signatures for application-specific threats, rate-based signatures for detecting scanning behavior.. all testable topics. Web filtering categories, URL filtering, and application control that identifies applications regardless of port or protocol're standard enterprise requirements.
The performance impact of enabling multiple security profiles simultaneously? Significant. CPU utilization spikes, throughput drops, latency increases. The exam'll test your understanding of these tradeoffs and how to optimize profile assignments for performance without sacrificing necessary security.
High availability when you can't afford downtime
HA clustering in active-passive or active-active modes provides redundancy. Active-passive's simpler: one unit handles all traffic, the other sits idle until failover. Active-active distributes load but requires more careful configuration. Configuration requirements include identical hardware models, same FortiOS version, and dedicated HA heartbeat interfaces for synchronization.
Session synchronization ensures that established sessions survive failover in active-passive clusters. Not all session types're synchronized. IPsec VPN sessions, for instance, have their own sync mechanisms. The performance impact of session sync's real, especially in high-session-count environments.
Failover triggers include interface monitoring (if a monitored interface fails, trigger failover), chassis failure, and manual failover for maintenance. Troubleshooting HA involves checking heartbeat connectivity, configuration sync status, and diagnosing split-brain scenarios where both units think they're primary.
Virtual clustering with VDOMs lets you assign different VDOMs to different cluster members, enabling active-active operation at the VDOM level even on hardware that doesn't support full active-active clustering. HA with FortiGate VMs in cloud environments like AWS or Azure requires special consideration: unicast HA instead of multicast, using SDN connectors for failover automation, and understanding the limitations of cloud networking.
Logging and diagnostics that save your sanity
FortiGate generates multiple log types: traffic logs for allowed/denied sessions, event logs for system events and admin actions, and security logs for AV detections, IPS blocks, web filtering blocks, etc. Local logging's limited by disk space. Enterprise deployments typically send logs to FortiAnalyzer for centralized storage and analysis.
Configuring FortiAnalyzer integration involves setting up reliable or real-time logging mode, configuring log encryption if required, and troubleshooting connectivity issues when logs aren't uploading. FortiView dashboards provide quick visual summaries of traffic patterns, top sources/destinations, threats detected, and bandwidth usage.
CLI diagnostic commands're essential for troubleshooting. The diag debug flow command shows you exactly how the firewall's processing a specific traffic flow: which policy it matches, whether NAT's applied, routing decisions, and why traffic might be dropped. Interpreting debug flow output's a skill you absolutely need for this exam.
The diag sniffer packet command lets you capture traffic on any interface, apply filters to narrow down what you're capturing, and save the output for analysis in Wireshark. Knowing when to use sniffer versus debug flow, and how to construct useful filters? Critical for efficient troubleshooting.
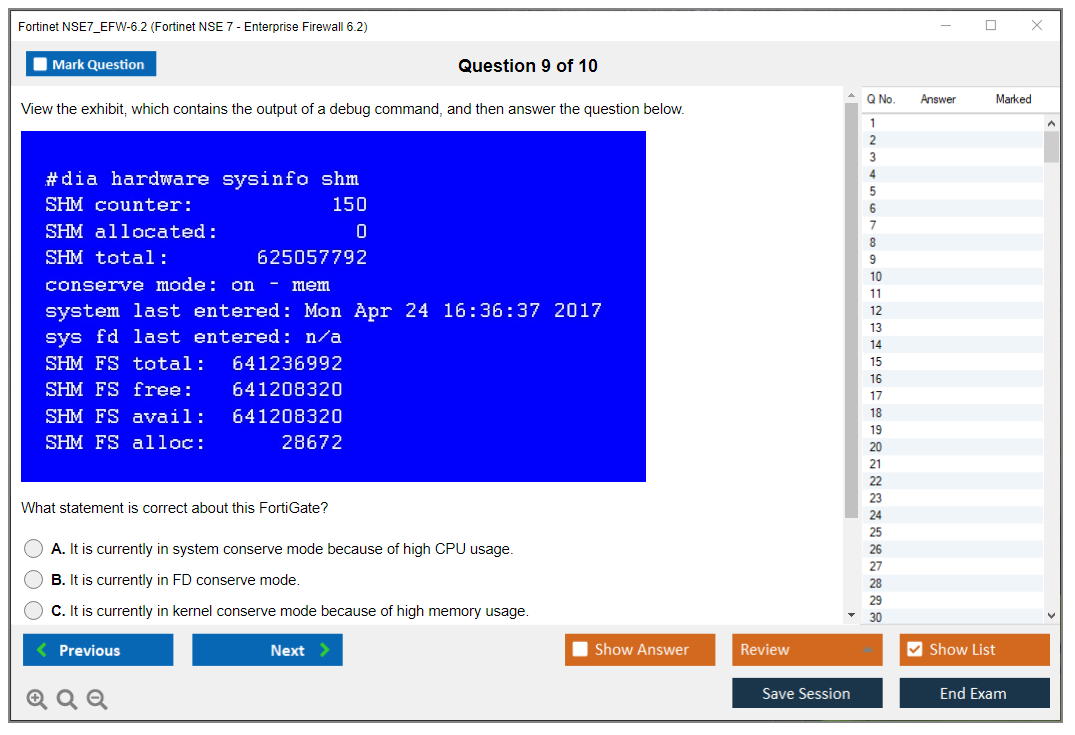
Performance monitoring (CPU, memory, session counts, bandwidth utilization) helps identify bottlenecks. The command get system performance status gives you a quick overview, and more detailed diagnostics can pinpoint whether you're hitting CPU limits, memory exhaustion, or session table exhaustion.
Actually preparing for this exam
If you're serious about passing, you need hands-on practice with FortiOS 6.2 specifically. Download a FortiGate VM. Build lab scenarios. Break things, fix them. The NSE7_EFW-6.2 Practice Exam Questions Pack at $36.99 gives you scenario-based questions that mirror the actual exam format, which is honestly worth the investment if you want to test your readiness before spending $400 on the real thing.
Study the FortiOS 6.2 administration guide cover to cover. Not gonna lie, it's dry reading. But it's the authoritative source. Fortinet's official training courses're good if you have access, though they're expensive unless your employer's paying. Cookbooks and feature-specific documentation fill in gaps the admin guide glosses over.
The troubleshooting methodology matters as much as technical knowledge. When you hit a scenario question, think systematically: what's the expected behavior, what's the actual behavior, what could cause that discrepancy, how would you verify each possibility? The exam rewards this structured approach over random guessing.
Common mistakes? Overthinking questions. Second-guessing correct answers. Running out of time because you spent too long on early questions. Budget your time, mark difficult questions for review, and don't let one hard question derail your entire exam.
Keeping your cert current
Fortinet's recertification requirements change periodically, so check their official certification program page for current renewal policies. Generally, NSE 7 certifications require periodic renewal through continuing education or re-examination. FortiOS versions evolve quickly. 6.2's several major versions behind current releases, so even if your certification's valid, your practical knowledge needs updating as new features and changes're introduced.
If you're planning to pursue NSE7_EFW-7.0 or other advanced Fortinet certifications, the concepts you learn for NSE7_EFW-6.2 transfer well, though you'll need to study version-specific changes. The troubleshooting skills and systematic approach're timeless, even when commands and features evolve.
Prerequisites and Recommended Experience for NSE7_EFW-6.2
Fortinet NSE7_EFW-6.2 (NSE 7, Enterprise Firewall 6.2) overview
The Fortinet NSE7_EFW-6.2 exam is the "you'd better know what you're doing in production" checkpoint. It's not theory. And it's definitely not about memorizing where buttons live in the GUI. This exam tests advanced troubleshooting plus design decisions on FortiOS 6.2 behavior, where one dumb assumption about policy order, routing tables, or how inspection flow actually works can ruin your entire outage call and make you look clueless.
What the Fortinet NSE 7 Enterprise Firewall 6.2 certification validates is straightforward enough: you can keep enterprise firewall services running when everything's on fire, and you can explain what broke using logs, CLI output, packet captures instead of just waving your hands around and hoping nobody asks follow-up questions. That's what hiring managers actually want when they say "senior firewall engineer."
Typical job roles? Senior network security engineer. FortiGate admin who owns multiple sites. Escalation engineer at an MSP. Anyone who gets tagged when "VPN is down" or "apps are timing out" becomes a business emergency. Not entry level.
NSE7_EFW-6.2 exam details
Exam format: Fortinet exams in this track usually go with multiple choice and multiple select, delivered through Pearson VUE. Testing center or online proctored depending on region and what's actually available when you book. Time and question count? They can change between versions, so treat any third-party numbers like a rumor and check the current listing when you actually book. Also, scenario questions are the real time sink. Short questions exist, sure, but the long ones eat minutes like crazy.
Exam cost
As of recent Pearson VUE pricing for Fortinet, many candidates see USD $400 as the list price for NSE 7 exams, but it varies with country, currency conversion, taxes, and whatever Pearson's doing locally that week. Some regions show equivalent pricing in EUR/GBP/AUD, and a few employers have voucher deals that change the out-of-pocket number completely. If you want the exact NSE7_EFW-6.2 exam cost, check the exam's page on Fortinet Training Institute and then the price at checkout in Pearson VUE for your specific region.
Passing score
People always ask the NSE 7 EFW 6.2 passing score, and here's the annoying answer: Fortinet typically doesn't publish a universal fixed score across all their exams, and scoring models can vary between exam versions and delivery methods. So you can't reliably aim for "X%". You aim for "I can troubleshoot this cold, no notes, at 3 a.m." Confirm whatever Fortinet publishes in the official exam description because that's the only source that actually matters.
Difficulty
Is it hard?
Yeah.
The difficulty comes from depth, not trick questions or weird gotchas. You need to understand how FortiOS actually processes traffic in its guts, how routing decisions interact with policy lookup sequencing, how security profile inspection changes flow behavior in unexpected ways, and how to prove your theory with CLI output instead of guessing. If you've only ever clicked around the GUI and copied a working template from some blog, the FortiGate 6.2 enterprise firewall exam feels like a brick wall to the face.
I once watched a colleague who was brilliant with ASA configurations completely freeze during troubleshooting because FortiOS processes packets differently than he expected. Different order of operations. Different logging behavior. He kept looking for Cisco-style outputs that just don't exist in FortiGate. Took him three tries to pass because he had to unlearn assumptions first.
NSE7_EFW-6.2 exam objectives (what you'll be tested on)
Treat the NSE7_EFW-6.2 exam objectives like your map. If your "study guide" doesn't map to them, it's entertainment, not prep. A decent NSE7_EFW-6.2 study guide should keep pulling you back to "can I troubleshoot this scenario under pressure" instead of "can I define this term on a flashcard."
Firewall policy and NAT basics that still trip people
You're expected to be fluent in FortiOS 6.2 firewall policies and NAT. Policy order. VIP behavior that doesn't match what you think it should do. Central NAT versus policy-based NAT. The weird stuff, like when you think you fixed NAT but you're actually matching a different policy due to interface pair assumptions and implicit ordering you forgot about.
One detail I see people miss constantly: once you're troubleshooting in production, you stop thinking "I configured it right" and start thinking "what policy is actually matching this traffic right now." That means checking hit counts, confirming the incoming interface matches what you expect, and verifying the route lookup happened the way you assumed. A correct policy that never matches is basically fan fiction.
Authentication, users, and identity-based policies
Identity-based policies, FSSO concepts, external auth like AD and RADIUS show up a lot in real life. Same on the exam. The point isn't "can you join a FortiGate to AD," which is basic. The point is "can you tell whether auth is the actual problem or just the thing everyone's blaming because they don't understand the policy logic."
Strong routing chops matter here. Static routing is table stakes. OSPF and BGP understanding is where the senior level starts, especially when asymmetric routing and SD-WAN-ish path choices start messing with sessions in ways that make no sense until you draw it out. VLAN tagging, subnetting without a calculator, basic network troubleshooting discipline. No shortcuts.
IPsec is a major theme, and FortiGate routing and VPN troubleshooting is a lifestyle for many FortiGate admins at this point. Phase 1 versus Phase 2 mismatches. Proposals. Lifetimes. Selectors that don't match what the other side expects. DPD. NAT-T. Routing to the tunnel interface properly. SSL VPN basics can appear too, but IPsec is the constant headache.
If you can't look at ike debug output and quickly say "this is proposal mismatch" or "this is peer ID/auth failure," you're going to burn time. Lots of it. Embarrassingly lots.
Expect questions around the security profiles inspection flow (IPS/AV/Web Filter), plus application control behavior and SSL inspection weirdness. This is where people who "always turn on the default profile and call it a day" get punished hard, because troubleshooting requires you to know what gets scanned where in the order of operations, what certificate issues look like to end users, and how deep inspection fundamentally changes the story.
High availability and resiliency
HA is not optional knowledge at this level. Period. You need comfort with HA clustering and session synchronization, failover behavior when things go sideways, and what breaks catastrophically when config sync is off or when monitors are misconfigured. Also, diagnosing "it failed over and now half the sessions are dead and users are screaming" is very much an NSE 7 style headache.
Logging, monitoring, and diagnostics
CLI diagnostics are the heart of it. Debug flow. Sniffer. Session table checks. Routing table verification. VPN status. Log interpretation without guessing. Also worth calling out: FortiAnalyzer/FortiManager log analysis for troubleshooting can appear because enterprise setups centralize management and logging, and you need to understand what those tools are showing you versus what the FortiGate is actually doing in the kernel.
Prerequisites and recommended experience
Fortinet does not mandate formal prerequisites for the Fortinet NSE7_EFW-6.2 exam. No hard gate. No required cert chain blocking your registration. But they strongly recommend you complete NSE 4 FortiGate Security and NSE 4 FortiGate Infrastructure first, and that recommendation is there to save you money and frustration, not to sell more exams.
Why NSE 4 is the foundation
NSE 4 covers the day-to-day fundamentals: basic FortiGate setup, firewall policies that actually work, NAT basics that don't break applications, VPN configuration, and security profiles. That stuff is not "beginner" if you do it properly with real requirements, but it is baseline operational knowledge, and NSE 7 assumes you already know it so well that you can troubleshoot it blind at 2 a.m. while someone is breathing into the bridge line asking for ETAs.
Here's the big gap people don't get: NSE 4 is often "can you configure this feature." NSE 7 is "can you prove why it's broken using evidence." That means you're working backward from symptoms, logs, and packet behavior, and you're expected to understand the processing path well enough to predict what you should see next if your theory is correct.
Hands-on experience requirement (the part people ignore)
Minimum 2 to 3 years of real-world FortiGate administration is what I recommend if you're trying to pass without brute-force memorization and dump sites. Candidates without substantial hands-on time typically struggle with scenario-based questions because you can't fake pattern recognition. You either know what debug flow output looks like when the route is wrong, or you don't and you're guessing.
And look, "hands-on" means you owned tickets, not watched someone else own tickets. You did upgrades. You dealt with outages where management wanted answers yesterday. You changed policies and then cleaned up the mess when an app team said "it worked yesterday, what did you break." Watching videos is fine for concepts but it's not the same as fixing production at all.
FortiOS 6.2 familiarity
Direct experience with FortiOS 6.2.x deployments is ideal because little differences matter in troubleshooting scenarios. If you've worked in 6.0 or 6.4 extensively, a lot transfers between versions. Concepts stay consistent. Commands often stay the same. But the exam is version-pinned to 6.2, so read 6.2 docs and release notes anyway because exam writers absolutely love version-specific behavior and edge cases.
CLI comfort level (non-negotiable)
NSE 7 heavily stresses CLI diagnostics, so if you're not comfortable here, you're going to suffer. You should be comfortable moving around the FortiGate CLI quickly, checking config without scrolling for five minutes, running debug commands without looking up syntax every time, and interpreting output without relying solely on the GUI to translate for you. If you need the GUI to find everything, you'll feel slow and lost when the question drops a CLI snippet and asks what it means.
Get used to the rhythm: verify route, verify policy match, verify session, sniff traffic if needed, then debug flow if you're still confused. Not always in that exact order, but you need a repeatable troubleshooting method you can execute under time pressure.
Enterprise deployment exposure
Experience with complex deployments is a force multiplier here: multi-site VPNs, HA clusters in active-active or active-passive, segmentation with VLANs/VDOMs depending on environment, and integrating auth sources like AD and RADIUS without breaking everything. These are the setups where "simple rules" stop working and you learn what FortiOS really does under the hood. Also the setups where exam scenarios tend to live, because they're more interesting than "single firewall, flat network, one policy."
Networking fundamentals and security concepts
Strong TCP/IP knowledge is the base layer you can't skip: routing, ARP, MTU issues, asymmetric routing symptoms, DNS weirdness, and general troubleshooting discipline. Add routing protocols like OSPF and BGP, VLAN trunking, subnetting without needing a calculator, and you're in the right zone for this level.
Security-wise, you need comfort with common threats, IPS/IDS principles beyond buzzwords, malware types, web filtering goals that make sense, and basic best practices. Not marketing buzzwords but practical understanding. Why you'd block something, where you'd inspect traffic, what false positives look like in real life, and how SSL inspection changes absolutely everything about troubleshooting.
Skills checklist before you start
If you're thinking about booking the exam, ask yourself a few blunt questions and be honest with the answers:
Can you configure firewall policies from CLI without the GUI?
Can you interpret debug flow output and explain where a session died and why?
Can you troubleshoot IPsec Phase 1 and Phase 2 negotiations from logs and debugs without Googling every error code?
Can you diagnose HA failover issues and tell whether it's link monitoring, split brain, or session sync behavior causing the problem?
If most of those are "not really" or "maybe with documentation open," get more hands-on time first. Not because you're not smart enough, but because the exam expects muscle memory and pattern recognition you only get from repetition.
Lab environment access
You need a lab. Period. Physical FortiGate is nice if you have budget, but a FortiGate VM works perfectly fine, and cloud instances can work too if you can afford the runtime costs. The point is repetition: build something, break it on purpose, fix it, and then prove the fix with CLI output you can interpret. That's how you turn an NSE7_EFW-6.2 training course from "watched it once" into "can do it under pressure."
Best study materials for NSE7_EFW-6.2
Fortinet's official training aligned to Enterprise Firewall 6.2 is the obvious starting point, not because it's magical or exciting, but because it maps to what Fortinet thinks you should know and how they ask questions.
Documentation to focus on: FortiOS 6.2 admin guide, cookbooks, feature-specific docs, and release notes. Release notes sound boring, I know. They're not. They tell you what changed between builds and what got fixed, which is basically what troubleshooting in production is made of. Knowing what's supposed to work and what's a known bug.
Labs matter more than rereading the same chapter. Build an HA pair. Break it. Do IPsec with mismatched proposals on purpose. Turn on SSL inspection and watch what fails. Then fix it using the CLI and logs.
NSE7_EFW-6.2 practice tests and exam prep strategy
A good NSE7_EFW-6.2 practice test is useful for pacing and spotting weak areas you didn't know you had, not for memorizing answers verbatim. If a practice bank doesn't explain why you missed something and what the correct reasoning is, it's not helping much beyond making you feel busy.
For a study plan, I like two options depending on your current state: A 2 to 6 week sprint if you already do FortiGate work daily and you just need to formalize knowledge. A 6 to 10 week plan if you're rusty or you're learning routing and VPN troubleshooting concepts at the same time as exam prep. Either way, map everything back to the NSE7_EFW-6.2 exam objectives and keep a running "things I got wrong" list you review weekly.
Common mistakes candidates make: ignoring routing because "it's a firewall exam, not a routing exam," relying on GUI-only workflows, and not understanding inspection order well enough. Another big one is people don't read the question carefully and miss a detail like incoming interface or NAT mode, then pick an answer that would be right in a different scenario.
What to expect on exam day
Time management matters a lot because scenario questions can be wordy and dense. Don't get stuck trying to prove you're right on one question. Pick the best answer based on what the outputs and logs indicate, flag it if you're unsure, and move on. You can always come back.
For troubleshooting questions, force yourself to use a method: what's the traffic path, what's the route decision, what policy matches, what does the session table show, what do logs say, what does a packet sniff confirm. If you practice that sequence in your lab until it's automatic muscle memory, you'll feel calmer during the exam and make fewer dumb mistakes.
Certification renewal and validity
Fortinet changes program rules over time, so I'm not going to pretend a blog post is the source of truth here. Check Fortinet's official certification policy page for current validity periods and recertification requirements for NSE 7, because those details shift.
Version drift is real, by the way. FortiOS moves fast. Even if you pass on 6.2, your job may be on 7.x now or next year, and the concepts transfer but the menus, defaults, and behaviors can shift enough to trip you up if you're not paying attention. Keep your notes updated and reread release notes when you change versions in production.
FAQ (people also ask)
Commonly around $400 USD, but the final NSE7_EFW-6.2 exam cost depends on region, currency, local taxes, and Pearson VUE pricing in your specific country.
What is the passing score for NSE7_EFW-6
Conclusion
Wrapping this up
Okay, real talk here.
The Fortinet NSE7_EFW-6.2 exam? It's not something you just breeze through on a weekend after skimming a PDF. I've seen way too many people underestimate this beast and regret it. This is enterprise-level troubleshooting where you're expected to know FortiOS 6.2 firewall policies and NAT configurations cold, debug VPN tunnels that won't come up at 3am, and understand exactly how security profiles inspection flow works when a user complains their legitimate traffic got blocked. They're testing whether you can actually fix problems in production, not just recite textbook definitions.
The difficulty ramps up. Why?
You need real command-line comfort. You'll face scenarios where FortiGate routing and VPN troubleshooting require you to interpret debug output, trace packets through policy chains, and understand HA clustering and session synchronization well enough to know why sessions aren't failing over properly. If you haven't spent serious time in a FortiGate CLI troubleshooting real issues, you're gonna struggle with the depth they expect here. I say that from experience watching colleagues crash and burn.
Your study approach matters more than how many hours you log, the thing is. Sure, go through the official NSE7_EFW-6.2 training course and documentation. The FortiOS 6.2 admin guide is your bible. But couple that with actual lab time where you break things on purpose and fix them. Set up tricky policy scenarios, misconfigure your HA cluster, create NAT conflicts, then troubleshoot using FortiAnalyzer/FortiManager log analysis for troubleshooting like you would in the real world.
Not gonna lie.
The exam cost (typically around $400 depending on your region) and the NSE 7 EFW 6.2 passing score requirements (Fortinet keeps the exact number close to the vest, but expect you'll need to nail most questions) mean you don't want to walk in unprepared and burn your first attempt. Practice tests are big here. They expose gaps in your knowledge around specific exam objectives you might've glossed over, though I've got mixed feelings about relying too heavily on them. I once spent three weeks drilling practice questions only to find the real exam threw me curveballs I'd never seen in any prep material, which was humbling to say the least.
Here's the thing about certification renewal: Fortinet's recertification policies have shifted over the years, so check their current requirements because letting an NSE 7 Enterprise Firewall 6.2 certification lapse after all that work would be frustrating. Wait, actually, it'd be downright maddening.
If you're serious about passing the Fortinet NSE7_EFW-6.2 exam on your first shot, you need realistic practice questions that mirror the actual test format and difficulty. The NSE7_EFW-6.2 Practice Exam Questions Pack at /fortinet-dumps/nse7_efw-6.2/ gives you scenario-based questions that actually test troubleshooting skills, not just memorization. Use it to spot weak areas in your NSE7_EFW-6.2 study guide coverage, then go back and lab those topics until they're second nature. You've put in the work to get this far in the NSE track. Finish strong with prep materials that don't waste your time.