ECCouncil 312-49v10 (Computer Hacking Forensic Investigator (CHFI-v10))
ECCouncil 312-49v10 (CHFI v10) Overview
What the ECCouncil 312-49v10 CHFI v10 exam actually measures
The ECCouncil 312-49v10 CHFI v10 exam isn't just another multiple-choice security cert. This represents the current version of the Computer Hacking Forensic Investigator certification, validating hands-on skills in computer forensics investigation and digital evidence handling that actually matters when you're standing in front of a judge explaining your methodology. We're talking about real capabilities that hold up in court, not just theory you forget two weeks after passing.
The computer forensics investigator certification shows you can detect hacking attacks, properly extract evidence without contaminating it, document every single step of your investigation process, and present findings that'll survive cross-examination. I've seen brilliant techs who can image a drive perfectly but completely fall apart when opposing counsel starts grilling them about hash algorithms and write-blockers. CHFI v10 addresses that gap.
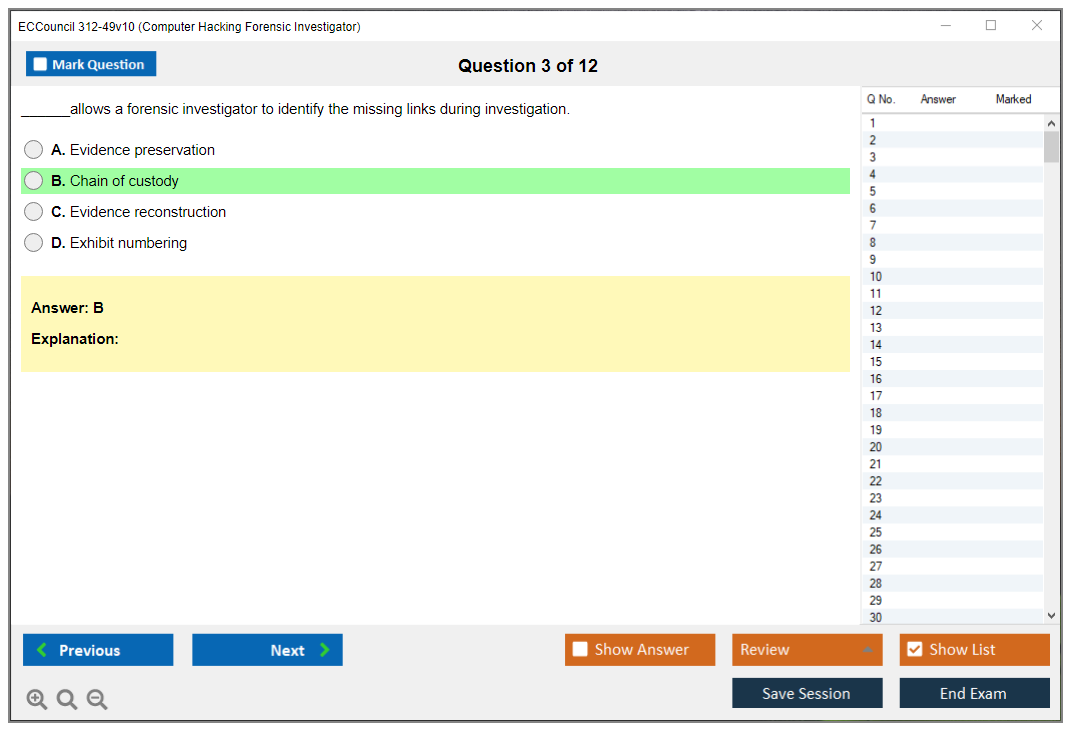
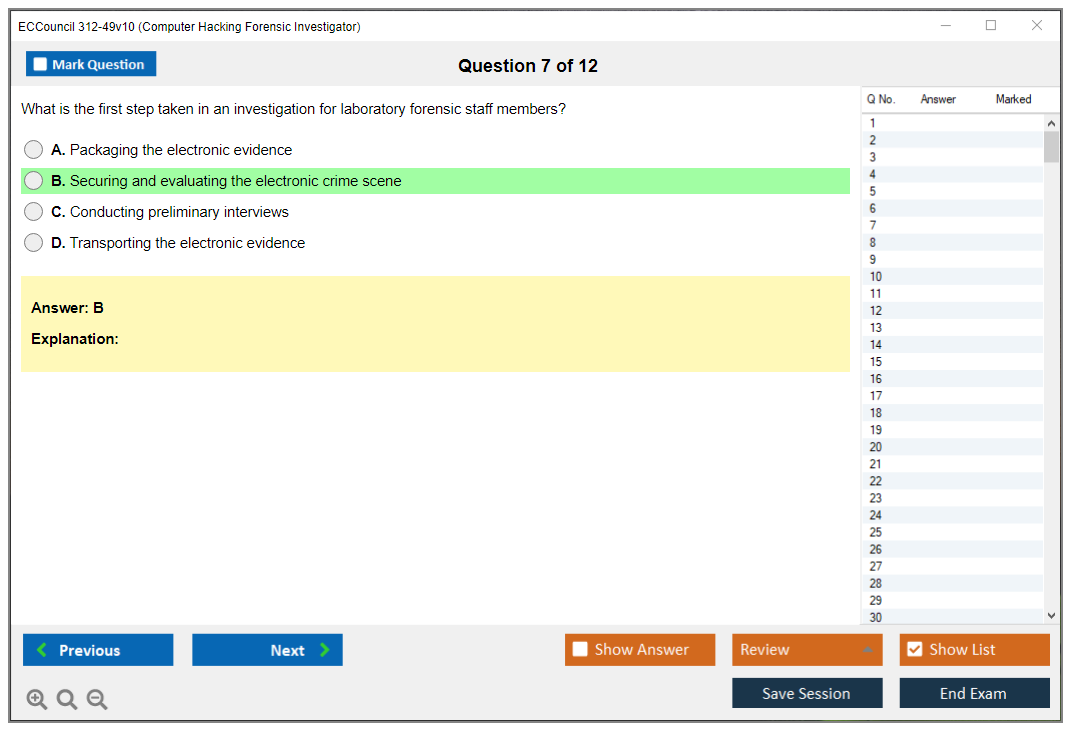
Skills measured? Long list. This exam covers practical abilities across evidence acquisition, analysis, reporting, and maintaining chain of custody throughout forensic investigations. Chain of custody is huge here. Break it once, and your entire case falls apart, no matter how solid your technical findings are or how many smoking-gun artifacts you recovered from unallocated clusters.
Who actually benefits from this certification
Digital forensics professionals are obvious candidates. But incident responders? They get massive value too. Cybersecurity analysts dealing with breaches, law enforcement personnel building criminal cases, IT auditors investigating internal incidents..all these roles benefit from CHFI v10. If you're in SOC work and want to move beyond alert-clicking into actual investigation, this cert opens doors you didn't even know existed.
The certification proves your ability to conduct forensic investigations on Windows, Linux, Mac, mobile devices, networks, cloud environments, and IoT systems. That's a lot of ground to cover. Some people still think forensics is just Windows registry analysis, but modern investigations span everything from Azure blob storage to Android app data to IoT device firmware dumps.
The EC-Council CHFI training and eligibility focuses on vendor-neutral forensic methods that work across multiple tools and platforms, which means you're not locked into EnCase or FTK or Autopsy. You learn principles that work regardless of your toolchain, and that matters when you join an outfit that's already standardized on different software or budget constraints force tool changes. I once consulted for a regional PD that switched forensic suites three times in four years due to licensing costs, and the investigators who understood underlying principles adapted fine while the tool-dependent folks struggled.
Why CHFI v10 matters in today's threat space
CHFI v10 tackles modern forensic challenges. Encrypted data, anti-forensics techniques, cloud storage analysis, volatile memory examination. Attackers know forensics exists, so they actively try to defeat it with timestomping, log wiping, fileless malware, and encryption-based evidence destruction that makes your job infinitely harder.
Version 10 updates reflect current attack vectors, modern operating systems, containerized environments, and emerging forensic technologies that weren't even considerations in earlier cert versions.
The certification distinguishes candidates in competitive job markets for forensic analyst, incident response, security operations, and compliance audit roles. When I see two resumes and one has CHFI while the other just lists "familiar with forensics," the CHFI holder gets the callback every time. Organizations seeking ISO 27001, GDPR, HIPAA, or PCI-DSS compliance value CHFI-certified professionals for breach investigation and evidence handling because you've proven you understand regulatory requirements beyond just reading a compliance checklist.
How CHFI v10 fits with other certifications
The exam emphasizes practical, real-world scenarios rather than pure memorization, requiring you to understand forensic workflows and tool application in ways that mirror actual casework. This isn't "what does this registry key mean?" It's more "given this timeline of events and these artifacts, reconstruct what the attacker did and when," which is a big difference from traditional certification approaches.
CHFI complements other EC-Council certifications like the Certified Ethical Hacker Exam (CEHv12) and EC-Council Certified Security Analyst (ECSA) in full security career paths. CEH teaches you offensive thinking, CHFI teaches you investigative rigor. Together? Powerful combination that makes you dangerous in the best possible way. It also stacks well with the Certified Incident Handler (ECIH) since incident response and forensics overlap heavily in real-world scenarios where you're simultaneously containing threats and preserving evidence.
CHFI v10 fits with NIST cybersecurity framework, SANS digital forensics guidelines, and international standards for evidence handling. Certification holders gain recognition for understanding legal requirements, expert witness testimony preparation, and courtroom presentation skills. Stuff that matters when you're sitting in a deposition explaining why your hash values prove file integrity and some attorney's trying to poke holes in your methodology.
What you're actually proving with this cert
The exam tests knowledge of forensic tool categories including disk imaging, file carving, timeline analysis, memory forensics, and network packet analysis. Memory forensics is getting massive attention lately because so many attacks live entirely in RAM and disappear the second you power down. The certification shows proficiency in both dead-box forensics (powered-off systems where you image drives) and live forensics (running systems where you capture volatile data before shutdown destroys critical evidence).
CHFI v10 prepares candidates for forensic challenges in hybrid work environments, remote investigation scenarios, and distributed infrastructure. Investigators now deal with evidence scattered across employee home networks, corporate VPNs, SaaS applications, and multi-cloud deployments where jurisdiction gets murky and data sovereignty laws complicate everything. The days of walking into an office and imaging one desktop? Long gone.
The exam tests understanding of forensic soundness principles, evidence integrity verification, and defensible investigation methods you'll actually use when building cases. You learn to identify, preserve, analyze, and present digital evidence that withstands legal scrutiny and cross-examination from attorneys who've been coached on how to discredit forensic findings.
CHFI certification signals commitment to ethical investigation practices, privacy considerations, and professional forensic standards. The kind of stuff that keeps you employed and out of malpractice situations where one procedural mistake tanks an entire investigation.
Organizations also value how CHFI holders understand legal frameworks around data collection, which matters if you work alongside Certified SOC Analysts or Threat Intelligence Analysts. You bring the investigative discipline that turns their detections into actionable evidence packages that legal teams can actually use instead of just interesting technical observations.
CHFI v10 Exam Details
ECCouncil 312-49v10 (CHFI v10) overview
The ECCouncil 312-49v10 CHFI v10 exam is how EC-Council proves you can actually think like someone who investigates computer crimes for a living. You collect evidence, build timelines, identify artifacts, and figure out how to explain what you discovered without completely destroying the legal case before it even starts. This is not "hacking." It's investigating. Totally different headspace.
Who takes it? SOC analysts pivoting into DFIR work, incident responders who keep getting asked to "make everything court-ready," and IT generalists who basically got voluntold to manage incident response and evidence handling since their company doesn't have anyone dedicated to forensics. You know the type.
CHFI v10 exam details (312-49v10)
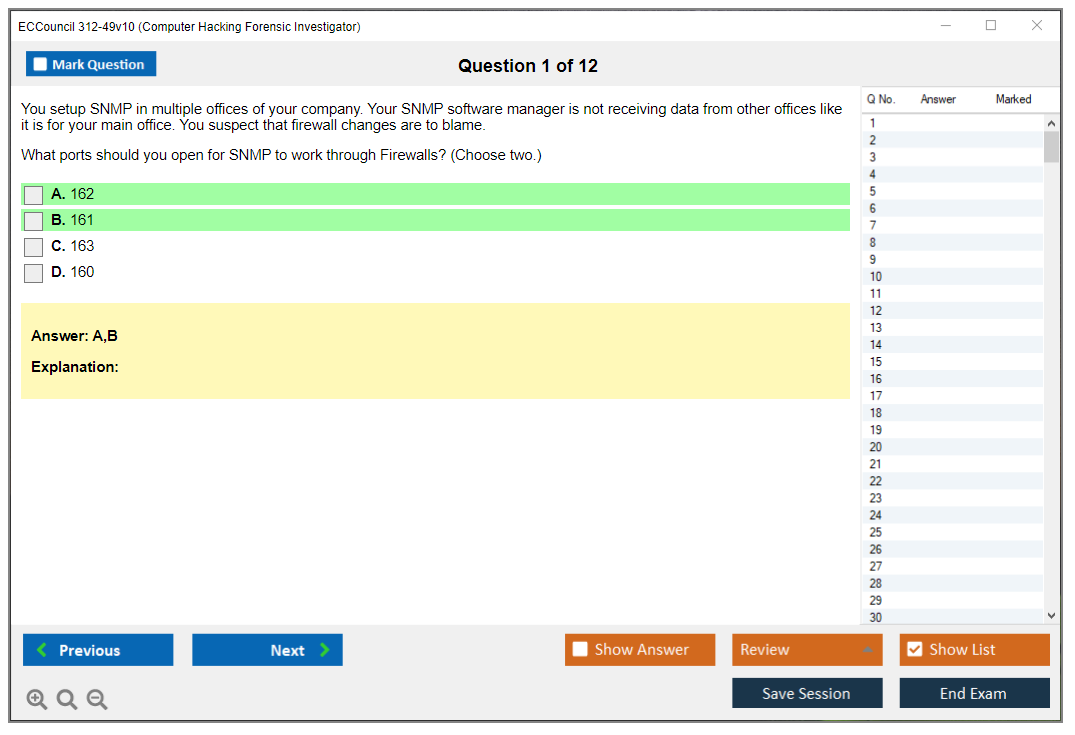
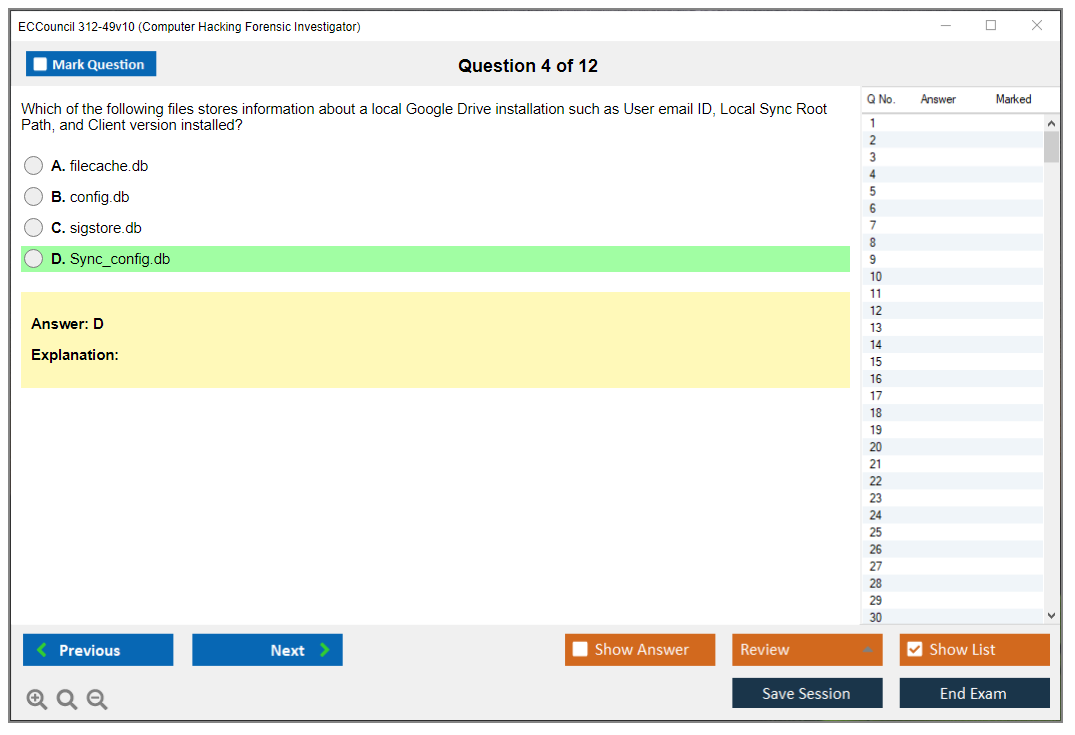
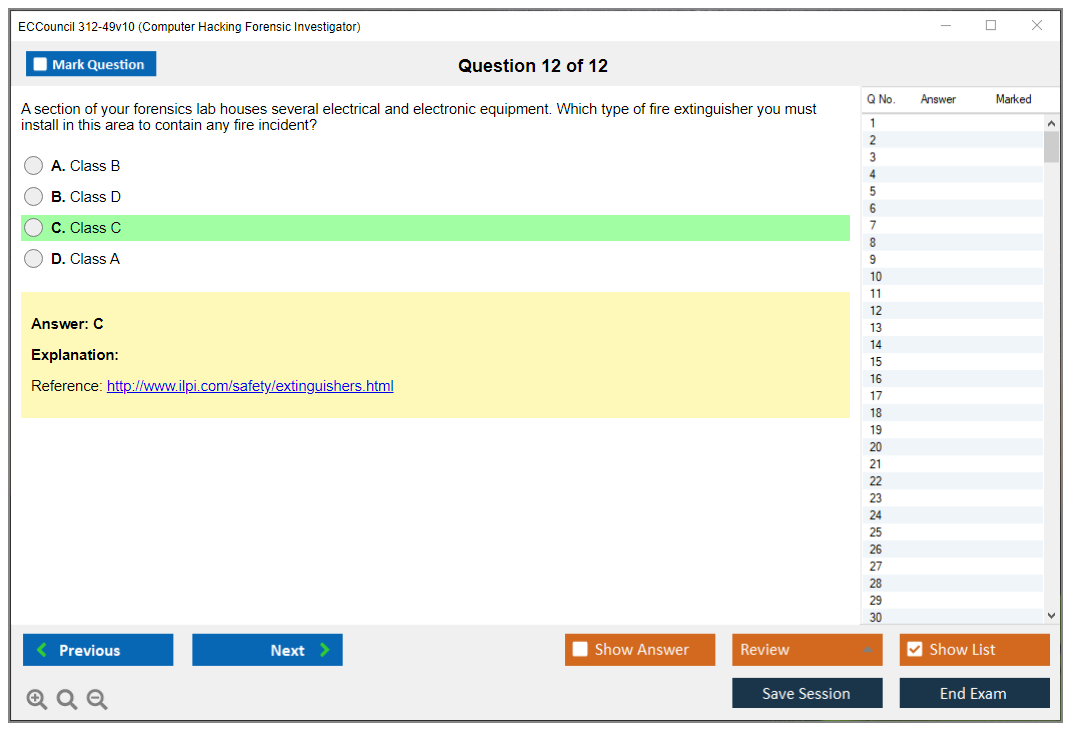
The ECCouncil 312-49v10 CHFI v10 exam throws 150 multiple-choice questions at you. Delivered through Pearson VUE testing centers or proctored online sessions, you get four hours total. That breaks down to roughly 1.6 minutes per question, which sounds luxurious until you're staring at massive scenarios about logs and timestamps and "which step should the investigator prioritize next" and you're re-reading the same paragraph for the third time wondering if you missed something.
Computer-based testing. You get immediate preliminary pass/fail results when you finish. That moment is honestly intense. Quiet. Then either relief washes over you or frustration kicks in hard.
Question formats vary. Some are straightforward single-answer multiple choice, others are scenario-based nightmares where you're analyzing forensic situations, picking correct sequences, or deciding what evidence actually holds up in court. Tool-identification questions appear too. You don't need to marry one specific vendor, but you absolutely need to recognize which type of tool fits which job and why, especially concerning forensic tools and chain of custody protocols.
CHFI v10 exam objectives (domain breakdown)
EC-Council describes CHFI v10 exam objectives as 11 primary domains, but most candidates notice the actual content sprawls across a much wider topic range in practice. Cloud, malware, mobile, IoT. Wait, that's more than 11 already. Either way, you're getting tested across the complete investigation lifecycle, from initial intake all the way through final reporting.
Here's the domain coverage you'll want to study against:
- Domain 1: Computer Forensics in Today's World (8-10%), legal frameworks, roles, ethics stuff.
- Domain 2: Computer Forensics Investigation Process (10-12%), phases, evidence handling, documentation requirements.
- Domain 3: Understanding Hard Disks and File Systems (12-14%), covers FAT, NTFS, ext, HFS+, partition tables.
- Domain 4: Data Acquisition and Duplication (14-16%), imaging techniques, write blockers, hashing, verification steps.
- Domain 5: Defeating Anti-Forensics Techniques (8-10%), encryption, steganography, wiping, artifact removal tactics.
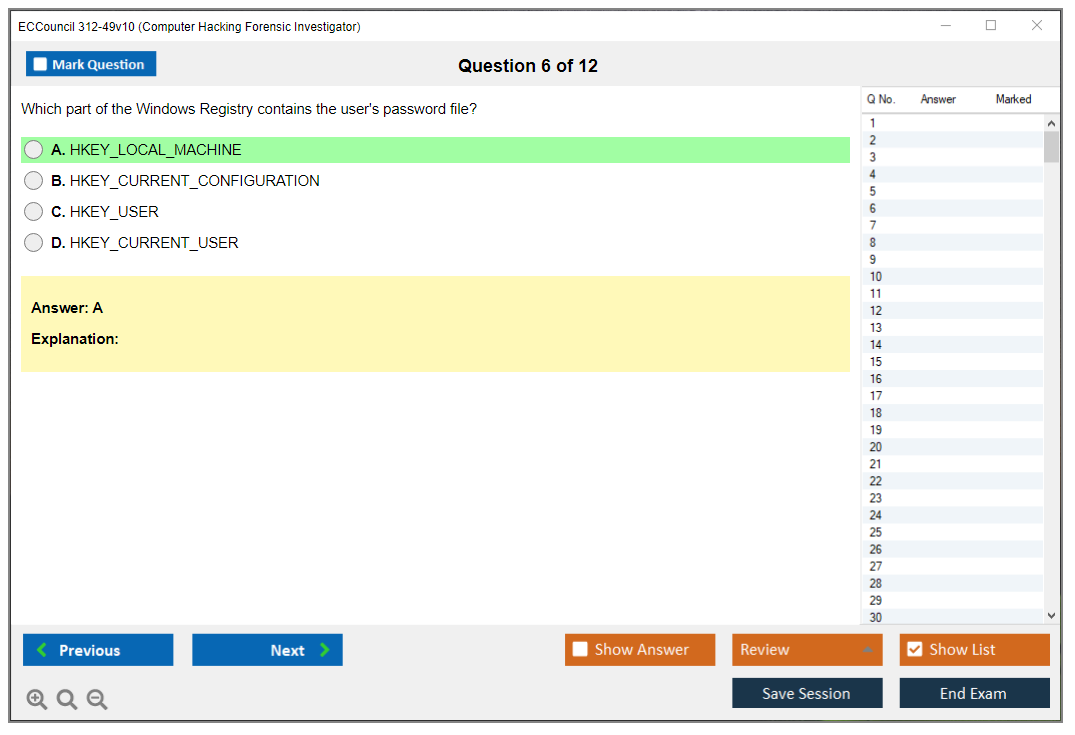
- Domain 6: Windows Forensics (12-14%), registry analysis, event logs, user artifacts, critical system files.
- Domain 7: Linux and Mac Forensics (8-10%), log files, command history, Mac-specific artifacts.
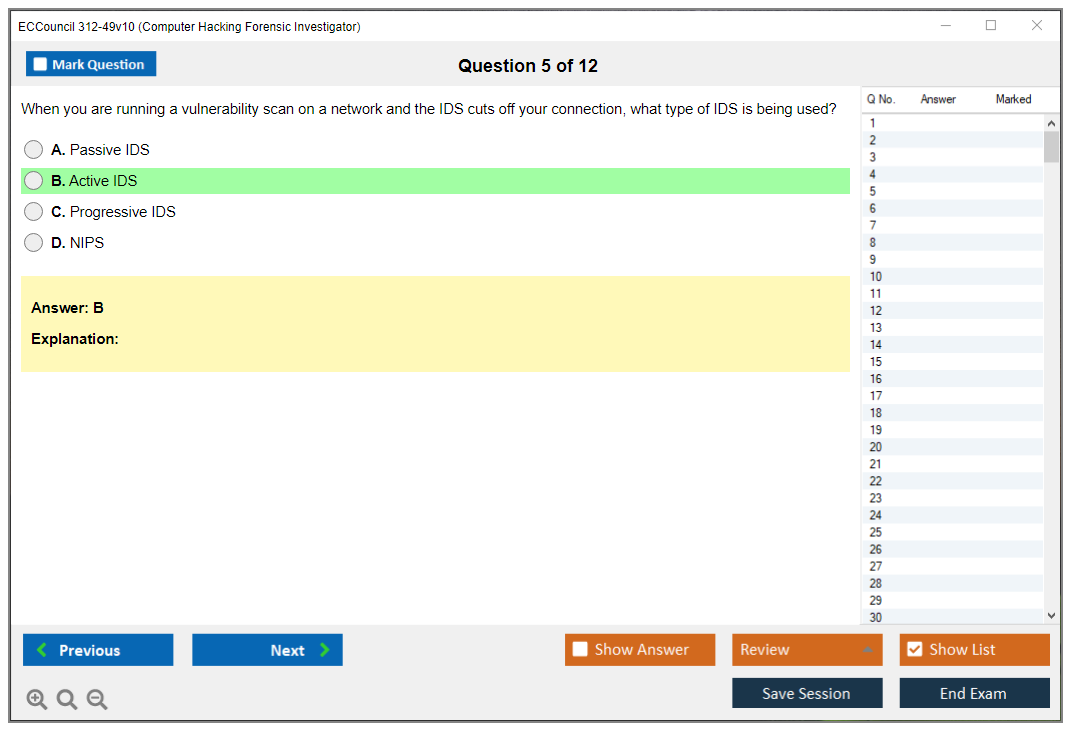
- Domain 8: Network Forensics (10-12%), PCAP analysis, protocol dissection, IDS data, traffic reconstruction.
- Domain 9: Investigating Web Attacks (8-10%), web server logs, application indicators, database evidence trails.
- Domain 10: Dark Web Forensics (6-8%), Tor networks, crypto tracing methods, anonymous communications.
- Domain 11: Database Forensics (4-6%), transaction logs, recovery procedures, SQLi evidence patterns.
- Domain 12: Cloud Forensics (6-8%), SaaS/PaaS/IaaS distinctions, APIs, multi-tenancy challenges.
- Domain 13: Malware Forensics (8-10%), behavioral analysis, basic code review, timeline reconstruction.
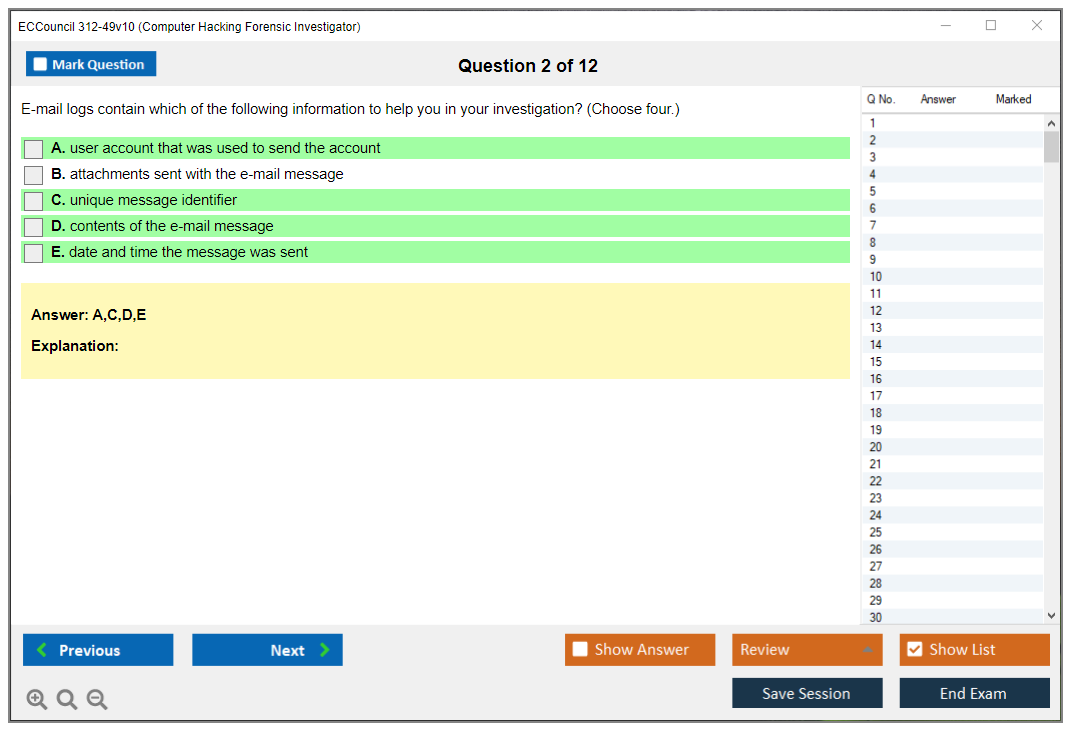
- Domain 14: Investigating Email Crimes (6-8%), header analysis, phishing indicators, server-side artifacts.
- Domain 15: Mobile Forensics (8-10%), iOS/Android differences, app data extraction, SIM card artifacts.
- Domain 16: IoT Forensics (4-6%), embedded device analysis, IoT network traffic patterns.
Yeah, that's more than 11. EC-Council's public summaries and training materials don't always line up cleanly with how candidates actually experience the blueprint, so treat this as the practical "what actually shows up" list and map your digital forensics exam preparation accordingly.
What's new in CHFI v10 vs prior versions
CHFI v10 updates lean heavily into modern reality: expanded cloud forensics coverage, cryptocurrency investigation methods, container forensics techniques, and way better treatment of current mobile platforms. That matters because honestly a ton of older forensics exams feel like they're still living in some fantasy world where every single case is just a Windows desktop and a USB drive. That's absolutely not what most organizations are dealing with nowadays. I once watched a junior analyst spend three days hunting through ext4 filesystems because nobody told him the evidence was sitting in a containerized database on AWS the whole time. Fun.
What the exam is really testing
The exam hits both theory and practical application. It's not a lab exam (no hands-on component), but the scenario questions absolutely test your decision-making under pressure: what to collect first, how to properly preserve it, when to perform full imaging versus quick triage, what to document at each stage, and how to avoid contaminating evidence that'll get thrown out later. Expect tons of "best next step" questions, plus compliance minutiae like chain of custody labeling requirements, storage protocols, transfer procedures, and report-writing expectations that matter in court.
Reporting matters. A lot. Executive summary skills. Technical detail balance. Findings presentation format. Also courtroom fundamentals: legal admissibility standards, expert witness responsibilities, testimony preparation techniques. People skip this section. Then they absolutely pay for it on exam day when those questions appear.
Cost, scoring, and the stuff people ask anyway
CHFI v10 certification cost varies wildly by region and voucher source, and EC-Council pricing changes semi-regularly, so your safest move is budgeting based on official store pricing plus whatever proctoring rules apply in your country, then shopping around for authorized training bundles if you actually need them. Retakes can sting financially. Plan accordingly.
For CHFI 312-49v10 passing score, EC-Council doesn't always publish one single fixed number the way some vendors do, and scoring can be presented as scaled or exam-form dependent depending on the version you get. On test day, you'll just see pass/fail immediately when you finish, then your official detailed report arrives after.
Difficulty, prerequisites, and prep reality
CHFI v10 exam difficulty sits at "medium-hard" if you've done actual real-world investigations, and jumps to "hard" if you've only watched tool demos on YouTube or sat through vendor webinars. Compared to CEH or Security+, it's less about memorizing buzzwords and way more about process discipline, artifact identification, and documentation rigor. Time management's the silent killer here, because those long scenario questions devour minutes frighteningly fast.
CHFI v10 prerequisites depend on whether you go through EC-Council CHFI training and eligibility routes or apply based purely on work experience. Either way, you'll want solid comfort with Windows internals, basic Linux operations, networking fundamentals, and evidence handling workflows that actually make sense.
For CHFI v10 study materials, pick resources that teach underlying concepts without being weirdly vendor-biased toward one tool ecosystem. Know what cryptographic hashing actually proves. Understand why write blockers exist physically. Know which artifacts live where in different operating systems. Add CHFI v10 practice tests, but don't treat them like gospel truth. Treat them more like timing drills and weak-area detectors that expose gaps. Then go actually practice with disk images, log files, and PCAPs, because just memorizing definitions won't save you when the question asks what you should do next in a multi-step investigation.
CHFI certification renewal
CHFI certification renewal operates as part of EC-Council's continuing education model, with a specific renewal cycle and continuing education credit requirements plus associated fees. Track your credits as you earn them throughout the period. Keep receipts and documentation. Audits happen randomly, and arguing after the fact is a complete waste of everyone's time.
FAQs
How much does the EC-Council CHFI v10 exam cost? It depends on voucher source and geographic region, so check current EC-Council pricing and authorized partner rates, then add retake budget buffer.
What is the passing score for CHFI 312-49v10? EC-Council may not provide a single fixed number publicly. Expect pass/fail notification at completion and detailed breakdown on your official score report.
Is the CHFI exam hard compared to CEH or Security+? Usually harder than Security+ and more process-heavy than CEH, with way more "what would you do" scenario-based questions.
What are the CHFI v10 exam objectives and domains? They cover the complete lifecycle, including disks, acquisition, Windows/Linux, network, web, cloud, malware, mobile, and reporting components.
How do I renew my CHFI certification and how often? Follow EC-Council's renewal cycle requirements, pay associated fees, and submit continuing education credits on time.
CHFI v10 Cost and Fees
What you're actually paying for CHFI v10
The actual cost? Honestly, it's complicated. The CHFI v10 certification cost completely depends on which route you're taking because there isn't just one fixed price that covers everything you'll need. When you purchase the exam voucher directly through EC-Council or one of their authorized partners, you're looking at $550-$650 USD, but that's really just your baseline starting point. I've watched people spend anywhere from that bare minimum exam fee all the way up to $5,000+ depending on whether they go for official training courses or try piecing together their own preparation strategy.
Regional pricing complicates things. Currency exchange rates and local testing center fees can inflate your costs by 10-20% if you're taking the test outside the US. Some international markets just get hit harder.
Now, here's where the real budget shock happens: official training packages from EC-Council. Their instructor-led training typically falls between $3,500-$5,000 USD. Yeah, that includes your exam voucher, courseware, hands-on lab access, and practice exercises as one package, but not gonna lie, that price makes tons of people immediately start hunting for alternatives. Third-party training providers? They're offering CHFI prep courses in the $1,200-$2,500 range, often throwing in exam vouchers with study resources that sometimes feel way more practical than the official materials. I know someone who went third-party and actually preferred the no-nonsense approach over all the official polished content.
Self-study versus structured training costs
Self-study route? It lets you dodge those massive training fees entirely. You just purchase the exam voucher separately and handle your own prep work, which brings your total certification cost down to basically the exam fee plus whatever study materials you decide to grab. EC-Council's iLearn platform sits somewhere in the middle ground with online self-paced training for $850-$1,200 that gives you 6-12 months of access to course materials. It's neither full instructor-led courses nor complete DIY.
Your study materials budget needs actual planning. Official EC-Council courseware runs $200-$400 when purchased separately. Supplementary books add another $50-$100. Practice test subscriptions cost $50-$150. You're realistically looking at an additional $300-$650 stacked on top of that exam fee. Lab environment setup? It varies wildly. Completely free if you're comfortable building virtual machines and working with open-source forensic tools, but potentially $200+ if you want commercial forensic tool trial licenses for practicing with enterprise-grade software.
Training boot camps deliver intensive 5-day CHFI preparation ranging from $3,000-$4,500 including instruction, materials, labs, and exam voucher. These condensed formats work great when your employer's footing the bill and you need certification fast, but honestly the compressed timeline can be absolutely brutal for actually retaining knowledge. Virtual training options slash costs by eliminating travel expenses while still giving you live instruction and interaction with certified instructors.
Hidden costs and budget considerations
Retake fees? Budget for these upfront. When your first attempt doesn't pan out, retake vouchers cost exactly the same as initial exam fees. That $550-$650 hits your wallet again. Some training packages include one free retake voucher, which honestly provides valuable insurance if exam difficulty worries you. The retake policies let candidates who fail reschedule within specific timeframes, though waiting periods between attempts can seriously delay your certification timeline.
Testing center fees get bundled into your exam voucher price, but online proctored exams may require specific equipment like a quality webcam and reliable high-speed internet. If you need to purchase or upgrade equipment, tack on another $50-150.
Travel costs matter for in-person training at locations distant from home. Lodging, meals, time away from work. It all adds up ridiculously fast. I've watched colleagues drop $1,000+ on travel expenses for a week-long boot camp on top of the training fee.
Discounts and reimbursement options
Some employers maintain certification reimbursement programs covering exam fees upon successful completion or as professional development benefits. Government and military personnel may access discounted training through specific EC-Council government programs or agency training contracts that aren't publicly advertised anywhere. Group training discounts become available when organizations send multiple employees through official CHFI training at the same time. Corporate training contracts may negotiate volume pricing for multiple certifications across EC-Council's entire certification portfolio.
Annual membership in professional organizations like ISSA, HTCIA, or InfraGard occasionally provides member discounts on EC-Council certifications, though honestly these savings typically only knock off 10-15% of exam fees.
Subscription-based training platforms offer another cost-effective alternative here. Cybrary, Pluralsight, and INE provide CHFI preparation content for $30-$100 monthly, which works perfectly if you can dedicate focused study time and don't need formal course structure. Free resources including EC-Council webinars, community forums, and sample chapters help reduce overall preparation costs, though you'll still need quality practice tests and lab environments.
Long-term costs and return on investment
Certification maintenance includes annual fees of $80-$100 and continuing education activities to maintain your active credential status. Factor these recurring costs into your multi-year budget because letting your certification lapse means potentially retaking the entire exam.
Tax deductions? Professional development may offset certification costs for self-employed consultants or business owners, something definitely worth discussing with your accountant.
The investment return considerations justify these costs for tons of candidates. Salary increases of $5,000-$15,000 annually, new job opportunities, and career advancement potential make the initial outlay worthwhile in most cases. I've seen digital forensics roles that simply won't interview candidates without CHFI certification. It becomes less of an optional credential and more of a mandatory career expense in specific job markets.
Compare your total cost of ownership across training paths before committing to anything. Related certifications like the Certified Ethical Hacker Exam (CEHv12) or EC Council Certified Incident Handler (ECIH v3) might offer better value depending on your career goals and current skill level.
CHFI 312-49v10 Passing Score and Scoring
ECCouncil 312-49v10 (CHFI v10) overview
The ECCouncil 312-49v10 CHFI v10 exam is the Computer Hacking Forensic Investigator cert test. It proves you can handle a real investigation workflow, not just name-drop tools. We're talking acquisition, preservation, analysis, and reporting here. Real work. Paperwork too.
This cert fits SOC folks moving into forensics, incident responders who keep getting pulled into evidence handling, and sysadmins who somehow became the "log person" at 2 a.m. Also consultants. Students. Different reasons, but same exam.
CHFI v10 exam details (312-49v10)
Format's straightforward.
150 questions, 4 hours, no adaptive weirdness. Everybody gets the same number of questions, and unanswered counts wrong. That last part bites people who read too slowly or get stuck arguing with themselves about two "almost correct" options, which happens more than you'd think.
Question types? Mostly multiple choice. The vibe is "do you know the process" mixed with "do you know what this artifact means." You'll see material tied to CHFI v10 exam objectives, like chain of custody, acquisition methods, hash verification, Windows and Linux artifacts, email and web traces, investigation reporting. Not every test form's identical, because the pool's randomized, but the blueprint stays consistent.
What's different versus older versions? More modern environment coverage and more focus on workflow and defensible handling, not just clicking around in a tool. That's good. But it means memorizing tool menus won't save you.
CHFI v10 cost and fees
People always ask about CHFI v10 certification cost. The thing is, it depends where you buy and what bundle you pick. Exam vouchers often land in a few-hundred-dollar range, and official training can push the total way up if you go all-in with EC-Council packages. Self-study's cheaper. It can also be messier, which I've seen firsthand.
Retakes are where budgeting gets real. There's a waiting period, commonly 14 days between attempts, and multiple consecutive failures can trigger longer waits or extra steps. That's not punishment, it's there to stop panic-retake behavior where people just burn vouchers and learn nothing.
If you want a low-cost way to pressure-test readiness, a targeted practice pack can help, like the 312-49v10 Practice Exam Questions Pack at $36.99. Not magic. But useful.
CHFI 312-49v10 passing score and scoring
The CHFI 312-49v10 passing score is set at 70%. That's 105 correct answers out of 150, based on EC-Council's published exam standards. That threshold's EC-Council's line for minimum competency, meaning you're expected to know enough to operate like a safe, effective investigator who won't break evidence handling, chain of custody, or basic analysis hygiene when someone's job or a lawsuit's on the line.
Scoring's raw.
Correct answers add up, incorrect answers don't subtract, and there's no negative marking. So you should guess if you're down to two options, because leaving it blank's the same as wrong, and you only have 4 hours to get through everything. Time management matters. Not glamorous. Still true.
You get an immediate preliminary pass/fail when you finish, whether you're at a test center or using online proctoring, and then the official score report shows up by email within 24 to 48 hours. Here's the part that annoys number-people: the report doesn't give your exact numerical score, and it can't be reverse-engineered into a percentage because EC-Council doesn't disclose precise results or question-by-question outcomes.
Instead, you get domain-level performance indicators like "Above Target," "Near Target," or "Below Target." That feedback's useful if you fail because it tells you where to focus next, and it lines up with your CHFI v10 study materials plan and whatever labs you're doing, even if you can't point to the exact missed items. I know that frustrates some folks but it makes sense from a security angle.
Also, EC-Council applies psychometric analysis and difficulty weighting behind the scenes to keep standards consistent across different versions of the exam, since the question pool's randomized. The published passing standard stays at 70% across testing windows, but the specific questions vary, so chasing "the minimum" is a bad strategy. Aim higher. Employers don't care that you scraped by. They care that you can do incident response and evidence handling without improvising your way into a mess.
One more practical point. Score confidentiality's a thing. Results go to you, not your boss, not your school, not a recruiter, unless you choose to share.
I had a colleague once who passed with what he claimed was "exactly 70 percent" based on his own tally during the exam. Guy spent the entire debrief lunch trying to calculate backward from the domain feedback. Never got anywhere with it, but he was convinced there was a pattern. There wasn't.
CHFI v10 difficulty: how hard is the exam?
CHFI v10 exam difficulty depends on whether you've done actual investigations. If you've handled imaging, hashing, triage, timelines, and basic reporting, you'll recognize the logic. If your background's purely pentest or purely theory, you might struggle because forensics is slower, more procedural, and way more picky about documentation.
Common fail reasons?
People ignore process questions. They underestimate legal and reporting topics. They rely on CHFI v10 practice tests without doing hands-on tool work. Another big one's spending too long on early questions and then speed-clicking the final 30. That's how you donate a passing score.
CHFI v10 prerequisites and eligibility
EC-Council has eligibility rules that can involve training paths or experience documentation, so check current CHFI v10 prerequisites before you schedule. Background-wise, you want comfort with Windows internals, basic Linux, networking, and incident response workflows. Logs. Filesystems. Permissions. The boring stuff. The important stuff.
Best CHFI v10 study materials
Official courseware's structured, but it can be expensive and sometimes heavier on reading than doing, which isn't everyone's learning style. I like mixing it with labs where you practice imaging, validate hashes, and walk through artifacts with a checklist. Notes help too. Chain of custody forms. Report templates. Simple stuff that keeps you consistent under stress.
If you're shopping for practice questions, the 312-49v10 Practice Exam Questions Pack is an affordable way to find weak domains early, then go back to the objective list and patch gaps with labs instead of just rereading slides.
CHFI certification renewal
CHFI certification renewal is where people get surprised later. You pass, your score validity starts right away, and the certification becomes active once eligibility requirements are verified. But staying certified means tracking the renewal cycle, fees, and continuing education submissions. Keep receipts. Keep documentation. Audits happen.
FAQs (quick hits)
How much does the EC-Council CHFI v10 exam cost?
Voucher pricing varies by channel and bundle, and training can change the total a lot, so budget for exam plus any retake buffer. For cheaper prep testing, the 312-49v10 Practice Exam Questions Pack is $36.99.
What is the passing score for CHFI 312-49v10?
70%, or 105 out of 150 correct.
Is the CHFI exam hard compared to CEH or Security+?
Harder if you haven't done forensics work, easier if you already live in artifacts, timelines, and reporting.
What are the CHFI v10 exam objectives and domains?
They cover acquisition, preservation, analysis across systems and artifacts, plus documentation and legal considerations. Use the official objectives list as your checklist.
How do I renew my CHFI certification?
Follow EC-Council's renewal cycle rules, pay renewal fees, submit continuing education credits on time, and keep proof in case of audit.
CHFI v10 Difficulty: How Hard Is the Exam?
Difficulty factors: forensics concepts, tools, and legal requirements
CHFI v10's moderately challenging. Honestly.
If you're walking in with nothing but textbook theory, you'll get crushed because the exam doesn't just want theoretical understanding. It demands you actually know how forensic investigation workflows operate in the real world. Memorizing tool names gets you absolutely nowhere when you're staring at scenario-based questions that require you to think through multi-layered investigation pathways.
What really makes this thing brutal? Breadth across 16 domains plus deep technical detail. You've gotta understand tool capabilities conceptually without actually touching them during the exam, which destroys a lot of candidates. I mean, clicking through EnCase or FTK in some controlled lab environment? That's easy. Answering questions about which forensic approach actually works when you're handed a complex investigation scenario that could branch five different ways? Completely different beast.
Practical scenarios separate winners from losers.
These aren't basic recall questions like "What's SMTP's port?" Instead, you're handed an investigation scenario and need to apply forensic principles. Determine best evidence collection approaches, identify which artifacts actually matter, or explain chain of custody preservation in specific situations. The exam's testing whether you understand "why" behind procedures, not just "what" steps you're supposed to follow.
Legal and procedural stuff? That crushes candidates from pure IT backgrounds. Evidence handling standards, chain of custody requirements, courtroom admissibility criteria. Most sysadmins or security analysts never touch this stuff. If you've never documented an investigation knowing it might land in court, this feels unnecessarily rigid and, the thing is, completely foreign to your experience. I once watched a candidate with a decade of network security experience completely freeze on a basic admissibility question because he'd simply never dealt with legal preservation requirements.
Technical depth gets brutal fast. File system structures, disk geometry, partition analysis, low-level data organization. These require storage technology background that tons of security professionals simply lack. Questions about Master File Table structure or journal parsing aren't trivial whatsoever. Network forensics demands protocol understanding, packet analysis, log correlation, traffic pattern recognition across multiple layers, and you'd better know both theory and practical application or you're sunk.
Who finds CHFI easiest versus hardest
Candidates with hands-on investigation experience? They handle this better.
If you've actually worked cases, collected evidence, written reports, testified about findings, the exam scenarios feel familiar because you've dealt with investigations' messy reality where nothing goes exactly as textbooks describe.
Pure infosec backgrounds struggle hard without forensics experience. You might crush malware analysis questions and understand network protocols perfectly, but evidence preservation rigor and documentation requirements feel like overkill. Law enforcement folks sometimes find technical depth challenging despite rock-solid understanding of legal and procedural requirements. I mean, registry forensics and partition analysis aren't exactly police academy curriculum.
Legacy systems plus modern technologies? Weird knowledge gaps everywhere.
You need understanding of older Windows versions and traditional file systems while simultaneously knowing cloud forensics, container investigations, mobile platforms. Career changers and entry-level candidates typically require 200-300 hours preparation compared to experienced investigators who can manage 100-150 hours if they're already doing this work daily.
Not gonna lie. Candidates without Windows registry analysis experience get absolutely destroyed by those questions. Registry forensics and artifact interpretation appear frequently, and if you've never actually parsed NTUSER.DAT or analyzed UserAssist keys, you're just guessing blindly. Linux and Unix forensics prove equally difficult for Windows-focused professionals unfamiliar with command-line tools, log locations, Unix file permissions.
Common reasons candidates fail
Time pressure amplifies everything else.
Four hours for 150 questions sounds reasonable until you're actually sitting there analyzing complex scenarios. That works out to roughly 1.6 minutes per question, and some scenarios demand careful deliberation about multiple technically correct options to identify the "best" answer.
The tool-agnostic approach constantly trips people up. You can't just memorize clicking through Autopsy or X-Ways. You must understand forensic capabilities conceptually, what artifacts each tool type extracts, what analysis techniques apply to different evidence types, how to prioritize investigative steps. Similar to how 312-50v12 tests ethical hacking concepts rather than specific exploitation tool interfaces.
Anti-forensics techniques coverage requires understanding encryption, steganography, timestomping, artifact elimination methods attackers employ. Memory forensics concepts include process analysis, malware detection in RAM, volatile data extraction. These challenge candidates without live forensics experience hard. Mobile forensics complexity stems from diverse platforms, frequent OS updates, app sandboxing, encryption implementations changing constantly.
Cloud forensics difficulty arises from distributed data, multi-tenancy complications, limited direct access, dependency on service provider cooperation for pretty much everything meaningful.
Database forensics requires SQL knowledge and transaction log understanding. Email forensics covers header analysis and SMTP protocol knowledge. Dark web and cryptocurrency investigation topics present challenges due to anonymization technologies and blockchain concepts most people barely grasp.
IoT forensics introduces embedded systems. Limited logging. Proprietary protocols.
Each domain's deep enough that you absolutely can't fake your way through.
Failure reasons include inadequate hands-on practice, over-reliance on memorization, poor time management, gaps in specific domain knowledge. Honestly, if you haven't actually imaged a disk, analyzed memory dumps, or correlated logs from multiple sources, you're at a serious disadvantage compared to practitioners. The 312-49v10 practice exam questions pack helps tremendously with scenario familiarity and time management, letting you identify weak areas before the actual exam destroys you.
Compared to other forensic certifications? CHFI v10's easier than GIAC GCFE but more thorough than 212-82 or the forensics portions of CompTIA CySA+. Experienced forensic practitioners with 2+ years hands-on investigation work typically find difficulty manageable with proper preparation.
But make no mistake. This exam requires real understanding of forensic investigation workflows, not just surface-level familiarity with concepts.
CHFI v10 Prerequisites and Eligibility
CHFI v10 prerequisites and eligibility
The ECCouncil 312-49v10 CHFI v10 exam isn't a free-for-all. People think it is. You can sometimes just register and show up, but EC-Council actually gates exam eligibility in a surprisingly rigid way. If you ignore that upfront you're gonna waste time, money, and momentum right when you should be laser-focused on digital forensics exam preparation instead of drowning in bureaucratic paperwork and verification emails.
Two real routes exist. That's it. No shortcuts.
EC-Council's official stance on CHFI v10 prerequisites boils down to this: either you complete their official training, or you prove you've been neck-deep in information security work long enough to justify sitting for a computer forensics investigator certification exam. I actually appreciate the clarity even though the admin process feels painfully corporate.
The two eligibility pathways EC-Council accepts
EC-Council offers two primary eligibility pathways for the CHFI 312-49v10 exam:
- Training-based eligibility (complete official CHFI v10 training)
- Experience-based eligibility (submit application with verified work history)
Training's the "easy button." Experience is the "prove it to us" route. This difference totally changes how fast you can book your test date, plus it can really shift your total CHFI v10 certification cost once you factor in that sneaky extra fee nobody mentions until checkout.
Training-based pathway (automatic eligibility)
Complete official training? You're eligible. This pathway involves taking an EC-Council CHFI v10 instructor-led course, the online self-paced iLearn course, or training delivered through an authorized partner. After that you can schedule the exam without mailing additional documentation or sitting around waiting for EC-Council to arbitrarily decide whether your job titles "count" according to some mysterious internal rubric.
Fast. Clean. Way less stress.
You've still gotta pass the actual exam though. That's where CHFI v10 exam difficulty becomes real, because the content hammers process, artifacts, and procedure instead of just superficial tool trivia and vendor marketing fluff. But eligibility-wise, training-based is straightforward, which explains why tons of employers push it hard even when the training bill makes finance people visibly wince.
Quick reality check: official training costs bounce around wildly depending on region and delivery method, so it can absolutely dominate your CHFI v10 certification cost compared to someone who qualifies through experience and just buys an exam voucher outright. Casually mentioning it since prices fluctuate constantly.
Experience-based pathway (application + verification)
Not gonna sugarcoat this. It's the route most working pros desperately want, because they've already got the background and they'd much rather spend precious time on CHFI v10 study materials and endless lab reps than sit through a full course rehashing stuff they've done for years. But it comes with annoying admin steps.
To qualify via experience, you submit an eligibility application with solid documentation showing at least two years of information security related work experience. EC-Council reviews it to verify the experience really connects to CHFI domains, which includes things like incident response and evidence handling, basic investigative workflow, and the kind of methodical thinking you need to respect forensic tools and chain of custody instead of just "pulling random logs and desperately hoping something useful appears."
There's also a non-refundable eligibility application fee of $100 tacked onto experience-based applications. That's on top of exam voucher costs, which catches people off guard. So if you're comparing paths strictly by dollars and cents, don't conveniently forget that extra hundred bucks. You definitely can't claw it back if you change your mind or the application gets rejected for missing critical details.
Approval time usually runs a few business days. EC-Council commonly quotes something like 5 to 10 working days depending on application volume, completeness, and whether they need clarification on vague job descriptions. Don't treat this like a Friday-night impulse buy where you're planning to test next Tuesday.
What counts as "acceptable experience"
EC-Council's hunting for information security experience that connects to investigation, monitoring, auditing, or response. Not necessarily "I was a full-time forensic examiner with a crime lab badge." Acceptable roles commonly include security analyst, incident responder, IT auditor, network administrator, and other related information security positions.
Some are obvious. Some are borderline. Job titles lie constantly.
If you're technically a network admin but you've spent two solid years doing firewall reviews, log analysis, phishing investigations, endpoint triage, or actively helping with containment efforts during incidents, that's the kind of granular detail that makes an application way stronger. If you're an IT auditor who mostly lives in soul-crushing policy documents but you also validate logging configurations, access controls, and evidence retention practices, that can map surprisingly well too. CHFI isn't exclusively about flashy tools. It's about method, documentation, and making defensible decisions under pressure.
Side note: I've seen people get approved with the strangest combinations of experience. One guy was primarily a database admin but had done breach response work for six months during a ransomware nightmare at his company. He documented it thoroughly and got approved within a week. Another person with a "security engineer" title got rejected initially because their job description read like generic IT support. Specificity matters more than fancy titles.
Recommended background (what helps even if it's not "required")
Even though the formal eligibility requirement is just training or experience, the practical prerequisite for not suffering through this cert is having a solid baseline in Windows, Linux, networking, and security operations. You'll constantly run into artifacts and workflows that assume you understand file systems, processes, ports, authentication mechanisms, and basic investigative logic. The exam loves testing whether you know what to do first, what to preserve, and what not to contaminate like a rookie.
A few examples that matter way more than people initially think:
- Chain of custody: if you can't explain it cleanly you'll lose easy points and struggle with nuanced scenario questions
- Hashing and imaging: this shows up everywhere and ties directly to evidence integrity and courtroom admissibility
- Reporting: dry as toast, yes, but it's part of the job and maps to the way CHFI deliberately words tricky questions
The rest, like hyper-specific vendor tools, gets mentioned constantly in marketing materials. You should still practice with them, but don't over-index on memorizing tool screenshots instead of understanding underlying forensic process.
Documentation tips (so you don't get stuck)
If you're going the experience path, treat the application like you're crafting a mini case note: crystal-clear dates, crystal-clear responsibilities, and enough specificity that a reviewer can connect your work to CHFI topics without playing guessing games. Include concrete examples of what you did related to investigations, monitoring, audits, response workflows, or evidence handling procedures. Keep everything grounded in reality.
Also, plan your timeline around this approval process. While you're waiting on eligibility confirmation, you can still start mapping your study plan to the CHFI v10 exam objectives, line up CHFI v10 practice tests (avoid sketchy outdated dumps), and get realistic about how scoring actually works. People obsessively ask about the CHFI 312-49v10 passing score even though EC-Council's published policy is that it varies by exam form.
Want feedback? Tell me your current role and a quick bullet list of what you actually do week to week. I'll tell you which eligibility pathway I'd pick and exactly how I'd word the experience description to match EC-Council CHFI training and eligibility expectations.
Conclusion
Wrapping it all up
Look, you don't just pass this thing.
The ECCouncil 312-49v10 CHFI v10 exam demands real forensic knowledge. Not just theory but actual understanding of how evidence acquisition works, how chain of custody gets maintained, and how you'd handle a live investigation without contaminating everything. Which, honestly, happens more than anyone wants to admit. The CHFI v10 exam objectives cover Windows artifacts, Linux filesystem forensics, network packet analysis, mobile device extraction, and reporting procedures that hold up in court. That's a lot to absorb.
The thing is? The CHFI v10 exam difficulty sits somewhere between accessible for experienced IR folks and pretty challenging for anyone coming in cold. If you've worked tickets involving malware cleanup or user activity timelines, you'll recognize scenarios instantly. If not, expect to struggle with tool outputs and interpretation. The forensic tool space alone can overwhelm newcomers.
The CHFI 312-49v10 passing score policy from EC-Council isn't always published openly, but most candidates report needing around 70% or better. The scaled scoring means you won't know your exact percentage, just pass/fail. Not gonna lie, that uncertainty adds pressure you don't need.
The CHFI v10 certification cost adds up fast when you factor in the exam voucher (typically $550-950 depending on region and whether you bundle training), official courseware if you go that route, and potential retake fees if things don't go your way the first time. CHFI v10 prerequisites technically require either attending official training or submitting work experience documentation, which can delay your exam scheduling if you're unprepared. Bureaucracy at its finest. I mean, who enjoys that process? And once you earn it, CHFI certification renewal kicks in every three years. You'll need continuing education credits and another fee to stay current.
Side note: I've seen people blow their entire professional development budget on one cert attempt, then scramble when their employer won't cover the retake. Plan accordingly.
Honestly?
For digital forensics exam preparation that actually sticks, you need CHFI v10 practice tests that mirror the real question styles. I mean really mirror them. Scenario-based prompts about evidence handling, tool selection for specific artifact types, legal considerations during seizure. Generic practice dumps won't cut it because the exam tests applied knowledge of forensic tools and chain of custody procedures, not just memorization of definitions.
Before you schedule, grab the 312-49v10 Practice Exam Questions Pack and work through it multiple times. Focus on your weak domains, whether that's memory forensics, email header analysis, or mobile extraction procedures, and drill until the workflow feels automatic. Almost second-nature. This computer forensics investigator certification proves you can handle real casework. Make sure your prep reflects that reality.